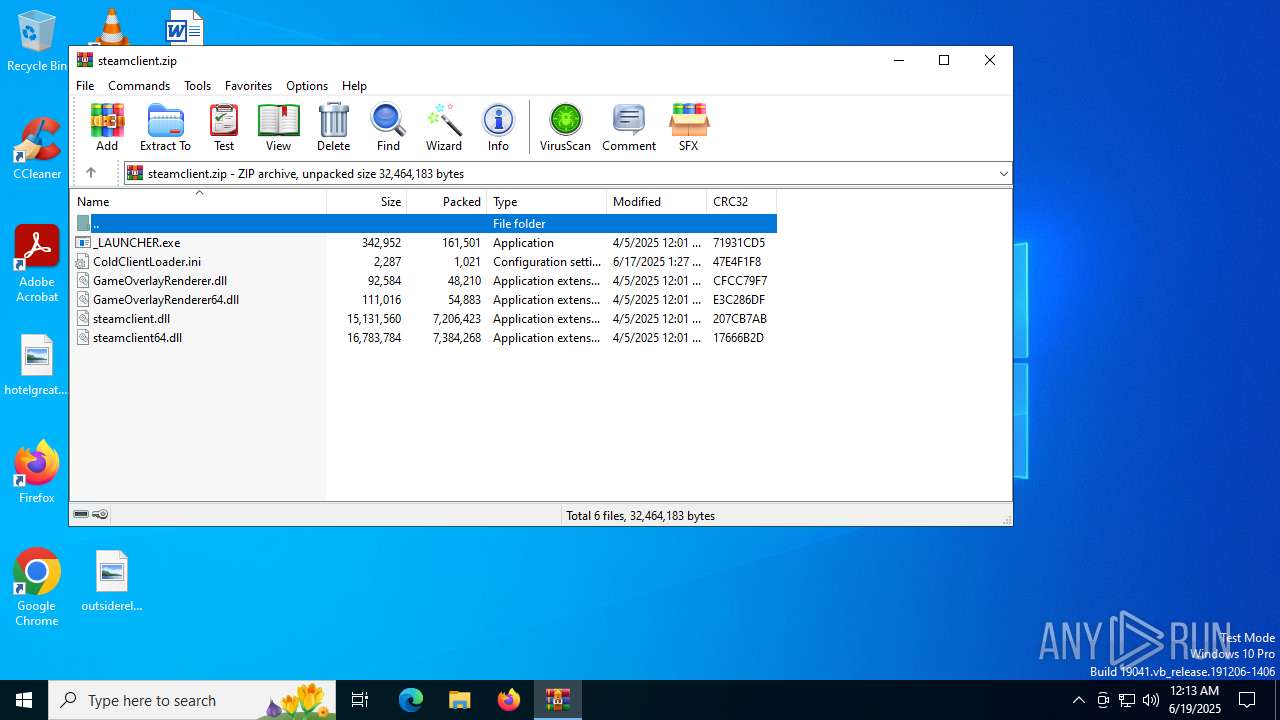
| File name: | steamclient.zip |
| Full analysis: | https://app.any.run/tasks/ff0198cf-f8e4-49f0-a4ec-f34aa5c7ae48 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 00:13:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3FC76A4EC97328036690B44301CE302F |
| SHA1: | B6C961B438D1A9E2DD1D5015BBAF05759FF601FD |
| SHA256: | 0A98BE2AD44FFE8D01A77FB3B2848BE1D82BFAFE02A770948AECC54F51A1FD84 |
| SSDEEP: | 98304:eQ20F0oXLL/+lhQARUKpPhfbZ4njSC4pRJo5pjIBLuT59i711kVNh+z3T0gddEml:eI7IYmKgXcCUHS+2efY7YamiGXU4M |
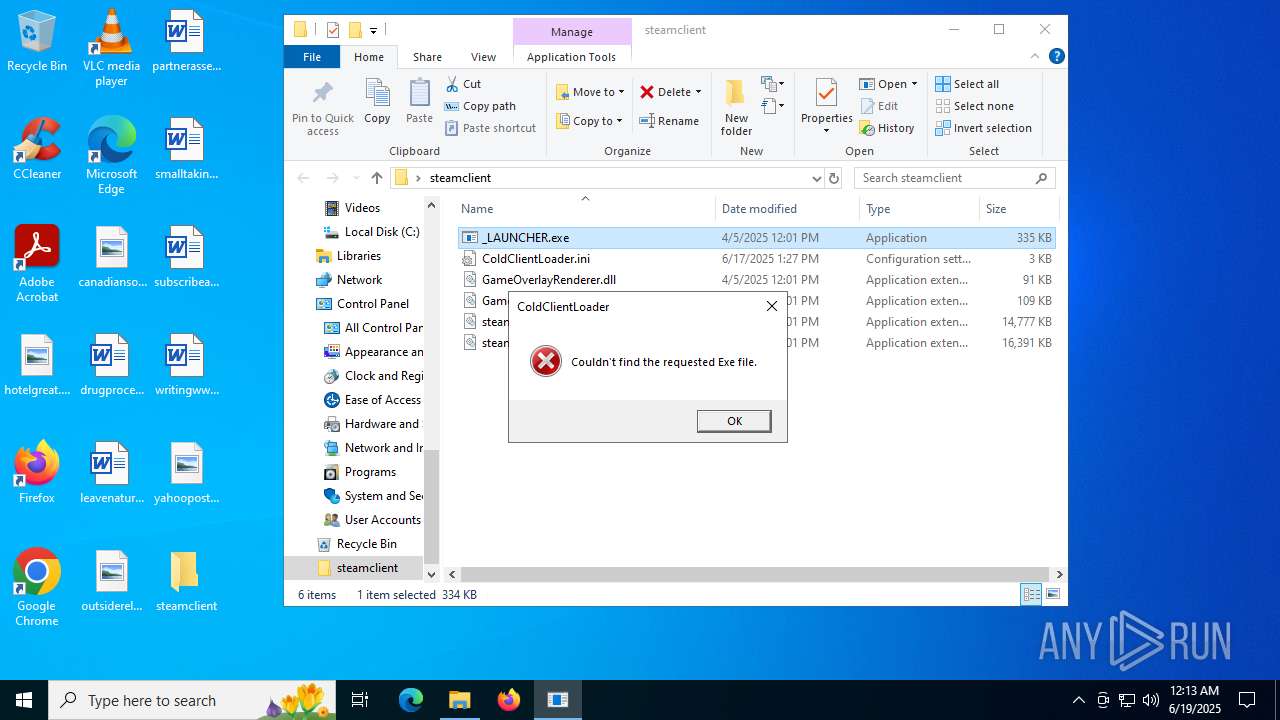
MALICIOUS
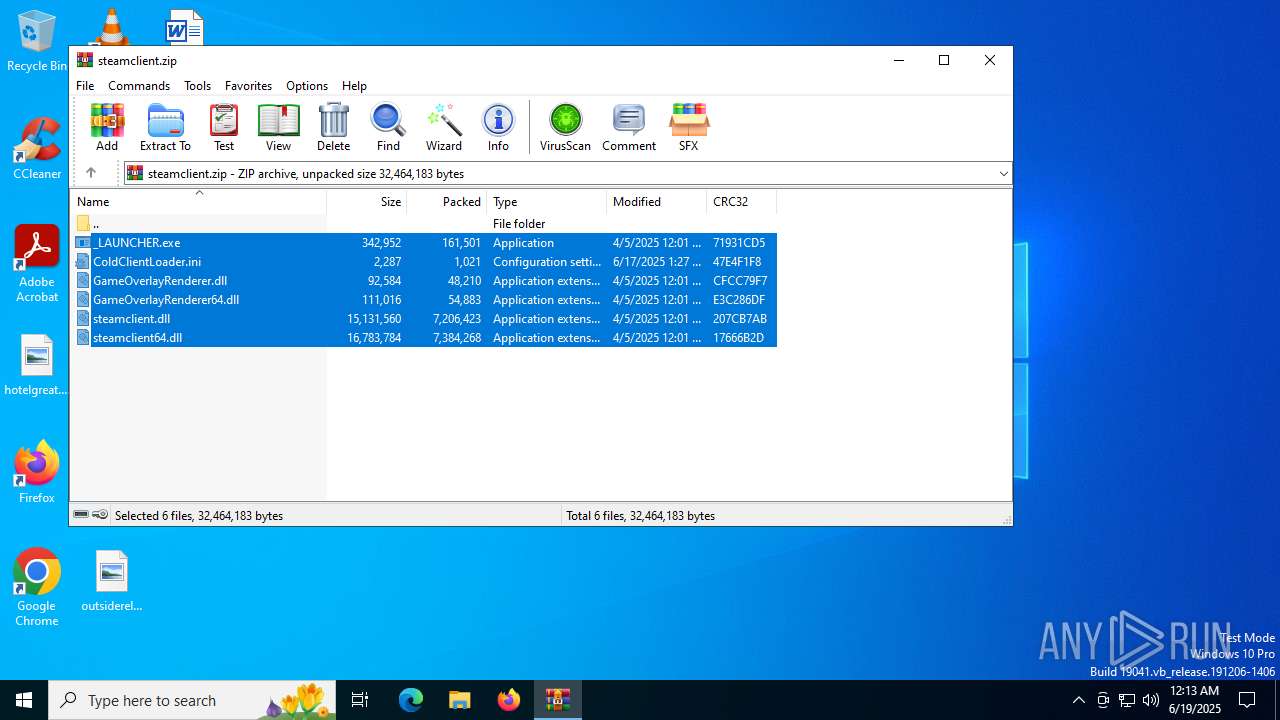
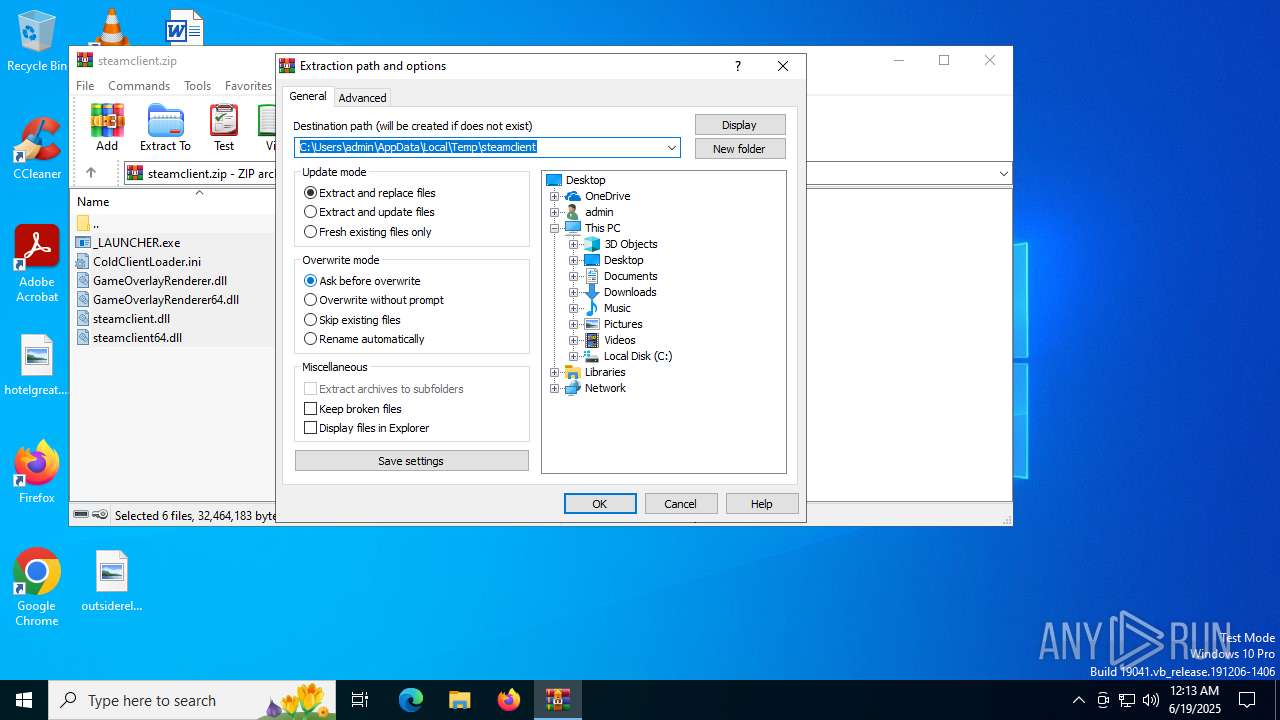
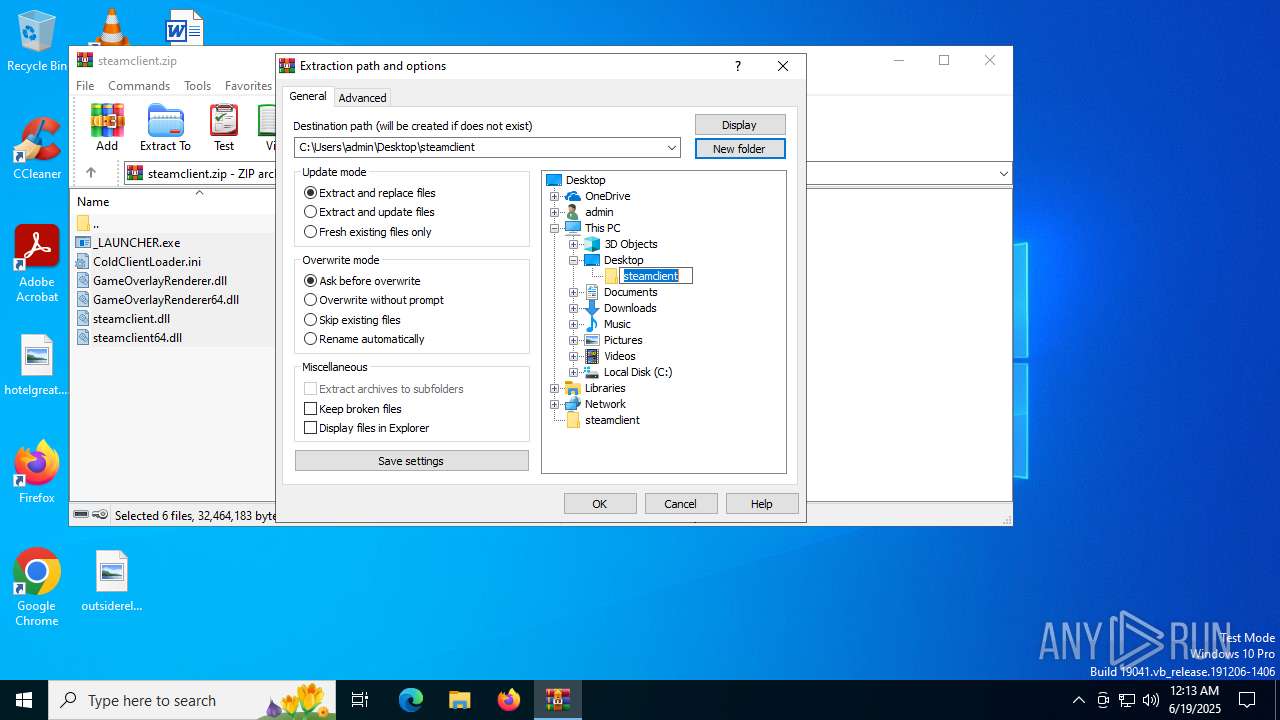
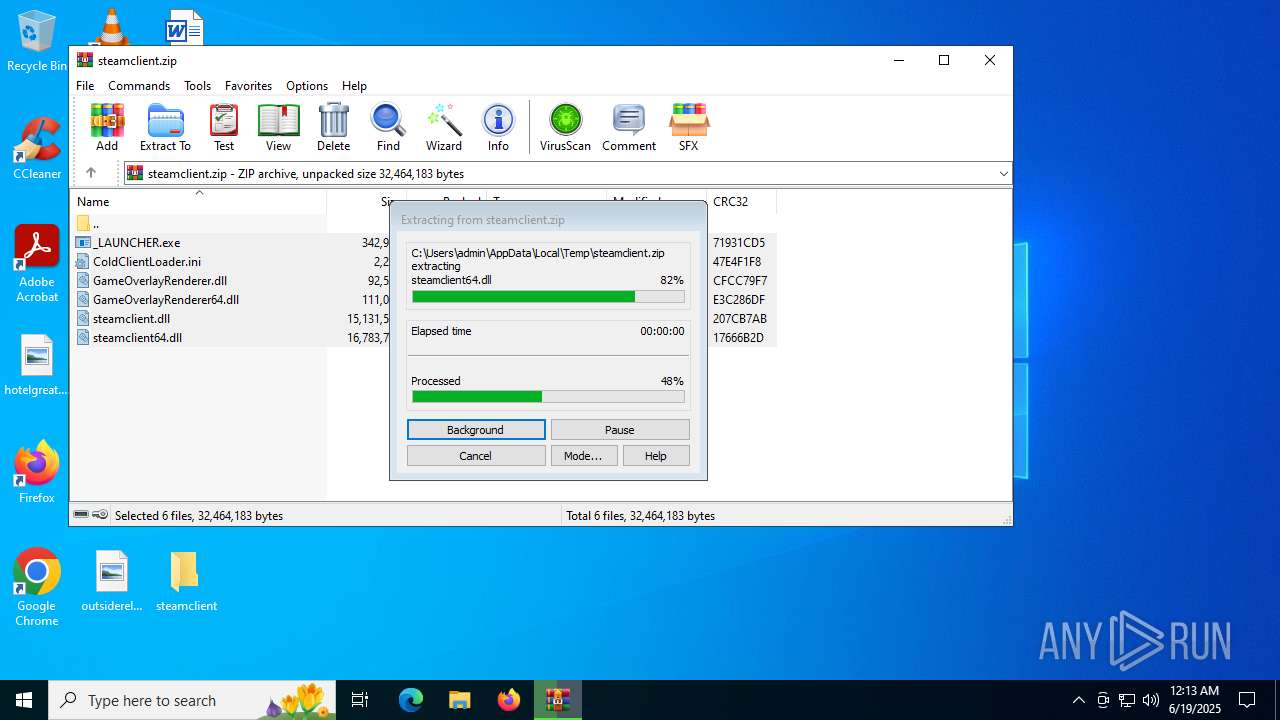
Generic archive extractor
- WinRAR.exe (PID: 6684)
Executing a file with an untrusted certificate
- _LAUNCHER.exe (PID: 3720)
SUSPICIOUS
No suspicious indicators.INFO
Manual execution by a user
- _LAUNCHER.exe (PID: 3720)
The sample compiled with english language support
- WinRAR.exe (PID: 6684)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6684)
Checks supported languages
- _LAUNCHER.exe (PID: 3720)
Reads the computer name
- _LAUNCHER.exe (PID: 3720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:05 14:01:38 |
| ZipCRC: | 0x207cb7ab |
| ZipCompressedSize: | 7206423 |
| ZipUncompressedSize: | 15131560 |
| ZipFileName: | steamclient.dll |
Total processes
139
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2468 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2532 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
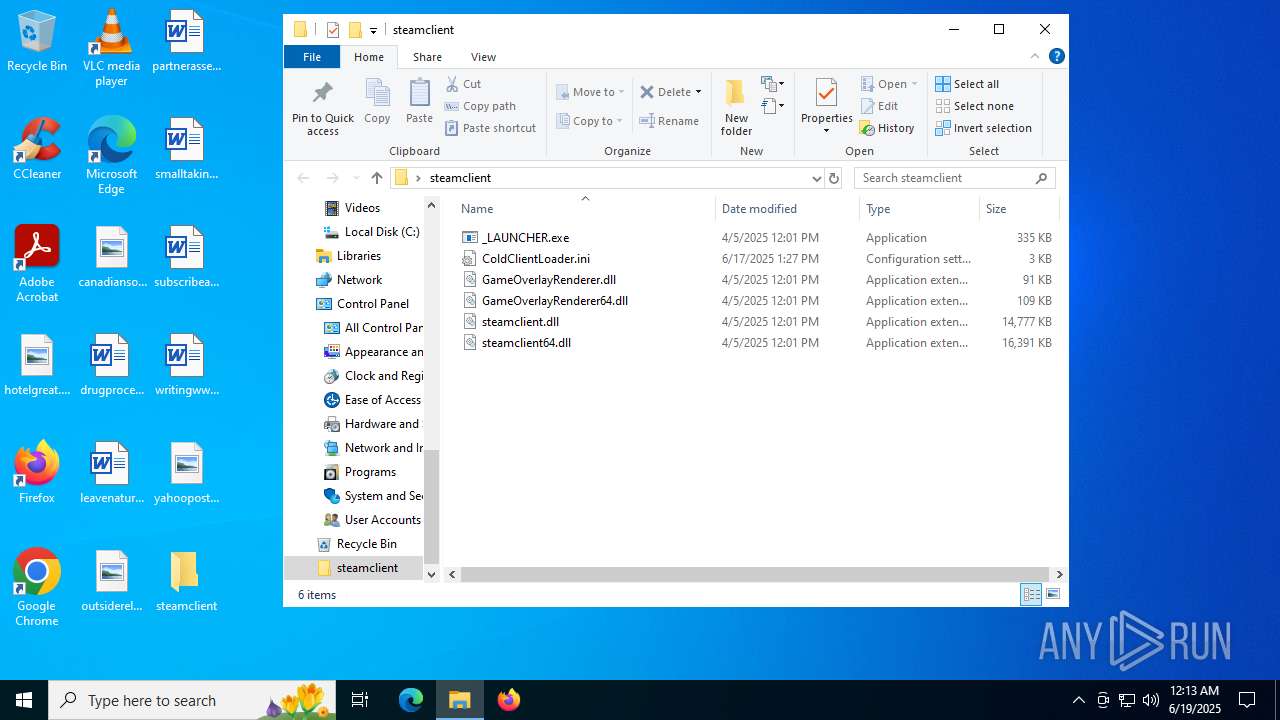
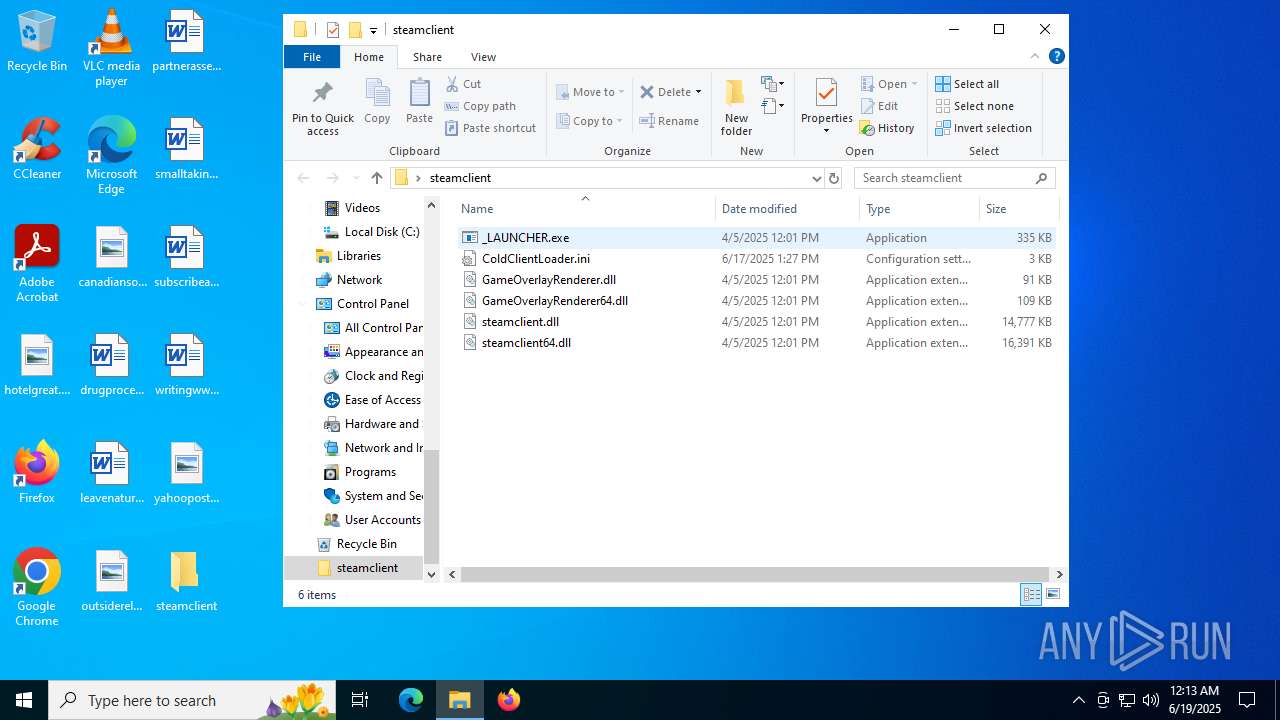
| 3720 | "C:\Users\admin\Desktop\steamclient\_LAUNCHER.exe" | C:\Users\admin\Desktop\steamclient\_LAUNCHER.exe | — | explorer.exe | |||||||||||
User: admin Company: GSE Integrity Level: MEDIUM Description: GSE Exit code: 1 Version: 08.56.38.63 Modules
| |||||||||||||||
| 6684 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\steamclient.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 560
Read events
2 526
Write events
21
Delete events
13
Modification events
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\steamclient.zip | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
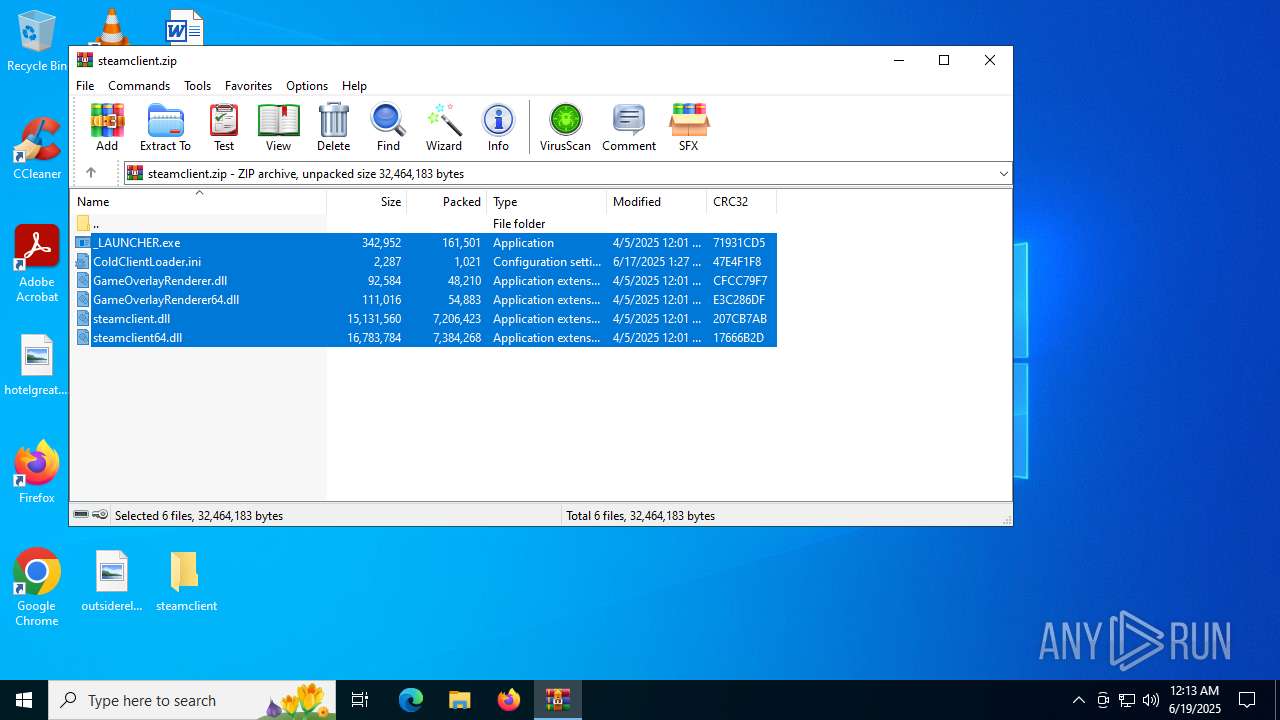
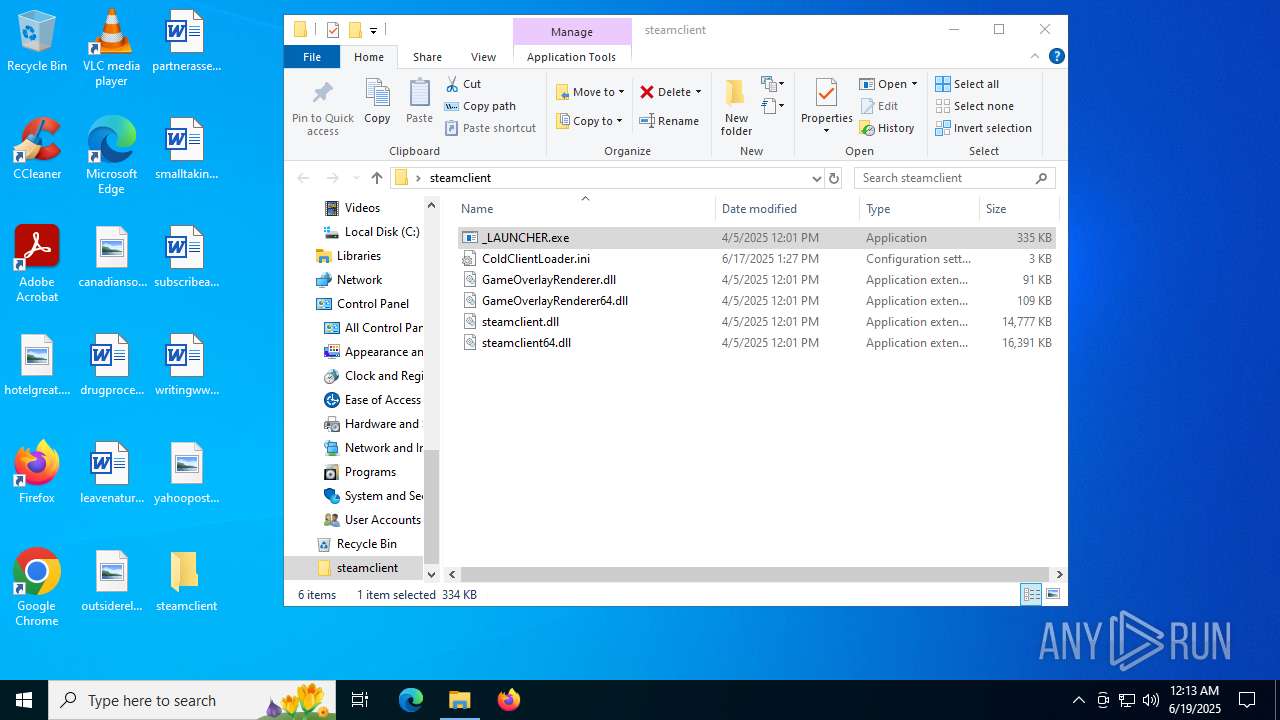
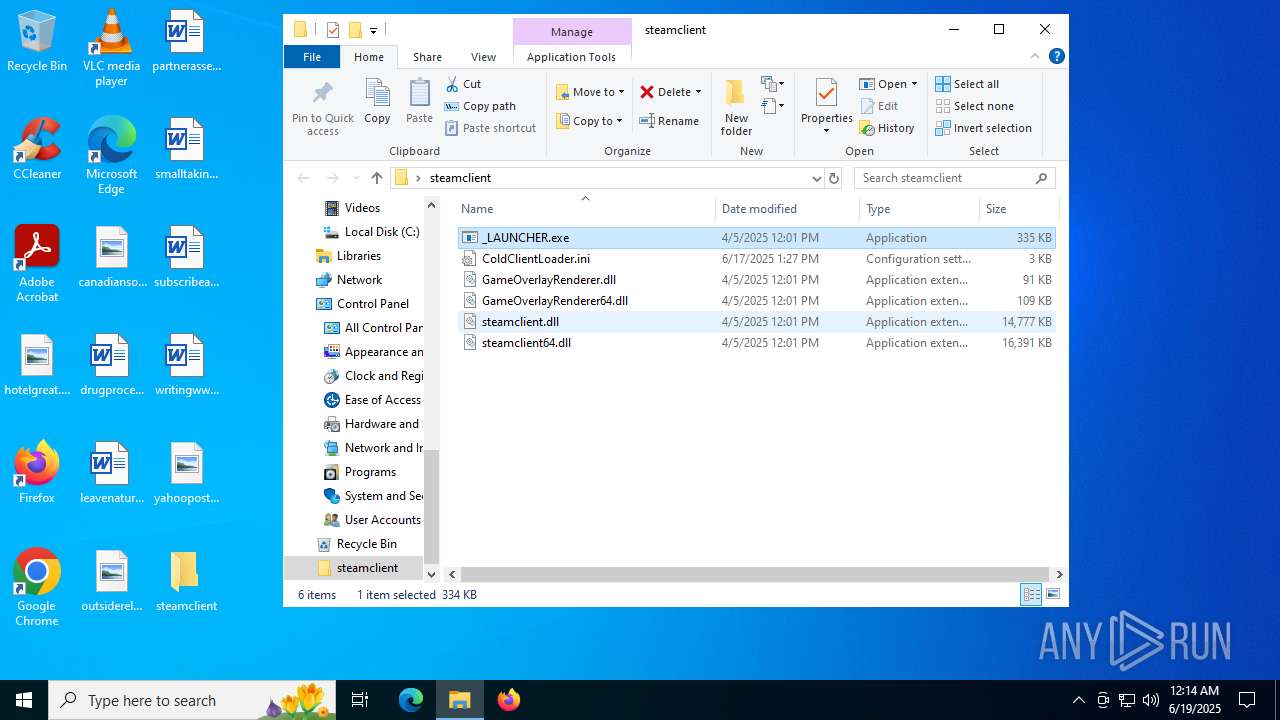
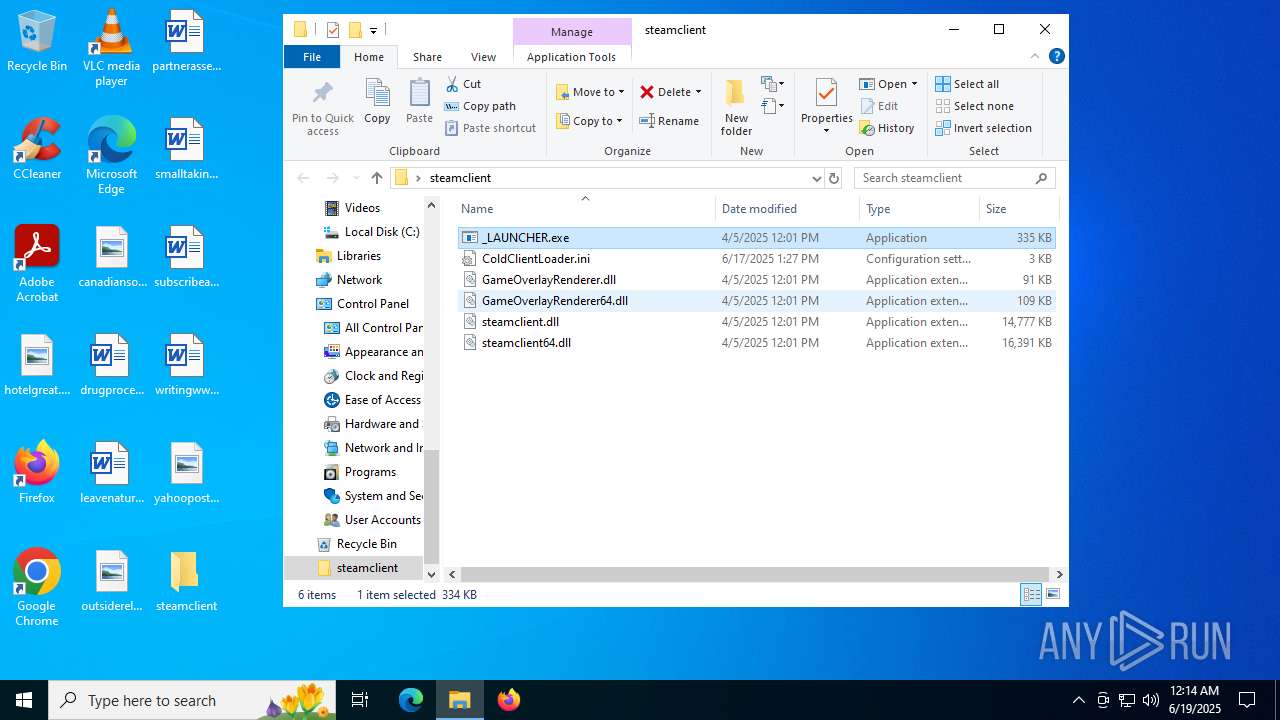
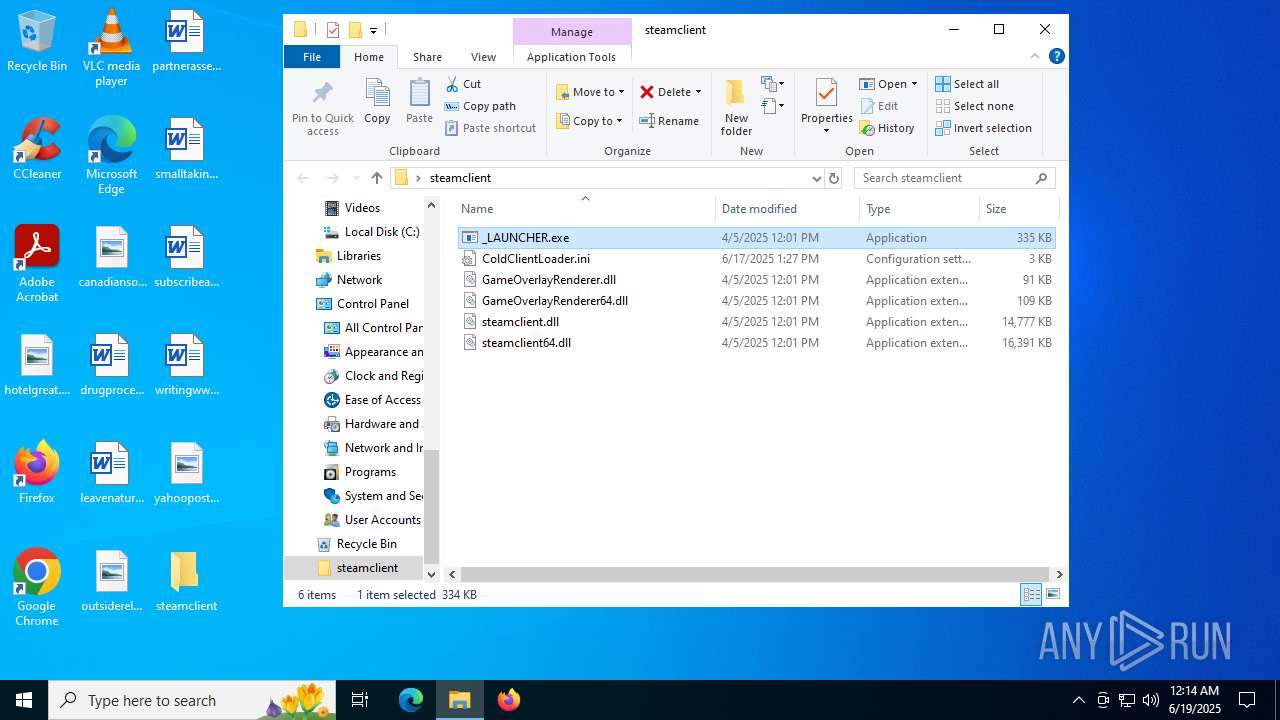
Executable files
5
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6684 | WinRAR.exe | C:\Users\admin\Desktop\steamclient\_LAUNCHER.exe | executable | |
MD5:F94BD57B1DD83B0072550DC06D162FD9 | SHA256:C5764BAD9D5E65A079BC3613BB8497A95ECEC355DFCAE1336D45C2D0F4D0F319 | |||
| 6684 | WinRAR.exe | C:\Users\admin\Desktop\steamclient\steamclient.dll | executable | |
MD5:685C001046FB80F8D2A8699F471F5235 | SHA256:B5B39E755A889E2BC874EDCB81D4363CF12EB54C129FF6E6A00FD832B0D44576 | |||
| 6684 | WinRAR.exe | C:\Users\admin\Desktop\steamclient\GameOverlayRenderer.dll | executable | |
MD5:8E47BD5744BD51AD6C95456B1483BEDF | SHA256:79D9522667F86B770BFA79599426F131E94C0C0F4DCFB6B1DA70C0530B3F9FF8 | |||
| 6684 | WinRAR.exe | C:\Users\admin\Desktop\steamclient\ColdClientLoader.ini | text | |
MD5:05C583F39C9CAE724282BA08F50CCFA7 | SHA256:D71214F9F7E348C6FEF3C94916465CD1DD45A88580A65C2A2FC841DDC8E20BEC | |||
| 6684 | WinRAR.exe | C:\Users\admin\Desktop\steamclient\GameOverlayRenderer64.dll | executable | |
MD5:ECE746C001DD4943C6D1F702D87D13C0 | SHA256:AED664C80B625BB6BDD492DAF86D060E54E43A694B04C7908790AA10D2FE01C6 | |||
| 6684 | WinRAR.exe | C:\Users\admin\Desktop\steamclient\steamclient64.dll | executable | |
MD5:9D596C6C1538D376D7224D1469E71C5E | SHA256:4A409226BA7700E347F97013BA2D26509760114290791B8EDE021FDB036B45A4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2524 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1036 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1036 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1644 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2524 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2524 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |