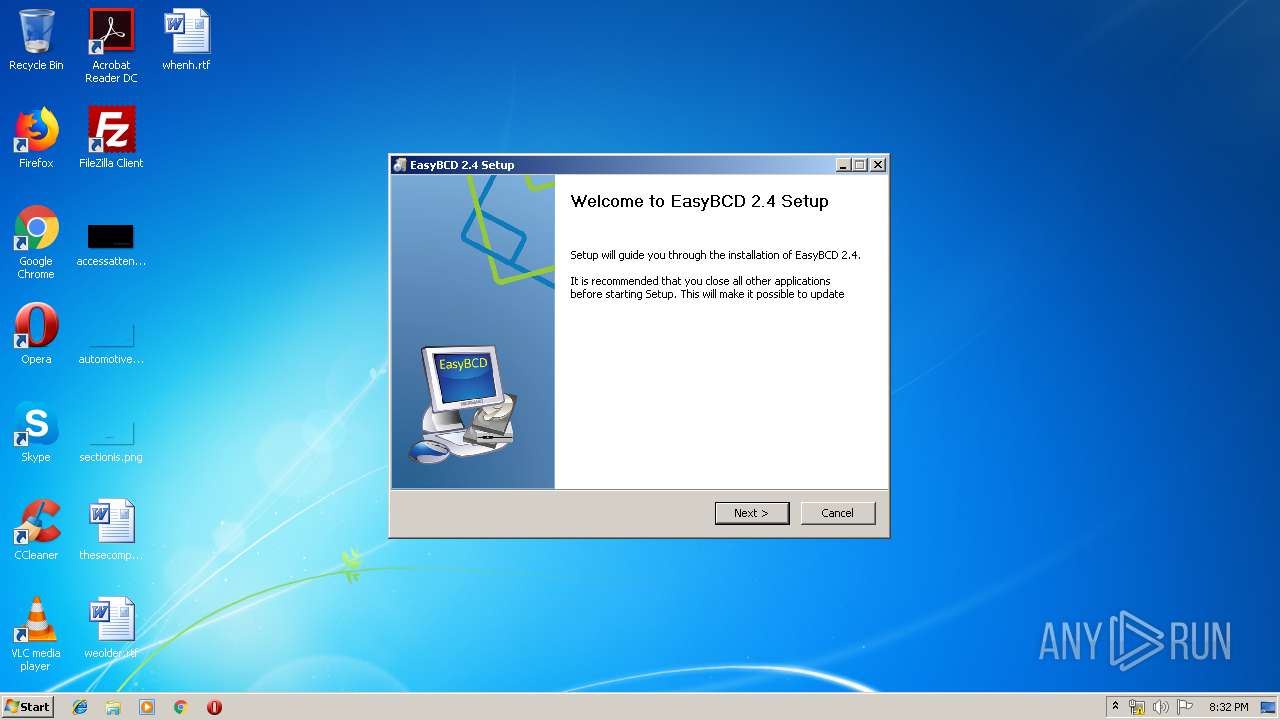
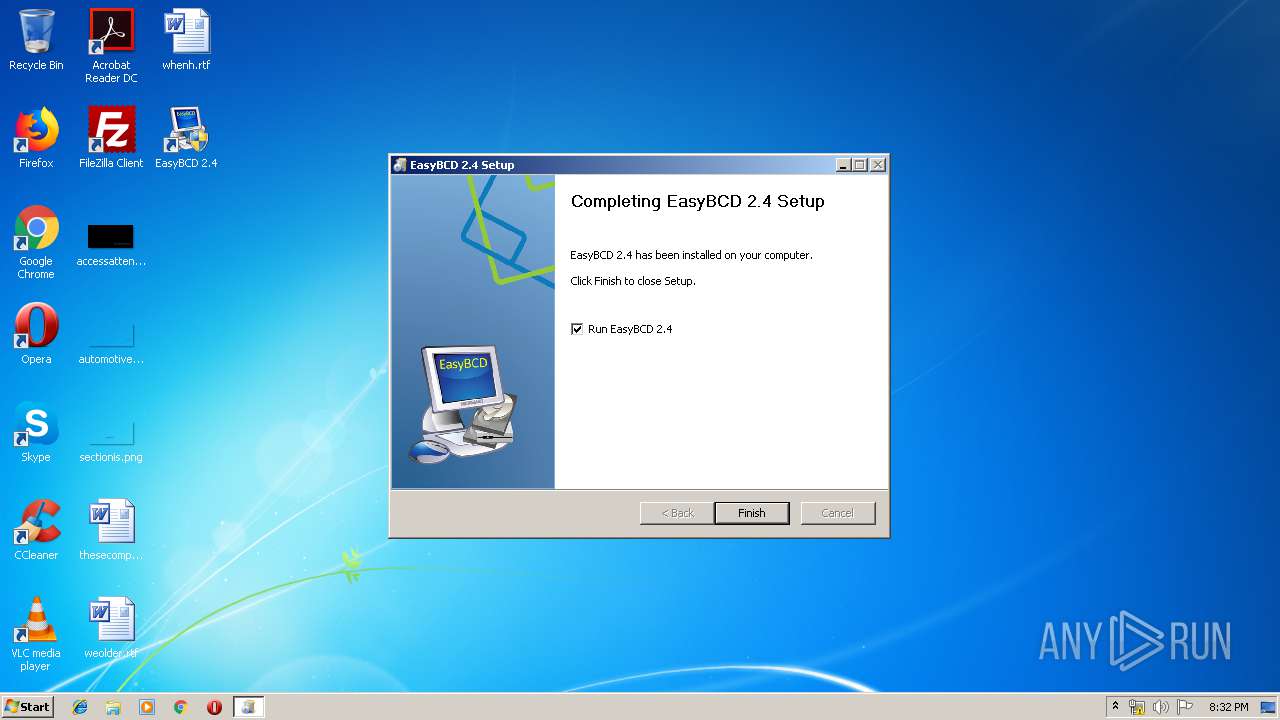
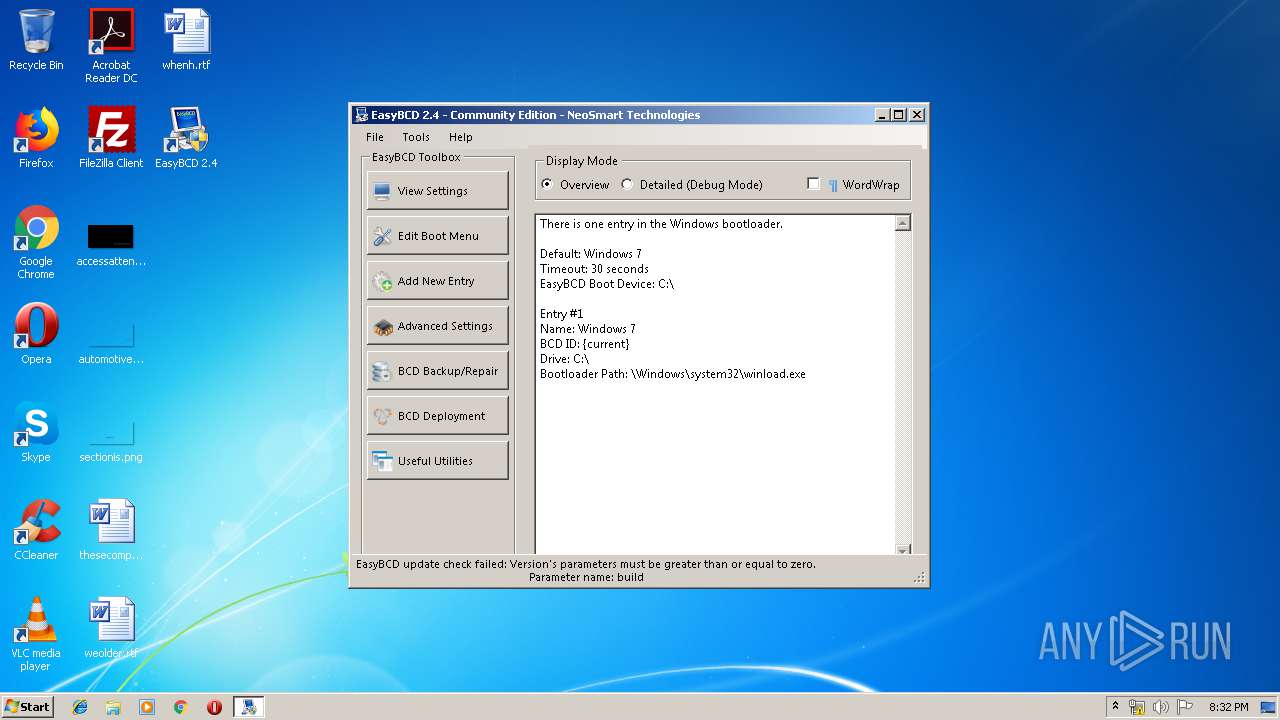
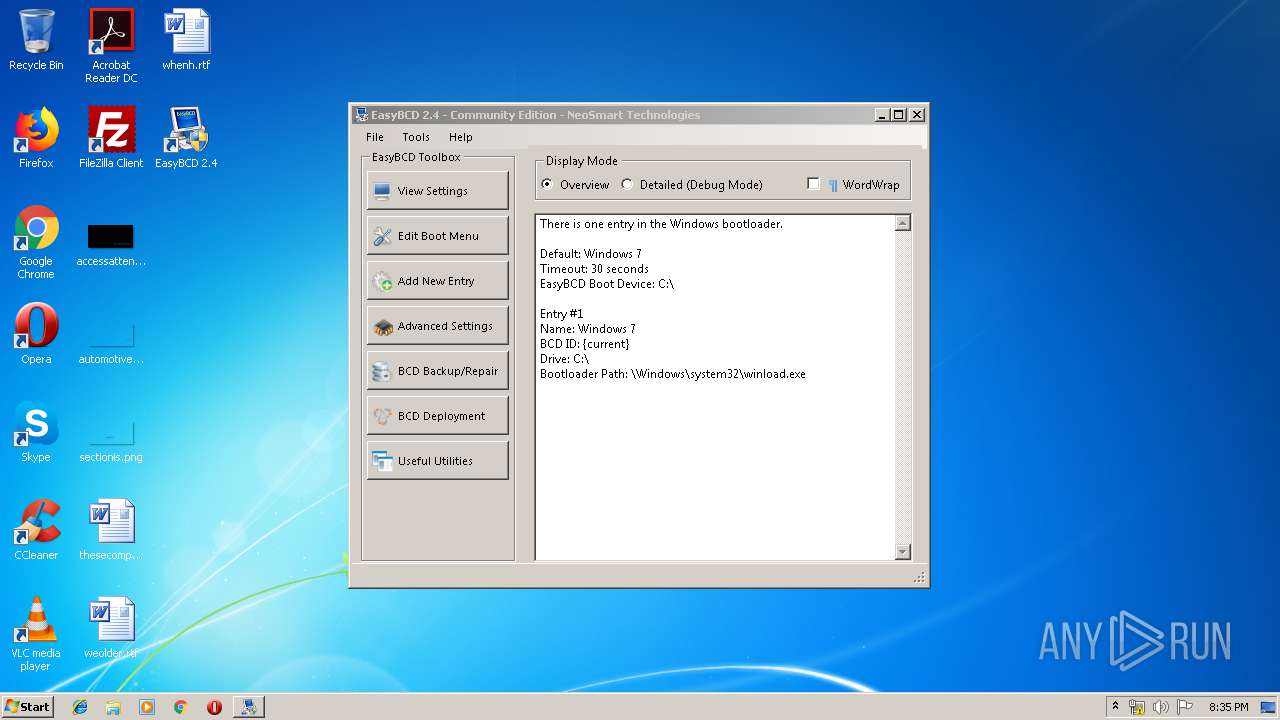
| File name: | EasyBCD 2.4.exe |
| Full analysis: | https://app.any.run/tasks/08e79204-d8fa-4535-8d20-0315302ab2ab |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2019, 19:32:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 2E06476EBE1137F543EE7176D34716E7 |
| SHA1: | 6EAA6AA0E829CE8AF54213F6DE77E748C4388E23 |
| SHA256: | 0A94A43AF2DB7BDBADA87B34BF03D3B221110D1CA21BBEBEC55B08767C1281CC |
| SSDEEP: | 49152:vHQLkhcj2sy/yOnZMS3NTQDxX7Cc8kRD7zei:vwLKcjW/yGMoN+Obk1zD |
MALICIOUS
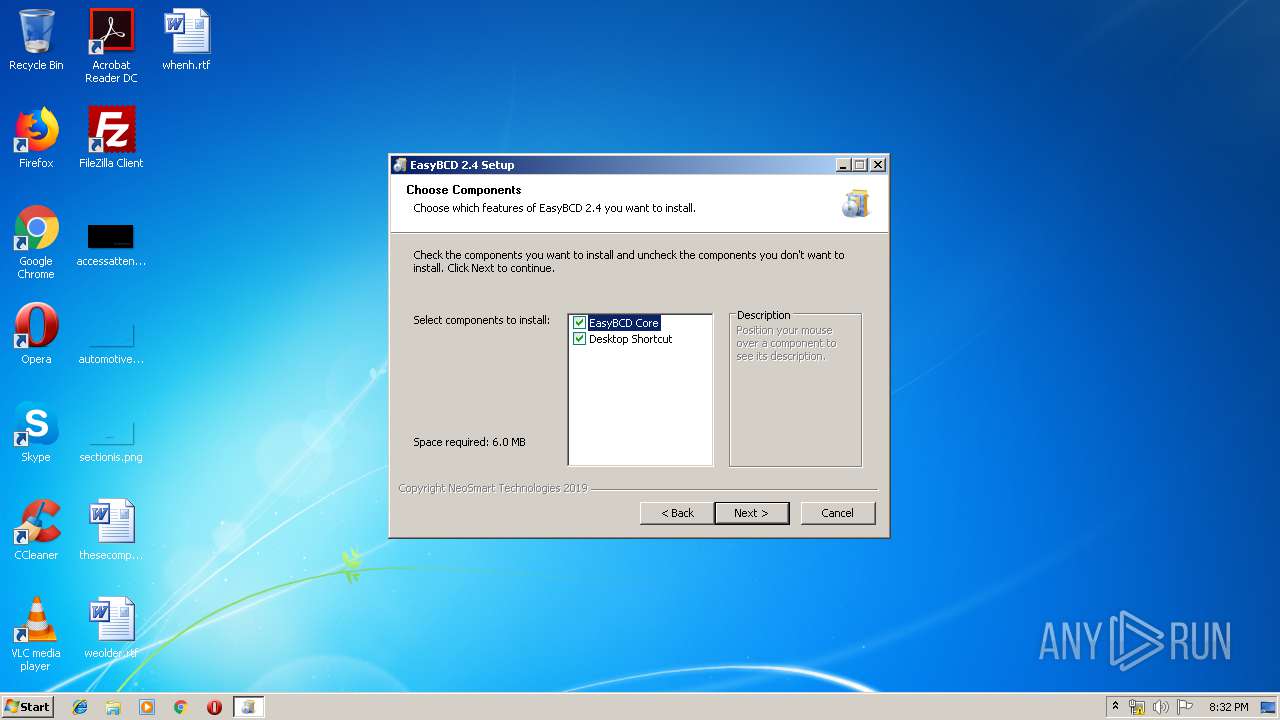
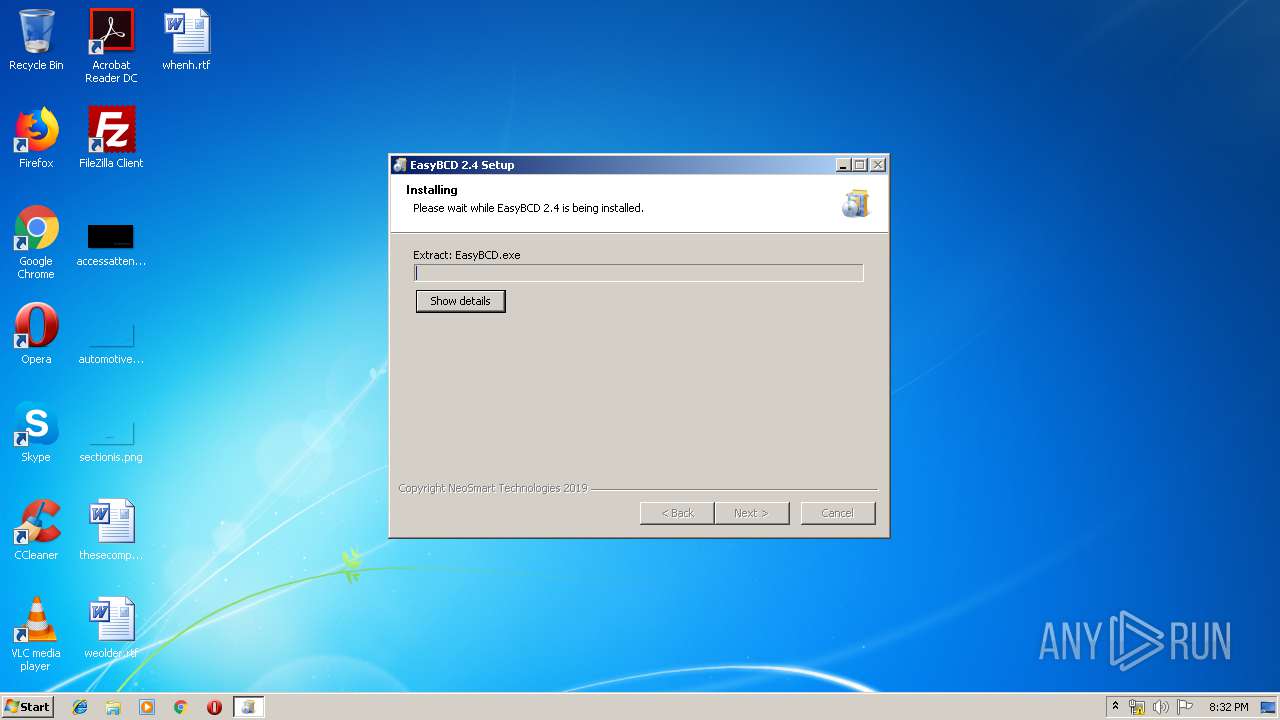
Loads dropped or rewritten executable
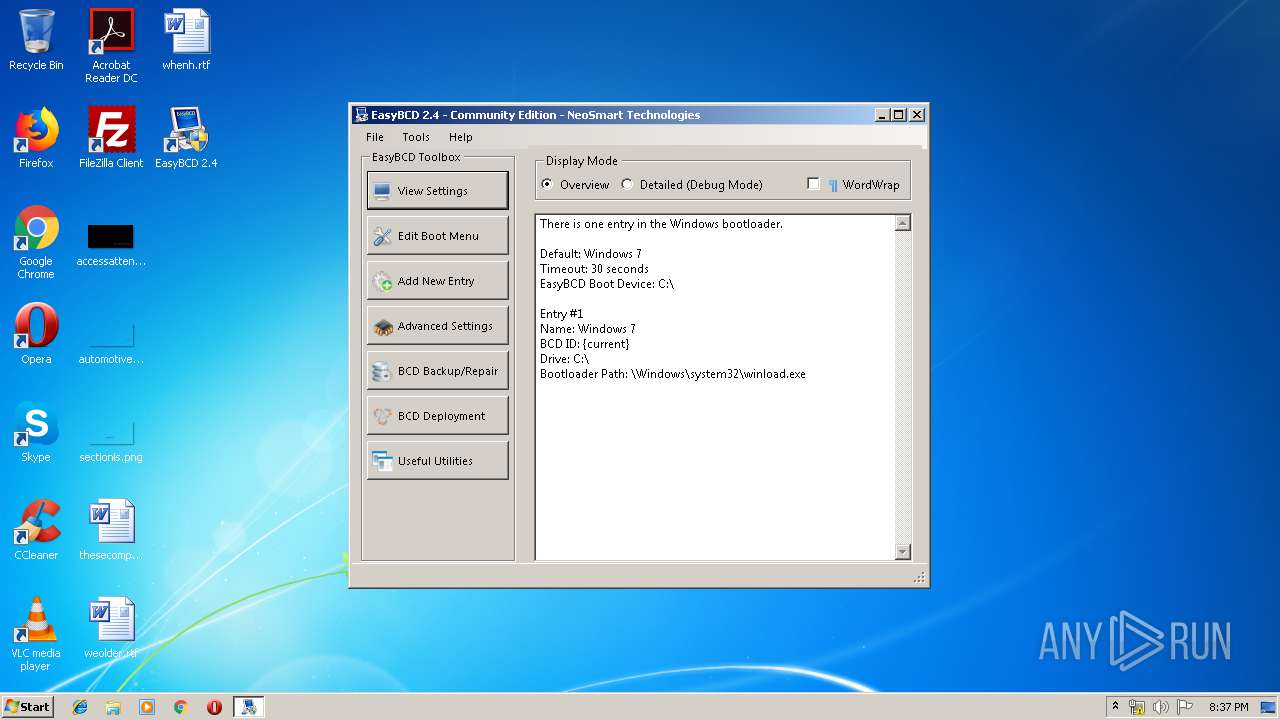
- EasyBCD 2.4.exe (PID: 668)
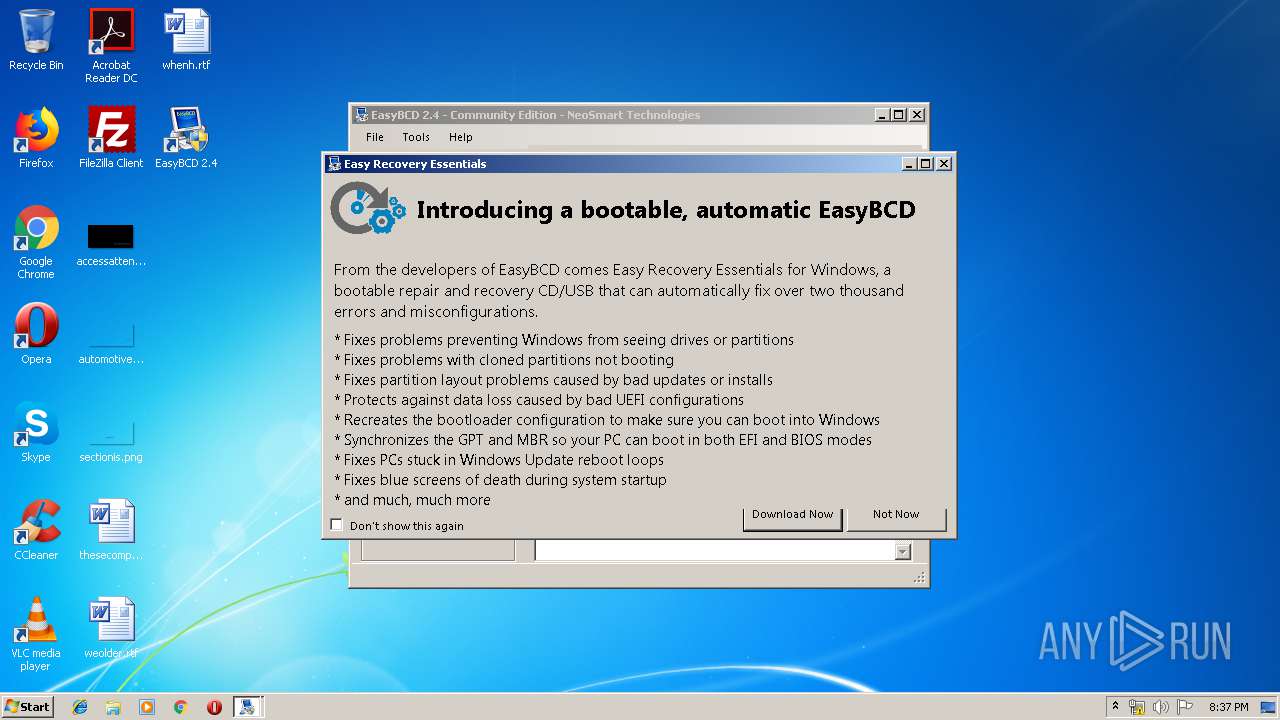
- EasyBCD.exe (PID: 3488)
Application was dropped or rewritten from another process
- EasyBCD.exe (PID: 3488)
- bootgrabber.exe (PID: 3632)
- UtfRedirect.exe (PID: 2084)
- UtfRedirect.exe (PID: 2360)
- bcdedit.exe (PID: 3772)
- bcdedit.exe (PID: 2684)
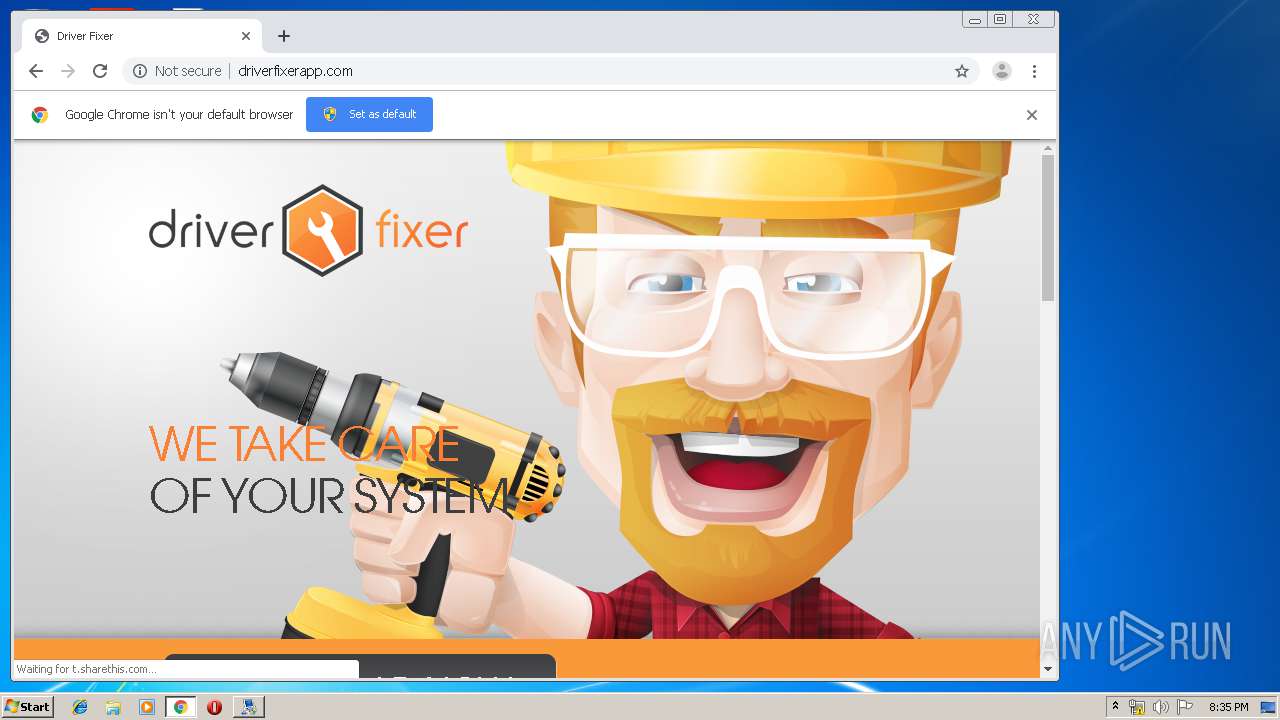
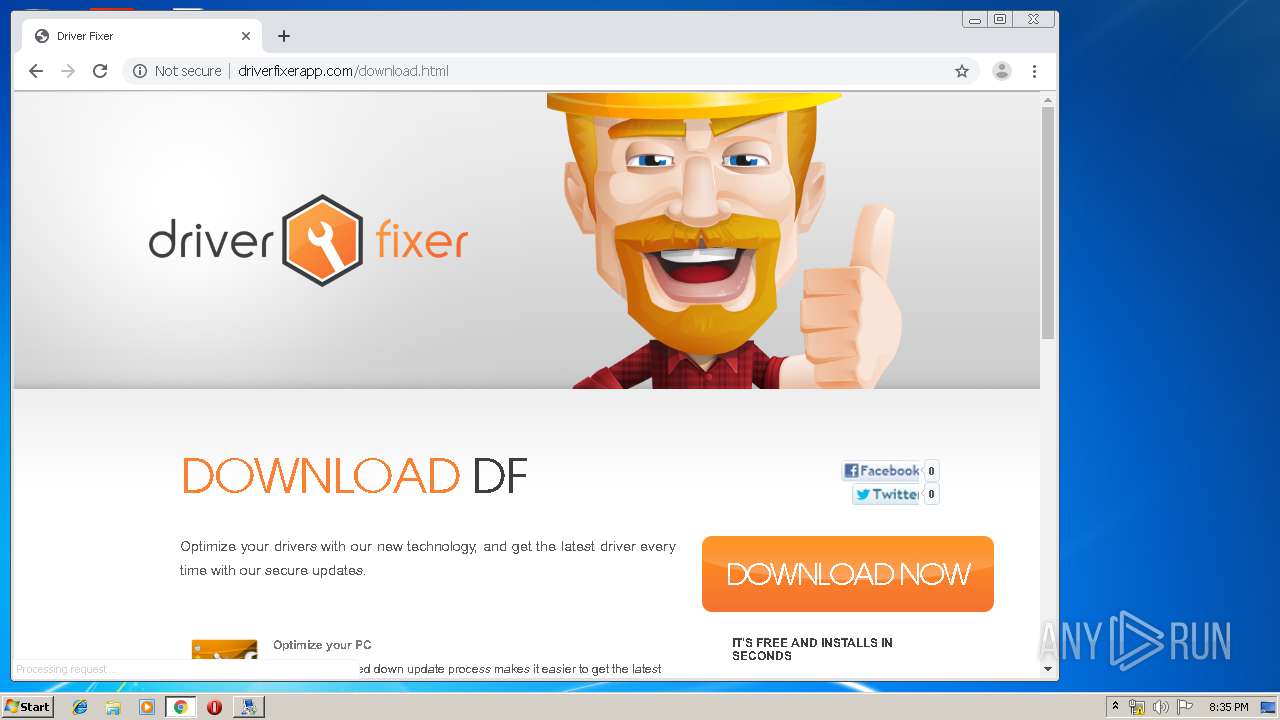
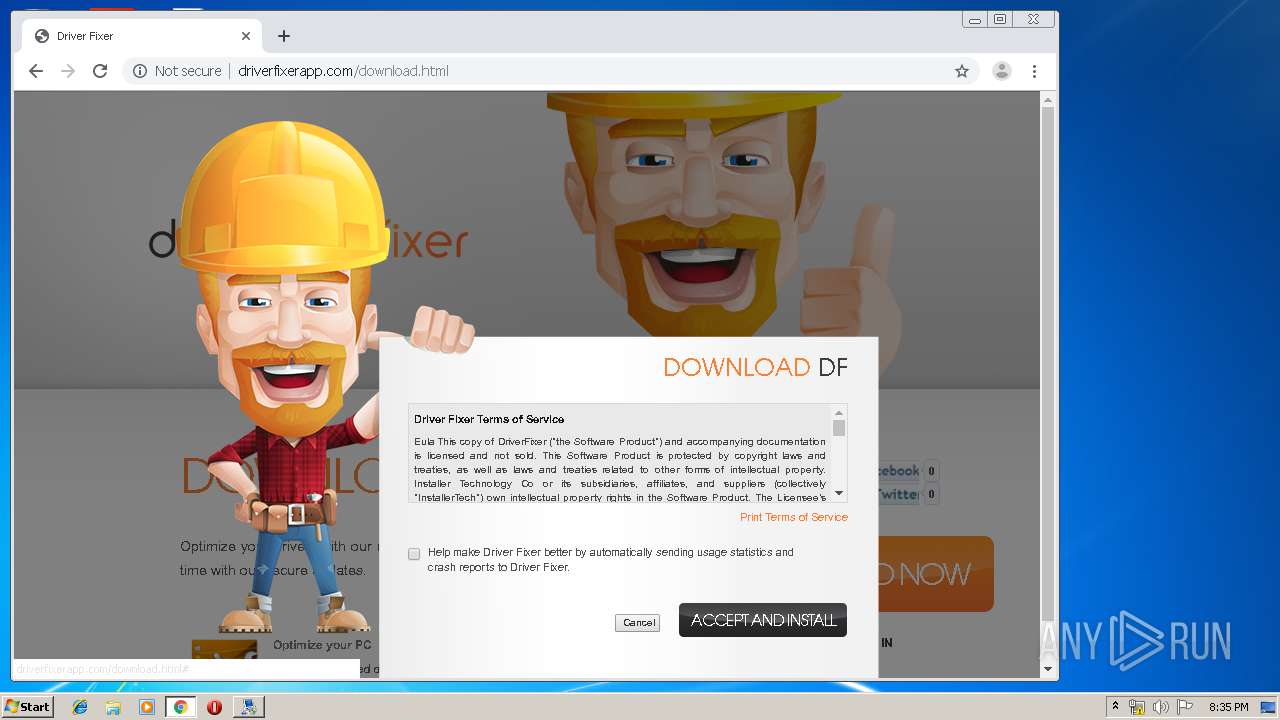
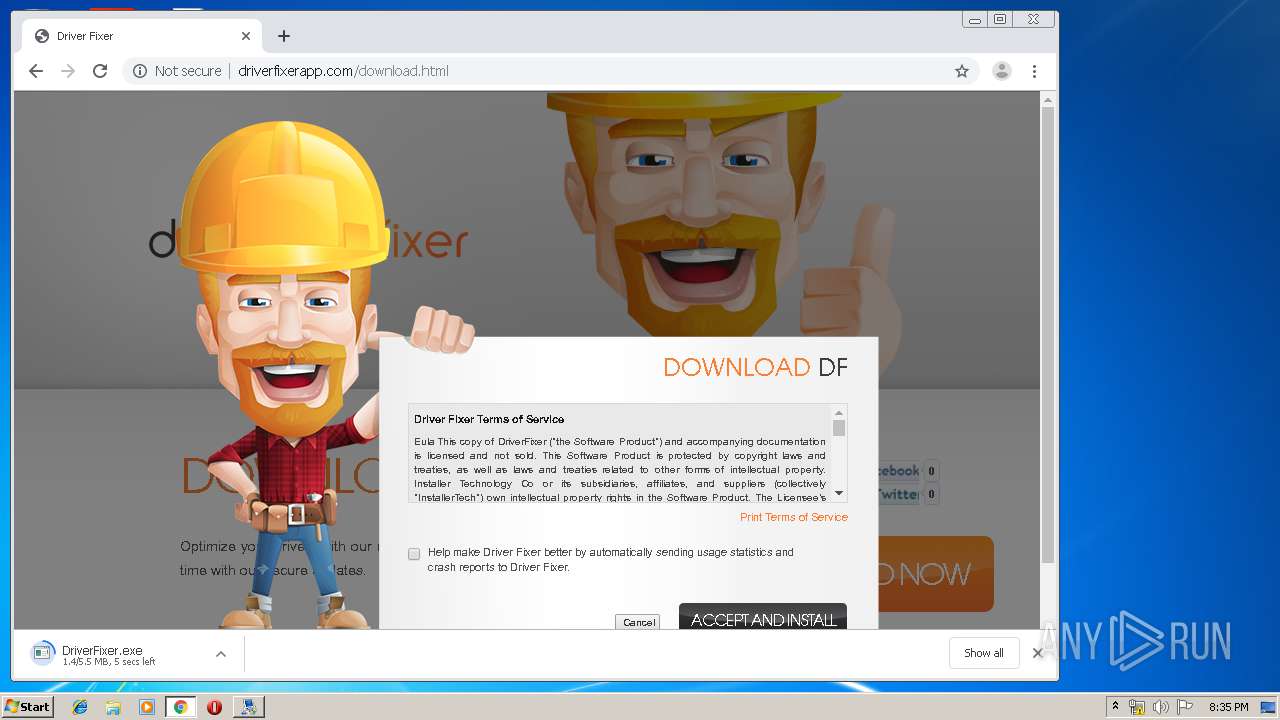
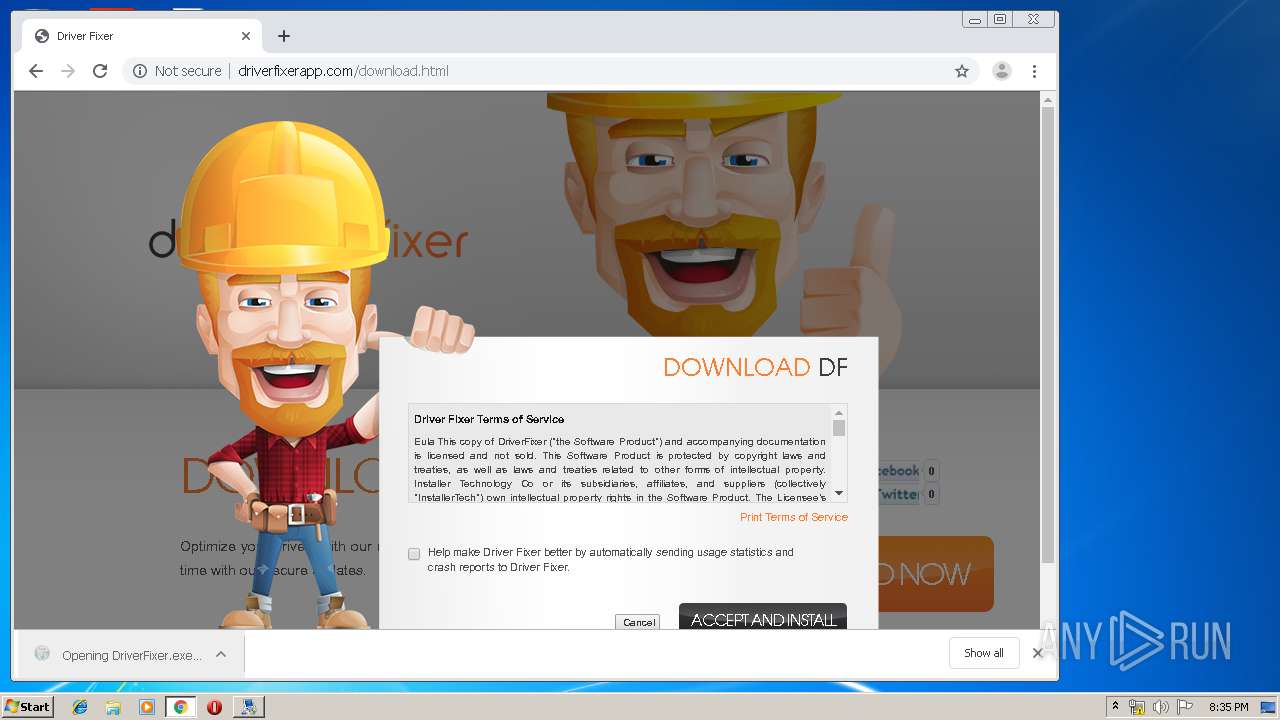
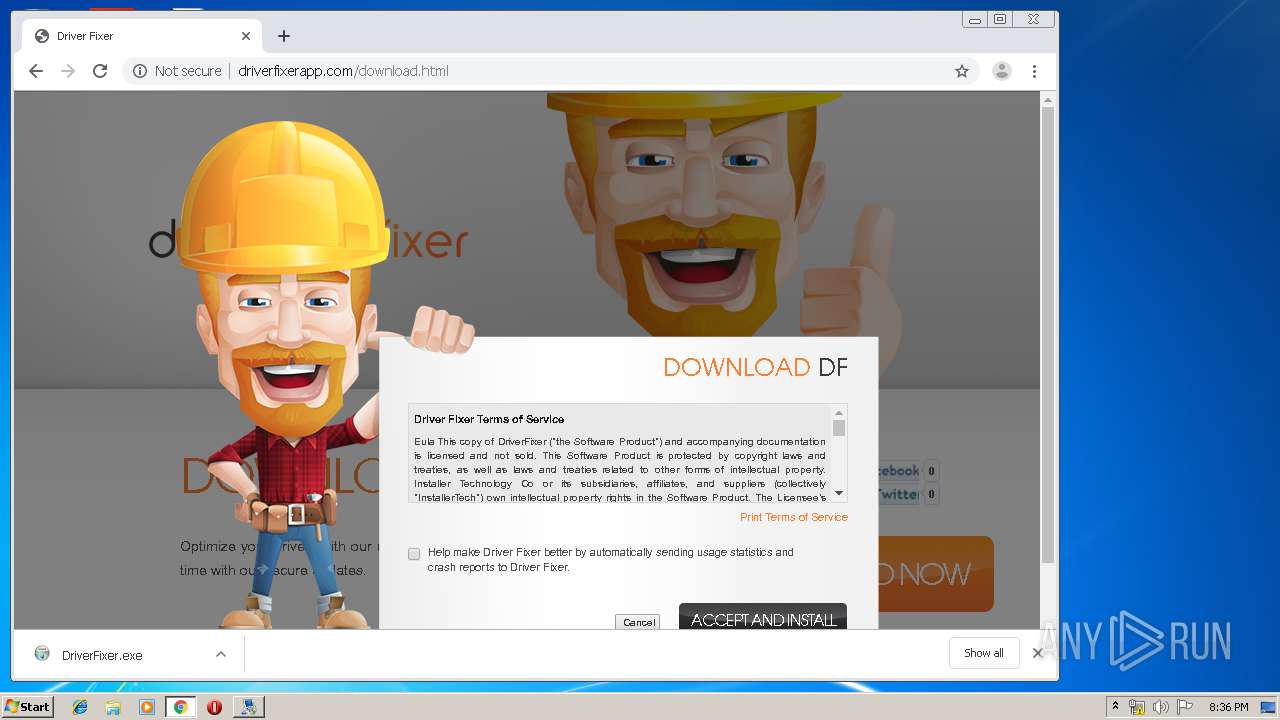
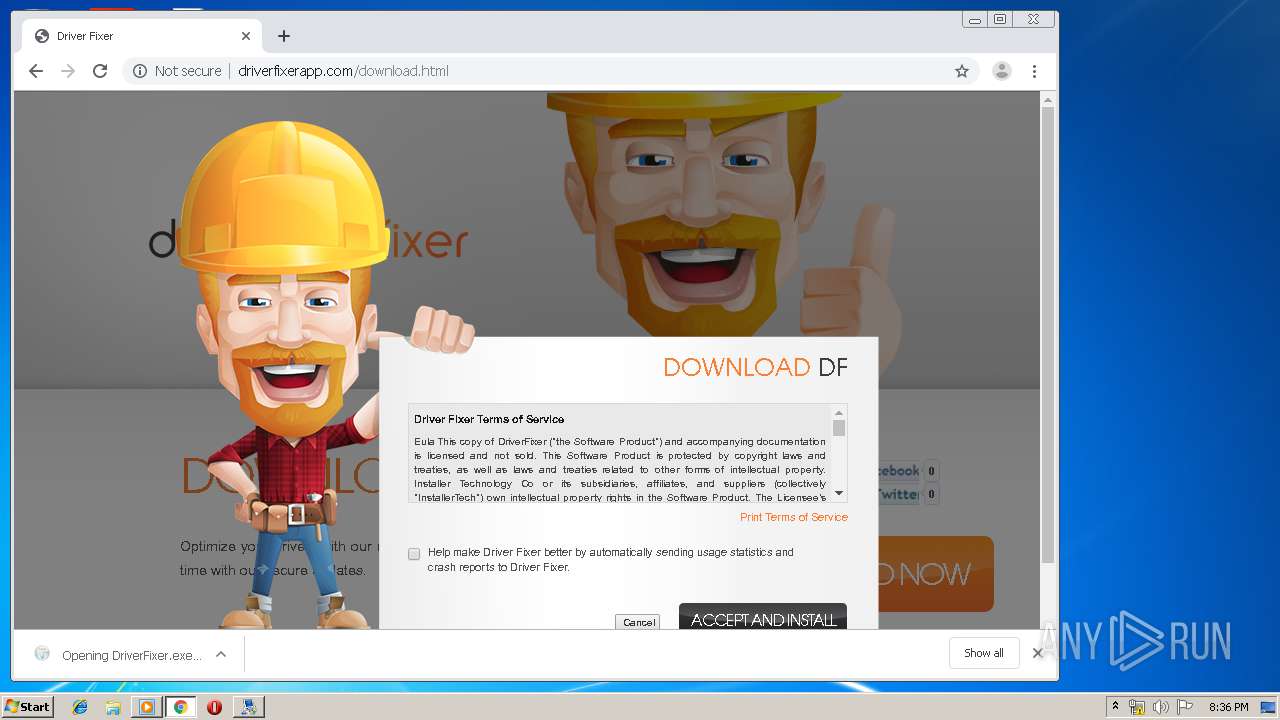
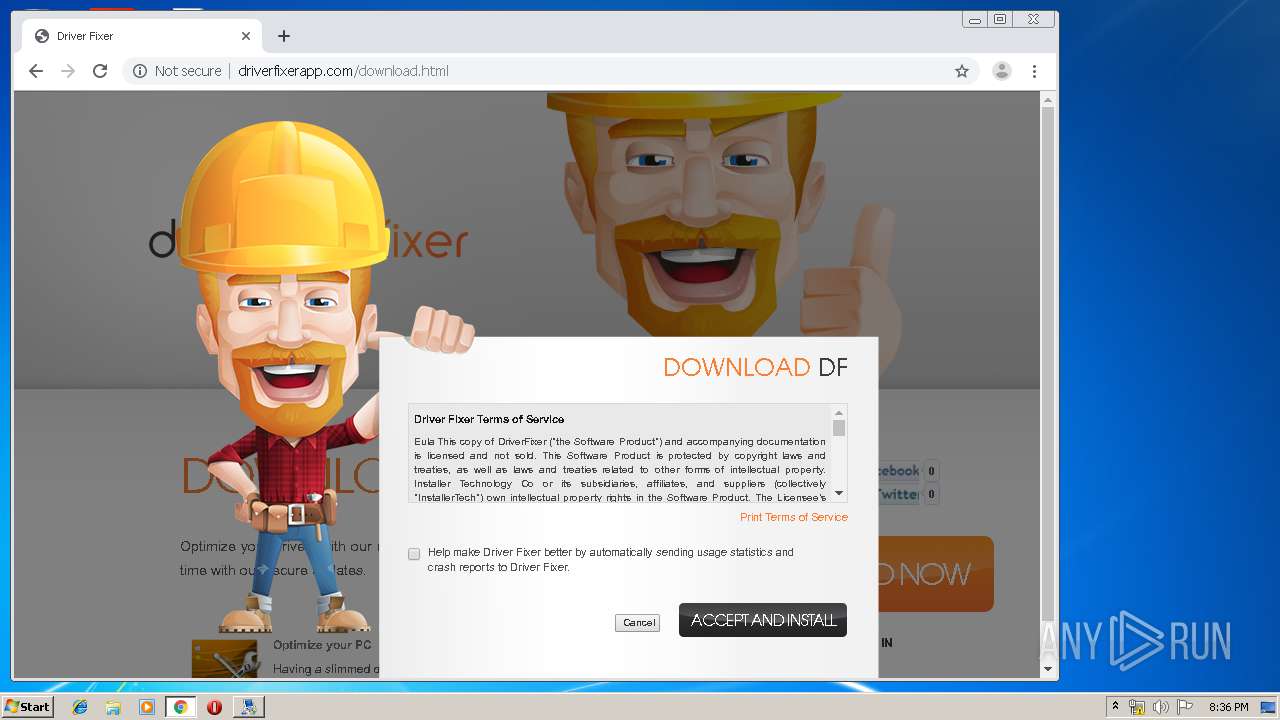
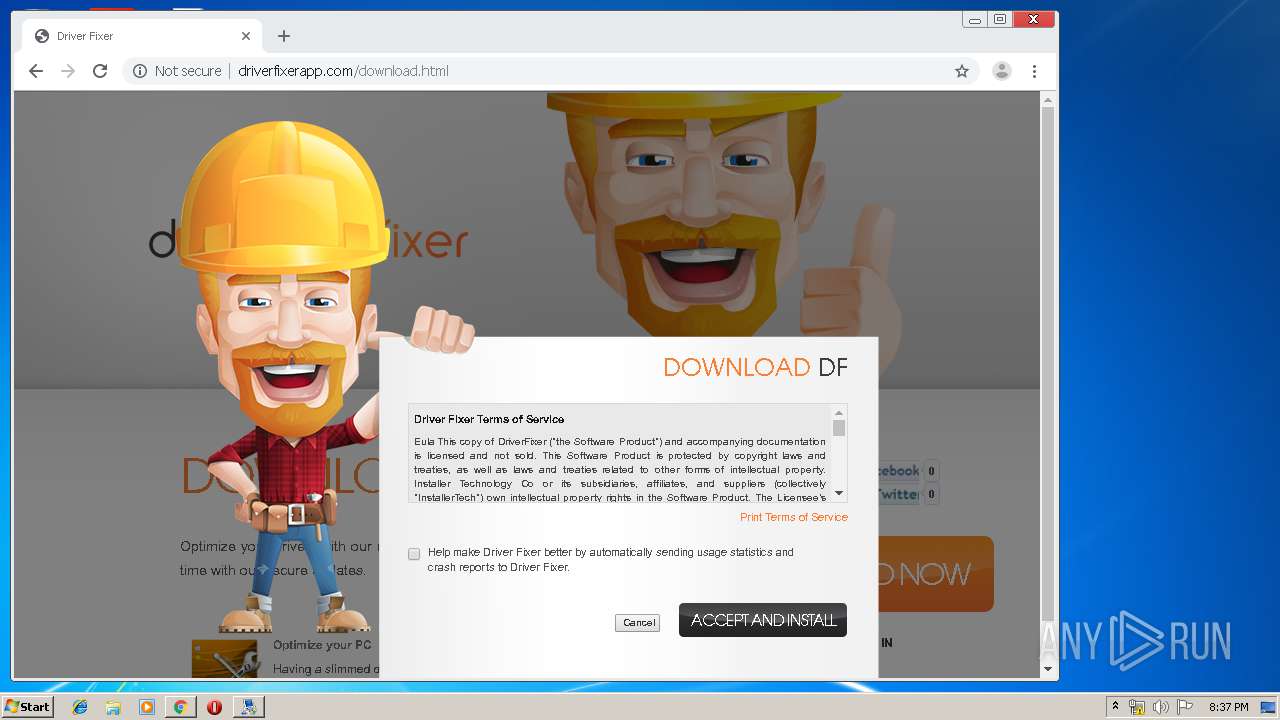
- DriverFixer.exe (PID: 1808)
- DriverFixer.exe (PID: 2420)
- DriverFixer.exe (PID: 2328)
- helper.exe (PID: 2624)
- DriverFixer.exe (PID: 2120)
- helper.exe (PID: 3016)
Loads the Task Scheduler DLL interface
- msfeedssync.exe (PID: 2692)
Loads the Task Scheduler COM API
- EasyBCD.exe (PID: 3488)
- msfeedssync.exe (PID: 2692)
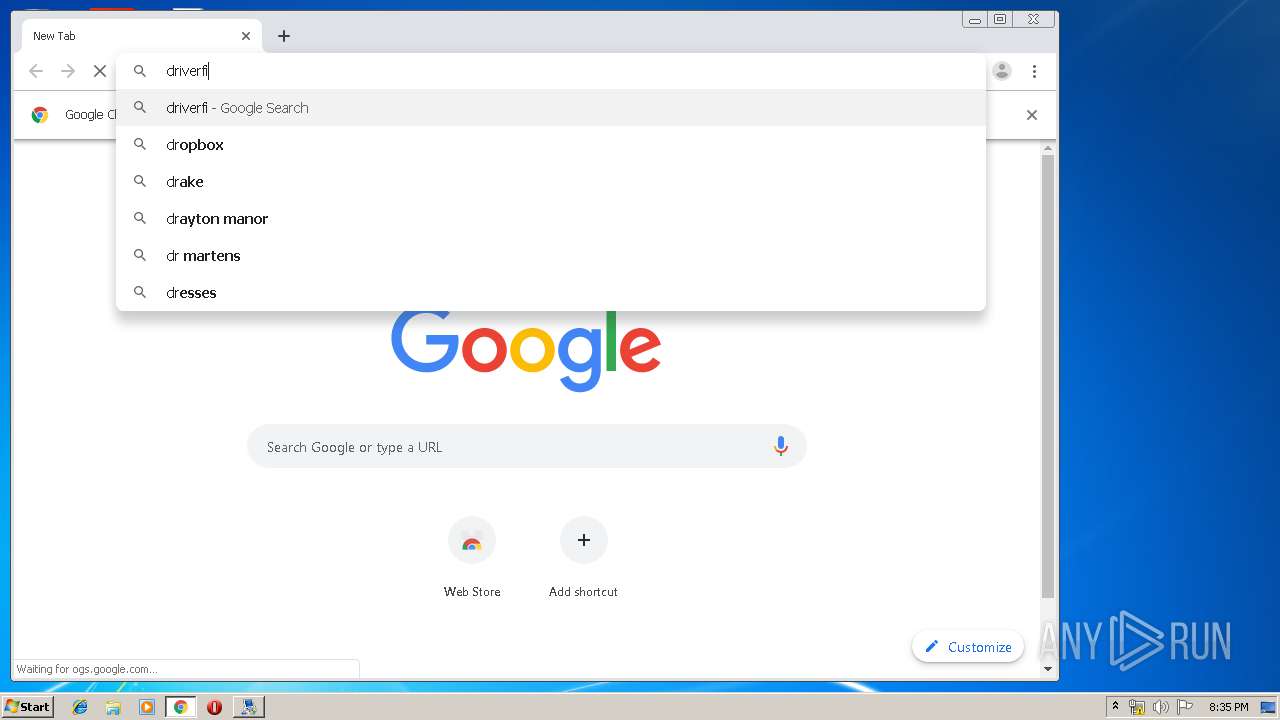
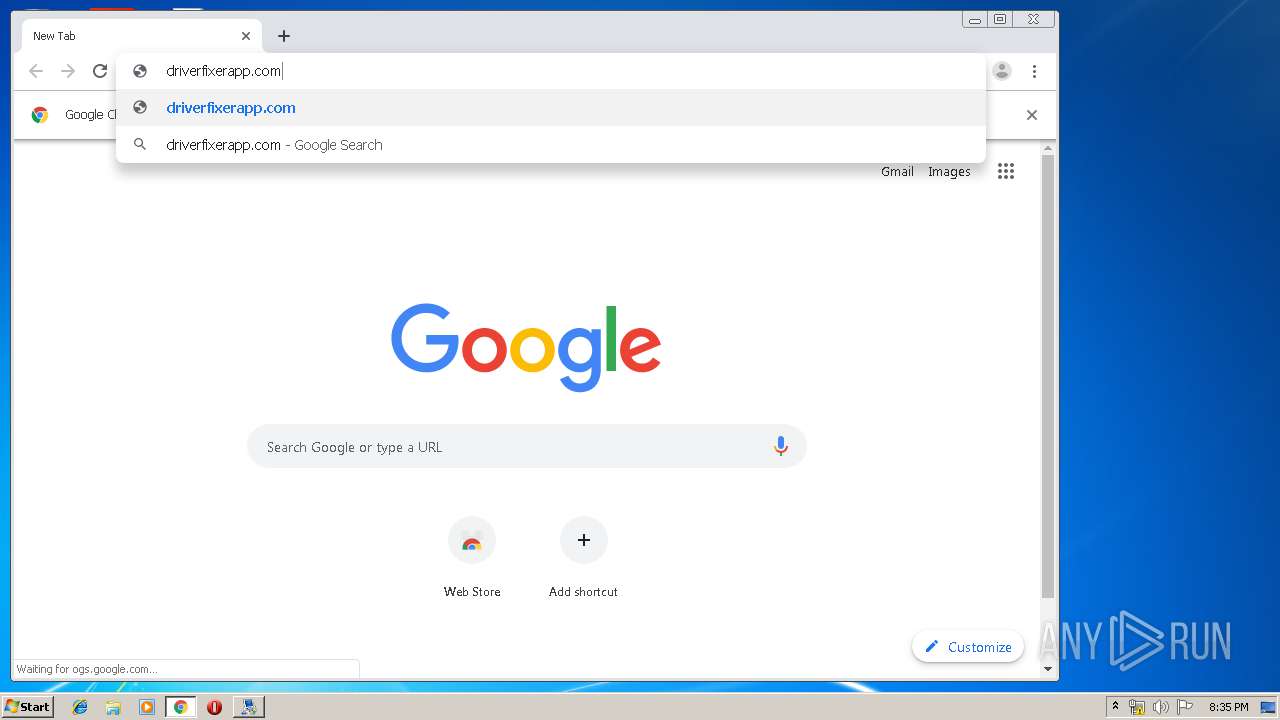
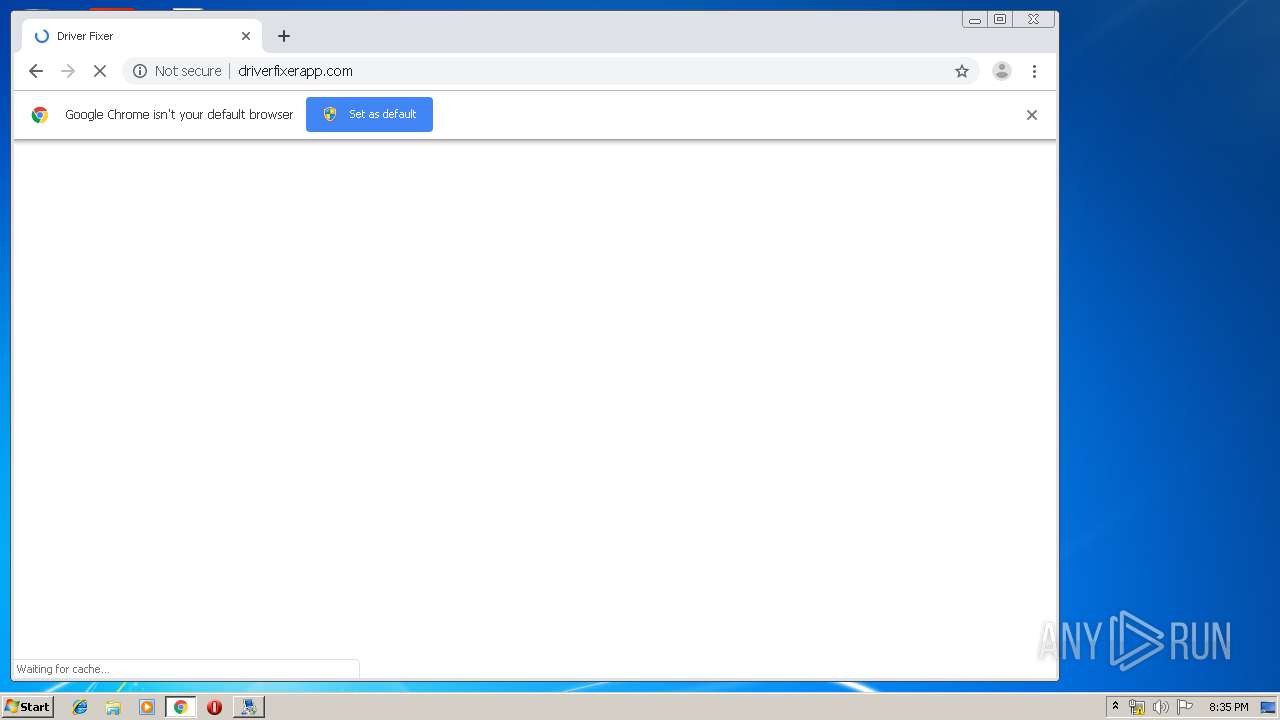
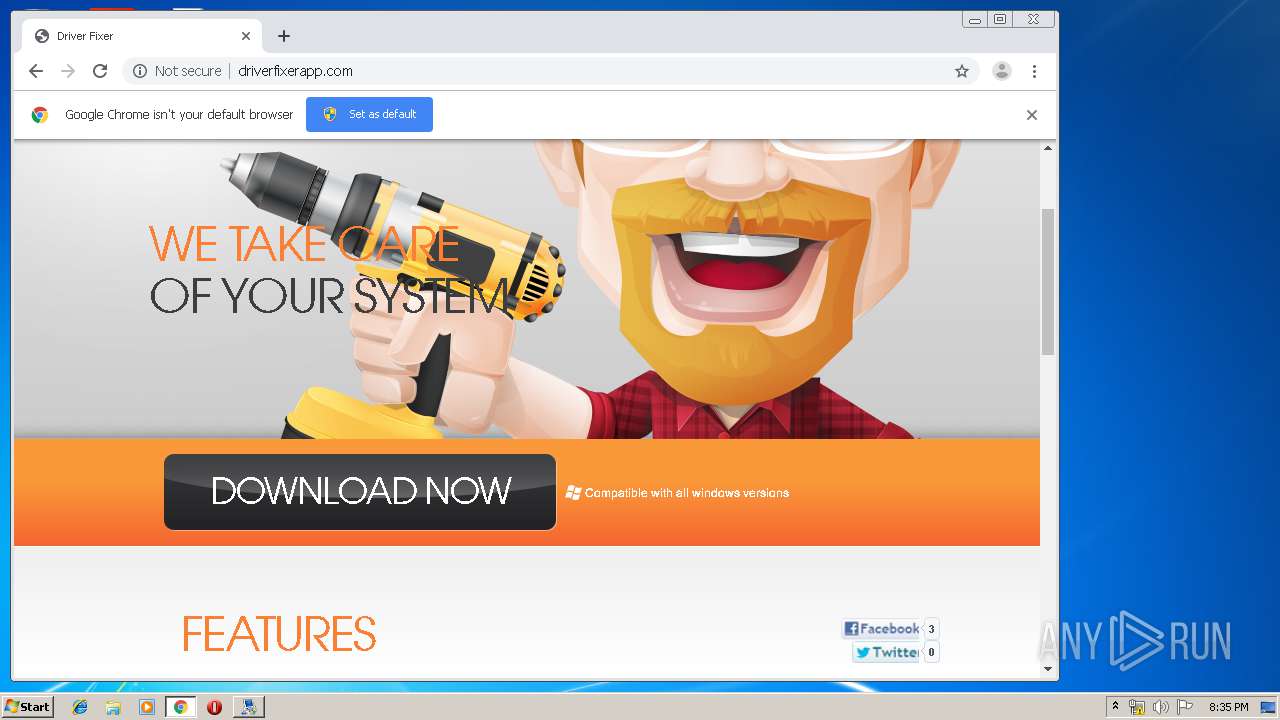
Downloads executable files from the Internet
- chrome.exe (PID: 2224)
SUSPICIOUS
Uses TASKKILL.EXE to kill process
- EasyBCD 2.4.exe (PID: 668)
Reads internet explorer settings
- EasyBCD.exe (PID: 3488)
- msfeedssync.exe (PID: 2692)
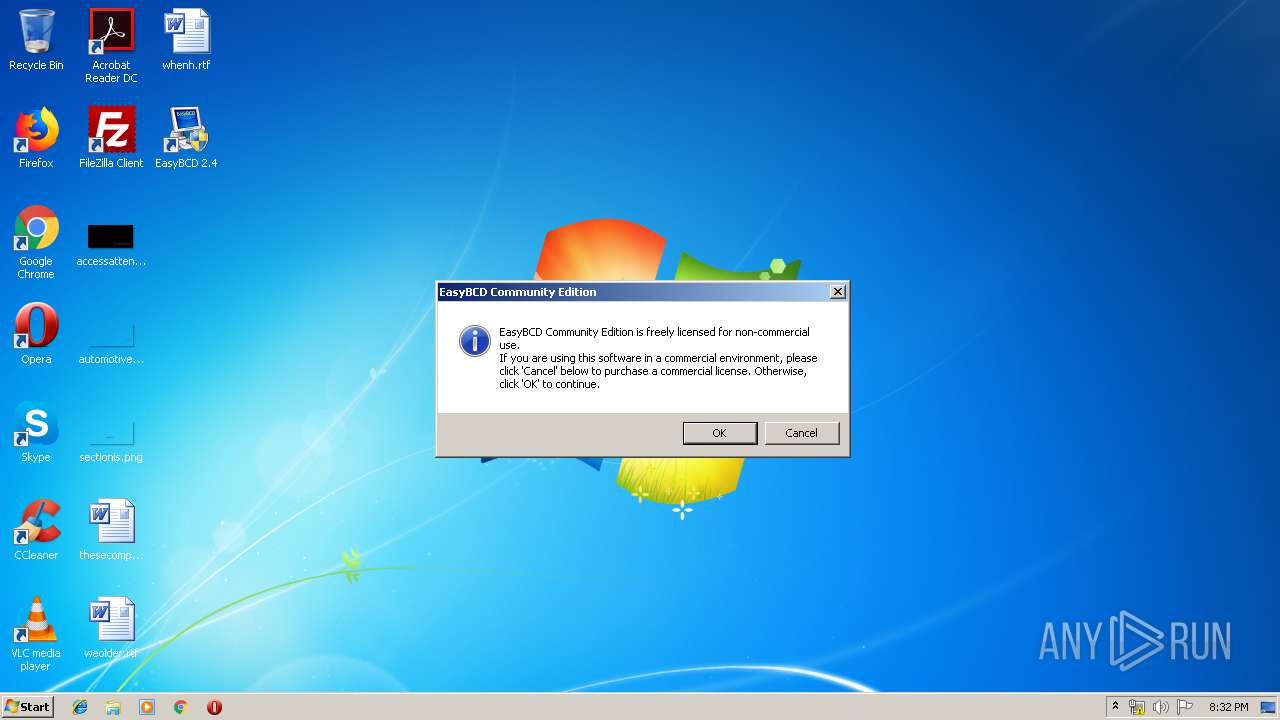
Creates a software uninstall entry
- EasyBCD 2.4.exe (PID: 668)
Executable content was dropped or overwritten
- EasyBCD 2.4.exe (PID: 668)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 2224)
- DriverFixer.exe (PID: 2420)
- DriverFixer.exe (PID: 2120)
Reads Environment values
- EasyBCD.exe (PID: 3488)
Low-level read access rights to disk partition
- bootgrabber.exe (PID: 3632)
- bcdedit.exe (PID: 3772)
Reads Internet Cache Settings
- EasyBCD.exe (PID: 3488)
Creates files in the program directory
- EasyBCD 2.4.exe (PID: 668)
- DriverFixer.exe (PID: 2420)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4088)
Starts Internet Explorer
- EasyBCD.exe (PID: 3488)
Creates files in the user directory
- msfeedssync.exe (PID: 2692)
INFO
Reads settings of System Certificates
- EasyBCD.exe (PID: 3488)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 4088)
Manual execution by user
- chrome.exe (PID: 4088)
Reads Internet Cache Settings
- chrome.exe (PID: 4088)
- iexplore.exe (PID: 1864)
Application launched itself
- chrome.exe (PID: 4088)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2224)
- chrome.exe (PID: 4088)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1864)
Reads internet explorer settings
- iexplore.exe (PID: 1864)
Changes settings of System certificates
- iexplore.exe (PID: 1864)
Creates files in the user directory
- iexplore.exe (PID: 1864)
Changes internet zones settings
- iexplore.exe (PID: 3736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:38 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40397 |
.rdata | 0x00008000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04426 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22445 |
.ndata | 0x00025000 | 0x00011000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00036000 | 0x000101D0 | 0x00010200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.22105 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27881 | 1260 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.14157 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.26965 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.80315 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 3.89244 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
106
Monitored processes
52
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5692498983727077517,3441103337622909252,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18041169041520036847 --mojo-platform-channel-handle=4264 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 668 | "C:\Users\admin\AppData\Local\Temp\EasyBCD 2.4.exe" | C:\Users\admin\AppData\Local\Temp\EasyBCD 2.4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5692498983727077517,3441103337622909252,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6707283695081297989 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5692498983727077517,3441103337622909252,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9483122087590151851 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5692498983727077517,3441103337622909252,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2431938874082588634 --mojo-platform-channel-handle=3804 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5692498983727077517,3441103337622909252,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11045108847245780098 --mojo-platform-channel-handle=3348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5692498983727077517,3441103337622909252,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14014943033799183285 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,5692498983727077517,3441103337622909252,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=985604386746600434 --mojo-platform-channel-handle=4356 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1808 | "C:\Users\admin\Downloads\DriverFixer.exe" | C:\Users\admin\Downloads\DriverFixer.exe | — | chrome.exe | |||||||||||
User: admin Company: AppSmart Integrity Level: MEDIUM Description: DriverFixer Exit code: 3221226540 Version: 2.0.0.1 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3736 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 787
Read events
2 423
Write events
357
Delete events
7
Modification events
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\NeoSmart Technologies\EasyBCD |
| Operation: | write | Name: | |
Value: C:\Program Files\NeoSmart Technologies\EasyBCD | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | DisplayName |
Value: EasyBCD 2.4 | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\NeoSmart Technologies\EasyBCD\uninstall.exe | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\NeoSmart Technologies\EasyBCD\EasyBCD.exe | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | HelpLink |
Value: http://neosmart.net/forums/ | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | URLUpdateInfo |
Value: http://neosmart.net/EasyBCD/ | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | VersionMajor |
Value: 2 | |||
| (PID) Process: | (668) EasyBCD 2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EasyBCD |
| Operation: | write | Name: | VersionMinor |
Value: 4 | |||
Executable files
24
Suspicious files
90
Text files
581
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 668 | EasyBCD 2.4.exe | C:\Users\admin\AppData\Local\Temp\nscDECE.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 668 | EasyBCD 2.4.exe | C:\Users\admin\AppData\Local\Temp\nscDECE.tmp\System.dll | executable | |
MD5:B0C77267F13B2F87C084FD86EF51CCFC | SHA256:A0CAC4CF4852895619BC7743EBEB89F9E4927CCDB9E66B1BCD92A4136D0F9C77 | |||
| 668 | EasyBCD 2.4.exe | C:\Program Files\NeoSmart Technologies\EasyBCD\bin\bcdedit.exe | executable | |
MD5:A60CBAEA0F8AC802D21C0CC7BC2589BE | SHA256:8BF1B71182FED18D6B4112BDC4D496800B5BF6681DE4C4F6536BA67378F38A12 | |||
| 668 | EasyBCD 2.4.exe | C:\Program Files\NeoSmart Technologies\EasyBCD\EasyBCD.exe | executable | |
MD5:E478C92160A3C73C77CDC9F515DFD8B0 | SHA256:6A6E16C176004128B918EF3F9ECF1D51D828E6099FBA6542B5AC6ABDB67C1030 | |||
| 668 | EasyBCD 2.4.exe | C:\Users\admin\AppData\Local\Temp\nscDECE.tmp\InstallOptions.dll | executable | |
MD5:8D5A5529462A9BA1AC068EE0502578C7 | SHA256:E625DCD0188594B1289891B64DEBDDEB5159ACA182B83A12675427B320BF7790 | |||
| 668 | EasyBCD 2.4.exe | C:\Program Files\NeoSmart Technologies\EasyBCD\bin\BootGrabber.exe | executable | |
MD5:2E12B37D32C8BCF8920F5EBB6D24A6B9 | SHA256:F9842333F0B562B4AB5349A09FC173B0B2971C1F600502C4284781C78A735D7E | |||
| 668 | EasyBCD 2.4.exe | C:\Program Files\NeoSmart Technologies\EasyBCD\NeoSmart.Localization.dll | executable | |
MD5:AD0A59AE87D4BA106E965C62F0BC3D88 | SHA256:3A56005B2EFB34620019EF432FE90EEB63726FC78B37BE841F25C2AED82EB1DB | |||
| 668 | EasyBCD 2.4.exe | C:\Program Files\NeoSmart Technologies\EasyBCD\bin\UtfRedirect.exe | executable | |
MD5:5B40791899FA37507E7C08BC3D9F5294 | SHA256:5A87D9485F6E13EE2C3BA4AC289A3E237D17A43ED428B8A5BD5F00FC4800D1AC | |||
| 668 | EasyBCD 2.4.exe | C:\Program Files\NeoSmart Technologies\EasyBCD\LICENSE | text | |
MD5:2458D2762467CD07CC91448A30A2E572 | SHA256:FFBFE4D5757BD4315B79F55B9151625C29110EA16ABF81517D27E17136BF4094 | |||
| 668 | EasyBCD 2.4.exe | C:\Program Files\NeoSmart Technologies\EasyBCD\bin\bcdboot.exe | executable | |
MD5:9F9E397630A146E875735F2F42339E6B | SHA256:9898F537B8D3097A05B42F42523CD66FCA7C020E8083EDBE461E6D9A12DD168E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
103
DNS requests
80
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3488 | EasyBCD.exe | GET | — | 65.182.170.12:80 | http://feeds.neosmart.net/neosmart | US | — | — | unknown |
2692 | msfeedssync.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkId=129794 | unknown | — | — | whitelisted |
2692 | msfeedssync.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkId=121315 | unknown | — | — | whitelisted |
2692 | msfeedssync.exe | GET | 200 | 92.122.253.175:80 | http://www.microsoft.com/athome/community/rss.xml | unknown | — | — | whitelisted |
2692 | msfeedssync.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkId=68929 | unknown | — | — | whitelisted |
2692 | msfeedssync.exe | GET | 200 | 92.122.253.175:80 | http://www.microsoft.com/atwork/community/rss.xml | unknown | — | — | whitelisted |
2692 | msfeedssync.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkId=129793 | unknown | — | — | whitelisted |
2692 | msfeedssync.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkId=68928 | unknown | — | — | whitelisted |
3488 | EasyBCD.exe | GET | 200 | 216.58.206.19:80 | http://rss.neosmart.net/neosmart | US | xml | 59.3 Kb | malicious |
2692 | msfeedssync.exe | GET | 200 | 204.79.197.203:80 | http://www.msn.com/en-us?devicegroup=downlevel.mobile&webslice=ieslice | US | xml | 2.65 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3488 | EasyBCD.exe | 13.32.158.44:443 | api.neosmart.net | Amazon.com, Inc. | US | unknown |
3488 | EasyBCD.exe | 65.182.170.12:80 | feeds.neosmart.net | NetSource Communications, Inc. | US | unknown |
3488 | EasyBCD.exe | 65.182.170.12:443 | feeds.neosmart.net | NetSource Communications, Inc. | US | unknown |
3488 | EasyBCD.exe | 216.58.206.19:80 | rss.neosmart.net | Google Inc. | US | whitelisted |
2692 | msfeedssync.exe | 2.19.38.59:80 | go.microsoft.com | Akamai International B.V. | — | whitelisted |
2692 | msfeedssync.exe | 204.79.197.203:80 | www.msn.com | Microsoft Corporation | US | malicious |
2692 | msfeedssync.exe | 92.122.253.175:80 | www.microsoft.com | GTT Communications Inc. | — | suspicious |
2692 | msfeedssync.exe | 2.16.186.19:80 | rssgov.windows.microsoft.com | Akamai International B.V. | — | whitelisted |
2692 | msfeedssync.exe | 65.182.170.12:80 | feeds.neosmart.net | NetSource Communications, Inc. | US | unknown |
2692 | msfeedssync.exe | 216.58.206.19:80 | rss.neosmart.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.neosmart.net |
| malicious |
feeds.neosmart.net |
| unknown |
neosmart.net |
| whitelisted |
rss.neosmart.net |
| malicious |
go.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
rssgov.windows.microsoft.com |
| whitelisted |
rss.msn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2224 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |