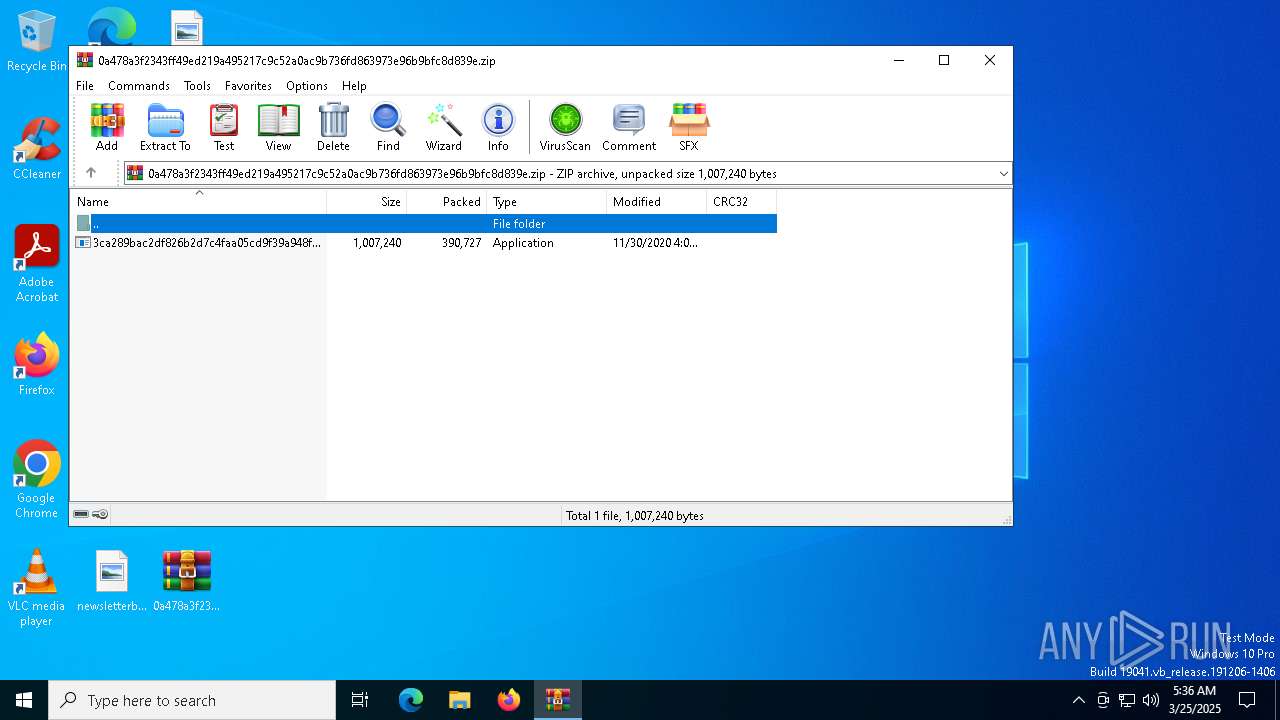
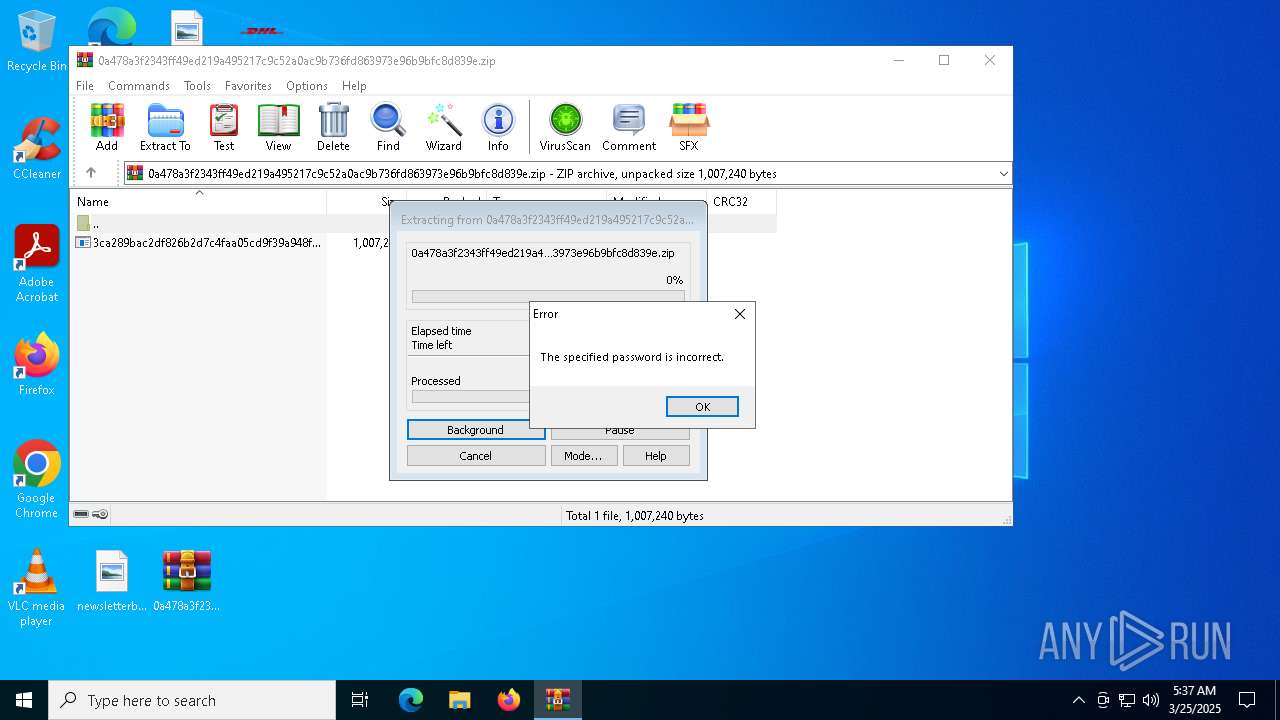
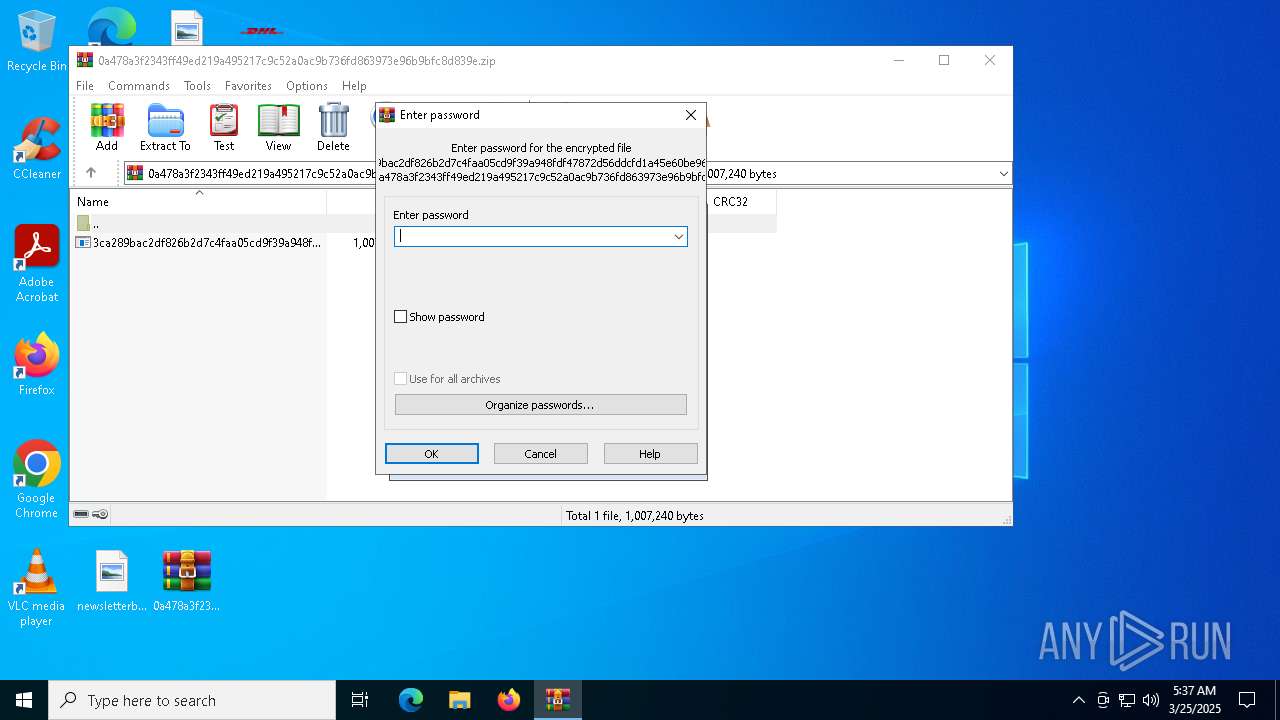
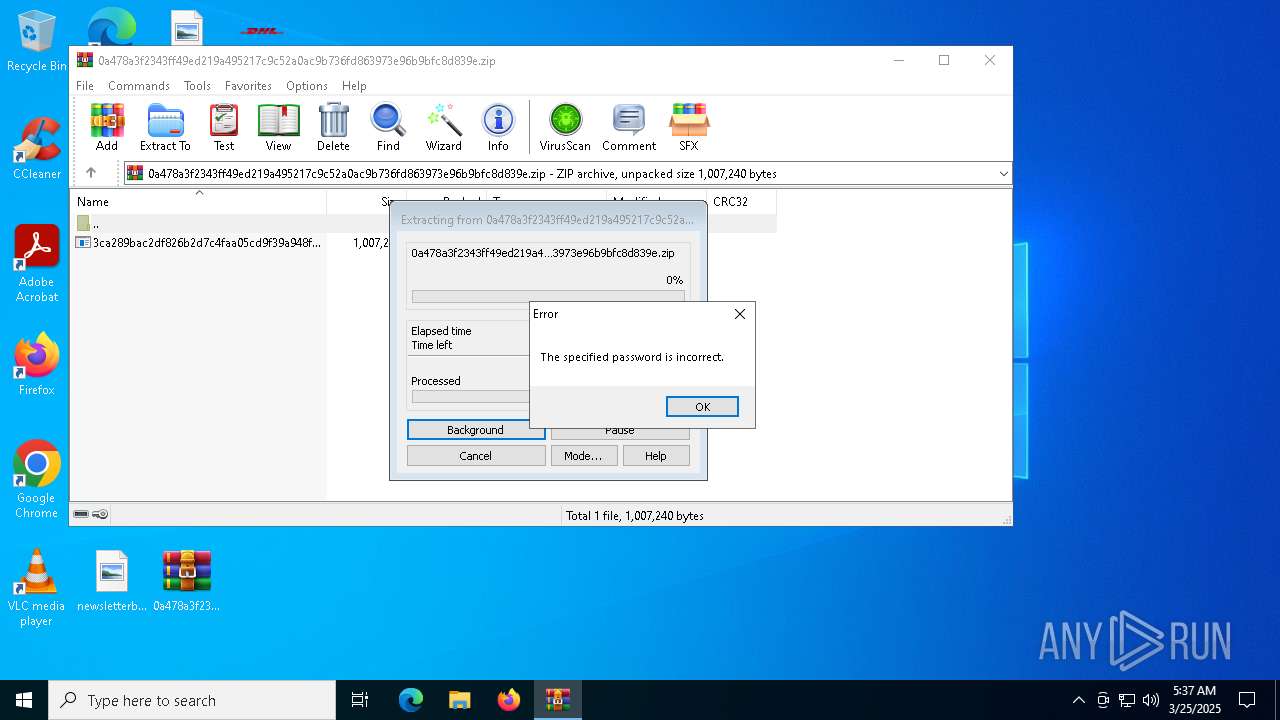
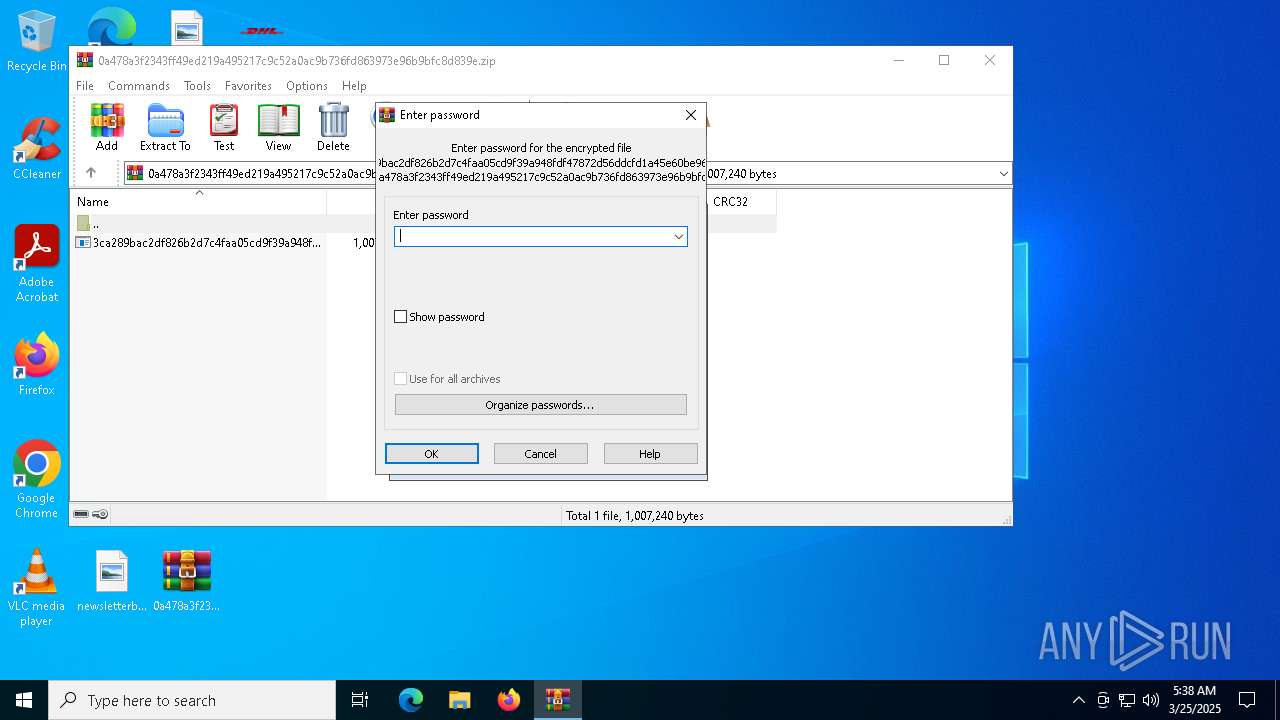
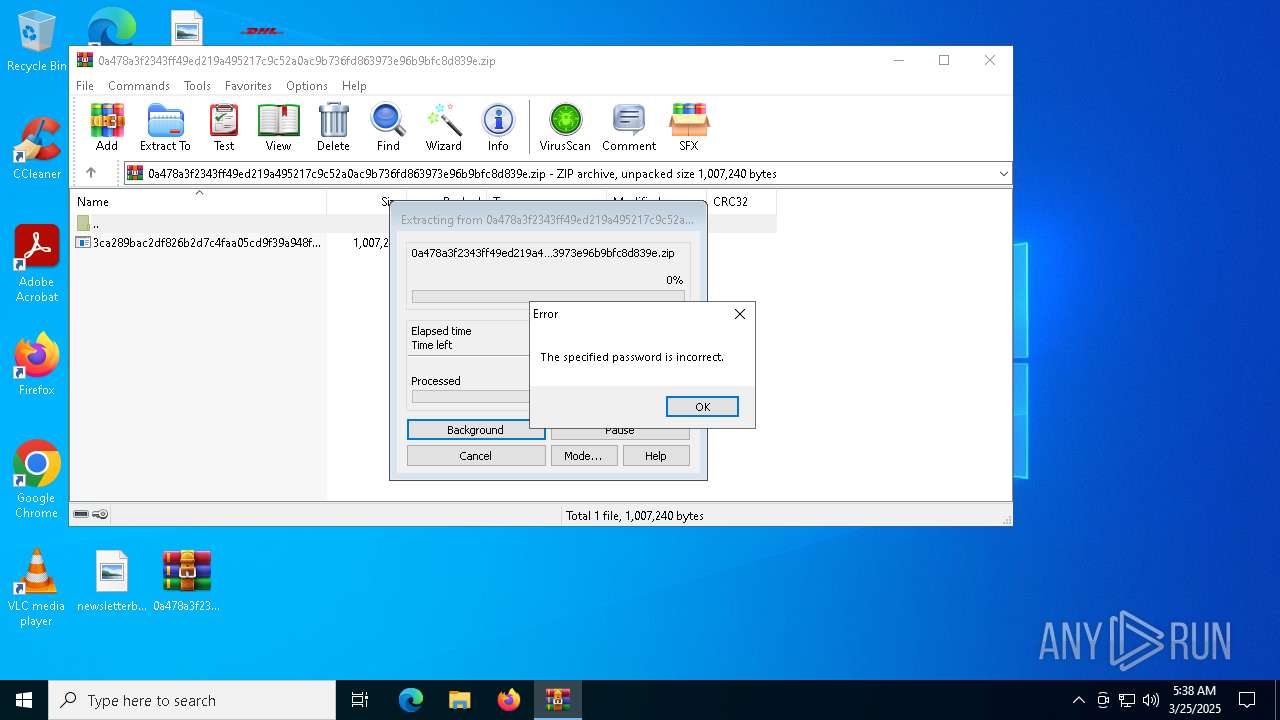
| File name: | 0a478a3f2343ff49ed219a495217c9c52a0ac9b736fd863973e96b9bfc8d839e.zip |
| Full analysis: | https://app.any.run/tasks/134186c7-6c15-4d03-a591-3123495ee864 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 05:36:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
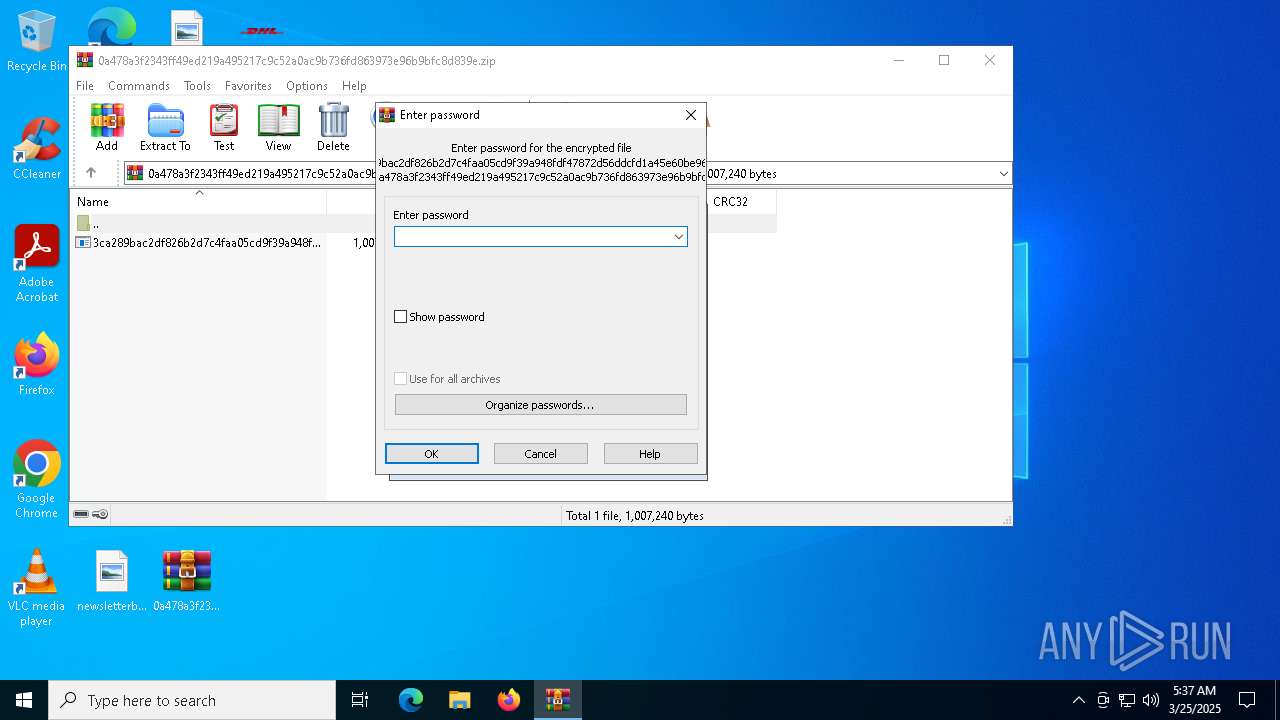
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 9AEE314D9BD3F6E8B636E94F1F25752C |
| SHA1: | 1288143C20F054C3B3FD42832CA80C840B479012 |
| SHA256: | 0A478A3F2343FF49ED219A495217C9C52A0AC9B736FD863973E96B9BFC8D839E |
| SSDEEP: | 12288:5As2TZYqkCws2WT2/7YjbsmH9Wg0cidcwIwv0C+CR2oOJh:m9ZBkzc2/UjbsQsg0vdzIwv0C+8Bsh |
MALICIOUS
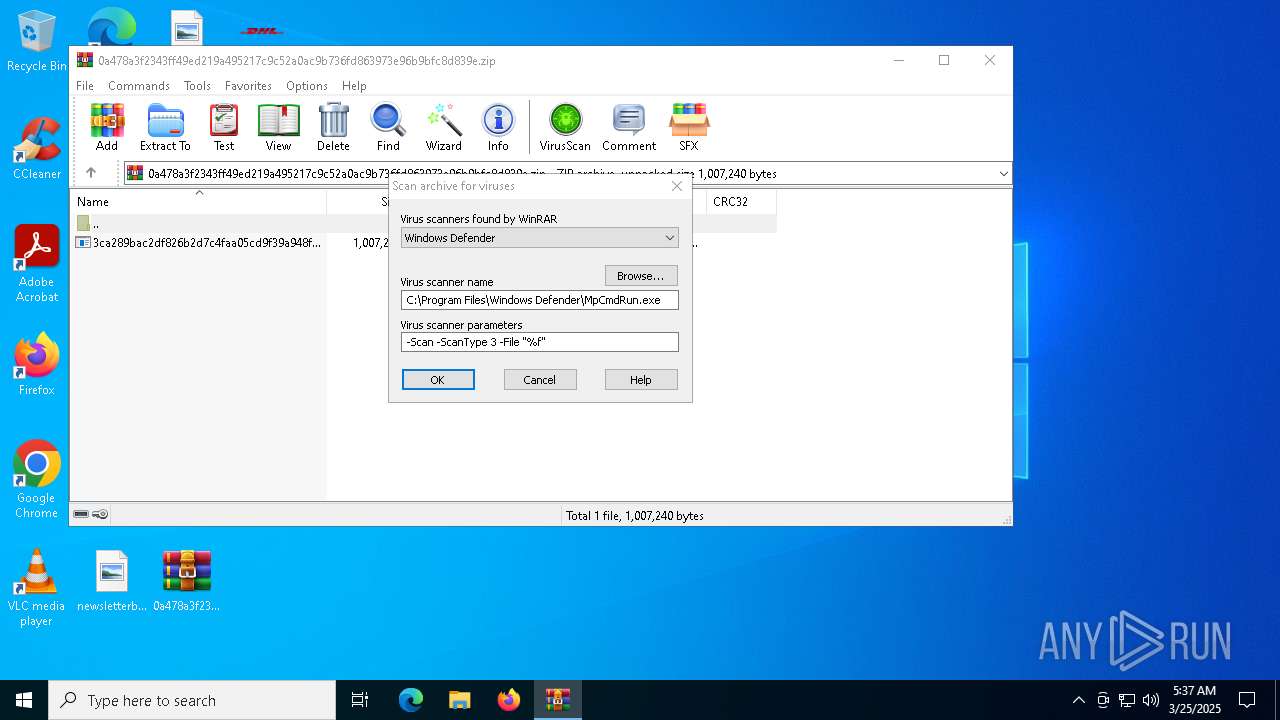
Generic archive extractor
- WinRAR.exe (PID: 7480)
Changes the autorun value in the registry
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7592)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 5868)
Executing a file with an untrusted certificate
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7956)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7980)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7968)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7592)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 2616)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 5868)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 5008)
SUSPICIOUS
Executable content was dropped or overwritten
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7592)
Application launched itself
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7592)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 5868)
Checks for external IP
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- svchost.exe (PID: 2196)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Reads security settings of Internet Explorer
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Starts CMD.EXE for commands execution
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Starts application with an unusual extension
- cmd.exe (PID: 8072)
- cmd.exe (PID: 5256)
Executing commands from a ".bat" file
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 8072)
- cmd.exe (PID: 5256)
INFO
Manual execution by a user
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7592)
Creates files or folders in the user directory
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7592)
Reads the computer name
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7592)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 5868)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 5008)
Checks supported languages
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7592)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- chcp.com (PID: 8140)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 5868)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
- chcp.com (PID: 6112)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 5008)
Reads the machine GUID from the registry
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Disables trace logs
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Checks proxy server information
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- slui.exe (PID: 7852)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Process checks computer location settings
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Changes the display of characters in the console
- cmd.exe (PID: 8072)
- cmd.exe (PID: 5256)
Reads the software policy settings
- slui.exe (PID: 7852)
Create files in a temporary directory
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 7992)
- 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:11:30 16:01:16 |
| ZipCRC: | 0x3e190704 |
| ZipCompressedSize: | 390727 |
| ZipUncompressedSize: | 1007240 |
| ZipFileName: | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe |
Total processes
141
Monitored processes
20
Malicious processes
5
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\Users\admin\Desktop\3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe" | C:\Users\admin\Desktop\3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | — | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Pidgin Installer Exit code: 4294967295 Version: 2.14.1.99 Modules
| |||||||||||||||
| 3884 | "C:\Users\admin\Desktop\3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe" | C:\Users\admin\Desktop\3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Pidgin Installer Exit code: 0 Version: 2.14.1.99 Modules
| |||||||||||||||
| 4652 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | "C:\Users\admin\Desktop\3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe" | C:\Users\admin\Desktop\3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Pidgin Installer Version: 2.14.1.99 Modules
| |||||||||||||||
| 5256 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\LxAOU50M1cMC.bat" " | C:\Windows\SysWOW64\cmd.exe | — | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5380 | ping -n 10 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5868 | "C:\Users\admin\Desktop\3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe" | C:\Users\admin\Desktop\3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Pidgin Installer Exit code: 0 Version: 2.14.1.99 Modules
| |||||||||||||||
| 6112 | chcp 65001 | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7480 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\0a478a3f2343ff49ed219a495217c9c52a0ac9b736fd863973e96b9bfc8d839e.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
9 439
Read events
9 409
Write events
30
Delete events
0
Modification events
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\0a478a3f2343ff49ed219a495217c9c52a0ac9b736fd863973e96b9bfc8d839e.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7992 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | C:\Users\admin\AppData\Local\Temp\yOQGRcBQBjRH.bat | text | |
MD5:FC92CAE1A5A1EAEB41F25C46E3294ED1 | SHA256:D63EBA1948B0DD653122CD84DABB4C1580B0F51DF8DA16BD9FBD4DC531C05090 | |||
| 7592 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\VideoLAN\vlc.exe | executable | |
MD5:2A02D57E4AD5117EB724BE65697AFD66 | SHA256:3CA289BAC2DF826B2D7C4FAA05CD9F39A948FDF47872D56DDCFD1A45E60BE963 | |||
| 3884 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | C:\Users\admin\AppData\Local\Temp\LxAOU50M1cMC.bat | text | |
MD5:83661D968A82EB09A2F2C10DF3C26FD4 | SHA256:30DFBC5D0A5AFF40AB304918E8AB2209910F078AA8C60C6489606A237AC722FA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
8
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7992 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
3884 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
5024 | RUXIMICS.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5024 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5024 | RUXIMICS.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7368 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7992 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
7852 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3884 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
ip-api.com |
| whitelisted |
devils.shacknet.us |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.shacknet .us Domain |
7992 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
7992 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3884 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.shacknet .us Domain |
3884 | 3ca289bac2df826b2d7c4faa05cd9f39a948fdf47872d56ddcfd1a45e60be963.exe | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |