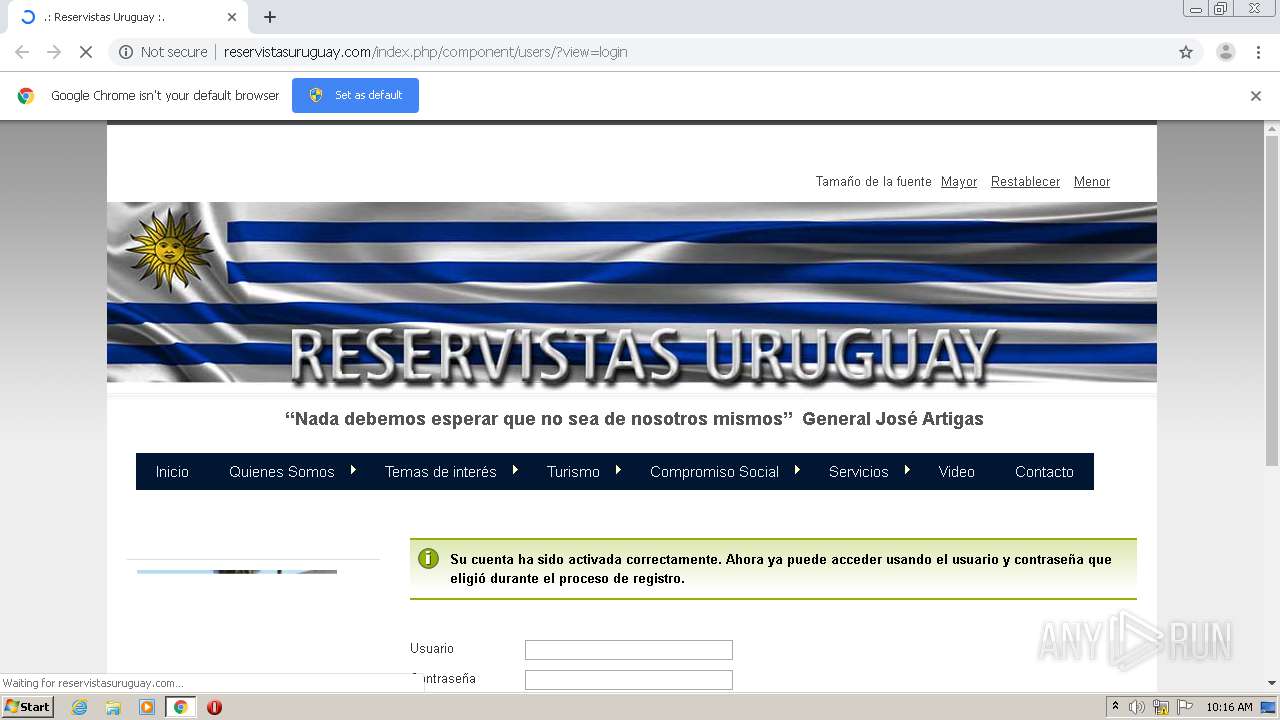
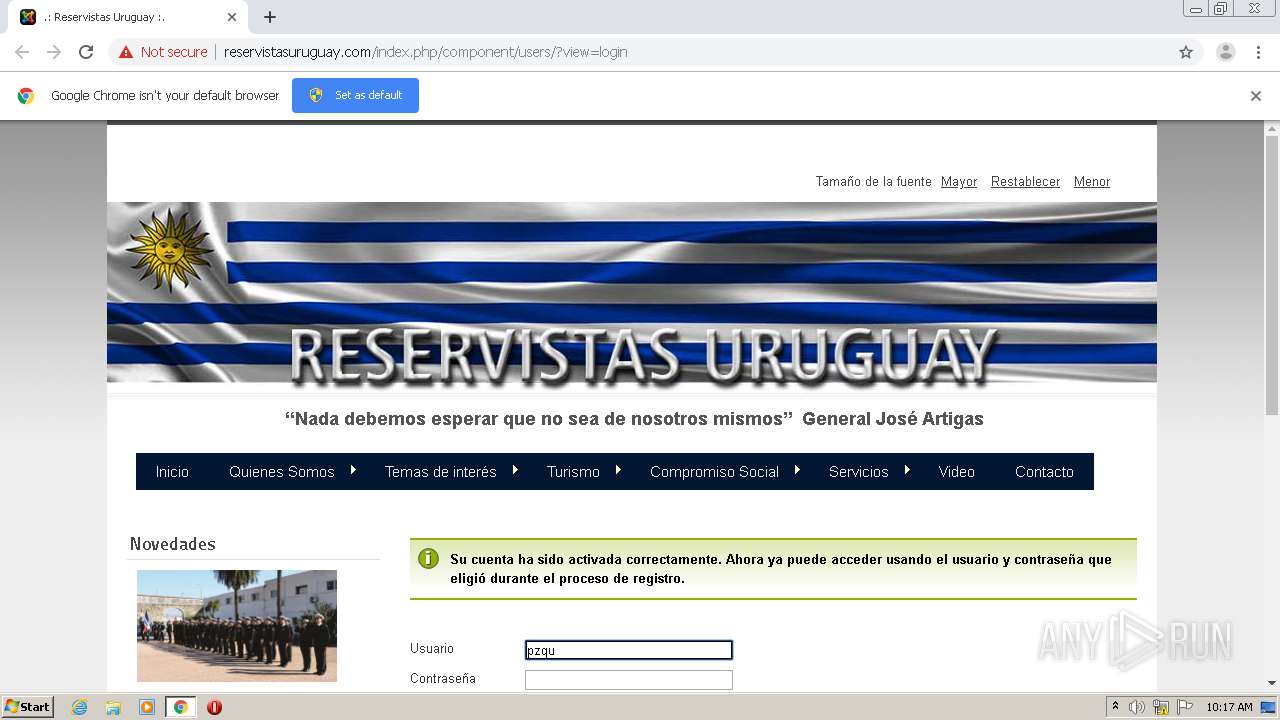
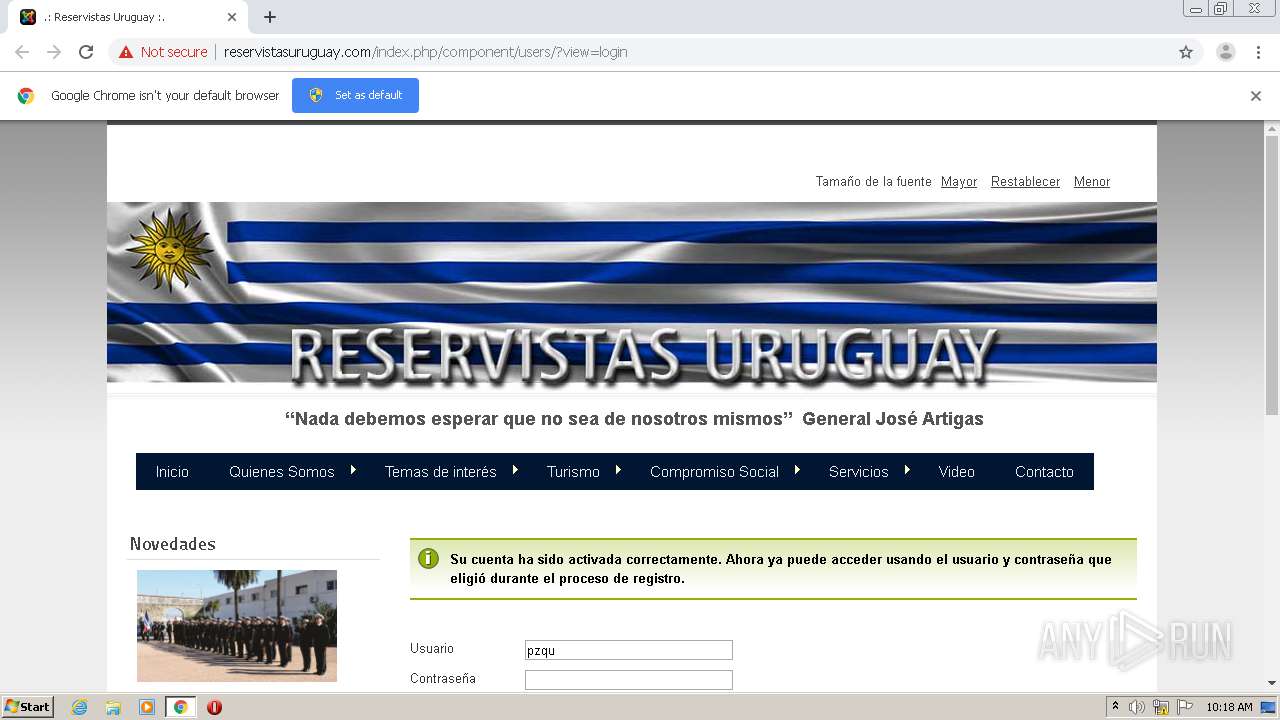
| URL: | http://reservistasuruguay.com/index.php/component/users/?task=registration.activate&token=dba9b2915e10fc1c9a1e017e4845f9a2 |
| Full analysis: | https://app.any.run/tasks/b0783acb-41b9-44b5-8328-4c6d03841072 |
| Verdict: | No threats detected |
| Analysis date: | December 01, 2020, 10:16:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6CDA9AA1AE5BDA0EEC87569BB71DC12D |
| SHA1: | 68F25928009871A762640D59397FFA73407E44F8 |
| SHA256: | 0A6A981E7759727B39B4B028529995A6DCFC51700F50D876A4FD536AEA5FC5FF |
| SSDEEP: | 3:N1KMBXXhcLGTKLbHd0LAsFBiWA0QLCI0RtfsRDa1Uw0QhXn:CMVXKLGTabHiL9FBmnKAu1rLXn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2728)
- chrome.exe (PID: 2192)
Application launched itself
- chrome.exe (PID: 2728)
Manual execution by user
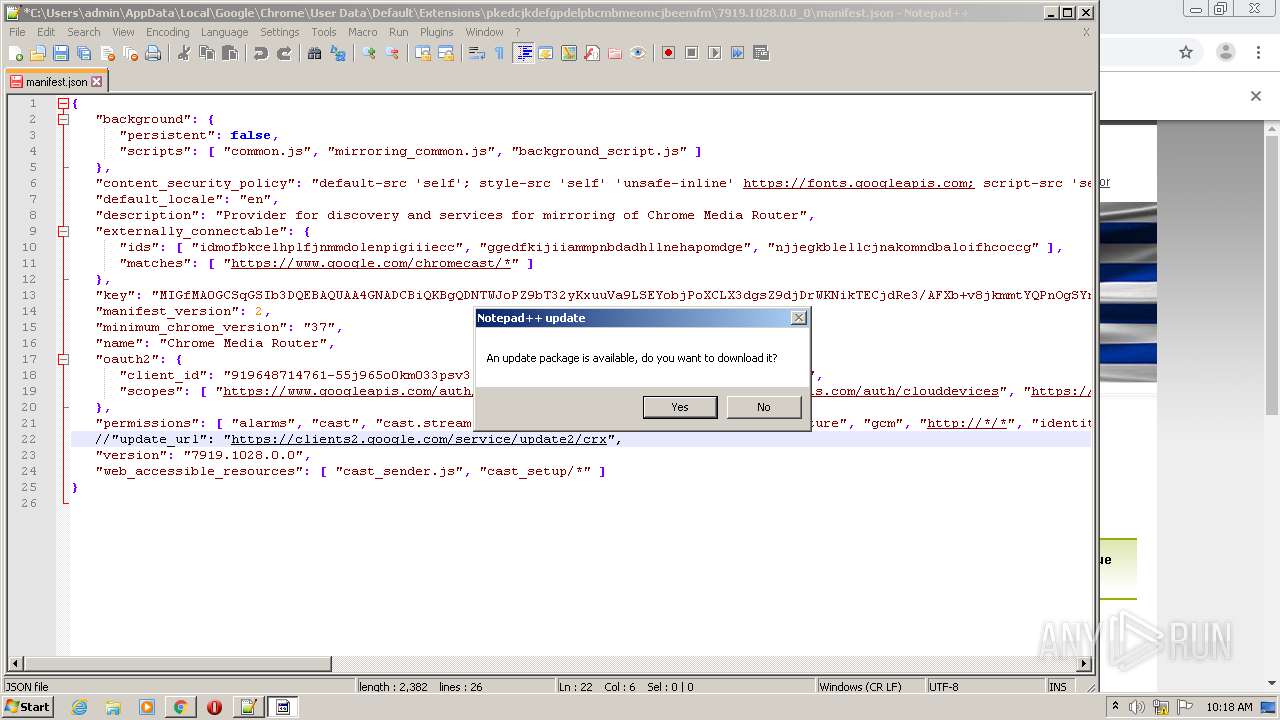
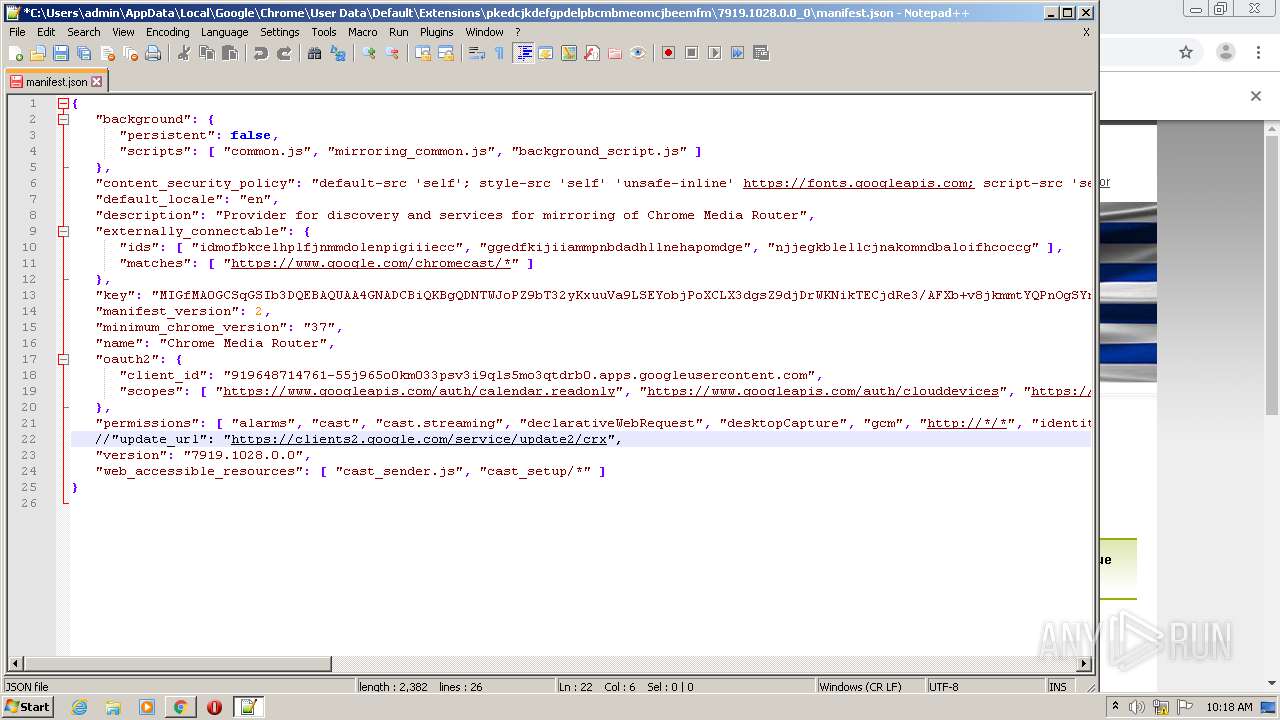
- notepad++.exe (PID: 1136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1136 | "C:\Program Files\Notepad++\notepad++.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,12573054526670255389,14297192922168597243,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17497593929504182589 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,12573054526670255389,14297192922168597243,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1752979104959704268 --mojo-platform-channel-handle=3620 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2732 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,12573054526670255389,14297192922168597243,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7766491531334467130 --mojo-platform-channel-handle=1492 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12573054526670255389,14297192922168597243,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16172351446728902914 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://reservistasuruguay.com/index.php/component/users/?task=registration.activate&token=dba9b2915e10fc1c9a1e017e4845f9a2" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,12573054526670255389,14297192922168597243,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12406025889013798787 --mojo-platform-channel-handle=3508 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12573054526670255389,14297192922168597243,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8985387806067522503 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
638
Read events
570
Write events
65
Delete events
3
Modification events
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2728-13251291405188500 |
Value: 259 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
28
Text files
70
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC6180D-AA8.pma | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\afbcb2be-d7c6-4c48-81a8-cd2940a71c00.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF152f95.TMP | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF152fe3.TMP | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF153179.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
29
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
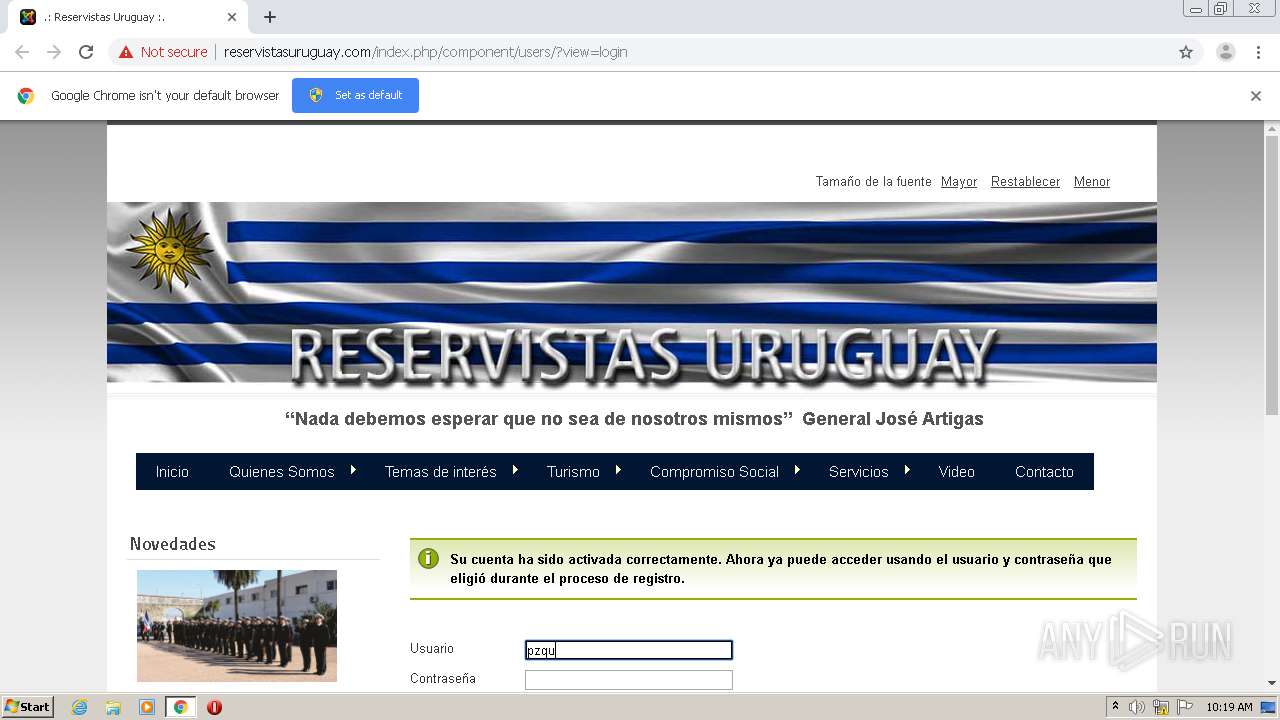
2192 | chrome.exe | GET | 303 | 67.225.214.61:80 | http://reservistasuruguay.com/index.php/component/users/?task=registration.activate&token=dba9b2915e10fc1c9a1e017e4845f9a2 | US | — | — | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/templates/beez5/css/beez5.css | US | text | 21.4 Kb | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/modules/mod_swmenufree/curvycorners.src.js | US | text | 58.8 Kb | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/templates/beez5/images/fruits.jpg | US | image | 27.0 Kb | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/images/novedades/aniversario.jpg | US | image | 1.93 Mb | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/index.php/component/users/?view=login | US | html | 20.7 Kb | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/templates/beez5/css/layout.css | US | text | 29.4 Kb | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/modules/mod_featured_youtube_slider/css/style-responsive.css | US | text | 1.44 Kb | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/templates/system/css/system.css | US | text | 896 b | unknown |
2192 | chrome.exe | GET | 200 | 67.225.214.61:80 | http://reservistasuruguay.com/modules/mod_swmenufree/hoverIntent.js | US | text | 3.10 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2192 | chrome.exe | 104.243.42.114:80 | s07.flagcounter.com | Choopa, LLC | US | suspicious |
2192 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.168.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.168.2:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2192 | chrome.exe | 216.58.207.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.168.70:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
2192 | chrome.exe | 64.233.165.139:443 | clients1.google.com | Google Inc. | US | whitelisted |
1348 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
2192 | chrome.exe | 172.217.168.65:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.23.54:443 | i.ytimg.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
reservistasuruguay.com |
| unknown |
accounts.google.com |
| shared |
i3.ytimg.com |
| whitelisted |
s07.flagcounter.com |
| suspicious |
www.youtube.com |
| whitelisted |
clients1.google.com |
| whitelisted |
showlands.com |
| unknown |
www.joomla.org |
| unknown |
info.flagcounter.com |
| unknown |
googleads.g.doubleclick.net |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|