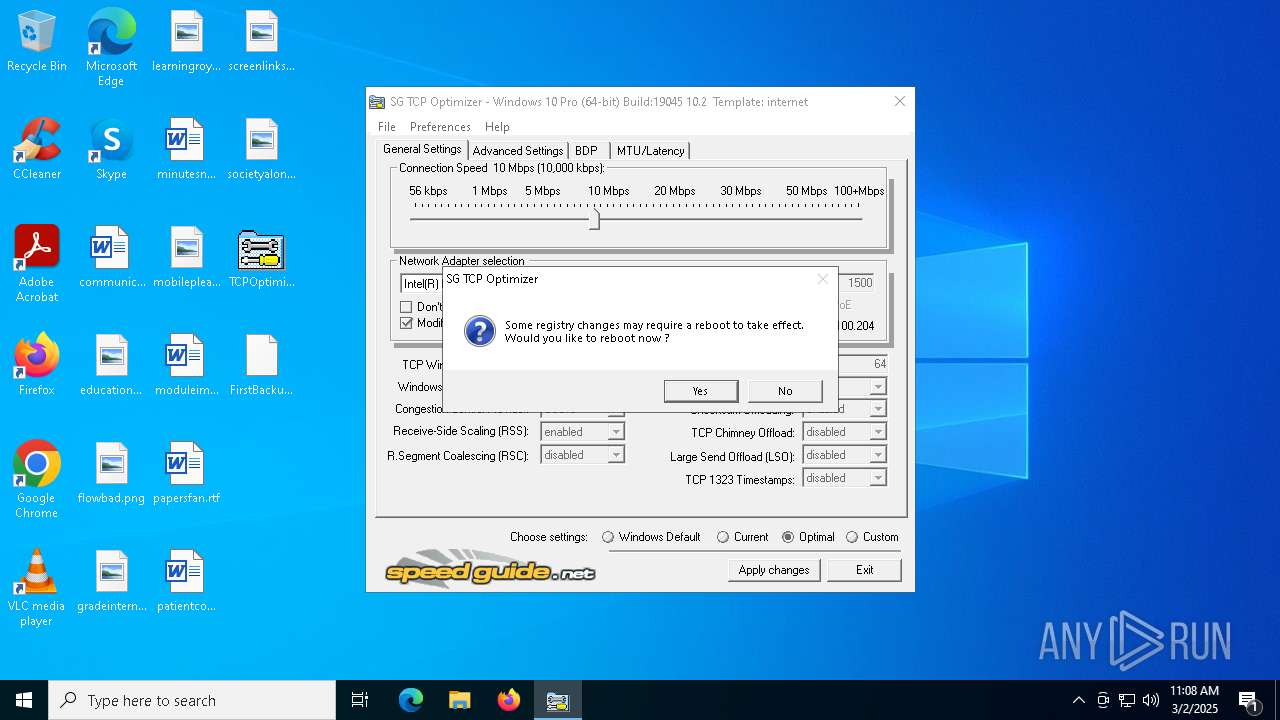
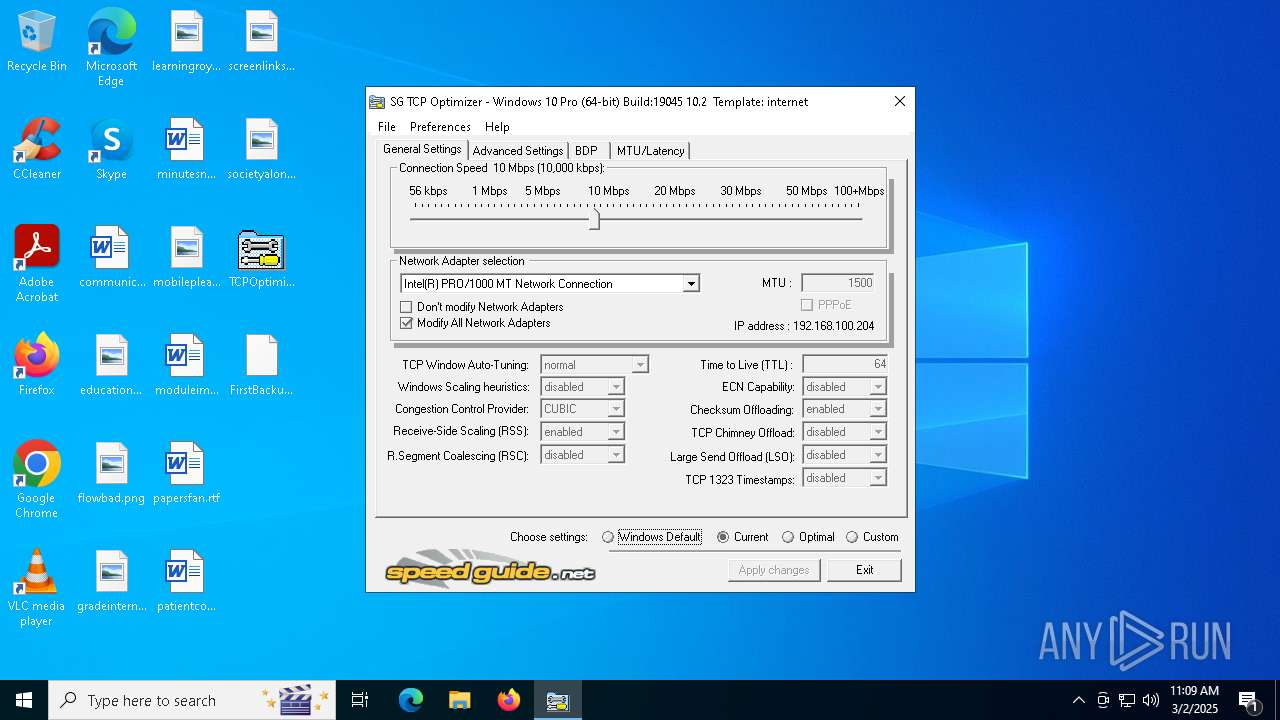
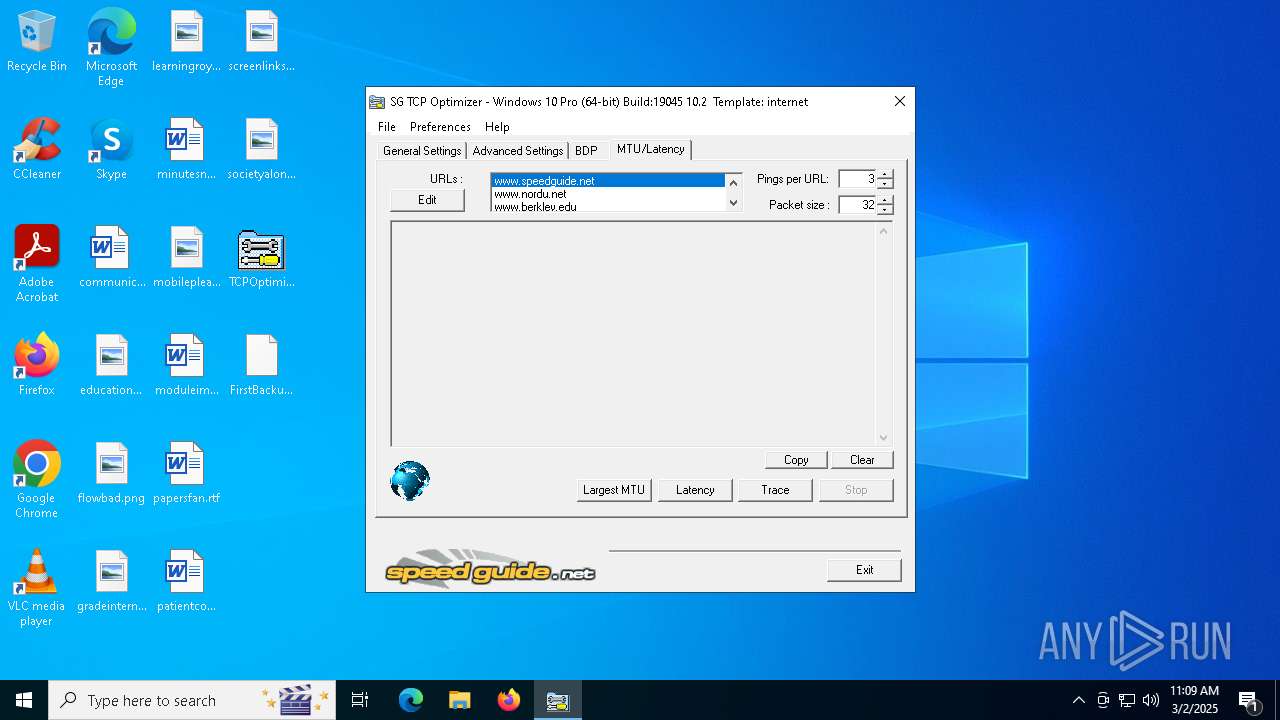
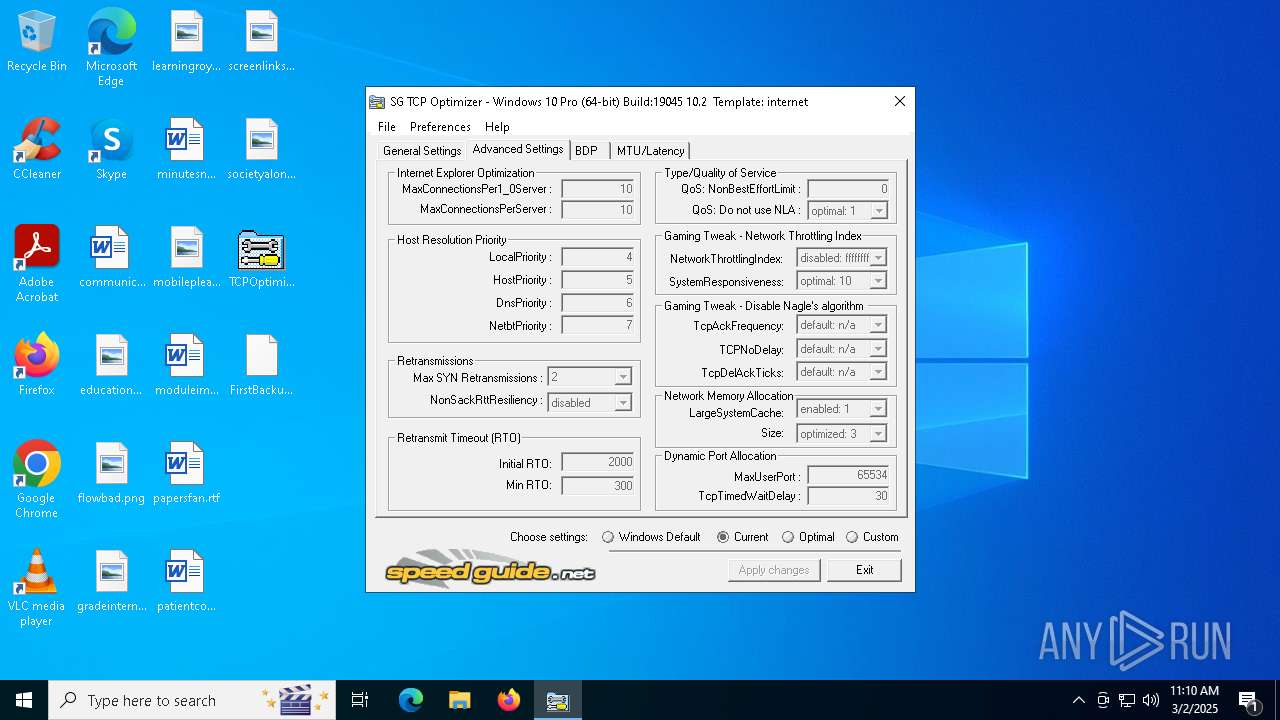
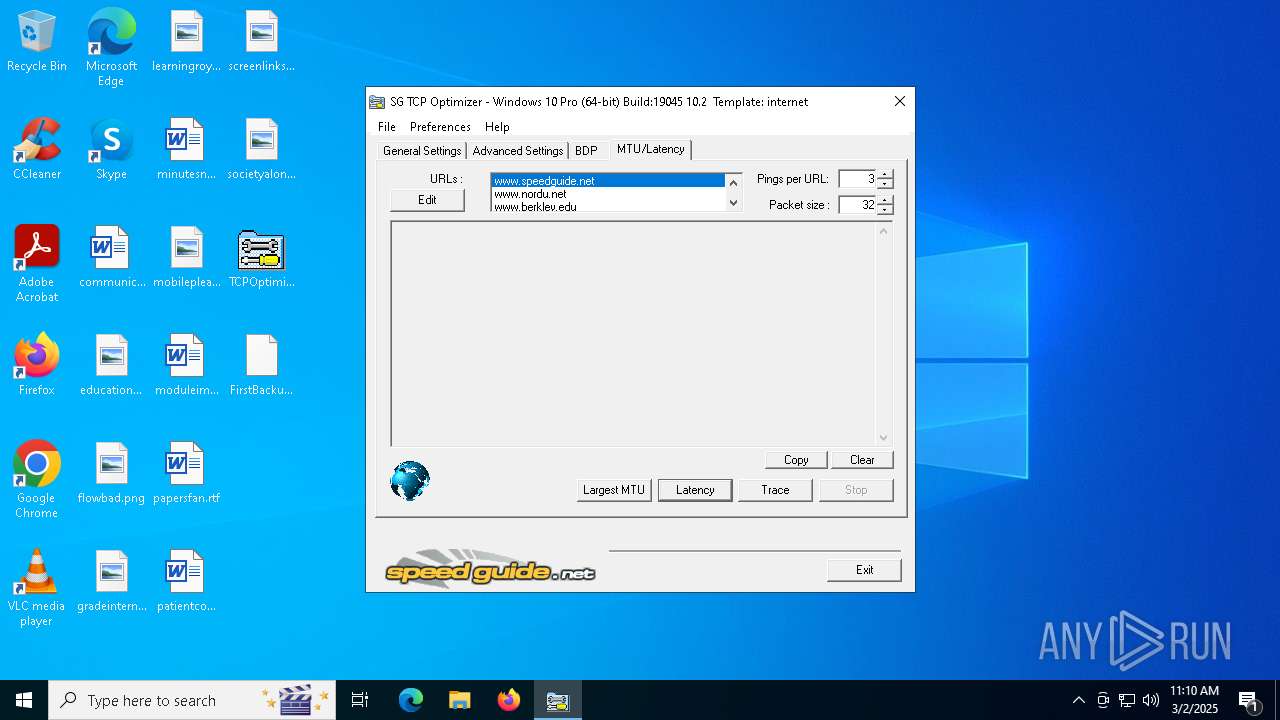
| File name: | TCPOptimizer.exe |
| Full analysis: | https://app.any.run/tasks/e77ecf2c-dd4a-4b30-94f5-3b57cffbd703 |
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2025, 11:07:13 |
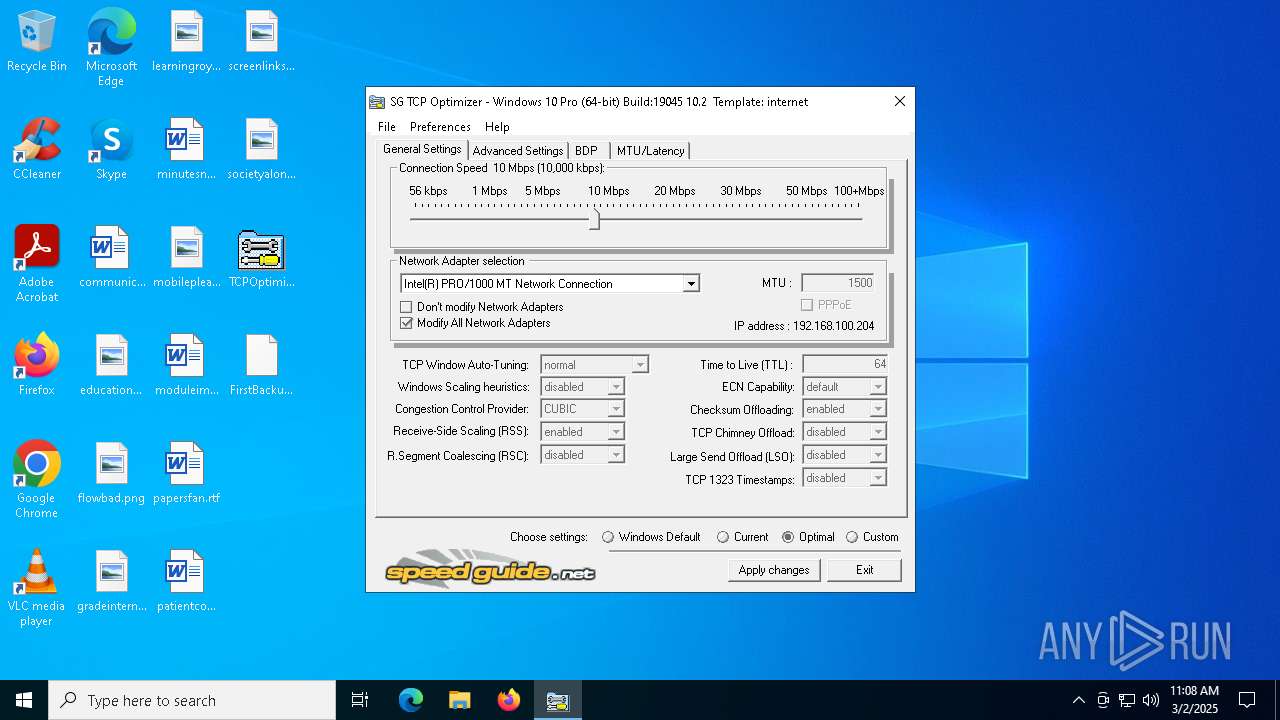
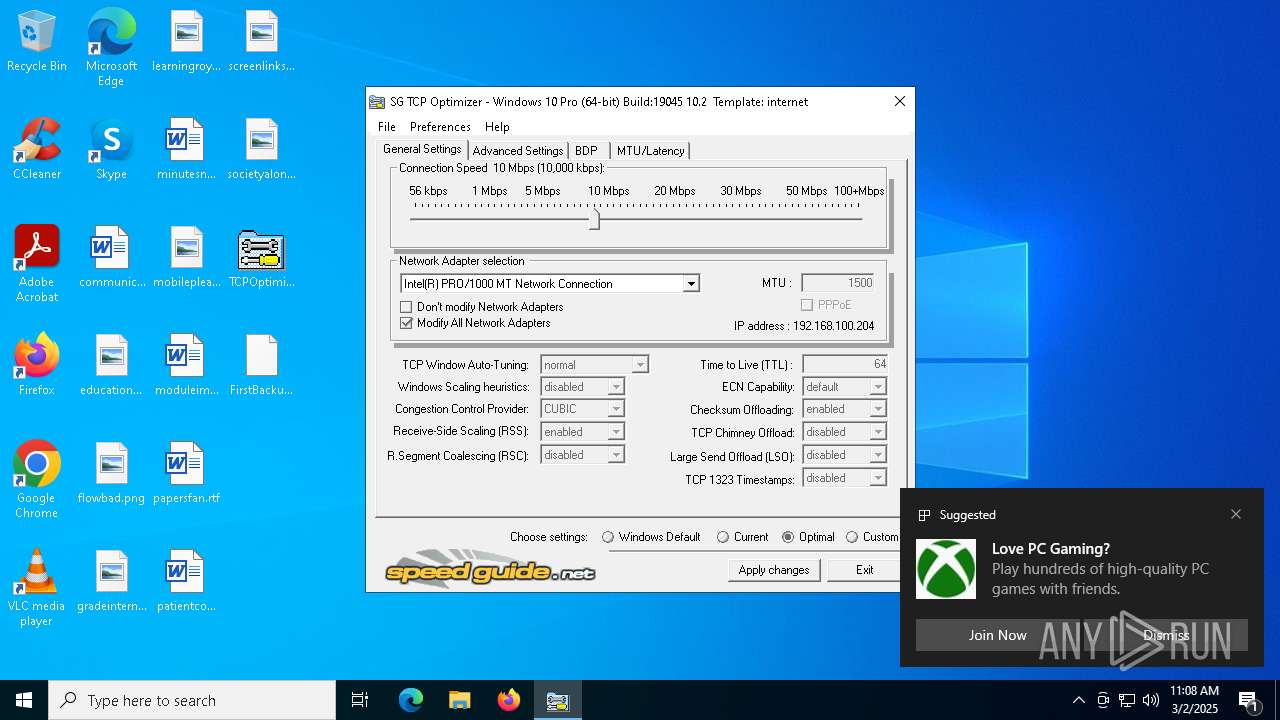
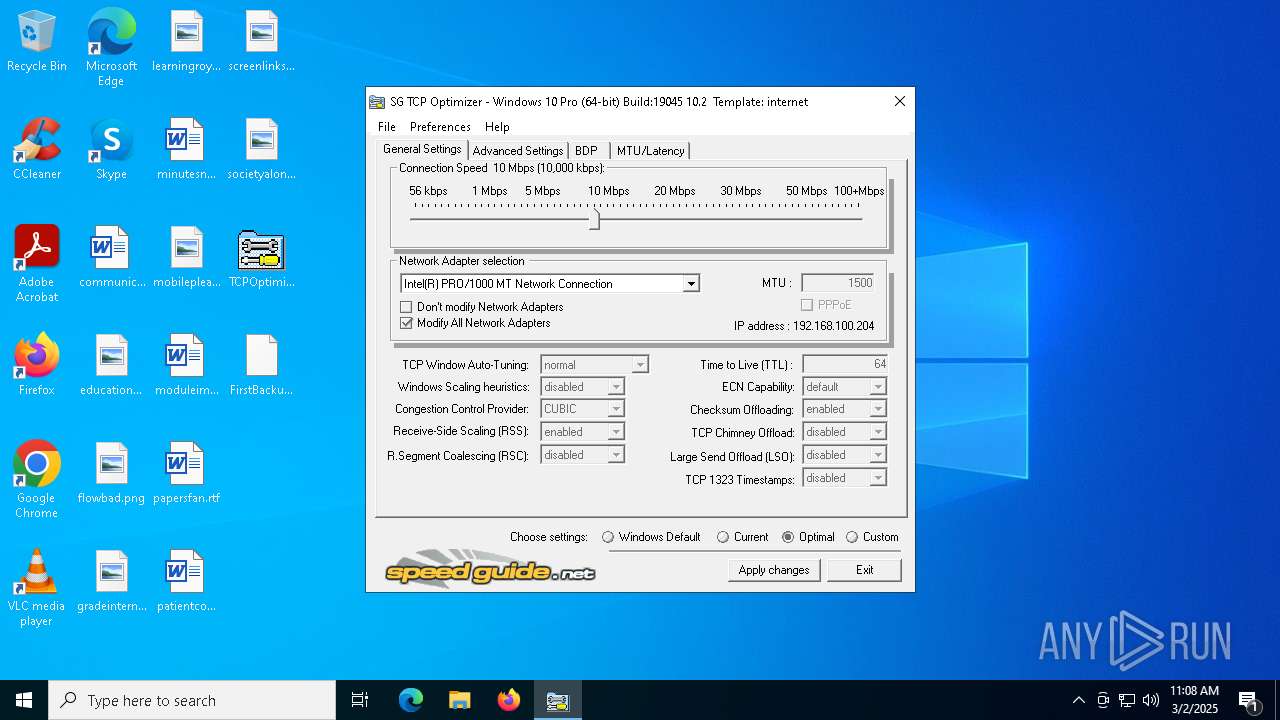
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | D8292150C8CE862A97A923318DF07805 |
| SHA1: | 917F917FF9FE33E199388E5E1D4C0696882D2991 |
| SHA256: | 0A49DC0D2CE725AF347DF632539B70AFCFD22B38E285920B515143332A5511E9 |
| SSDEEP: | 12288:C1B8g1arhMAURdndzQTEEI7b6Yz3m5W6:pujRdndzQfqb3K |
MALICIOUS
No malicious indicators.SUSPICIOUS
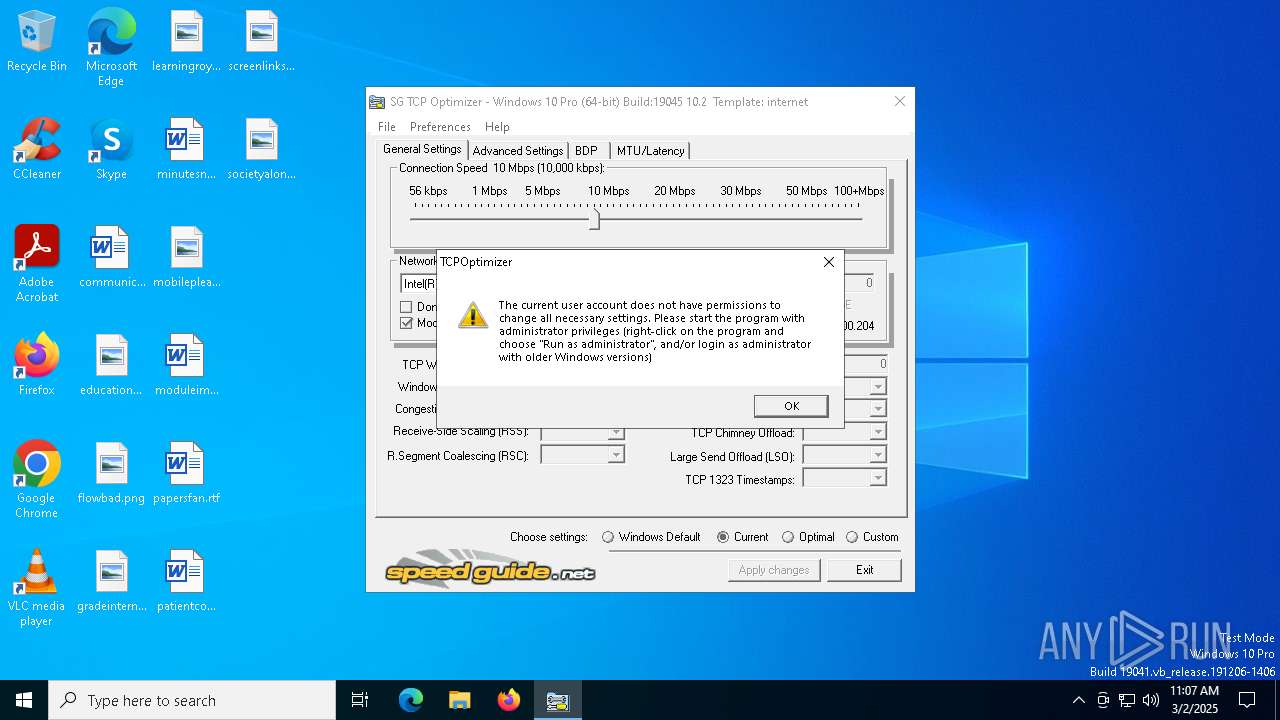
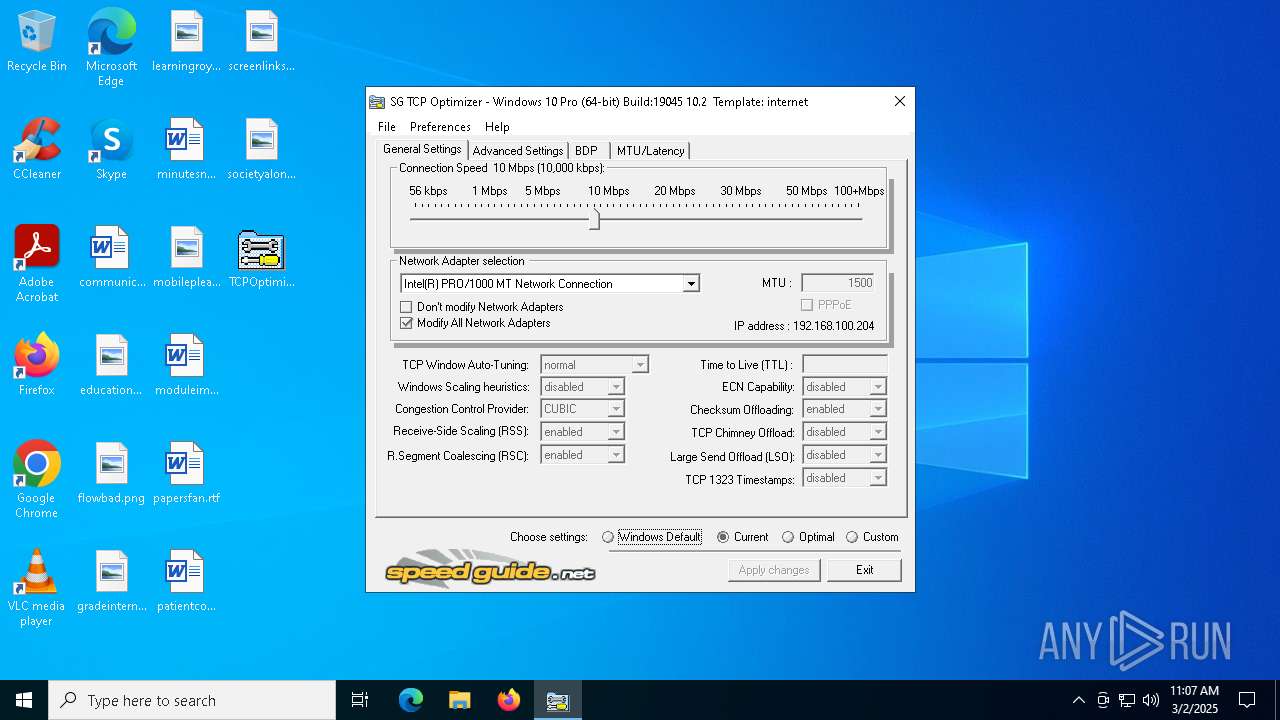
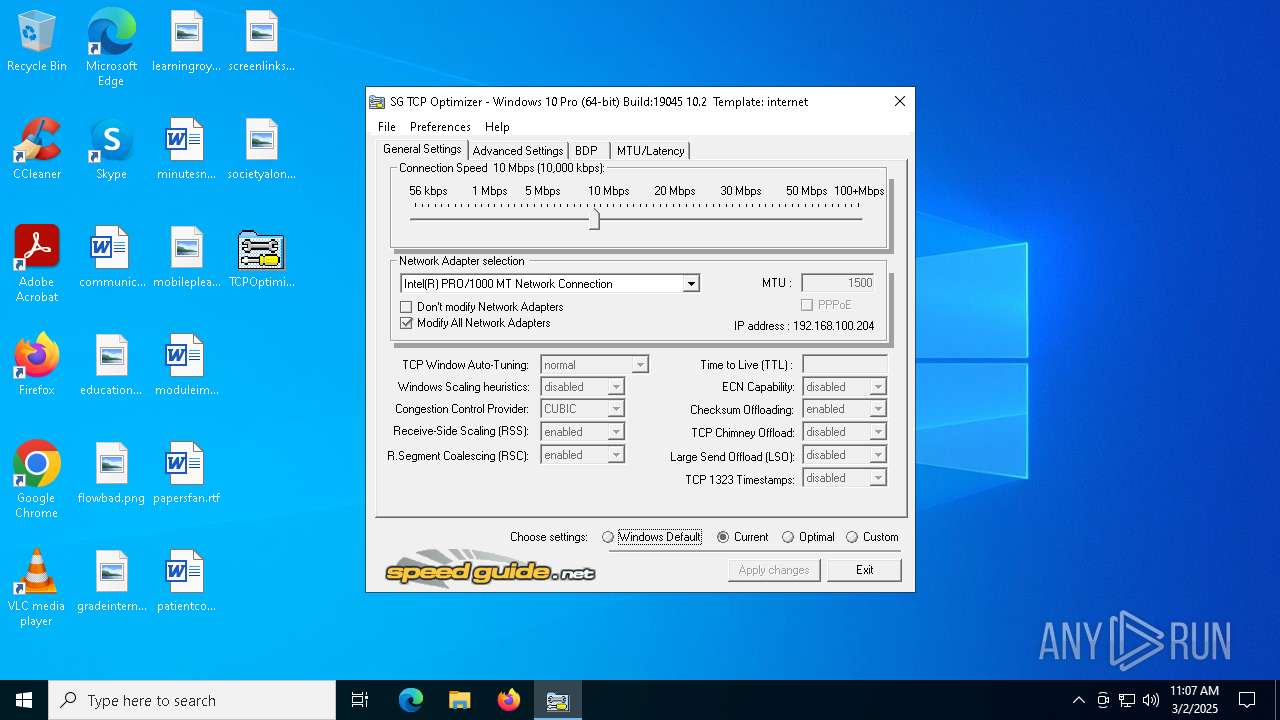
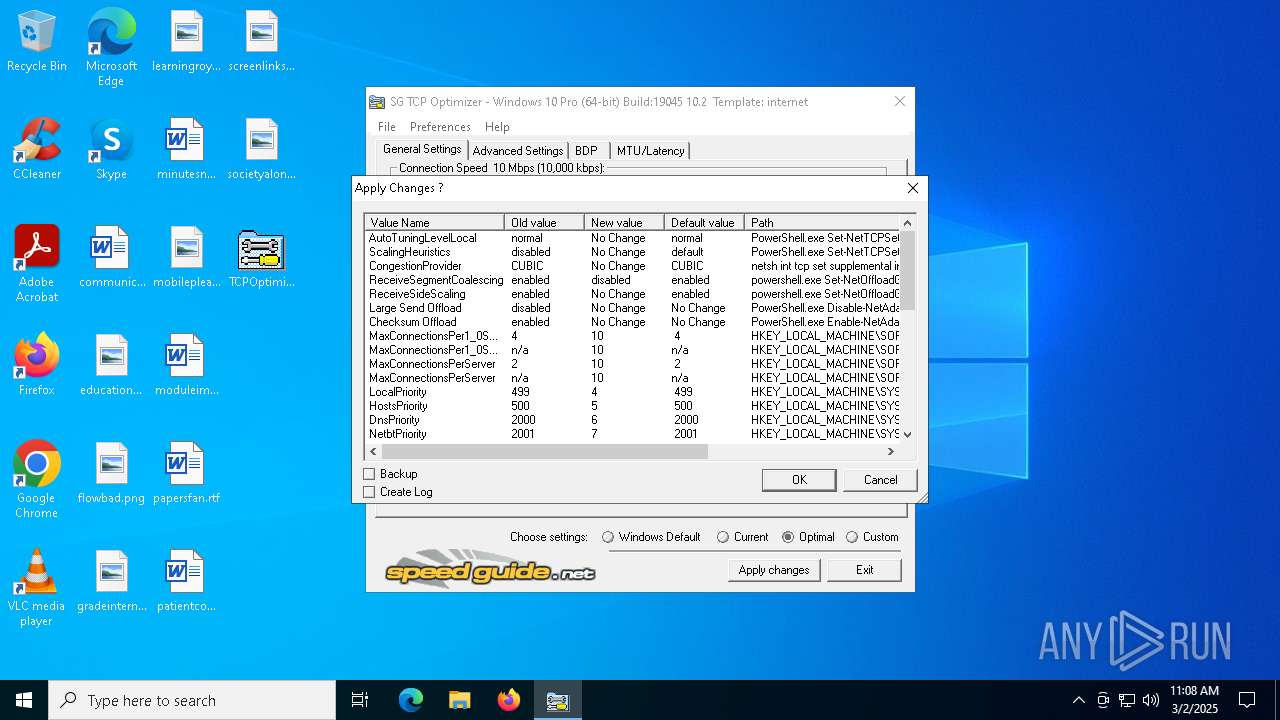
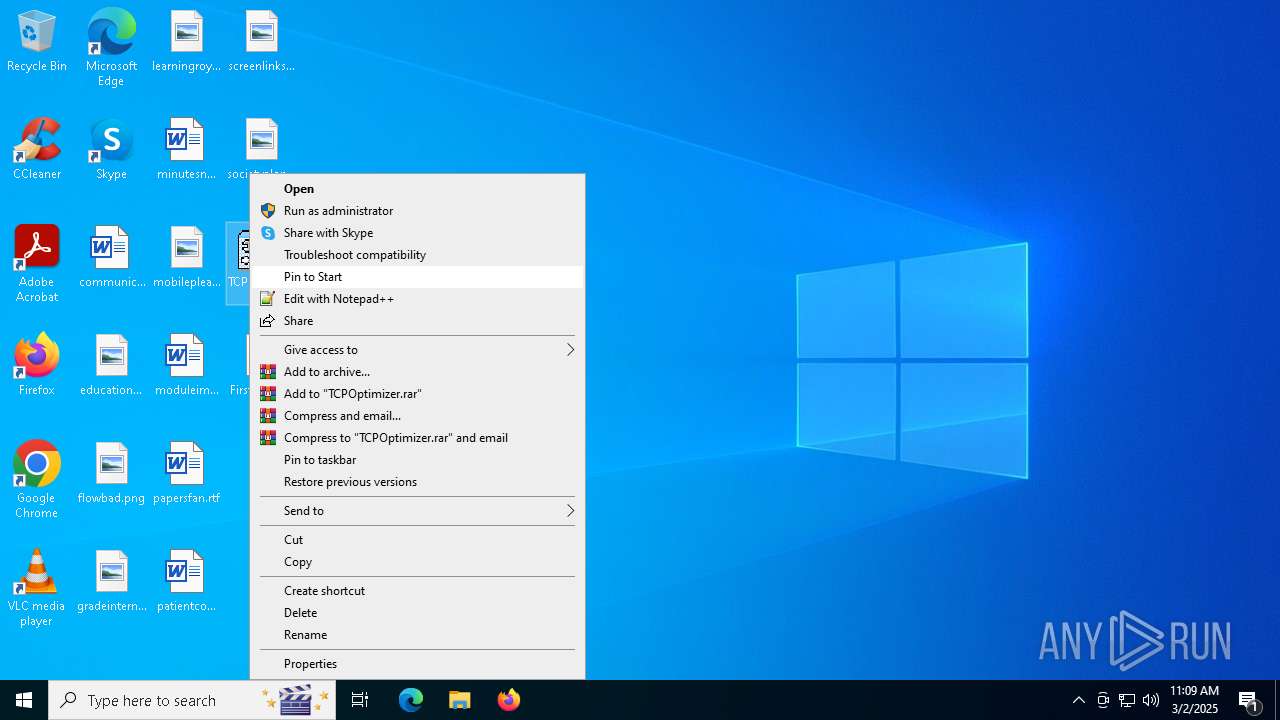
Suspicious use of NETSH.EXE
- TCPOptimizer.exe (PID: 5280)
- TCPOptimizer.exe (PID: 2740)
- TCPOptimizer.exe (PID: 6396)
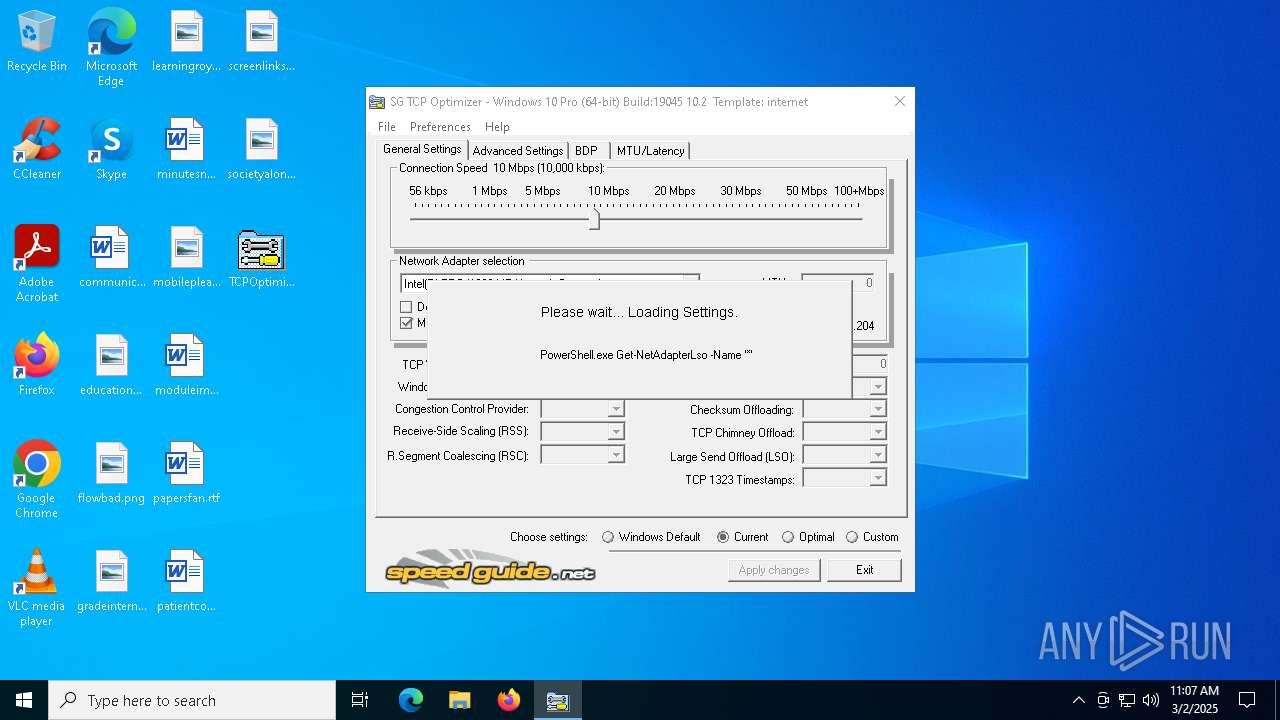
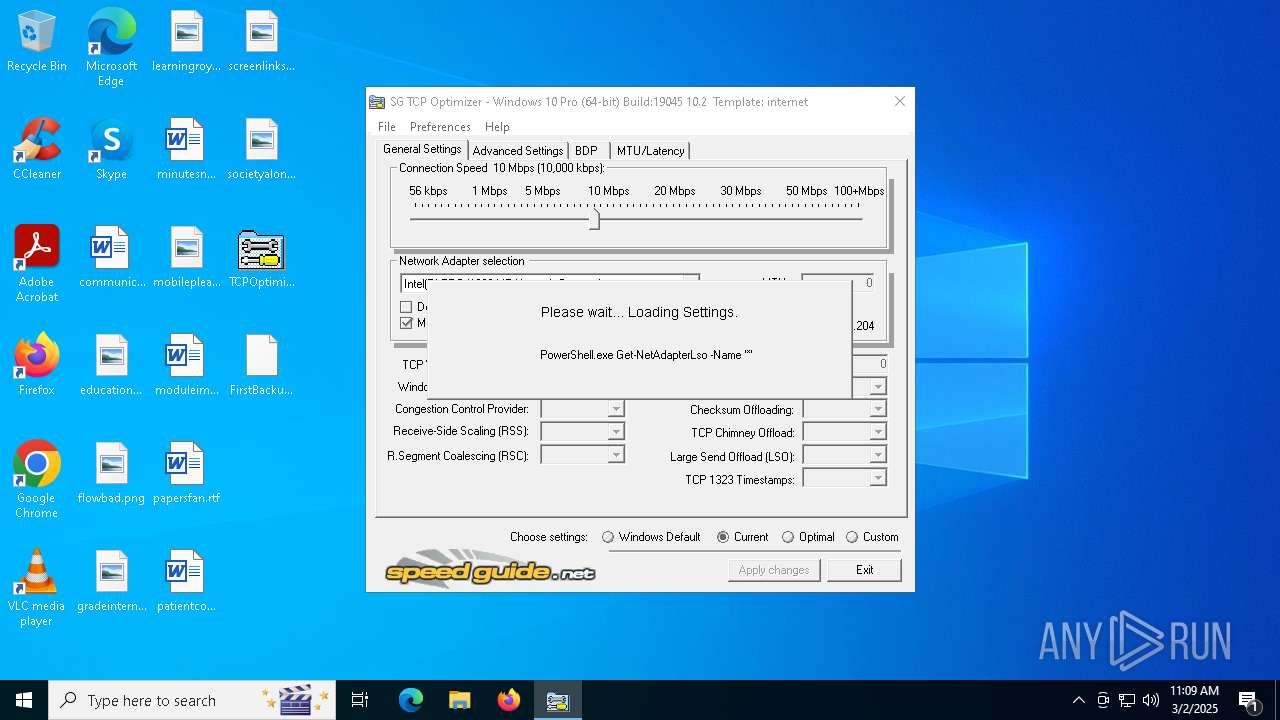
Starts POWERSHELL.EXE for commands execution
- TCPOptimizer.exe (PID: 5280)
- TCPOptimizer.exe (PID: 2740)
- TCPOptimizer.exe (PID: 6396)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7632)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 2928)
INFO
Checks supported languages
- TCPOptimizer.exe (PID: 5280)
- TCPOptimizer.exe (PID: 2740)
- ShellExperienceHost.exe (PID: 7632)
- PLUGScheduler.exe (PID: 2928)
- TCPOptimizer.exe (PID: 6396)
Create files in a temporary directory
- TCPOptimizer.exe (PID: 5280)
- TCPOptimizer.exe (PID: 2740)
- TCPOptimizer.exe (PID: 6396)
The sample compiled with english language support
- TCPOptimizer.exe (PID: 5280)
Disables trace logs
- netsh.exe (PID: 4380)
- netsh.exe (PID: 5244)
- netsh.exe (PID: 7432)
- netsh.exe (PID: 4988)
- netsh.exe (PID: 8112)
- netsh.exe (PID: 7832)
- netsh.exe (PID: 7380)
- netsh.exe (PID: 6740)
- netsh.exe (PID: 6484)
- netsh.exe (PID: 6580)
- netsh.exe (PID: 6512)
Reads the computer name
- TCPOptimizer.exe (PID: 5280)
- TCPOptimizer.exe (PID: 2740)
- ShellExperienceHost.exe (PID: 7632)
- PLUGScheduler.exe (PID: 2928)
- TCPOptimizer.exe (PID: 6396)
Reads product name
- TCPOptimizer.exe (PID: 5280)
- TCPOptimizer.exe (PID: 2740)
- TCPOptimizer.exe (PID: 6396)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7464)
- BackgroundTransferHost.exe (PID: 7720)
- BackgroundTransferHost.exe (PID: 8084)
- BackgroundTransferHost.exe (PID: 7260)
- BackgroundTransferHost.exe (PID: 7296)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 7656)
- powershell.exe (PID: 7884)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 7684)
- powershell.exe (PID: 3180)
- powershell.exe (PID: 496)
- powershell.exe (PID: 7524)
- powershell.exe (PID: 7796)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 7320)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 6972)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7720)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7720)
- slui.exe (PID: 3268)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7720)
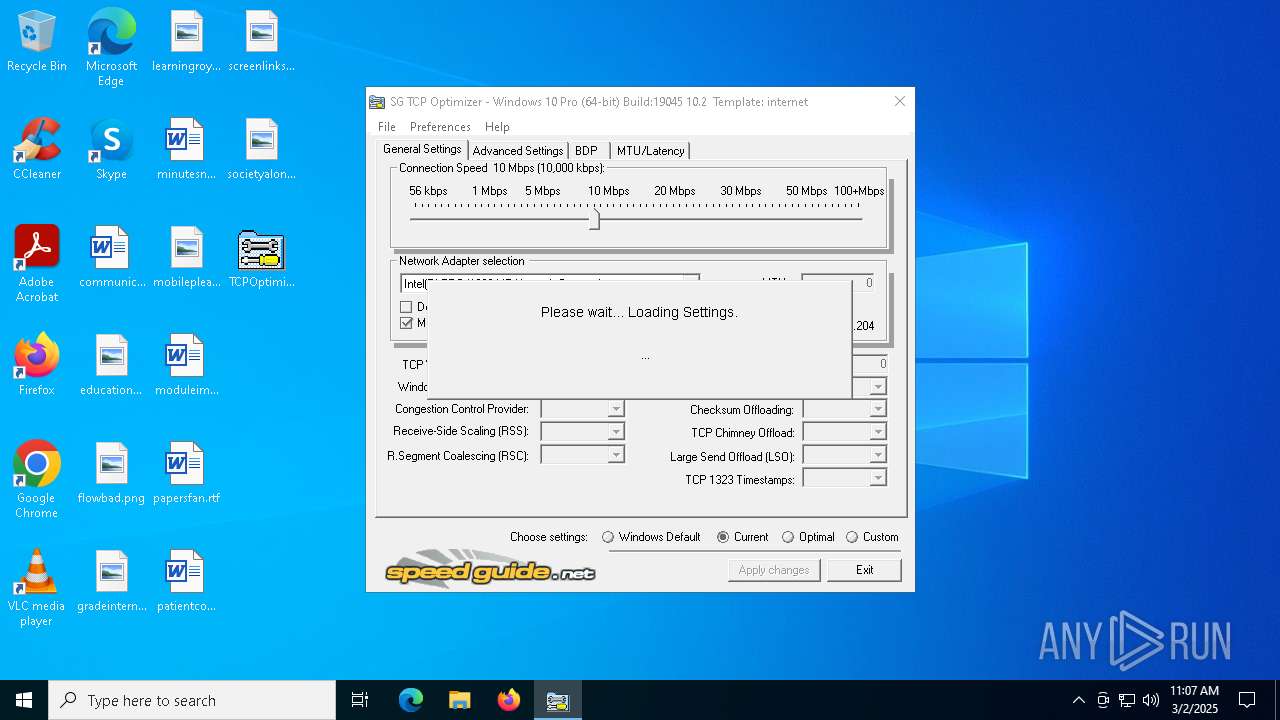
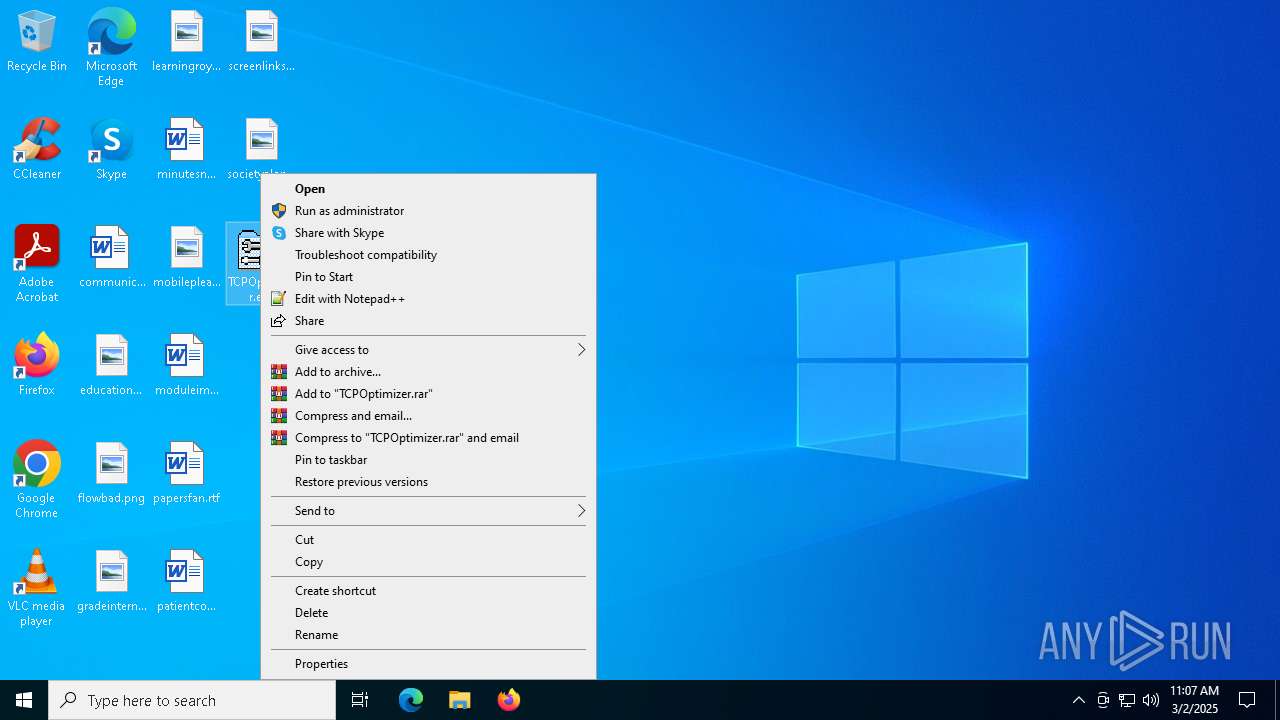
Manual execution by a user
- TCPOptimizer.exe (PID: 2740)
- TCPOptimizer.exe (PID: 6396)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5124)
Creates files in the program directory
- PLUGScheduler.exe (PID: 2928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:01:09 20:32:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 348160 |
| InitializedDataSize: | 720896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3205f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.1.0 |
| ProductVersionNumber: | 4.1.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Coded and (c) Speed Guide, Inc. - webmaster@speedguide.net / outsorcing@gmail.com |
| CompanyName: | Speed Guide Inc. |
| FileDescription: | SG TCP Optimizer |
| FileVersion: | 4.1.1.0 |
| InternalName: | TCP Optimizer |
| LegalCopyright: | Copyright (c) 2001-2021 |
| LegalTrademarks: | Speed Guide Inc |
| OriginalFileName: | TCPOptimizer.exe |
| ProductName: | SG TCP Optimizer Application |
| ProductVersion: | 4.1.1.0 |
Total processes
357
Monitored processes
75
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | PowerShell.exe Set-NetTCPSetting -SettingName internet -MaxSynRetransmissions 2 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | TCPOptimizer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2316 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2740 | "C:\Users\admin\Desktop\TCPOptimizer.exe" | C:\Users\admin\Desktop\TCPOptimizer.exe | explorer.exe | ||||||||||||
User: admin Company: Speed Guide Inc. Integrity Level: HIGH Description: SG TCP Optimizer Exit code: 0 Version: 4.1.1.0 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3180 | powershell.exe Set-NetOffloadGlobalSetting -ReceiveSegmentCoalescing disabled | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | TCPOptimizer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
138 066
Read events
138 023
Write events
42
Delete events
1
Modification events
| (PID) Process: | (4380) netsh.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MPRAPI |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4380) netsh.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MPRAPI |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4380) netsh.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MPRAPI |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4380) netsh.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MPRAPI |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4380) netsh.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MPRAPI |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4380) netsh.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MPRAPI |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4380) netsh.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MPRAPI |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7464) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7464) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7464) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
53
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7720 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\d049e68e-00d0-408e-8dd9-6ea039a38427.down_data | — | |
MD5:— | SHA256:— | |||
| 5548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_erlu3qul.ixt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7720 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\2c3389b0-8392-4a4f-a0da-f4fedde58c51.up_meta_secure | binary | |
MD5:2C2889DF0E1695247E9D93FED81D1C81 | SHA256:ED96F304B8CA271A859050E54C3483A1679C0F6F8329031B9B9D2C77D8762DF8 | |||
| 7884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kafv0x0a.ger.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7720 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\d049e68e-00d0-408e-8dd9-6ea039a38427.0a9a35b0-75c1-462a-96b2-0f13041b971d.down_meta | binary | |
MD5:2E4EAF4273E57E97554174EB1B467BBF | SHA256:006626F2486591BAA5E125996B8FC8C2708C1737C483CB3FAB7BF0A37BD42B26 | |||
| 7884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ykkqmpig.w1d.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2nwgfmht.acx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7720 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\2c3389b0-8392-4a4f-a0da-f4fedde58c51.0a9a35b0-75c1-462a-96b2-0f13041b971d.down_meta | binary | |
MD5:2E4EAF4273E57E97554174EB1B467BBF | SHA256:006626F2486591BAA5E125996B8FC8C2708C1737C483CB3FAB7BF0A37BD42B26 | |||
| 7720 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:CA6173FC5E87CAB1BEF55DAC3B19CB8F | SHA256:2784FA484E6E373A9A1451396BA9BF7E52CB1D3208E446A62EE6FC9E9D3D73D1 | |||
| 7796 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3kobxwb1.apq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
57
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7720 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7556 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7556 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5552 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3008 | backgroundTaskHost.exe | 104.126.37.129:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2040 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2040 | backgroundTaskHost.exe | 20.223.36.55:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |