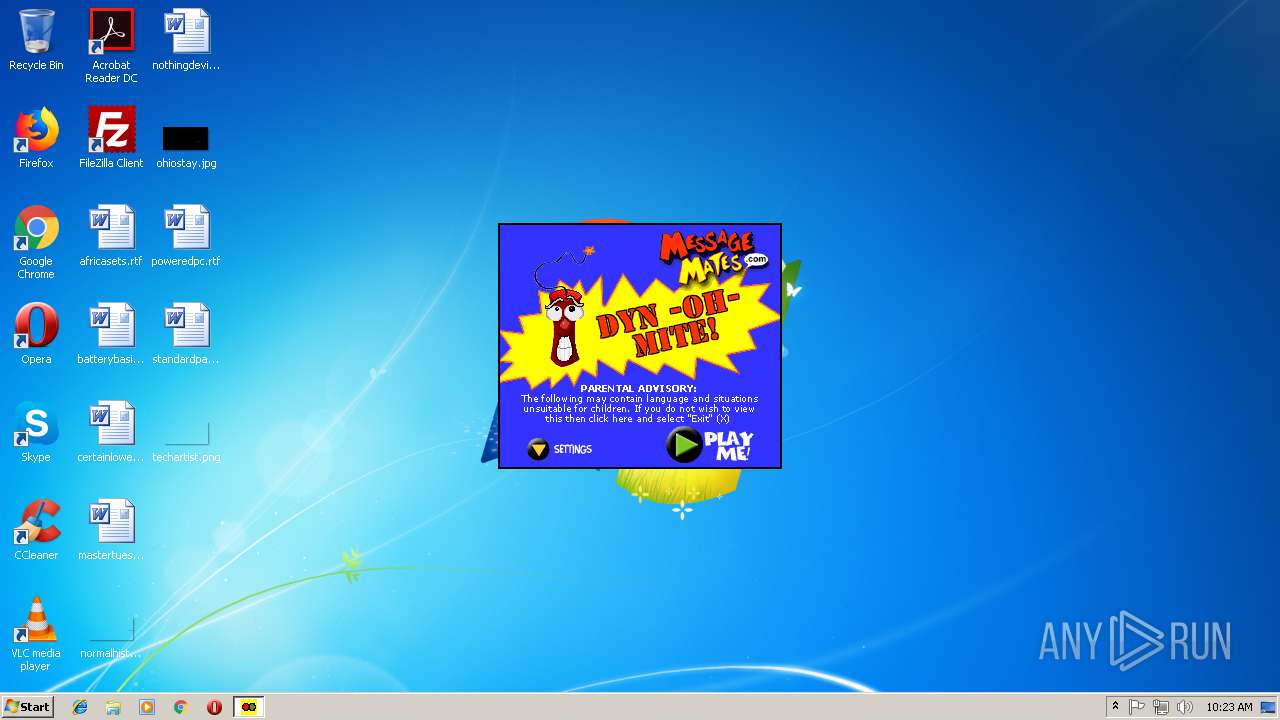
| File name: | dinamita.EXE |
| Full analysis: | https://app.any.run/tasks/655f1fe6-8b15-4048-98d5-ac1628602c43 |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2018, 09:23:05 |
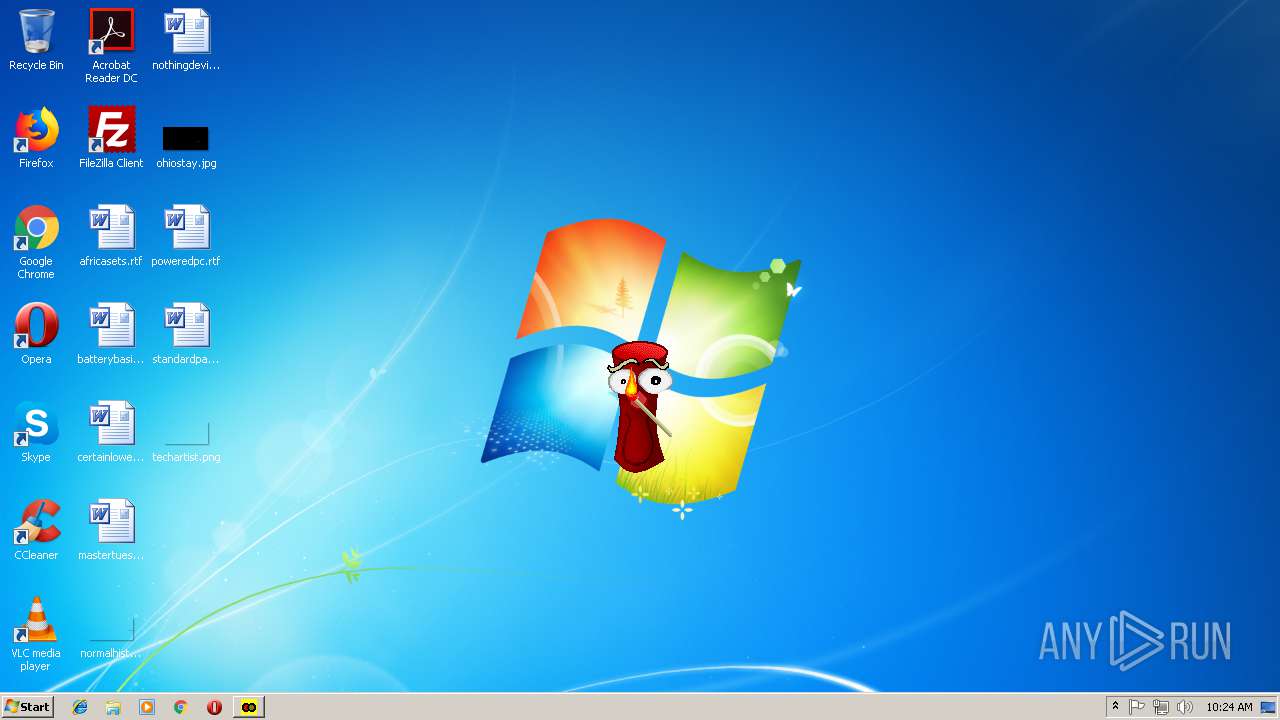
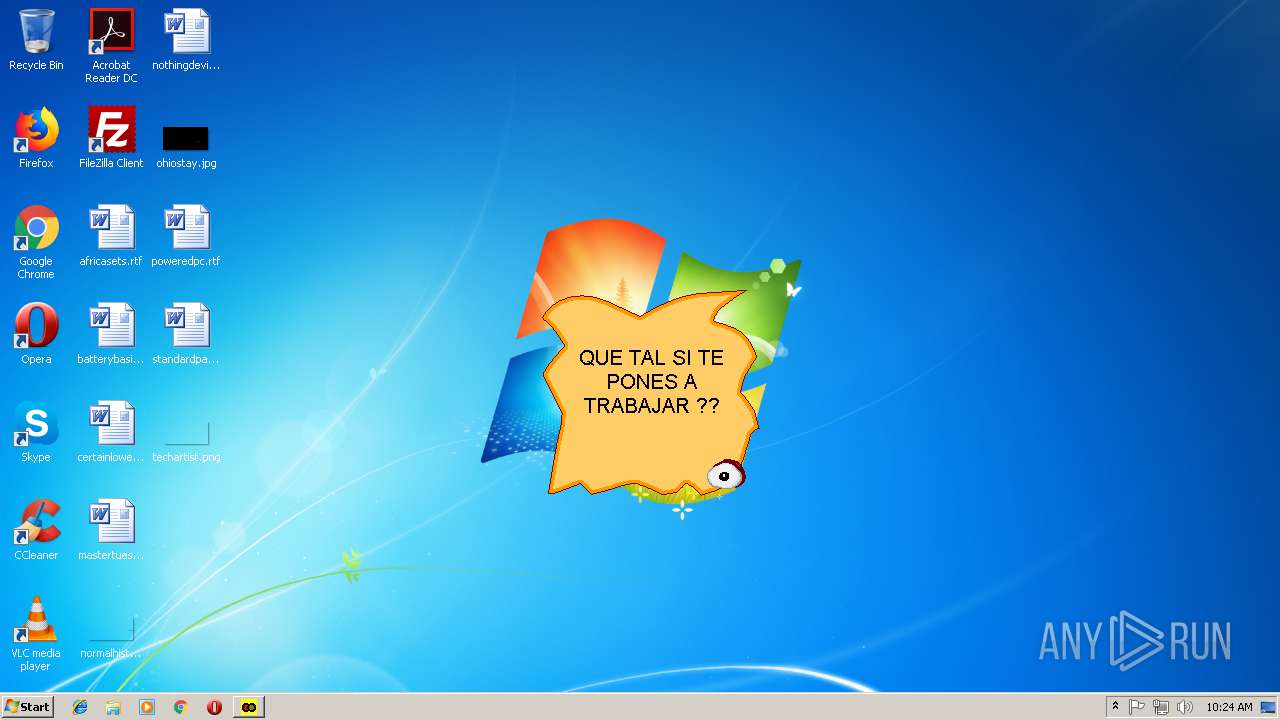
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E8302725DCA4BF150C730168B608927A |
| SHA1: | A4D7C4256263110F2B9F491CC70882652A027581 |
| SHA256: | 0A48B8F8A8A9C719AA9E6CEE0E2C3A4170DA617D868BCAA9C9A2F329A11EC364 |
| SSDEEP: | 6144:LDXw6FQVVxsz+OWH2qETKv9GGnep0p7jcAdBtzf0uI:LDA6FeVOz+OWH2qEuvzep0pVBBg |
MALICIOUS
No malicious indicators.SUSPICIOUS
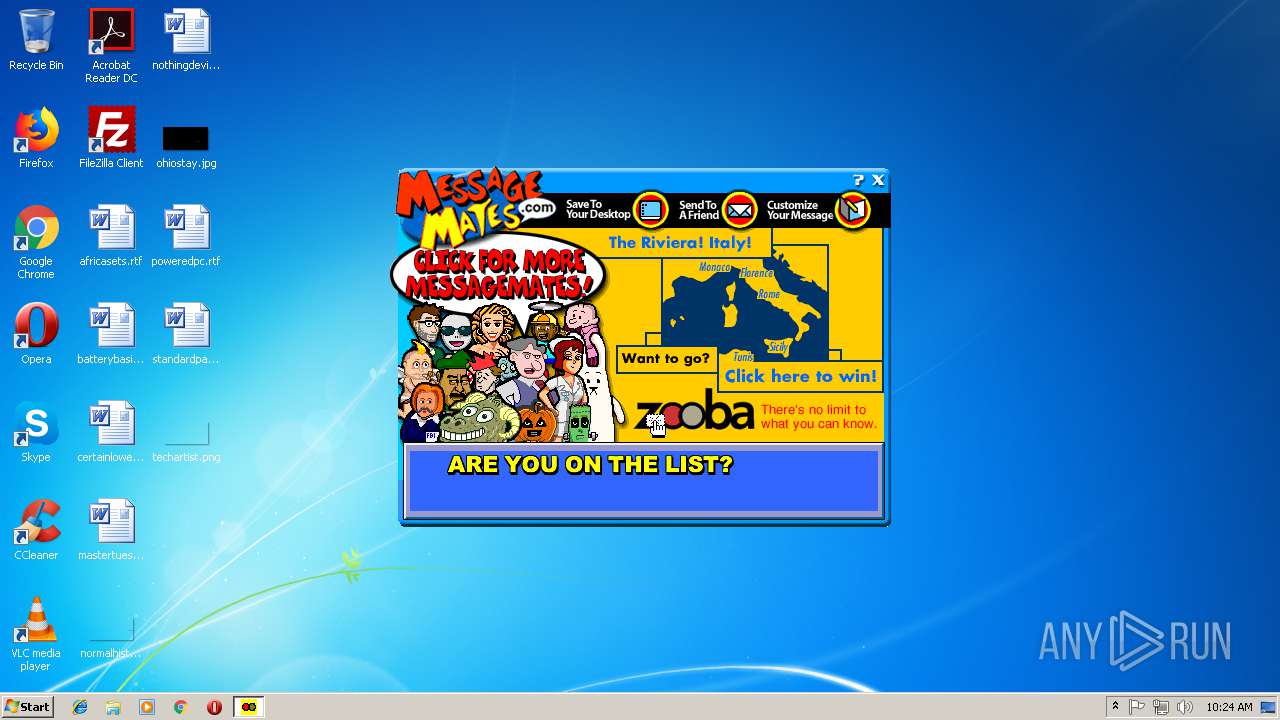
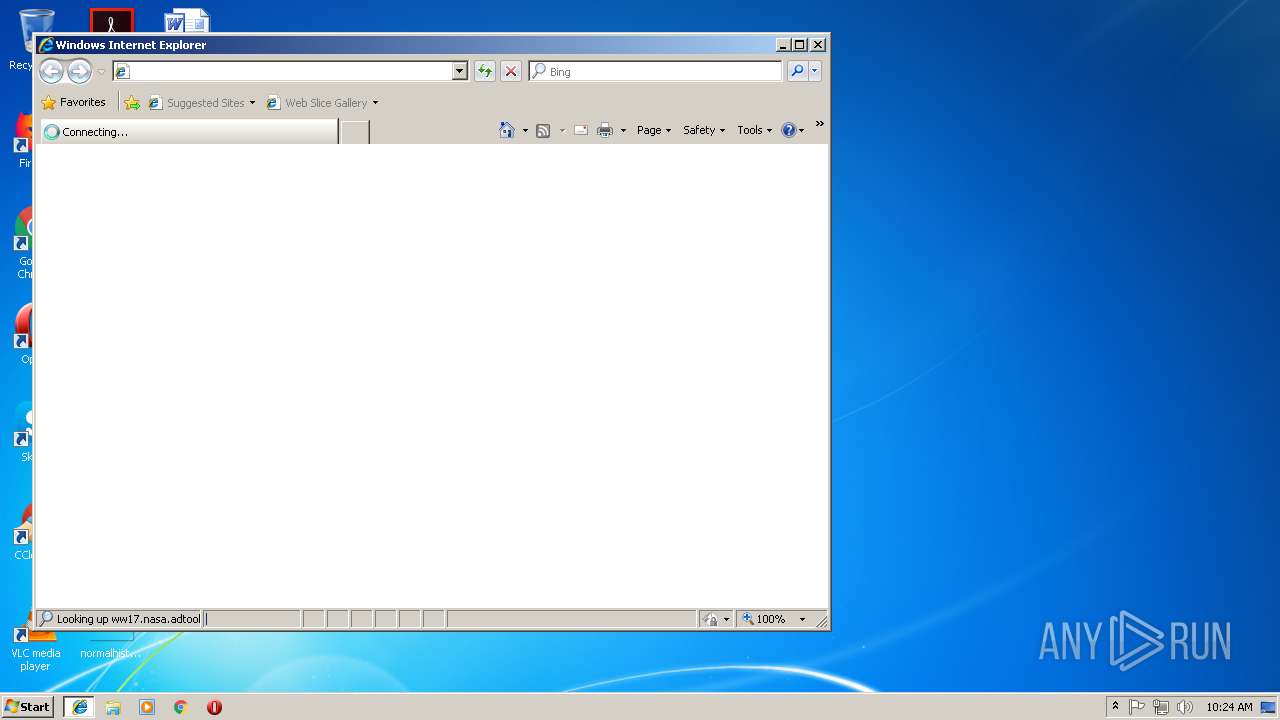
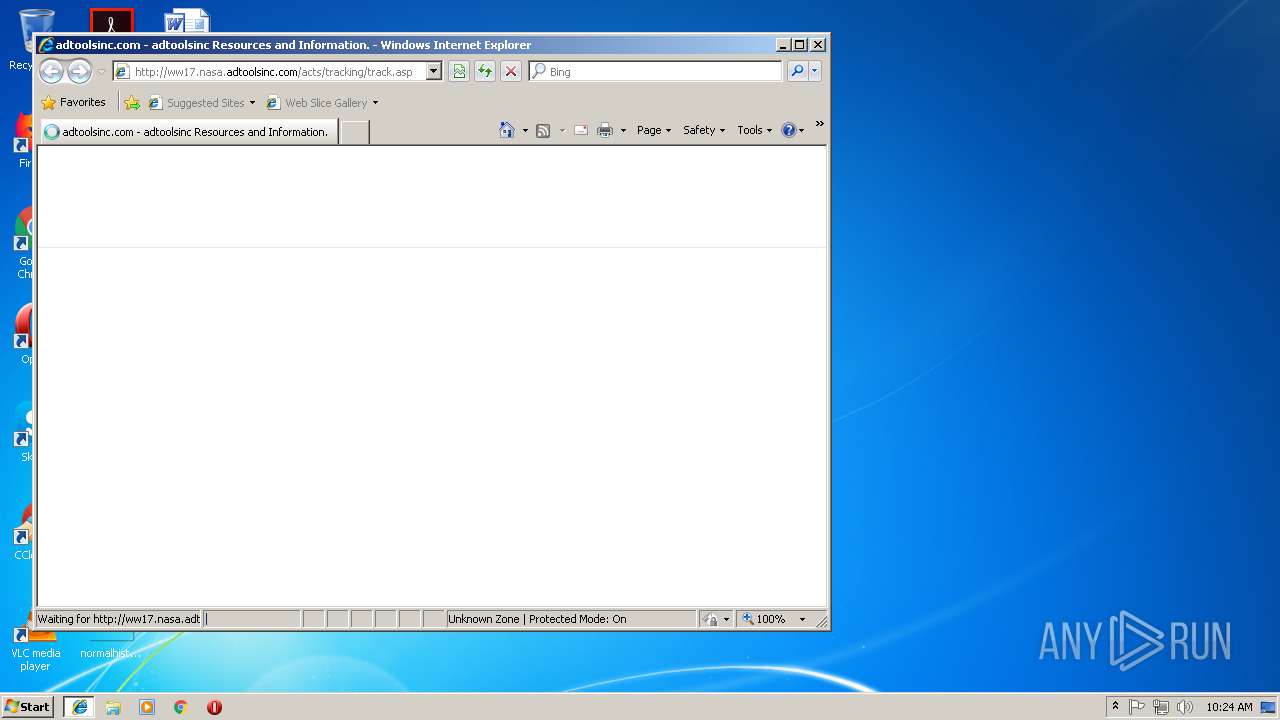
Starts Internet Explorer
- dinamita.EXE (PID: 3904)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2108)
Changes internet zones settings
- iexplore.exe (PID: 2152)
Reads internet explorer settings
- iexplore.exe (PID: 2108)
Reads Internet Cache Settings
- iexplore.exe (PID: 2108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2000:05:09 17:09:48+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 73728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x351c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-May-2000 15:09:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-May-2000 15:09:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004D56 | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64222 |
.rdata | 0x00006000 | 0x000007E6 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.13807 |
.data | 0x00007000 | 0x00000C38 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.52828 |
.zexe | 0x00008000 | 0x0001CFBD | 0x0001D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98387 |
.rsrc | 0x00025000 | 0x0001D7D8 | 0x0001E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.86441 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.21222 | 744 | UNKNOWN | English - United Kingdom | RT_ICON |
2 | 2.33711 | 296 | UNKNOWN | English - United Kingdom | RT_ICON |
100 | 2.37086 | 34 | UNKNOWN | English - United Kingdom | RT_GROUP_ICON |
101 | 7.97997 | 68597 | UNKNOWN | English - United Kingdom | XML |
102 | 2 | 4 | UNKNOWN | English - United Kingdom | TEXT |
109 | 3.38429 | 776 | UNKNOWN | English - United Kingdom | RT_DIALOG |
129 | 5.94525 | 117 | UNKNOWN | English - United Kingdom | TRACKINGDATA |
160 | 3.19493 | 1142 | UNKNOWN | English - United Kingdom | DIB |
200 | 7.30703 | 602 | UNKNOWN | English - United Kingdom | FIG |
201 | 3.38096 | 838 | UNKNOWN | English - United Kingdom | RT_DIALOG |
Imports
KERNEL32.dll |
Total processes
35
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2152 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | dinamita.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3904 | "C:\Users\admin\AppData\Local\Temp\dinamita.EXE" | C:\Users\admin\AppData\Local\Temp\dinamita.EXE | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
Total events
408
Read events
340
Write events
65
Delete events
3
Modification events
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_CURRENT_USER\Software\AdTools, Inc.\Connection |
| Operation: | write | Name: | Installed |
Value: 1 | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_CURRENT_USER\Software\AdTools, Inc.\Temp |
| Operation: | write | Name: | Dir |
Value: C:\Users\admin\AppData\Local\Temp\B1C\ | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_CURRENT_USER\Software\AdTools, Inc.\UserInfo |
| Operation: | write | Name: | Identifier |
Value: 64689f87-f85a-4c19-bccc-ea1e3491b78f | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dinamita_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dinamita_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dinamita_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dinamita_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dinamita_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dinamita_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3904) dinamita.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dinamita_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
5
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3904 | dinamita.EXE | C:\Users\admin\AppData\Local\Temp\B1C\B5B.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | dinamita.EXE | C:\Users\admin\AppData\Local\Temp\B1C\B5C.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | dinamita.EXE | C:\Users\admin\AppData\Local\Temp\B1C\B5D.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | dinamita.EXE | C:\Users\admin\AppData\Local\Temp\B1C\B6E.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | dinamita.EXE | C:\Users\admin\AppData\Local\Temp\B1C\B6F.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | dinamita.EXE | C:\Users\admin\AppData\Local\Temp\B1C\BCEE.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | dinamita.EXE | C:\Users\admin\AppData\Local\Temp\B1C\BCEF.tmp | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\track[1].asp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
5
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3904 | dinamita.EXE | POST | 302 | 103.224.182.245:80 | http://nasa.adtoolsinc.com/acts/tracking/track.asp | AU | — | — | malicious |
2108 | iexplore.exe | GET | 200 | 91.195.240.49:80 | http://ww17.nasa.adtoolsinc.com/acts/tracking/track.asp | DE | html | 19.4 Kb | whitelisted |
2152 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2108 | iexplore.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/js/jquery-1.11.3.custom.min.js | US | text | 24.5 Kb | whitelisted |
2108 | iexplore.exe | GET | 200 | 91.195.240.49:80 | http://ww17.nasa.adtoolsinc.com/search/tsc.php?200=MjU0OTY0NDY2&21=MTA0LjE5NC4yMjAuMTI4&681=MTUzOTI0OTg1NTNkN2E0YzVjNDQ2OTA1NDZjMTgzZGE3NThjMTYwMjY0&crc=1df19ddf0bdd829da949964b9debbe697c012361&cv=1 | DE | compressed | 19.4 Kb | whitelisted |
2108 | iexplore.exe | GET | 200 | 172.217.17.100:80 | http://www.google.com/adsense/domains/caf.js | US | text | 54.6 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3904 | dinamita.EXE | 103.224.182.245:80 | nasa.adtoolsinc.com | Trellian Pty. Limited | AU | malicious |
2152 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2108 | iexplore.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
2108 | iexplore.exe | 172.217.17.100:80 | www.google.com | Google Inc. | US | whitelisted |
2108 | iexplore.exe | 91.195.240.49:80 | ww17.nasa.adtoolsinc.com | SEDO GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nasa.adtoolsinc.com |
| malicious |
www.bing.com |
| whitelisted |
ww17.nasa.adtoolsinc.com |
| unknown |
img.sedoparking.com |
| whitelisted |
www.google.com |
| malicious |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
dinamita.EXE | Campaign ID: 5091.
File ID:Đ |
dinamita.EXE | Campaign ID: 5091.
File ID: 1.
Consumer ID: DWN1084759.
Tracking server: http://nasa.adtoolsinc.com/acts/tracking/track.asp.
|