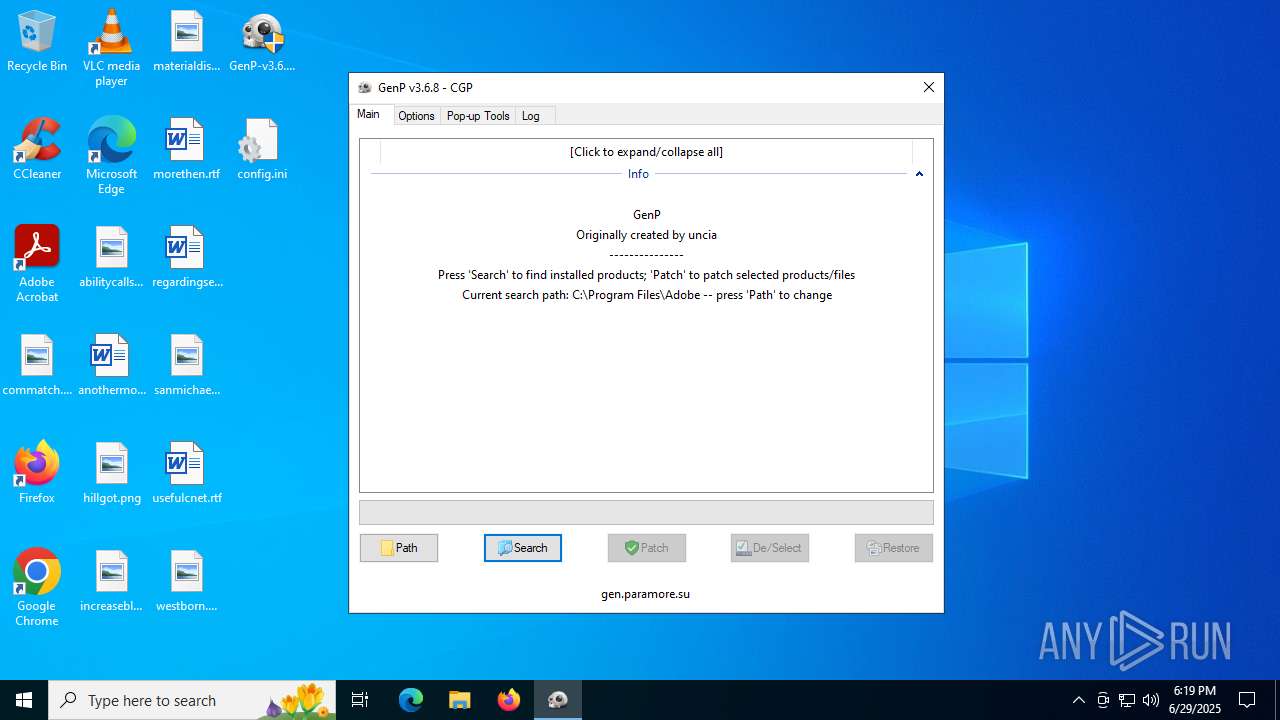
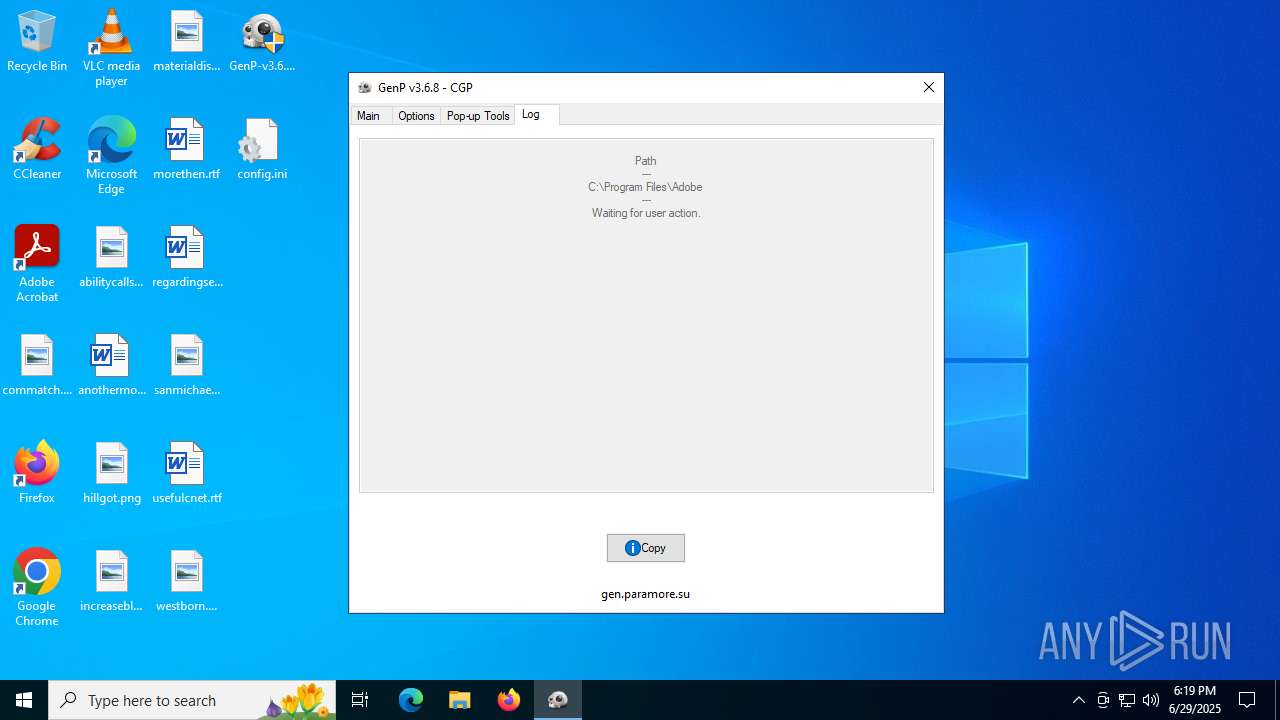
| File name: | GenP-v3.6.8.exe |
| Full analysis: | https://app.any.run/tasks/dd7f3c3d-6a2f-41a1-9962-4c76df1d0489 |
| Verdict: | Malicious activity |
| Analysis date: | June 29, 2025, 18:19:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 3 sections |
| MD5: | 43A927F79EAB66D778C66F1CC37B786E |
| SHA1: | E7818DD001C37E2CD86A4B9445D932C42E8029DC |
| SHA256: | 0A6A100266EF8416E6E02EEC5AC64078C14F4C47A9593C2FB1BE955B2FFF5736 |
| SSDEEP: | 49152:fetKmupSfNHjl4ClQaig25jSHY7GvXiADpB/4mPU3hIHNd/KlNKYOJCTOB2U20wz:WtKDpSRjVKjg25j1ShpC8EhmOKYYCTOq |
MALICIOUS
No malicious indicators.SUSPICIOUS
There is functionality for taking screenshot (YARA)
- GenP-v3.6.8.exe (PID: 724)
INFO
Reads mouse settings
- GenP-v3.6.8.exe (PID: 724)
The sample compiled with english language support
- GenP-v3.6.8.exe (PID: 724)
Reads the computer name
- GenP-v3.6.8.exe (PID: 724)
Checks supported languages
- GenP-v3.6.8.exe (PID: 724)
Create files in a temporary directory
- GenP-v3.6.8.exe (PID: 724)
The process uses AutoIt
- GenP-v3.6.8.exe (PID: 724)
Checks proxy server information
- slui.exe (PID: 1036)
UPX packer has been detected
- GenP-v3.6.8.exe (PID: 724)
Reads the software policy settings
- slui.exe (PID: 1036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:20 13:18:09+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 421888 |
| InitializedDataSize: | 1105920 |
| UninitializedDataSize: | 1740800 |
| EntryPoint: | 0x20fe70 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.6.8.0 |
| ProductVersionNumber: | 3.6.8.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.6.8.0 |
| Comments: | GenP |
| FileDescription: | GenP |
| ProductName: | GenP |
| ProductVersion: | 3.6.8 |
| CompanyName: | GenP |
| LegalCopyright: | GenP 2025 |
| LegalTradeMarks: | GenP 2025 |
Total processes
137
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 724 | "C:\Users\admin\Desktop\GenP-v3.6.8.exe" | C:\Users\admin\Desktop\GenP-v3.6.8.exe | explorer.exe | ||||||||||||
User: admin Company: GenP Integrity Level: HIGH Description: GenP Version: 3.6.8.0 Modules
| |||||||||||||||
| 1036 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5080 | "C:\Users\admin\Desktop\GenP-v3.6.8.exe" | C:\Users\admin\Desktop\GenP-v3.6.8.exe | — | explorer.exe | |||||||||||
User: admin Company: GenP Integrity Level: MEDIUM Description: GenP Exit code: 3221226540 Version: 3.6.8.0 Modules
| |||||||||||||||
Total events
3 552
Read events
3 552
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 724 | GenP-v3.6.8.exe | C:\Users\admin\Desktop\config.ini | text | |
MD5:9E9E253A5B55B1C3E7406C95A90AAE58 | SHA256:A712B27B3327D95A09AE7EE08672DF63B2A84731EAD829124CA4D0EF4B75F130 | |||
| 724 | GenP-v3.6.8.exe | C:\Users\admin\AppData\Local\Temp\aut6050.tmp | binary | |
MD5:A7C593B86D7A8C26E6683C1AD90001FD | SHA256:CD1680B115EE923AB14C9A23317982B5EC0CFBC506DEFC1D4A23E04EDD6E5B79 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
45
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6336 | RUXIMICS.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.160.132:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.32.72:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
6336 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6336 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
6336 | RUXIMICS.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |