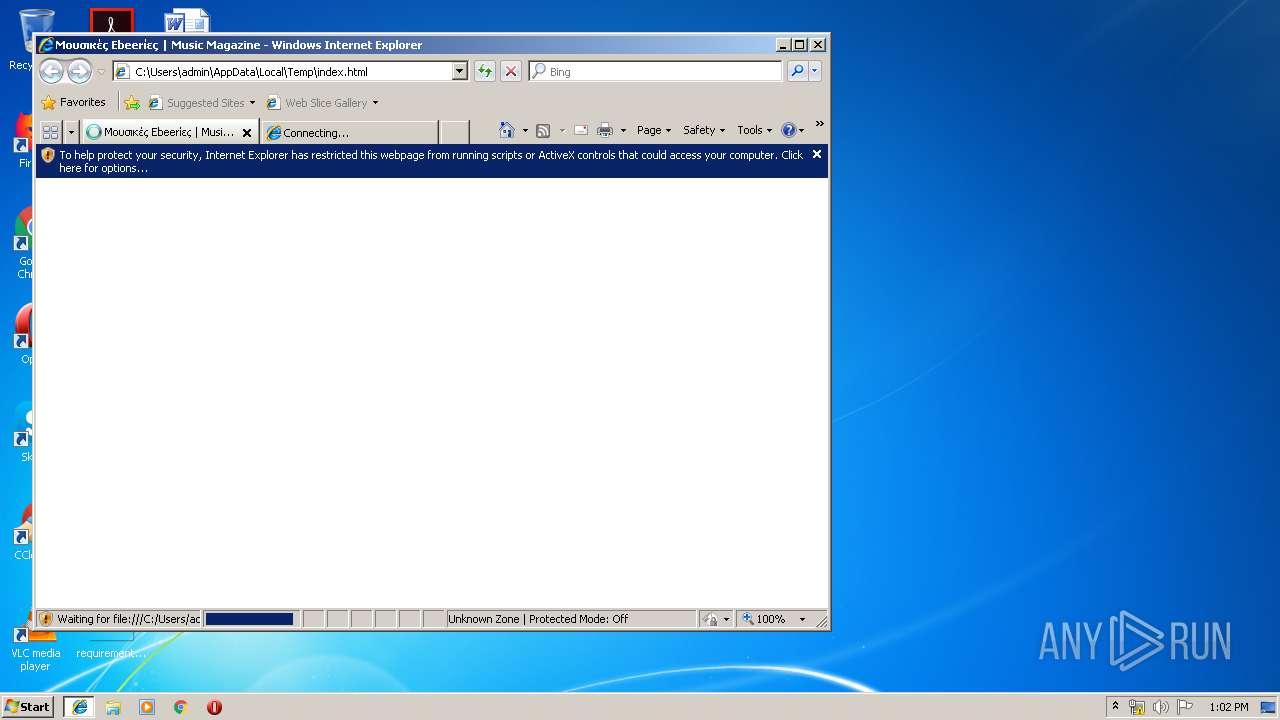
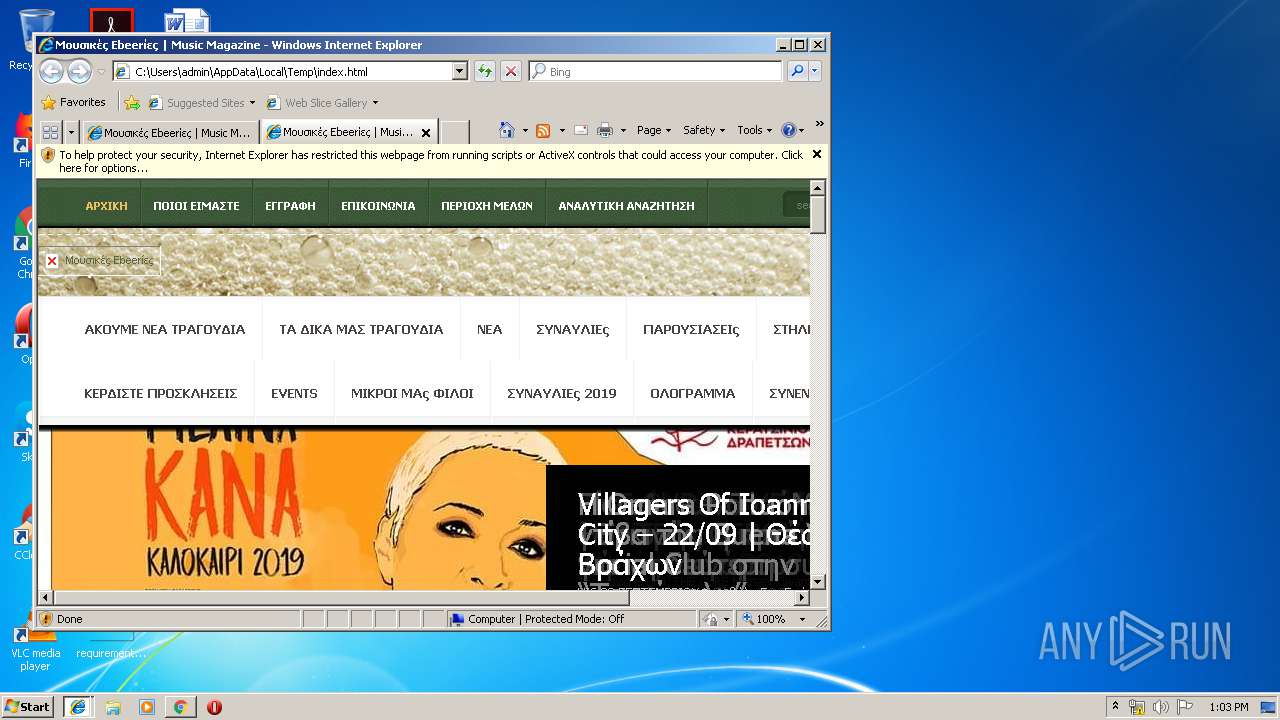
| File name: | index.html |
| Full analysis: | https://app.any.run/tasks/32fa0081-8aba-48d3-a14f-a0b3aa105db8 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 12:02:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 9E589D056F68BBC5A81F7C0C2BE59938 |
| SHA1: | D65F7EDA84286F686CBECBEDAC8C62E3A02C83A9 |
| SHA256: | 0A3F3A695DD33C7BF61B6DD00BD1FCB4043D482496BCE97216C95B6FF0B82FBC |
| SSDEEP: | 768:S2sdtb0KRvwiV7+EdHtrhLAMRk3bzfAmGq89w+u/BrsaO6Y5n:S2sdtb0KRvZn1R2AmGq89wzrsaO6Y5n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3012)
INFO
Application launched itself
- iexplore.exe (PID: 3840)
- chrome.exe (PID: 3012)
Reads settings of System Certificates
- chrome.exe (PID: 3056)
Creates files in the user directory
- chrome.exe (PID: 3012)
- iexplore.exe (PID: 3588)
Changes internet zones settings
- iexplore.exe (PID: 3840)
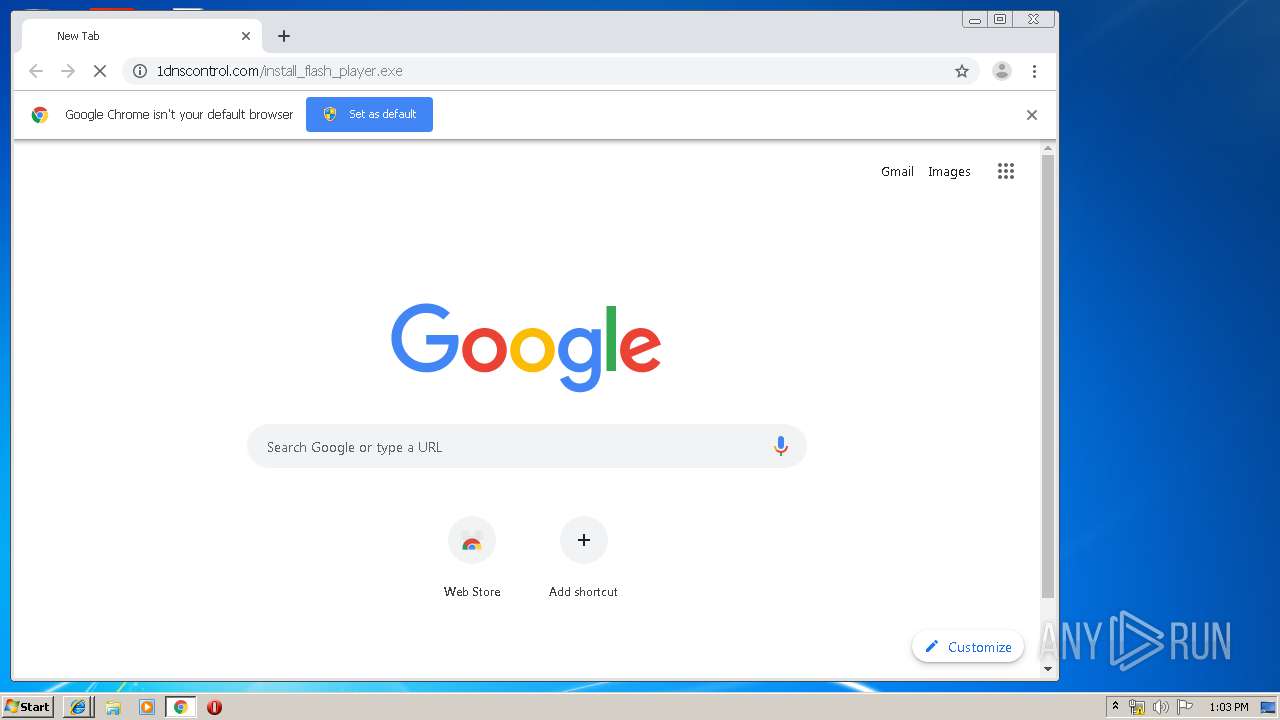
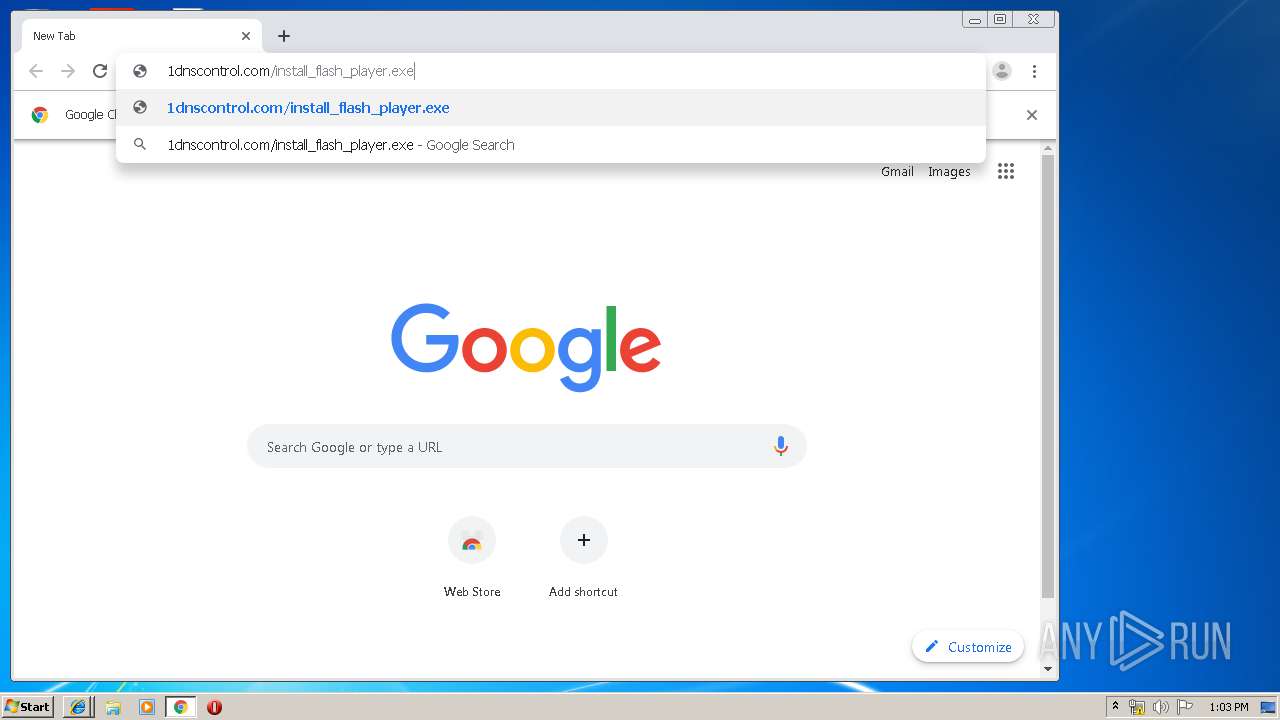
Manual execution by user
- chrome.exe (PID: 3012)
Reads Internet Cache Settings
- iexplore.exe (PID: 3588)
- iexplore.exe (PID: 2704)
Reads internet explorer settings
- iexplore.exe (PID: 3588)
- iexplore.exe (PID: 2704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=UTF-8 |
|---|---|
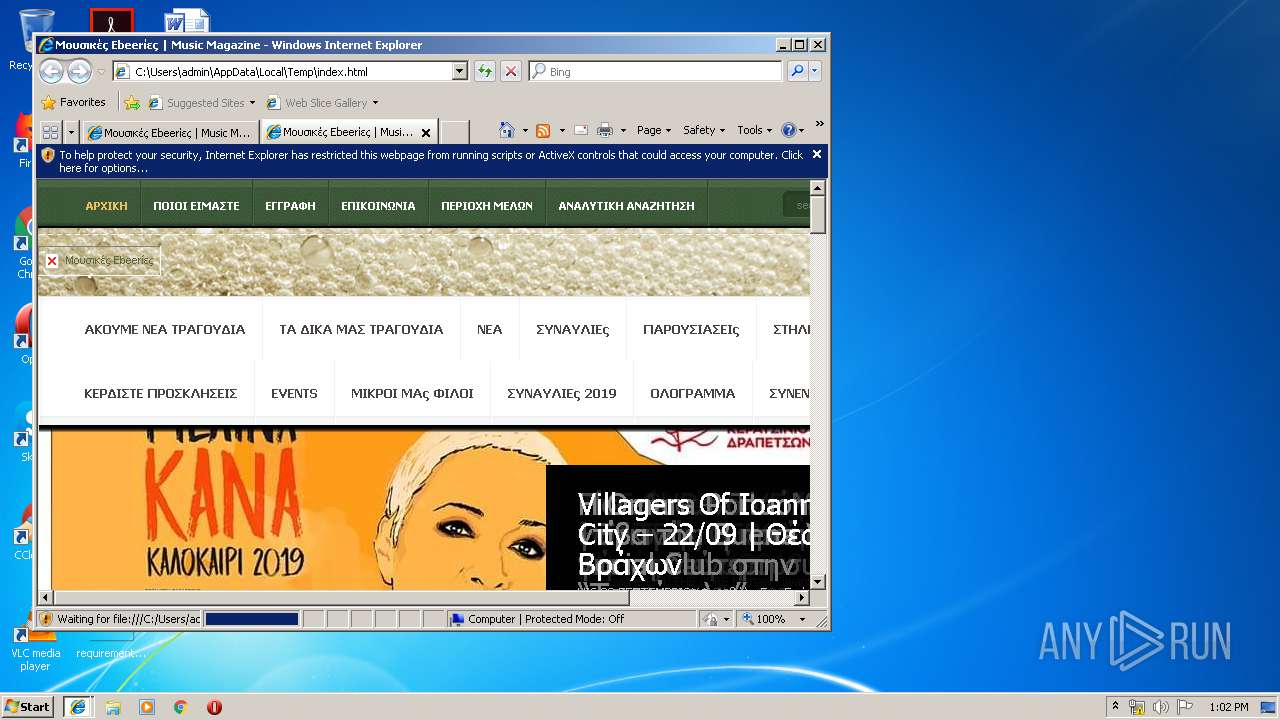
| Title: | Μουσικές Εbeerίες | Music Magazine |
| Generator: | WordPress 5.2.2 |
| et_featured_auto_speed: | 7000 |
| et_disable_toptier: | - |
| et_featured_slider_pause: | 1 |
| et_featured_slider_auto: | 1 |
| et_theme_folder: | http://www.mousikesebeeries.gr/wp-content/themes/Aggregate |
| msapplicationTileImage: | http://www.mousikesebeeries.gr/wp-content/uploads/2017/10/cropped-10968441_1036482156365415_1857211883644493081_n-1-270x270.jpg |
Total processes
72
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3187017290461065299 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=43721581970492147 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4536935833880368466 --mojo-platform-channel-handle=3676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8806928332951860751 --mojo-platform-channel-handle=2704 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18216936263221105275 --mojo-platform-channel-handle=3720 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12933792428330123061 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10407970679628609900 --mojo-platform-channel-handle=3776 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1736084972487210735 --mojo-platform-channel-handle=2540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8930541433834441093 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,12334619087157926856,3861245176214691132,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=293179772327604212 --mojo-platform-channel-handle=3304 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 178
Read events
996
Write events
176
Delete events
6
Modification events
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000078000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {EF1C96E1-A953-11E9-95C0-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700040012000C00020026004D01 | |||
Executable files
0
Suspicious files
44
Text files
449
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\css[2].txt | text | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\ie8style[1].css | text | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\style-Green[1].css | text | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\t5tuIRIUKY-TFHXHc2w[1].eot | eot | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\css[3].txt | text | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\style[1].css | text | |
MD5:— | SHA256:— | |||
| 2704 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\SlGVmQWMvZQIdix7AFxXkHNSaQ[1].eot | eot | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\page_templates[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
295
TCP/UDP connections
74
DNS requests
34
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3588 | iexplore.exe | GET | 200 | 145.239.7.103:80 | http://www.mousikesebeeries.gr/wp-content/themes/Aggregate/css/ie8style.css | GB | text | 35 b | suspicious |
3588 | iexplore.exe | GET | 200 | 145.239.7.103:80 | http://www.mousikesebeeries.gr/wp-content/themes/Aggregate/style.css | GB | text | 31.9 Kb | suspicious |
3588 | iexplore.exe | GET | 200 | 145.239.7.103:80 | http://www.mousikesebeeries.gr/wp-content/themes/Aggregate/epanel/page_templates/page_templates.css | GB | text | 8.55 Kb | suspicious |
3588 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://fonts.gstatic.com/s/kreon/v14/t5tuIRIUKY-TFHXHc2w.eot | US | eot | 15.1 Kb | whitelisted |
2704 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://fonts.gstatic.com/s/droidsans/v9/SlGVmQWMvZQIdix7AFxXkHNSaQ.eot | US | eot | 21.5 Kb | whitelisted |
2704 | iexplore.exe | GET | 200 | 145.239.7.103:80 | http://www.mousikesebeeries.gr/wp-content/themes/Aggregate/epanel/page_templates/page_templates.css | GB | text | 8.55 Kb | suspicious |
3588 | iexplore.exe | GET | 200 | 145.239.7.103:80 | http://www.mousikesebeeries.gr/wp-content/themes/Aggregate/style-Green.css | GB | text | 508 b | suspicious |
3588 | iexplore.exe | GET | 200 | 172.217.22.74:80 | http://fonts.googleapis.com/css?family=Kreon:light,regular | US | text | 157 b | whitelisted |
3588 | iexplore.exe | GET | 200 | 145.239.7.103:80 | http://www.mousikesebeeries.gr/wp-includes/css/dist/block-library/style.min.css?ver=5.2.2 | GB | text | 28.6 Kb | suspicious |
3588 | iexplore.exe | GET | 200 | 145.239.7.103:80 | http://www.mousikesebeeries.gr/wp-content/themes/Aggregate/css/colorpicker.css | GB | text | 3.25 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2704 | iexplore.exe | 172.217.18.99:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.99:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
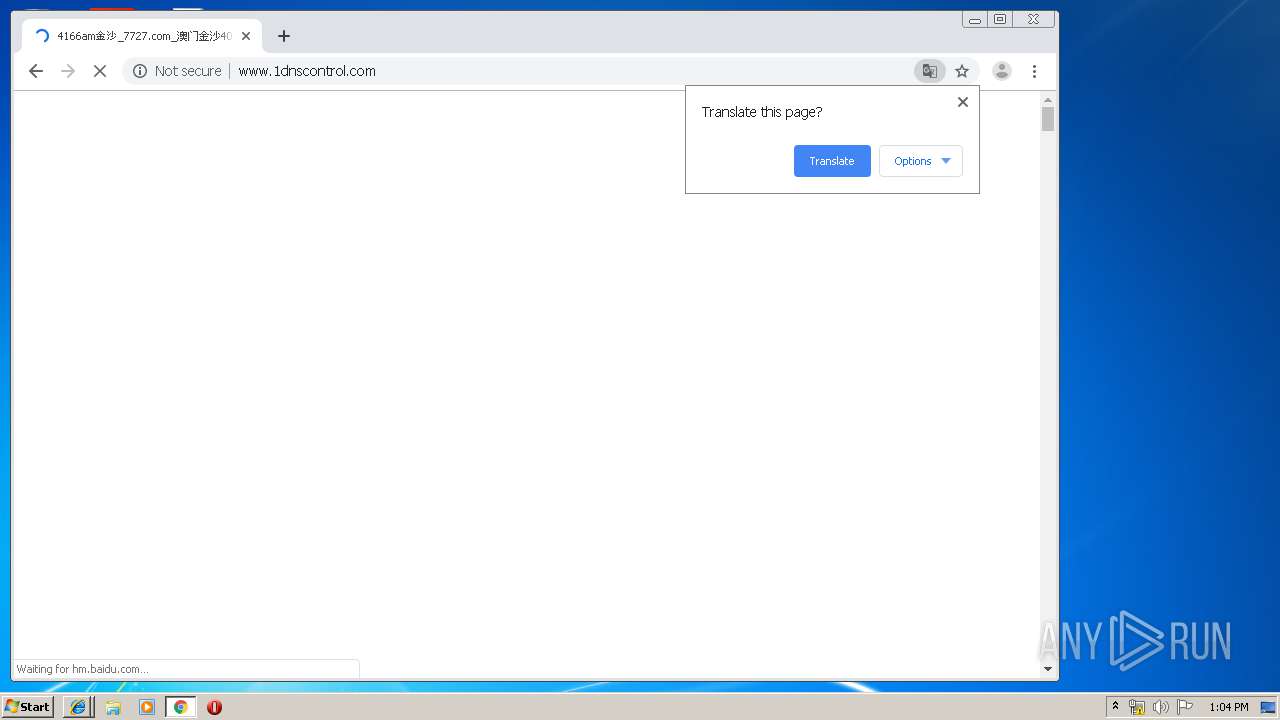
— | — | 217.182.164.9:443 | coin-hive.com | OVH SAS | FR | suspicious |
3056 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2704 | iexplore.exe | 145.239.7.103:80 | www.mousikesebeeries.gr | OVH SAS | GB | suspicious |
3056 | chrome.exe | 172.217.22.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3056 | chrome.exe | 172.217.16.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3588 | iexplore.exe | 172.217.22.74:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.74:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3056 | chrome.exe | 172.217.22.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mousikesebeeries.gr |
| suspicious |
fonts.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
coin-hive.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2704 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS Observed Coin-Hive In Browser Mining Domain (coin-hive .com in TLS SNI) |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3056 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |