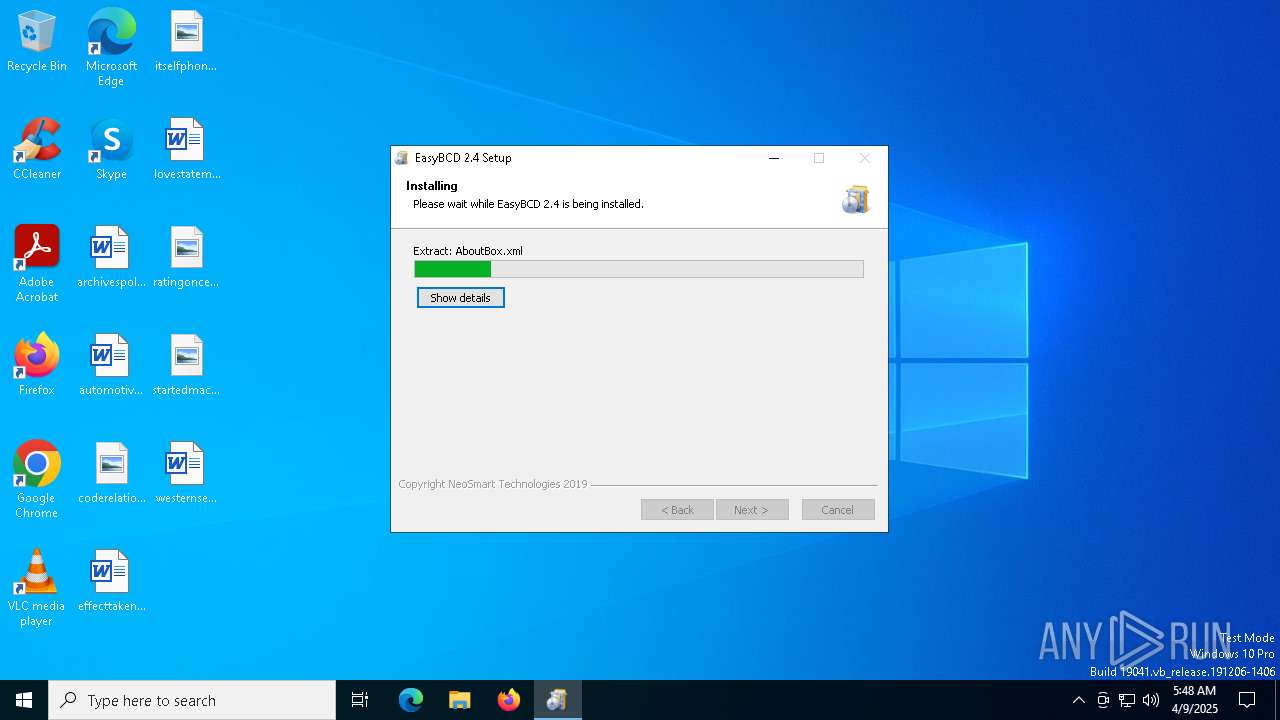
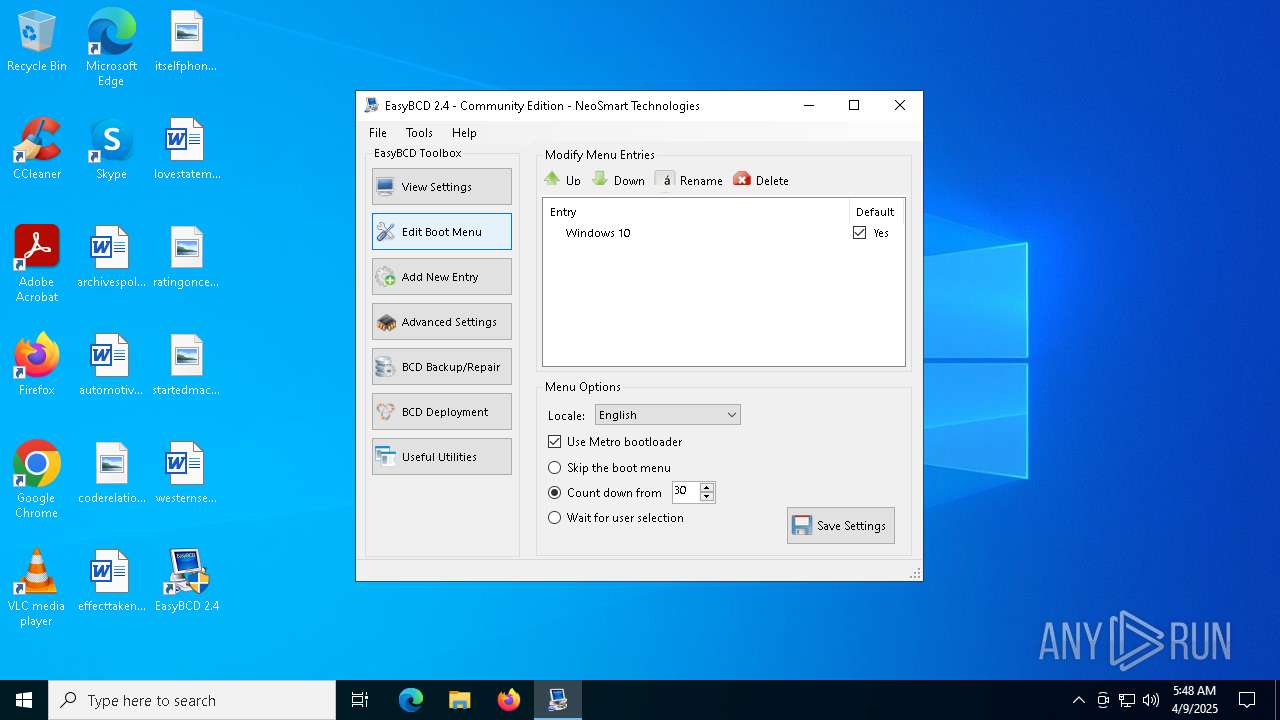
| File name: | EasyBCD 2.4.exe |
| Full analysis: | https://app.any.run/tasks/bd0360ff-ddaf-4263-932b-60ca4de11212 |
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2025, 05:48:08 |
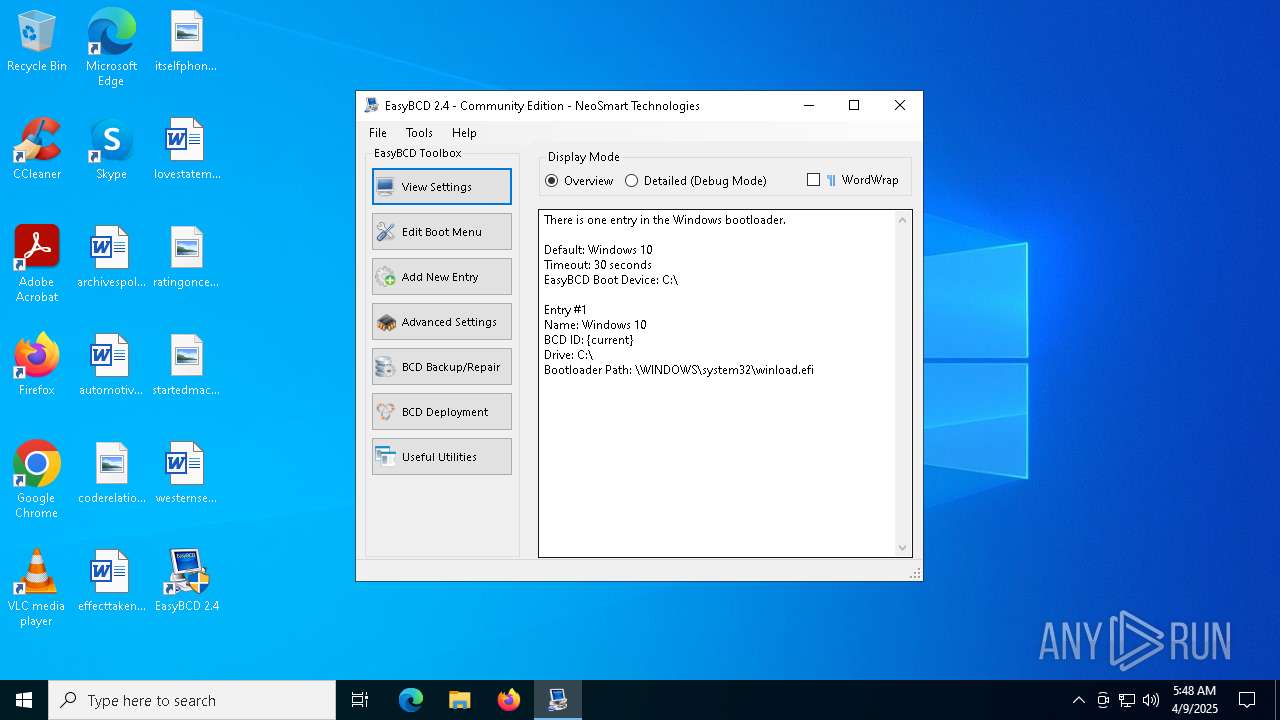
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 2E06476EBE1137F543EE7176D34716E7 |
| SHA1: | 6EAA6AA0E829CE8AF54213F6DE77E748C4388E23 |
| SHA256: | 0A94A43AF2DB7BDBADA87B34BF03D3B221110D1CA21BBEBEC55B08767C1281CC |
| SSDEEP: | 98304:ilHlURur2ooGWFdzLmi9pimQ43ZIbI7KjDgXC5b7V6n0pWzvx4X1aex55V9WSdzu:hBma |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- EasyBCD 2.4.exe (PID: 6068)
The process creates files with name similar to system file names
- EasyBCD 2.4.exe (PID: 6068)
Uses TASKKILL.EXE to kill process
- EasyBCD 2.4.exe (PID: 6068)
Process drops legitimate windows executable
- EasyBCD 2.4.exe (PID: 6068)
Reads security settings of Internet Explorer
- EasyBCD 2.4.exe (PID: 6068)
- EasyBCD.exe (PID: 3096)
Executable content was dropped or overwritten
- EasyBCD 2.4.exe (PID: 6068)
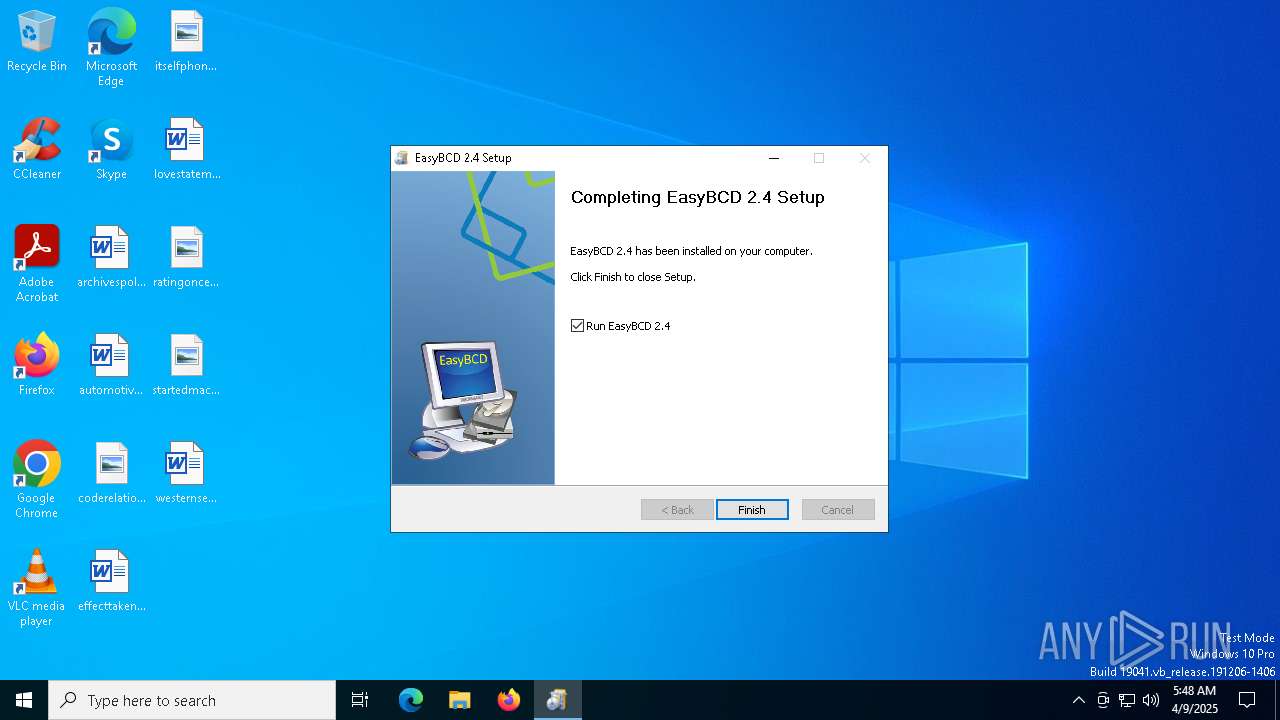
Creates a software uninstall entry
- EasyBCD 2.4.exe (PID: 6068)
There is functionality for taking screenshot (YARA)
- EasyBCD 2.4.exe (PID: 6068)
Reads Internet Explorer settings
- EasyBCD.exe (PID: 3096)
Reads the date of Windows installation
- EasyBCD.exe (PID: 3096)
INFO
Create files in a temporary directory
- EasyBCD 2.4.exe (PID: 6068)
- EasyBCD.exe (PID: 3096)
- msfeedssync.exe (PID: 2432)
- msfeedssync.exe (PID: 5344)
Checks supported languages
- EasyBCD 2.4.exe (PID: 6068)
- EasyBCD.exe (PID: 3096)
- BootGrabber.exe (PID: 1912)
- UtfRedirect.exe (PID: 5064)
- UtfRedirect.exe (PID: 1628)
- bcdedit.exe (PID: 6816)
- bcdedit.exe (PID: 536)
Reads the computer name
- EasyBCD 2.4.exe (PID: 6068)
- EasyBCD.exe (PID: 3096)
Creates files in the program directory
- EasyBCD 2.4.exe (PID: 6068)
Process checks computer location settings
- EasyBCD 2.4.exe (PID: 6068)
- EasyBCD.exe (PID: 3096)
The sample compiled with english language support
- EasyBCD 2.4.exe (PID: 6068)
Reads the machine GUID from the registry
- EasyBCD.exe (PID: 3096)
Creates files or folders in the user directory
- EasyBCD.exe (PID: 3096)
Reads Environment values
- EasyBCD.exe (PID: 3096)
Process checks whether UAC notifications are on
- EasyBCD.exe (PID: 3096)
Disables trace logs
- EasyBCD.exe (PID: 3096)
Checks proxy server information
- EasyBCD.exe (PID: 3096)
- msfeedssync.exe (PID: 2432)
Reads the software policy settings
- EasyBCD.exe (PID: 3096)
Reads security settings of Internet Explorer
- msfeedssync.exe (PID: 5344)
- msfeedssync.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
147
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | BootGrabber.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\bcdedit.exe" /export "C:\Users\admin\Documents\EasyBCD Backup (2025-04-09).bcd" | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\bcdedit.exe | — | UtfRedirect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.2.8250.0 (winmain_win8beta.120217-1520) Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UtfRedirect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UtfRedirect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
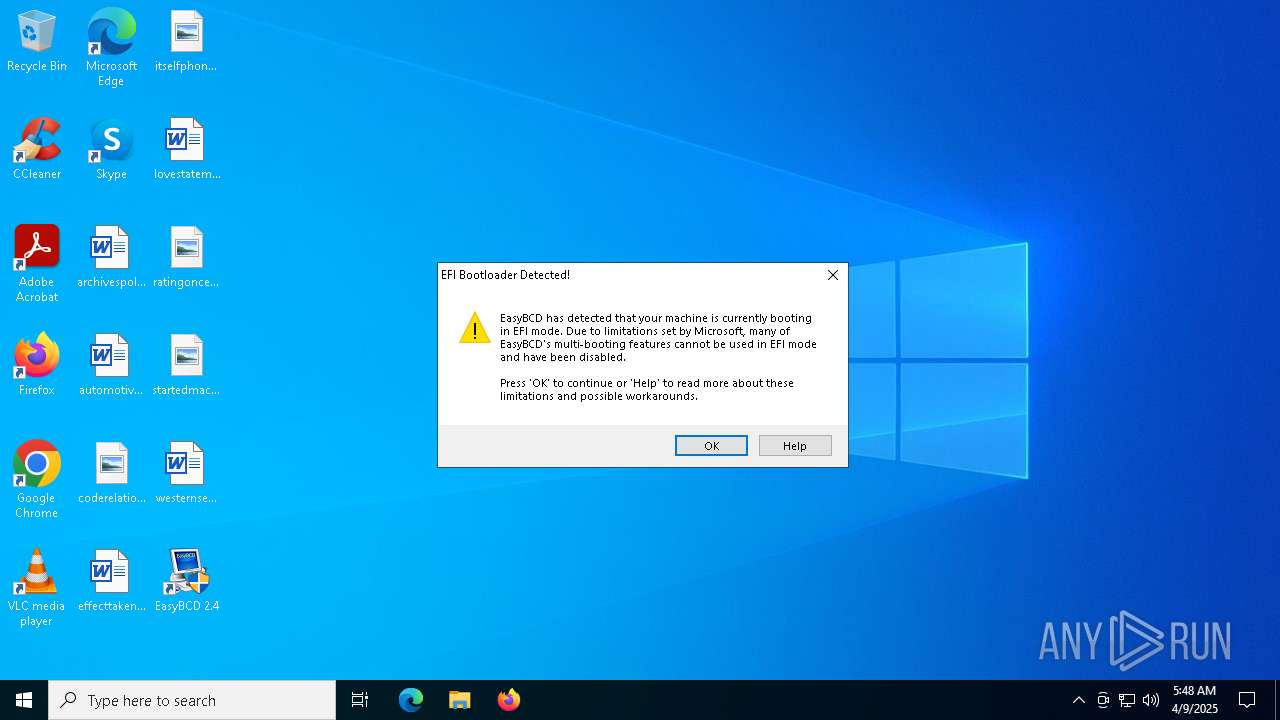
| 1628 | "C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\UtfRedirect.exe" | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\UtfRedirect.exe | — | EasyBCD.exe | |||||||||||
User: admin Company: NeoSmart Technologies Integrity Level: HIGH Description: UTF8 codepage proxy application Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1912 | "C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\bootgrabber.exe" /tlist | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\BootGrabber.exe | — | EasyBCD.exe | |||||||||||
User: admin Company: NeoSmart Technologies Integrity Level: HIGH Description: EasyBCD boot helper Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\EasyBCD 2.4.exe" | C:\Users\admin\AppData\Local\Temp\EasyBCD 2.4.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2432 | "C:\Windows\System32\msfeedssync.exe" forcesync | C:\Windows\System32\msfeedssync.exe | EasyBCD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Feeds Synchronization Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
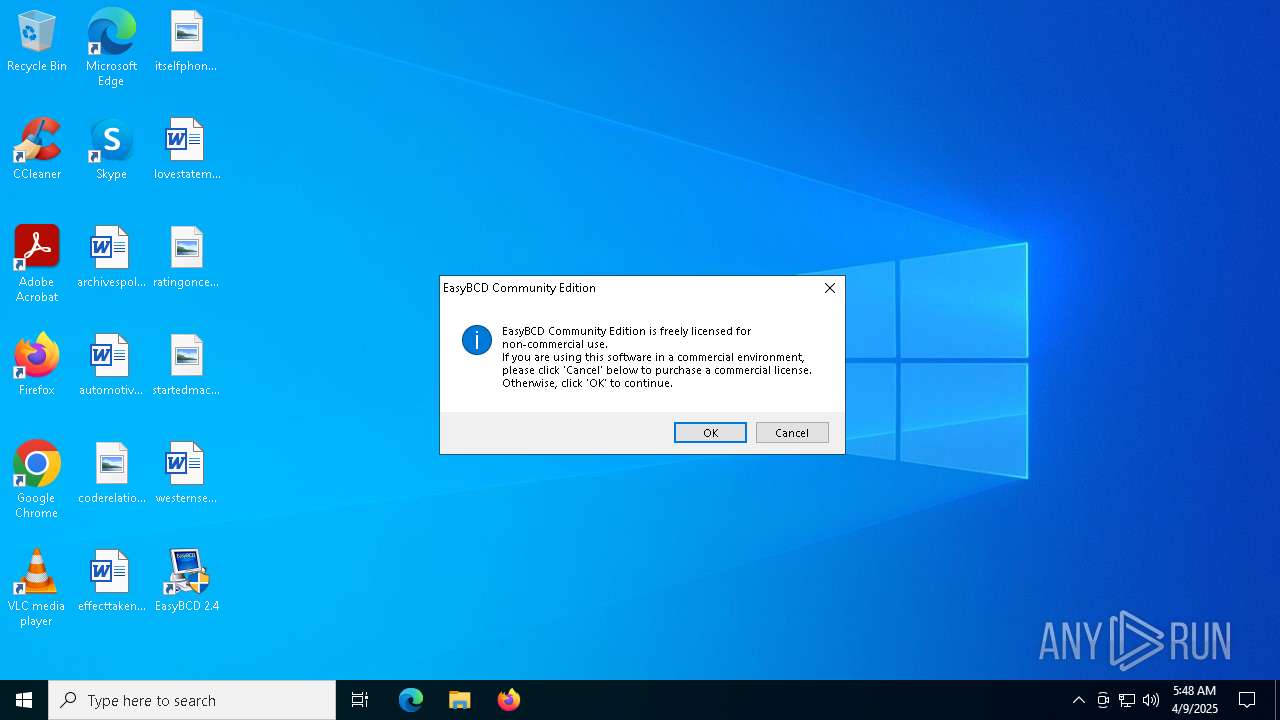
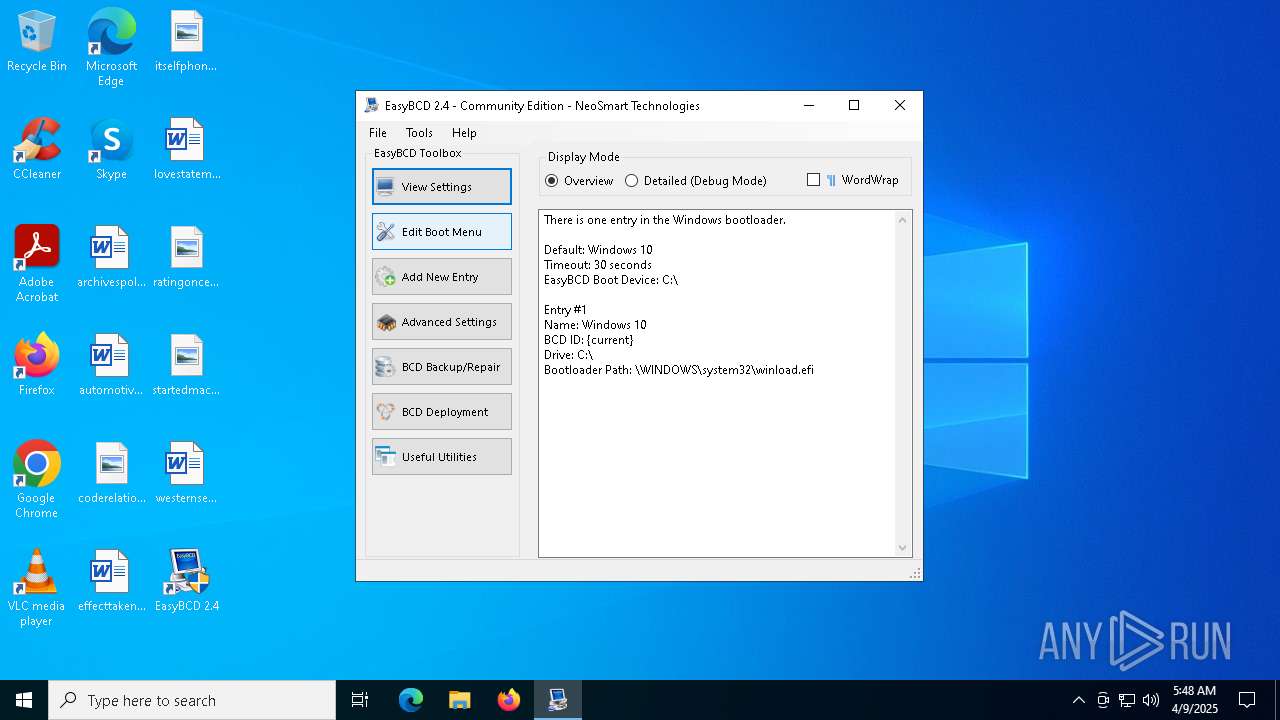
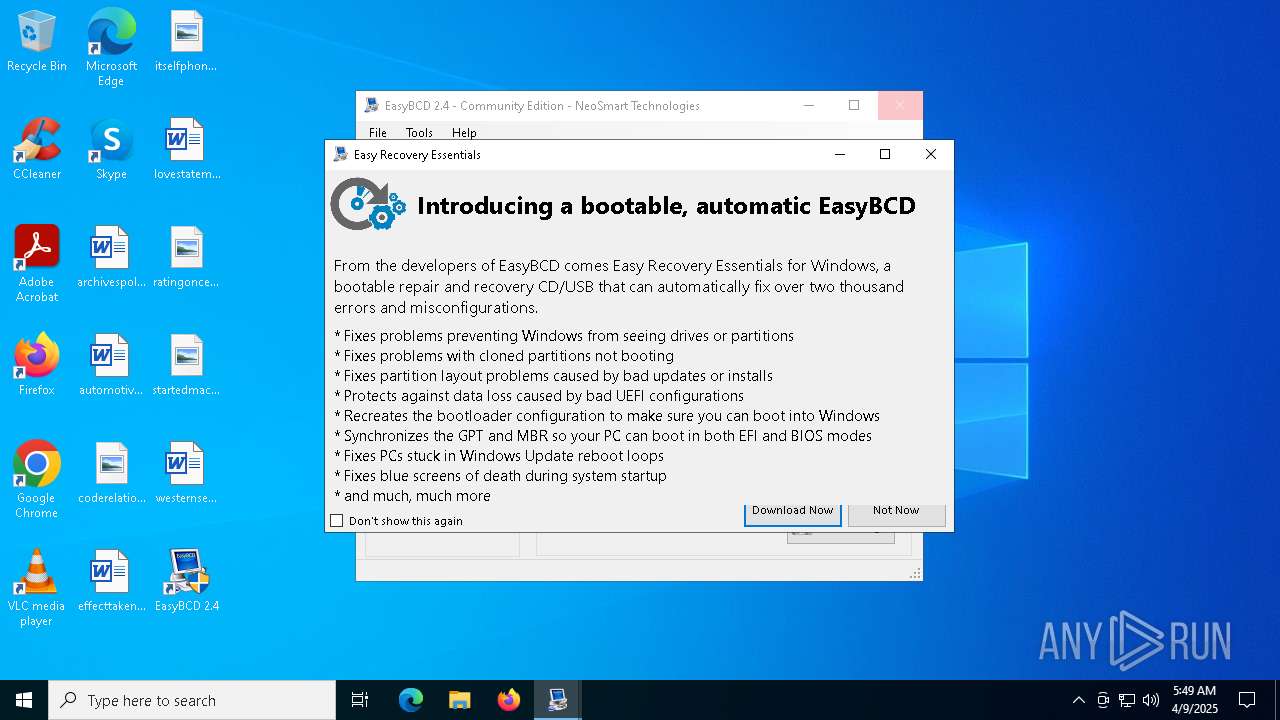
| 3096 | "C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\EasyBCD.exe" | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\EasyBCD.exe | EasyBCD 2.4.exe | ||||||||||||
User: admin Company: NeoSmart Technologies Integrity Level: HIGH Description: EasyBCD Exit code: 0 Version: 2.4.0.237 Modules
| |||||||||||||||
| 3300 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 651
Read events
6 355
Write events
267
Delete events
29
Modification events
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | DisplayName |
Value: EasyBCD 2.4 | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\uninstall.exe | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\EasyBCD.exe | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | HelpLink |
Value: http://neosmart.net/forums/ | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | URLUpdateInfo |
Value: http://neosmart.net/EasyBCD/ | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | VersionMajor |
Value: 2 | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | VersionMinor |
Value: 4 | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (6068) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | DisplayVersion |
Value: 2.4 | |||
Executable files
18
Suspicious files
51
Text files
310
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\udefrag.exe | executable | |
MD5:B28589BDE044417287D73EAC95142958 | SHA256:0863BE7C3A6D3FF526E2C333F605E6FC4ED96BF71DD8FD8F8B81489F721FFC52 | |||
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\NST Downloader.exe | executable | |
MD5:A5B3EA9EE11E9752417159BA1C618B95 | SHA256:B92B2FA8916C78CCFFEF058D3BE900C840CB996028D373BA55985FD1D1DDDAC8 | |||
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\BootGrabber.exe | executable | |
MD5:2E12B37D32C8BCF8920F5EBB6D24A6B9 | SHA256:F9842333F0B562B4AB5349A09FC173B0B2971C1F600502C4284781C78A735D7E | |||
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\bcdedit.exe | executable | |
MD5:A60CBAEA0F8AC802D21C0CC7BC2589BE | SHA256:8BF1B71182FED18D6B4112BDC4D496800B5BF6681DE4C4F6536BA67378F38A12 | |||
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\Newtonsoft.Json.dll | executable | |
MD5:0953851089821550EF013B487DA3915A | SHA256:4A56EF352F84AD19C1B4486C7C9E64FEF9A67C464C62E51BABABA79CD2D89551 | |||
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\bootsect.exe | executable | |
MD5:DA39BBA4267EC54DE12374BFD88D0DF4 | SHA256:F15E3C9A8F73C6DC4EA8F0A174915B6EDCA06C75332EEC8A28E7A4B347276D4D | |||
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\bcdboot.exe | executable | |
MD5:9F9E397630A146E875735F2F42339E6B | SHA256:9898F537B8D3097A05B42F42523CD66FCA7C020E8083EDBE461E6D9A12DD168E | |||
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\UtfRedirect.exe | executable | |
MD5:5B40791899FA37507E7C08BC3D9F5294 | SHA256:5A87D9485F6E13EE2C3BA4AC289A3E237D17A43ED428B8A5BD5F00FC4800D1AC | |||
| 6068 | EasyBCD 2.4.exe | C:\Users\admin\AppData\Local\Temp\nstC0C3.tmp\modern-wizard.bmp | image | |
MD5:1ED71CEF099AE50505B5F495CC50E2A2 | SHA256:B177ADA6638B5869390C39405CAF5BEF6FA74AFAFE00BCD14DE5282867E47A26 | |||
| 6068 | EasyBCD 2.4.exe | C:\Program Files (x86)\NeoSmart Technologies\EasyBCD\bin\NetTest.exe | executable | |
MD5:3F3BE08145D962F3146F9632CA1EC910 | SHA256:C35B26223B07D81E9AB638B52E5344D33E10DF874457A7B1CFBDA6F591A07C7F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
24
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3096 | EasyBCD.exe | GET | 302 | 65.182.170.12:80 | http://feeds.neosmart.net/neosmart | unknown | — | — | whitelisted |
3096 | EasyBCD.exe | GET | 200 | 142.250.184.243:80 | http://rss.neosmart.net/neosmart | unknown | — | — | whitelisted |
2432 | msfeedssync.exe | GET | 200 | 142.250.184.243:80 | http://rss.neosmart.net/neosmart | unknown | — | — | whitelisted |
5404 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5404 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2432 | msfeedssync.exe | GET | 302 | 65.182.170.12:80 | http://feeds.neosmart.net/neosmart | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.neosmart.net |
| whitelisted |
feeds.neosmart.net |
| whitelisted |
rss.neosmart.net |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |