| File name: | CVE-2017-0213_x86.exe |
| Full analysis: | https://app.any.run/tasks/be51e394-98c7-42f8-9236-41fa2cc11299 |
| Verdict: | No threats detected |
| Analysis date: | March 02, 2019, 08:10:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | E20BAED2F54AF658D546027C5F839656 |
| SHA1: | B3423B5D096CF915019CD8D7C994CF9919523901 |
| SHA256: | 0A4A0F0DF5EEA57F16A76BFF6489DD95A7089AFBA8E9E5C8BCADC46870AF33FB |
| SSDEEP: | 3072:tRKLeqLvv9kkrUWd924GBqCbnfoZw5IFXAeW8+StGwav:tpqLdfrUW+HnfoZD9X+xwm |
MALICIOUS
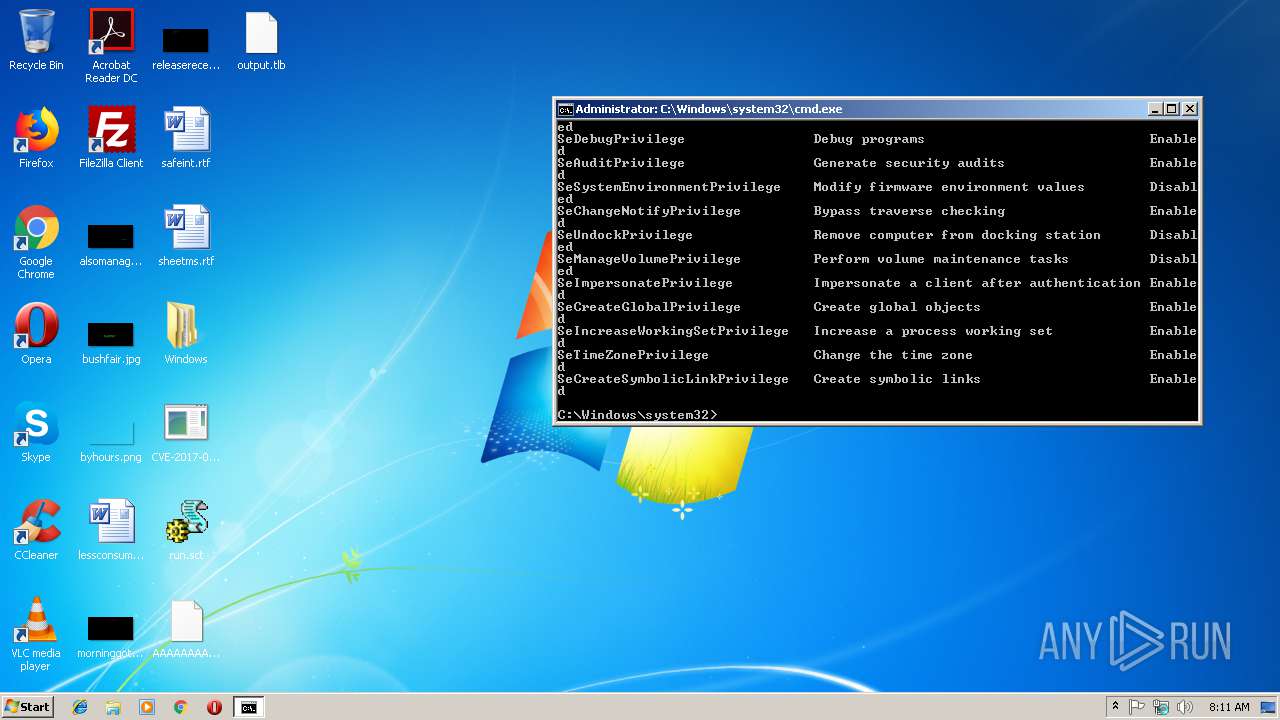
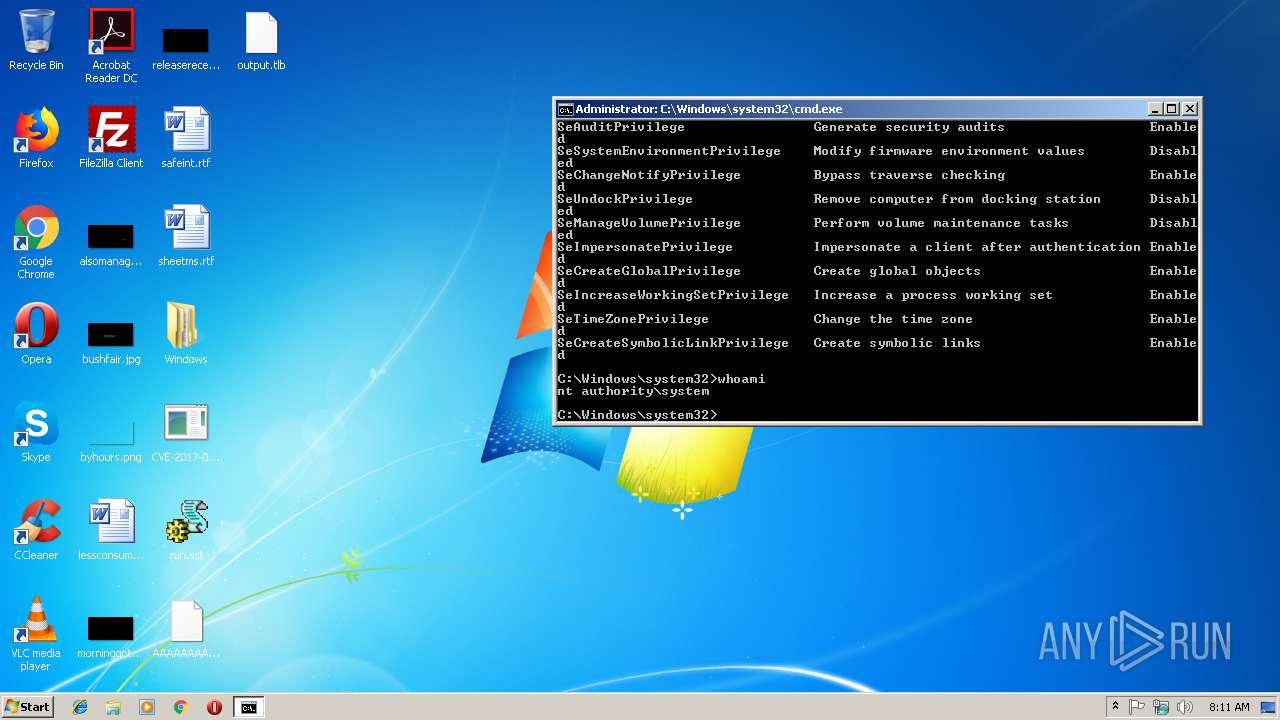
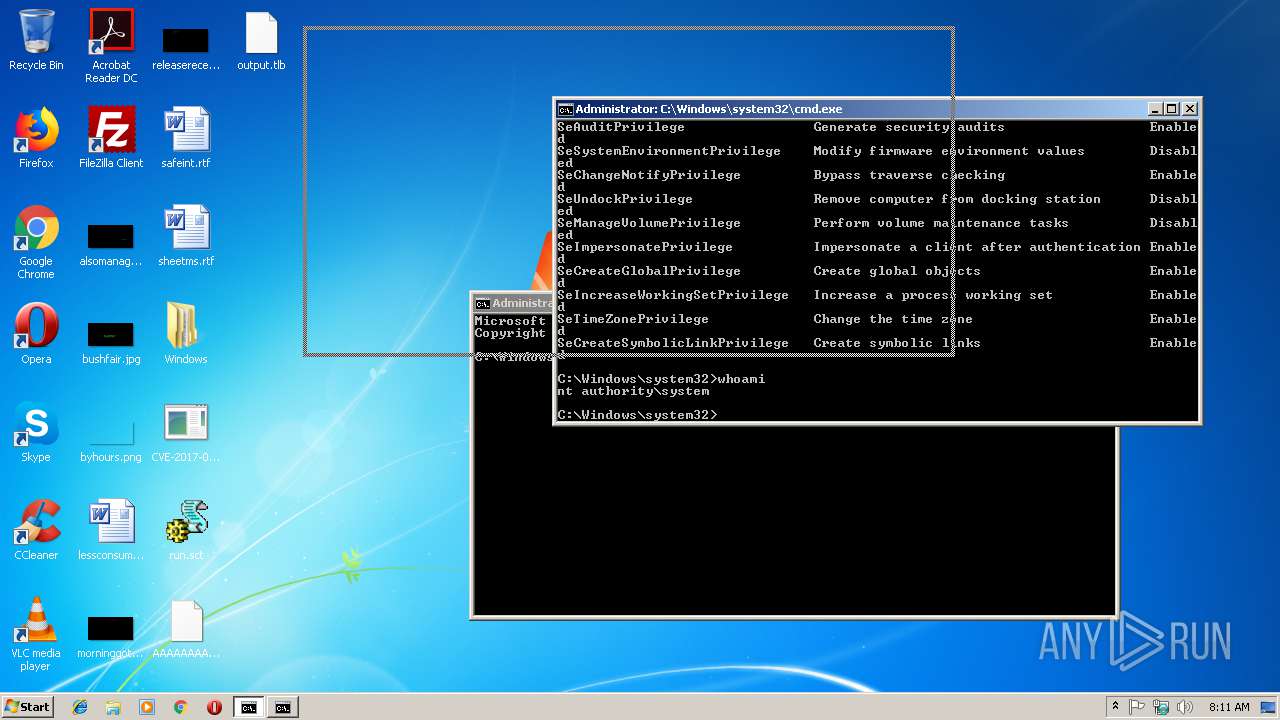
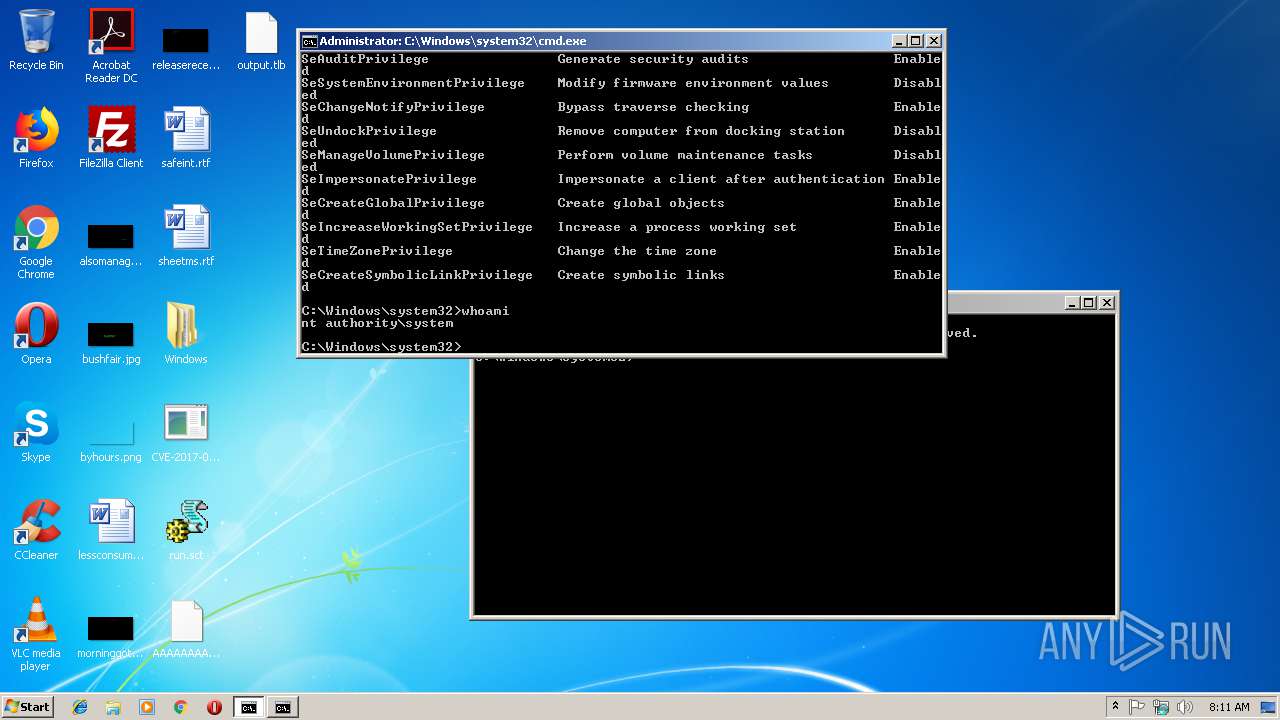
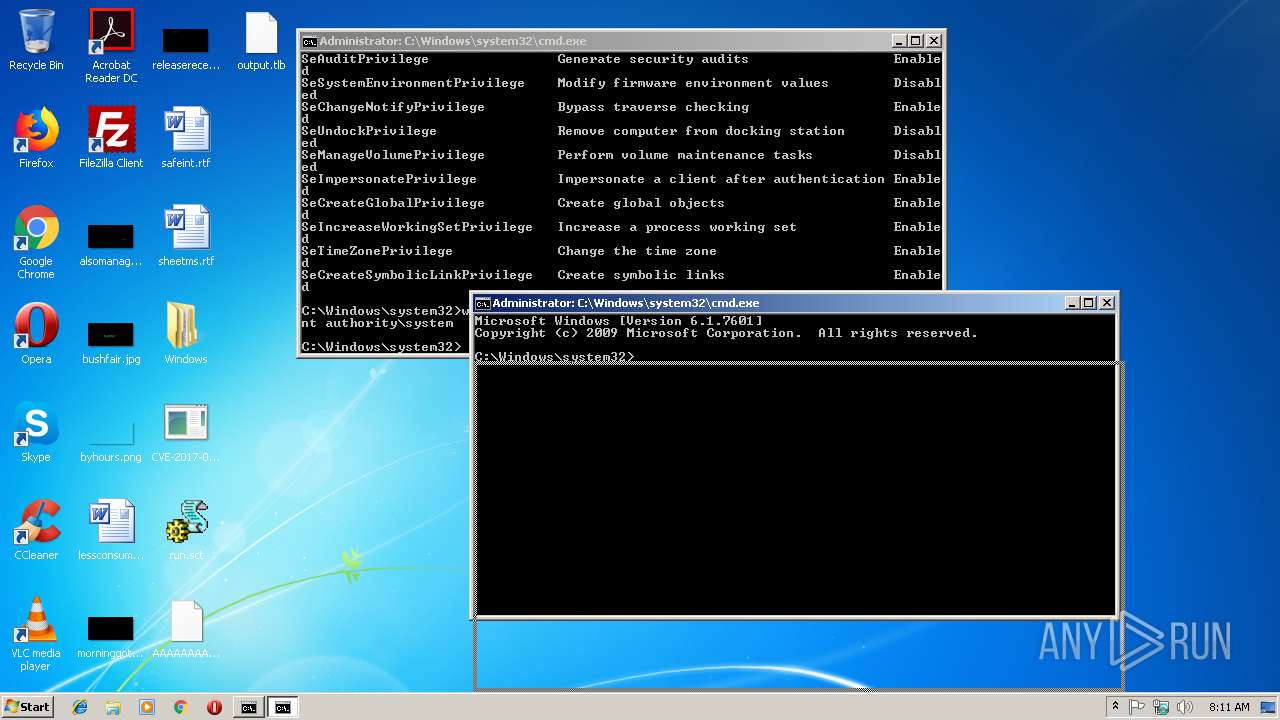
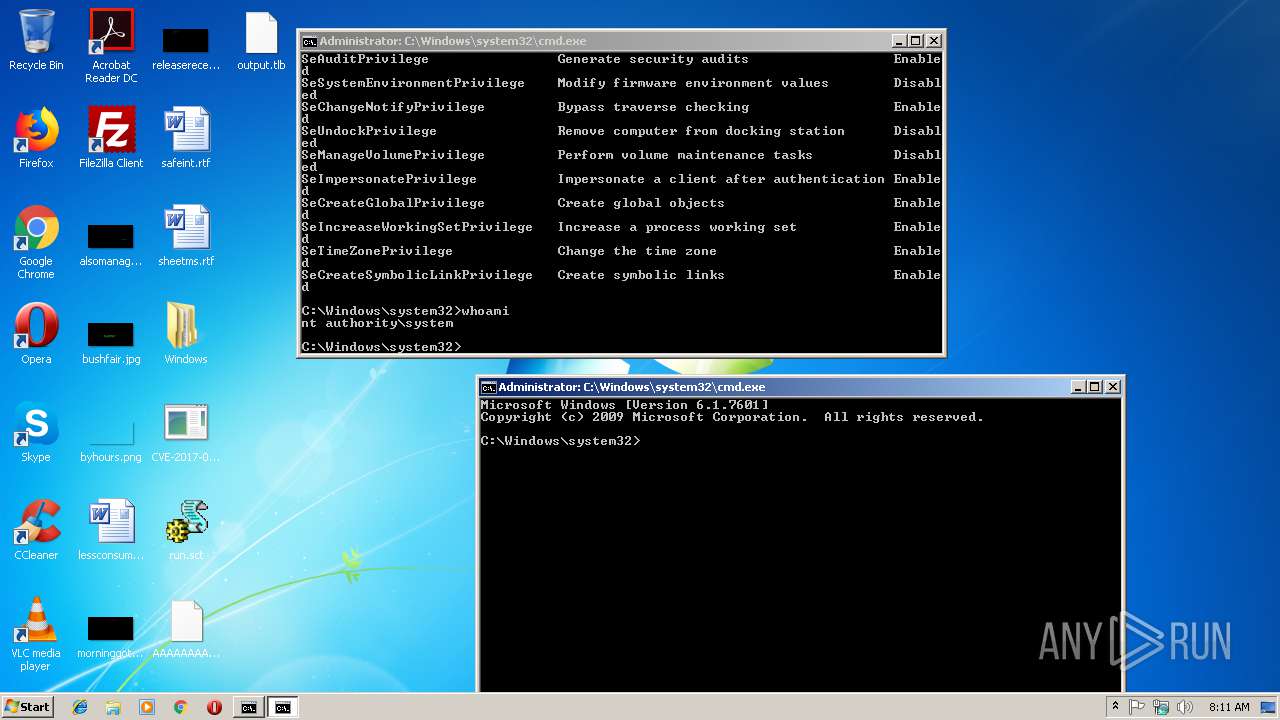
Runs app for hidden code execution
- CVE-2017-0213_x86.exe (PID: 2696)
- CVE-2017-0213_x86.exe (PID: 2900)
SUSPICIOUS
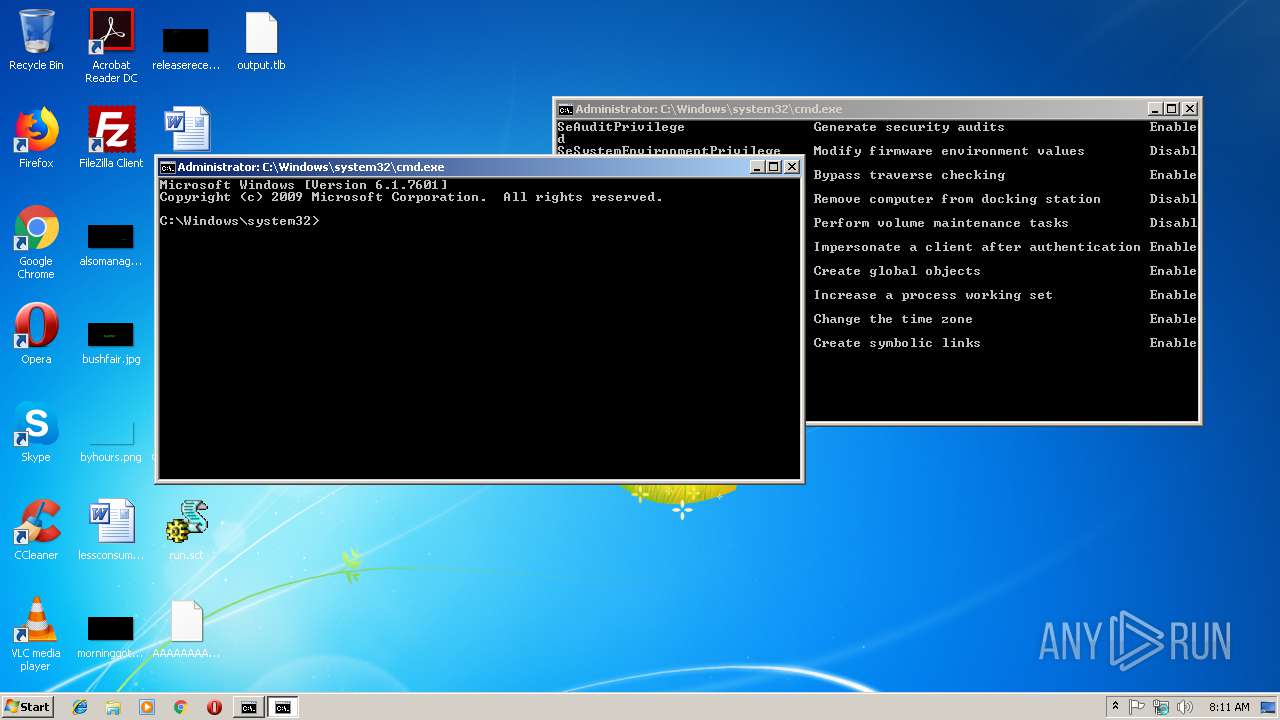
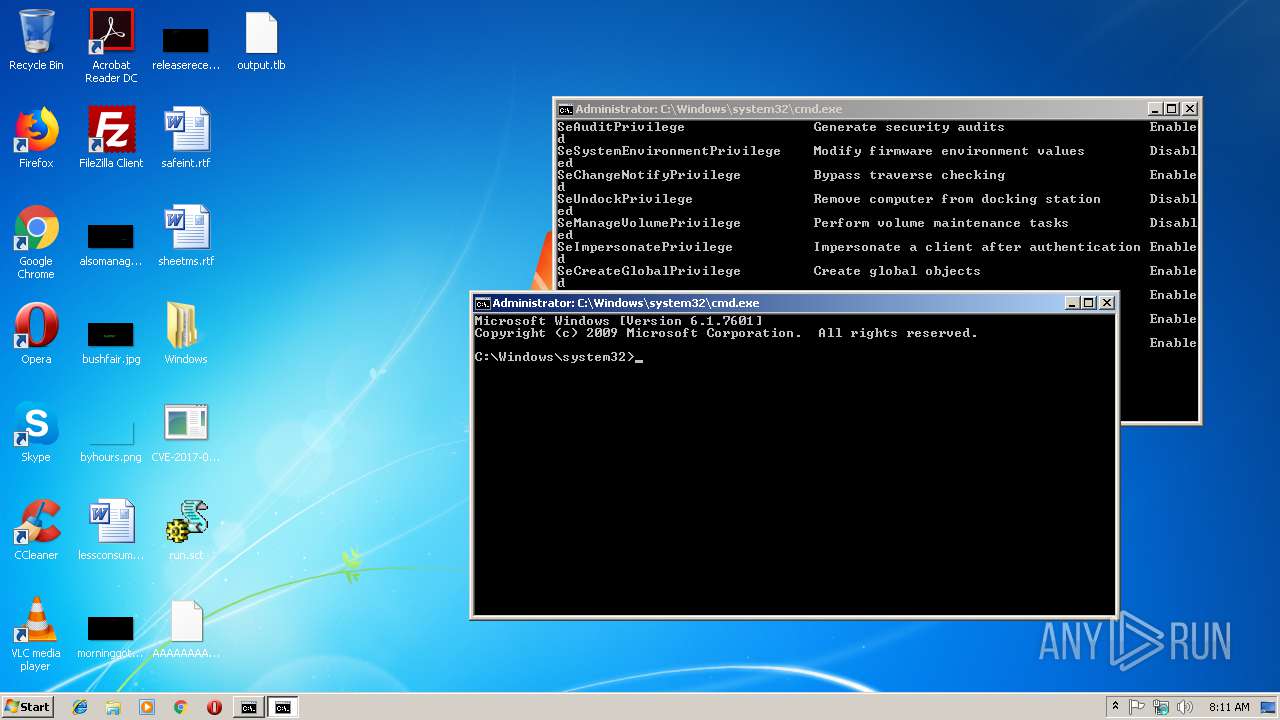
Starts CMD.EXE for commands execution
- CVE-2017-0213_x86.exe (PID: 2696)
- CVE-2017-0213_x86.exe (PID: 2900)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:06:06 12:21:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.1 |
| CodeSize: | 92672 |
| InitializedDataSize: | 44032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4993 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 06-Jun-2017 10:21:46 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Jun-2017 10:21:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001697C | 0x00016A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60887 |
.rdata | 0x00018000 | 0x00007D82 | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17892 |
.data | 0x00020000 | 0x00001494 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.77127 |
.rsrc | 0x00022000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.70436 |
.reloc | 0x00023000 | 0x0000144C | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.32429 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHLWAPI.dll |
ole32.dll |
Total processes
45
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2696 | "C:/Users/admin/Desktop/CVE-2017-0213_x86.exe" 1 | C:\Users\admin\Desktop\CVE-2017-0213_x86.exe | — | svchost.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2900 | "C:/Users/admin/Desktop/CVE-2017-0213_x86.exe" 1 | C:\Users\admin\Desktop\CVE-2017-0213_x86.exe | — | svchost.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3608 | "C:\Users\admin\Desktop\CVE-2017-0213_x86.exe" | C:\Users\admin\Desktop\CVE-2017-0213_x86.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3632 | "C:\Users\admin\Desktop\CVE-2017-0213_x86.exe" | C:\Users\admin\Desktop\CVE-2017-0213_x86.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
6
Read events
6
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
2
Unknown types
6
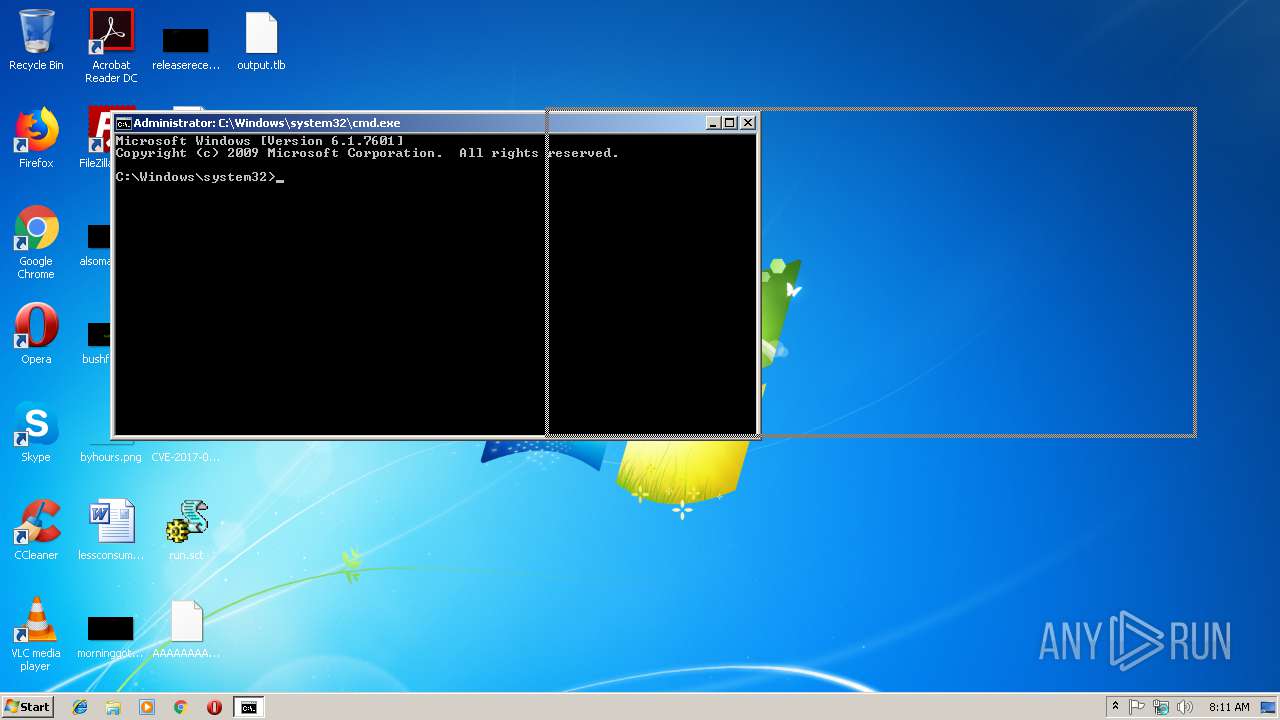
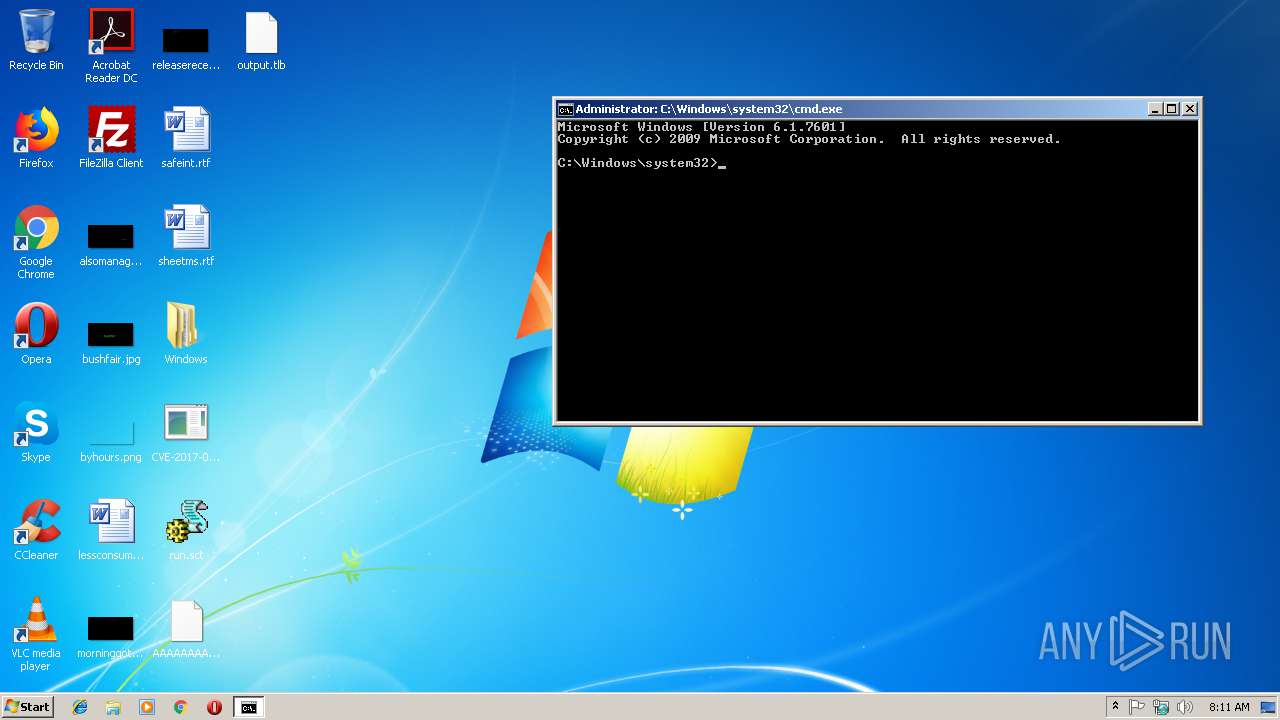
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3632 | CVE-2017-0213_x86.exe | C:\Users\admin\Desktop\run.sct | xml | |
MD5:— | SHA256:— | |||
| 3608 | CVE-2017-0213_x86.exe | C:\Users\admin\Desktop\run.sct | xml | |
MD5:— | SHA256:— | |||
| 3632 | CVE-2017-0213_x86.exe | C:\Users\admin\Desktop\output.tlb | tlb | |
MD5:1B174B78F5CABC467C759CF0D9A5CBD4 | SHA256:6DA864DF6F743611CF2CD0D902B28E15C15C6C3C9BFB8EFA72B067AACF7AE0DD | |||
| 3608 | CVE-2017-0213_x86.exe | C:\Users\admin\Desktop\Windows\system32\tapi3.dll | tlb | |
MD5:14DDD43E1BB31F7B30ACC85CE7CDD083 | SHA256:D5F7ADADAD598D25187656FB914EC121D72E124EE09DF71619A6583B9E34B603 | |||
| 3632 | CVE-2017-0213_x86.exe | C:\Users\admin\Desktop\AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA | tlb | |
MD5:7BB43024226008EE40928315979EC101 | SHA256:09374A035E6DBCC425B280724C732CD17107DFEC72979607B050EA86DD3B80E8 | |||
| 3632 | CVE-2017-0213_x86.exe | C:\Users\admin\Desktop\Windows\system32\tapi3.dll | tlb | |
MD5:14DDD43E1BB31F7B30ACC85CE7CDD083 | SHA256:D5F7ADADAD598D25187656FB914EC121D72E124EE09DF71619A6583B9E34B603 | |||
| 3608 | CVE-2017-0213_x86.exe | C:\Users\admin\Desktop\output.tlb | tlb | |
MD5:1B174B78F5CABC467C759CF0D9A5CBD4 | SHA256:6DA864DF6F743611CF2CD0D902B28E15C15C6C3C9BFB8EFA72B067AACF7AE0DD | |||
| 3608 | CVE-2017-0213_x86.exe | C:\Users\admin\Desktop\AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA | tlb | |
MD5:7BB43024226008EE40928315979EC101 | SHA256:09374A035E6DBCC425B280724C732CD17107DFEC72979607B050EA86DD3B80E8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report