| File name: | setup (3).exe |
| Full analysis: | https://app.any.run/tasks/285bc2b8-a53b-48f7-b57b-14df87158f61 |
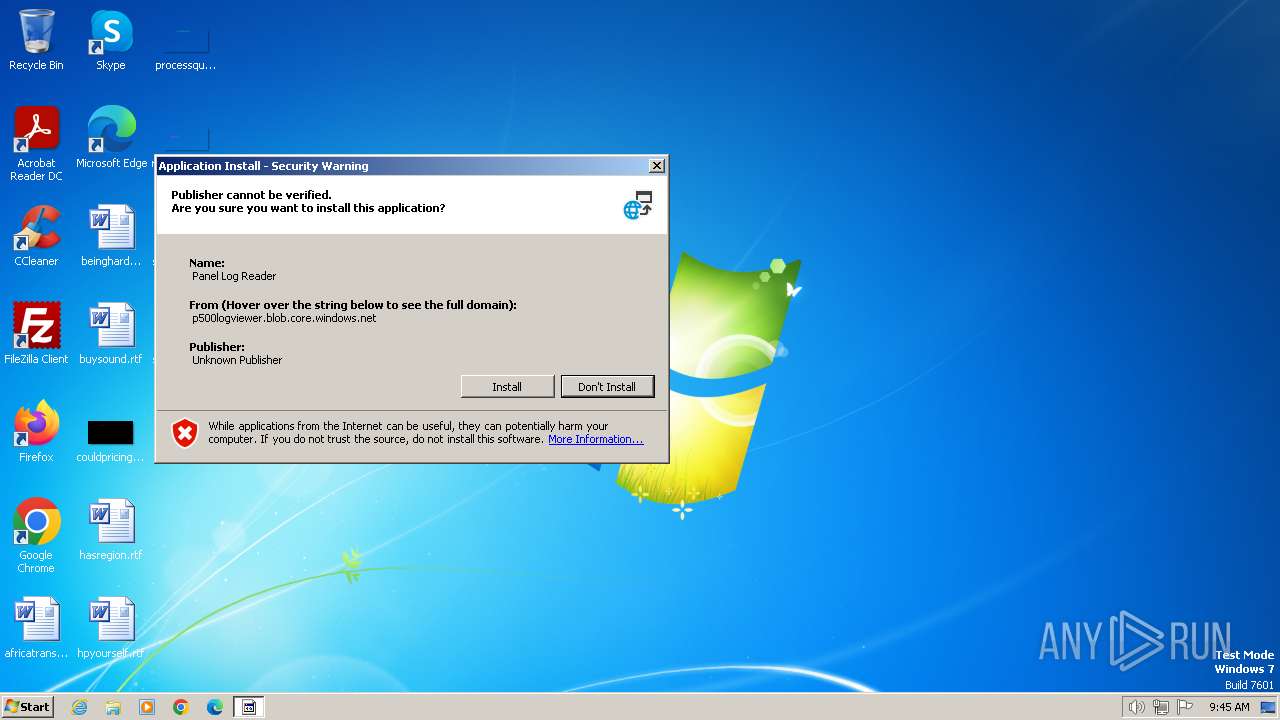
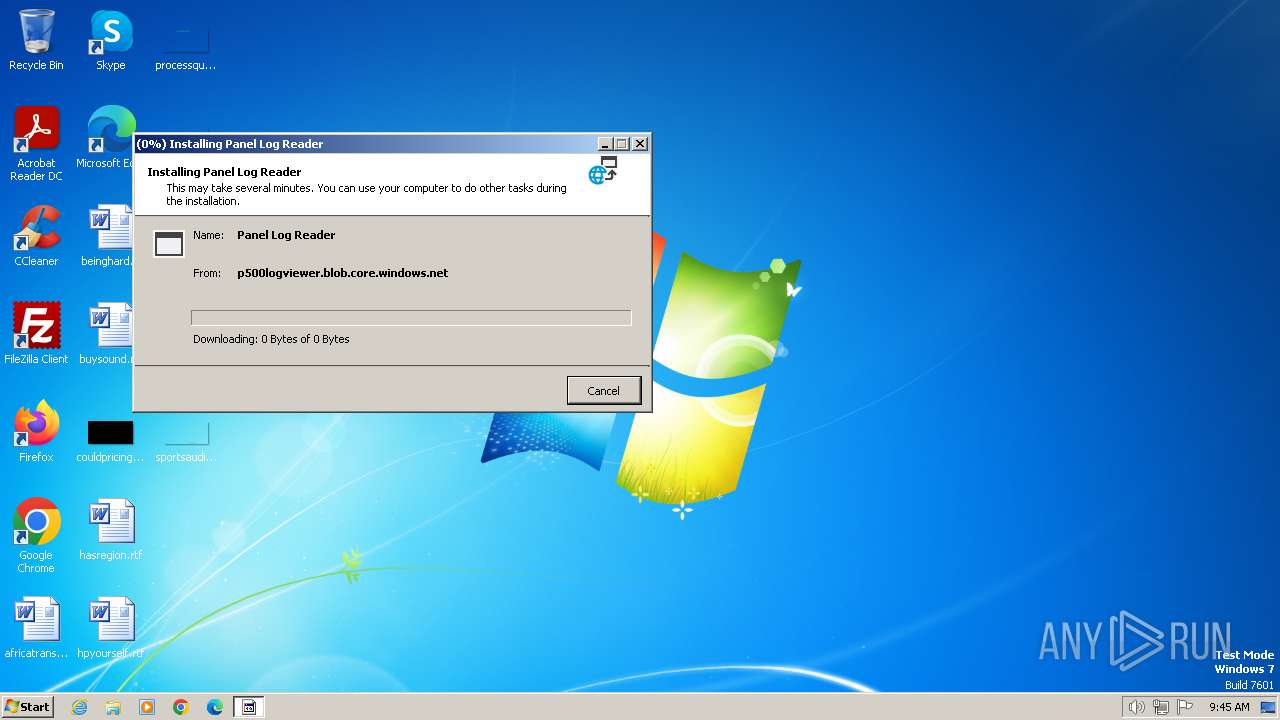
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2024, 08:44:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 250E23CEFD408C528FB34A0CE6FA2280 |
| SHA1: | 00634FCF1B0958FF15CB67013120CBB3C2DA26BE |
| SHA256: | 0A98569B57243069F9B5A4B5BC58B34AB21D0A7FCA75777C27117DB6ED0CA333 |
| SSDEEP: | 12288:H+bT9MaRjVdVbk8KHT7lcocklrtqZZrAttJVVVVVVVVVVVVVVVVVVVOVVVVVVVVp:H+VMaRjEz7Bnbf |
MALICIOUS
Drops the executable file immediately after the start
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
SUSPICIOUS
Reads the Internet Settings
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Reads security settings of Internet Explorer
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Checks Windows Trust Settings
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Reads settings of System Certificates
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Reads Internet Explorer settings
- dfsvc.exe (PID: 2896)
INFO
Checks supported languages
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Reads the computer name
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Create files in a temporary directory
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Checks proxy server information
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Reads the machine GUID from the registry
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Reads the software policy settings
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Creates files or folders in the user directory
- setup (3).exe (PID: 2120)
- dfsvc.exe (PID: 2896)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 2896)
Reads Environment values
- dfsvc.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:04:06 18:30:14+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.34 |
| CodeSize: | 387072 |
| InitializedDataSize: | 145920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x38be3 |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 17.0.33606.225 |
| ProductVersionNumber: | 17.0.33606.225 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 17.0.33606.225 built by: D17.6 |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | setup.exe |
| ProductName: | - |
| ProductVersion: | 17.0.33606.225 |
Total processes
38
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Users\admin\AppData\Local\Temp\setup (3).exe" | C:\Users\admin\AppData\Local\Temp\setup (3).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 17.0.33606.225 built by: D17.6 Modules
| |||||||||||||||
| 2896 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe | setup (3).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
10 199
Read events
10 082
Write events
101
Delete events
16
Modification events
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (2120) setup (3).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
4
Text files
5
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | setup (3).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2120 | setup (3).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2120 | setup (3).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2120 | setup (3).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\Panel_Log_Reader[1].application | xml | |
MD5:— | SHA256:— | |||
| 2120 | setup (3).exe | C:\Users\admin\AppData\Local\Temp\VSD2575.tmp\install.log | binary | |
MD5:— | SHA256:— | |||
| 2896 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\TEE4MDEG.M5N\OTWP63YO.Y9G.application | xml | |
MD5:— | SHA256:— | |||
| 2896 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\C575B66H.3KM\HA234MPD.4CD\Panel_Log_Reader.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 2896 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2896 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2896 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Cab2F77.tmp | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | setup (3).exe | GET | 304 | 173.222.108.226:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?54637f8936655088 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 304 | 2.22.242.105:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e90c163b6659448e | unknown | — | — | unknown |
2896 | dfsvc.exe | GET | 200 | 173.222.108.226:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?86d6139f3b7ef26c | unknown | — | — | unknown |
2120 | setup (3).exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | setup (3).exe | 52.239.170.68:443 | p500logviewer.blob.core.windows.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2120 | setup (3).exe | 173.222.108.226:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2120 | setup (3).exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2896 | dfsvc.exe | 52.239.170.68:443 | p500logviewer.blob.core.windows.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2896 | dfsvc.exe | 173.222.108.226:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
1080 | svchost.exe | 2.22.242.105:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
p500logviewer.blob.core.windows.net |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
dfsvc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
dfsvc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
dfsvc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
dfsvc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
dfsvc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
dfsvc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
dfsvc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|