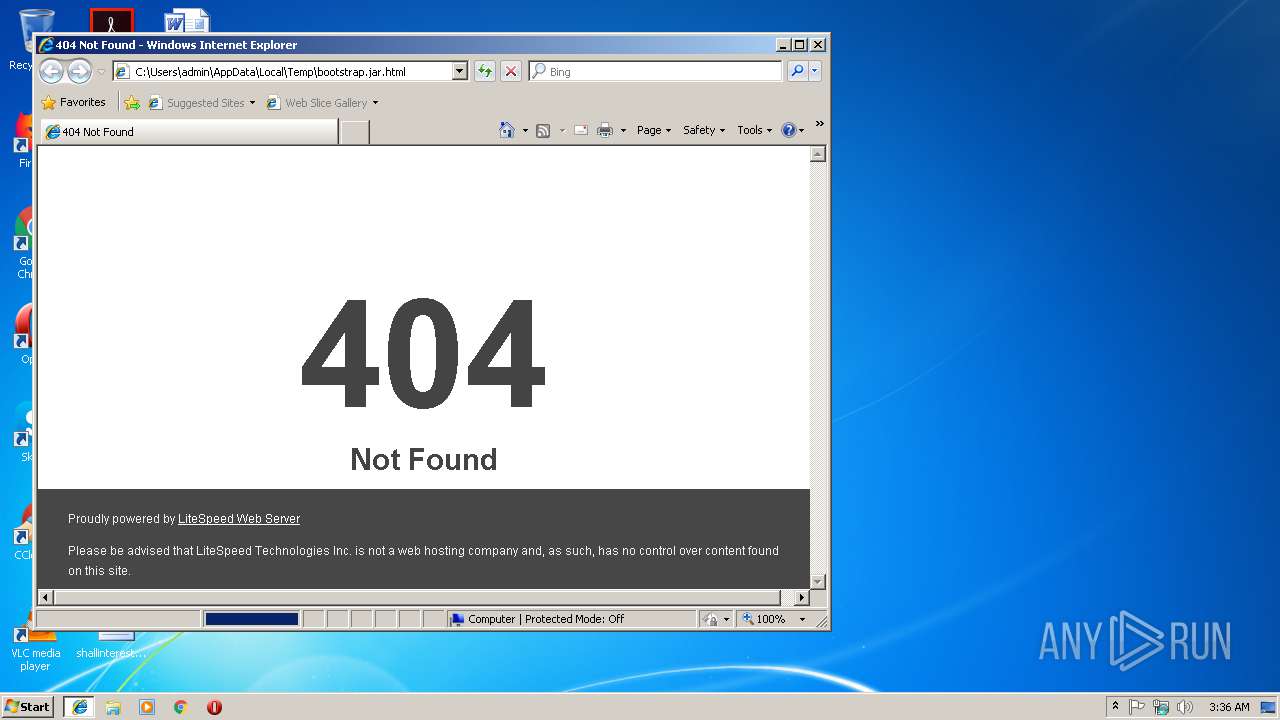
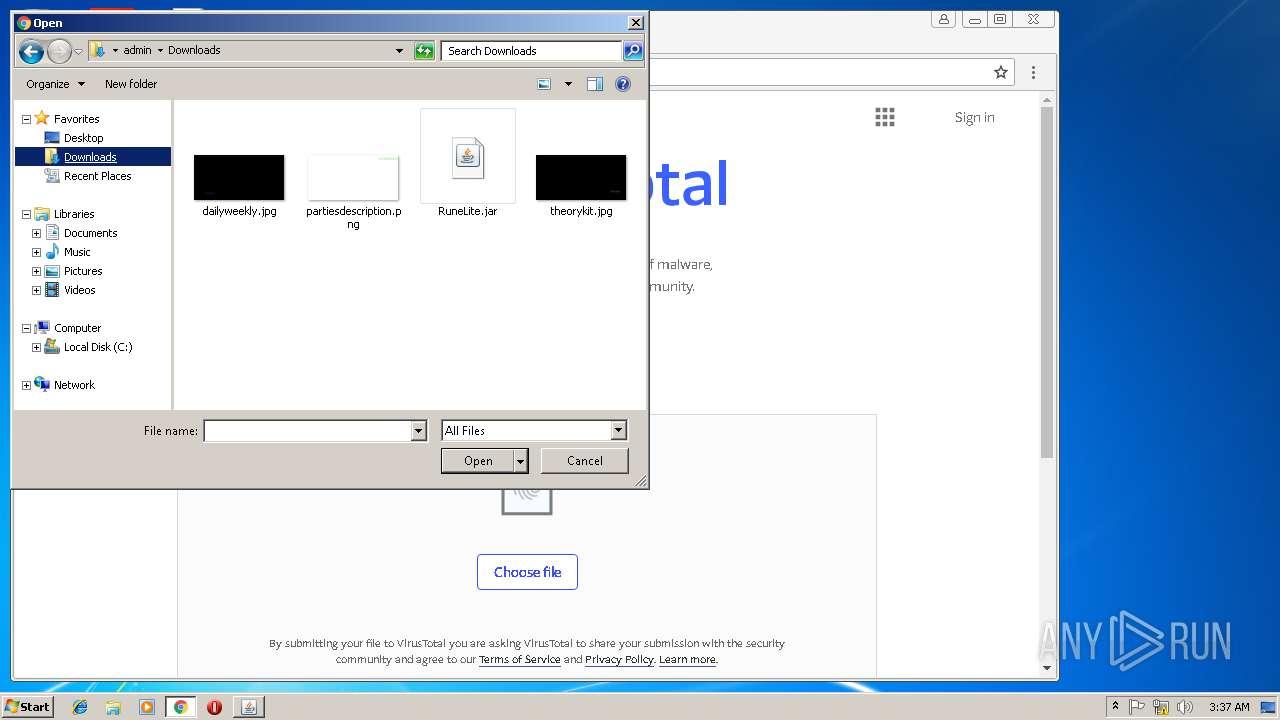
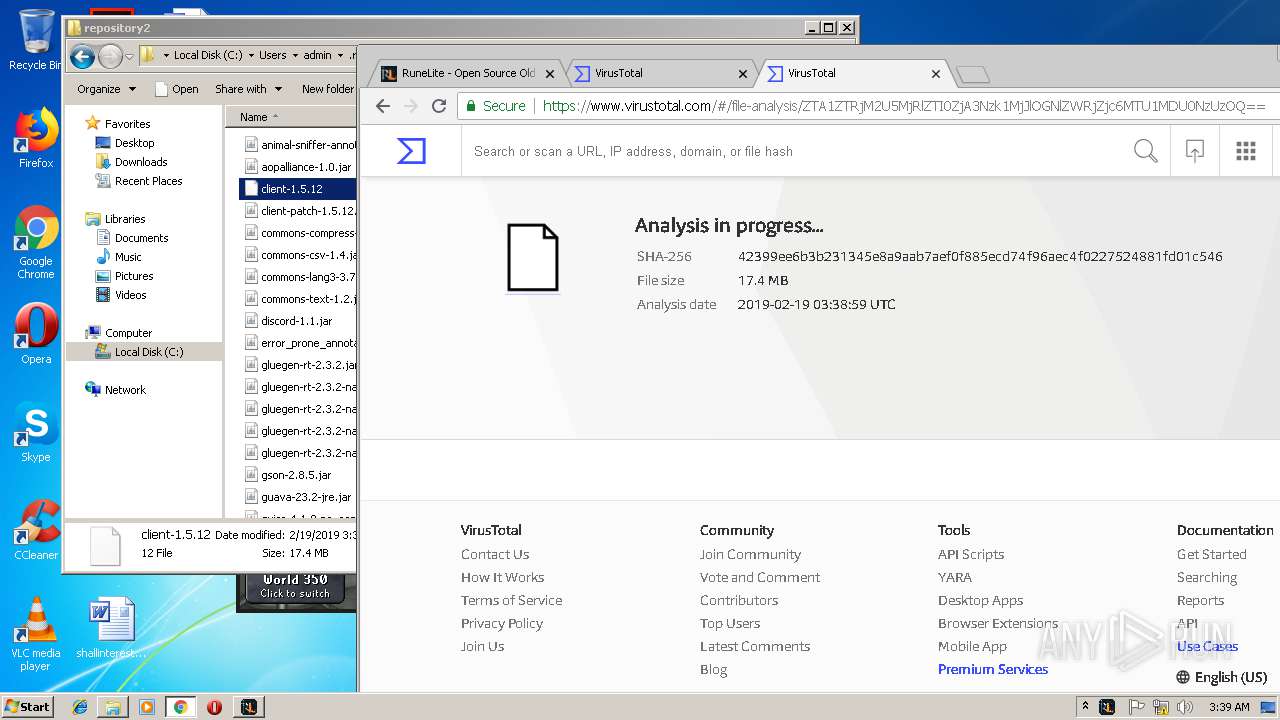
| download: | bootstrap.jar |
| Full analysis: | https://app.any.run/tasks/9354f90b-59c8-4ca3-a4ac-6d0c567bb322 |
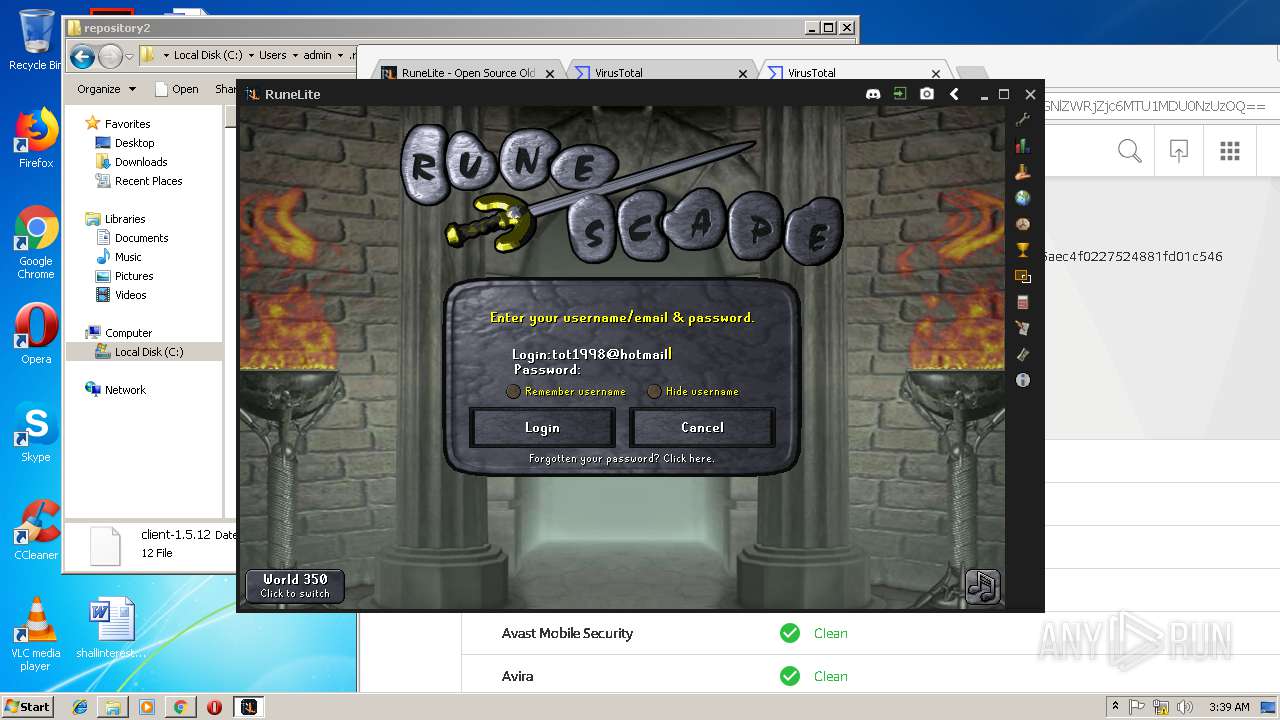
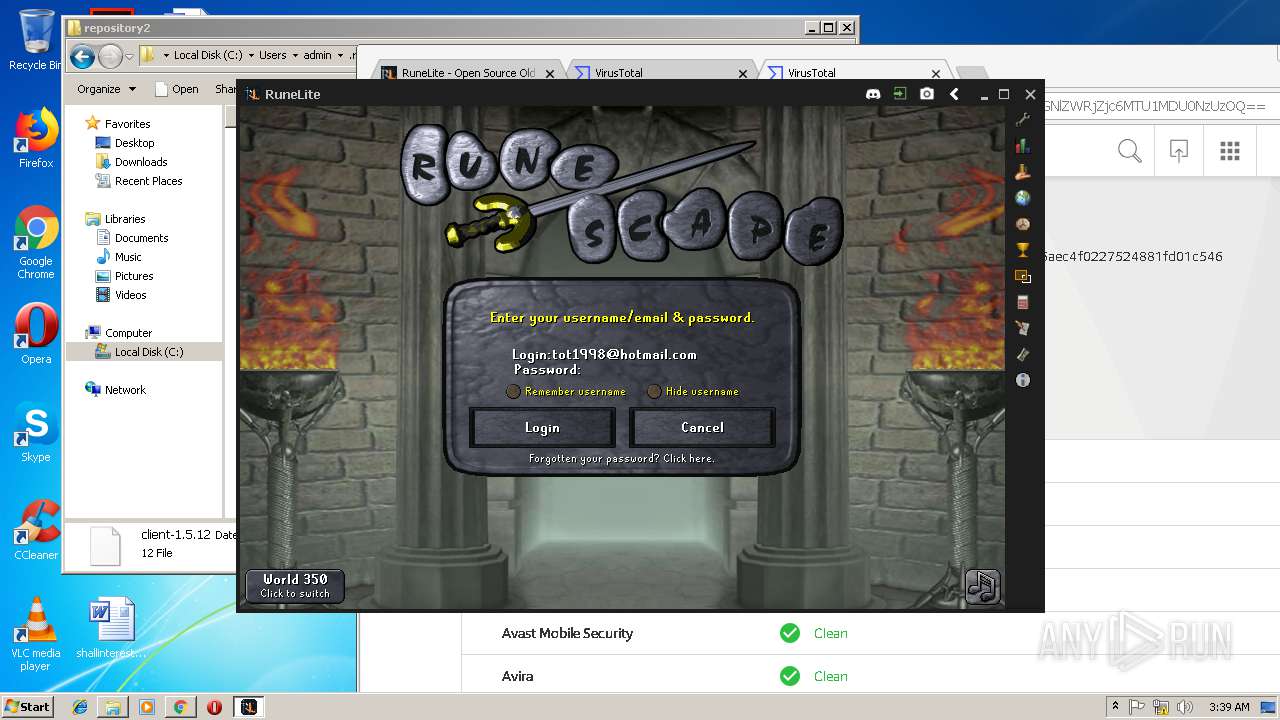
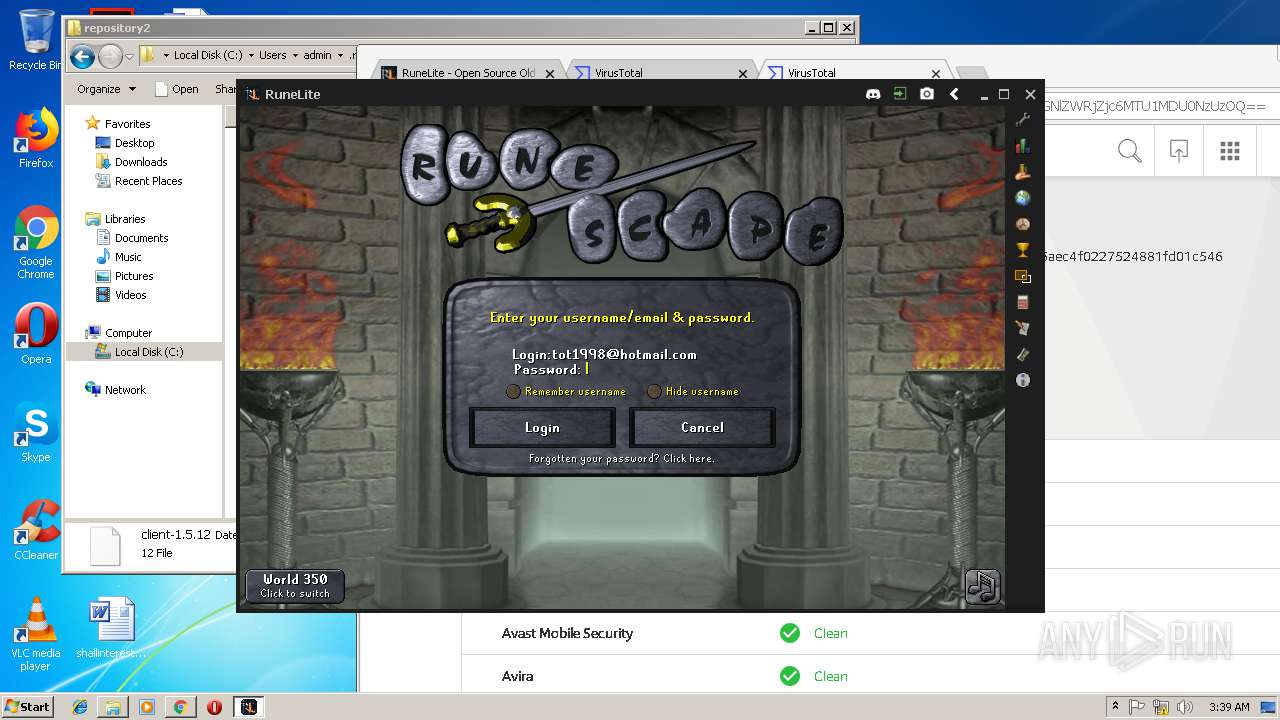
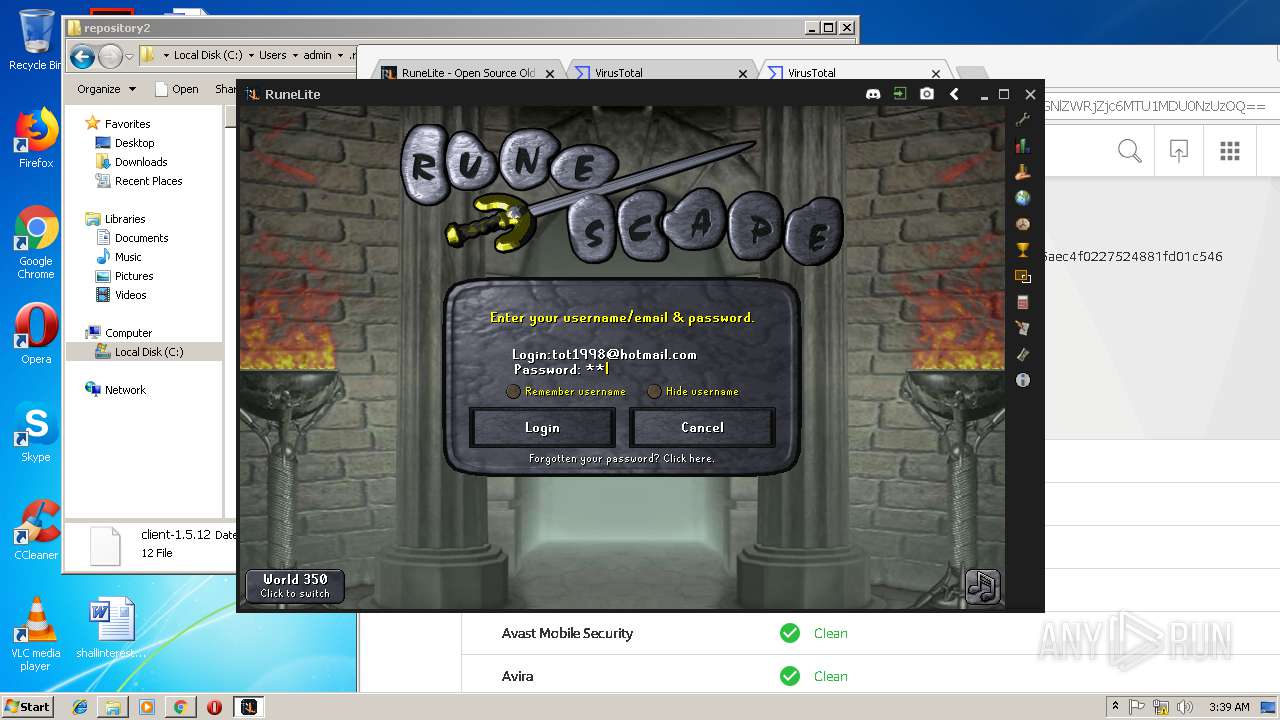
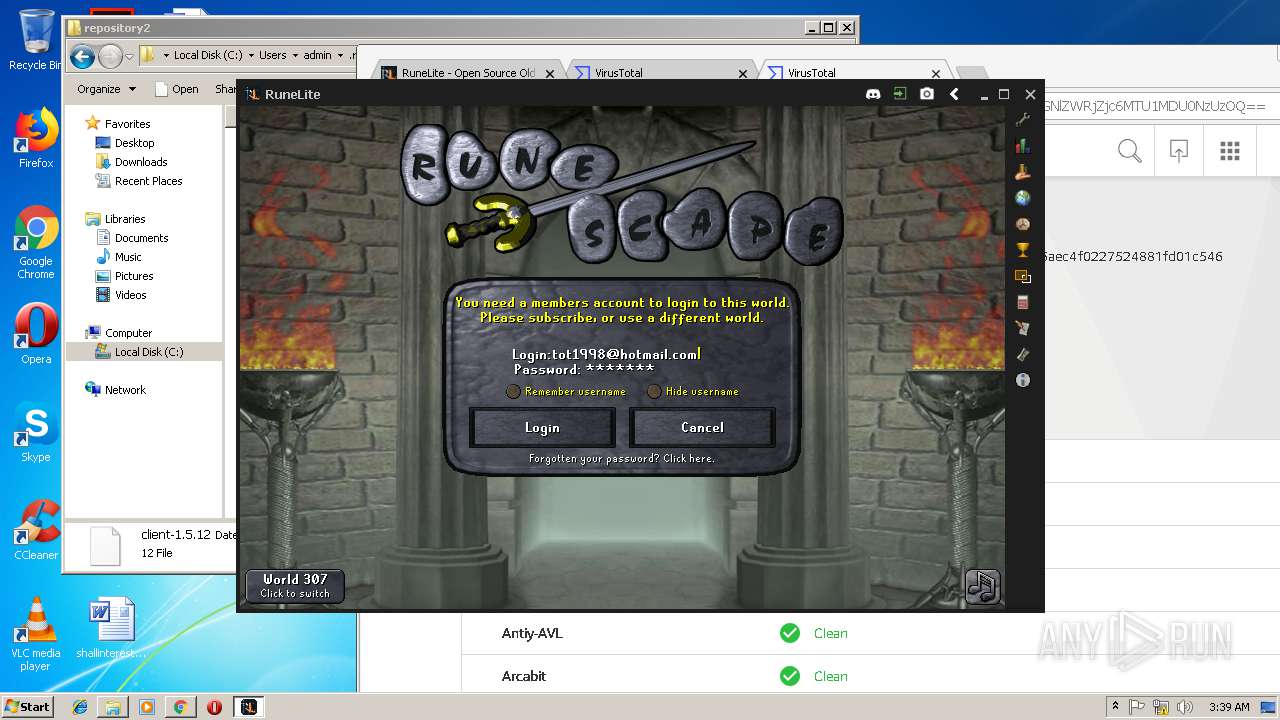
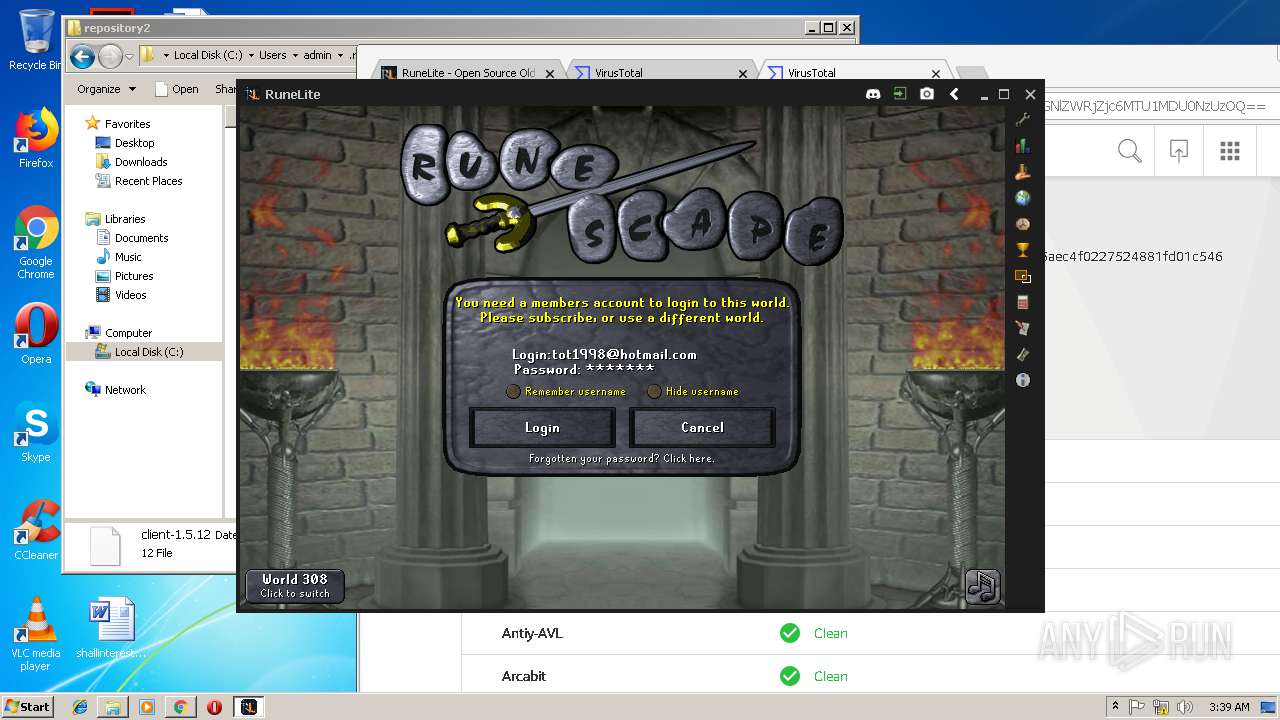
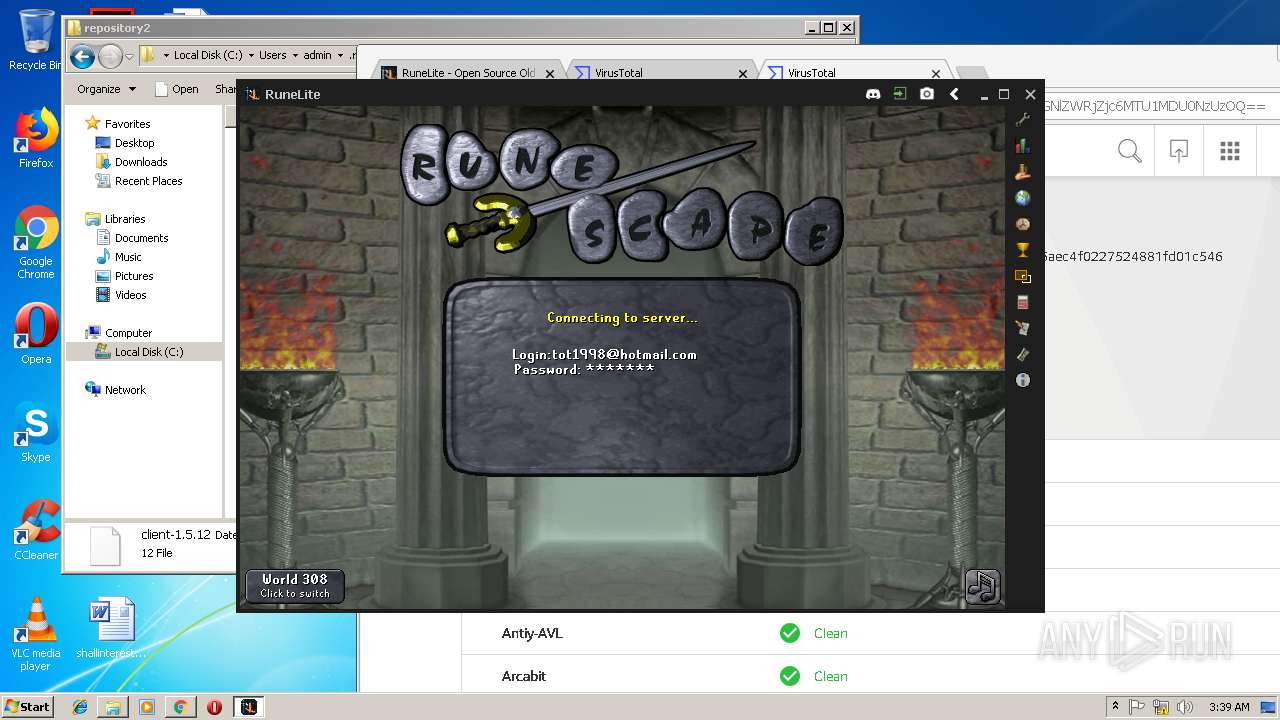
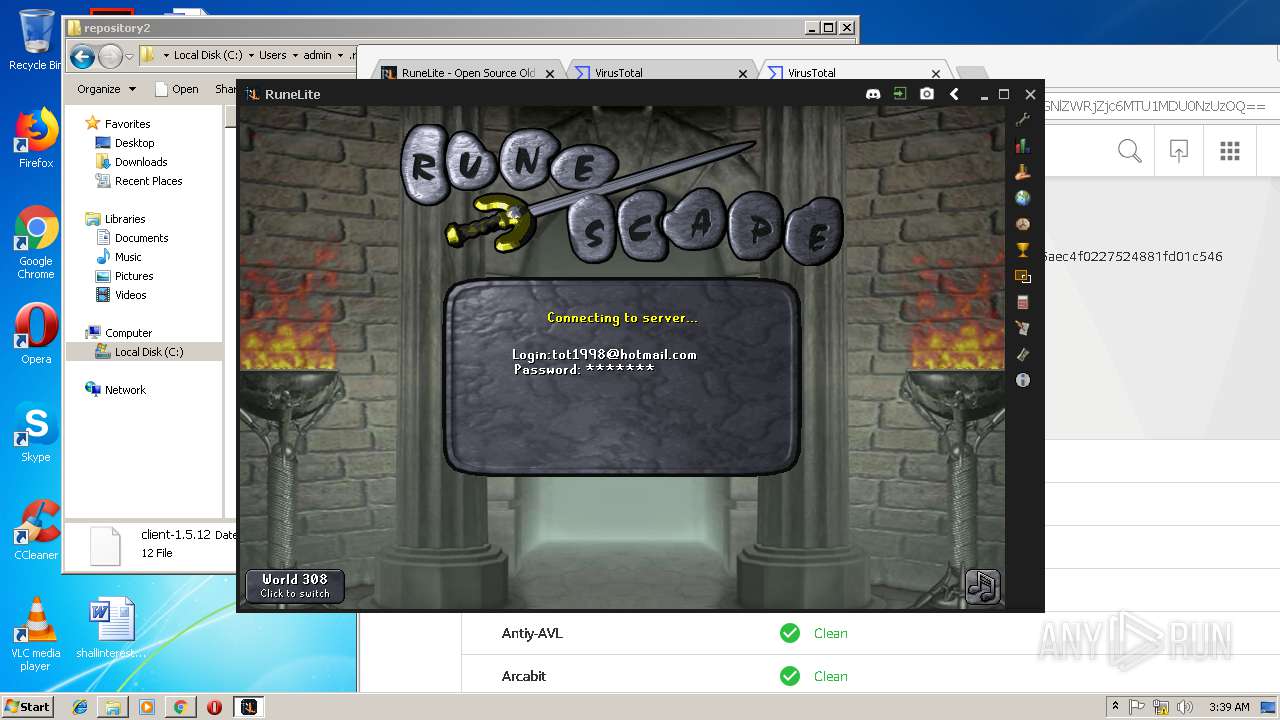
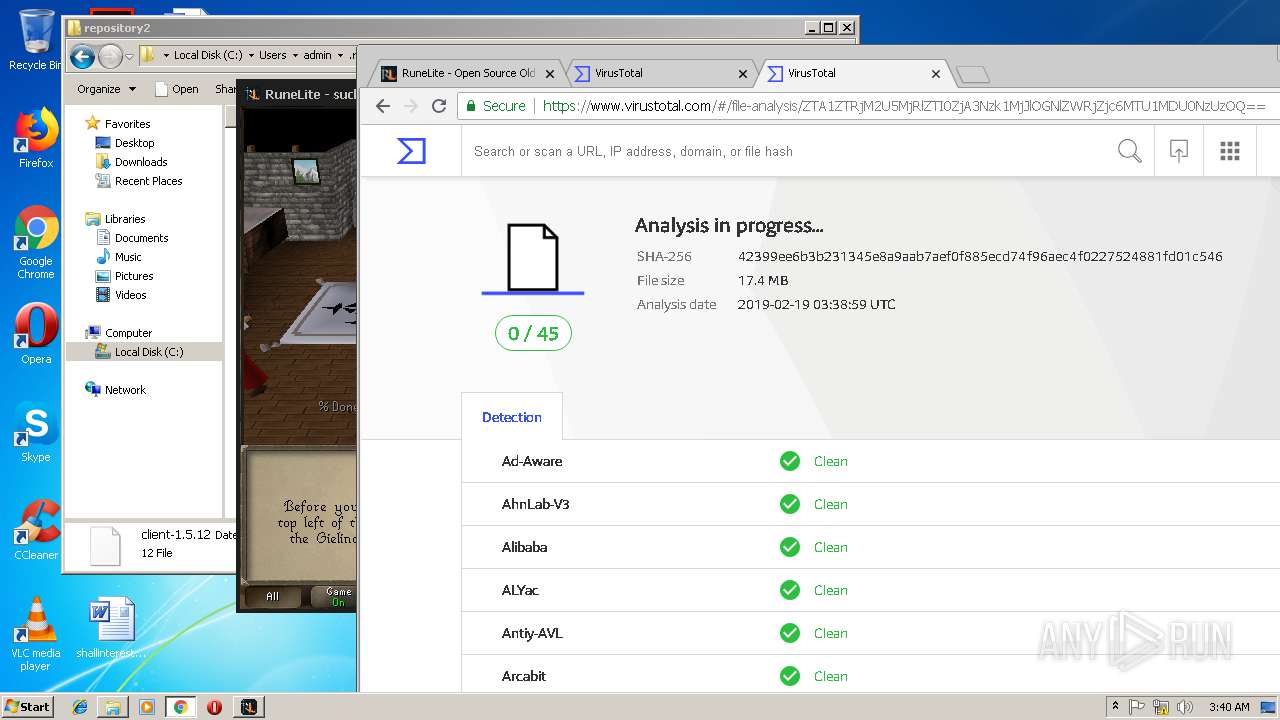
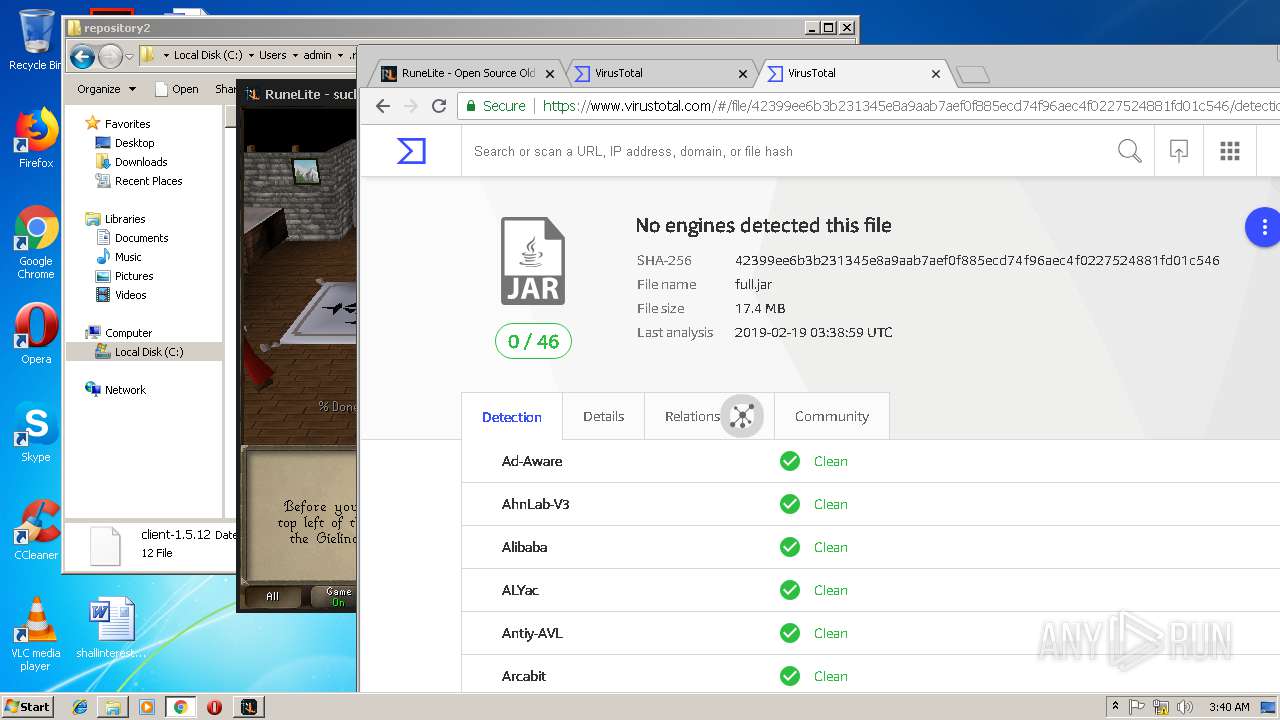
| Verdict: | Malicious activity |
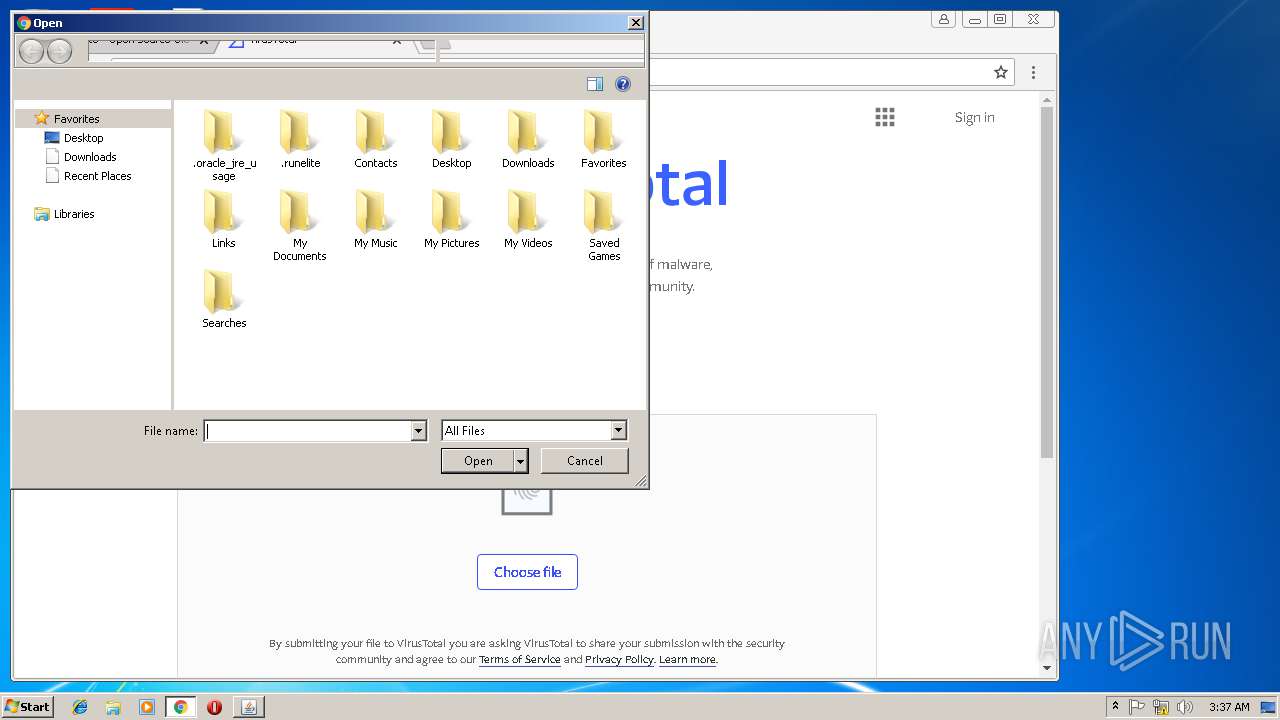
| Analysis date: | February 19, 2019, 03:36:11 |
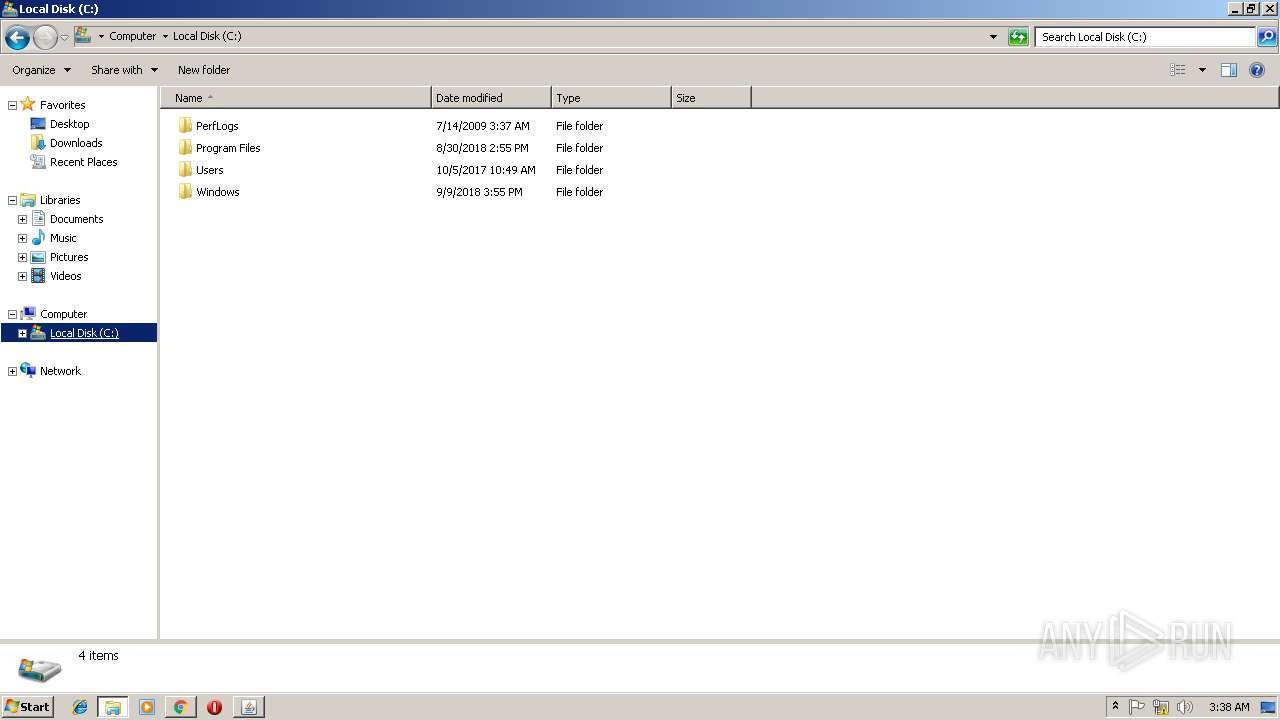
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
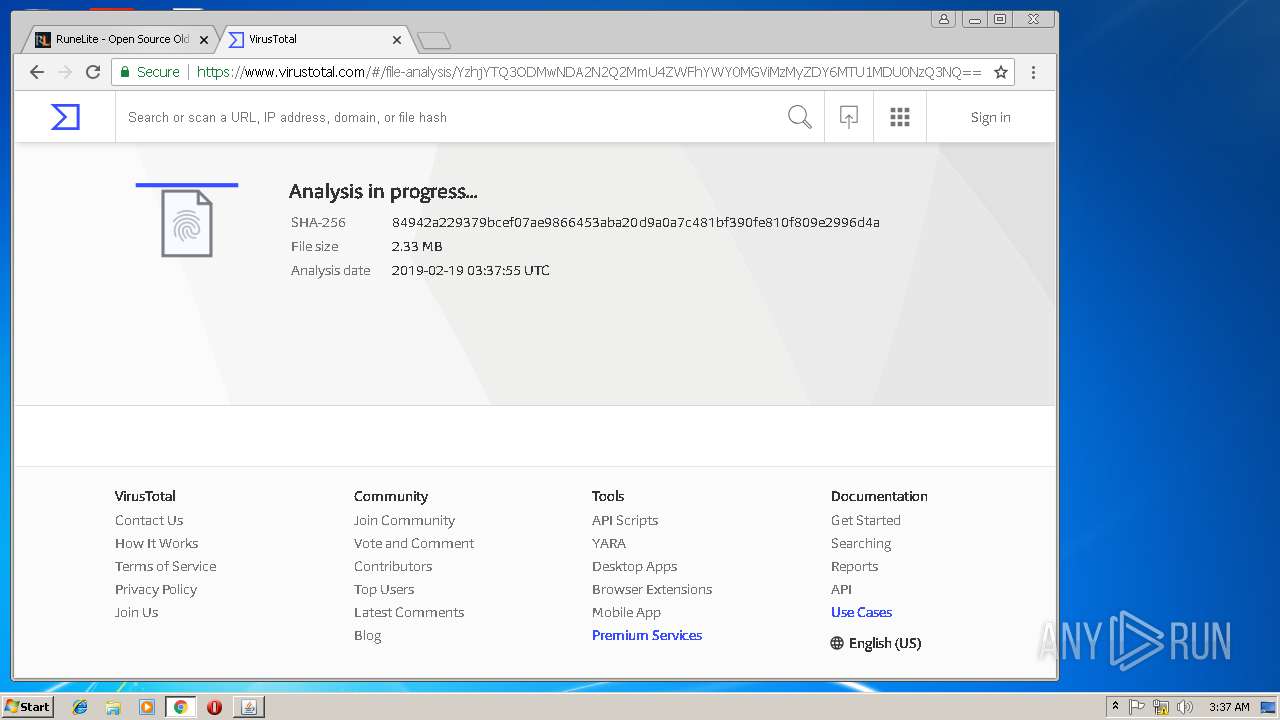
| MD5: | 92272AF0F8736D3B42A3804804AD987F |
| SHA1: | 4967947D5FFD87A1CE54C71BC4B739A15C06050A |
| SHA256: | 0A966DAC0108A3CB0B5A5A0019CF2BAD7BA82D3C81AEB758A4824EA915B560E0 |
| SSDEEP: | 24:hYYIN9ejNQCRtgoLY95Mu56+eMHLFCOXAkRcfRrzd0oj9O72rKQm:rK9ej2CZLY5Mc6NMLYzkYKoUOu |
MALICIOUS
Loads dropped or rewritten executable
- java.exe (PID: 2092)
SUSPICIOUS
Starts CMD.EXE for commands execution
- java.exe (PID: 2092)
Uses TASKLIST.EXE to query information about running processes
- java.exe (PID: 2092)
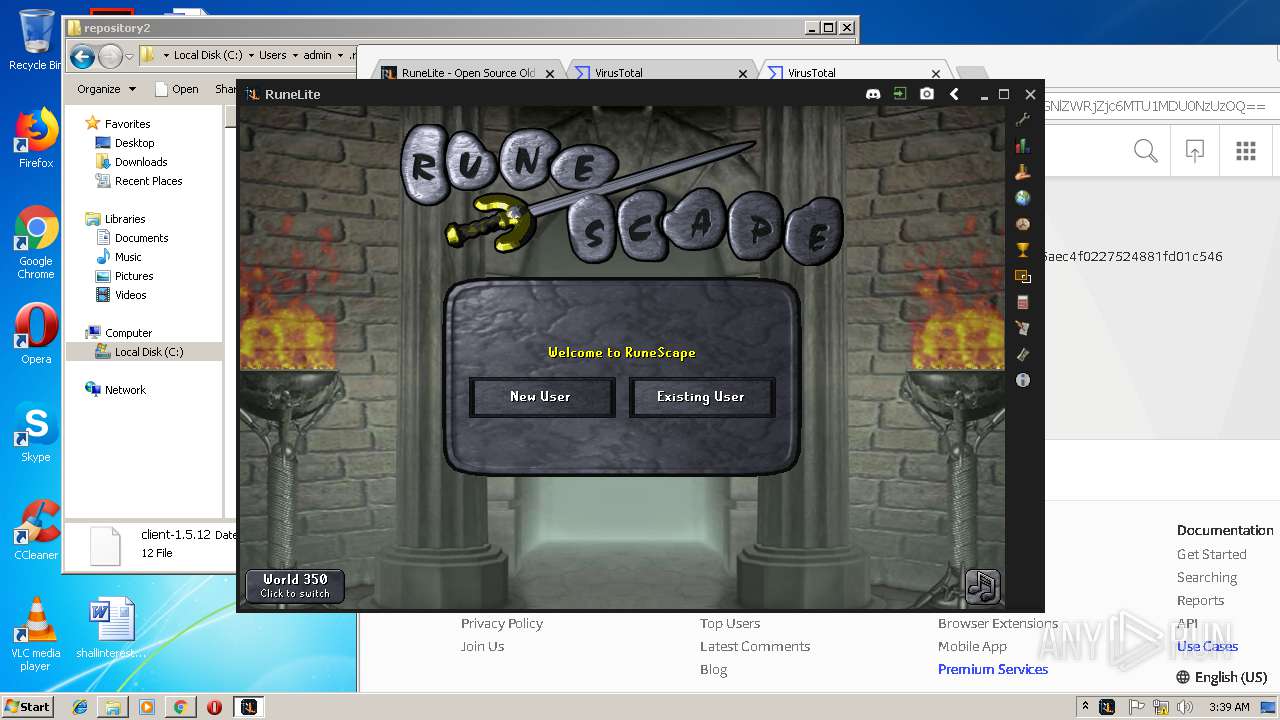
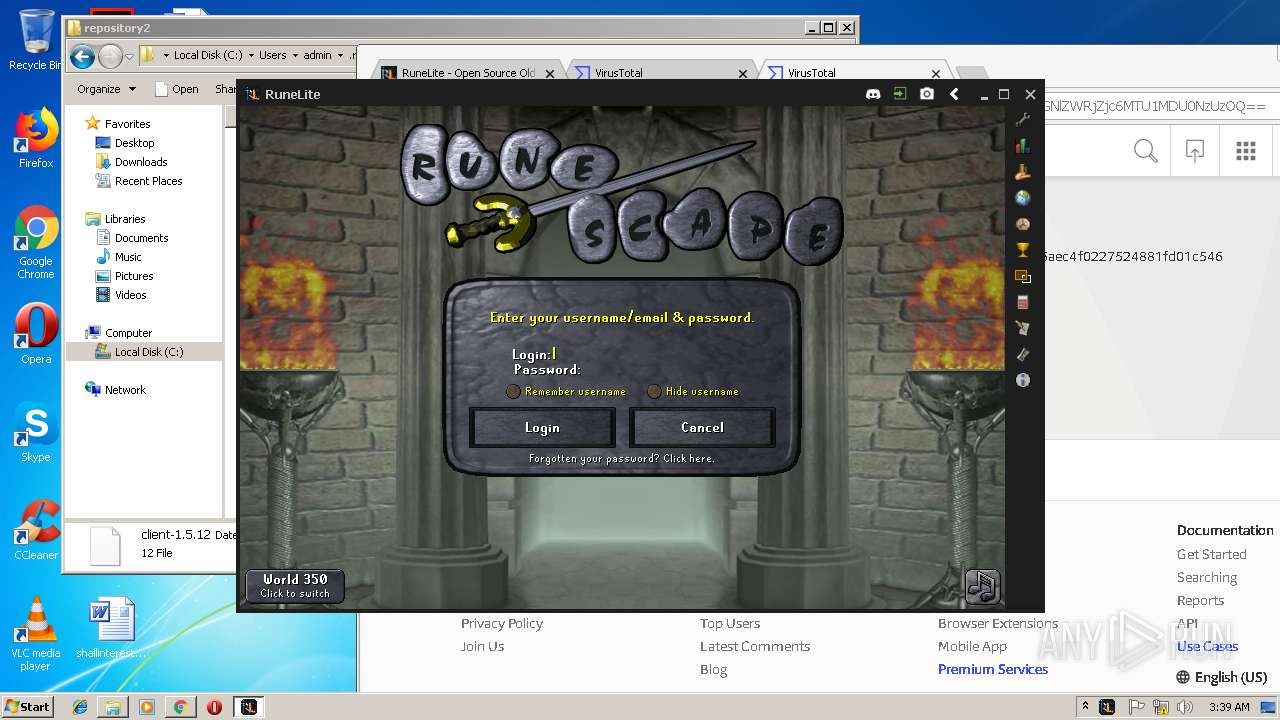
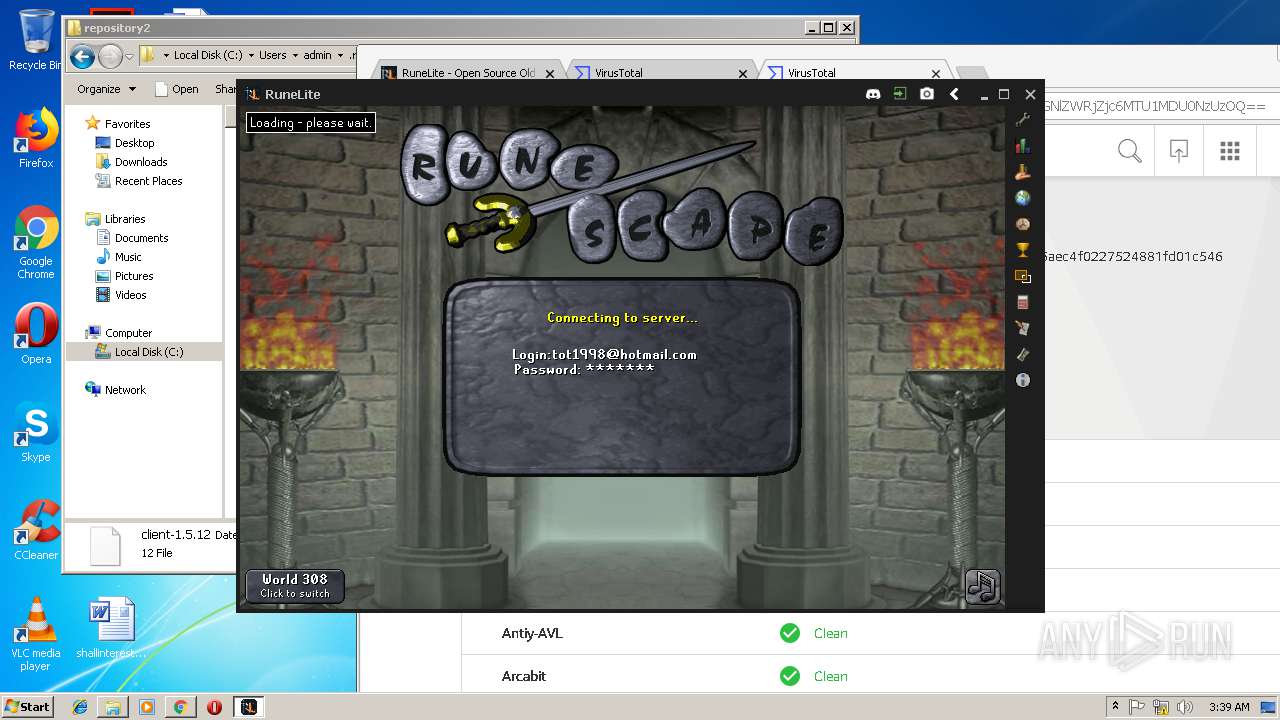
Executes JAVA applets
- javaw.exe (PID: 2596)
- chrome.exe (PID: 2312)
Modifies the open verb of a shell class
- java.exe (PID: 2092)
Connects to unusual port
- java.exe (PID: 2092)
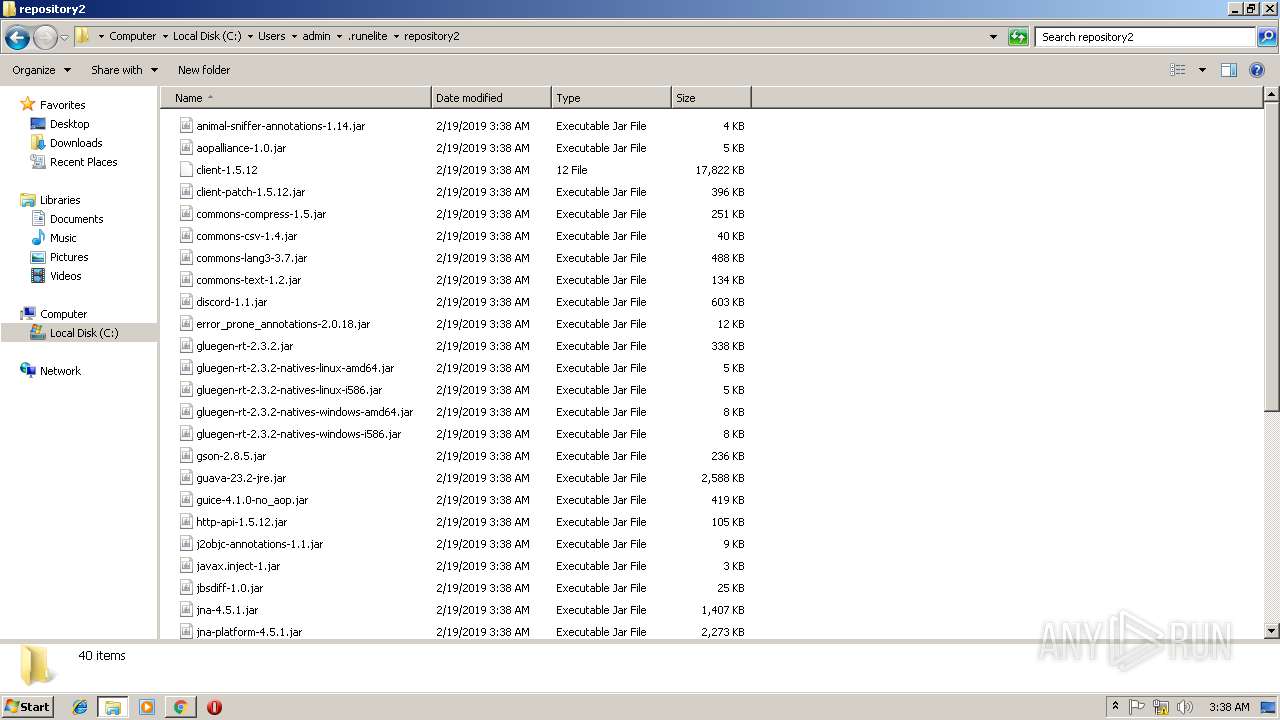
Executable content was dropped or overwritten
- java.exe (PID: 2092)
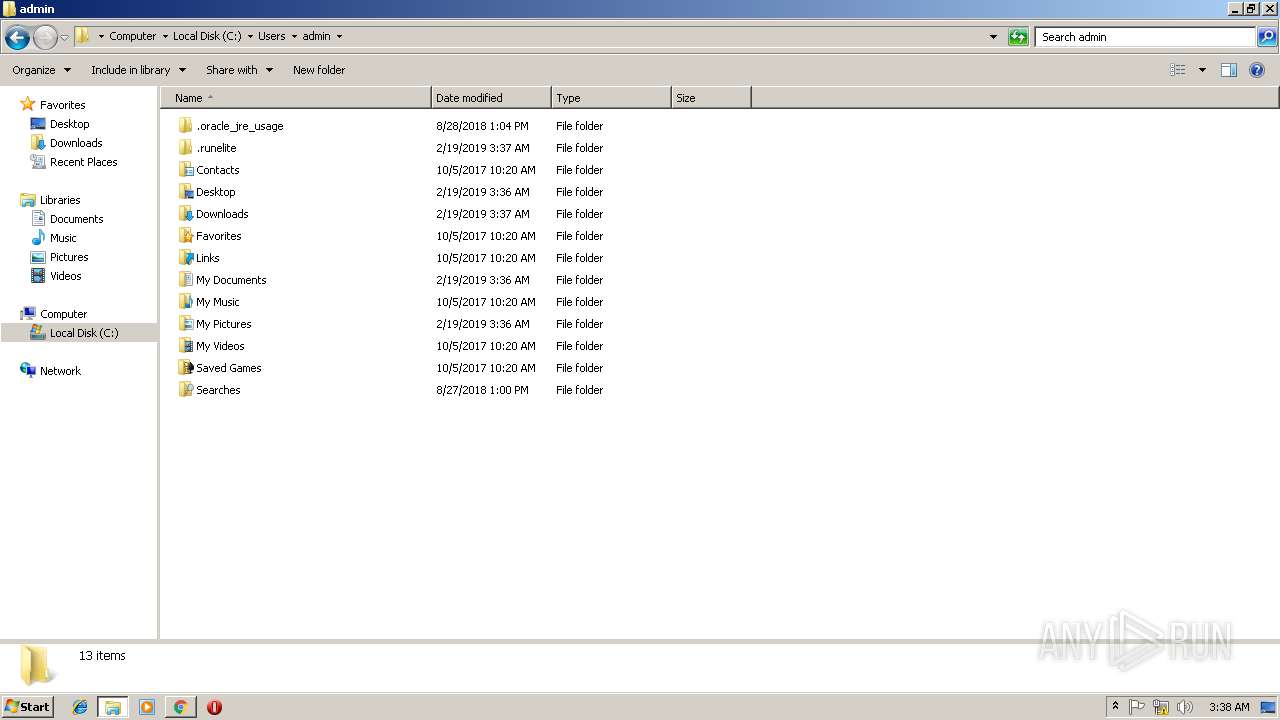
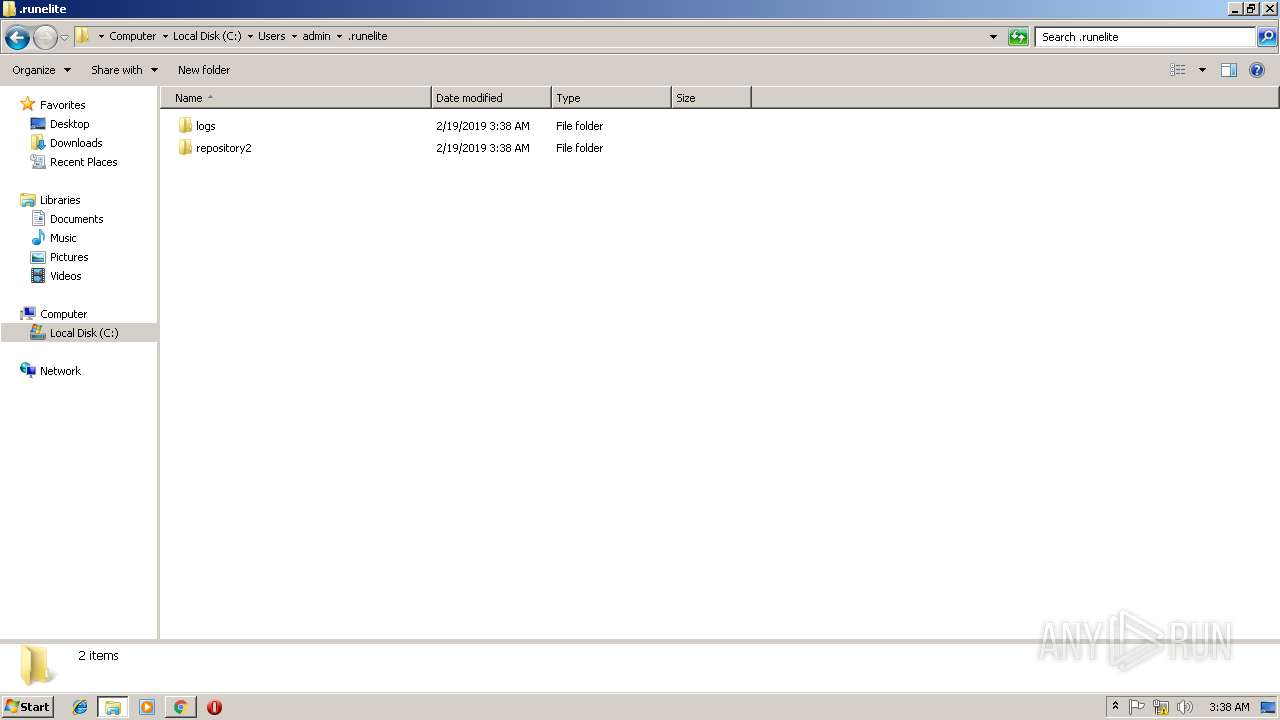
Creates files in the user directory
- java.exe (PID: 2092)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2960)
Application launched itself
- iexplore.exe (PID: 2960)
- chrome.exe (PID: 2312)
Reads internet explorer settings
- iexplore.exe (PID: 3244)
Reads settings of System Certificates
- chrome.exe (PID: 2312)
Creates files in the user directory
- chrome.exe (PID: 2312)
Reads Internet Cache Settings
- iexplore.exe (PID: 3244)
- iexplore.exe (PID: 2960)
- chrome.exe (PID: 2312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| Title: | 404 Not Found |
|---|
Total processes
71
Monitored processes
30
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | C:\Windows\system32\cmd.exe /c WMIC COMPUTERSYSTEM GET MODEL | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=868,16372513078222223386,8998679094437217574,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7FC879E4FBF7EC880AD702587F73C590 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7FC879E4FBF7EC880AD702587F73C590 --renderer-client-id=20 --mojo-platform-channel-handle=1692 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
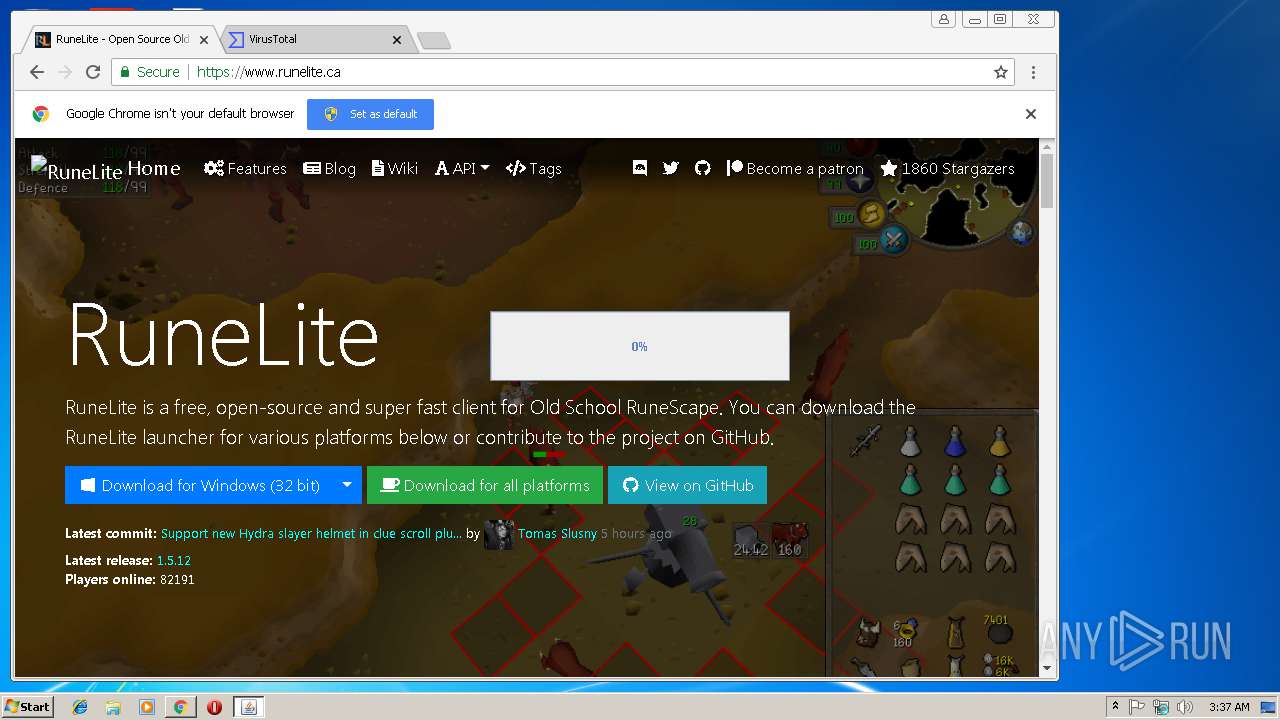
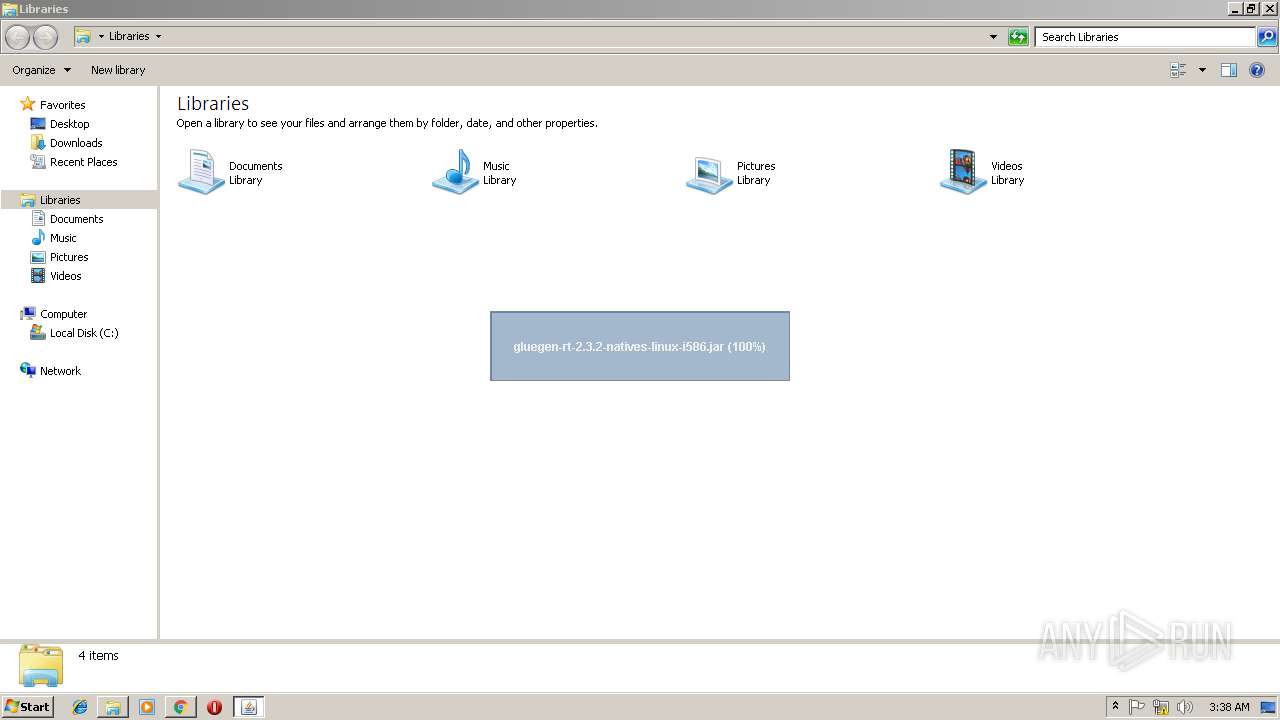
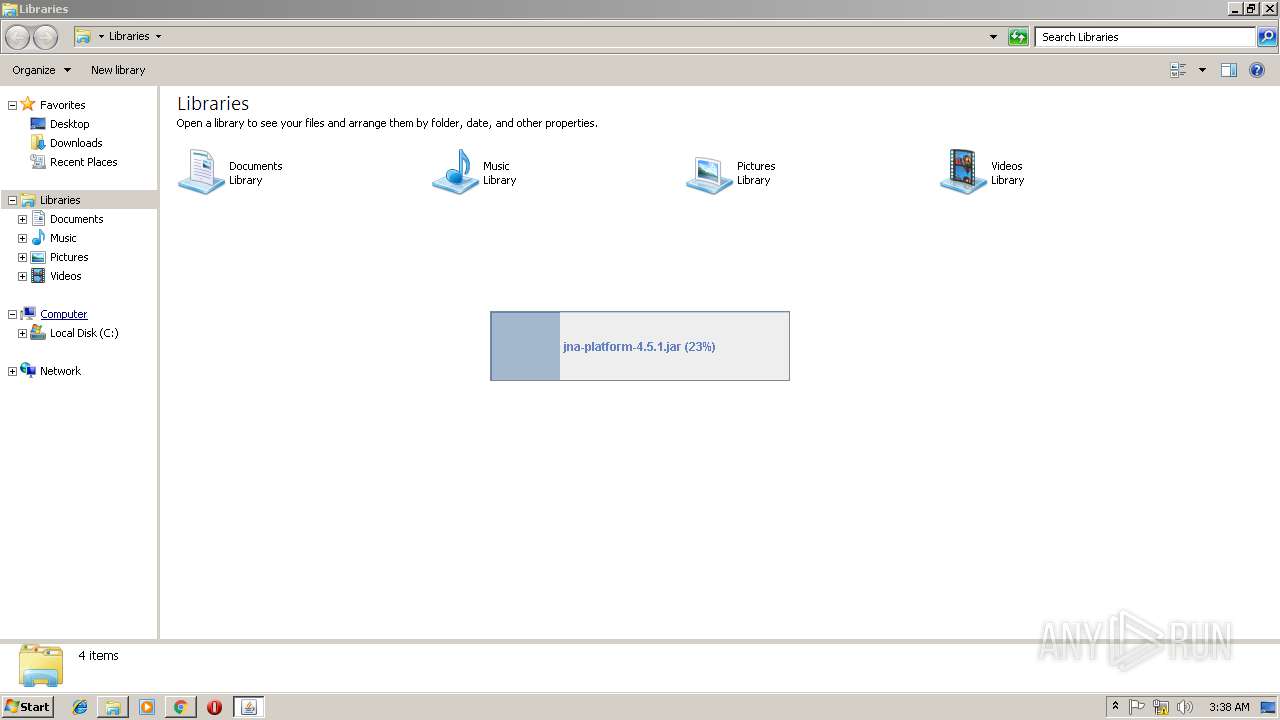
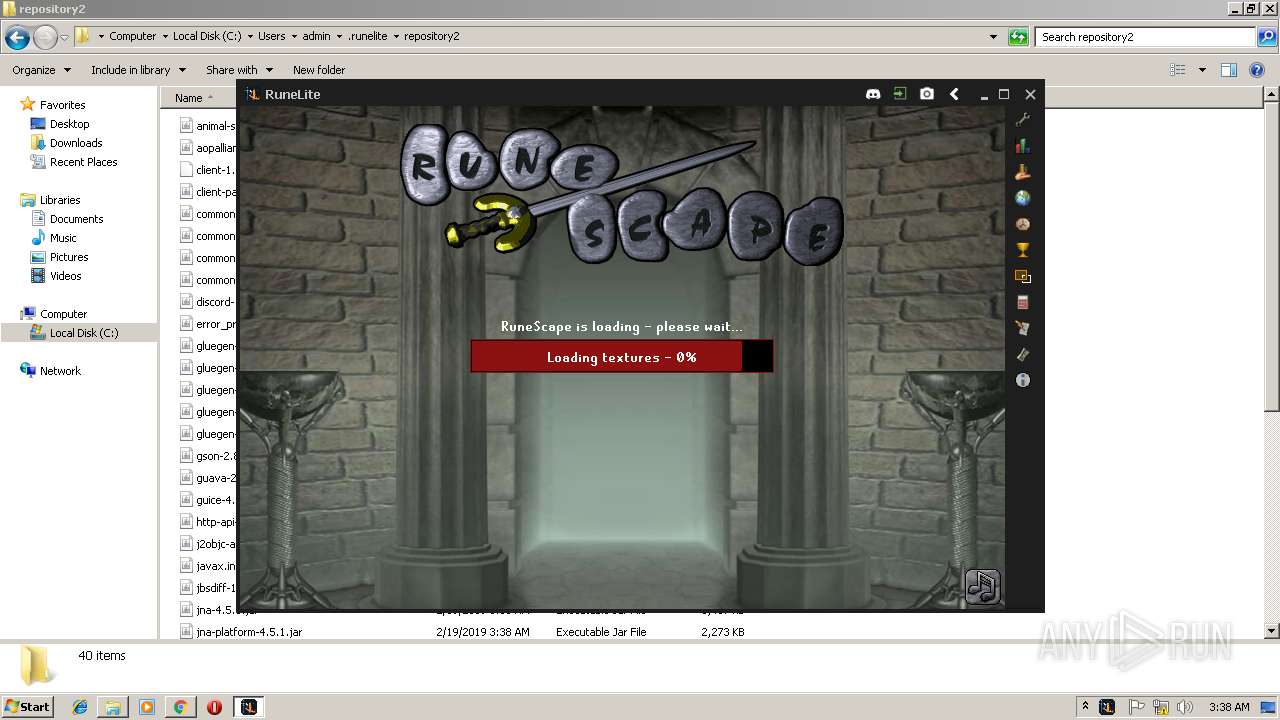
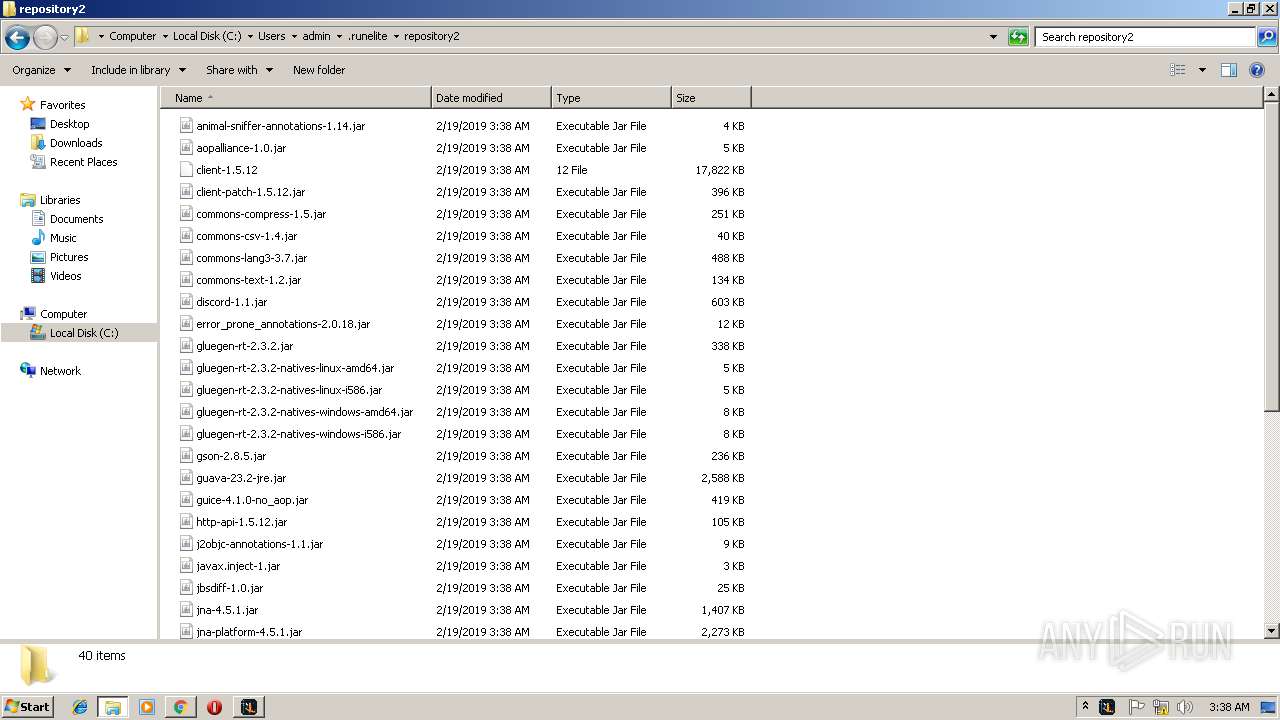
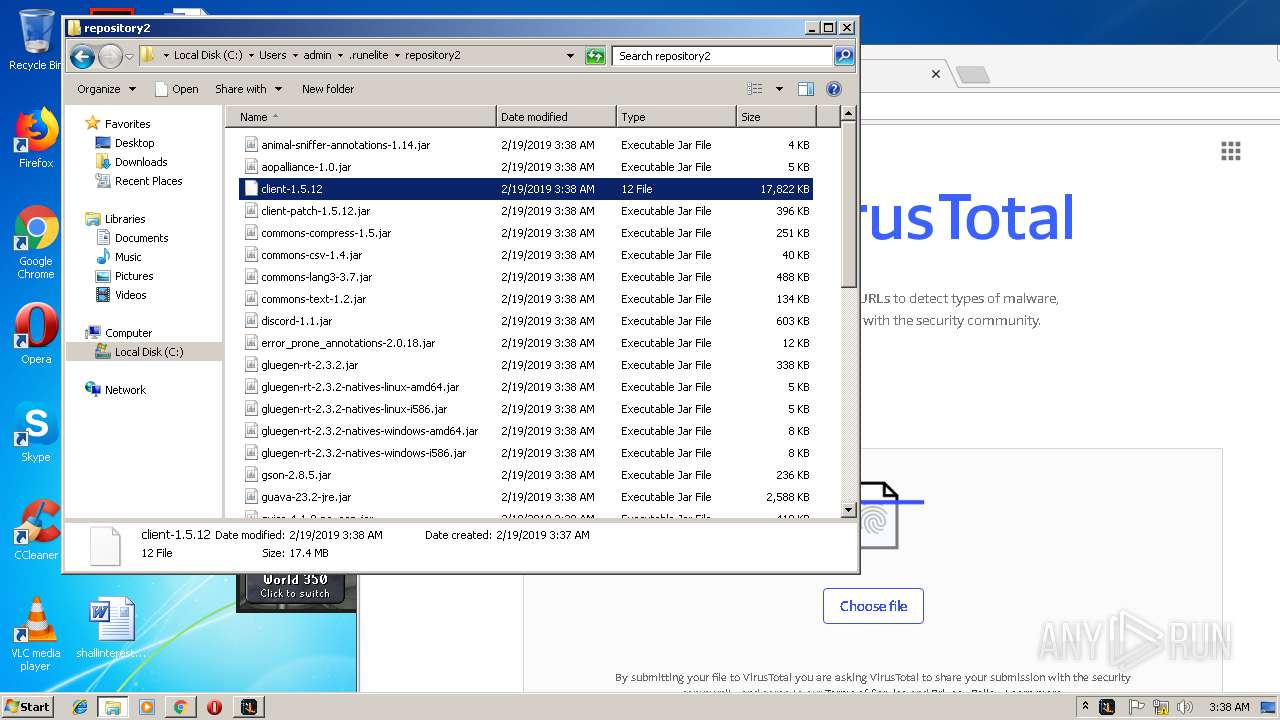
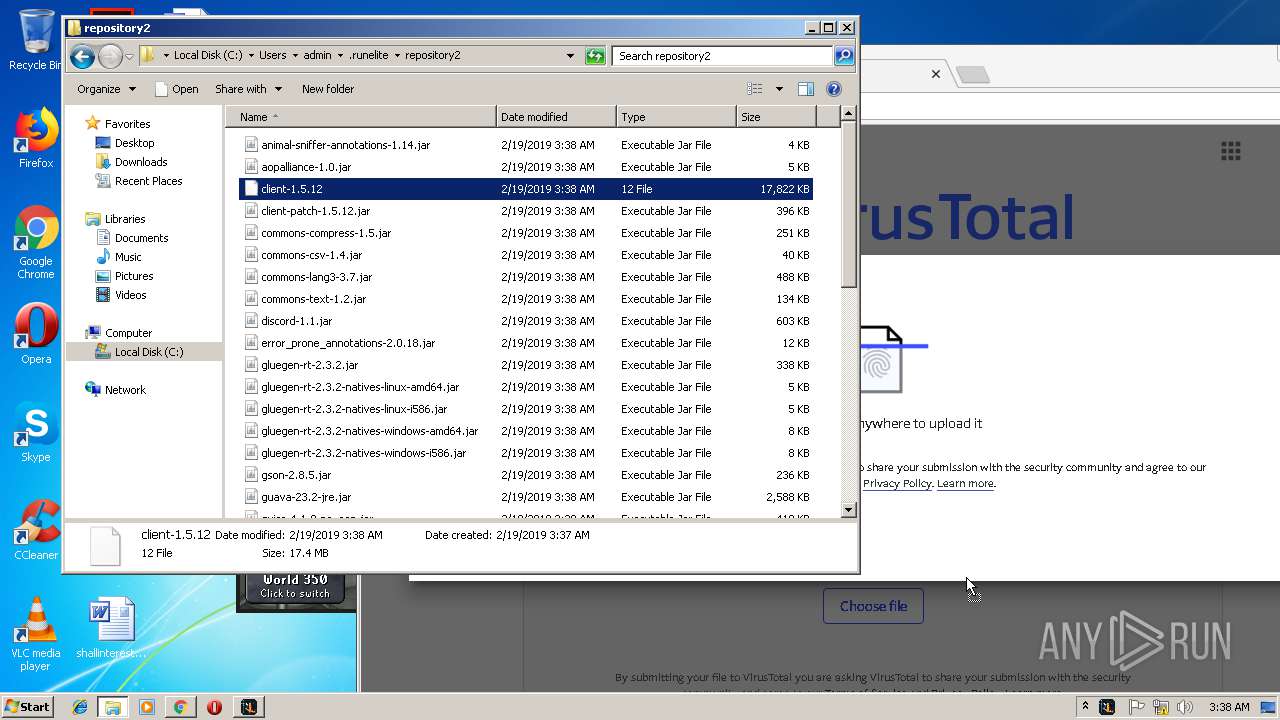
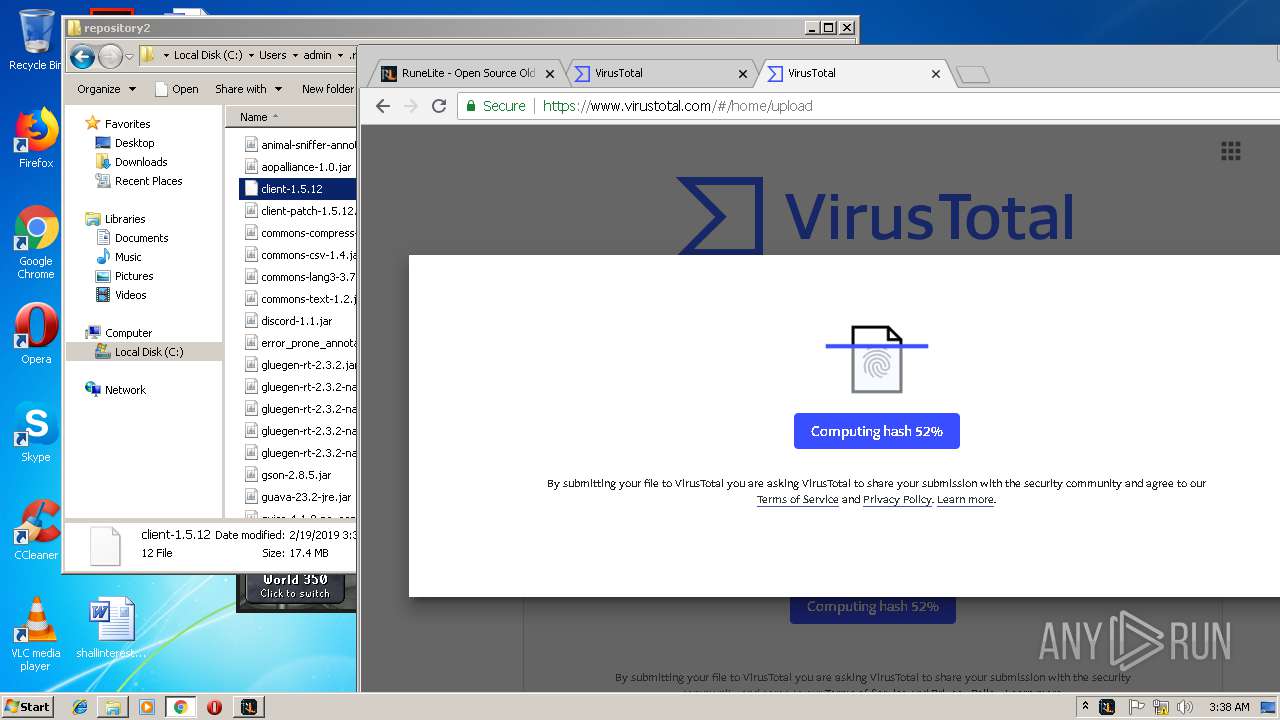
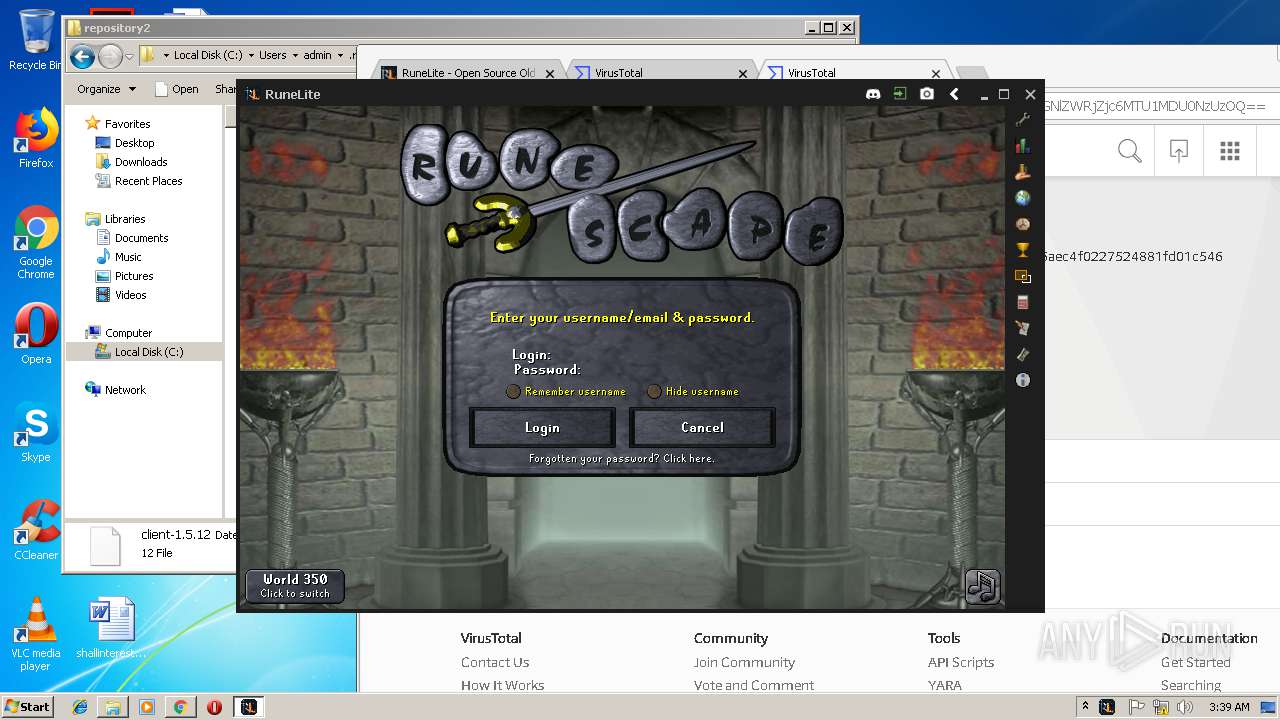
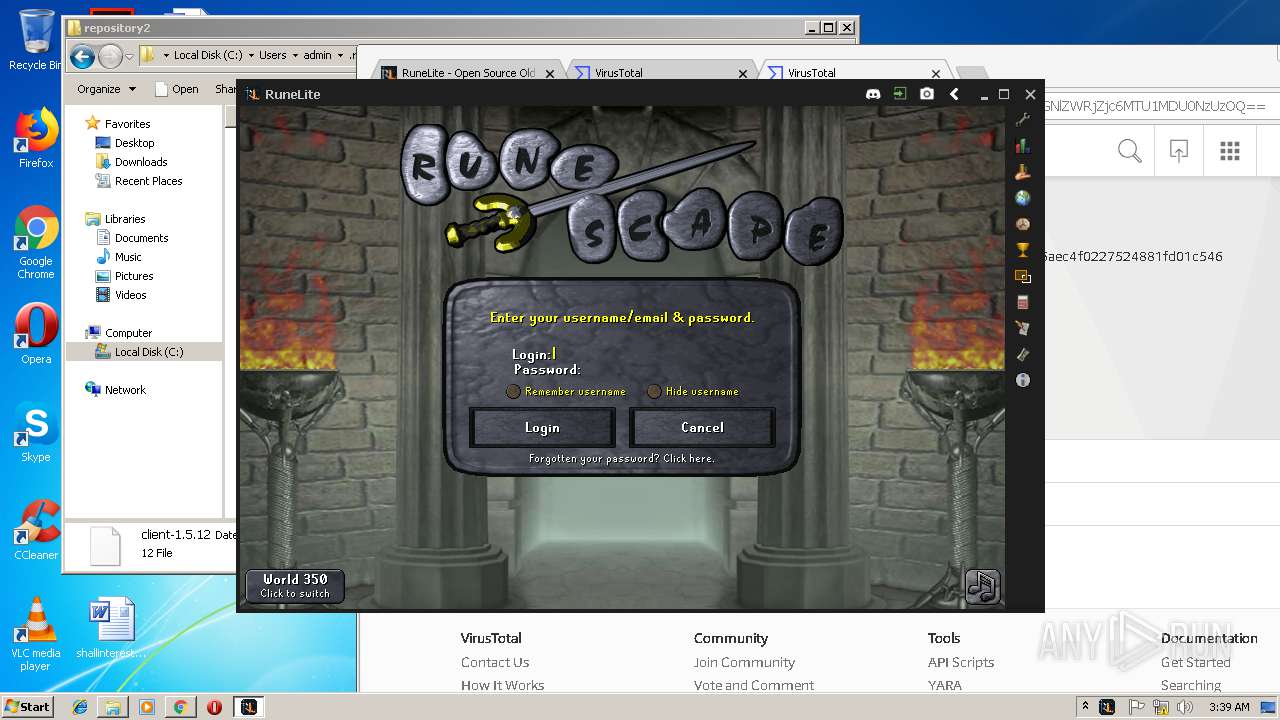
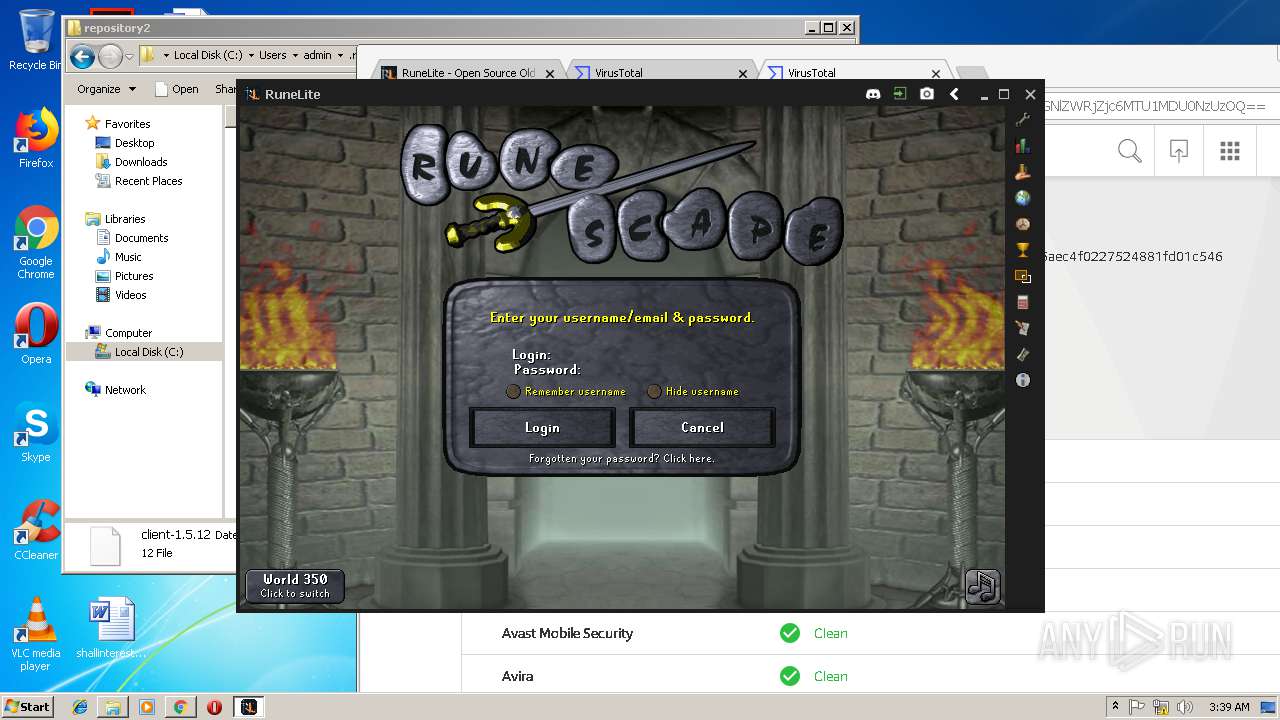
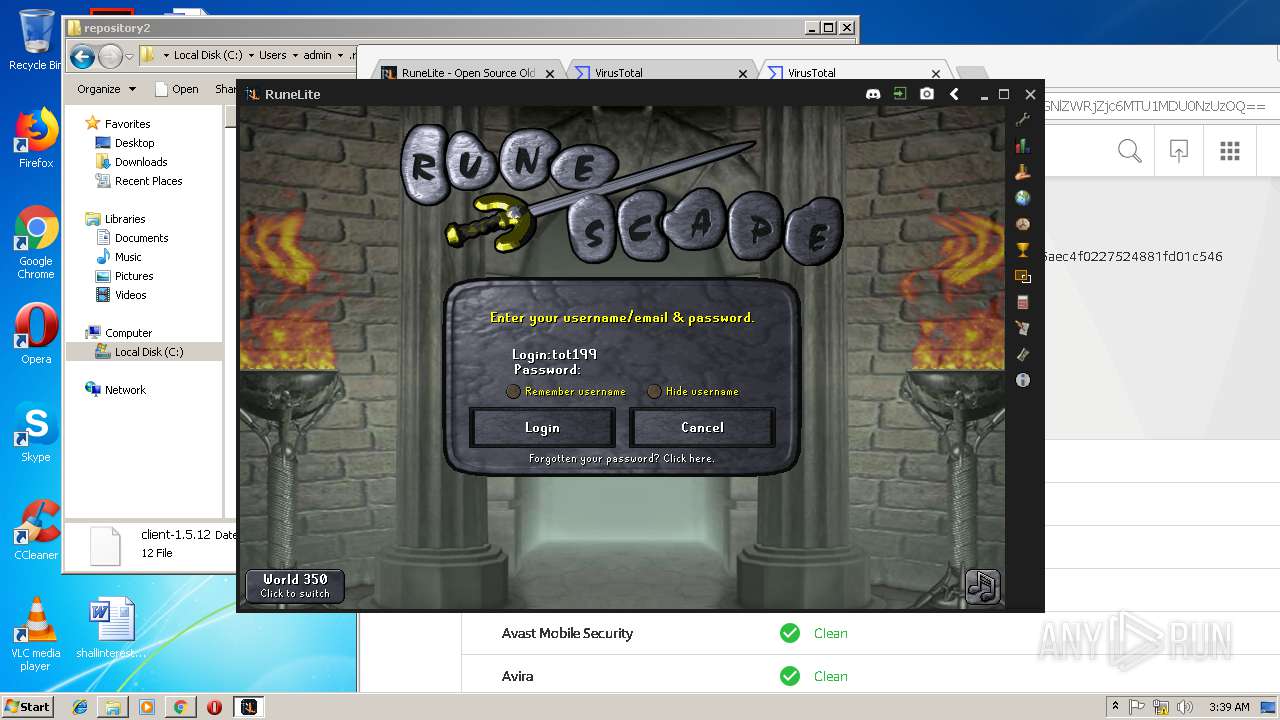
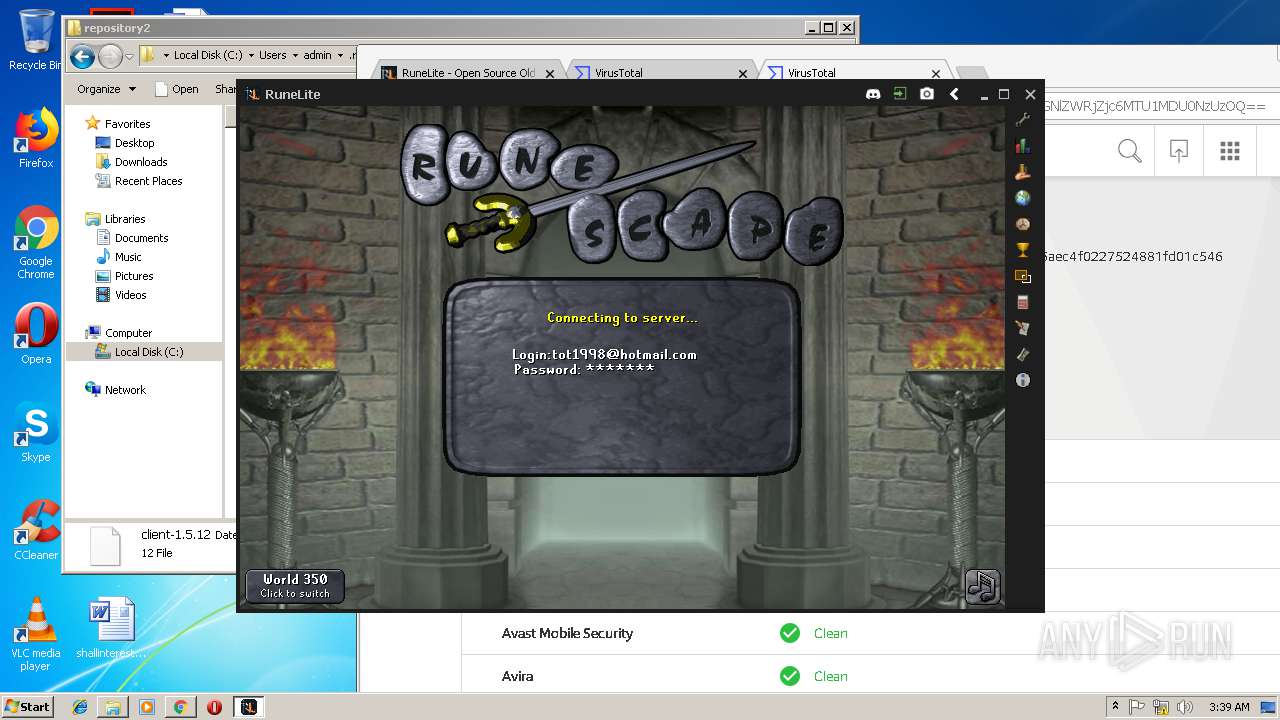
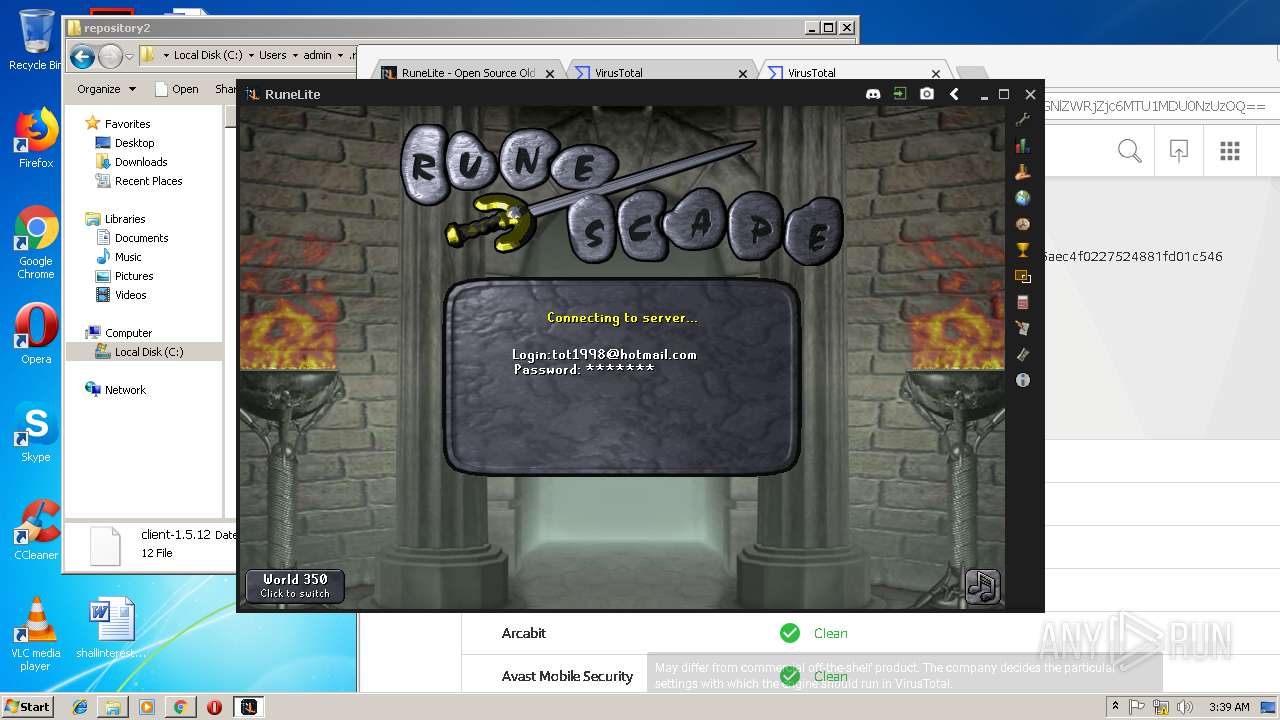
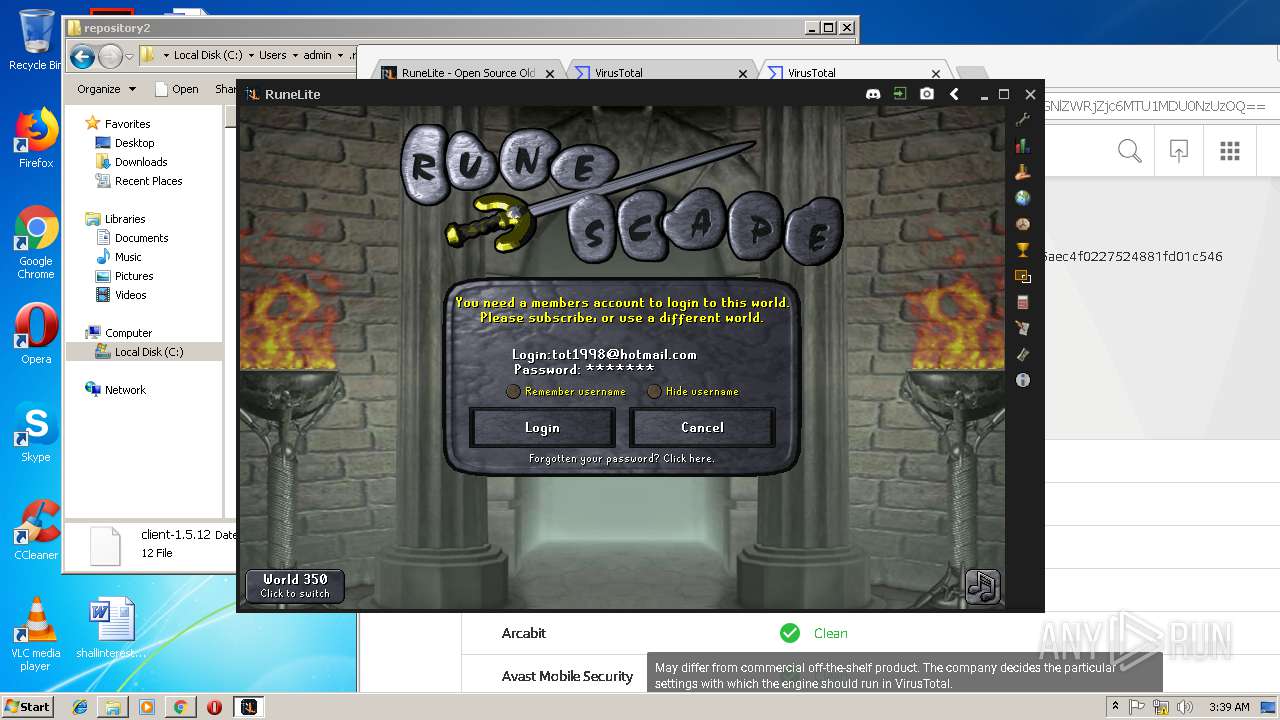
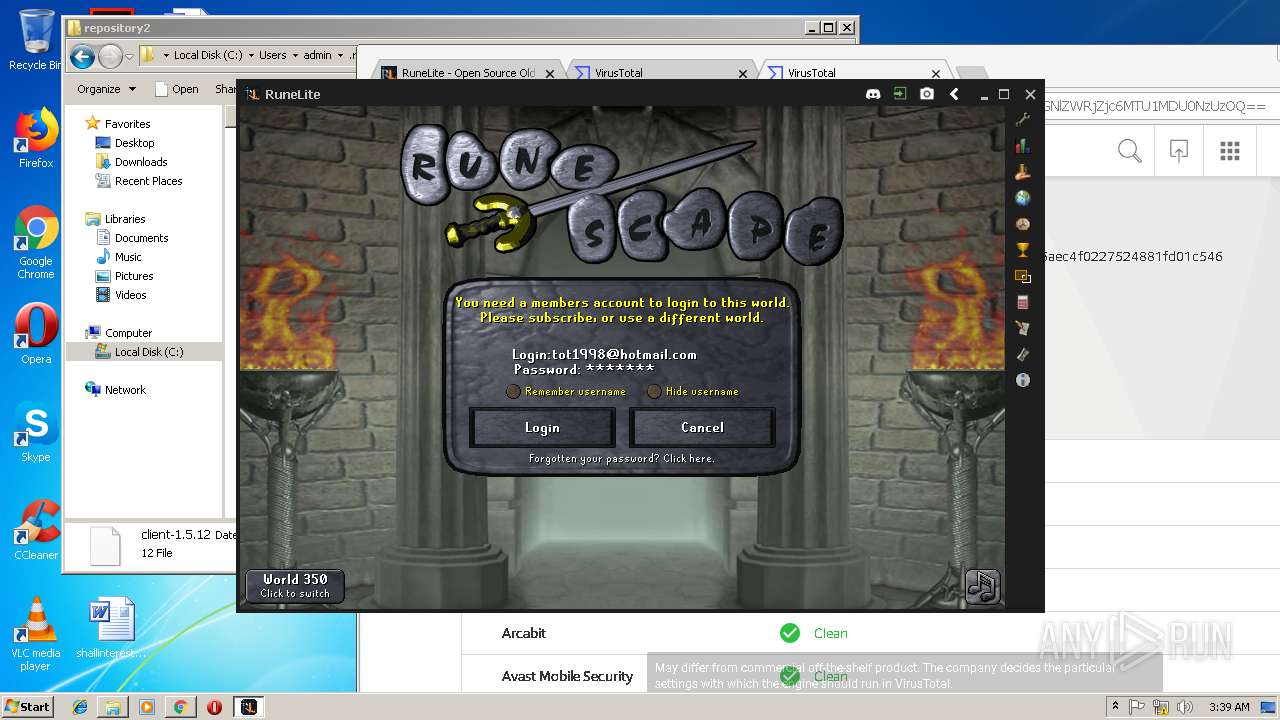
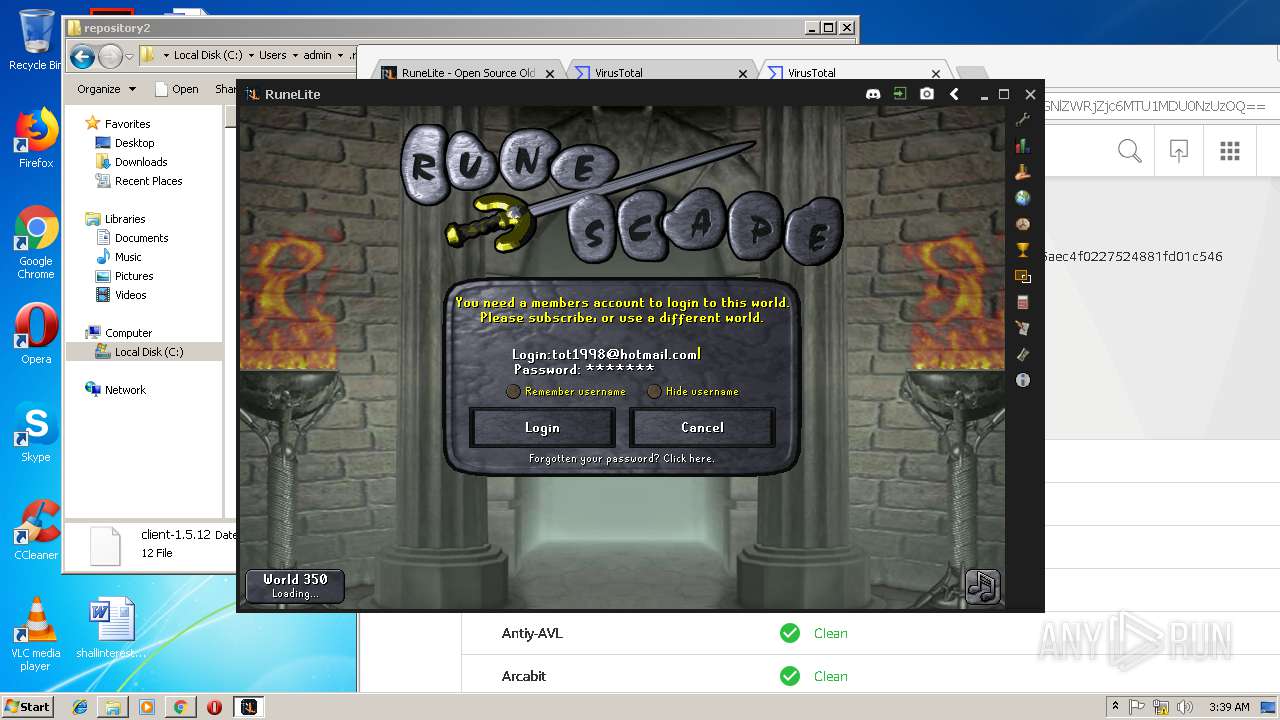
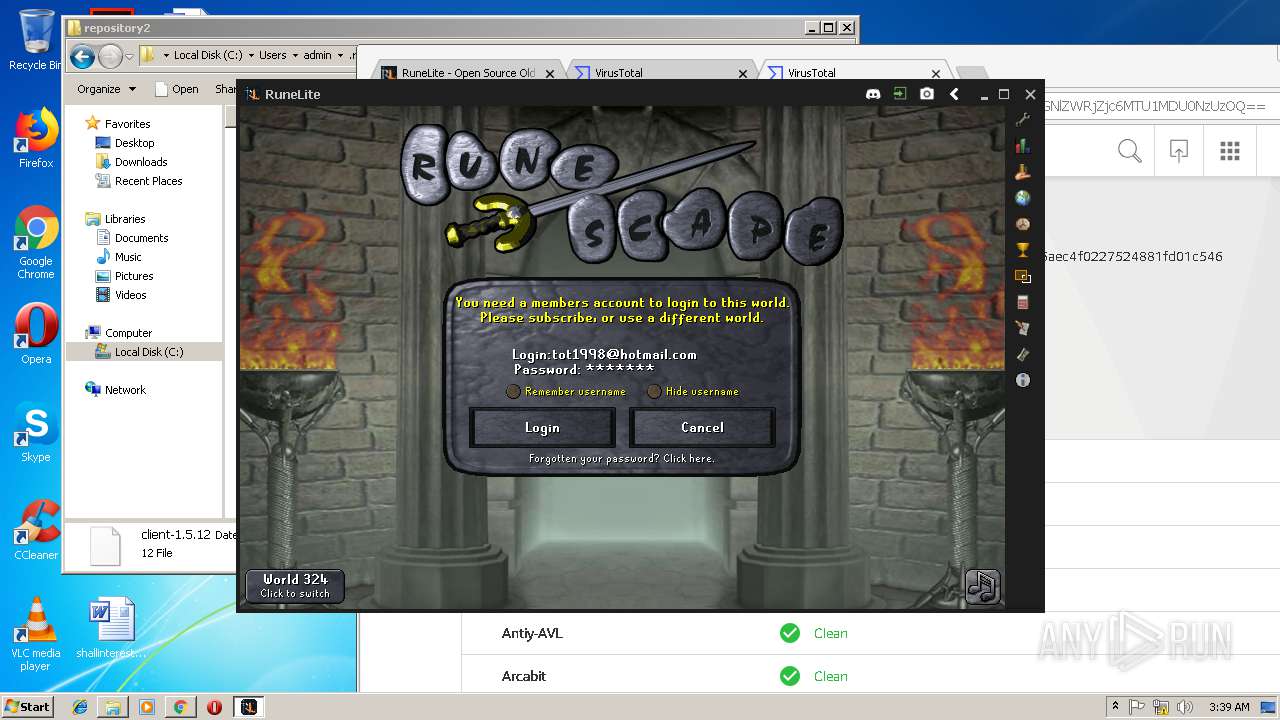
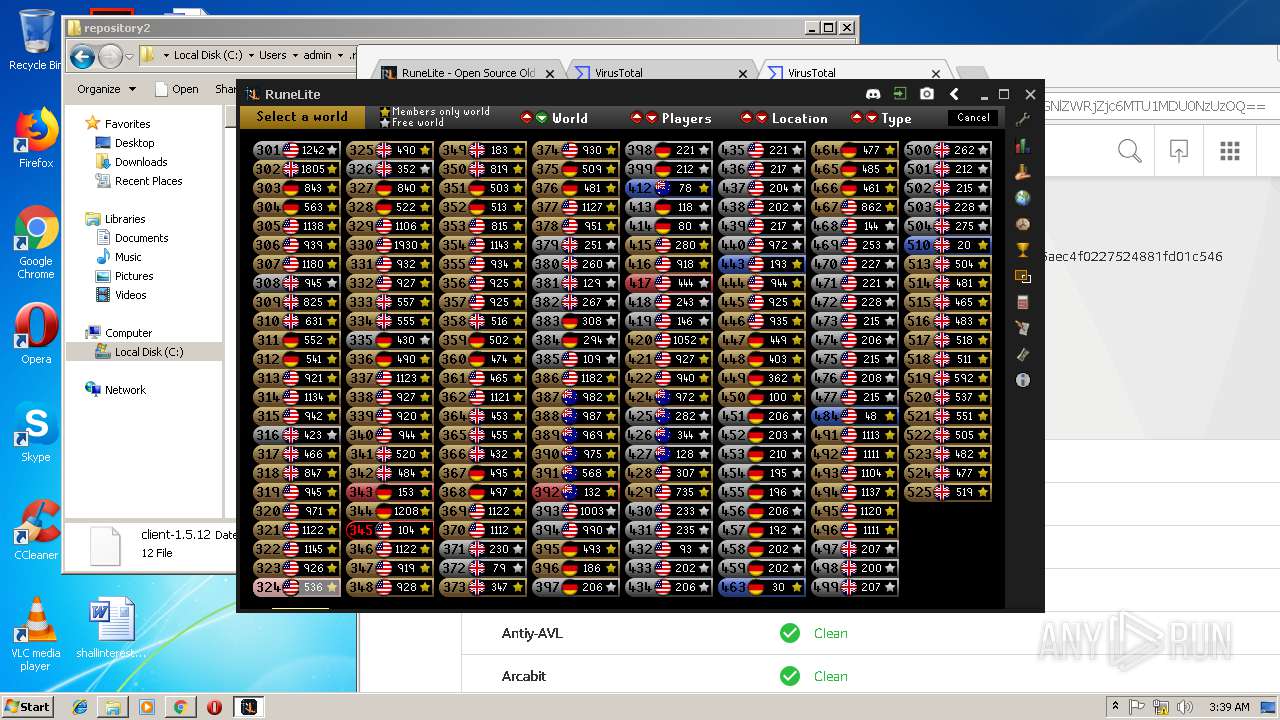
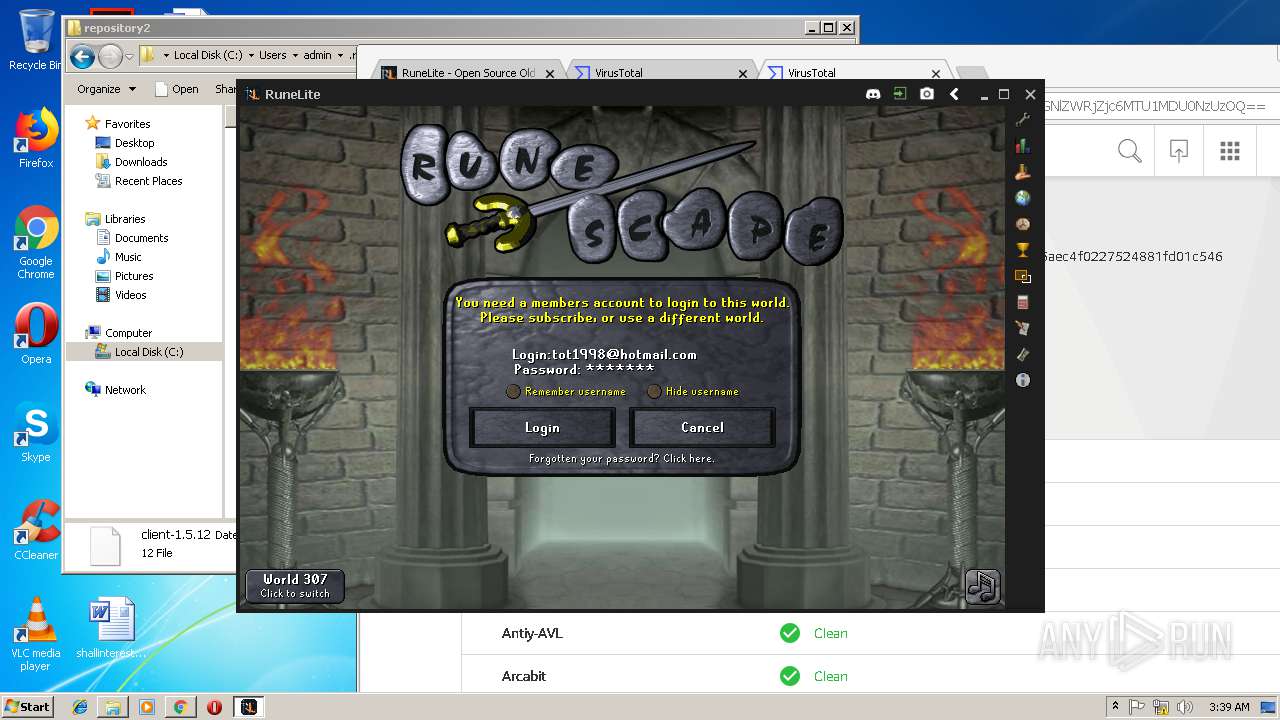
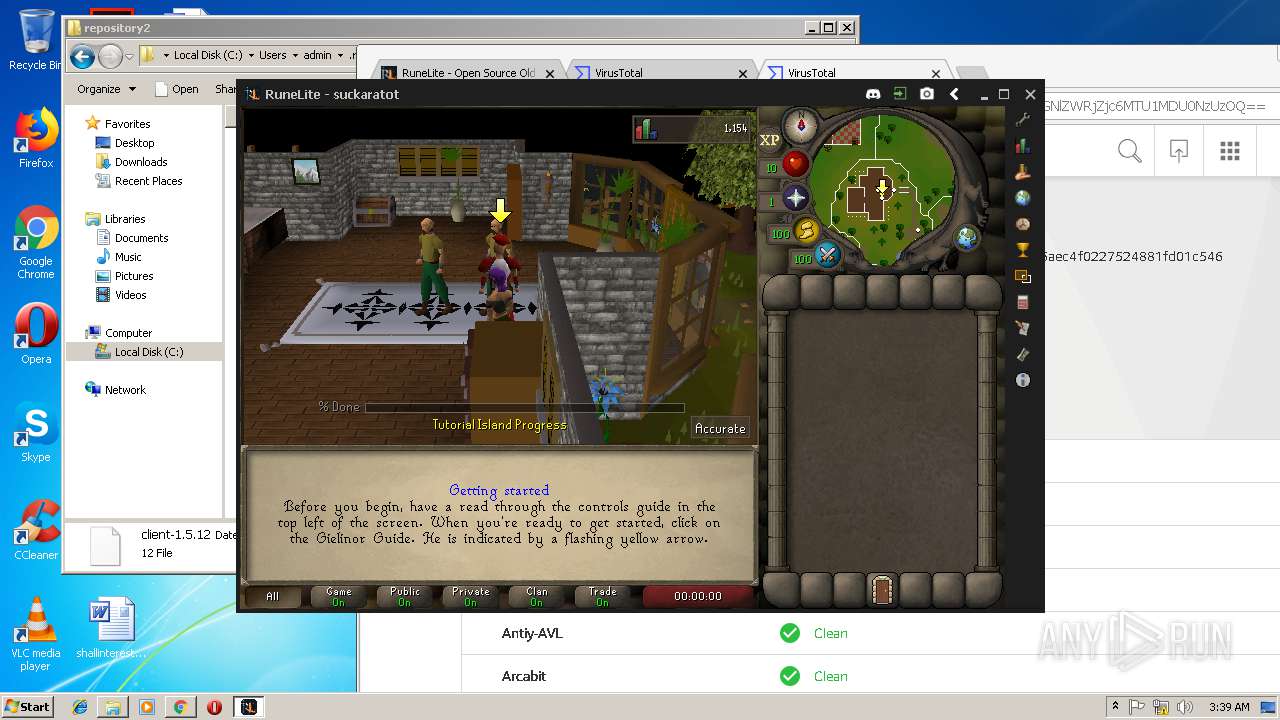
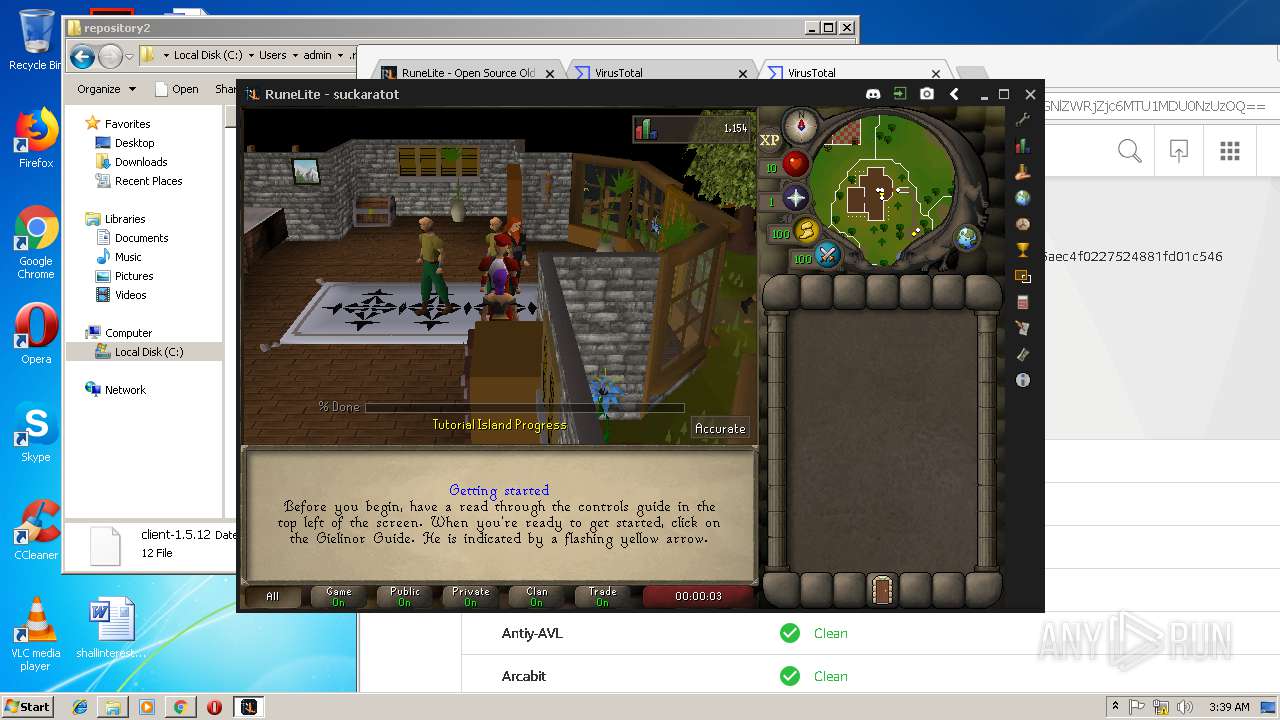
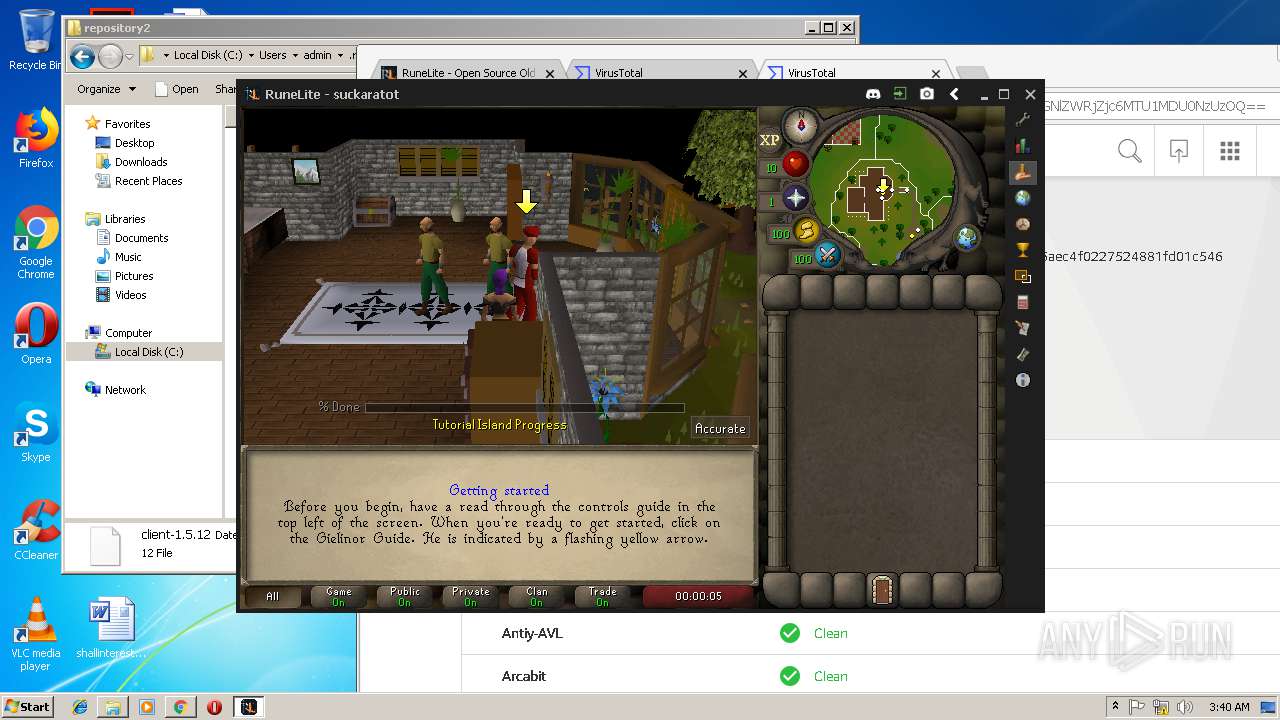
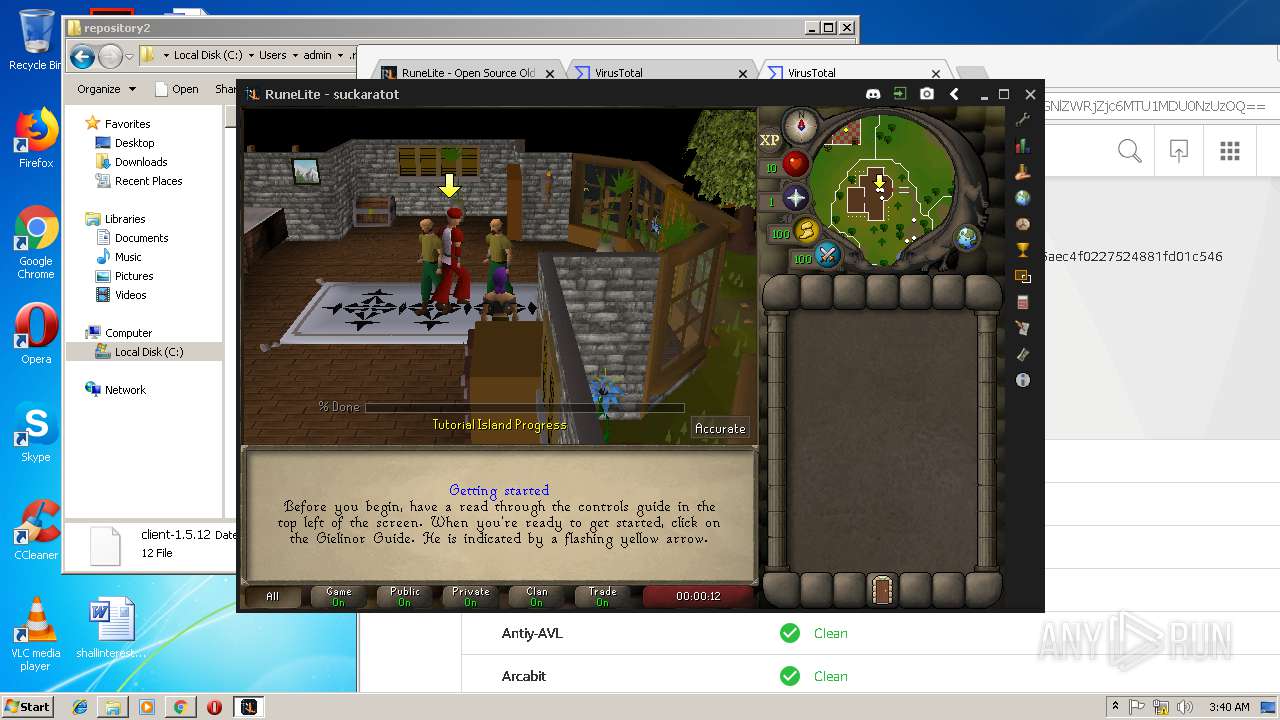
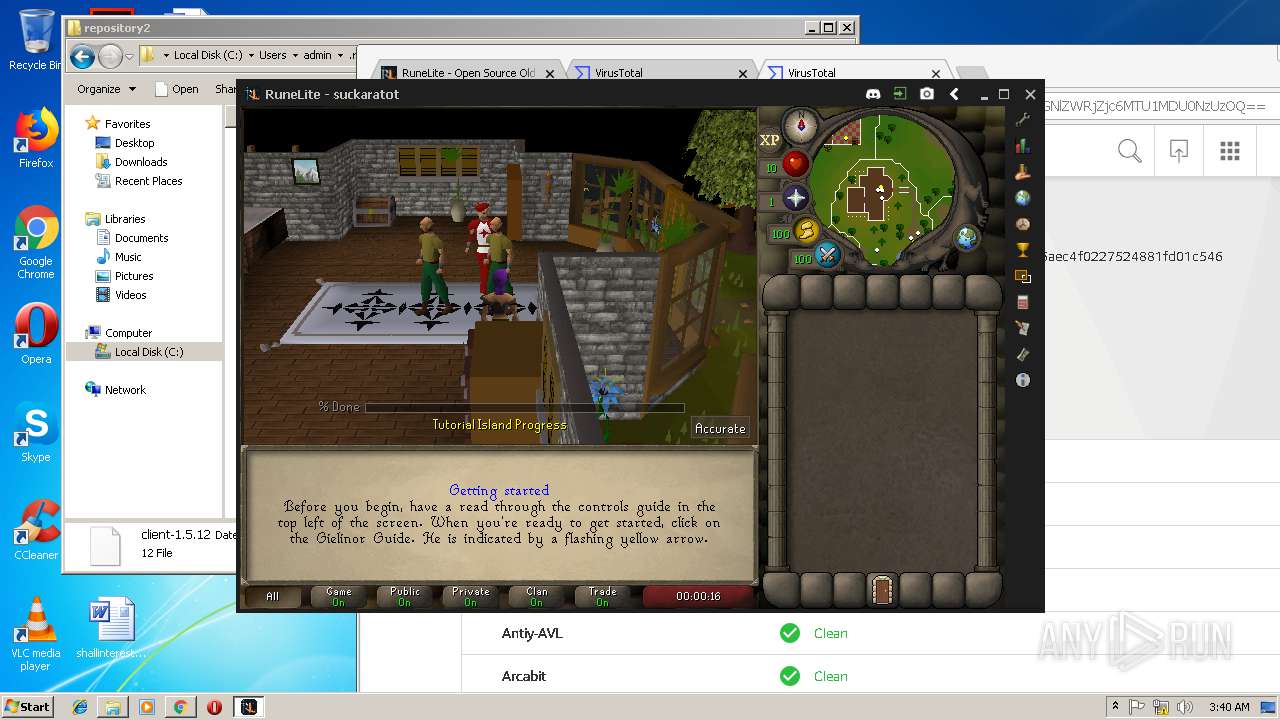
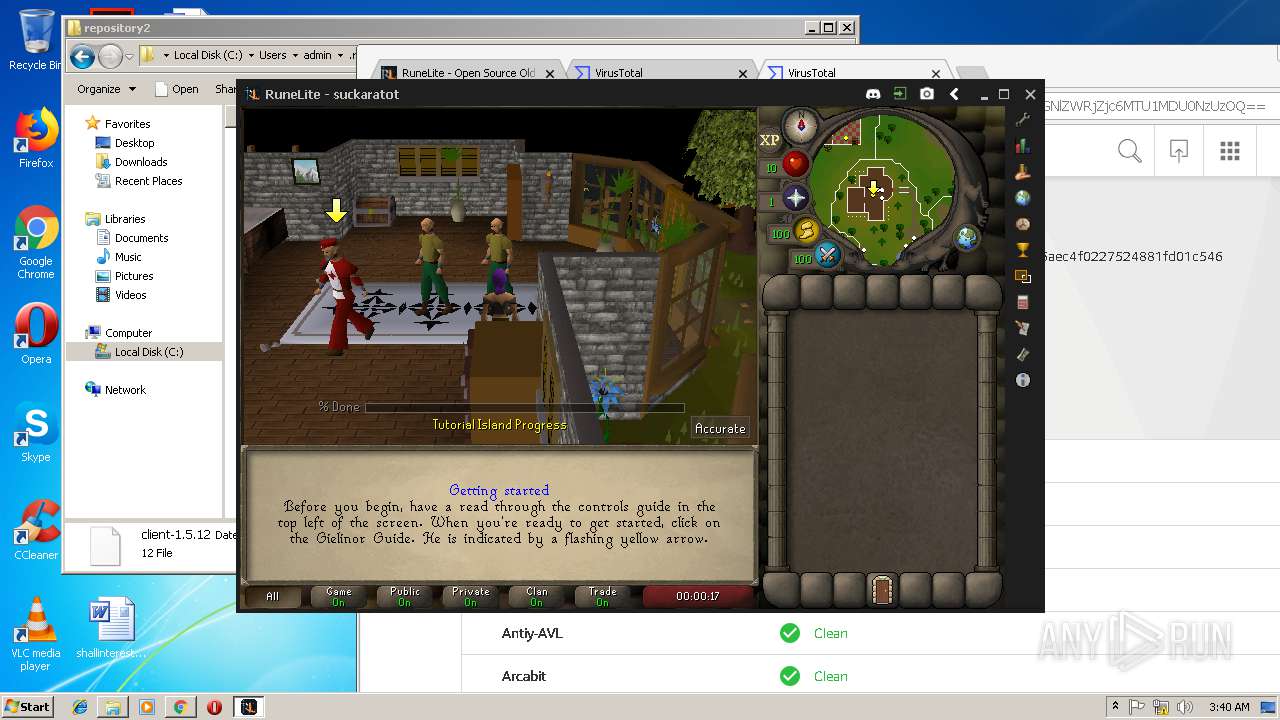
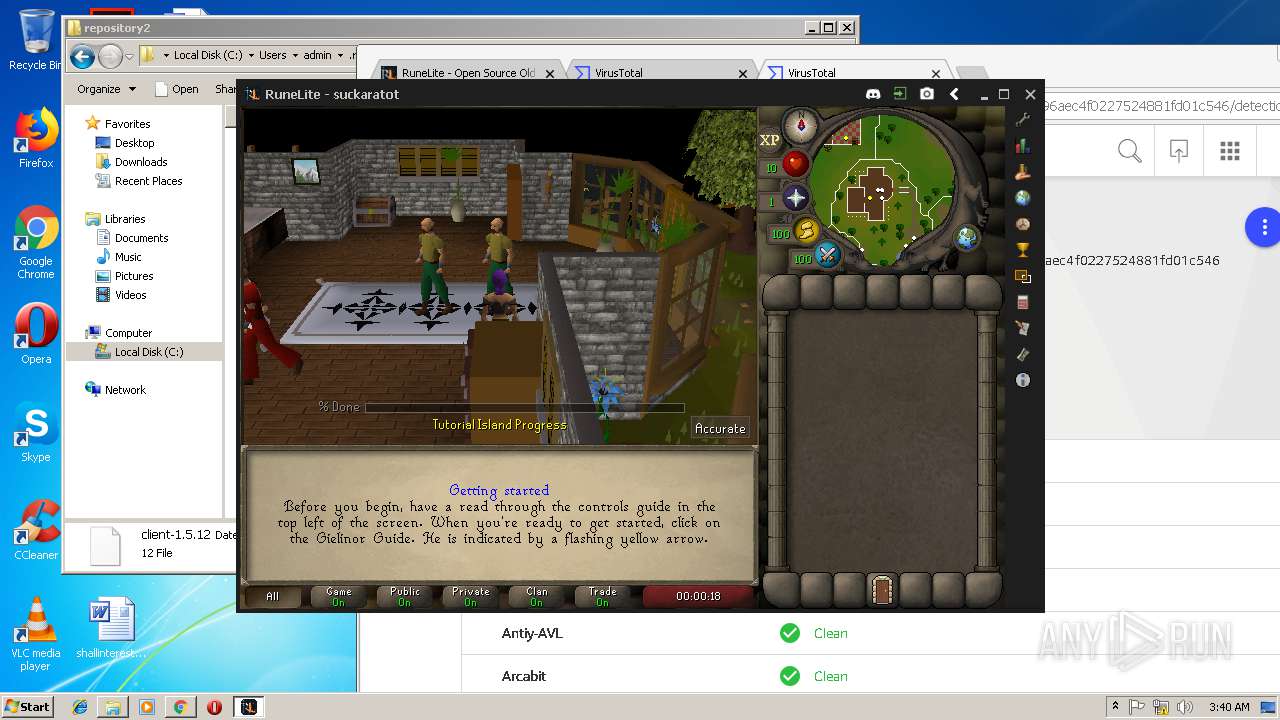
| 2092 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -cp C:\Users\admin\.runelite\repository2\client-1.5.12;C:\Users\admin\.runelite\repository2\slf4j-api-1.7.25.jar;C:\Users\admin\.runelite\repository2\logback-classic-1.2.3.jar;C:\Users\admin\.runelite\repository2\logback-core-1.2.3.jar;C:\Users\admin\.runelite\repository2\jopt-simple-5.0.1.jar;C:\Users\admin\.runelite\repository2\guava-23.2-jre.jar;C:\Users\admin\.runelite\repository2\jsr305-1.3.9.jar;C:\Users\admin\.runelite\repository2\error_prone_annotations-2.0.18.jar;C:\Users\admin\.runelite\repository2\j2objc-annotations-1.1.jar;C:\Users\admin\.runelite\repository2\animal-sniffer-annotations-1.14.jar;C:\Users\admin\.runelite\repository2\guice-4.1.0-no_aop.jar;C:\Users\admin\.runelite\repository2\javax.inject-1.jar;C:\Users\admin\.runelite\repository2\aopalliance-1.0.jar;C:\Users\admin\.runelite\repository2\gson-2.8.5.jar;C:\Users\admin\.runelite\repository2\substance-8.0.02.jar;C:\Users\admin\.runelite\repository2\trident-1.5.00.jar;C:\Users\admin\.runelite\repository2\commons-text-1.2.jar;C:\Users\admin\.runelite\repository2\commons-lang3-3.7.jar;C:\Users\admin\.runelite\repository2\jogl-all-2.3.2.jar;C:\Users\admin\.runelite\repository2\jogl-all-2.3.2-natives-windows-amd64.jar;C:\Users\admin\.runelite\repository2\jogl-all-2.3.2-natives-windows-i586.jar;C:\Users\admin\.runelite\repository2\jogl-all-2.3.2-natives-linux-amd64.jar;C:\Users\admin\.runelite\repository2\jogl-all-2.3.2-natives-linux-i586.jar;C:\Users\admin\.runelite\repository2\gluegen-rt-2.3.2.jar;C:\Users\admin\.runelite\repository2\gluegen-rt-2.3.2-natives-windows-amd64.jar;C:\Users\admin\.runelite\repository2\gluegen-rt-2.3.2-natives-windows-i586.jar;C:\Users\admin\.runelite\repository2\gluegen-rt-2.3.2-natives-linux-amd64.jar;C:\Users\admin\.runelite\repository2\gluegen-rt-2.3.2-natives-linux-i586.jar;C:\Users\admin\.runelite\repository2\jbsdiff-1.0.jar;C:\Users\admin\.runelite\repository2\commons-compress-1.5.jar;C:\Users\admin\.runelite\repository2\jna-4.5.1.jar;C:\Users\admin\.runelite\repository2\jna-platform-4.5.1.jar;C:\Users\admin\.runelite\repository2\runelite-api-1.5.12.jar;C:\Users\admin\.runelite\repository2\runescape-api-1.5.12.jar;C:\Users\admin\.runelite\repository2\client-patch-1.5.12.jar;C:\Users\admin\.runelite\repository2\http-api-1.5.12.jar;C:\Users\admin\.runelite\repository2\okhttp-3.7.0.jar;C:\Users\admin\.runelite\repository2\okio-1.12.0.jar;C:\Users\admin\.runelite\repository2\commons-csv-1.4.jar;C:\Users\admin\.runelite\repository2\discord-1.1.jar -Xmx512m -Xss2m -XX:CompileThreshold=1500 -Xincgc -XX:+UseConcMarkSweepGC -XX:+UseParNewGC -Djna.nosys=true -Dsun.java2d.noddraw=false -Dsun.java2d.opengl=false -Djava.net.preferIPv4Stack=true -Djava.net.preferIPv4Addresses=true -Drunelite.launcher.version=1.6.2-SNAPSHOT net.runelite.client.RuneLite | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2144 | C:\Windows\system32\tasklist.exe | C:\Windows\system32\tasklist.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2316 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=868,16372513078222223386,8998679094437217574,131072 --enable-features=PasswordImport --service-pipe-token=4A601672AAA924C8942941DF244BA2C0 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4A601672AAA924C8942941DF244BA2C0 --renderer-client-id=5 --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=868,16372513078222223386,8998679094437217574,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=68F99F7923F8FAA61A5A3AFB56BD18C9 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=68F99F7923F8FAA61A5A3AFB56BD18C9 --renderer-client-id=14 --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=868,16372513078222223386,8998679094437217574,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A4D2BF79318D733CA47A7074DD0686ED --mojo-platform-channel-handle=5088 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
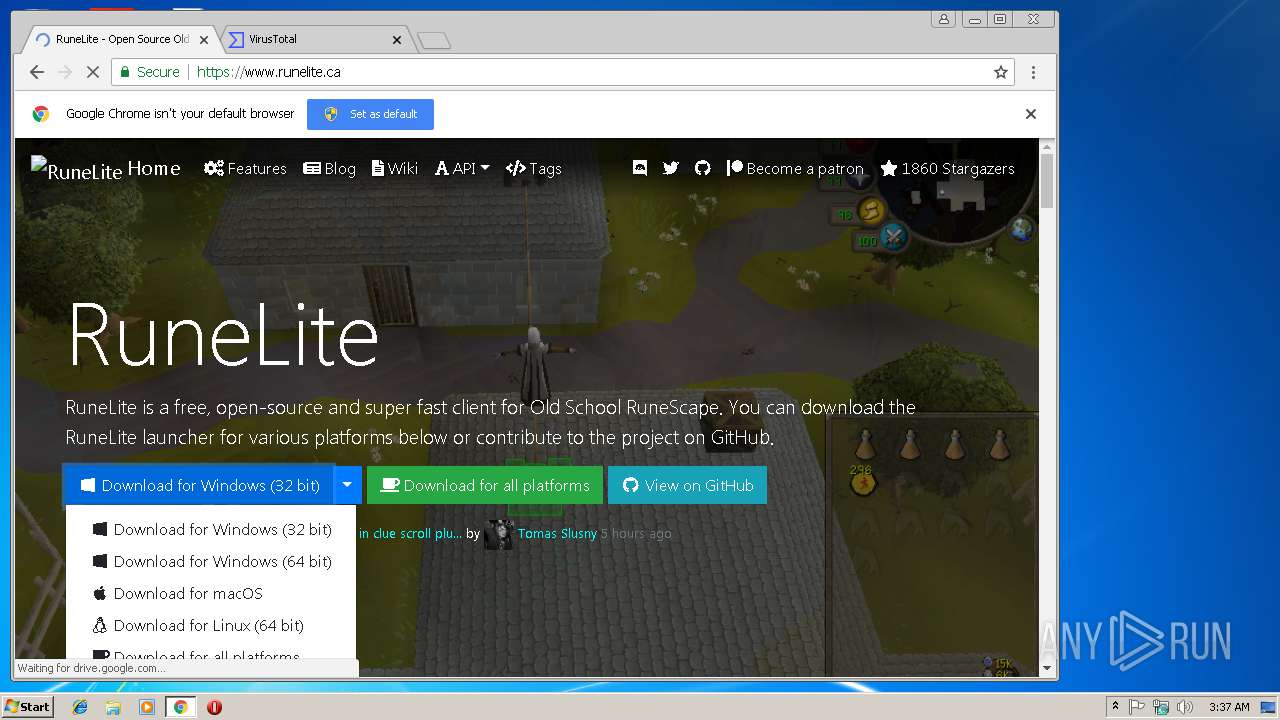
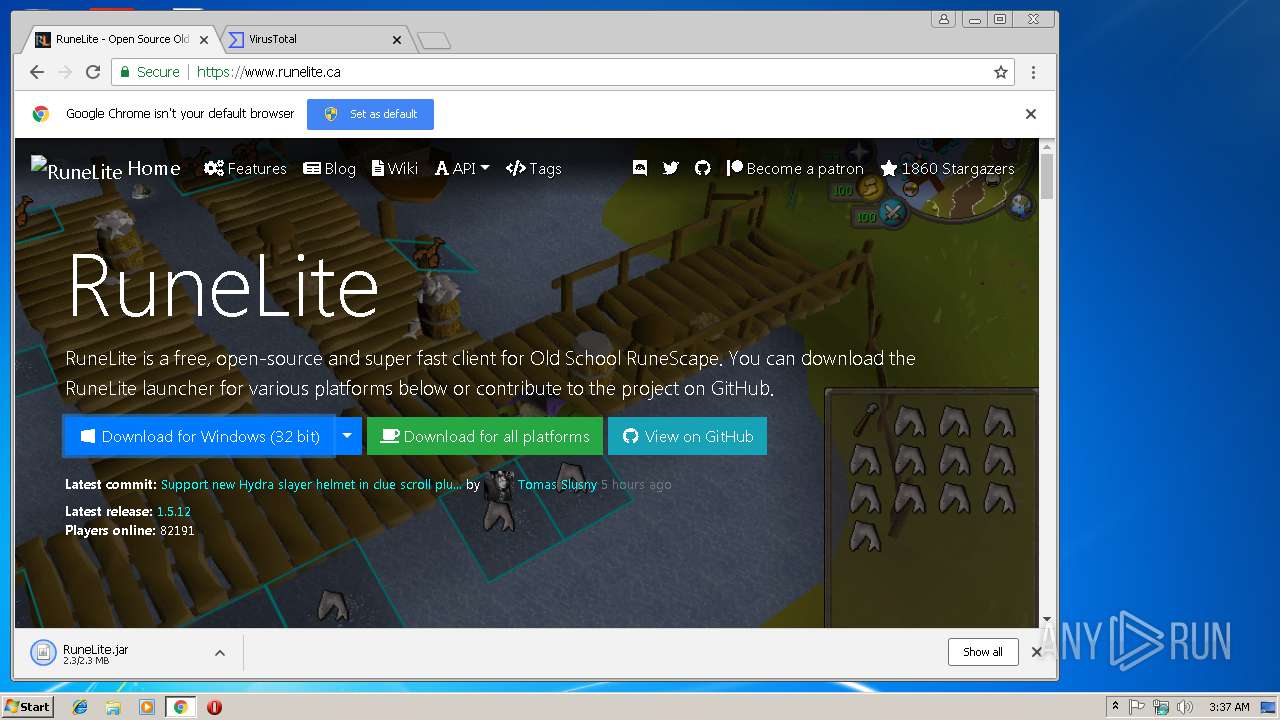
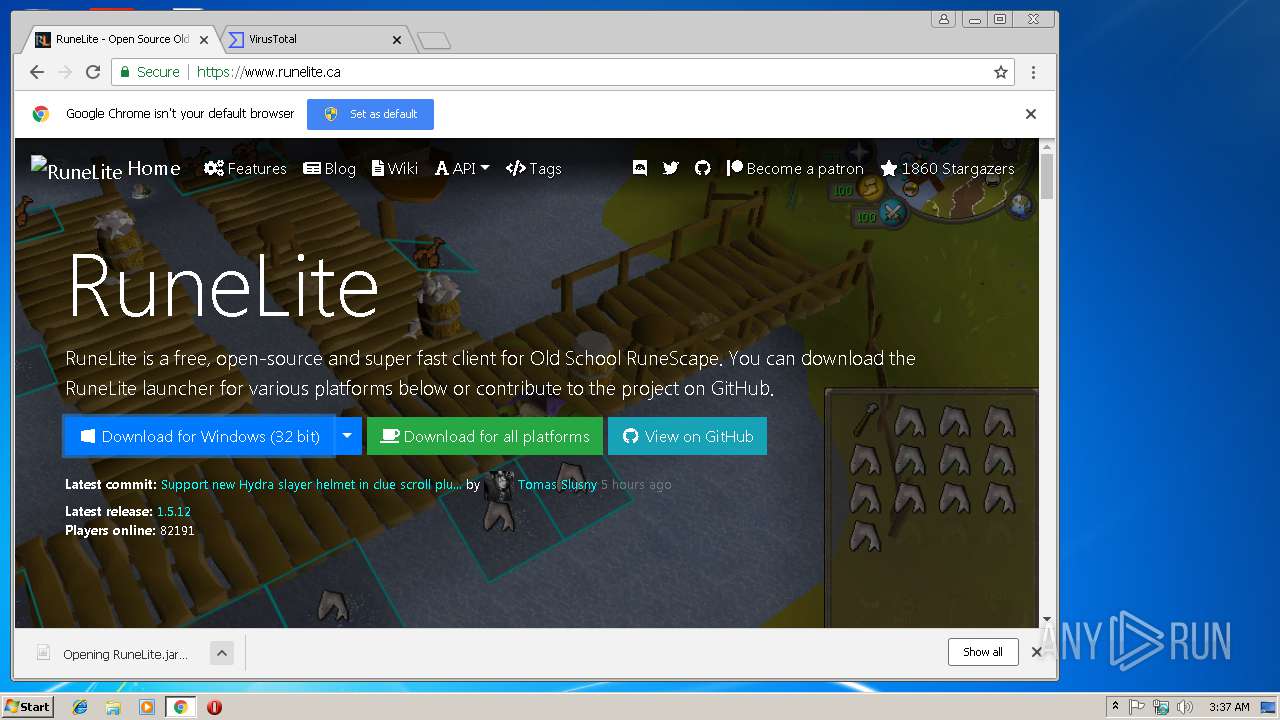
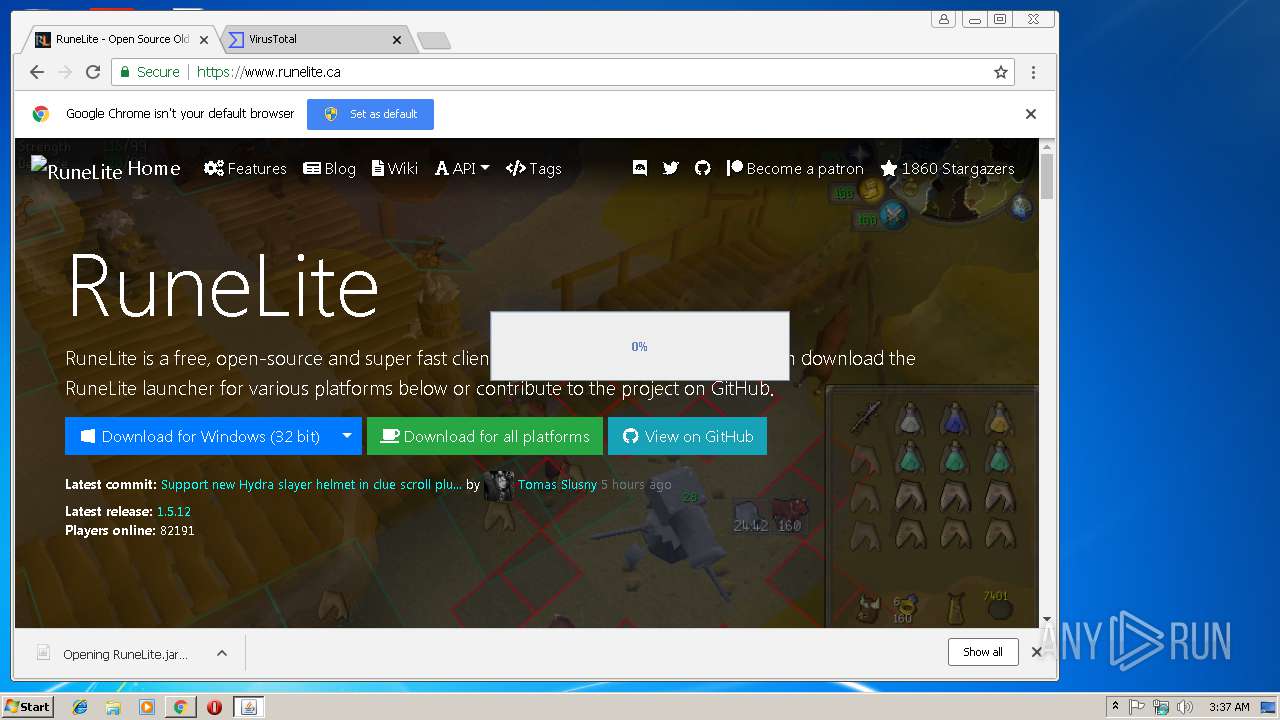
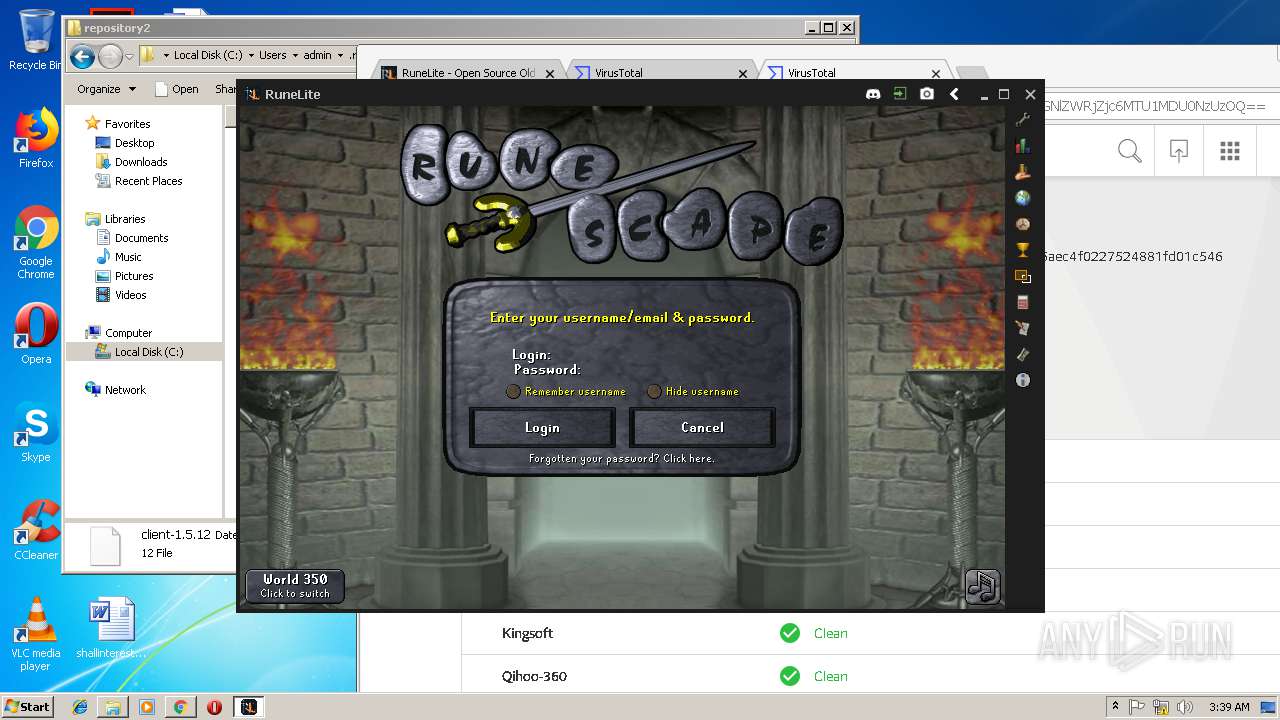
| 2596 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\RuneLite.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | chrome.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
1 691
Read events
1 441
Write events
242
Delete events
8
Modification events
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8C7C3603-33F7-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200020013000300240021004401 | |||
Executable files
15
Suspicious files
154
Text files
166
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF634B4AEABF133F94.TMP | — | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA157FE38475C4BDA.TMP | — | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB64FB7D629C49475.TMP | — | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{8C7C3604-33F7-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1372460190895C2B.TMP | — | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{8C7C3603-33F7-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\88ffe2b8-ec97-4ee2-a8b3-d63c6861410e.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
75
DNS requests
49
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
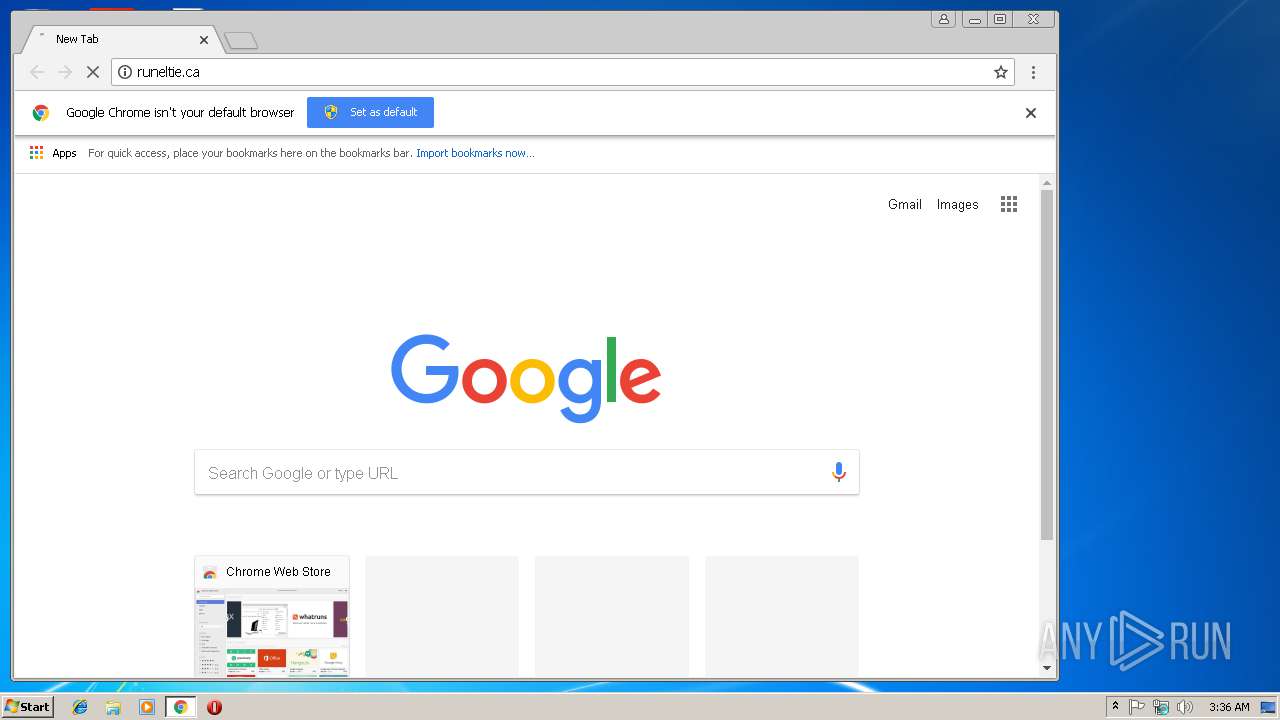
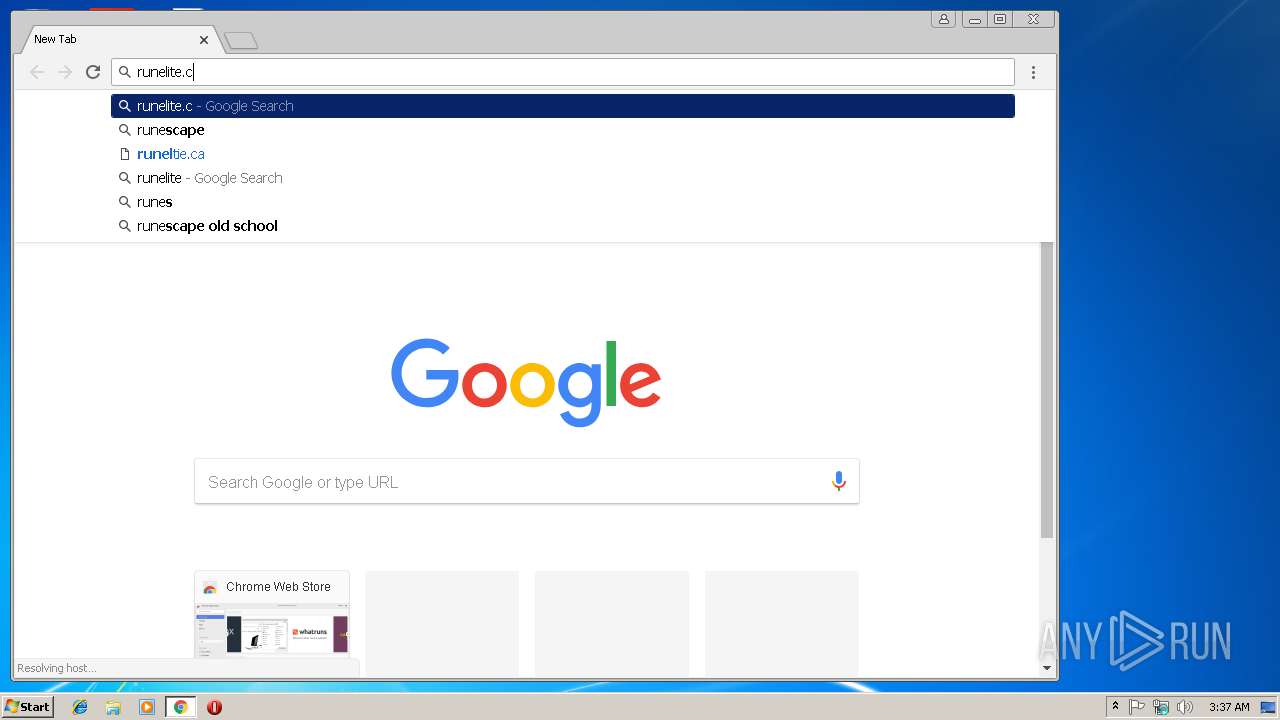
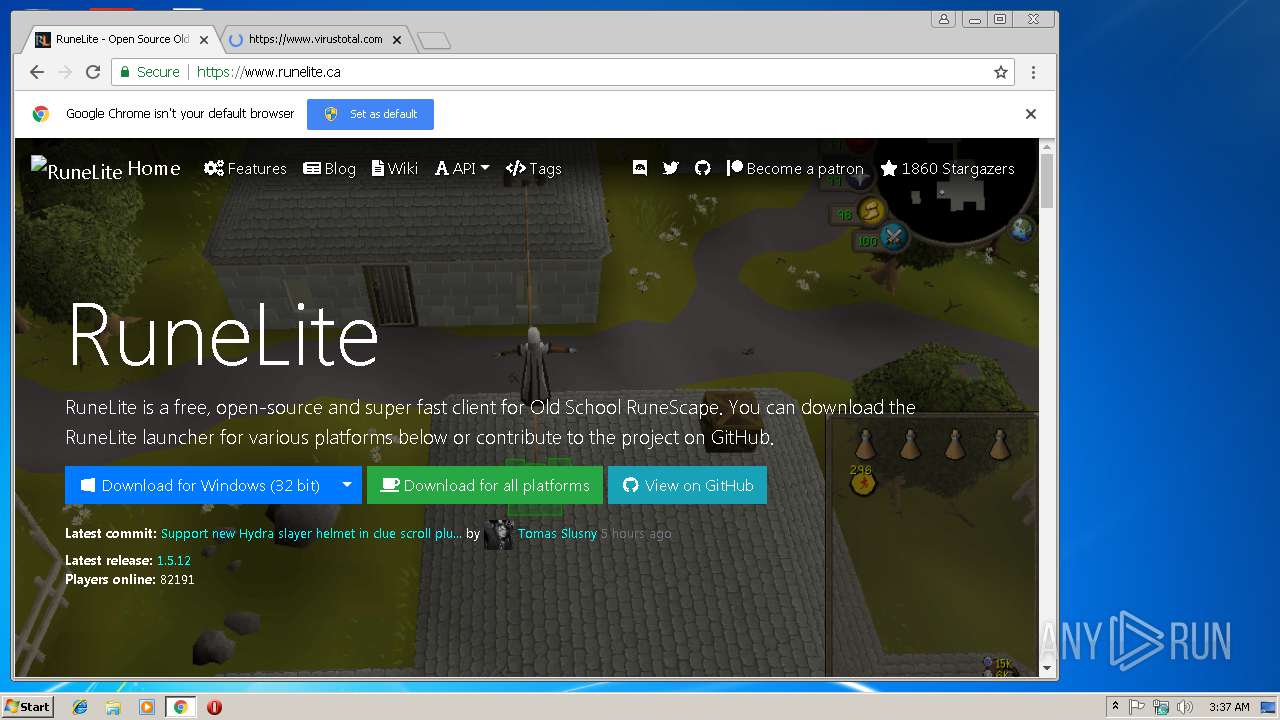
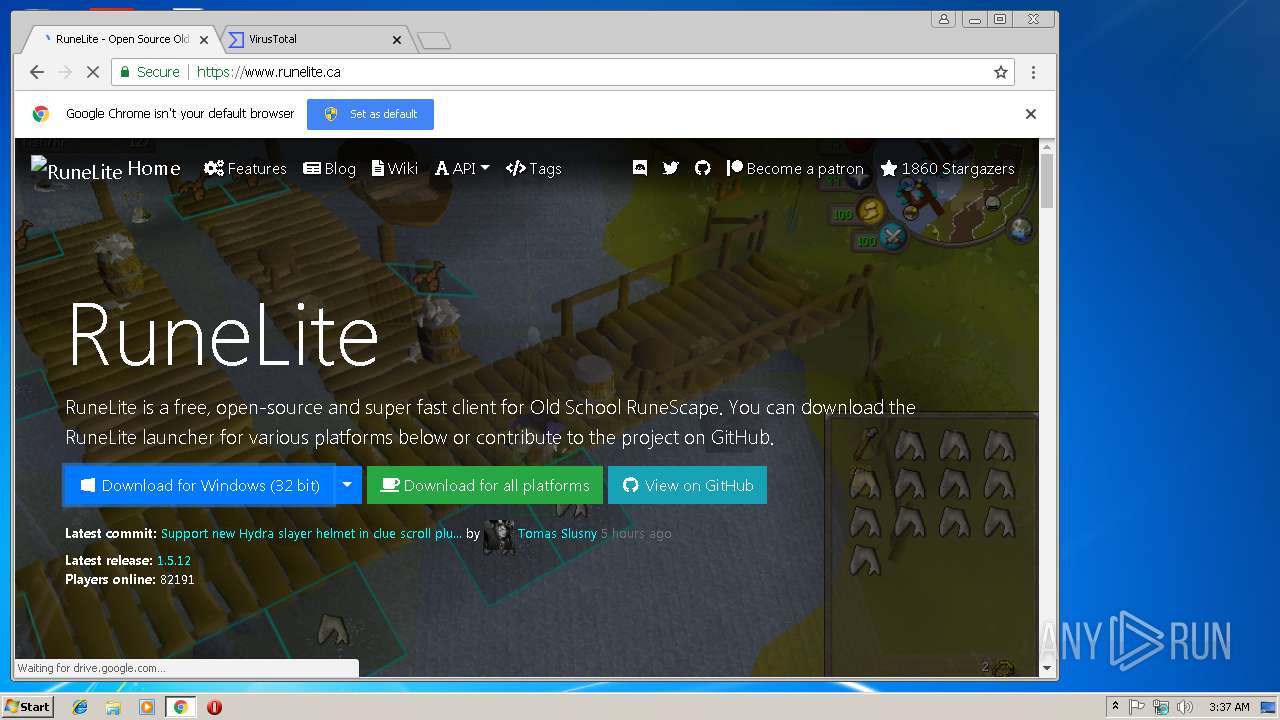
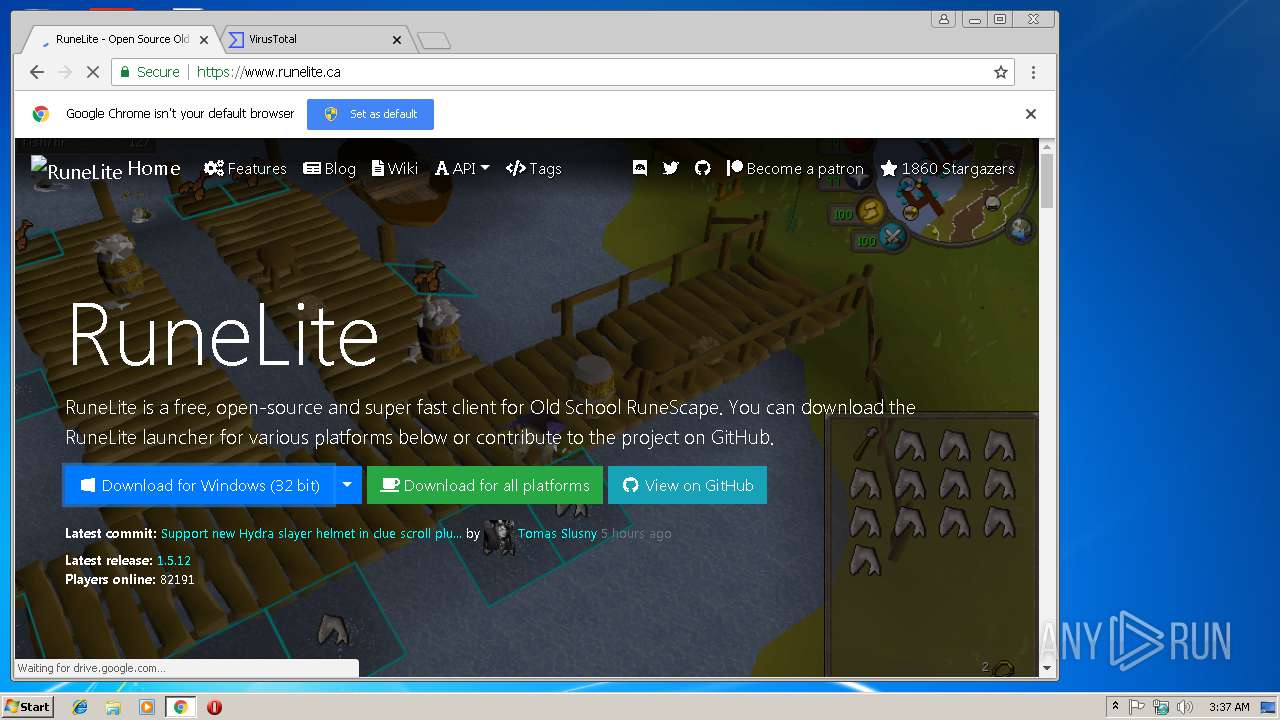
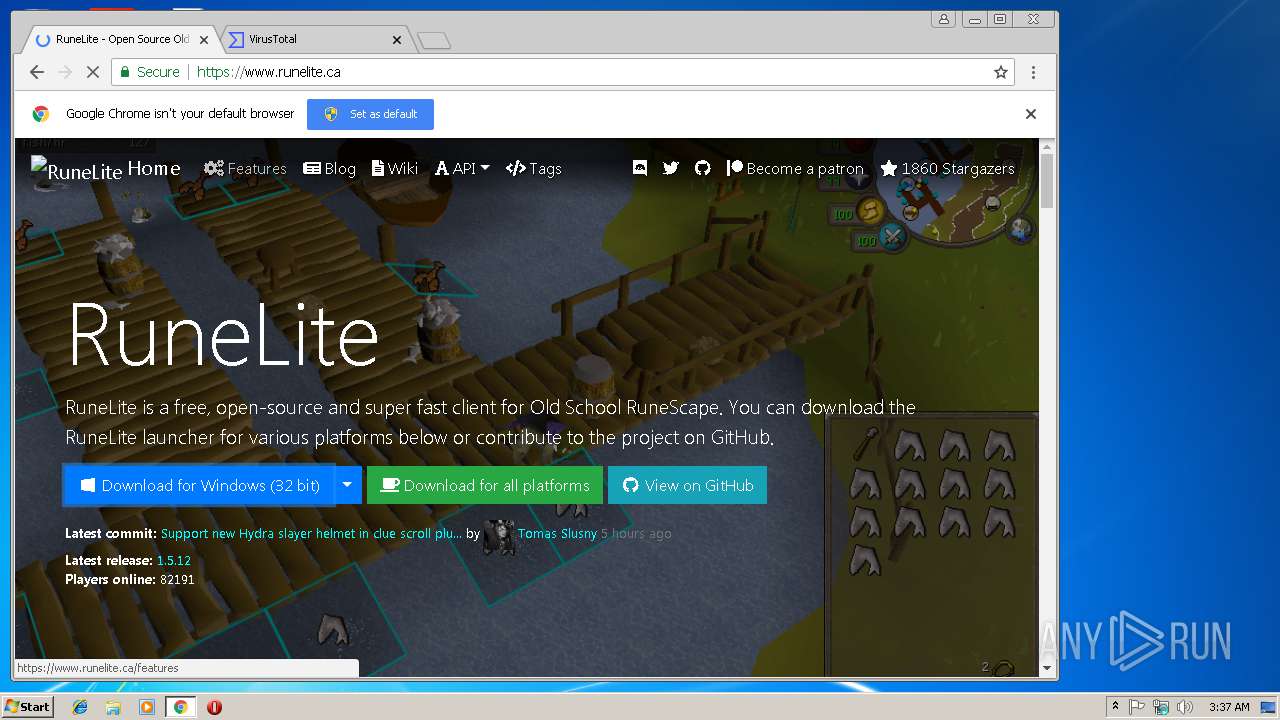
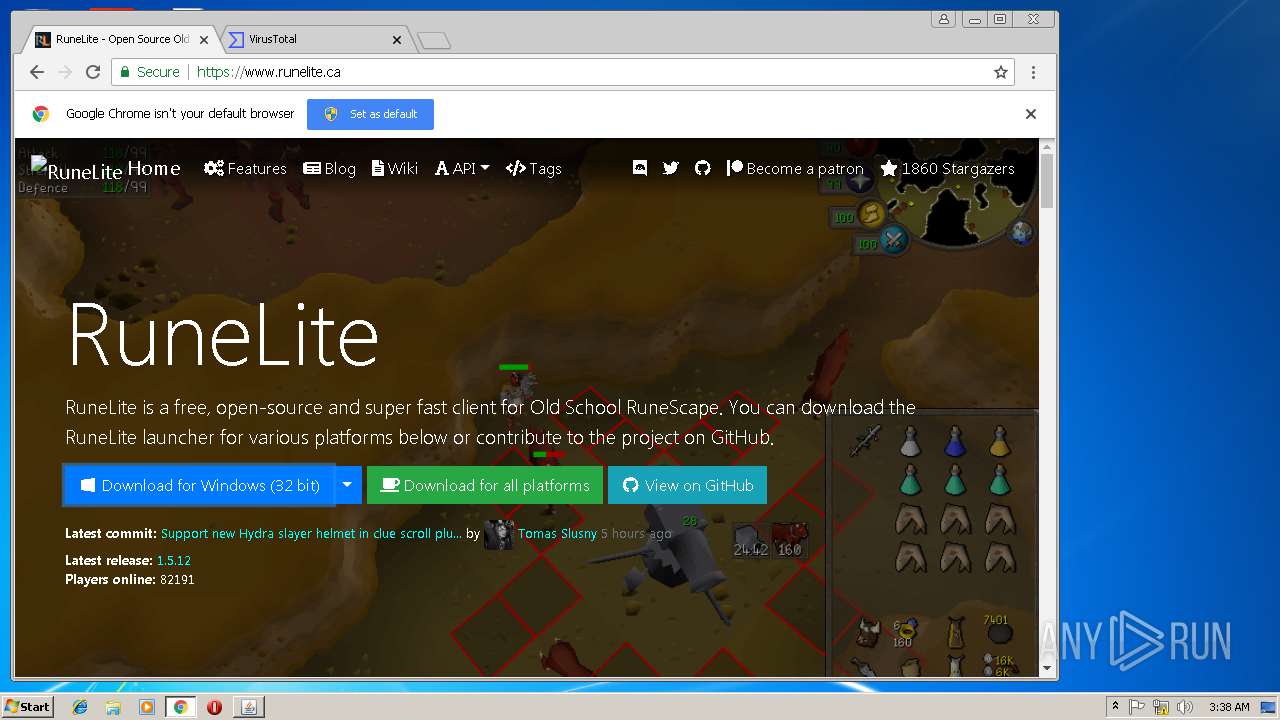
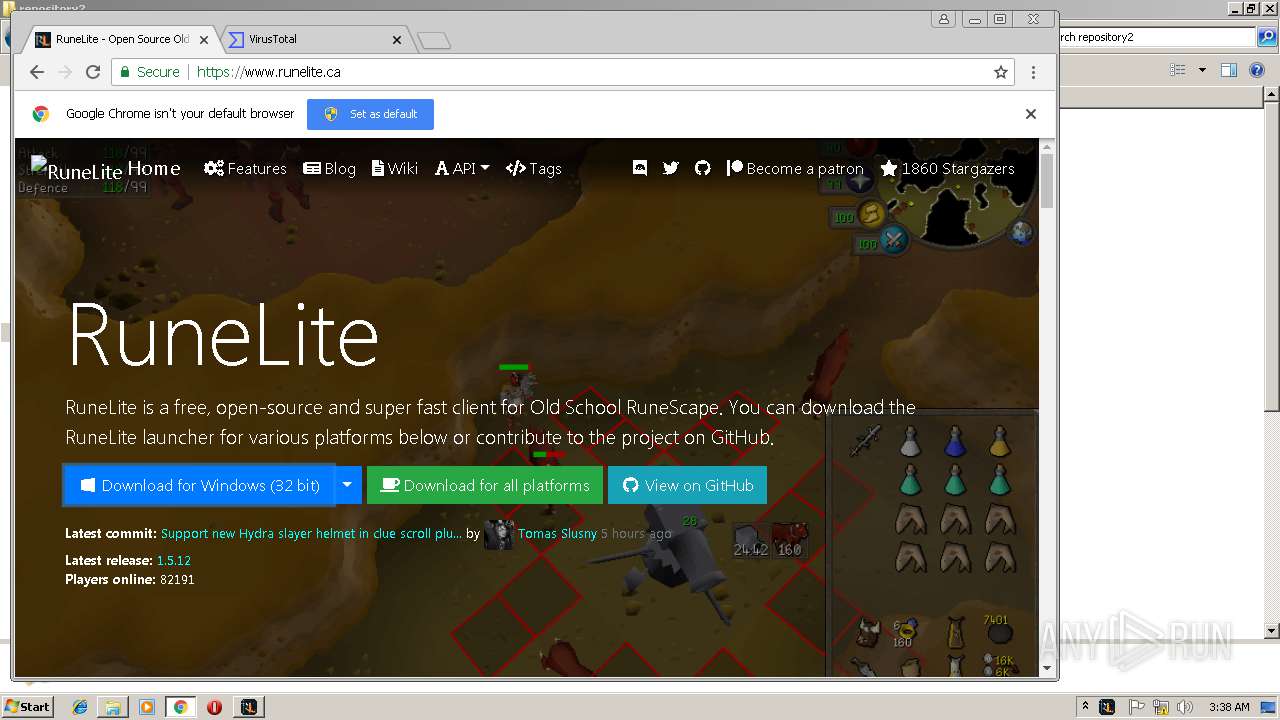
2312 | chrome.exe | GET | 301 | 104.28.27.223:80 | http://runelite.ca/ | US | html | 1.14 Kb | shared |
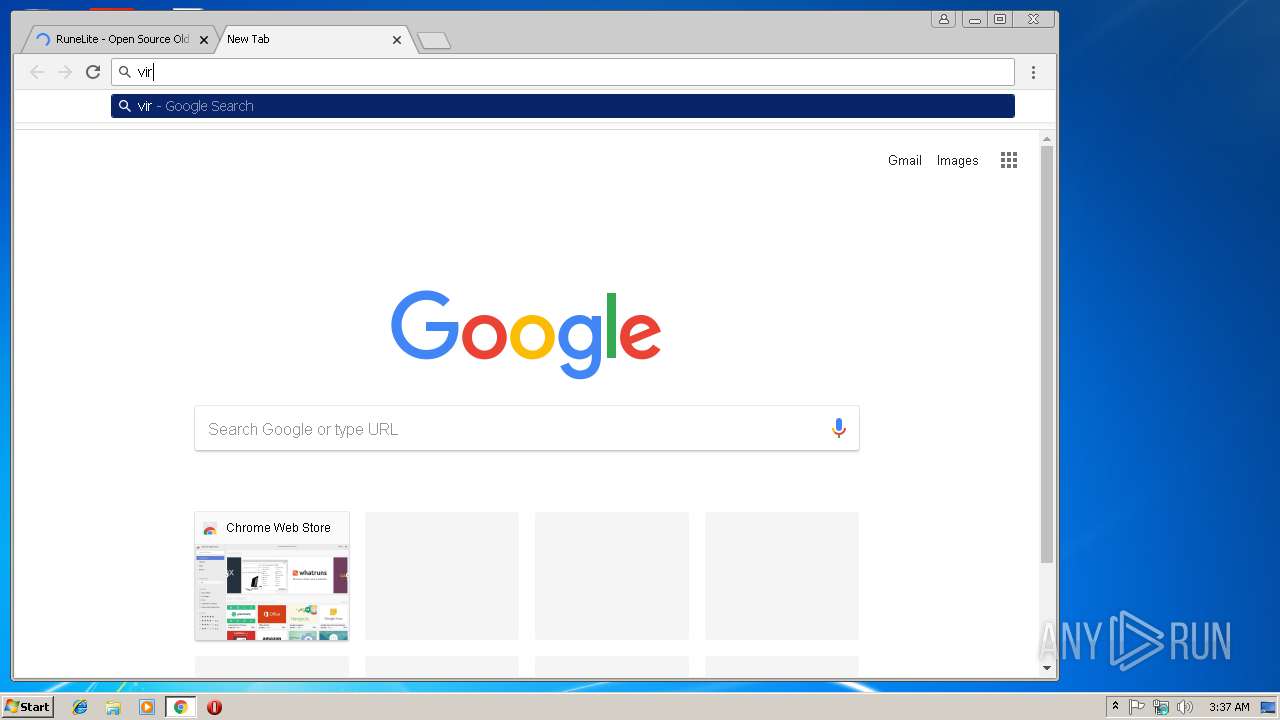
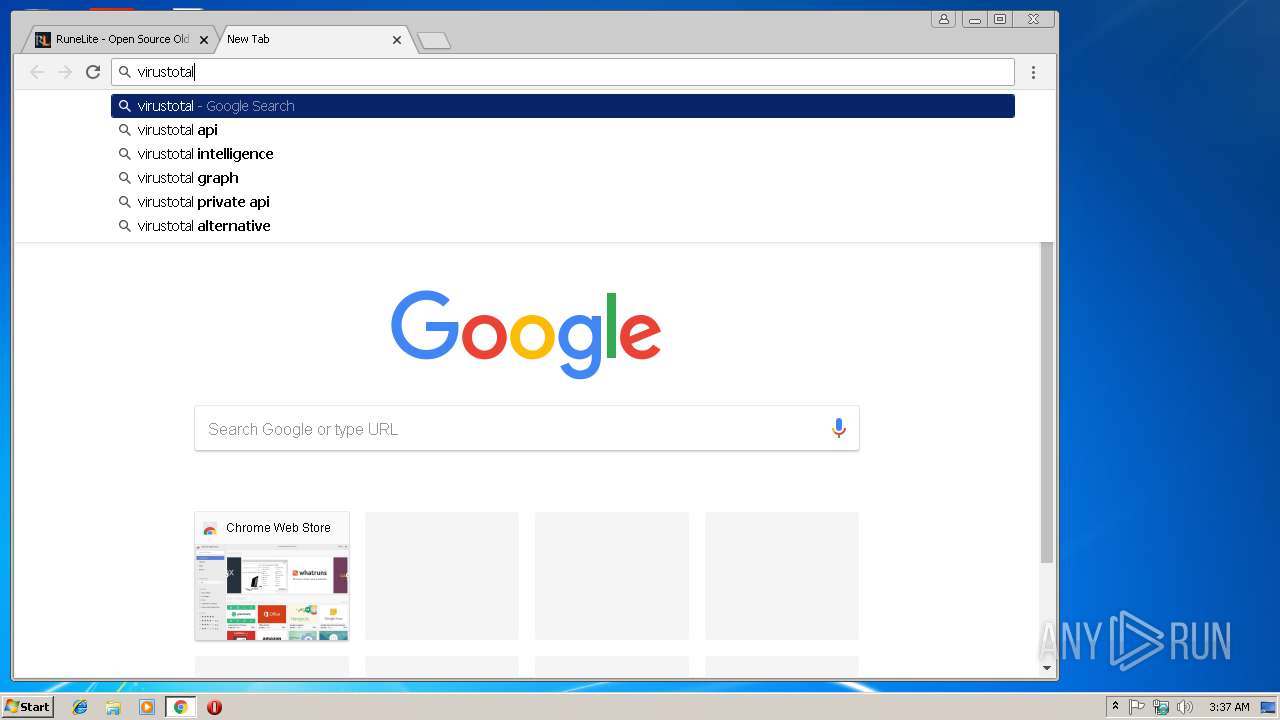
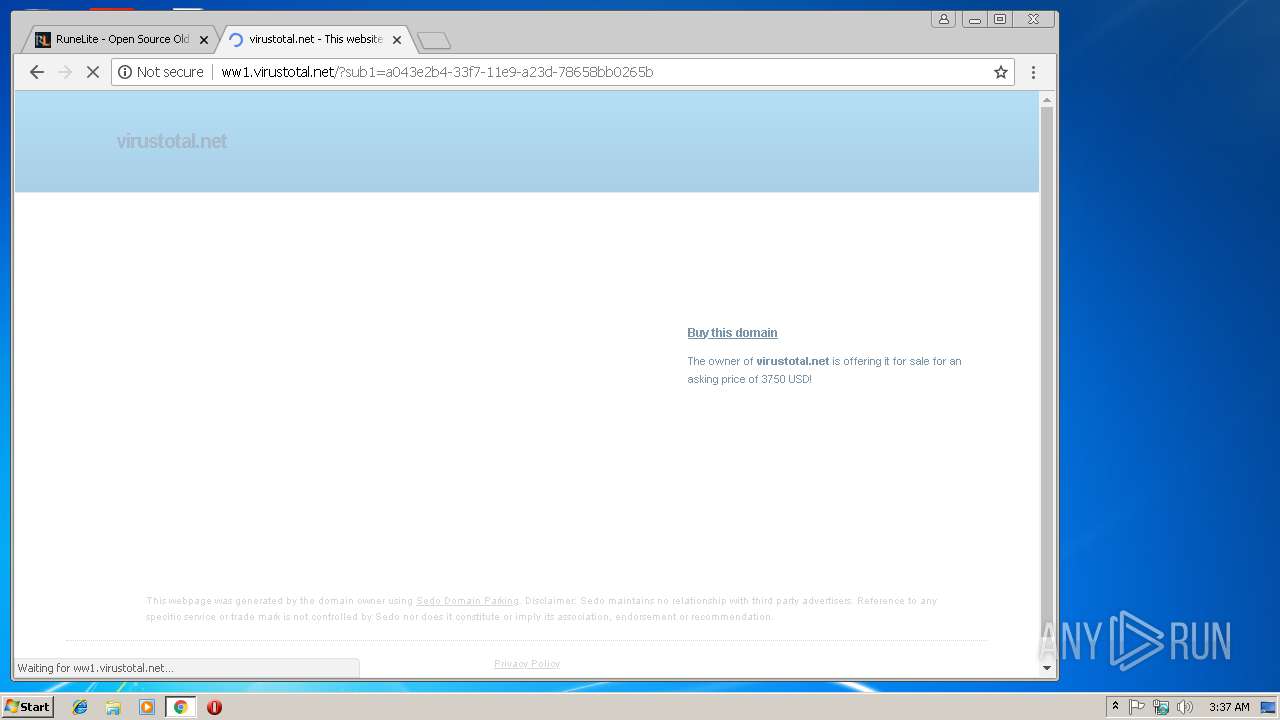
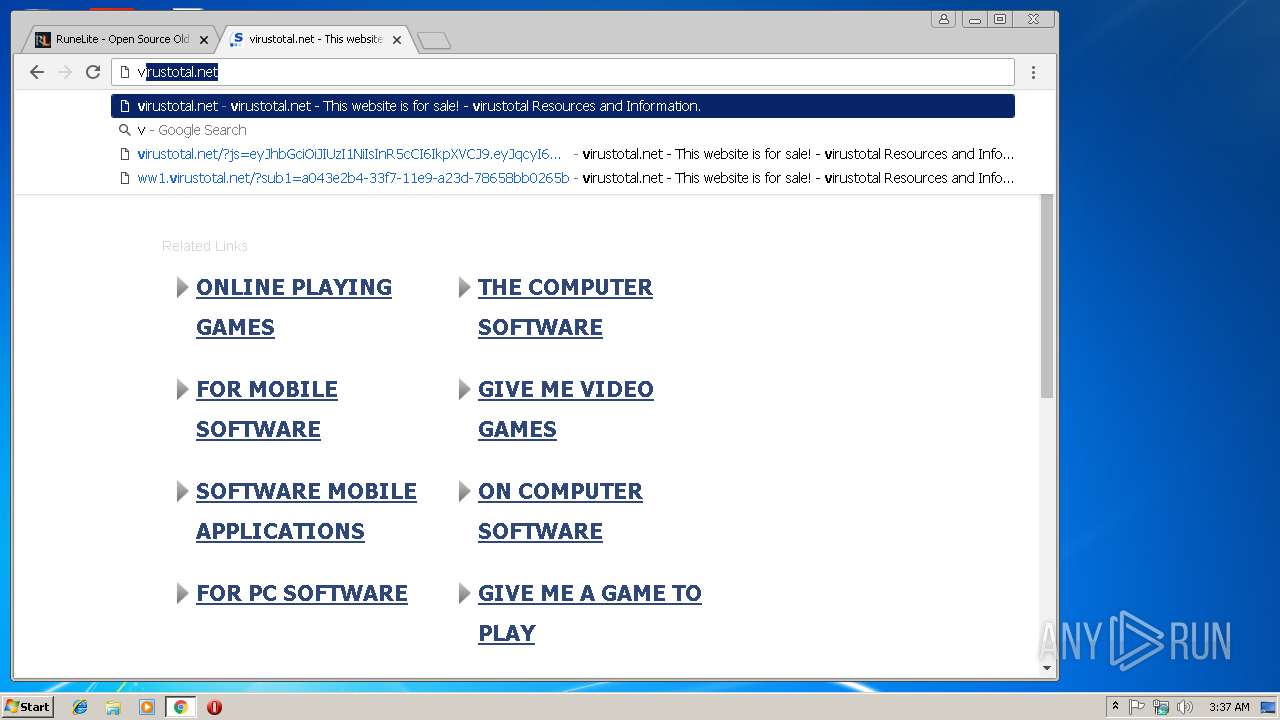
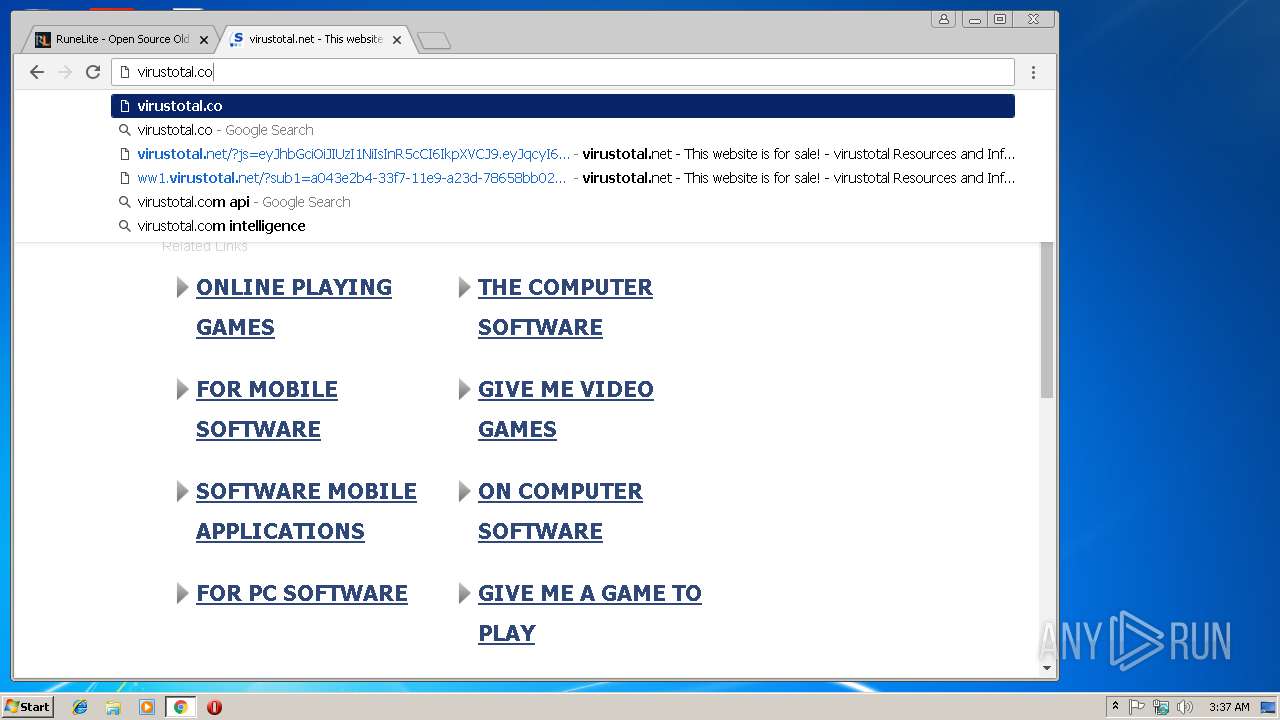
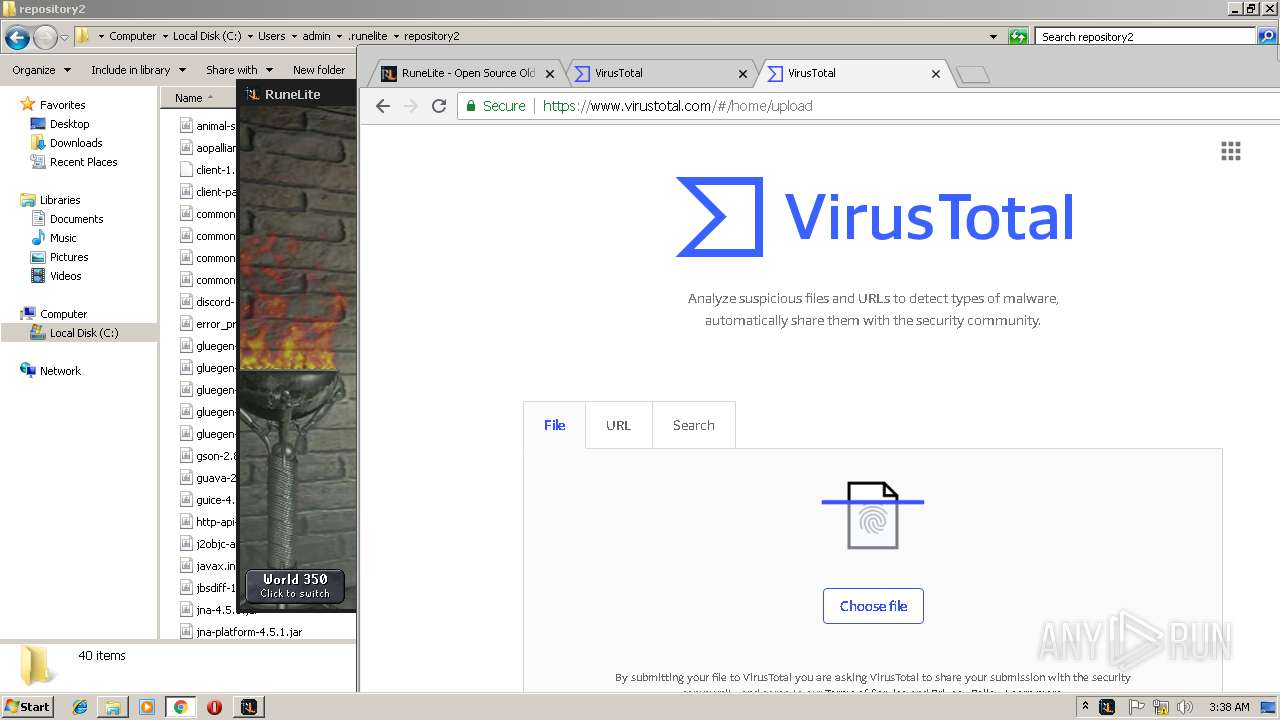
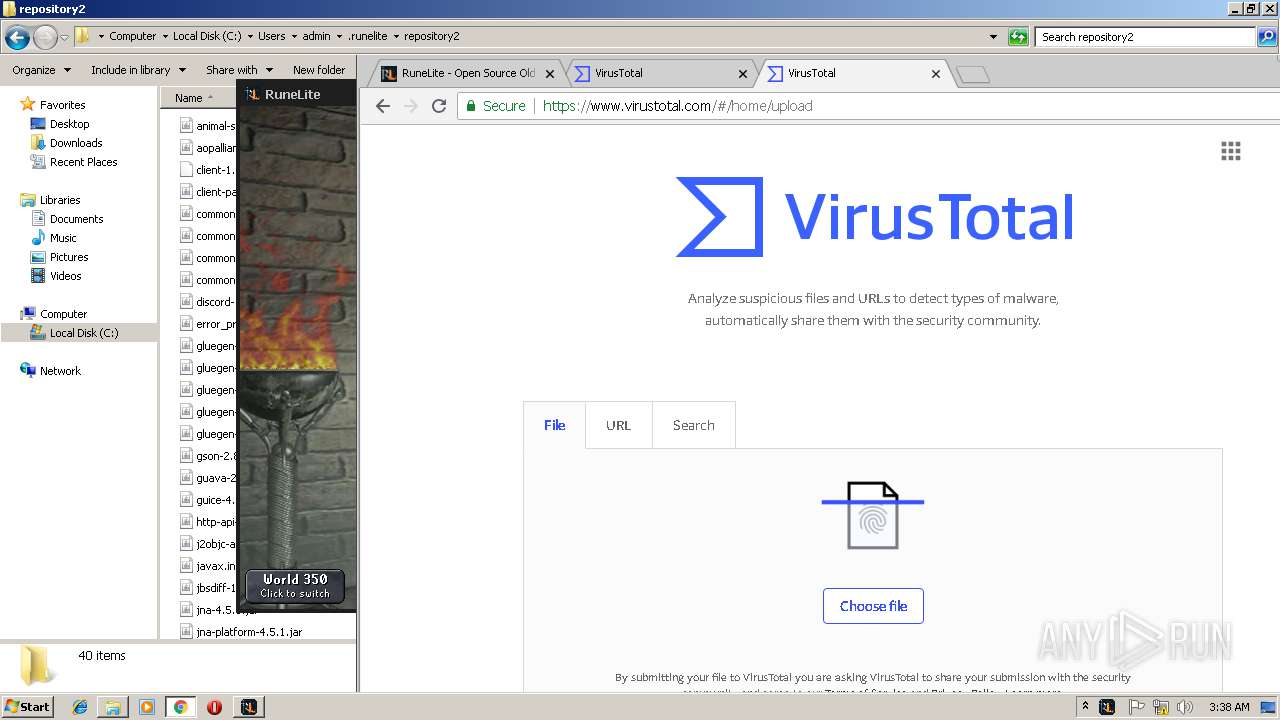
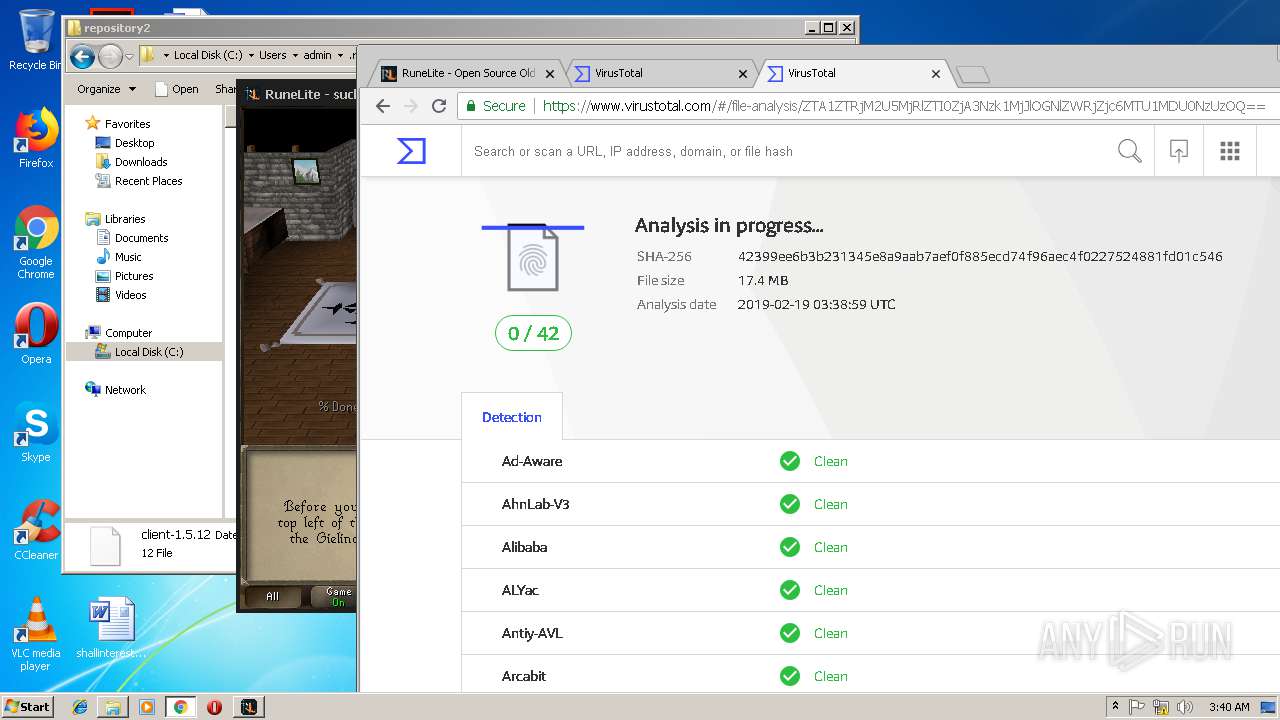
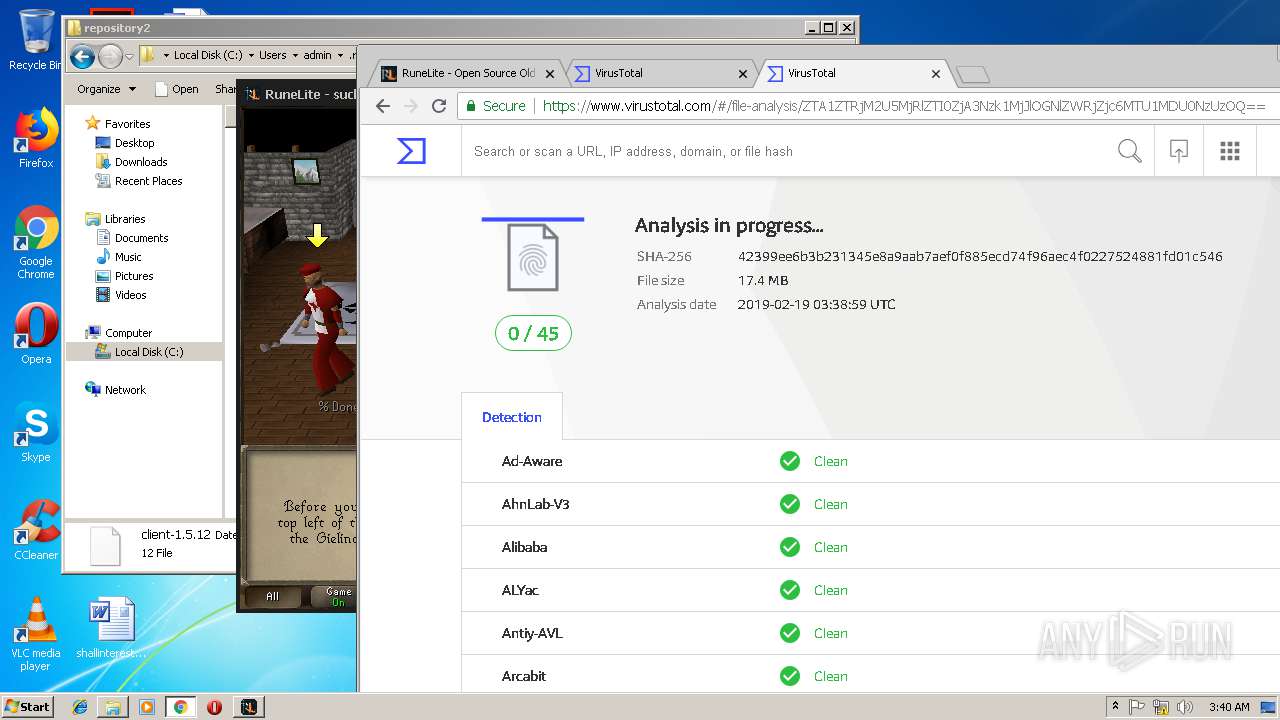
2312 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://ww1.virustotal.net/?sub1=a043e2b4-33f7-11e9-a23d-78658bb0265b | DE | html | 19.4 Kb | malicious |
2312 | chrome.exe | GET | 200 | 109.201.133.69:80 | http://virustotal.net/ | NL | html | 292 b | malicious |
2312 | chrome.exe | GET | 302 | 216.239.34.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
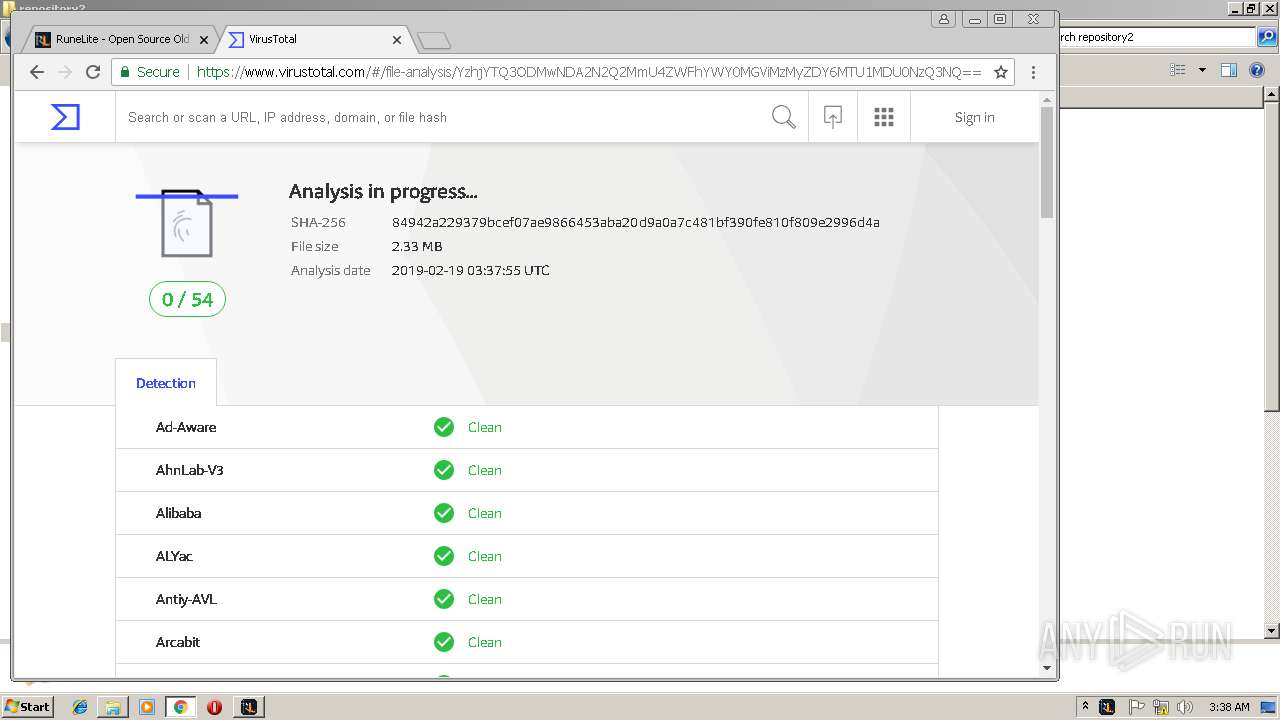
2596 | javaw.exe | GET | 200 | 104.31.209.10:80 | http://runelite.site/launcher/bootstrap.json | US | text | 16.5 Kb | suspicious |
2312 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://ww1.virustotal.net/search/tsc.php?200=MzAxMzMzNjQy&21=NzguMTEwLjE2Mi4yNDU=&681=MTU1MDU0NzQyNTQ2MTFjNDg5N2FhYmM3ZTU5ZjVmM2JkYmZhY2MzYzRj&crc=729d3b19432fb8f4dbb174bb53f4c182d4c68382&cv=1 | DE | compressed | 19.4 Kb | malicious |
2312 | chrome.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/js/jquery-1.11.3.custom.min.js | US | text | 24.5 Kb | whitelisted |
2960 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2312 | chrome.exe | GET | 200 | 172.217.18.113:80 | http://survey.g.doubleclick.net/async_survey?site=kv4ic6olrzkr6 | US | text | 17.6 Kb | whitelisted |
2312 | chrome.exe | GET | 200 | 172.217.22.67:80 | http://www.gstatic.com/domainads/tracking/caf.gif?ts=1550547425782&rid=4155016 | US | image | 43 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2312 | chrome.exe | 172.217.16.131:443 | www.google.de | Google Inc. | US | whitelisted |
2312 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2312 | chrome.exe | 104.28.27.223:80 | runelite.ca | Cloudflare Inc | US | shared |
2312 | chrome.exe | 172.217.22.35:443 | www.google.co.uk | Google Inc. | US | whitelisted |
2312 | chrome.exe | 104.28.27.223:443 | runelite.ca | Cloudflare Inc | US | shared |
2312 | chrome.exe | 151.101.2.109:443 | cdn.polyfill.io | Fastly | US | suspicious |
2312 | chrome.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
runeltie.ca |
| unknown |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2596 | javaw.exe | Potentially Bad Traffic | ET INFO Java File Sent With X-Powered By HTTP Header - Common In Exploit Kits |