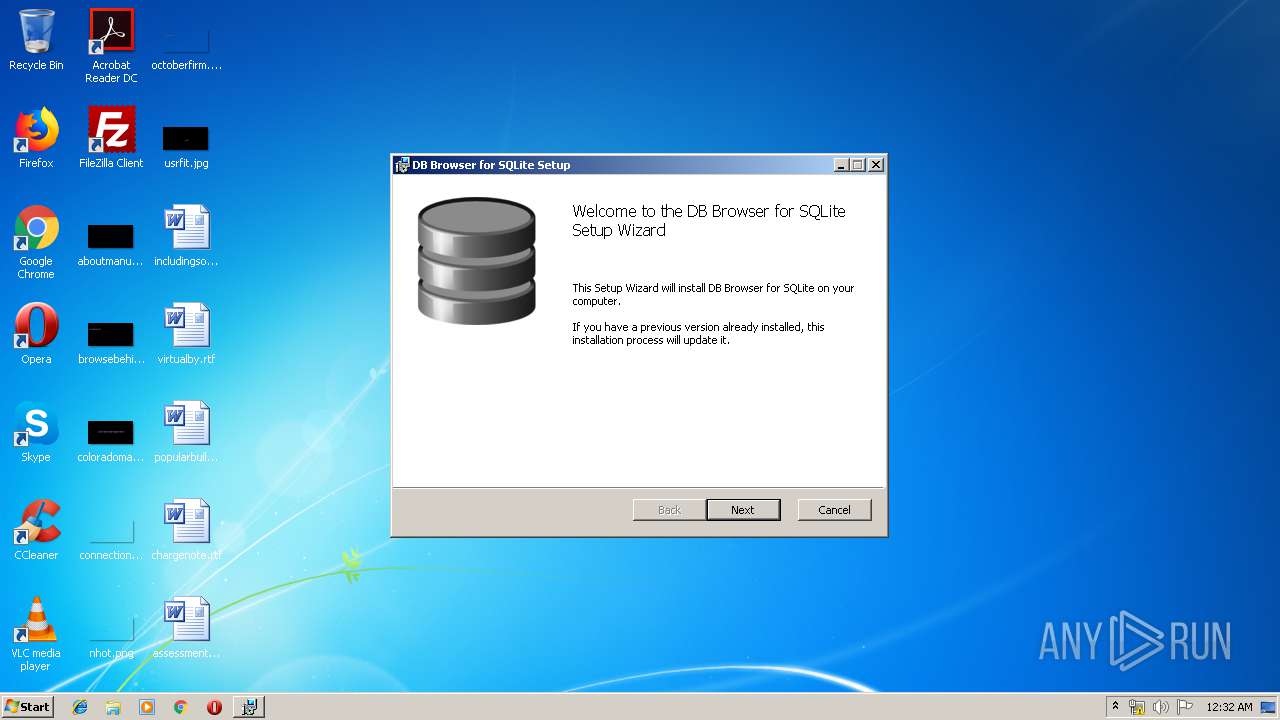
| File name: | DB.Browser.for.SQLite-3.11.2-win32.msi |
| Full analysis: | https://app.any.run/tasks/b39a51d5-f33a-482f-b4b2-67c4e29b9608 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2019, 23:32:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Title: Installation Database, Subject: DB Browser for SQLite, Author: DB Browser for SQLite Team, Keywords: Installer, Comments: This installer database contains the logic and data required to install DB Browser for SQLite., Template: Intel;1033, Revision Number: {D2DE548A-7573-454E-B78E-27F0B02A1982}, Create Time/Date: Wed Apr 3 13:55:54 2019, Last Saved Time/Date: Wed Apr 3 13:55:54 2019, Number of Pages: 405, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.1.2318), Security: 2 |
| MD5: | 9CC7D76481BB00EB3248F0EBE4A0624D |
| SHA1: | 9B0A8D798BEB6FB3D0E3B53756B06F02E825421D |
| SHA256: | 0A660C8EEFDFBB8BE6CF8BE2ABE223B0149CE8723CC1C19A36B88198BE071ABE |
| SSDEEP: | 393216:wmYYmBKm8Y9bzhy7yRvxRlj2D70qy0J4v:wmYYGKm8IBy8RlKD70AJ4 |
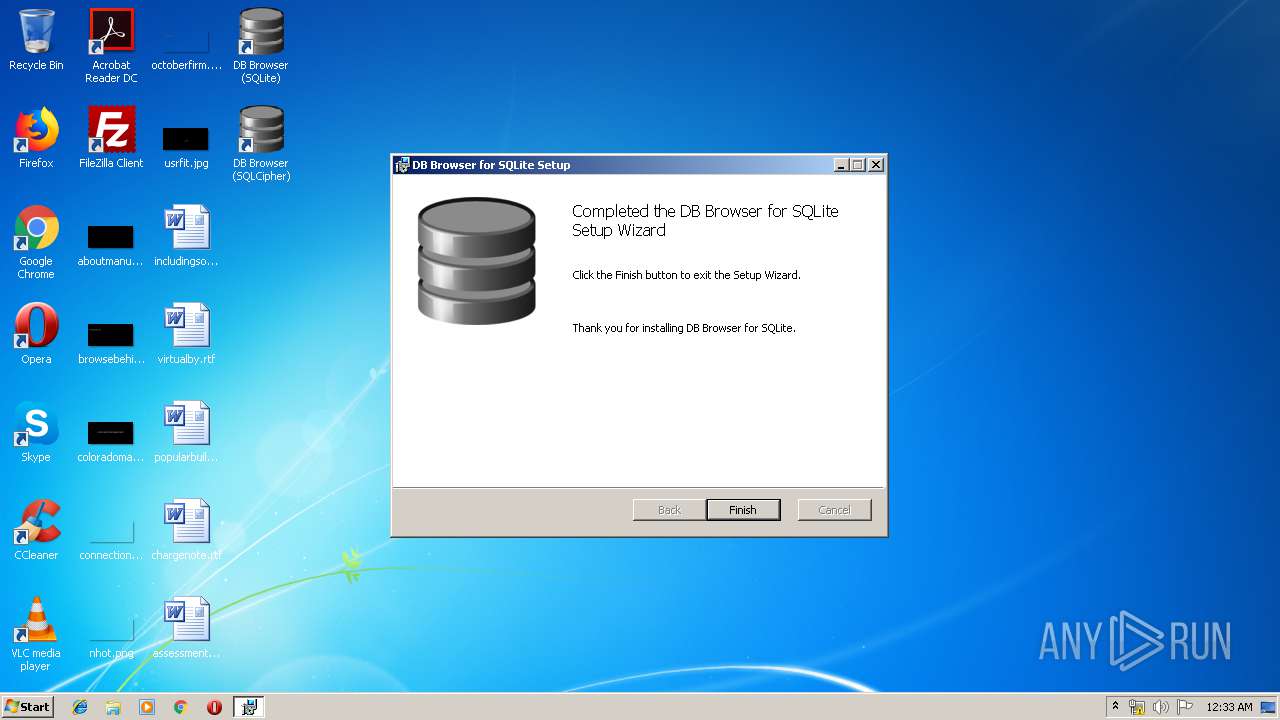
MALICIOUS
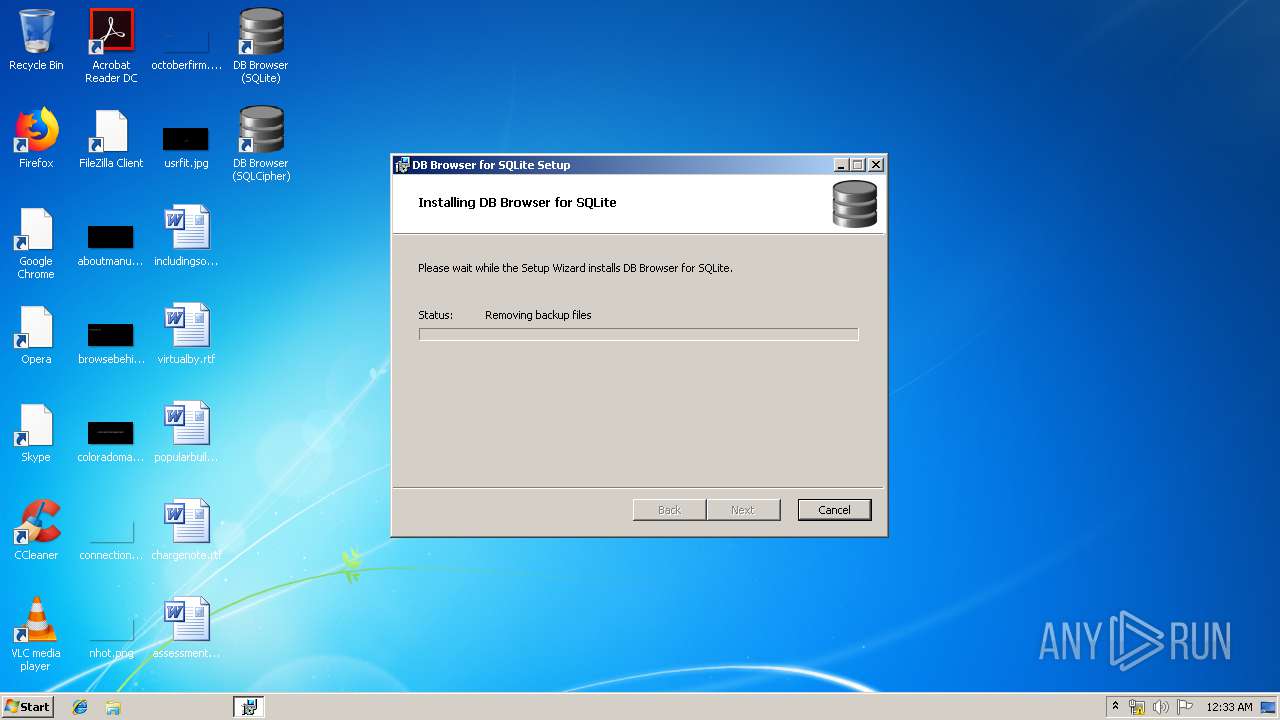
Loads dropped or rewritten executable
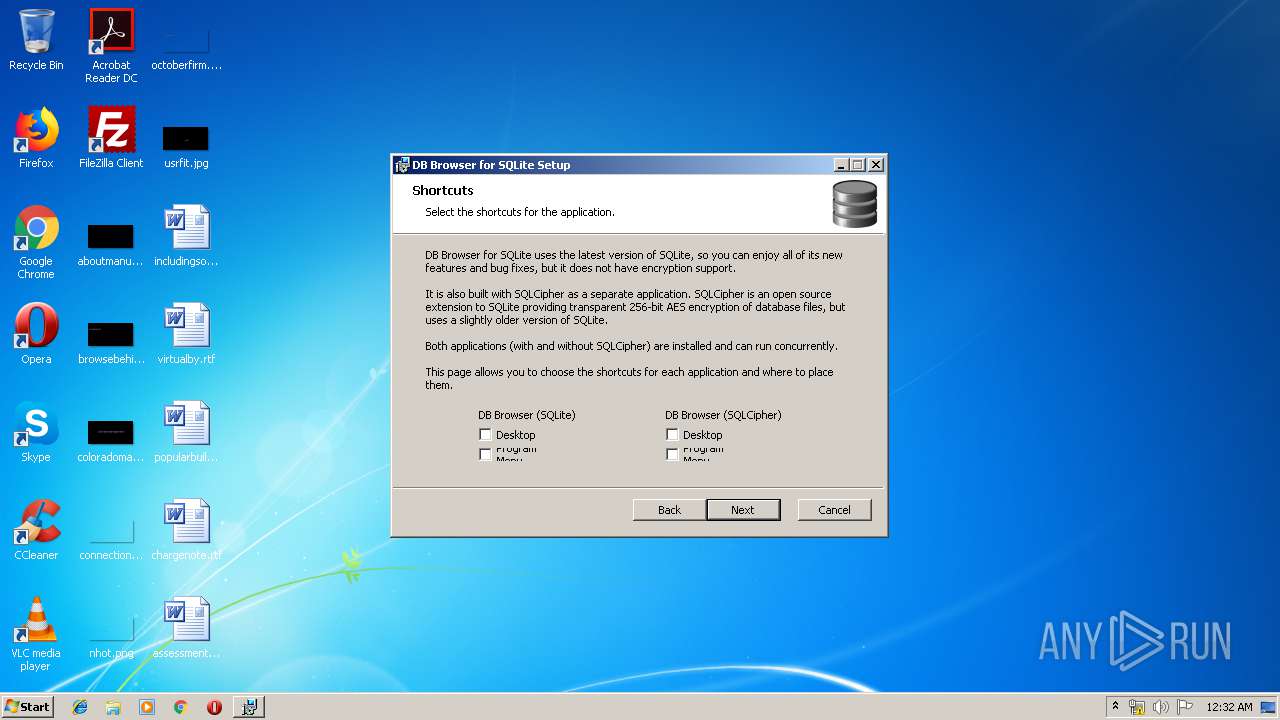
- DB Browser for SQLCipher.exe (PID: 856)
- DB Browser for SQLite.exe (PID: 2640)
Application was dropped or rewritten from another process
- DB Browser for SQLCipher.exe (PID: 856)
- DB Browser for SQLite.exe (PID: 2640)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 3172)
INFO
Searches for installed software
- msiexec.exe (PID: 3172)
Changes settings of System certificates
- DrvInst.exe (PID: 2300)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3396)
Creates a software uninstall entry
- msiexec.exe (PID: 3172)
Creates files in the program directory
- msiexec.exe (PID: 3172)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2300)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
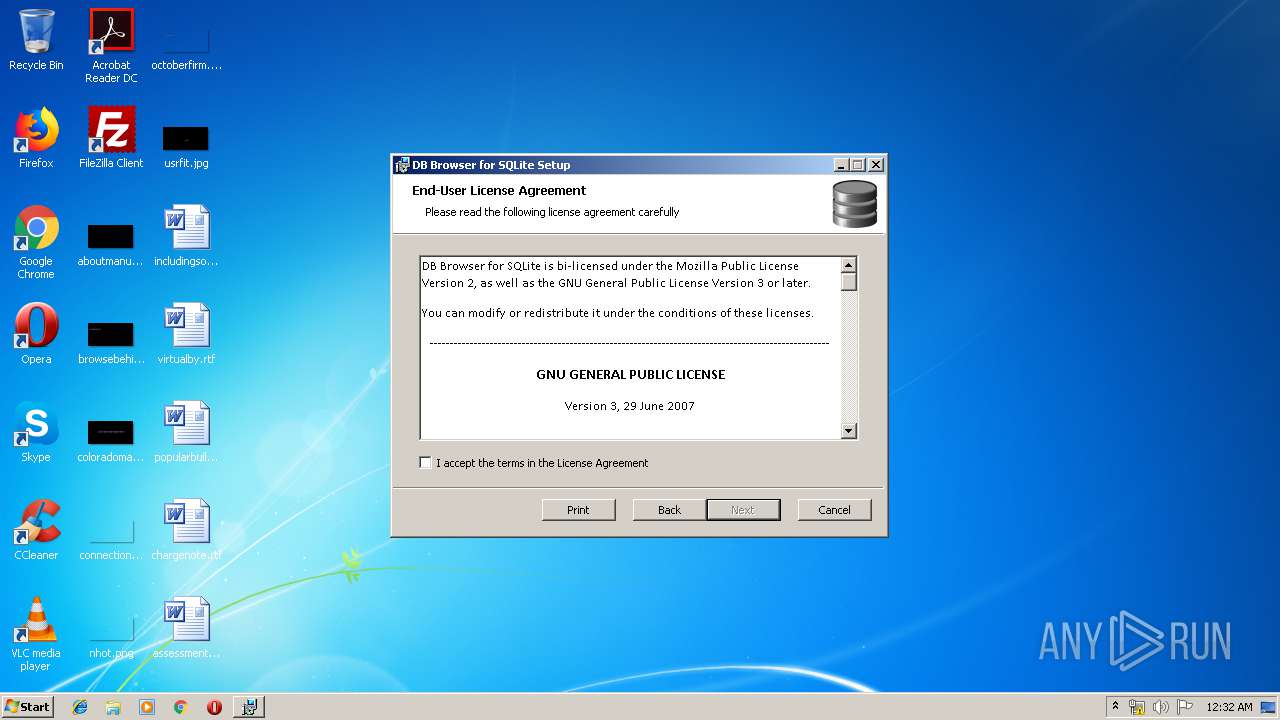
| Subject: | DB Browser for SQLite |
| Author: | DB Browser for SQLite Team |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install DB Browser for SQLite. |
| Template: | Intel;1033 |
| RevisionNumber: | {D2DE548A-7573-454E-B78E-27F0B02A1982} |
| CreateDate: | 2019:04:03 12:55:54 |
| ModifyDate: | 2019:04:03 12:55:54 |
| Pages: | 405 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.1.2318) |
| Security: | Read-only recommended |
Total processes
39
Monitored processes
6
Malicious processes
2
Suspicious processes
0
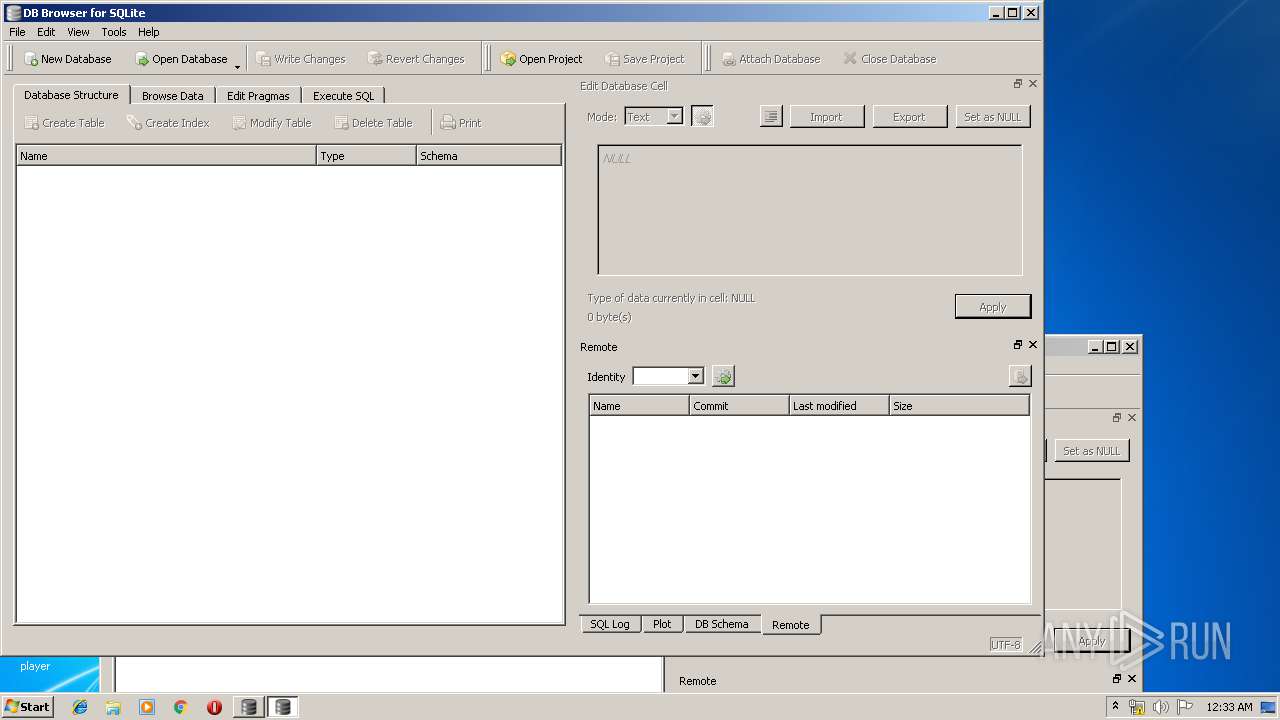
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
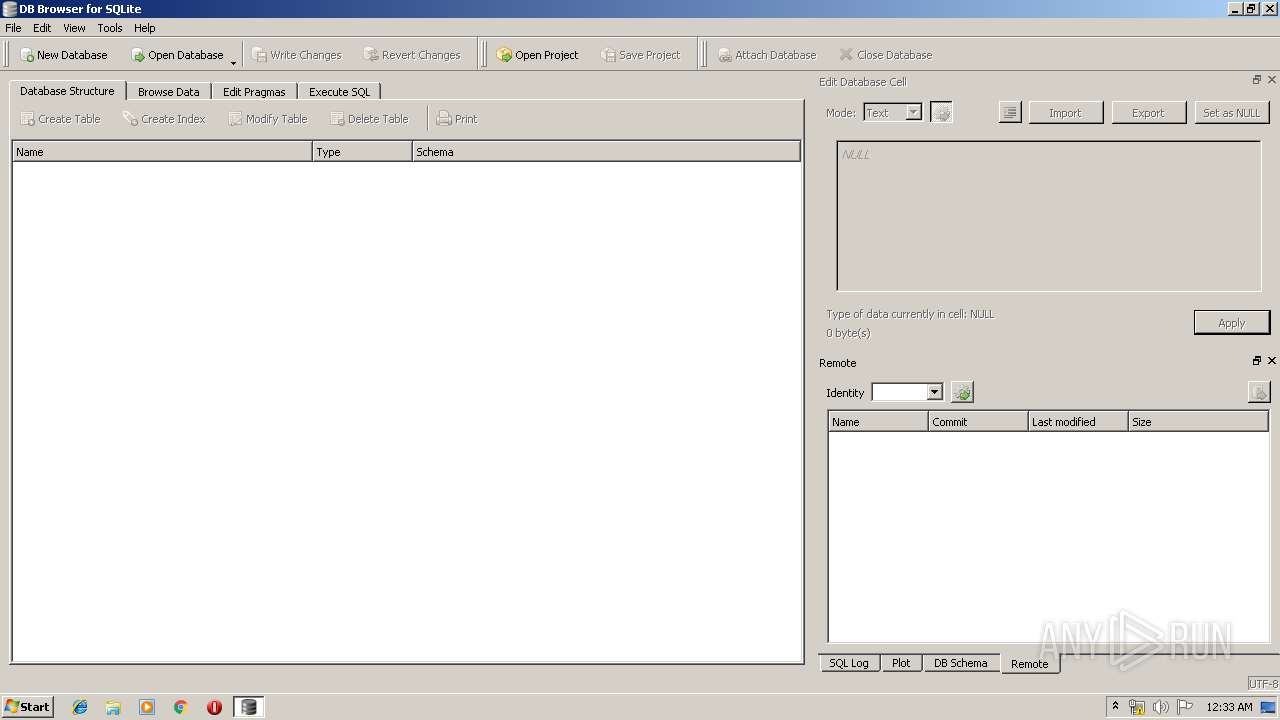
| 856 | "C:\Program Files\DB Browser for SQLite\DB Browser for SQLCipher.exe" | C:\Program Files\DB Browser for SQLite\DB Browser for SQLCipher.exe | — | explorer.exe | |||||||||||
User: admin Company: DB Browser for SQLite Team Integrity Level: MEDIUM Description: DB Browser for SQLite Exit code: 0 Version: 3.11.2.20190403 Modules
| |||||||||||||||
| 1380 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\DB.Browser.for.SQLite-3.11.2-win32.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000004C0" "000004AC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | "C:\Program Files\DB Browser for SQLite\DB Browser for SQLite.exe" | C:\Program Files\DB Browser for SQLite\DB Browser for SQLite.exe | explorer.exe | ||||||||||||
User: admin Company: DB Browser for SQLite Team Integrity Level: MEDIUM Description: DB Browser for SQLite Exit code: 0 Version: 3.11.2.20190403 Modules
| |||||||||||||||
| 3172 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3396 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 145
Read events
722
Write events
411
Delete events
12
Modification events
| (PID) Process: | (1380) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000400579B28807D501640C0000C4060000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000009A677BB28807D501640C0000C4060000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (3172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000088FFF4B28807D501640C0000C4060000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E261F7B28807D501640C0000A0050000E8030000010000000000000000000000D9C84F1D01804244945D60A90DF2D02B0000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FEAF05B38807D501440D0000DC080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FEAF05B38807D501440D0000780C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FEAF05B38807D501440D000068060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FEAF05B38807D501440D0000D40C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
29
Suspicious files
12
Text files
79
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1380 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab8A0B.tmp | — | |
MD5:— | SHA256:— | |||
| 1380 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar8A0C.tmp | — | |
MD5:— | SHA256:— | |||
| 1380 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab8A2D.tmp | — | |
MD5:— | SHA256:— | |||
| 1380 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar8A2E.tmp | — | |
MD5:— | SHA256:— | |||
| 1380 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab8AAC.tmp | — | |
MD5:— | SHA256:— | |||
| 1380 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar8AAD.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3172 | msiexec.exe | C:\Windows\Installer\efd67.msi | — | |
MD5:— | SHA256:— | |||
| 3172 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFB8361DA0B910C961.TMP | — | |
MD5:— | SHA256:— | |||
| 3396 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1380 | msiexec.exe | GET | 200 | 23.111.11.204:80 | http://repository.certum.pl/ctnca.cer | US | der | 959 b | whitelisted |
1380 | msiexec.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | DB Browser for SQLite.exe | 163.172.139.109:443 | download.sqlitebrowser.org | Online S.a.s. | FR | unknown |
1380 | msiexec.exe | 23.111.11.204:80 | repository.certum.pl | netDNA | US | unknown |
1380 | msiexec.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
repository.certum.pl |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
download.sqlitebrowser.org |
| unknown |