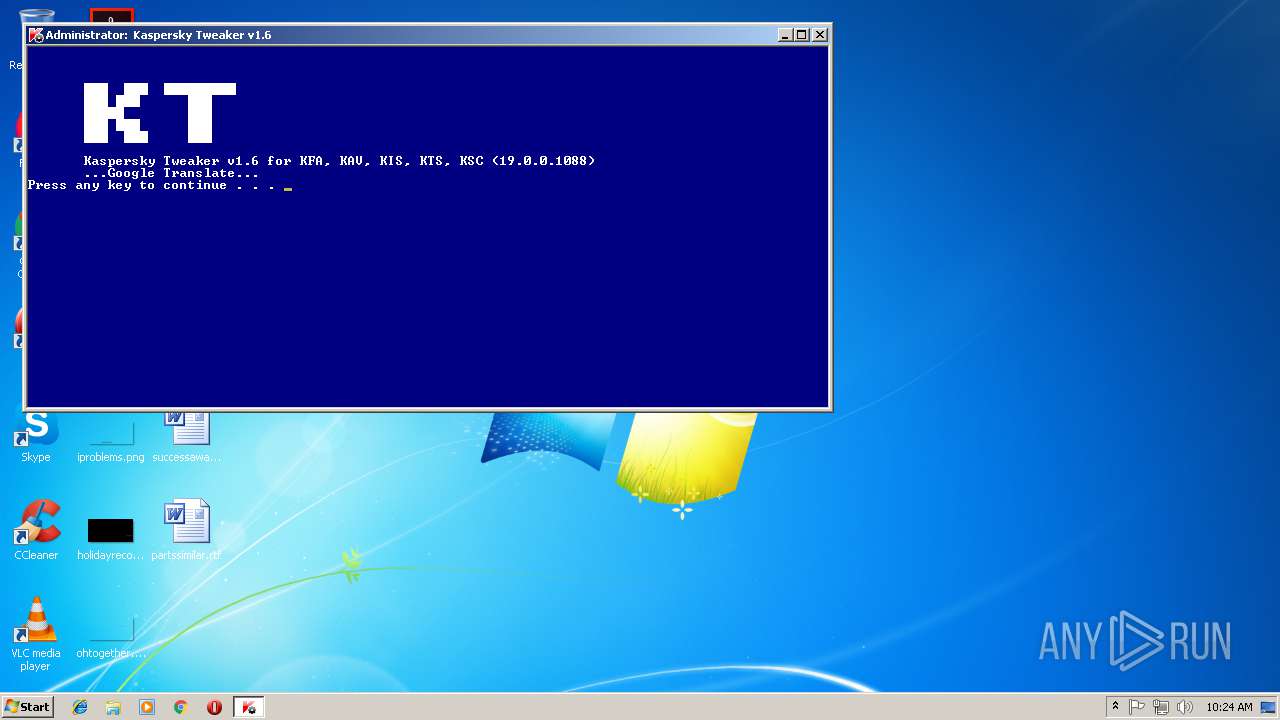
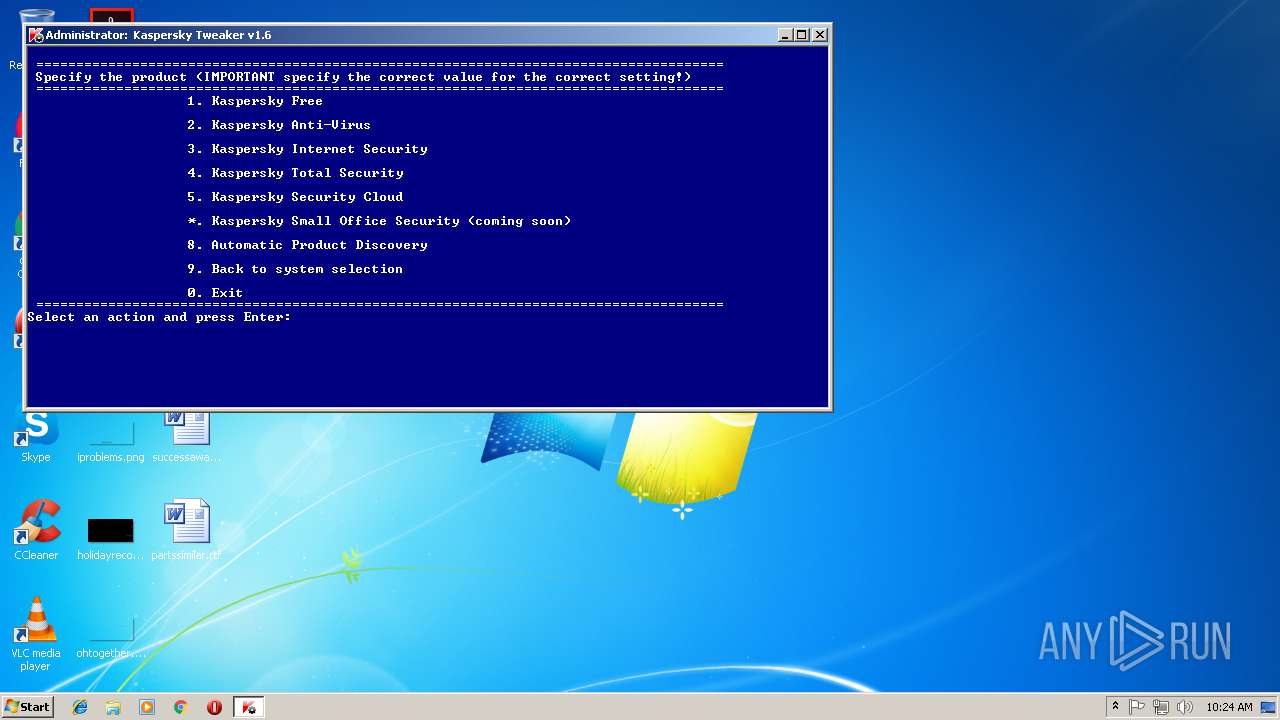
| File name: | Kaspersky Tweaker v1.6 (en).exe |
| Full analysis: | https://app.any.run/tasks/793c9889-c1e8-41f7-9b96-758ff15455d6 |
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2018, 10:24:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | DEC4C2B81FCFF62A61D6D24D99F735CE |
| SHA1: | 265CD8816FCE1CD020D718717FDFD8668605FAD6 |
| SHA256: | 0A51BA4BDF4C57FB680CEDEBAA9B6CC1EE806A001273C8D6E8DD665BFF20DE19 |
| SSDEEP: | 98304:pySv8eXyr9fk3Ar5P/TTPYzMrcVEzdZNte9BpQdQ8h:pyMJq5iArRPgzMTaeb |
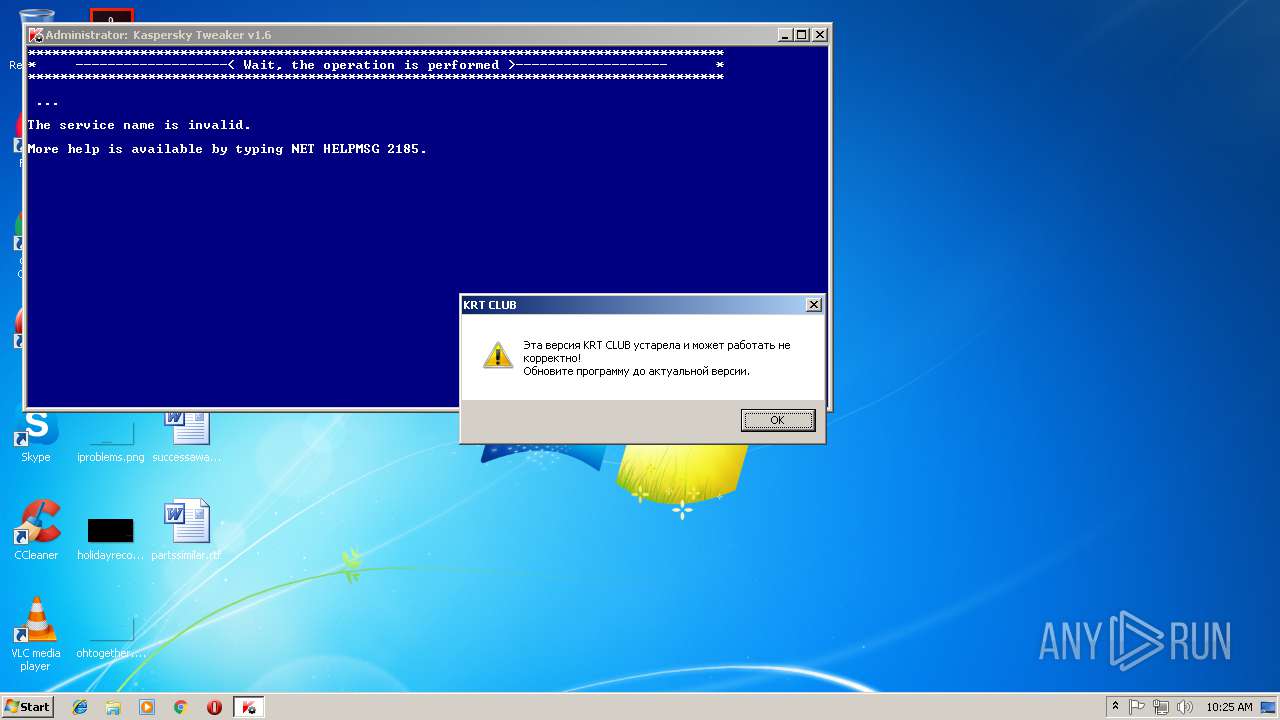
MALICIOUS
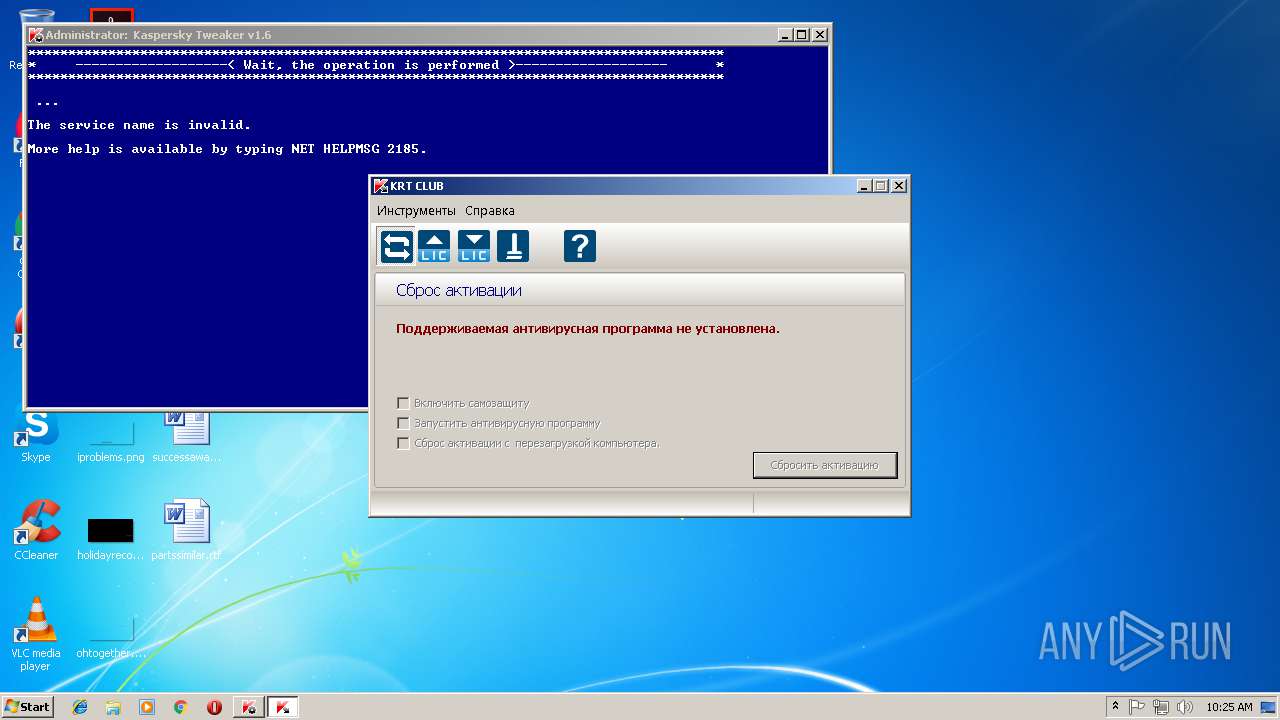
Application was dropped or rewritten from another process
- KRT.exe (PID: 3224)
- KRT.sfx.exe (PID: 4068)
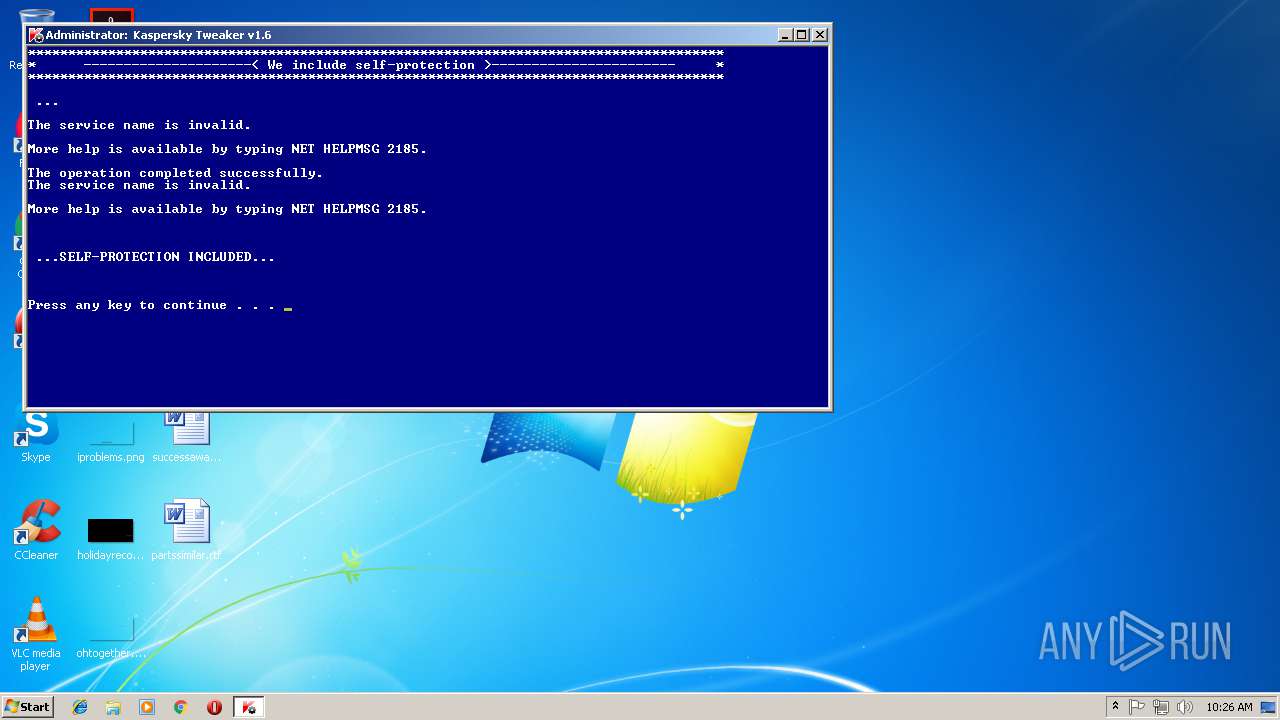
Starts NET.EXE for service management
- cmd.exe (PID: 3436)
SUSPICIOUS
Executable content was dropped or overwritten
- Kaspersky Tweaker v1.6 (en).exe (PID: 1460)
- KRT.exe (PID: 3224)
- KRT.sfx.exe (PID: 4068)
Starts CMD.EXE for commands execution
- Kaspersky Tweaker v1.6 (en).exe (PID: 1460)
Starts application with an unusual extension
- cmd.exe (PID: 3436)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3436)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (30.9) |
| .scr | | | Windows screen saver (14.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:01:18 11:10:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 61440 |
| InitializedDataSize: | 6020608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 18-Jan-2017 10:10:31 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Jan-2017 10:10:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x000035B7 | 0x00003600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.26514 |
.text | 0x00005000 | 0x0000B8BB | 0x0000BA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57376 |
.rdata | 0x00011000 | 0x0000098E | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.61645 |
.data | 0x00012000 | 0x00001C58 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.51695 |
.rsrc | 0x00014000 | 0x005BBE00 | 0x005BBE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.64688 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.06268 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.00088 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.8114 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.67353 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.82334 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.99472 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 3.91196 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.31648 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 4.48342 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
Total processes
49
Monitored processes
16
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | net stop AVP19.0.0 | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | net stop AVP19.0.0 | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1460 | "C:\Users\admin\AppData\Local\Temp\Kaspersky Tweaker v1.6 (en).exe" | C:\Users\admin\AppData\Local\Temp\Kaspersky Tweaker v1.6 (en).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 1736 | REG ADD HKEY_LOCAL_MACHINE\SOFTWARE\KasperskyLab\AVP19.0.0\Data\UCPRegistrationAlert /v lastEventTime /t REG_QWORD /d 18446744073709551615 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | REG ADD HKEY_LOCAL_MACHINE\SOFTWARE\KasperskyLab\AVP19.0.0\settings /v EnableSelfProtection /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2232 | REG ADD HKEY_LOCAL_MACHINE\SOFTWARE\KasperskyLab\AVP19.0.0\Data\UCPRegistrationAlert /v state /t REG_DWORD /d 4294967295 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2292 | C:\Windows\system32\net1 stop AVP19.0.0 | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2484 | C:\Windows\system32\net1 start AVP19.0.0 | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\KRT.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\KRT.exe | KRT.sfx.exe | ||||||||||||
User: admin Company: Collective Intelligence and ML Integrity Level: HIGH Exit code: 0 Version: 2.0.0.35 Modules
| |||||||||||||||
| 3228 | chcp 866 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
373
Read events
366
Write events
7
Delete events
0
Modification events
| (PID) Process: | (4068) KRT.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4068) KRT.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2232) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\KasperskyLab\AVP19.0.0\Data\UCPRegistrationAlert |
| Operation: | write | Name: | state |
Value: 4294967295 | |||
| (PID) Process: | (1736) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\KasperskyLab\AVP19.0.0\Data\UCPRegistrationAlert |
| Operation: | write | Name: | lastEventTime |
Value: FFFFFFFFFFFFFFFF | |||
| (PID) Process: | (2108) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\KasperskyLab\AVP19.0.0\settings |
| Operation: | write | Name: | EnableSelfProtection |
Value: 1 | |||
Executable files
4
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | KRT.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KRT_CLUB.ini | — | |
MD5:— | SHA256:— | |||
| 1460 | Kaspersky Tweaker v1.6 (en).exe | C:\Users\admin\AppData\Local\Temp\B32E.tmp\reset_skin.rar | compressed | |
MD5:— | SHA256:— | |||
| 4068 | KRT.sfx.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KRT.exe | executable | |
MD5:— | SHA256:— | |||
| 1460 | Kaspersky Tweaker v1.6 (en).exe | C:\Users\admin\AppData\Local\Temp\B32E.tmp\red_k.rar | compressed | |
MD5:— | SHA256:— | |||
| 1460 | Kaspersky Tweaker v1.6 (en).exe | C:\Users\admin\AppData\Local\Temp\B32E.tmp\B32F.bat | text | |
MD5:— | SHA256:— | |||
| 1460 | Kaspersky Tweaker v1.6 (en).exe | C:\Users\admin\AppData\Local\Temp\B32E.tmp\KRT.sfx.exe | executable | |
MD5:— | SHA256:— | |||
| 1460 | Kaspersky Tweaker v1.6 (en).exe | C:\Users\admin\AppData\Local\Temp\B32E.tmp\dark_skin.rar | compressed | |
MD5:— | SHA256:— | |||
| 4068 | KRT.sfx.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KRT_CLUB.ini | text | |
MD5:— | SHA256:— | |||
| 3224 | KRT.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KRT_SERVICE.exe | executable | |
MD5:— | SHA256:— | |||
| 1460 | Kaspersky Tweaker v1.6 (en).exe | C:\Users\admin\AppData\Local\Temp\B32E.tmp\rarreg.key | text | |
MD5:5842FF7DE1DFB236C5670A59129AE365 | SHA256:35BF205D0F8D6C54018ADADA52B0C6AE2A0001AD68453C785ED35999143DD7E1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report