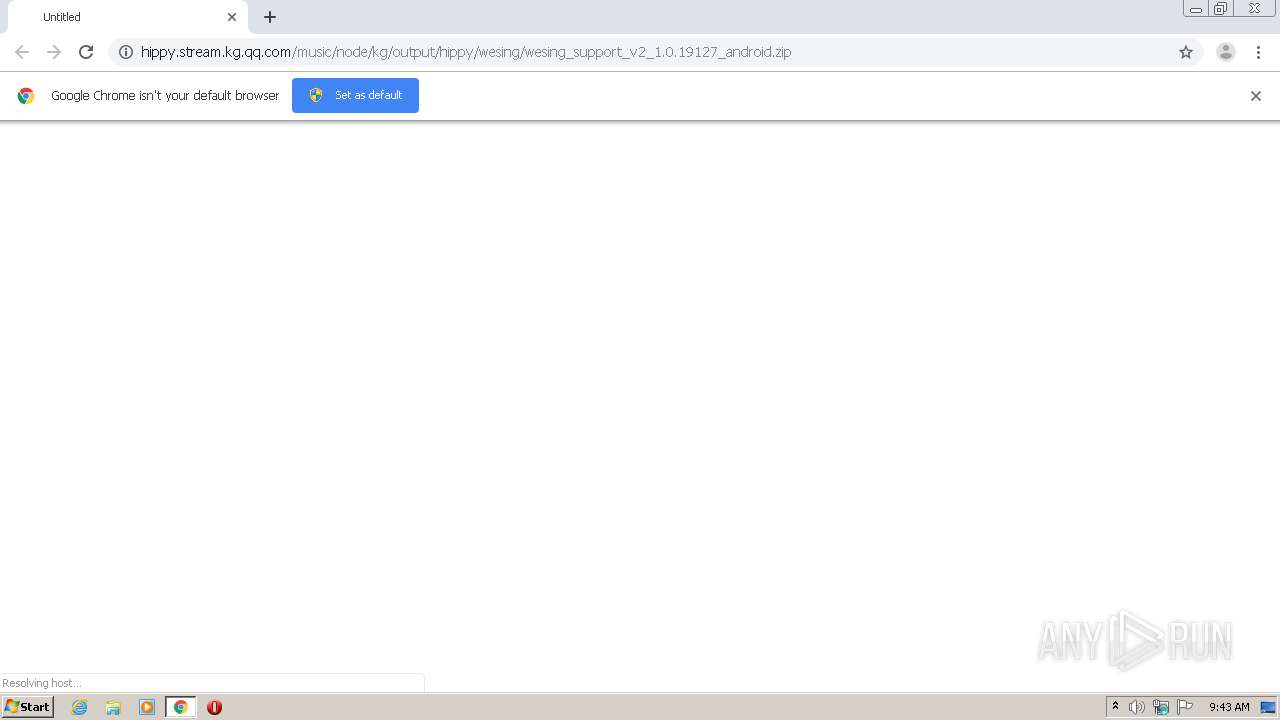
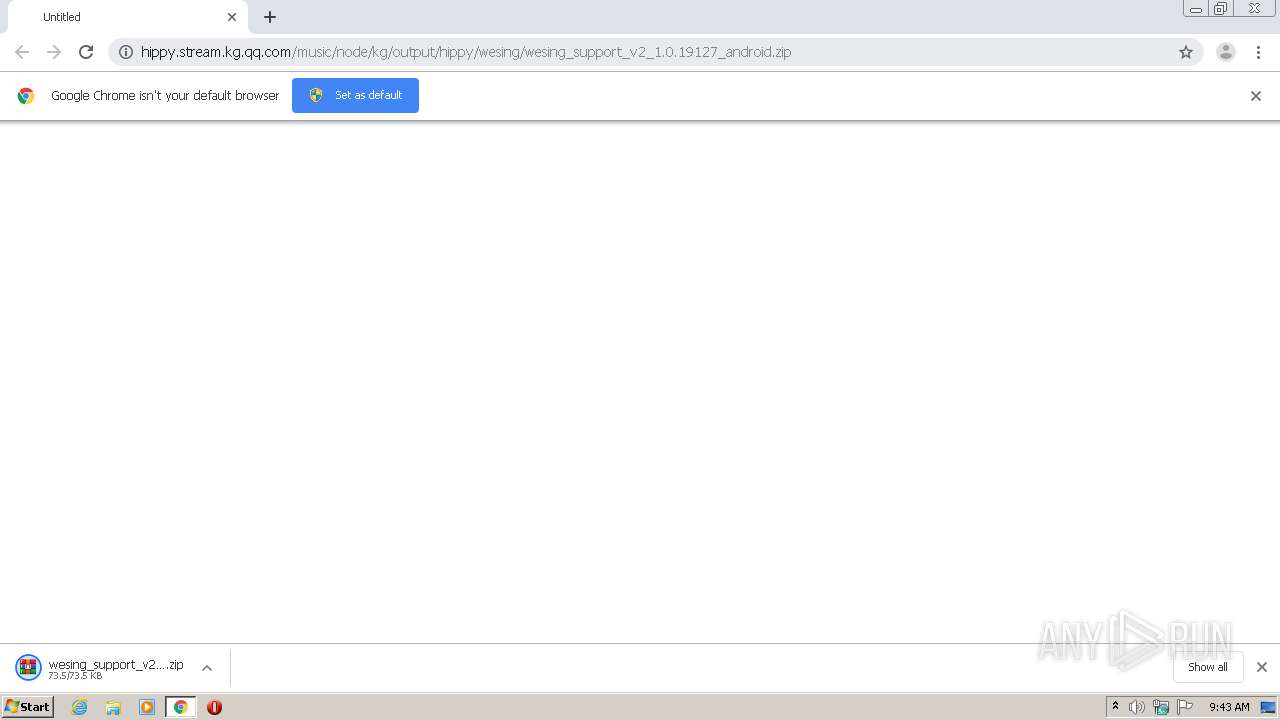
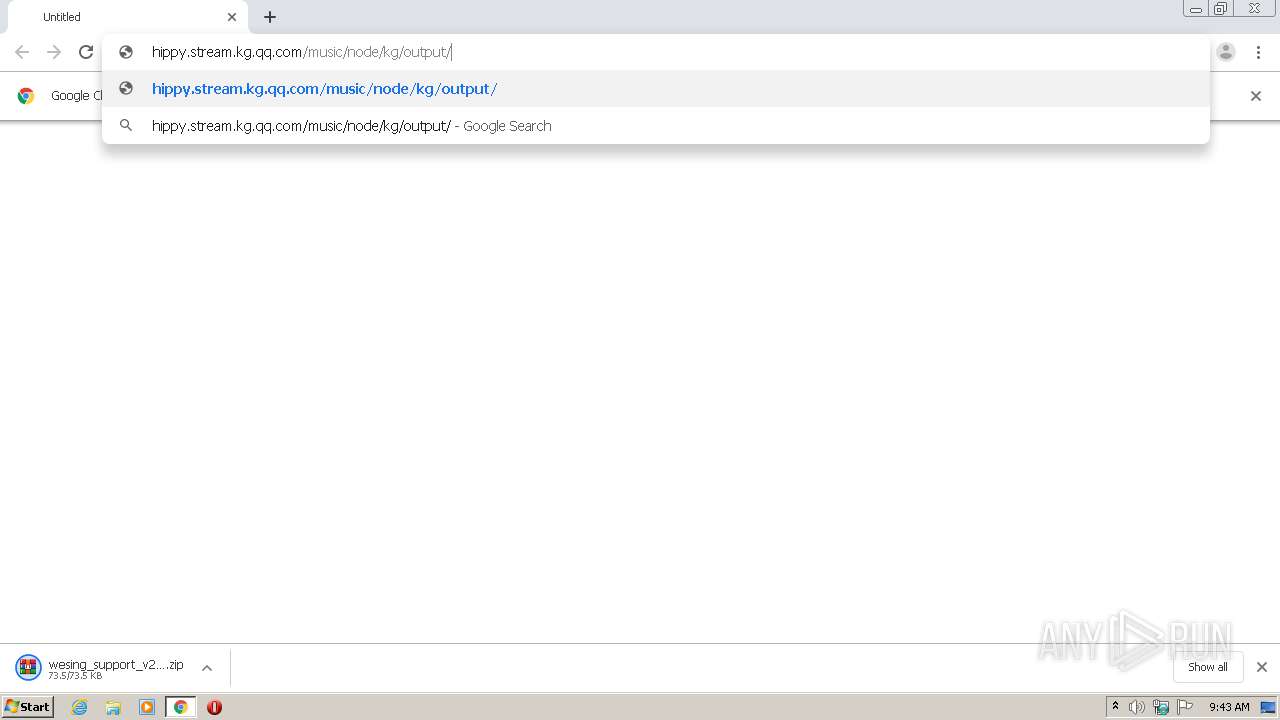
| URL: | http://hippy.stream.kg.qq.com/music/node/kg/output/hippy/wesing/wesing_support_v2_1.0.19127_android.zip |
| Full analysis: | https://app.any.run/tasks/a488231f-3e14-4ebf-84e6-79ce0f649f7e |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 08:43:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5B173399A64A531502FF0DEC6B5102A5 |
| SHA1: | EB9751521664B30CE316E1C1A9AD2EE166E306D1 |
| SHA256: | 0A6ECE74EE6CFC66B25DA07306DA94CA94E0FA0D451C5D3BFF50B0EA03B10C02 |
| SSDEEP: | 3:N1KWM/EESGfcaAKhseVgARSE/Q6bTUa1XXB4:CWMEE1fca5tVgA0FaTp1HB4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2980)
- chrome.exe (PID: 2540)
Reads Internet Cache Settings
- chrome.exe (PID: 2980)
Application launched itself
- chrome.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3130764157434024378 --mojo-platform-channel-handle=2928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14715863741693719037 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15951695125957192237 --mojo-platform-channel-handle=2532 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16450161021909937143 --mojo-platform-channel-handle=2968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16032601037503148625 --mojo-platform-channel-handle=1068 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13922893475450925888 --mojo-platform-channel-handle=1508 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11993981252688361653 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17837025770870817963 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8352600438342814575,1929334880674742407,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10514005314059246761 --mojo-platform-channel-handle=948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://hippy.stream.kg.qq.com/music/node/kg/output/hippy/wesing/wesing_support_v2_1.0.19127_android.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
962
Read events
865
Write events
93
Delete events
4
Modification events
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2980-13247657001618625 |
Value: 259 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
29
Text files
106
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8EA32A-BA4.pma | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\47275cc4-106f-4df2-b9b2-31757268c7ef.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF165141.TMP | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
56
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
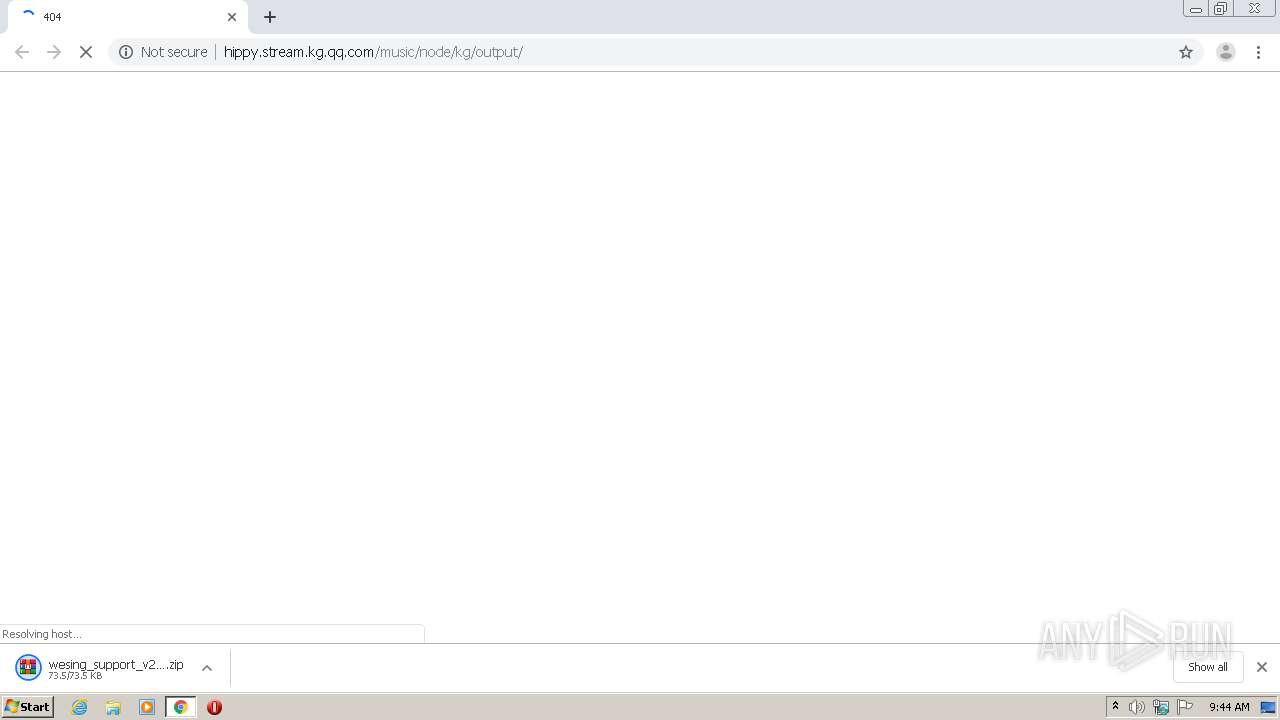
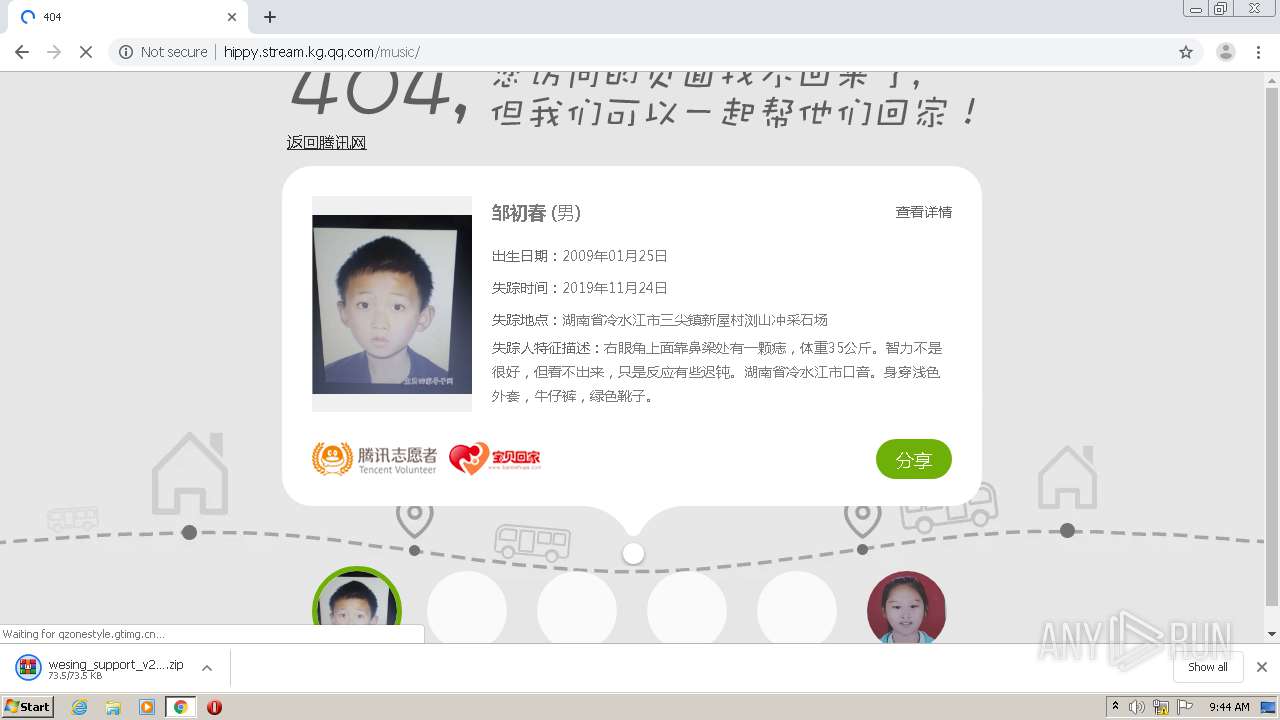
2540 | chrome.exe | GET | 200 | 203.205.224.17:80 | http://hippy.stream.kg.qq.com/music/node/kg/output/hippy/wesing/wesing_support_v2_1.0.19127_android.zip | CN | compressed | 73.4 Kb | unknown |
2540 | chrome.exe | GET | 200 | 203.205.136.77:80 | http://qzonestyle.gtimg.cn/qzone/hybrid/app/404/style/image/logo_tencentvolunteers.png | CN | image | 3.07 Kb | whitelisted |
2540 | chrome.exe | GET | 200 | 203.205.136.77:80 | http://qzonestyle.gtimg.cn/qzone/v6/portal/gy/404/data.js | CN | text | 2.70 Kb | whitelisted |
2540 | chrome.exe | GET | 302 | 203.205.254.103:80 | http://h5.qzone.qq.com/proxy/domain/boss.qzone.qq.com/fcg-bin/fcg_zone_info | CN | html | 169 b | malicious |
2540 | chrome.exe | GET | 200 | 203.205.136.77:80 | http://qzonestyle.gtimg.cn/qzone/hybrid/app/404/style/image/logo_baobeihuijia.png | CN | image | 3.59 Kb | whitelisted |
2540 | chrome.exe | GET | 200 | 203.205.136.77:80 | http://qzonestyle.gtimg.cn/qzone/hybrid/app/404/search_children.js | CN | text | 6.58 Kb | whitelisted |
2540 | chrome.exe | GET | 200 | 203.205.136.77:80 | http://qzonestyle.gtimg.cn/qzone/hybrid/app/404/style/image/bg_page.png | CN | image | 9.29 Kb | whitelisted |
2540 | chrome.exe | GET | 200 | 203.205.136.77:80 | http://qzonestyle.gtimg.cn/qzone/hybrid/app/404/style/image/txt_title.png | CN | image | 5.43 Kb | whitelisted |
2540 | chrome.exe | GET | 200 | 203.205.136.77:80 | http://qzonestyle.gtimg.cn/qzone/hybrid/app/404/style/404style_min.css | CN | text | 4.71 Kb | whitelisted |
2540 | chrome.exe | GET | 302 | 203.205.254.103:80 | http://h5.qzone.qq.com/proxy/domain/boss.qzone.qq.com/fcg-bin/fcg_zone_info | CN | html | 169 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2540 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 172.217.21.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 203.205.137.113:443 | qzone.qq.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
2540 | chrome.exe | 203.205.137.113:80 | qzone.qq.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
2540 | chrome.exe | 125.39.83.11:443 | ty.captcha.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
2540 | chrome.exe | 203.205.235.61:443 | aegis.qq.com | — | CN | unknown |
2540 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 203.205.224.17:80 | hippy.stream.kg.qq.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
2540 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hippy.stream.kg.qq.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
qzonestyle.gtimg.cn |
| whitelisted |
h5.qzone.qq.com |
| malicious |
e.t.qq.com |
| whitelisted |
bbs.baobeihuijia.com |
| unknown |
www.qq.com |
| whitelisted |