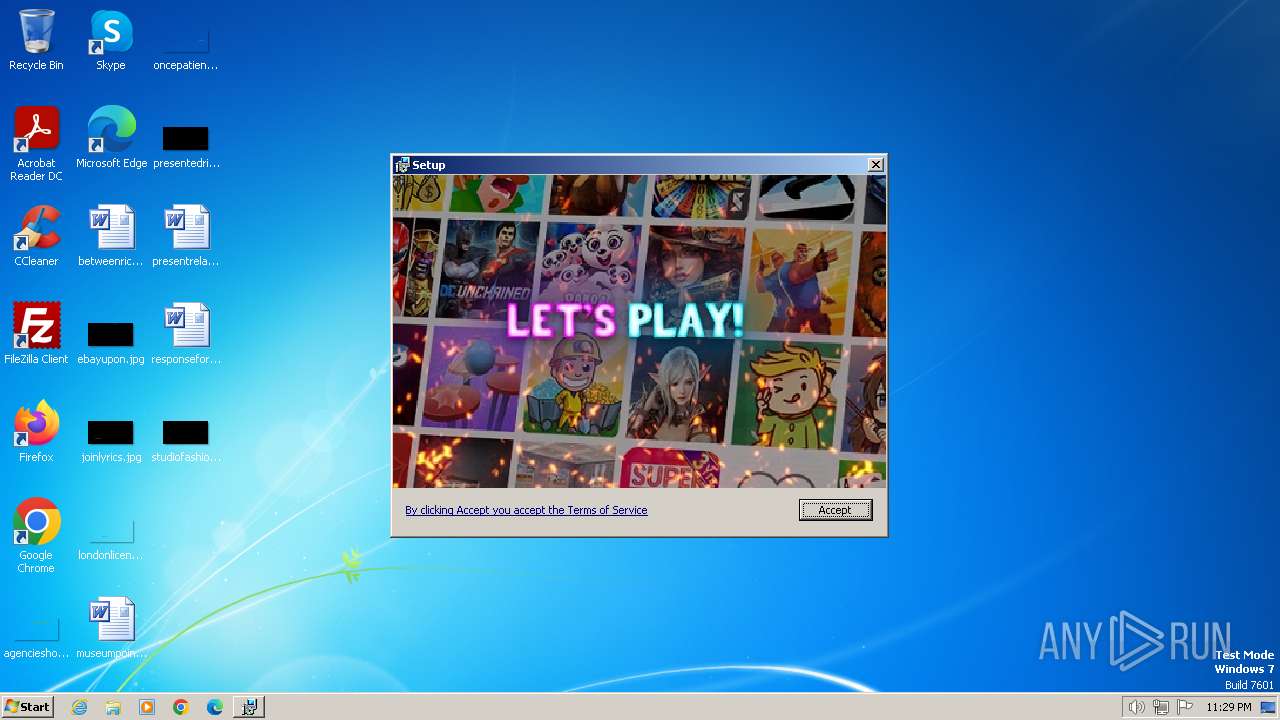
| File name: | com.steam.1228610_installer_46155619.msi |
| Full analysis: | https://app.any.run/tasks/d0b5aea4-9cd3-4a85-baa1-c54c912d7d08 |
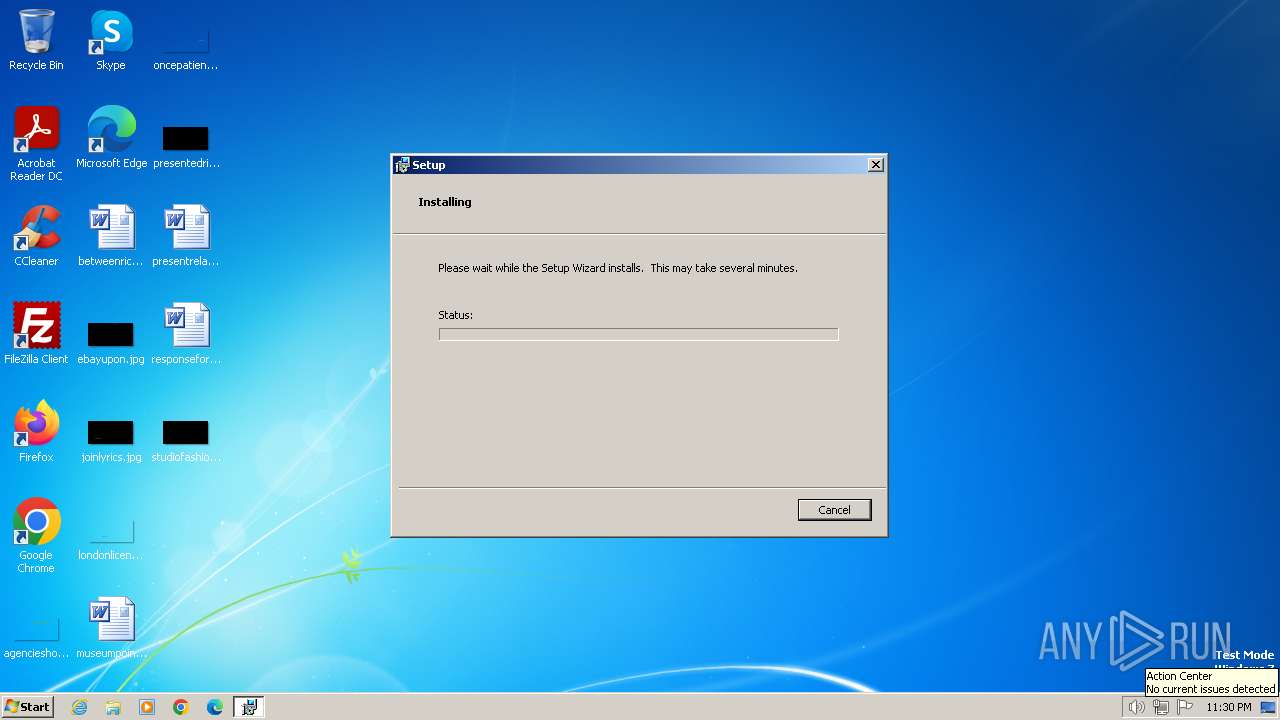
| Verdict: | Malicious activity |
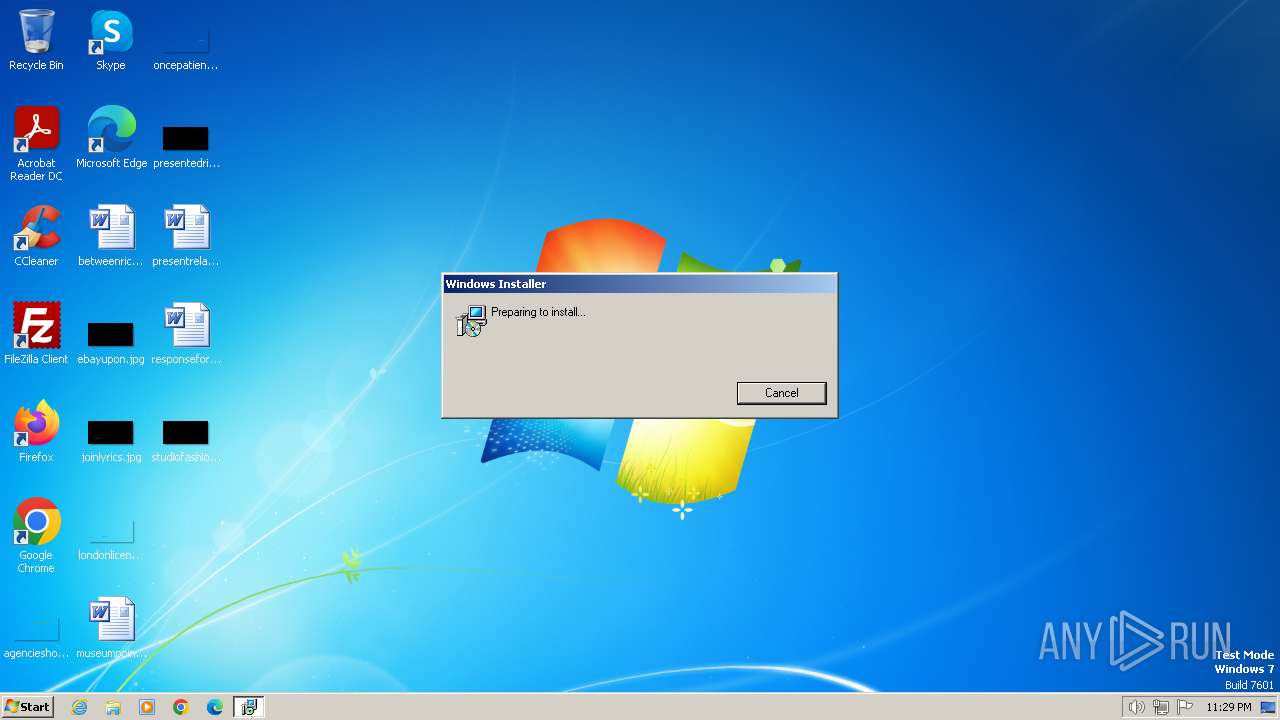
| Analysis date: | January 17, 2024, 23:29:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 15:06:51 2020, Security: 0, Code page: 1252, Revision Number: {25521D1A-AA3C-4EF0-93EA-2F70B86B47E9}, Number of Words: 10, Subject: Installer Assistant, Author: Eclipse Media Inc, Name of Creating Application: Installer Assistant, Template: ;1033, Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Sun Dec 24 04:16:12 2023, Number of Pages: 200 |
| MD5: | 1248BD7C2F491C6F5ADA1C2933CCE5A3 |
| SHA1: | BA1515DFCC9ED5B597C14F0BE62DE69C1B09F901 |
| SHA256: | 0A37D8D479FEDA4D86F19BA6FB87D1E59349613B6265BB355880F1B278900B24 |
| SSDEEP: | 98304:aAAfqNGhwz/bqac+oUKi4snyJHLxwE1uQ3okdcsC3Cs73xQc3srKdB0lVTxK49IB:2Dw |
MALICIOUS
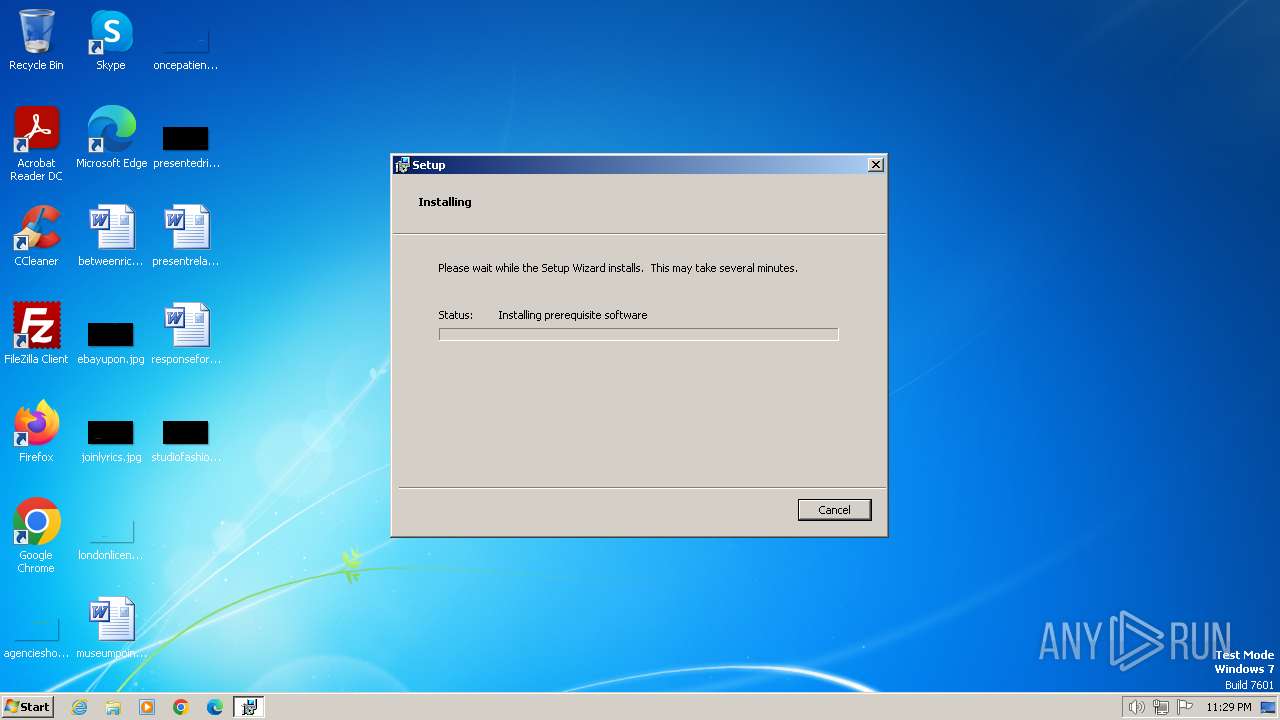
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2028)
- MSI9BCC.tmp (PID: 3528)
- msiexec.exe (PID: 148)
Bypass execution policy to execute commands
- powershell.exe (PID: 548)
- powershell.exe (PID: 2172)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 3064)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 2796)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3688)
- powershell.exe (PID: 3512)
- powershell.exe (PID: 3792)
- powershell.exe (PID: 452)
- powershell.exe (PID: 2880)
- powershell.exe (PID: 2664)
Drops the executable file immediately after the start
- msiexec.exe (PID: 2068)
- msiexec.exe (PID: 2044)
- 7za.exe (PID: 2356)
- msiexec.exe (PID: 148)
SUSPICIOUS
Reads the Internet Settings
- msiexec.exe (PID: 2044)
- powershell.exe (PID: 2172)
- msiexec.exe (PID: 2420)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 3064)
- powershell.exe (PID: 2796)
- powershell.exe (PID: 3268)
- MSI9BCC.tmp (PID: 3528)
- powershell.exe (PID: 3688)
- powershell.exe (PID: 3512)
- powershell.exe (PID: 3792)
- powershell.exe (PID: 452)
- powershell.exe (PID: 3240)
- msiexec.exe (PID: 148)
- powershell.exe (PID: 2664)
- powershell.exe (PID: 2880)
The process executes Powershell scripts
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2028)
- msiexec.exe (PID: 148)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2028)
- msiexec.exe (PID: 148)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2028)
- MSI9BCC.tmp (PID: 3528)
- msiexec.exe (PID: 148)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2028)
- MSI9BCC.tmp (PID: 3528)
- msiexec.exe (PID: 148)
Unusual connection from system programs
- powershell.exe (PID: 2172)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 3064)
- powershell.exe (PID: 2796)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3792)
- powershell.exe (PID: 3688)
- powershell.exe (PID: 2880)
- powershell.exe (PID: 452)
- powershell.exe (PID: 3512)
Searches for installed software
- powershell.exe (PID: 2172)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2068)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 2068)
Executable content was dropped or overwritten
- 7za.exe (PID: 2356)
- powershell.exe (PID: 2880)
Probably obfuscated PowerShell command line is found
- MSI9BCC.tmp (PID: 3528)
Checks Windows Trust Settings
- msiexec.exe (PID: 2068)
- msiexec.exe (PID: 148)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3792)
- powershell.exe (PID: 3512)
Executes as Windows Service
- VSSVC.exe (PID: 1044)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 148)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 2420)
The Powershell connects to the Internet
- powershell.exe (PID: 3688)
INFO
Checks supported languages
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2068)
- msiexec.exe (PID: 2028)
- 7za.exe (PID: 2356)
- MSI9BCC.tmp (PID: 3528)
- msiexec.exe (PID: 148)
Creates files or folders in the user directory
- msiexec.exe (PID: 2044)
- powershell.exe (PID: 548)
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2068)
- 7za.exe (PID: 2356)
- powershell.exe (PID: 3268)
- msiexec.exe (PID: 148)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2068)
- msiexec.exe (PID: 2028)
- msiexec.exe (PID: 148)
Create files in a temporary directory
- msiexec.exe (PID: 2044)
- msiexec.exe (PID: 2420)
- powershell.exe (PID: 548)
- powershell.exe (PID: 2172)
- msiexec.exe (PID: 2028)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 2748)
- msiexec.exe (PID: 2068)
- powershell.exe (PID: 3064)
- powershell.exe (PID: 2796)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3512)
- msiexec.exe (PID: 148)
- powershell.exe (PID: 452)
- powershell.exe (PID: 2664)
- powershell.exe (PID: 3792)
- powershell.exe (PID: 2880)
Reads the computer name
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2028)
- msiexec.exe (PID: 2068)
- 7za.exe (PID: 2356)
- MSI9BCC.tmp (PID: 3528)
- msiexec.exe (PID: 148)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2044)
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2068)
- msiexec.exe (PID: 148)
Reads security settings of Internet Explorer
- powershell.exe (PID: 548)
- powershell.exe (PID: 2172)
- msiexec.exe (PID: 2044)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 2748)
- powershell.exe (PID: 3064)
- powershell.exe (PID: 2796)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 3512)
- powershell.exe (PID: 3792)
- powershell.exe (PID: 452)
- powershell.exe (PID: 2880)
- powershell.exe (PID: 2664)
Application launched itself
- msiexec.exe (PID: 2420)
- msiexec.exe (PID: 2068)
Reads Environment values
- msiexec.exe (PID: 2028)
- msiexec.exe (PID: 2420)
- MSI9BCC.tmp (PID: 3528)
- msiexec.exe (PID: 148)
Starts application with an unusual extension
- msiexec.exe (PID: 2068)
Checks proxy server information
- msiexec.exe (PID: 148)
Drops the executable file immediately after the start
- powershell.exe (PID: 2880)
Reads settings of System Certificates
- powershell.exe (PID: 2880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| ModifyDate: | 2020:09:18 14:06:51 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {25521D1A-AA3C-4EF0-93EA-2F70B86B47E9} |
| Words: | 10 |
| Subject: | Installer Assistant |
| Author: | Eclipse Media Inc |
| LastModifiedBy: | - |
| Software: | Installer Assistant |
| Template: | ;1033 |
| Comments: | - |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2023:12:24 04:16:12 |
| Pages: | 200 |
Total processes
80
Monitored processes
29
Malicious processes
7
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | C:\Windows\system32\MsiExec.exe -Embedding F5A3C2513D015E240E8A4DB6DB8CA3A7 | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 452 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssBB9E.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msiBB8B.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scrBB9C.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scrBB9D.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 548 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss4D.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi4A.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr4B.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr4C.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1044 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1220 | "C:\Windows\system32\schtasks.exe" /delete /tn "WC ScheduledTask" /F | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss50F0.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2028 | C:\Windows\system32\MsiExec.exe -Embedding 74E9E44929A0A8965C4785B6A75F572E | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\com.steam.1228610_installer_46155619.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss543.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi531.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr532.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr533.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
33 002
Read events
32 845
Write events
131
Delete events
26
Modification events
| (PID) Process: | (2044) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2420) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2420) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2420) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2420) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2068) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\182\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2068) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\182 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2068) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\e2970.rbs |
Value: 31082909 | |||
| (PID) Process: | (2068) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\e2970.rbsLow |
Value: 416395936 | |||
| (PID) Process: | (2068) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
52
Suspicious files
72
Text files
44
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss4D.ps1 | — | |
MD5:— | SHA256:— | |||
| 2420 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi4A.txt | — | |
MD5:— | SHA256:— | |||
| 2420 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr4C.txt | — | |
MD5:— | SHA256:— | |||
| 2044 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2044 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C5C8CC0A7FE31816B4641D0465402560 | der | |
MD5:E94FB54871208C00DF70F708AC47085B | SHA256:7B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF86 | |||
| 548 | powershell.exe | C:\Users\admin\AppData\Roaming\BBWC\intermediate.dat | text | |
MD5:EBAF35B43B68AA14C1F4FDB9608BC3BA | SHA256:6CB626112EDFD4F410A34050A7288C56400F43A68E00936BF4262EBEAD24450E | |||
| 2044 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C5C8CC0A7FE31816B4641D0465402560 | binary | |
MD5:68C9236F2881681514F736BA00A6B196 | SHA256:9E05830C9175CFA421EEB32FBDB35FA91366ADD2DB413C206F063249804788A6 | |||
| 2420 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi531.txt | — | |
MD5:— | SHA256:— | |||
| 2420 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr532.ps1 | — | |
MD5:— | SHA256:— | |||
| 2420 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr533.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
30
DNS requests
13
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2572 | powershell.exe | POST | 200 | 18.66.121.3:80 | http://d6ahvgn4x5k57.cloudfront.net/ | unknown | binary | 19 b | unknown |
2044 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://secure.globalsign.com/cacert/codesigningrootr45.crt | unknown | binary | 1.37 Kb | unknown |
1904 | powershell.exe | POST | 200 | 18.66.121.3:80 | http://d6ahvgn4x5k57.cloudfront.net/ | unknown | binary | 19 b | unknown |
2044 | msiexec.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?cfb9a91dcbacd214 | unknown | compressed | 65.2 Kb | unknown |
2572 | powershell.exe | POST | 200 | 18.66.121.3:80 | http://d6ahvgn4x5k57.cloudfront.net/ | unknown | binary | 19 b | unknown |
2572 | powershell.exe | POST | 200 | 18.66.121.3:80 | http://d6ahvgn4x5k57.cloudfront.net/ | unknown | binary | 19 b | unknown |
2748 | powershell.exe | POST | 200 | 18.66.121.3:80 | http://d6ahvgn4x5k57.cloudfront.net/ | unknown | binary | 19 b | unknown |
1904 | powershell.exe | POST | 200 | 18.66.121.3:80 | http://d6ahvgn4x5k57.cloudfront.net/ | unknown | binary | 19 b | unknown |
3064 | powershell.exe | POST | 200 | 18.66.121.3:80 | http://d6ahvgn4x5k57.cloudfront.net/ | unknown | binary | 19 b | unknown |
3064 | powershell.exe | POST | 200 | 18.66.121.3:80 | http://d6ahvgn4x5k57.cloudfront.net/ | unknown | binary | 19 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2044 | msiexec.exe | 104.18.21.226:80 | secure.globalsign.com | CLOUDFLARENET | — | shared |
2044 | msiexec.exe | 184.24.77.194:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2172 | powershell.exe | 18.66.137.7:80 | dezxv1d7trgwl.cloudfront.net | AMAZON-02 | US | unknown |
2572 | powershell.exe | 18.66.121.3:80 | d6ahvgn4x5k57.cloudfront.net | AMAZON-02 | US | unknown |
1904 | powershell.exe | 18.66.121.3:80 | d6ahvgn4x5k57.cloudfront.net | AMAZON-02 | US | unknown |
2748 | powershell.exe | 18.66.121.3:80 | d6ahvgn4x5k57.cloudfront.net | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
secure.globalsign.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
dezxv1d7trgwl.cloudfront.net |
| unknown |
d6ahvgn4x5k57.cloudfront.net |
| unknown |
dhb63vq2dmigo.cloudfront.net |
| unknown |
x8k9eh.com |
| unknown |
mbdl219.com |
| shared |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3268 | powershell.exe | Potentially Bad Traffic | ET INFO POST to Double Slash in URI |
3268 | powershell.exe | Potentially Bad Traffic | ET INFO POST to Double Slash in URI |
3268 | powershell.exe | Potentially Bad Traffic | ET INFO POST to Double Slash in URI |
3688 | powershell.exe | Potentially Bad Traffic | ET INFO POST to Double Slash in URI |
3688 | powershell.exe | Potentially Bad Traffic | ET INFO POST to Double Slash in URI |