| File name: | N_06182019.doc |
| Full analysis: | https://app.any.run/tasks/59988760-5f4d-4682-a73f-4c181ff33a05 |
| Verdict: | Malicious activity |
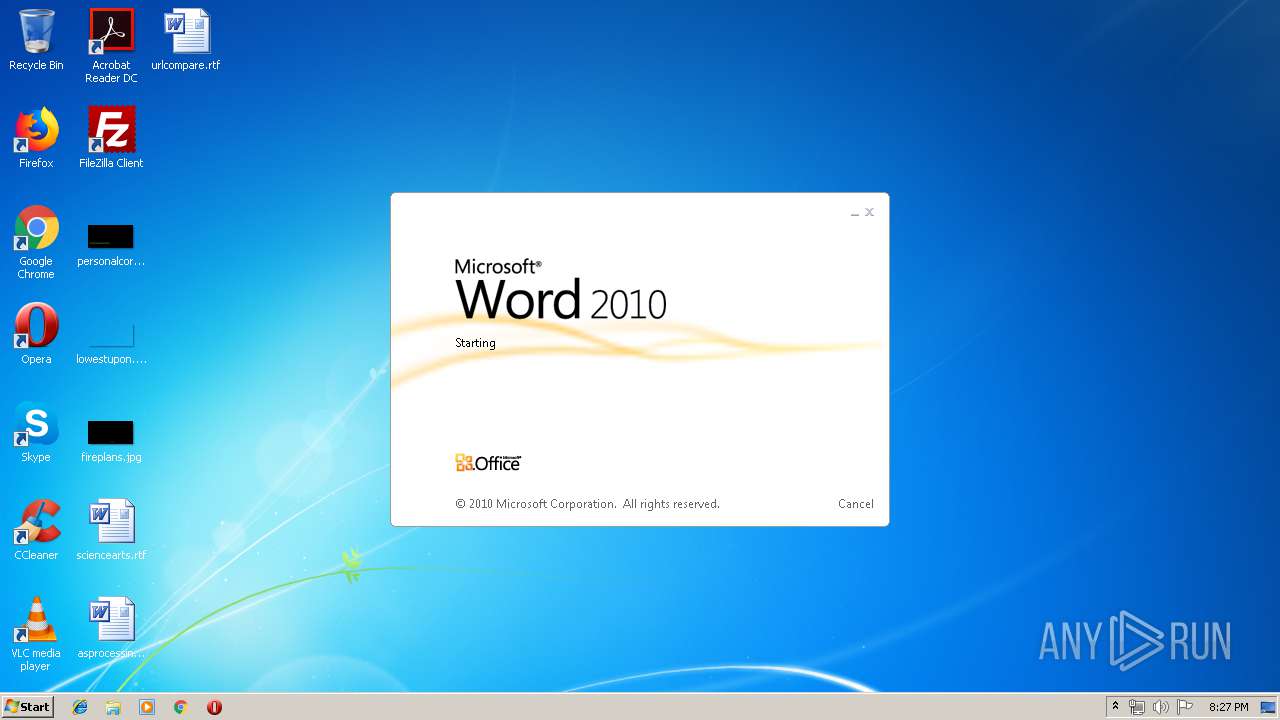
| Analysis date: | June 18, 2019, 19:27:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
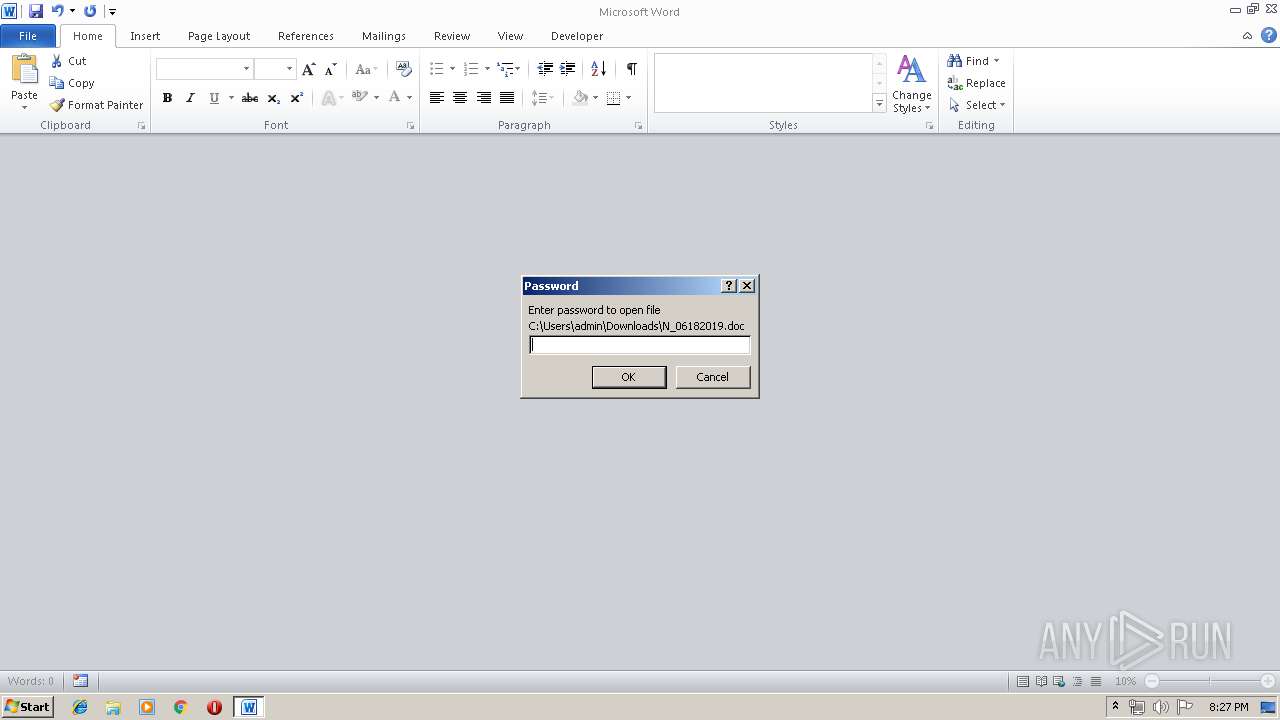
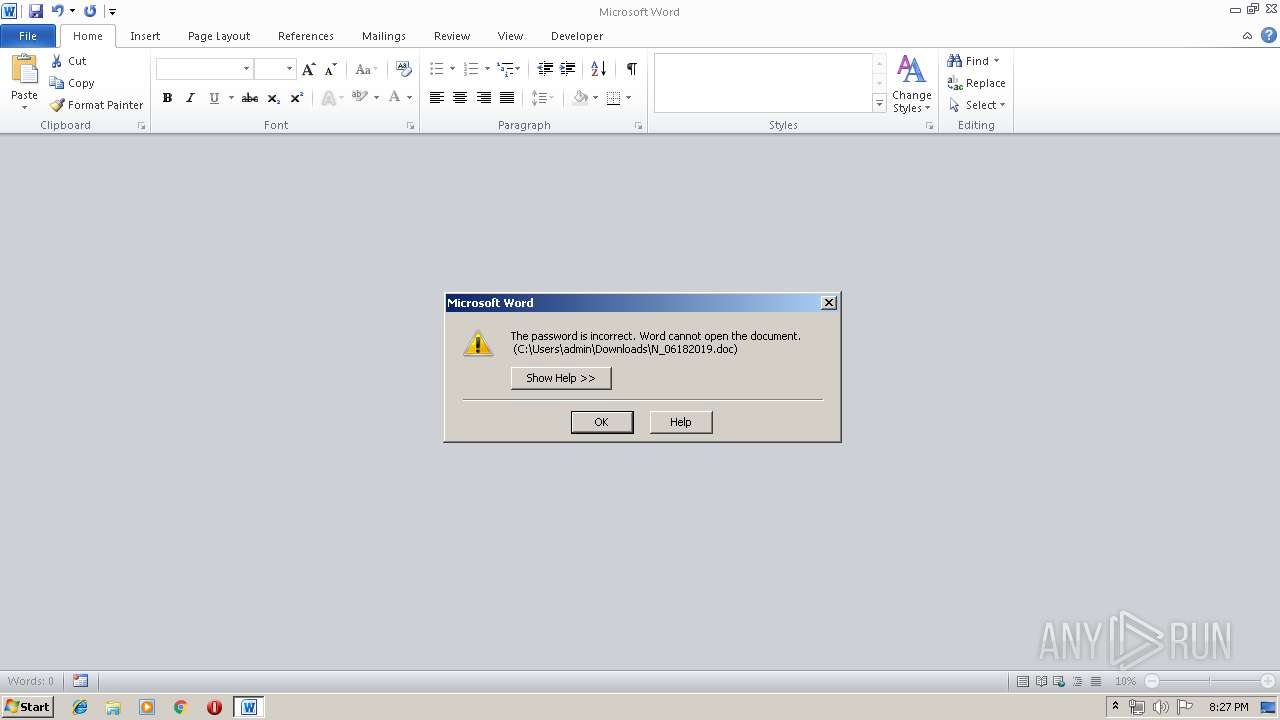
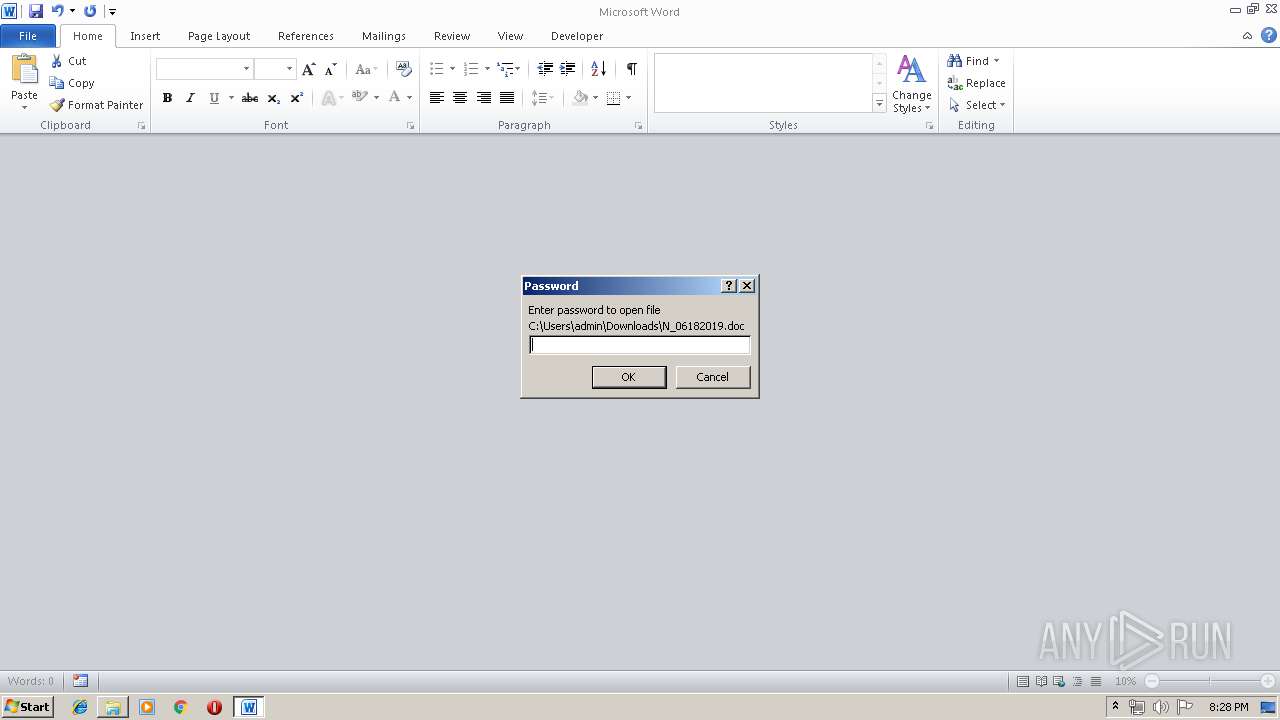
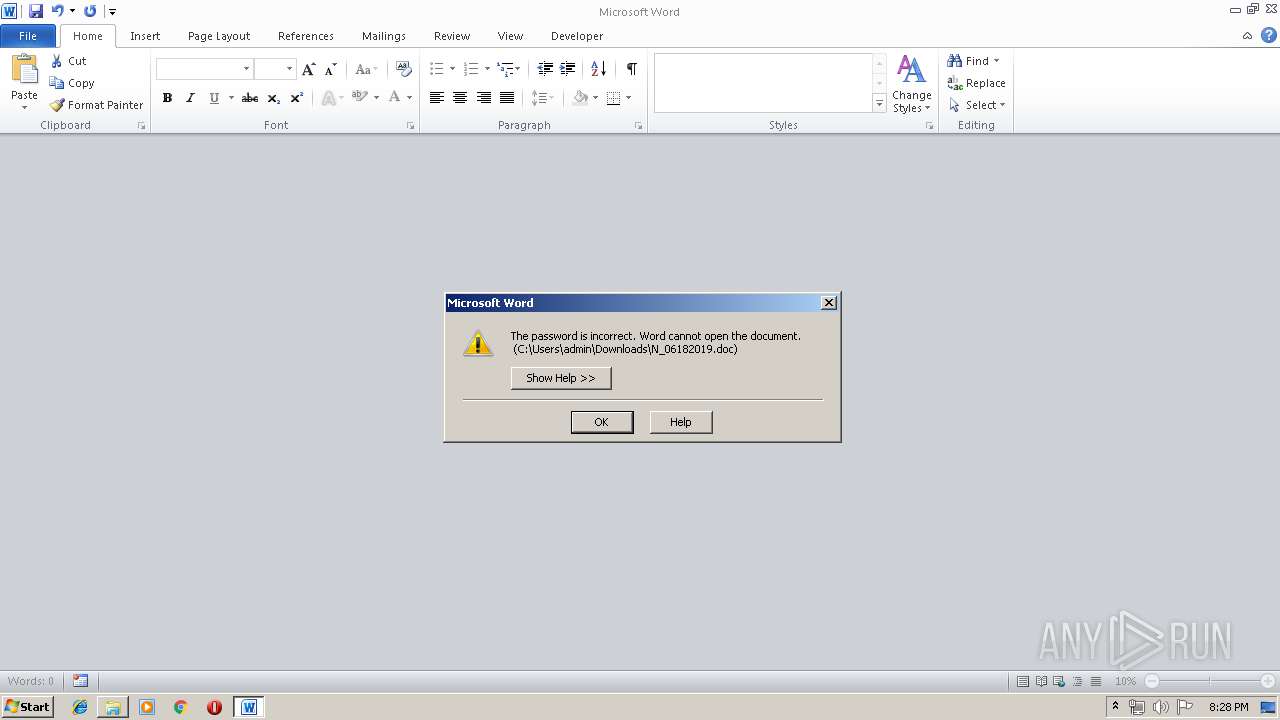
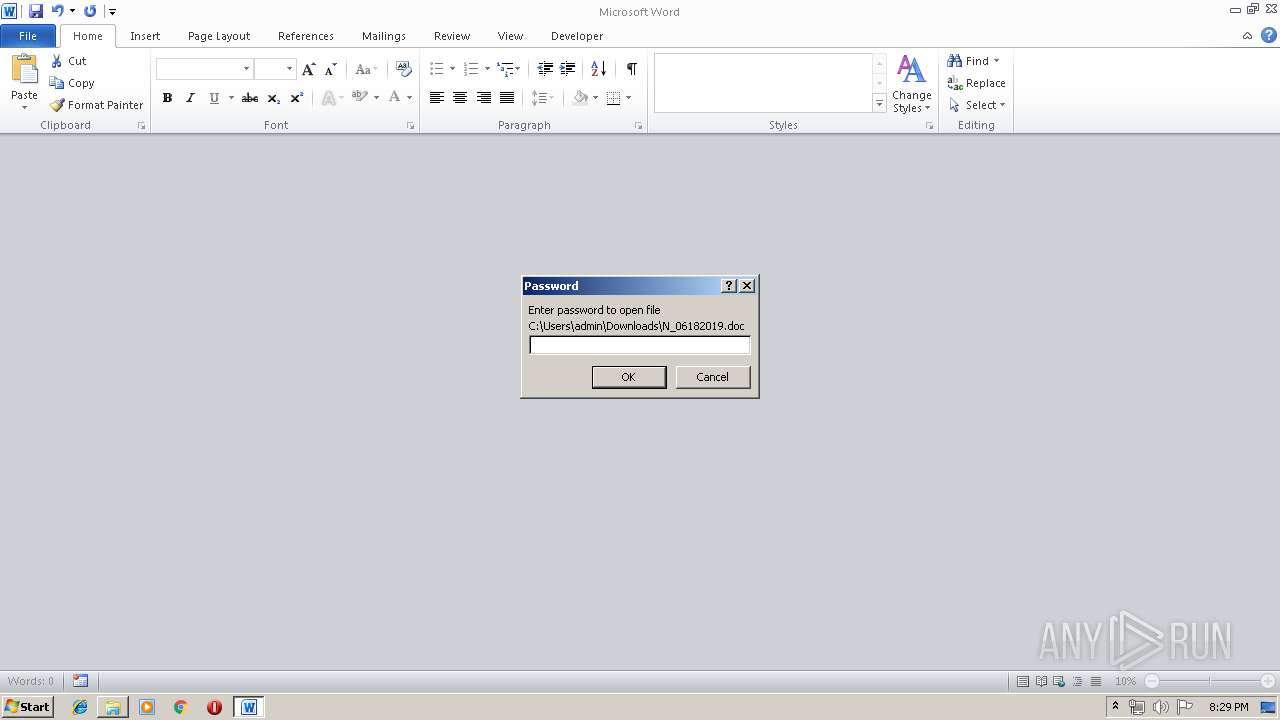
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | EA151D0A1534D19C096395892FD07C73 |
| SHA1: | B860BDAA94DA1A129B8B527E1362118293FB2BEA |
| SHA256: | 0A588FFE984C4C5FB76EB7C0FAC4747928DA26BB48FB94FC4BC79D9FD3B0DB68 |
| SSDEEP: | 1536:Ki8TDG58In7EwXX0FNi/u1eMFoVbjHRYAsYPdV:b8TQ8Sow0FNl4MCV/HmAhPdV |
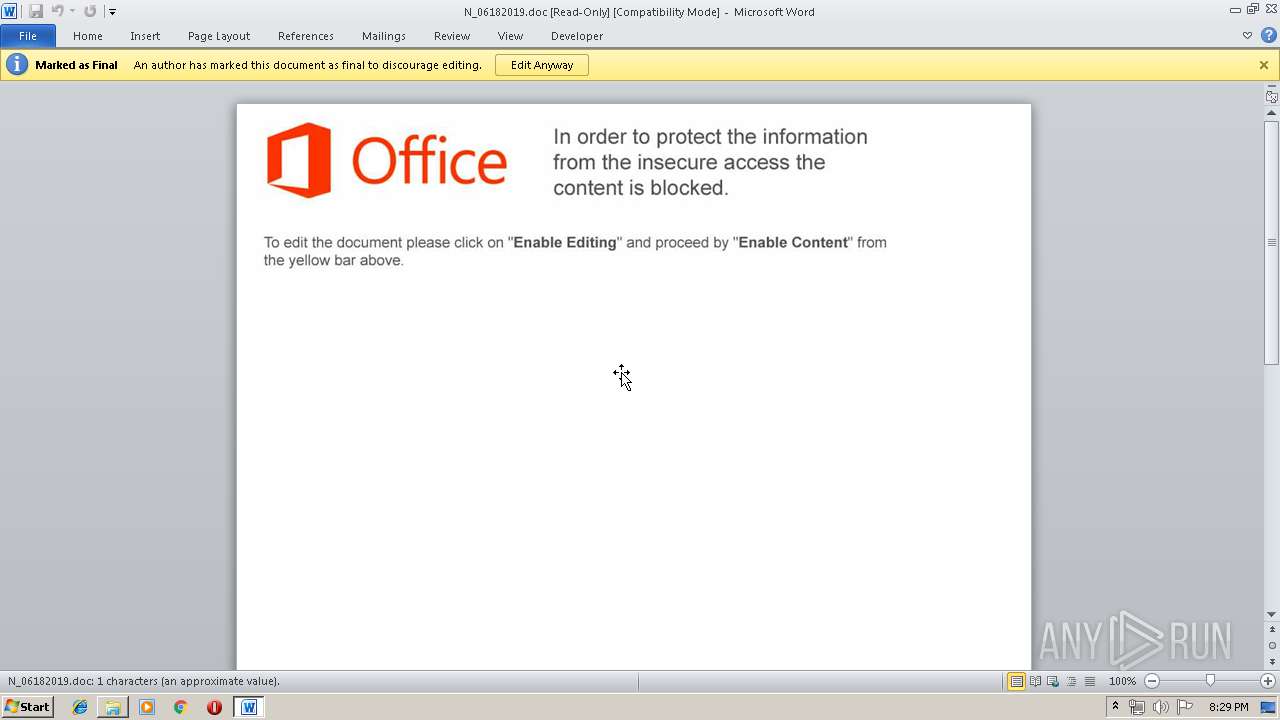
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3648)
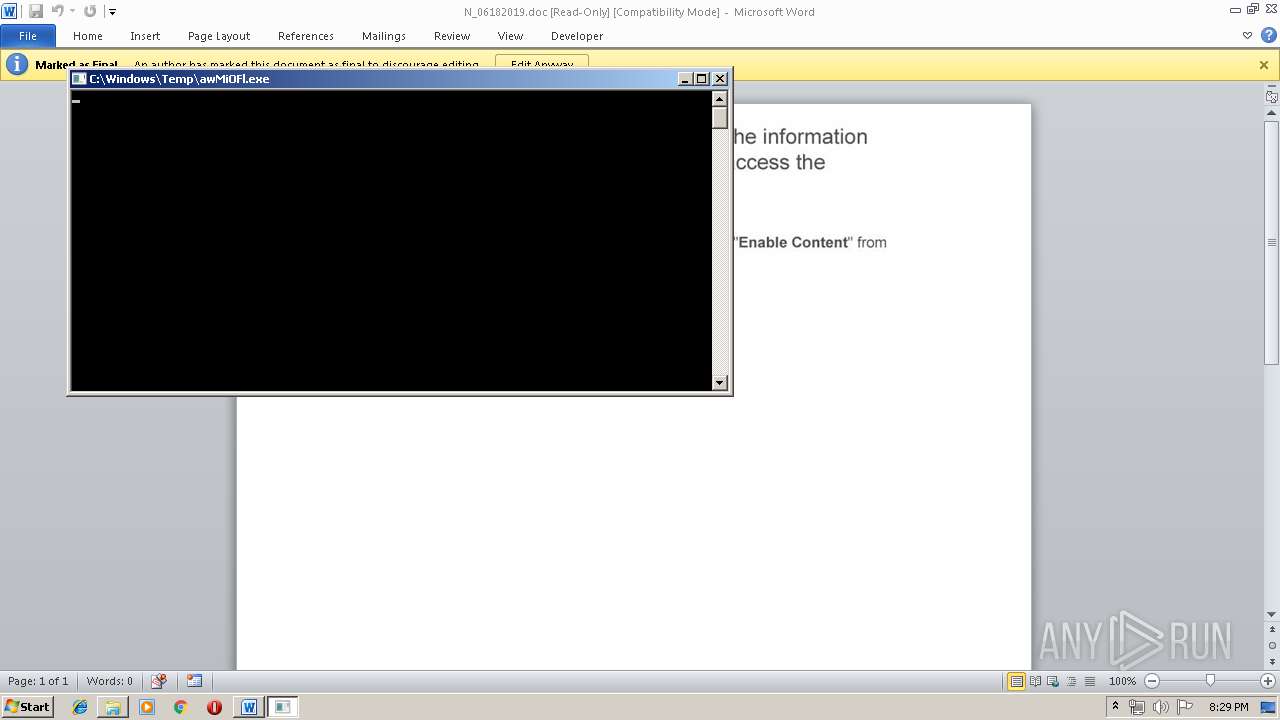
Application was dropped or rewritten from another process
- awMiOFl.exe (PID: 2204)
SUSPICIOUS
Creates files in the Windows directory
- wmic.exe (PID: 3496)
- WINWORD.EXE (PID: 3648)
Executable content was dropped or overwritten
- wmic.exe (PID: 3496)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1832)
- WINWORD.EXE (PID: 3648)
- WINWORD.EXE (PID: 2592)
Creates files in the user directory
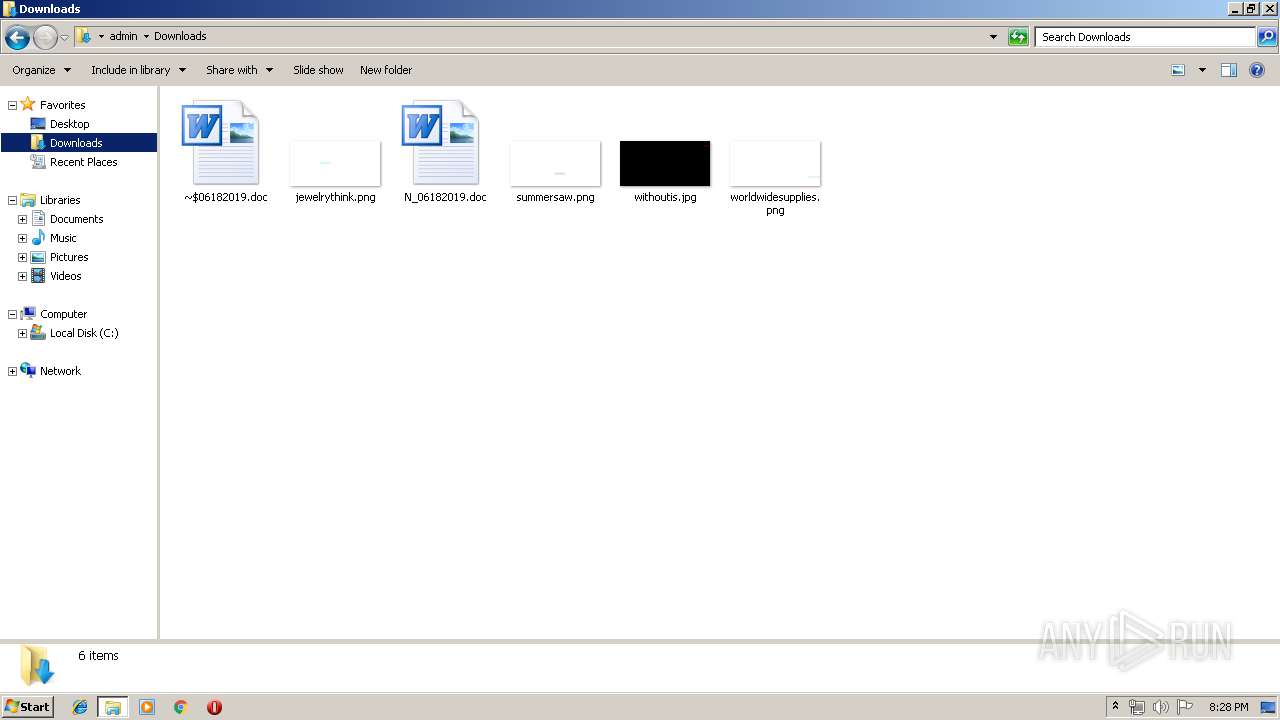
- WINWORD.EXE (PID: 1832)
- WINWORD.EXE (PID: 3648)
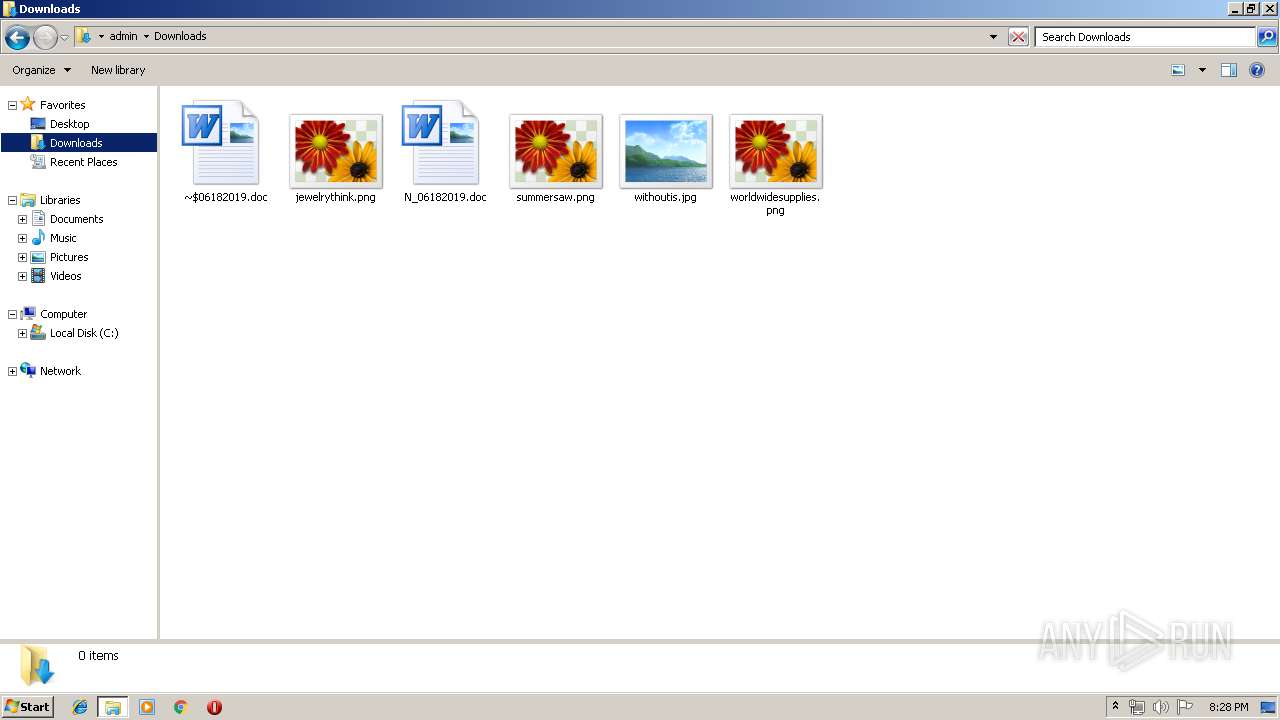
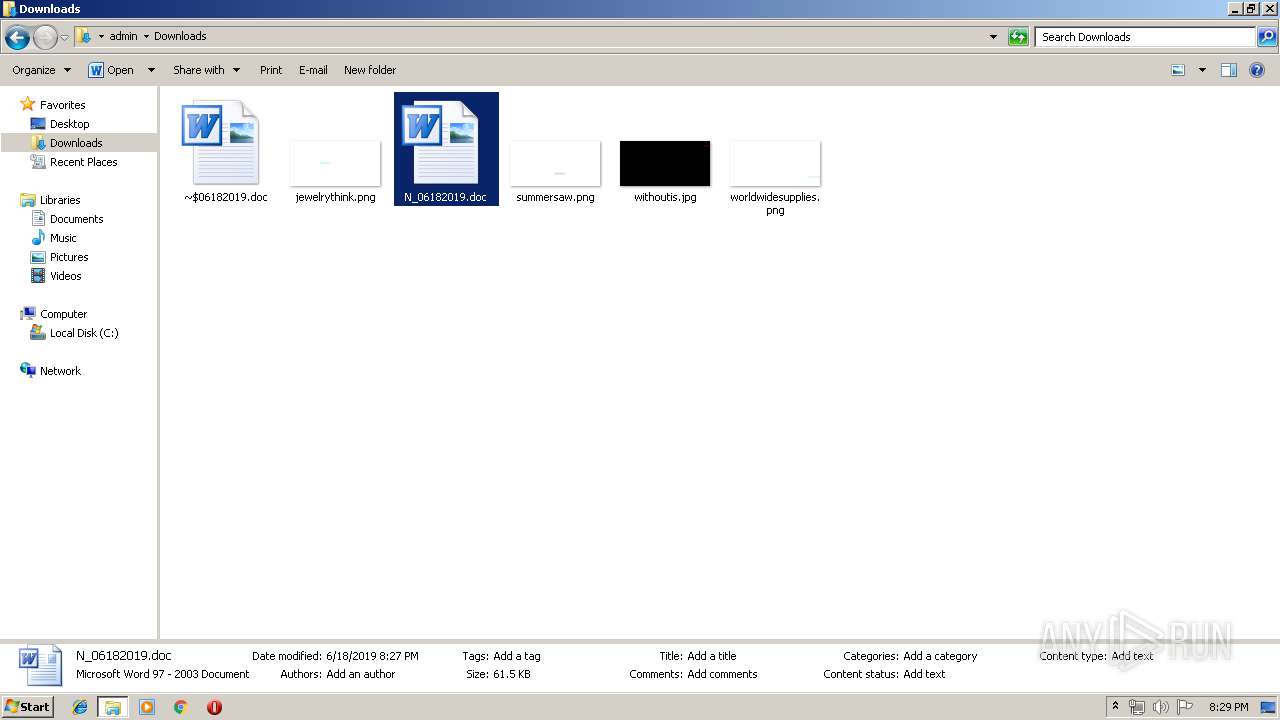
Manual execution by user
- explorer.exe (PID: 3796)
- WINWORD.EXE (PID: 2592)
- WINWORD.EXE (PID: 3648)
Dropped object may contain Bitcoin addresses
- wmic.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1832 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\N_06182019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2204 | "C:\Windows\Temp\awMiOFl.exe" | C:\Windows\Temp\awMiOFl.exe | wmic.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\N_06182019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3496 | wmic os get /format:"C:\\Windows\\Temp\\aXwZvnt48.xsl" | C:\Windows\System32\Wbem\wmic.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147614729 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3648 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\N_06182019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3796 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 918
Read events
1 856
Write events
1 043
Delete events
19
Modification events
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :w4 |
Value: 3A77340028070000010000000000000000000000 | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322385438 | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322385552 | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322385553 | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 28070000389619DD0B26D50100000000 | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | tx4 |
Value: 747834002807000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | tx4 |
Value: 747834002807000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF3A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFEDE17D4487F0997D.TMP | — | |
MD5:— | SHA256:— | |||
| 1832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF43217ED7272DEE71.TMP | — | |
MD5:— | SHA256:— | |||
| 1832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCA8E75CE43C25BD0.TMP | — | |
MD5:— | SHA256:— | |||
| 1832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF979396139F0125E0.TMP | — | |
MD5:— | SHA256:— | |||
| 1832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFBA0B35CC3D489536.TMP | — | |
MD5:— | SHA256:— | |||
| 1832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{668387D4-429F-4467-8365-EDE674F7C444}.tmp | — | |
MD5:— | SHA256:— | |||
| 2592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF95C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9C8688BE5820B099.TMP | — | |
MD5:— | SHA256:— | |||
| 2592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD568A52C29F7F113.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3496 | wmic.exe | 49.51.12.195:443 | tor2net.com | Tencent Building, Kejizhongyi Avenue | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tor2net.com |
| malicious |
Threats
Process | Message |
|---|---|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|