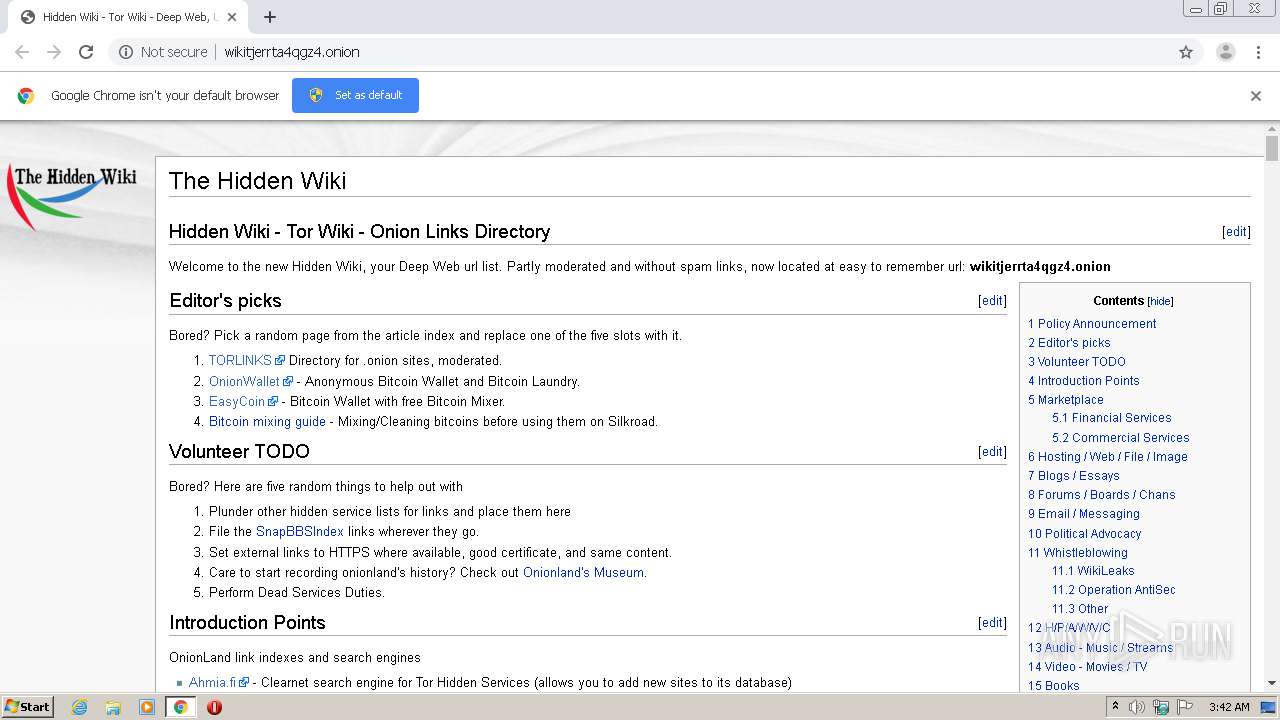
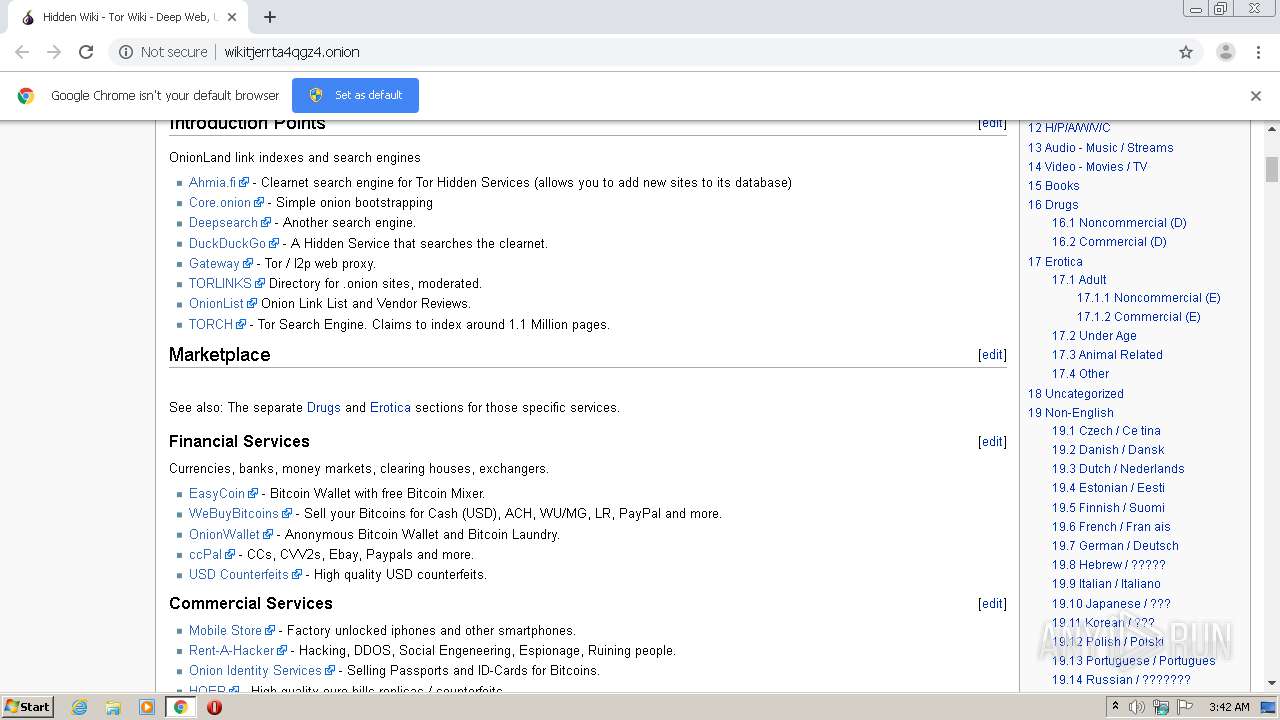
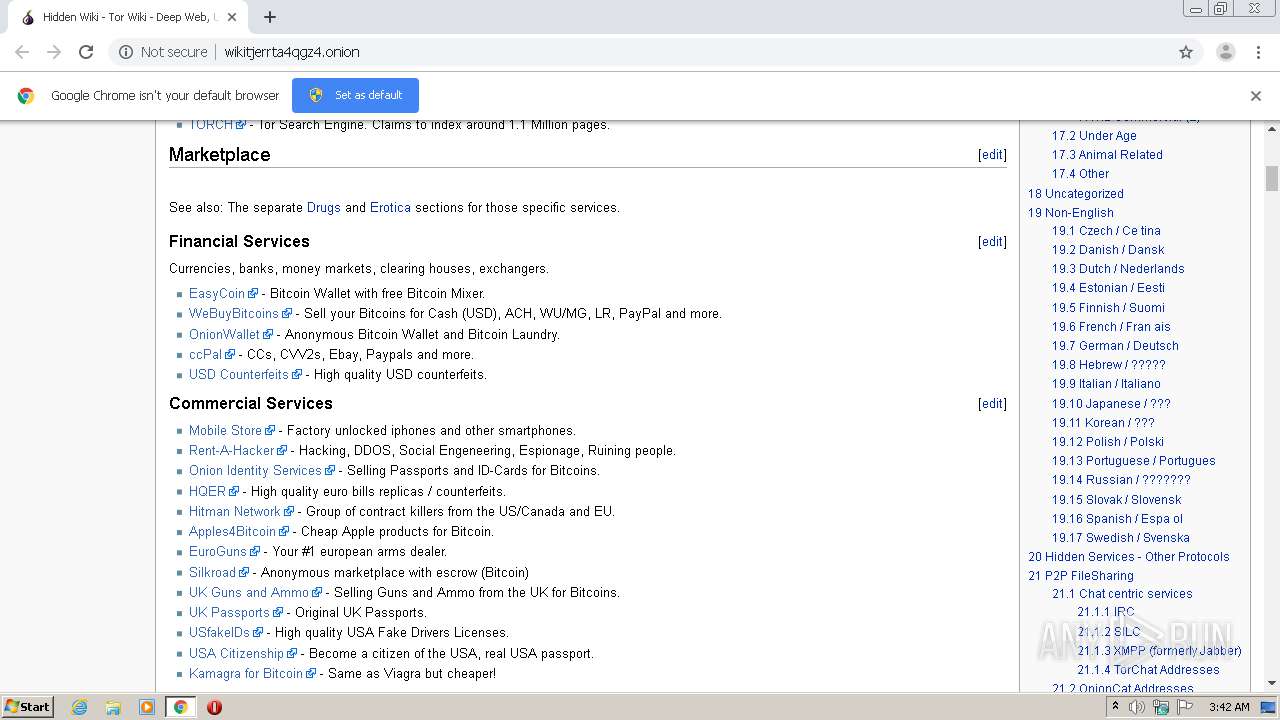
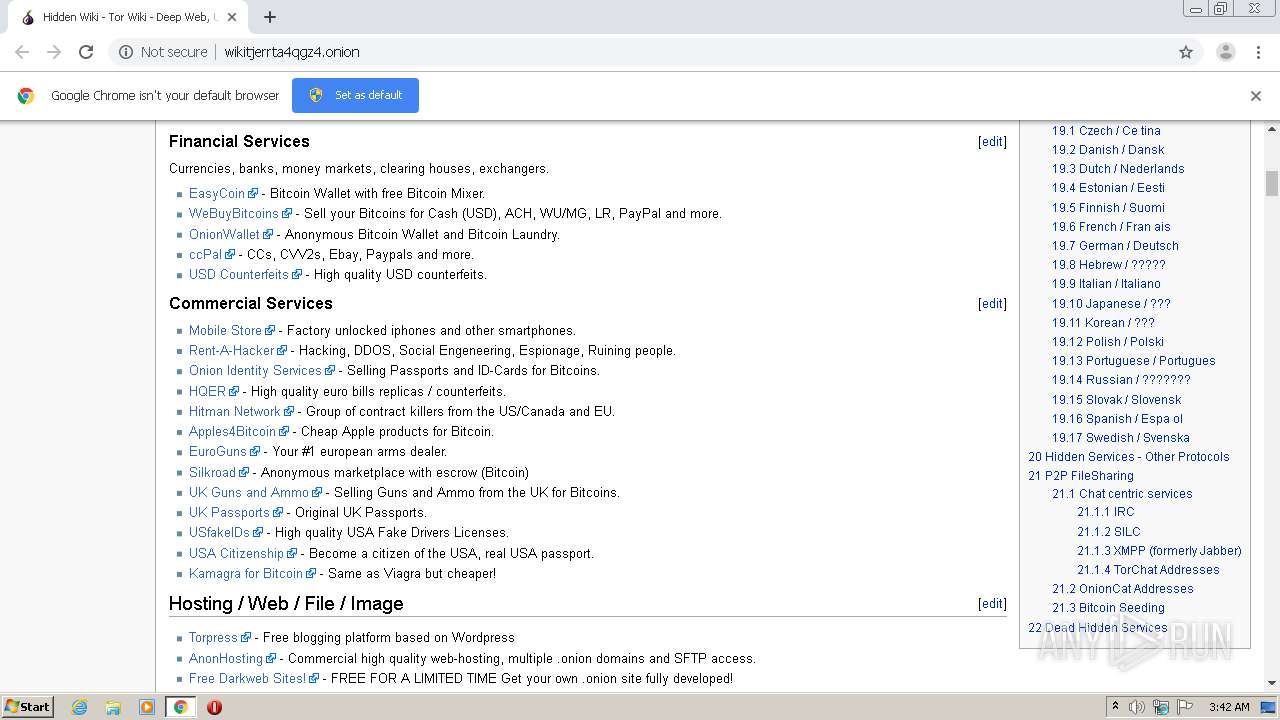
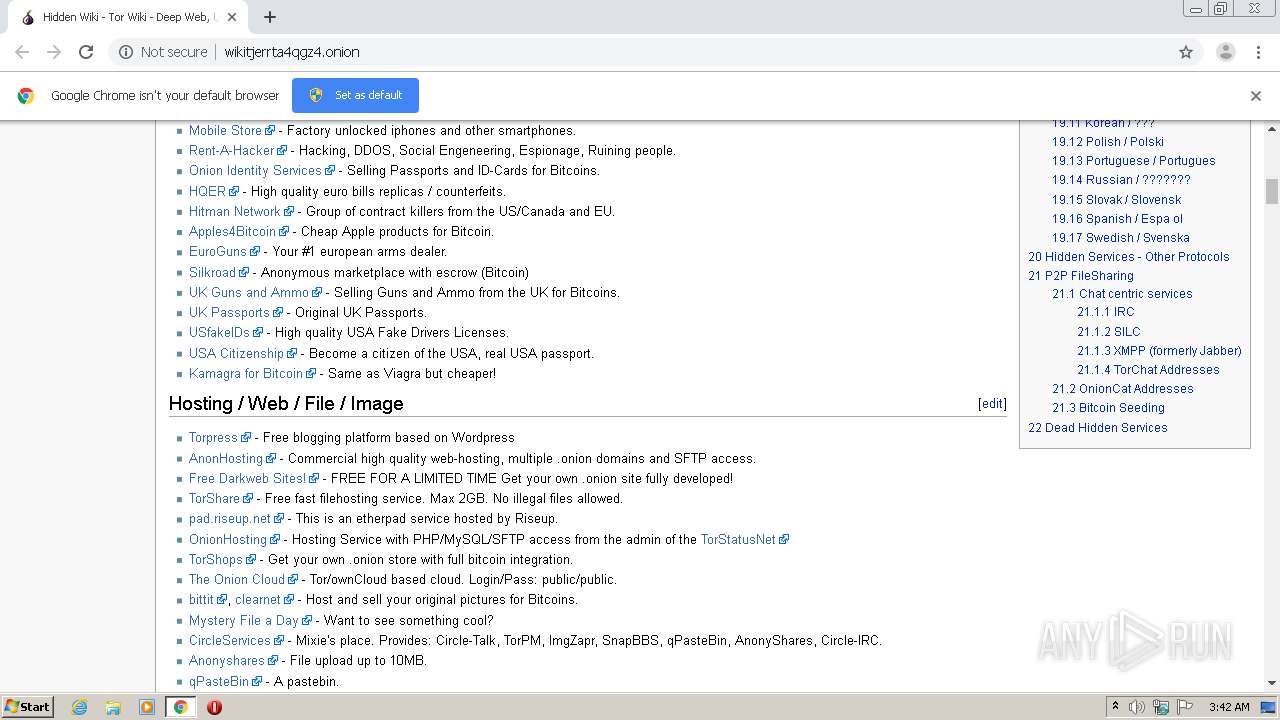
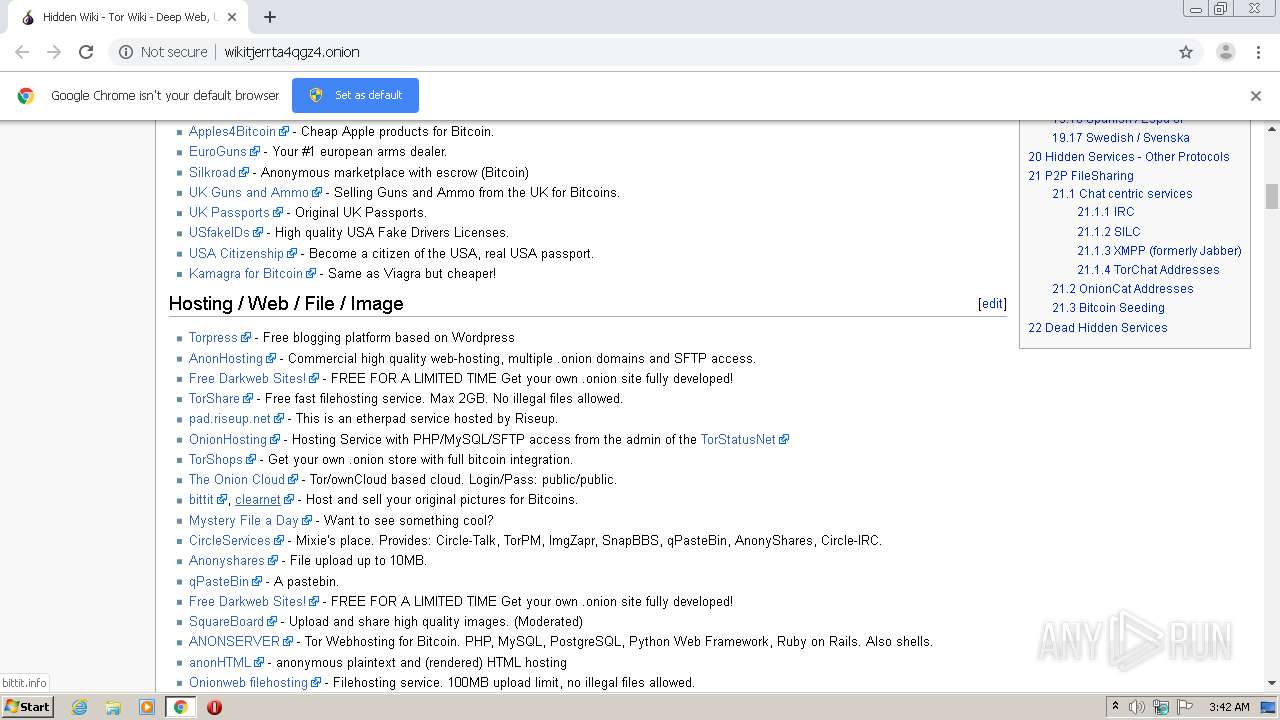
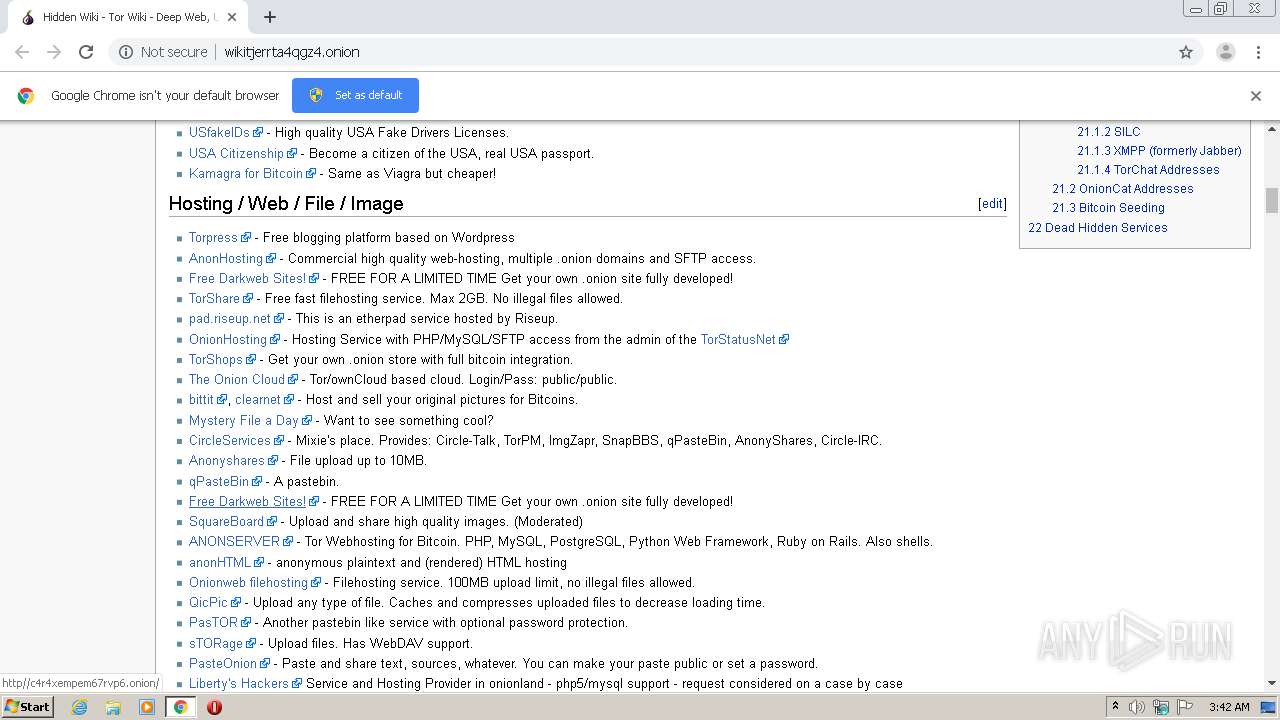
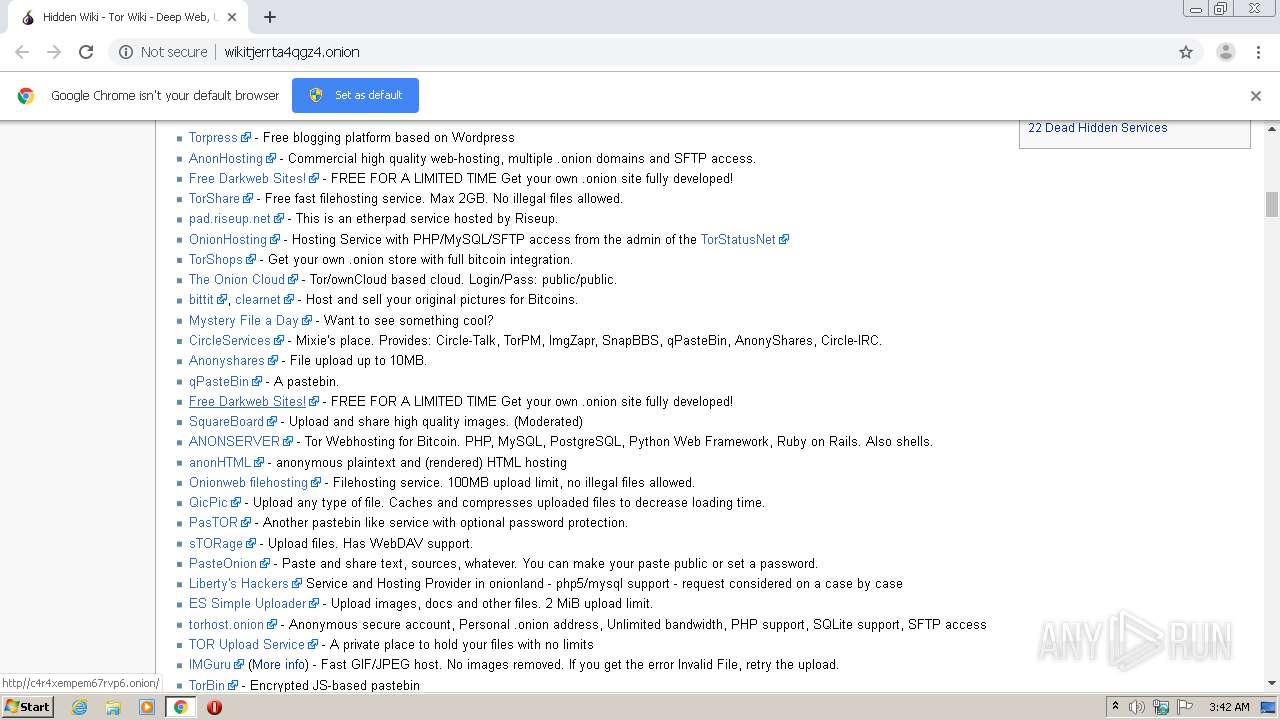
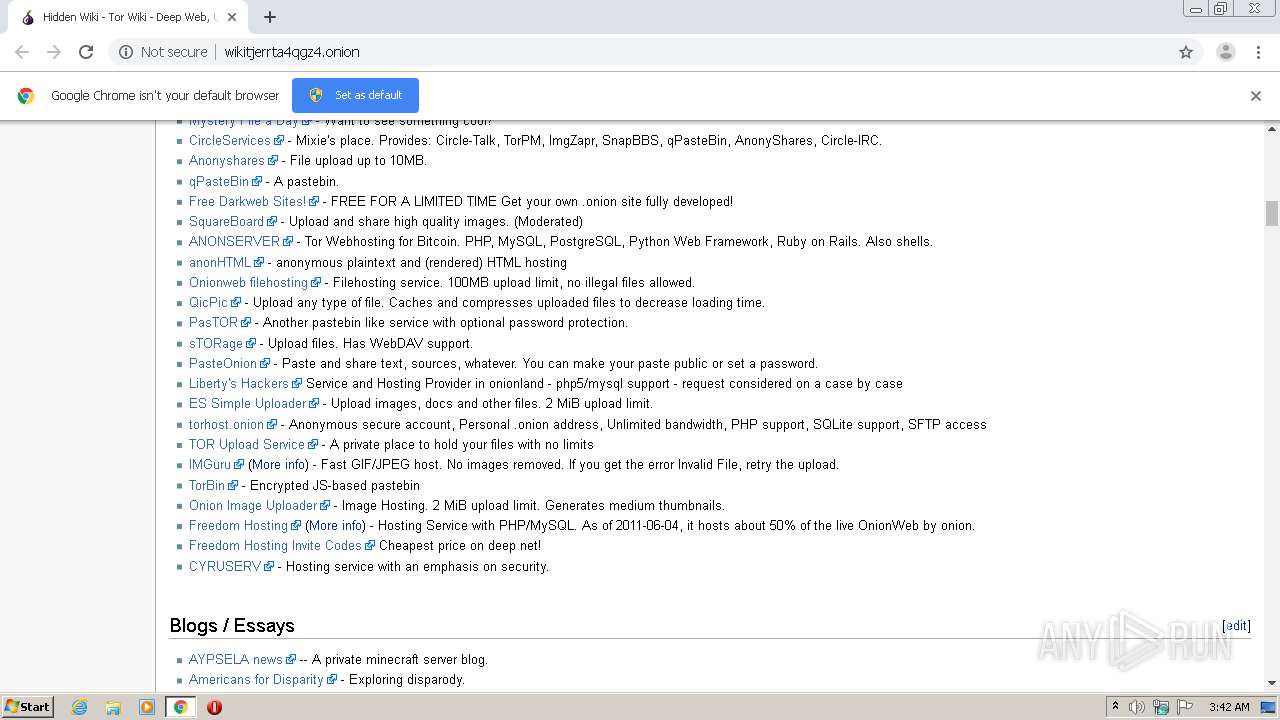
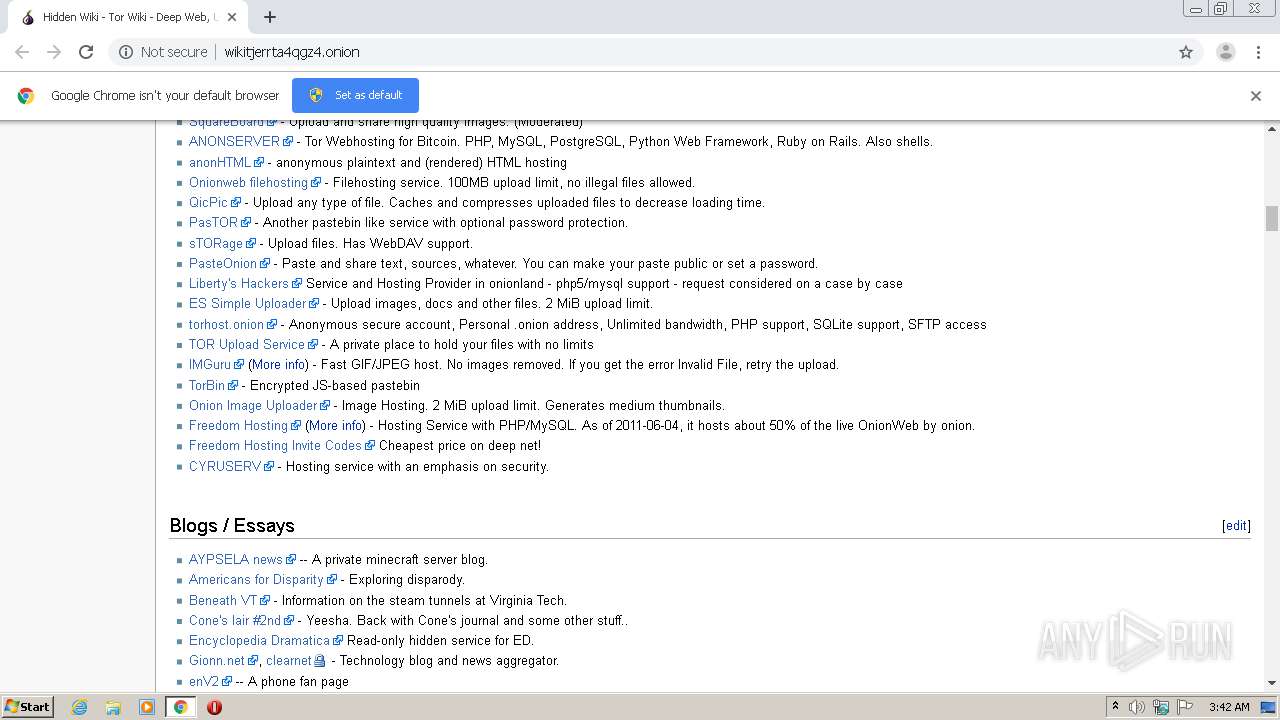
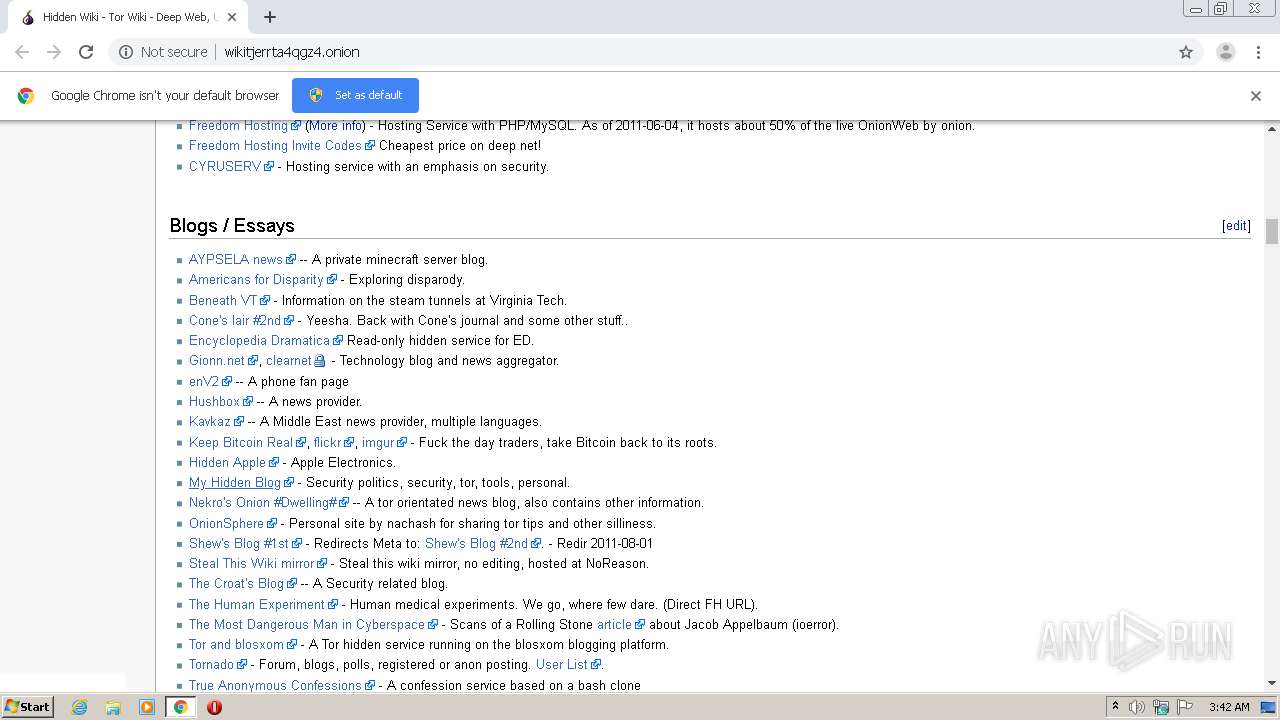
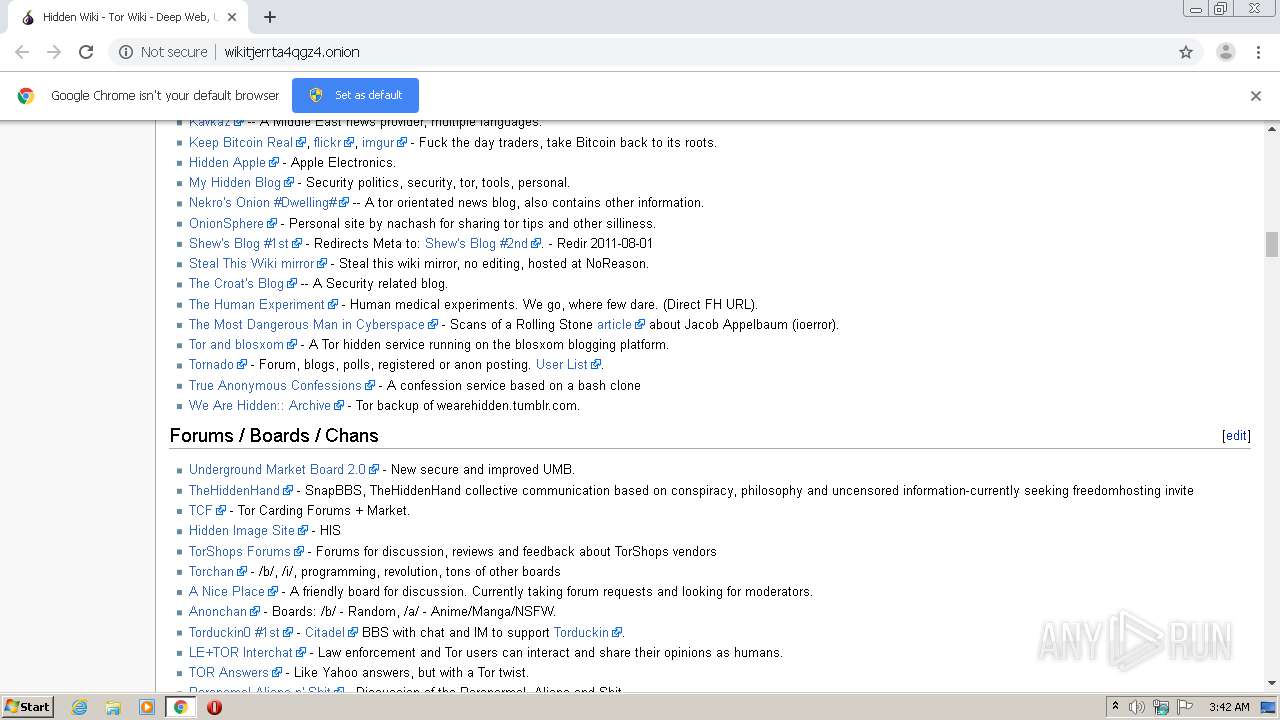
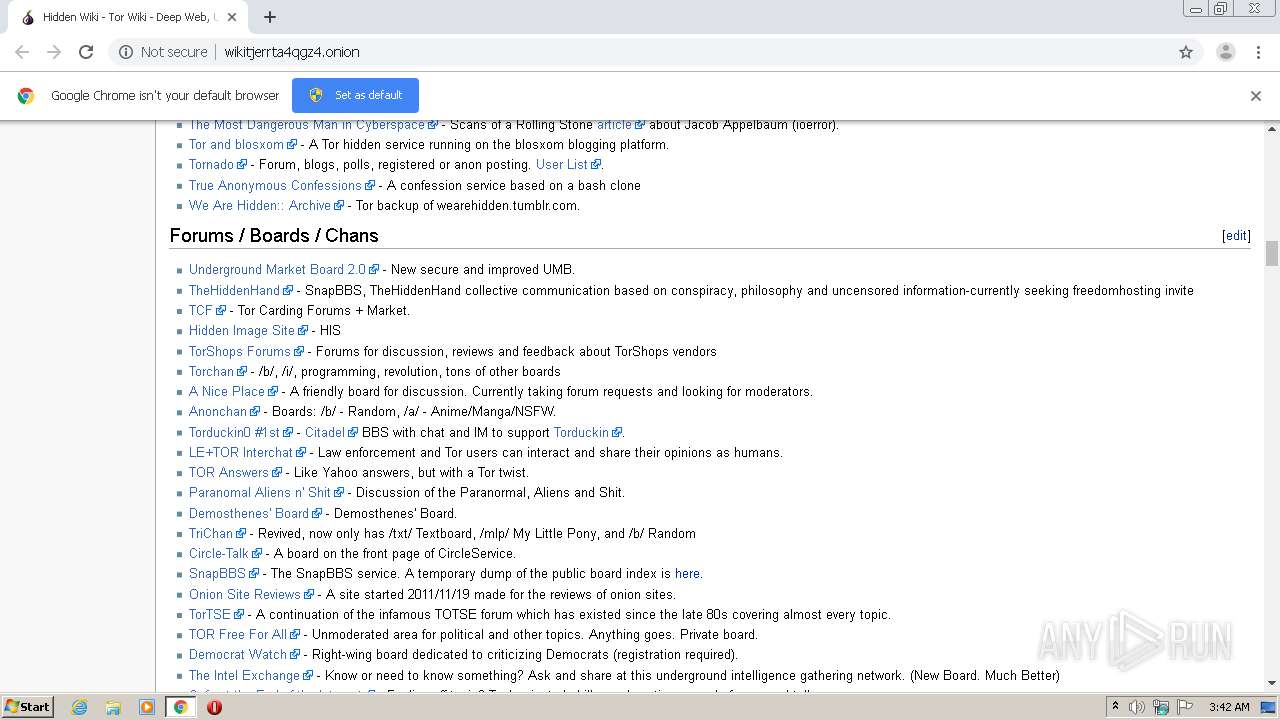
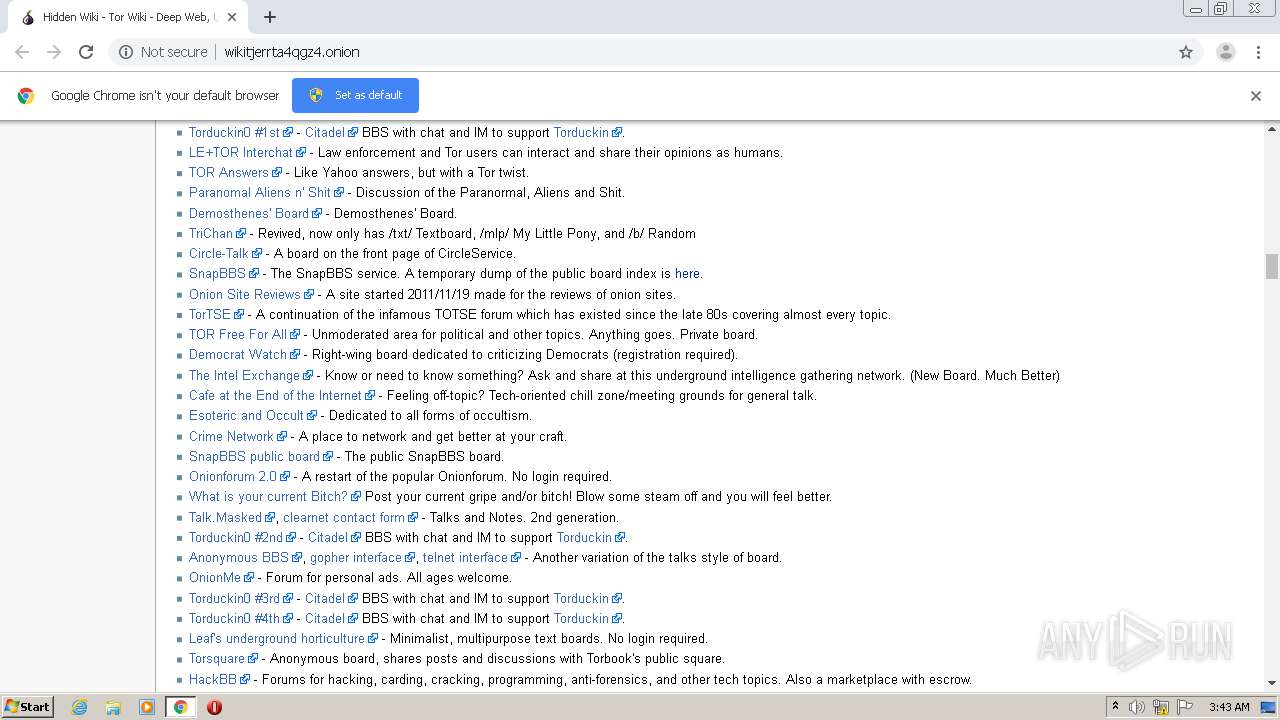
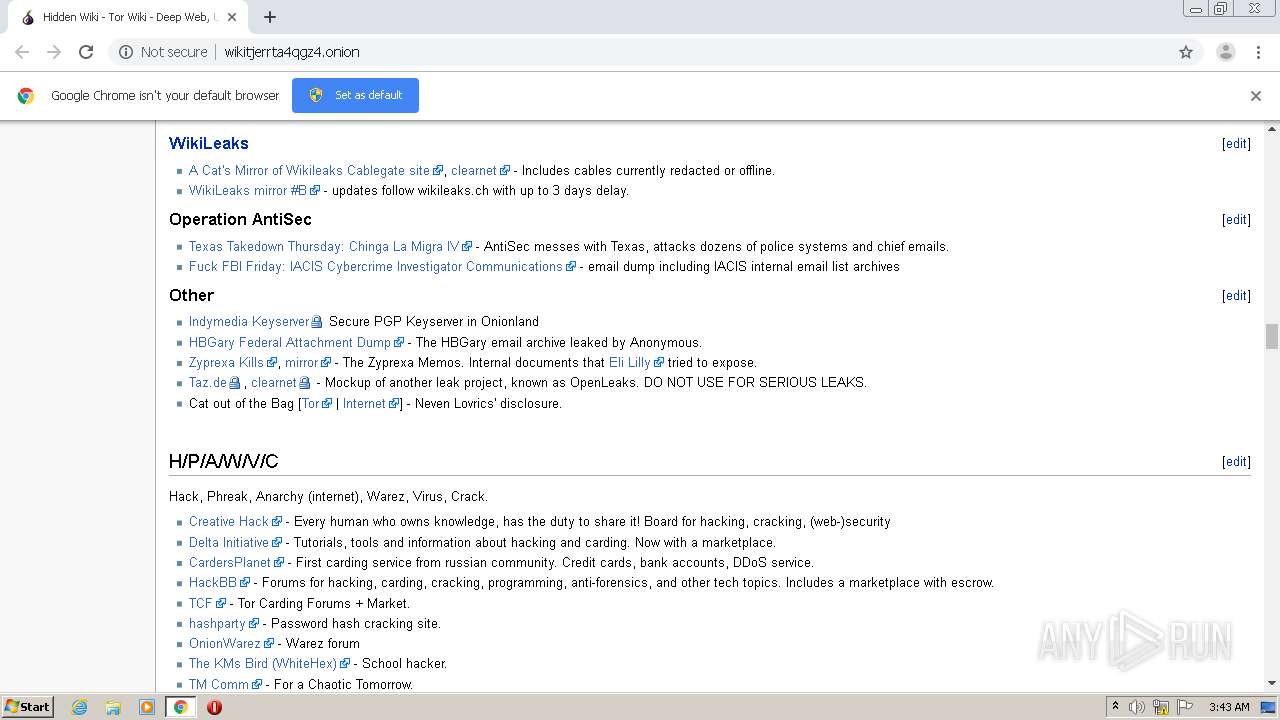
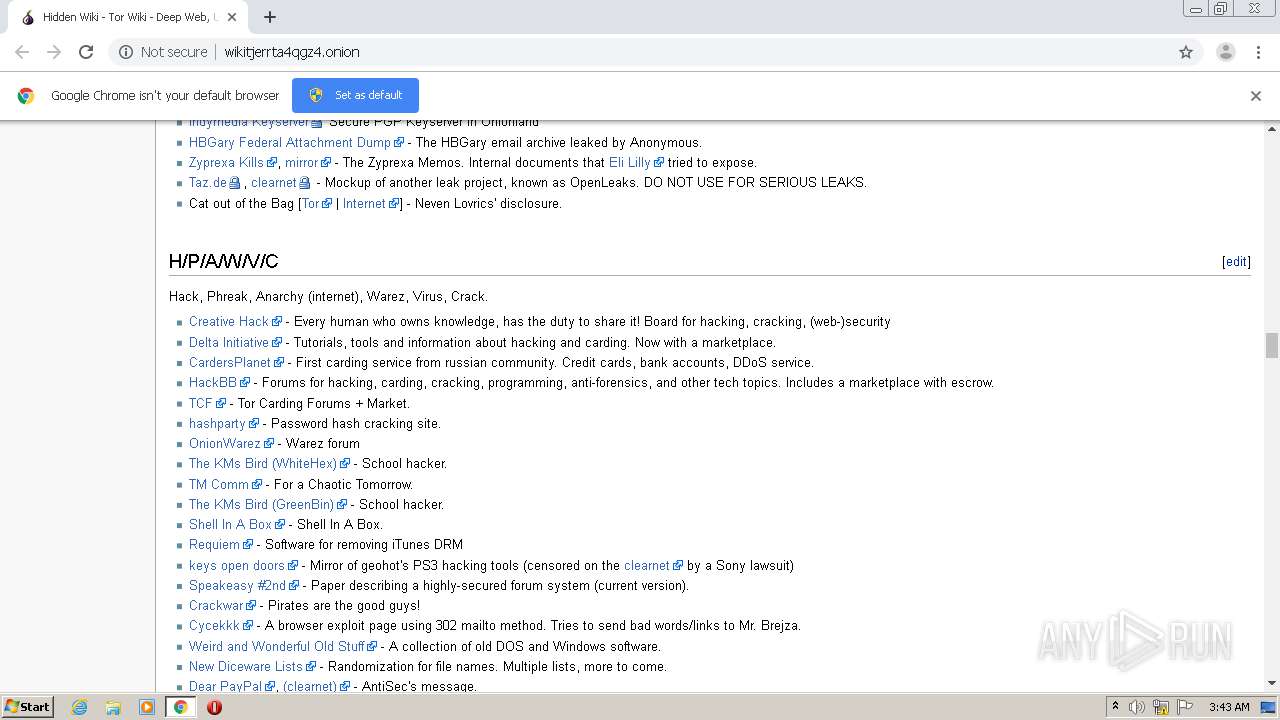
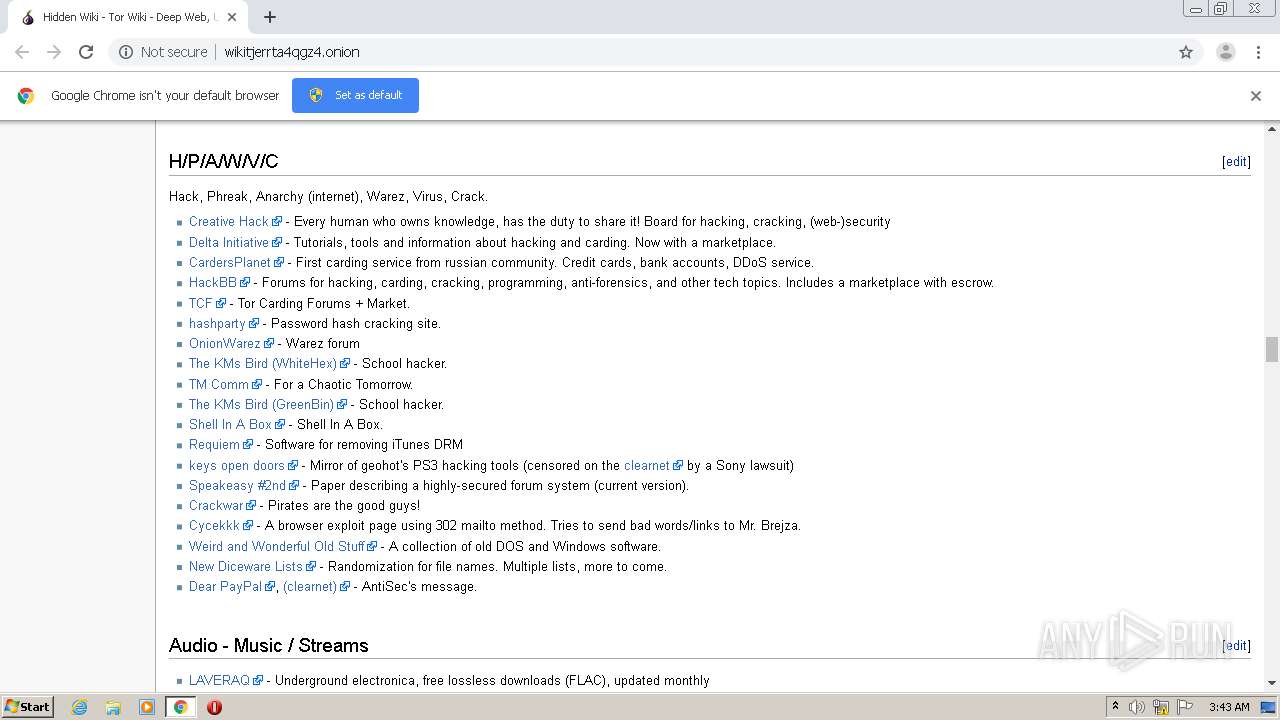
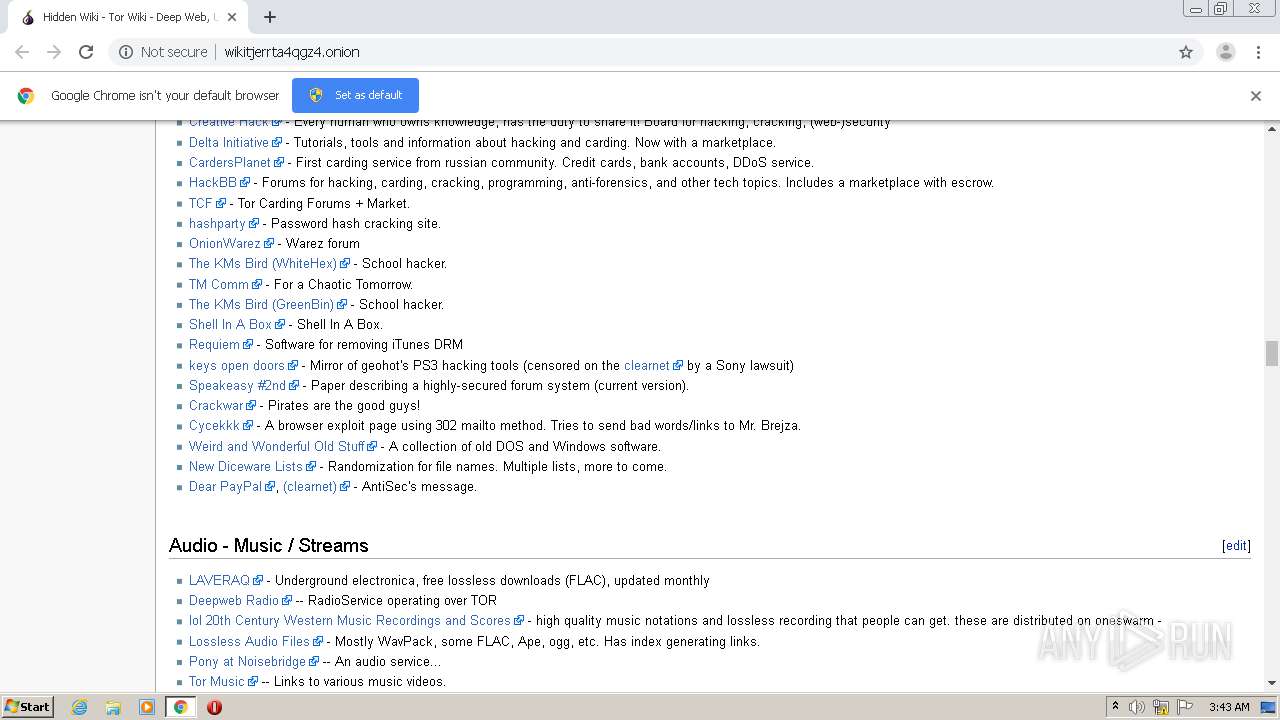
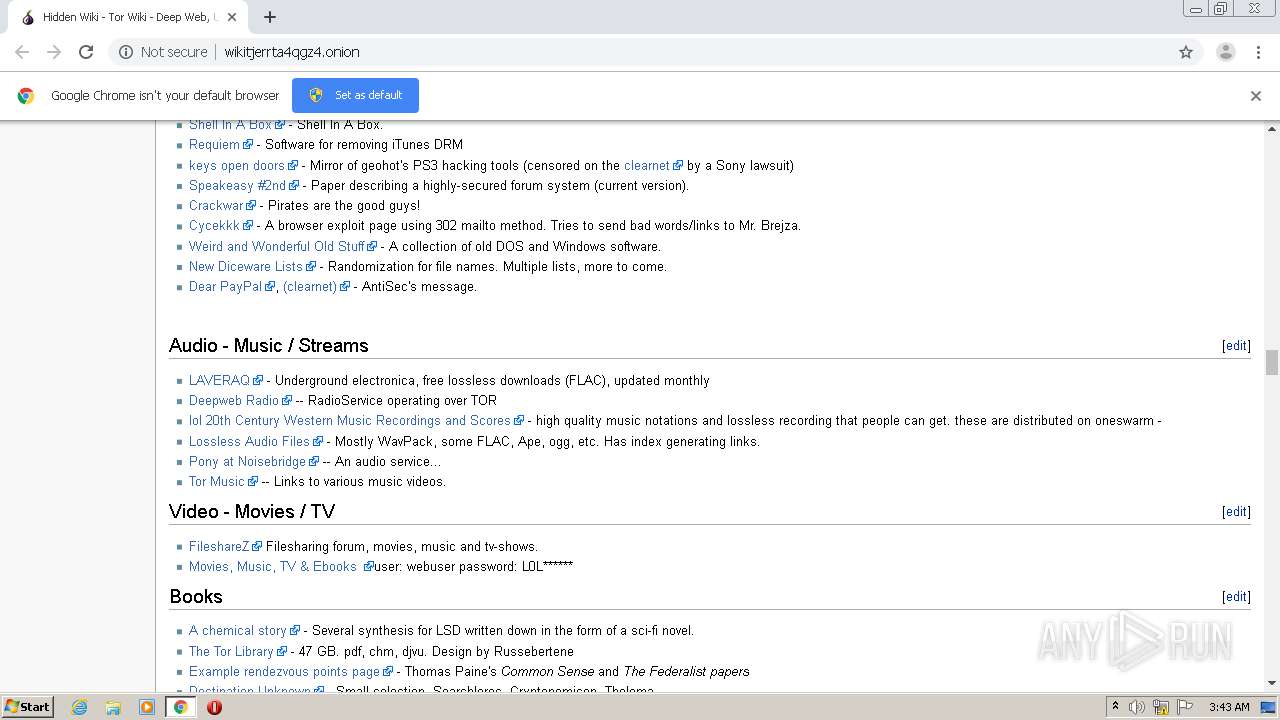
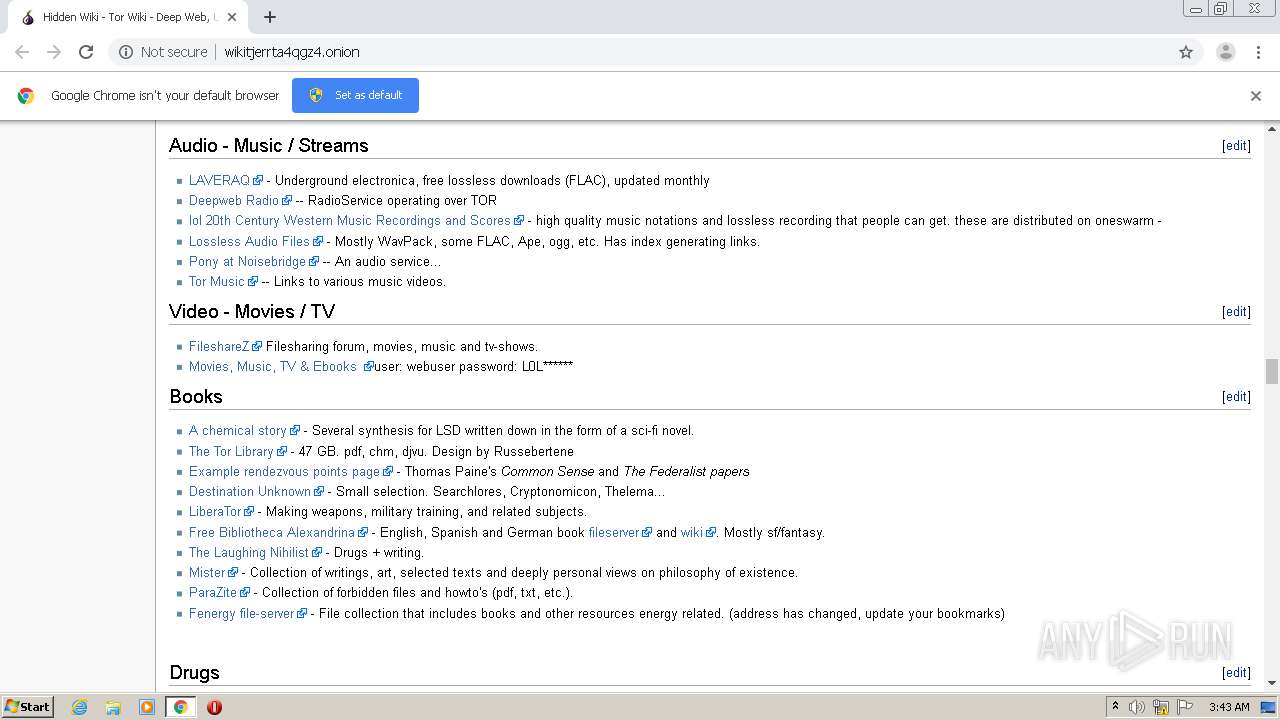
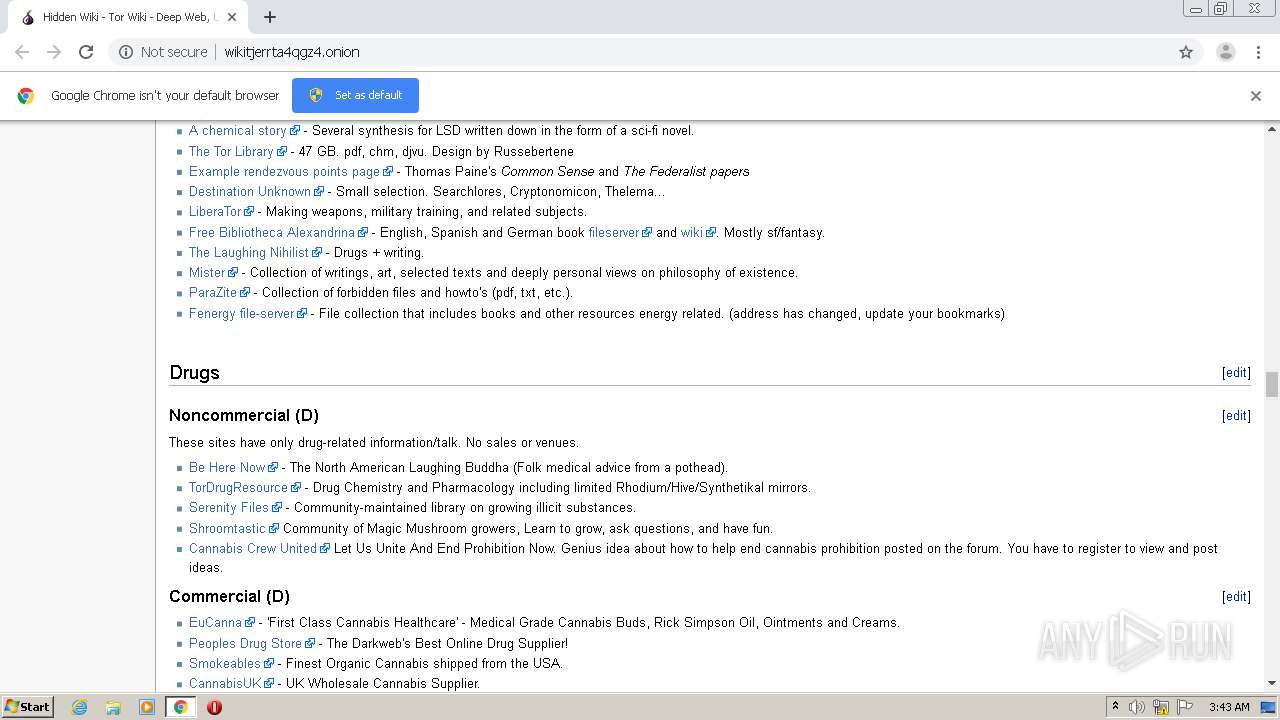
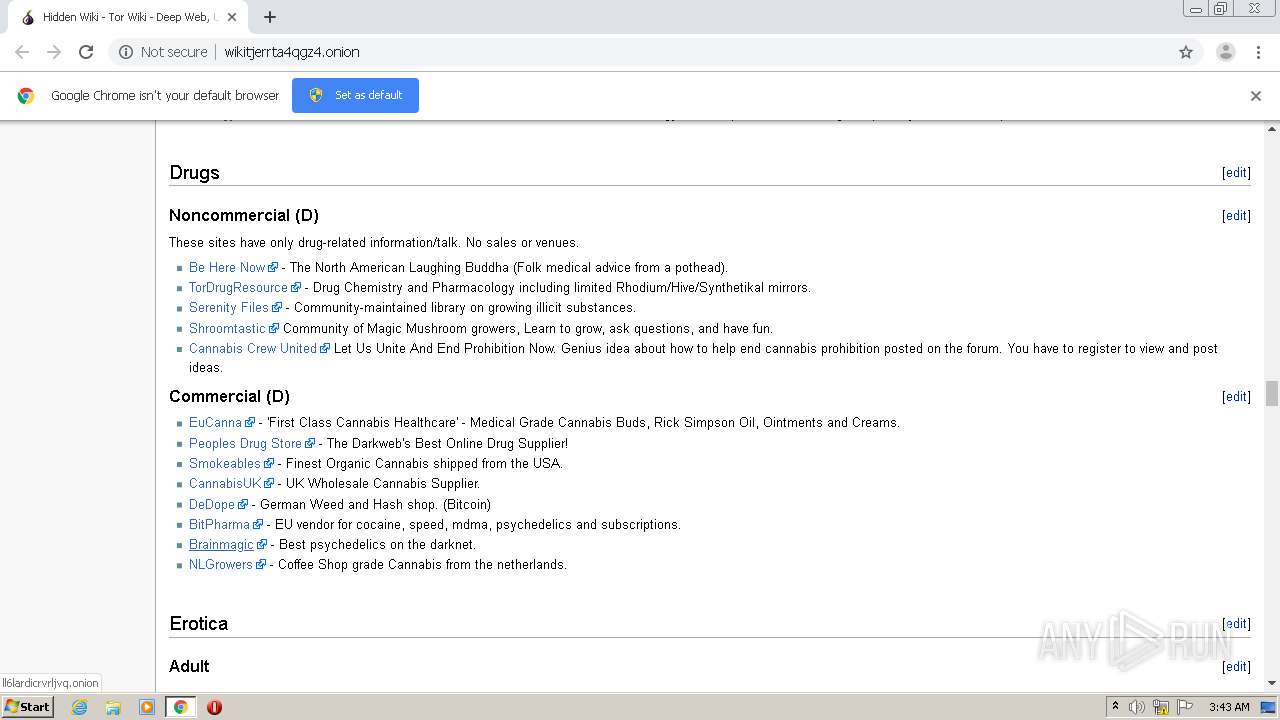
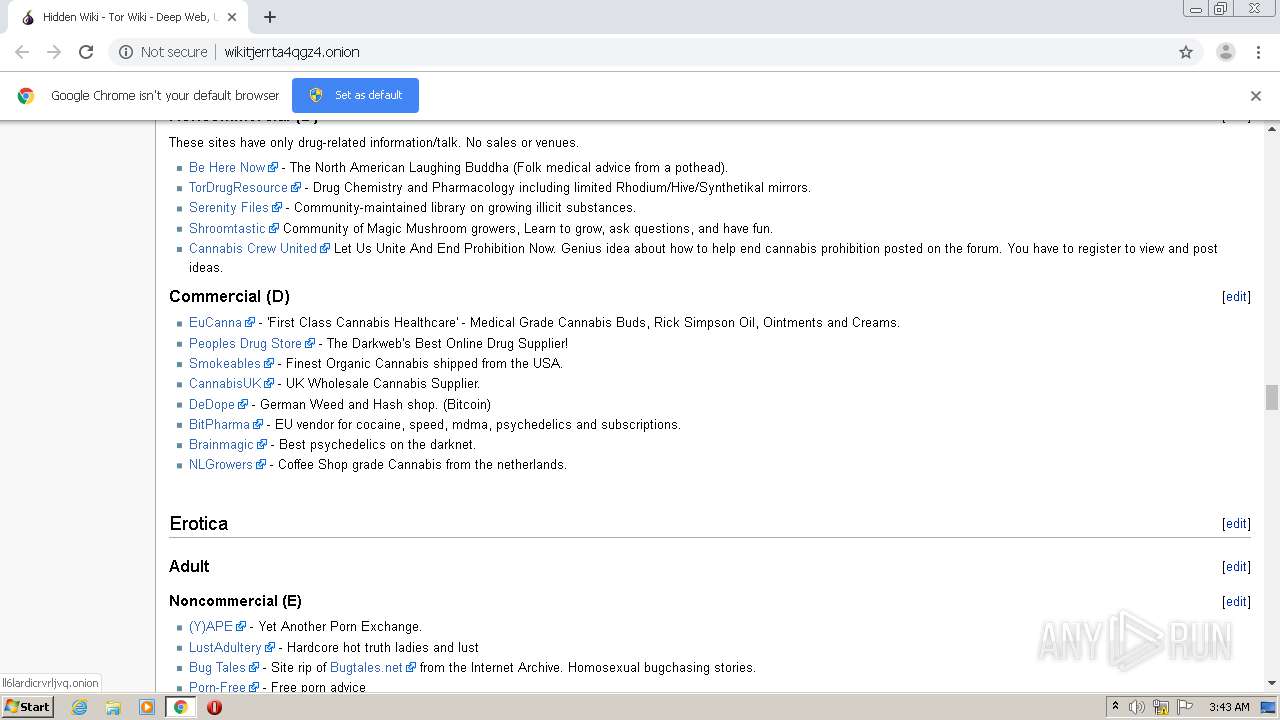
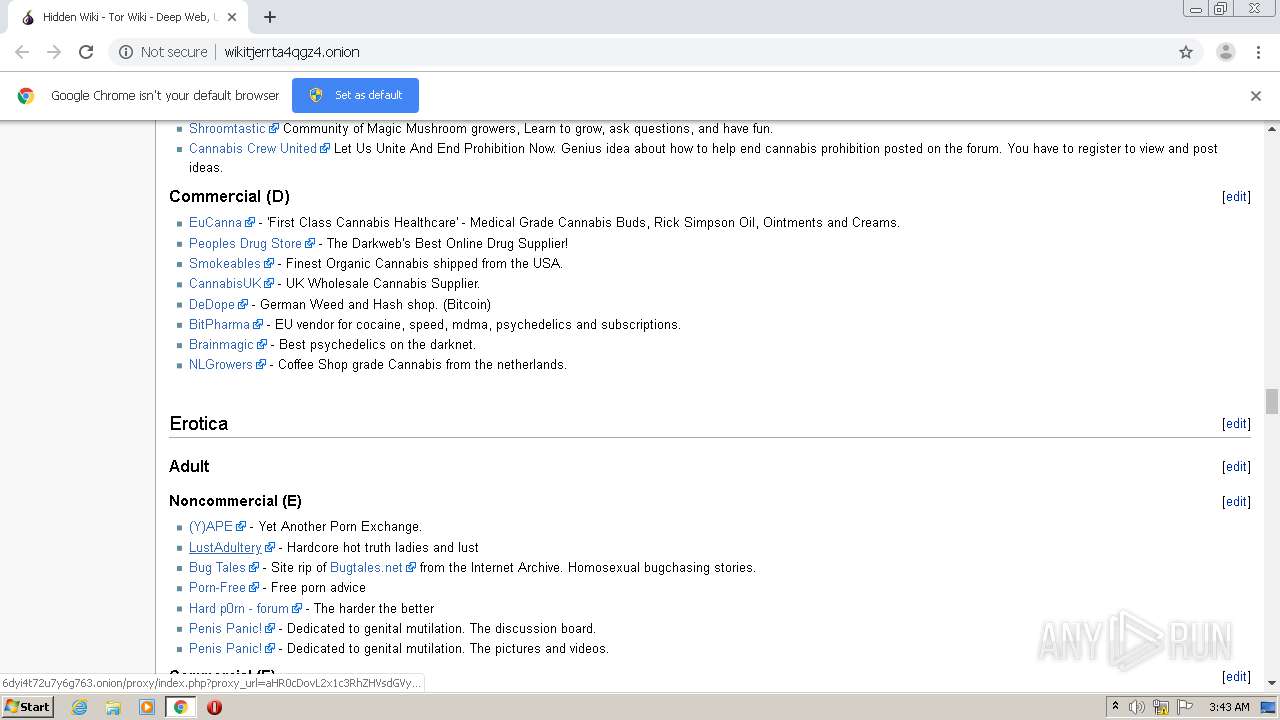
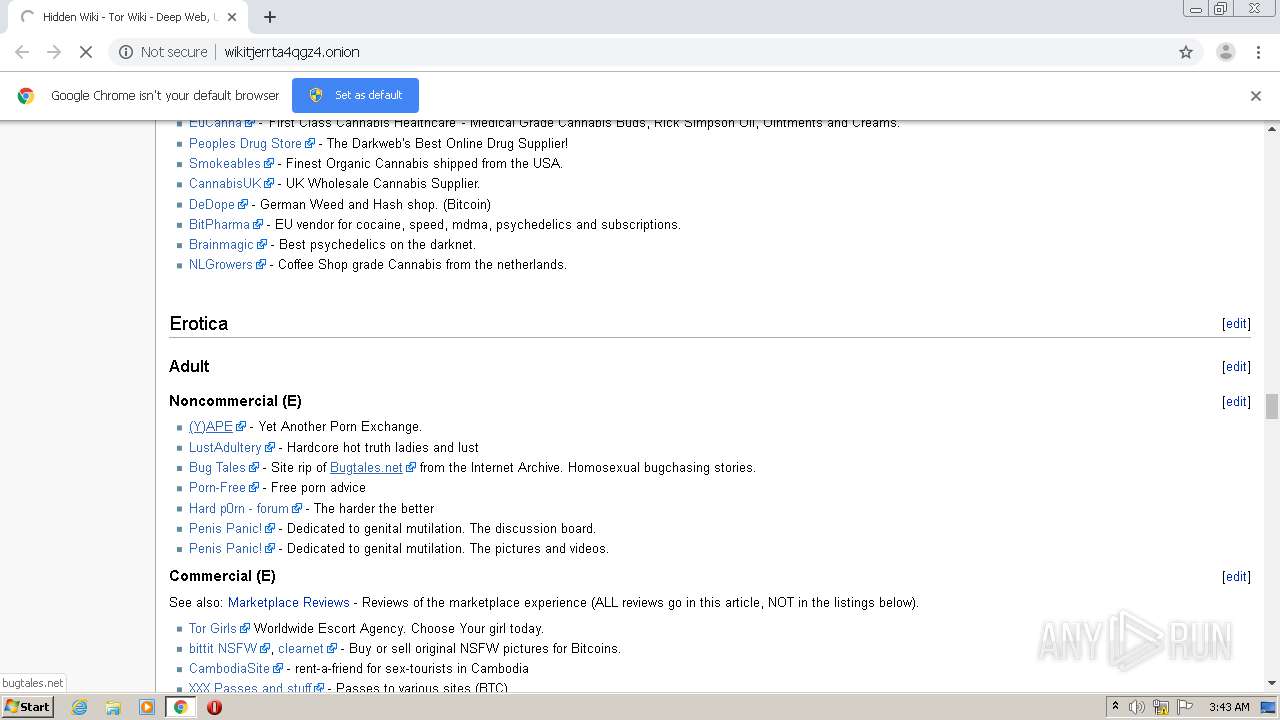
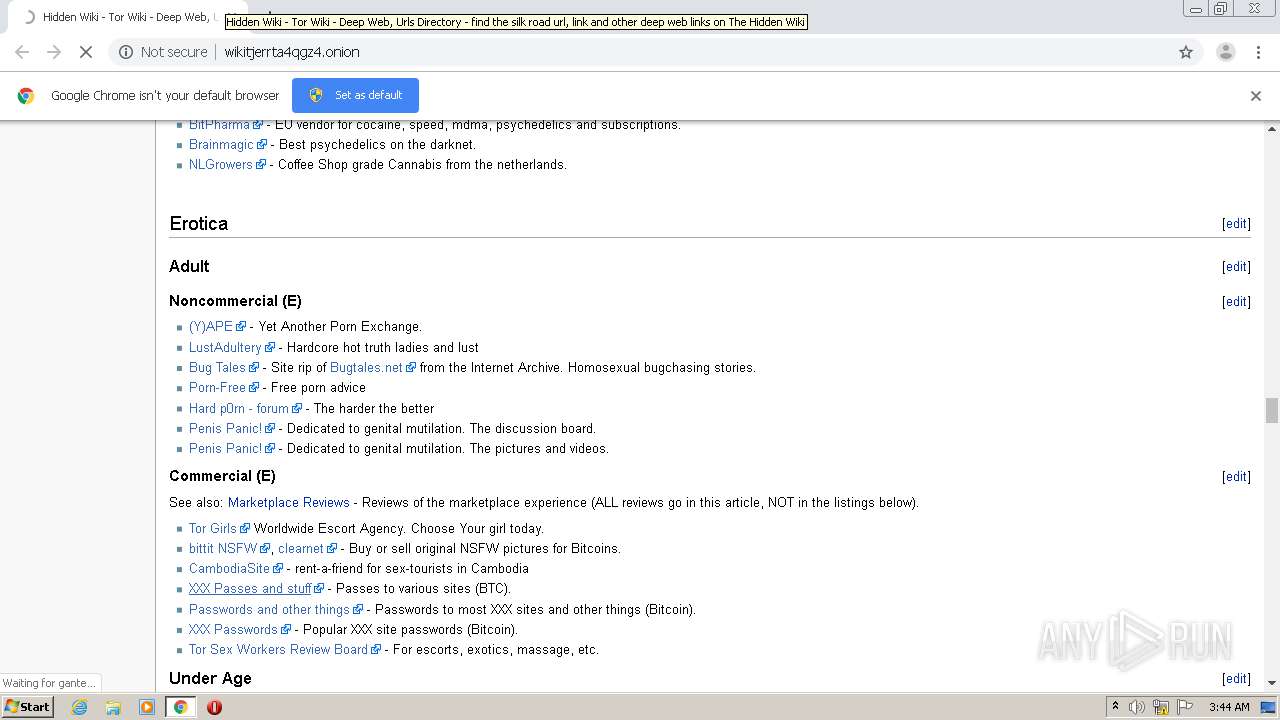
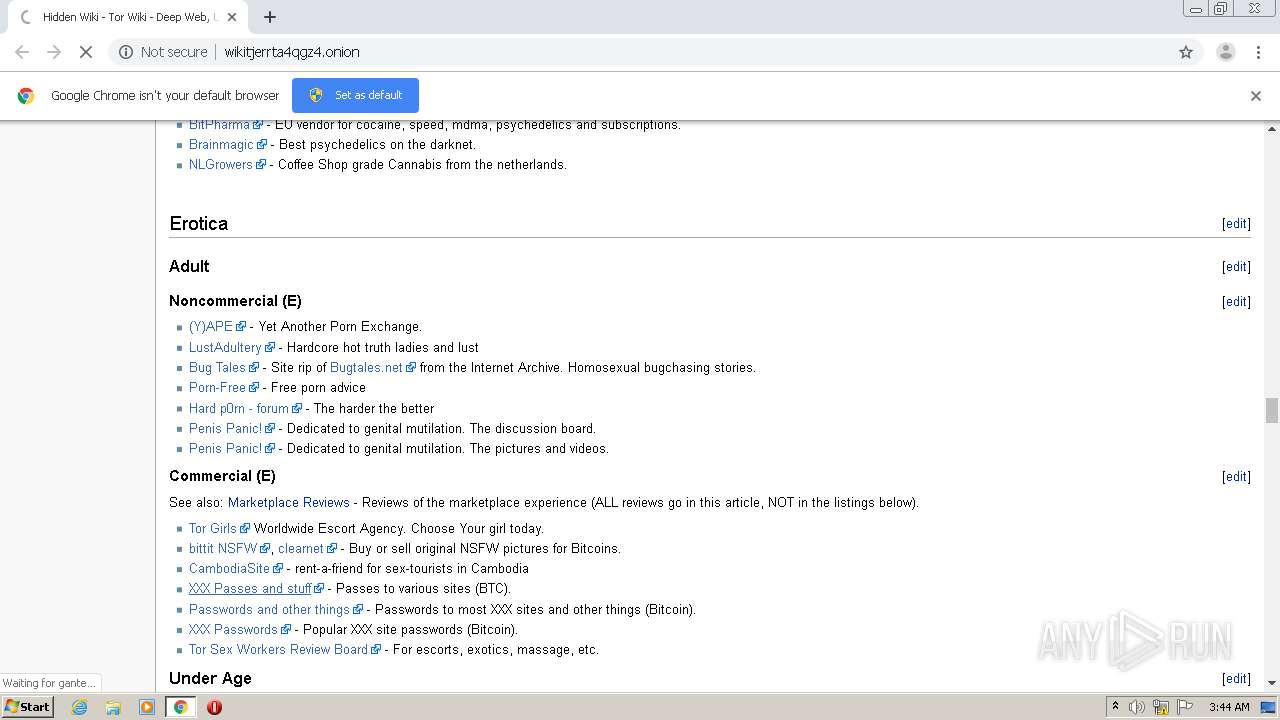
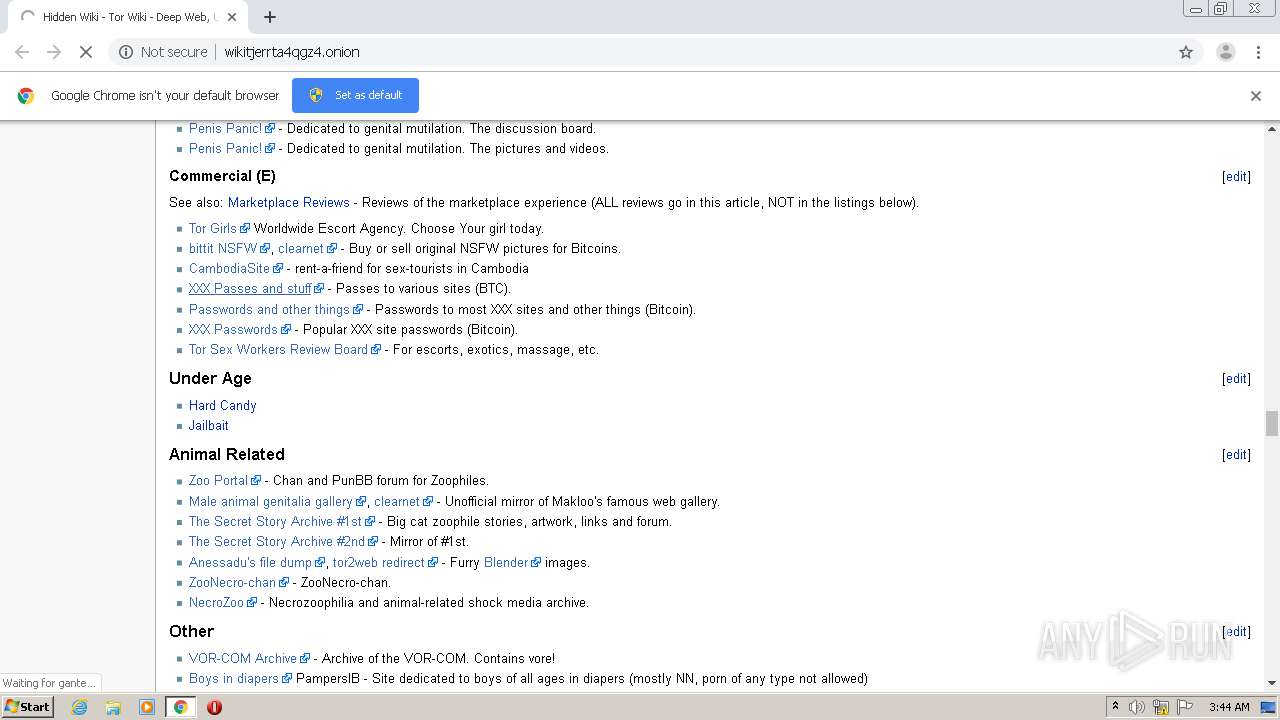
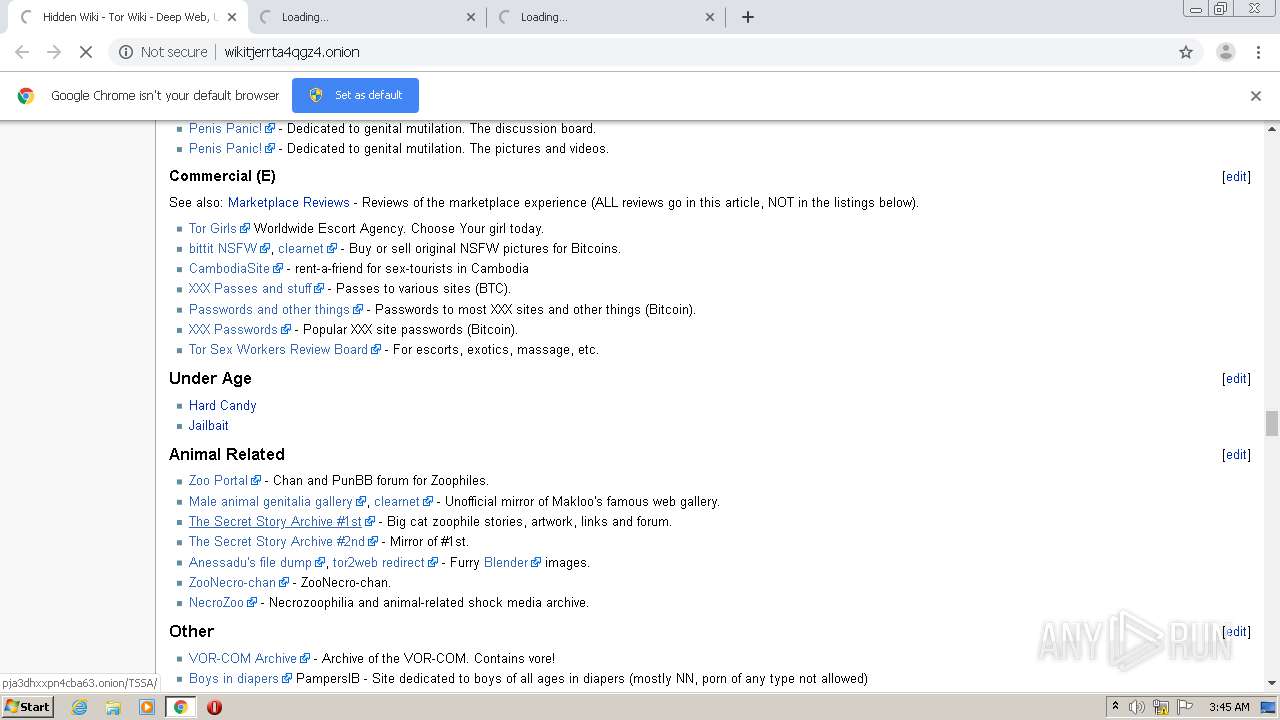
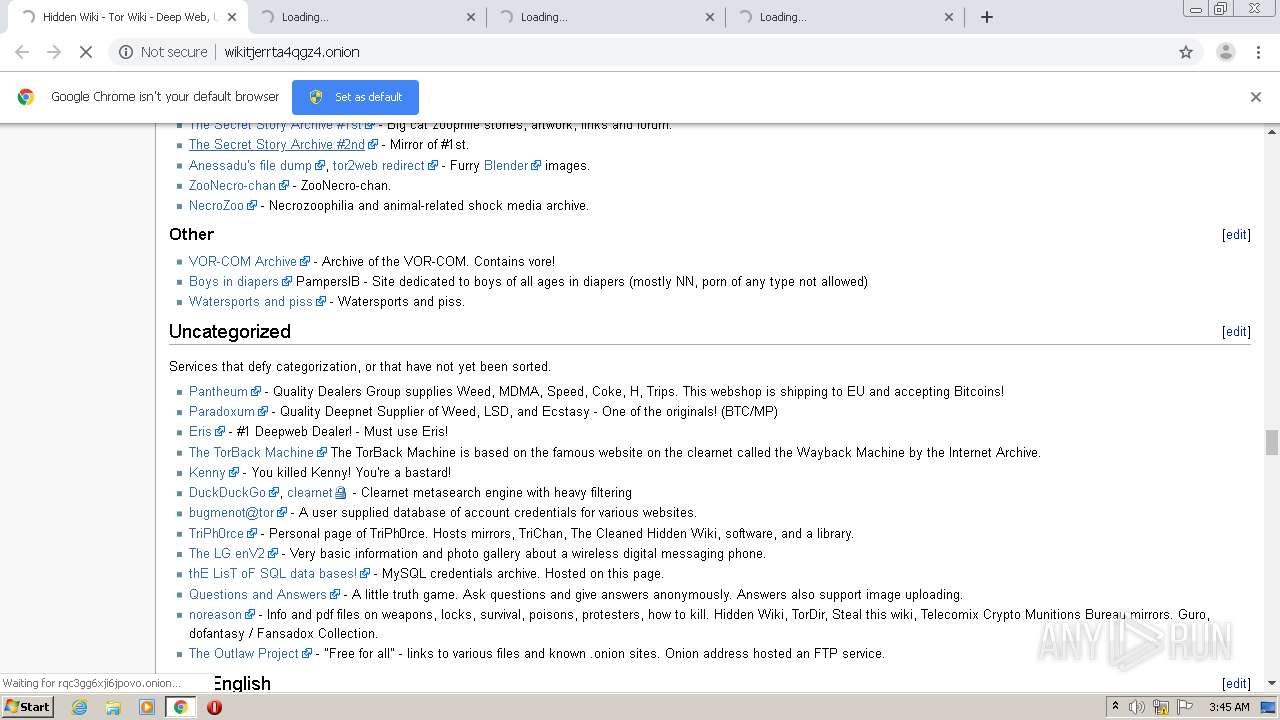
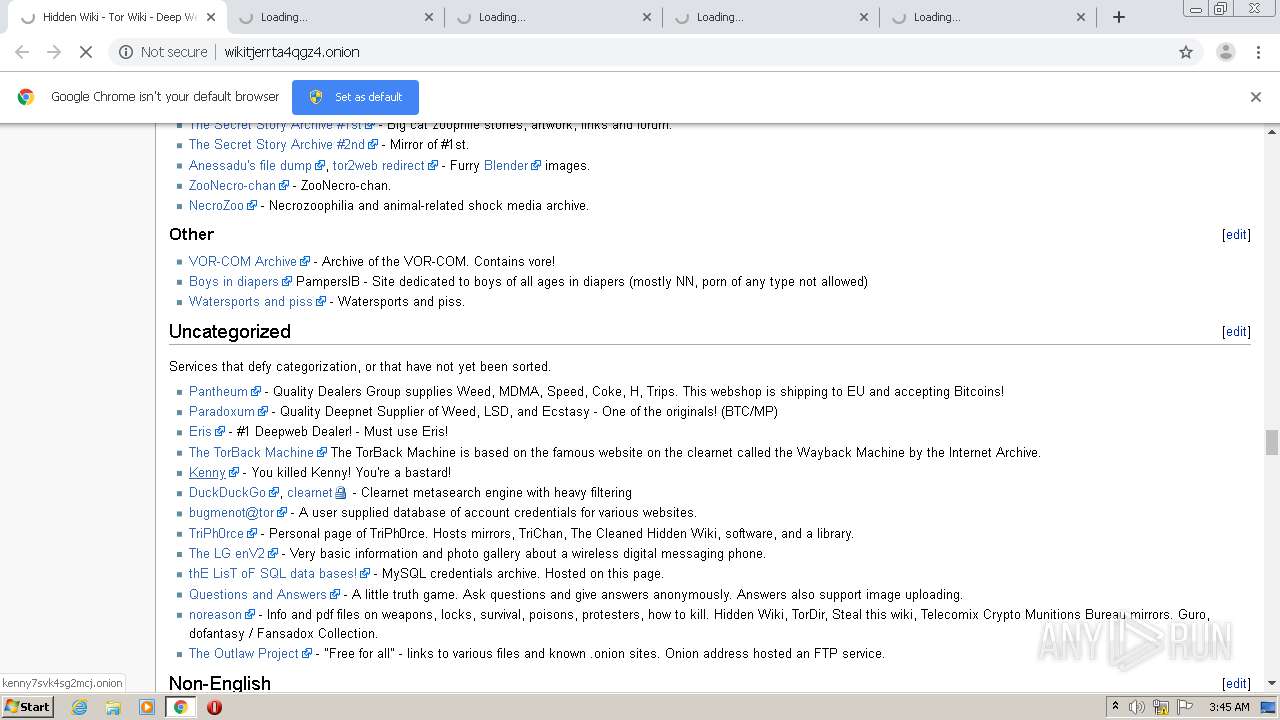
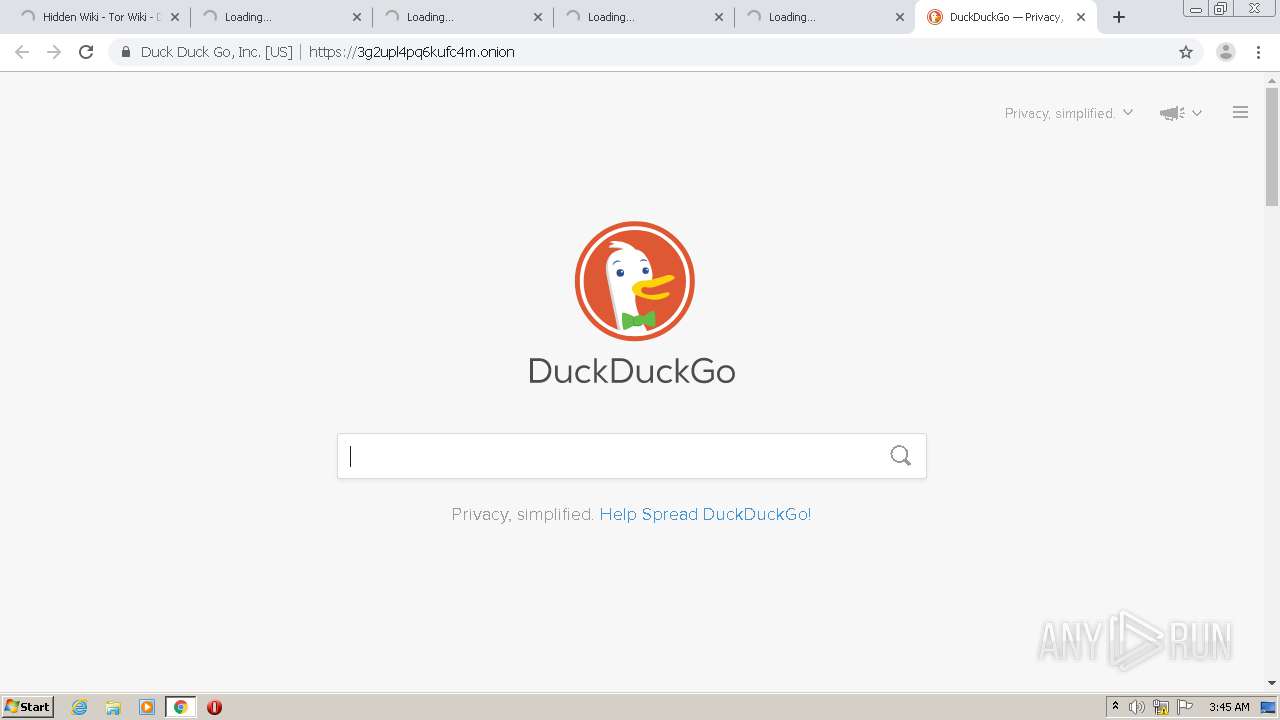
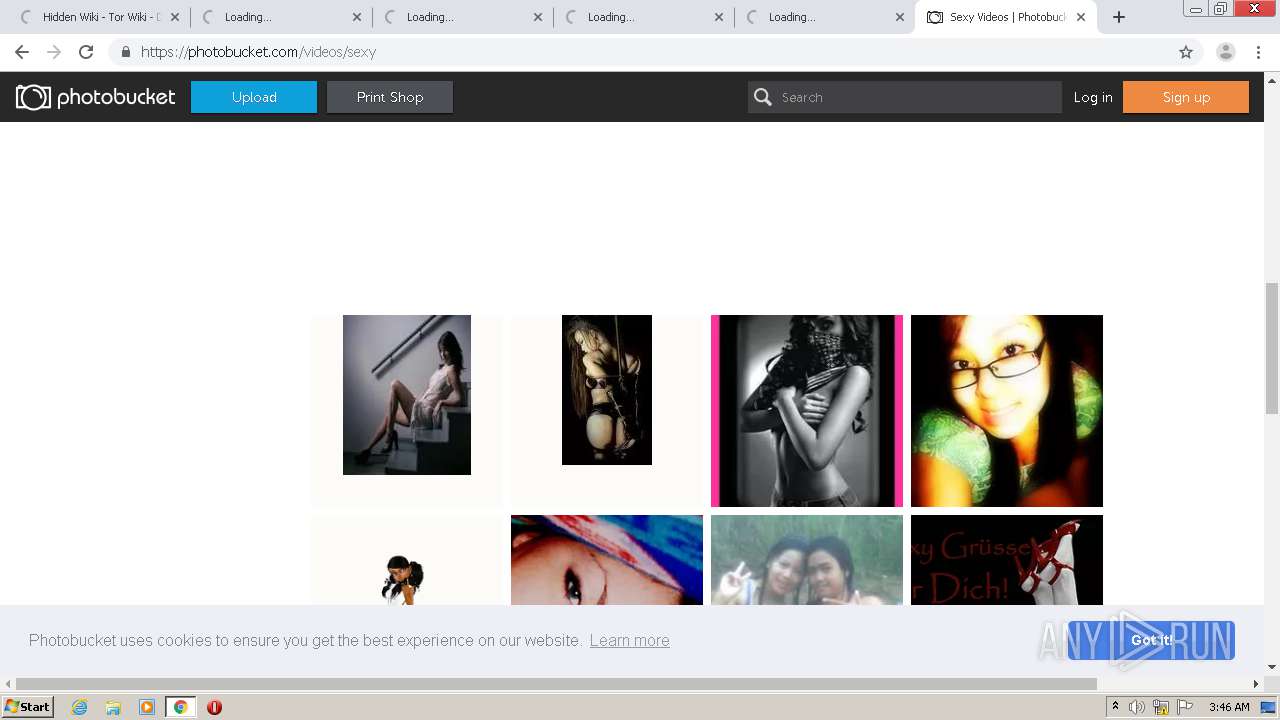
| URL: | HTTP://wikitjerrta4qgz4.onion |
| Full analysis: | https://app.any.run/tasks/787a3958-bb3b-42a3-be53-4af7e3aba761 |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2020, 02:41:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B55DEDEA2E1BCDD9975E51A16406006F |
| SHA1: | D7CFD3FC5A1EF642431EE01A8282BB9C2EF6BF5F |
| SHA256: | 0A1267189E6AD8AA25D159A6804D8F2A528E312E4CFC1A7DB397B21D05C89754 |
| SSDEEP: | 3:CKSPMYB0K4Q:CNF0ZQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 1848)
- chrome.exe (PID: 1720)
Reads settings of System Certificates
- chrome.exe (PID: 1720)
Application launched itself
- chrome.exe (PID: 1848)
Dropped object may contain TOR URL's
- chrome.exe (PID: 1848)
- chrome.exe (PID: 1720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
39
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16690224554134593169 --mojo-platform-channel-handle=5976 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16595170400093161126 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6939062257247013011 --mojo-platform-channel-handle=3552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13201030467236074506 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16316725739329035770 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8153456184372317077 --mojo-platform-channel-handle=3440 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1647381664211898364 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16638380982324119775 --mojo-platform-channel-handle=1676 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "HTTP://wikitjerrta4qgz4.onion" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,7741163118111032285,11748005827704600718,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11006262053576493 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
856
Read events
720
Write events
131
Delete events
5
Modification events
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1848-13241155325580750 |
Value: 259 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
160
Text files
154
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f37cbdbe-27c8-49d8-b872-a894220aeb04.tmp | — | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFde3f8.TMP | text | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFde3e8.TMP | text | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFde427.TMP | text | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFde475.TMP | text | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
149
DNS requests
427
Threats
563
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1720 | chrome.exe | GET | — | 10.217.47.118:80 | http://hb4pm4eznzhd6mts.onion/pe/train.php | unknown | — | — | unknown |
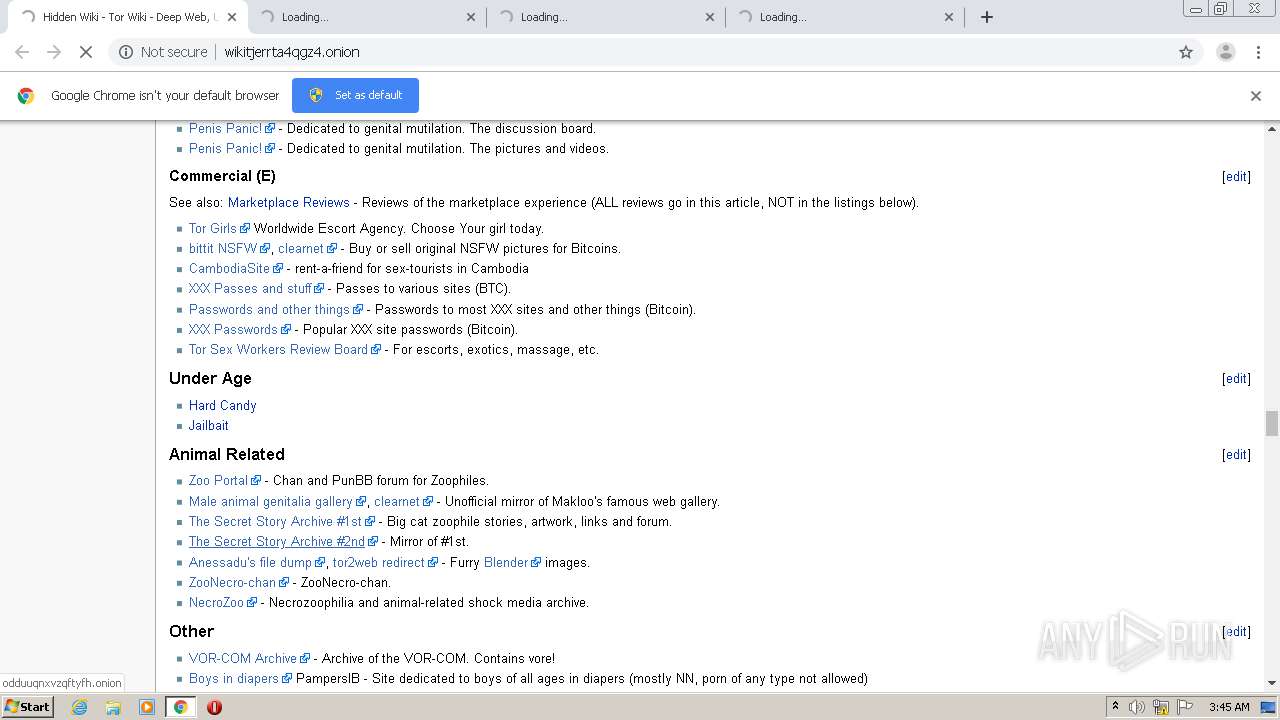
1720 | chrome.exe | GET | — | 10.233.192.195:80 | http://rqc3gg6xji6jpovo.onion/ | unknown | — | — | unknown |
1720 | chrome.exe | GET | — | 10.193.94.171:80 | http://odduuqnxvzqftyfh.onion/ | unknown | — | — | unknown |
1720 | chrome.exe | GET | — | 10.198.222.222:80 | http://kenny7svk4sg2mcj.onion/ | unknown | — | — | unknown |
1720 | chrome.exe | GET | — | 10.229.12.88:80 | http://s7nbvdbky4xqim7h.onion/ | unknown | — | — | unknown |
1720 | chrome.exe | GET | — | 10.240.82.79:80 | http://pja3dhxxpn4cba63.onion/TSSA/ | unknown | — | — | unknown |
1720 | chrome.exe | GET | — | 10.233.192.195:80 | http://rqc3gg6xji6jpovo.onion/ | unknown | — | — | unknown |
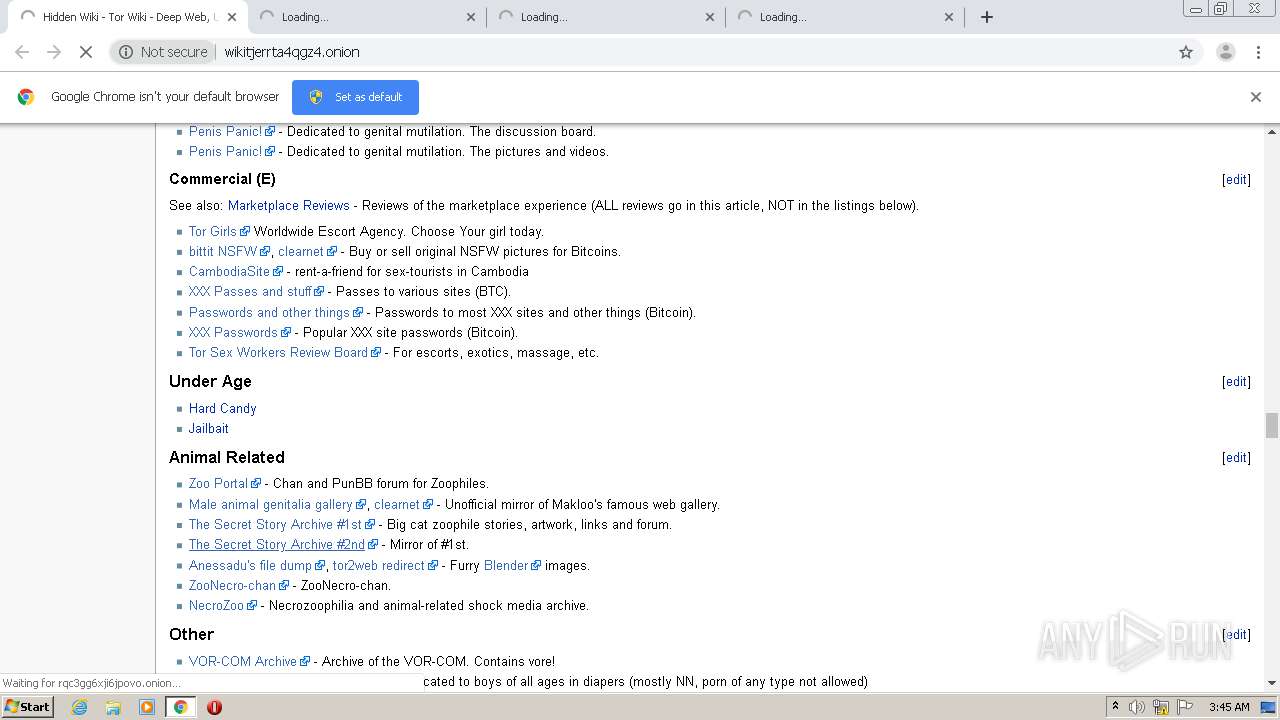
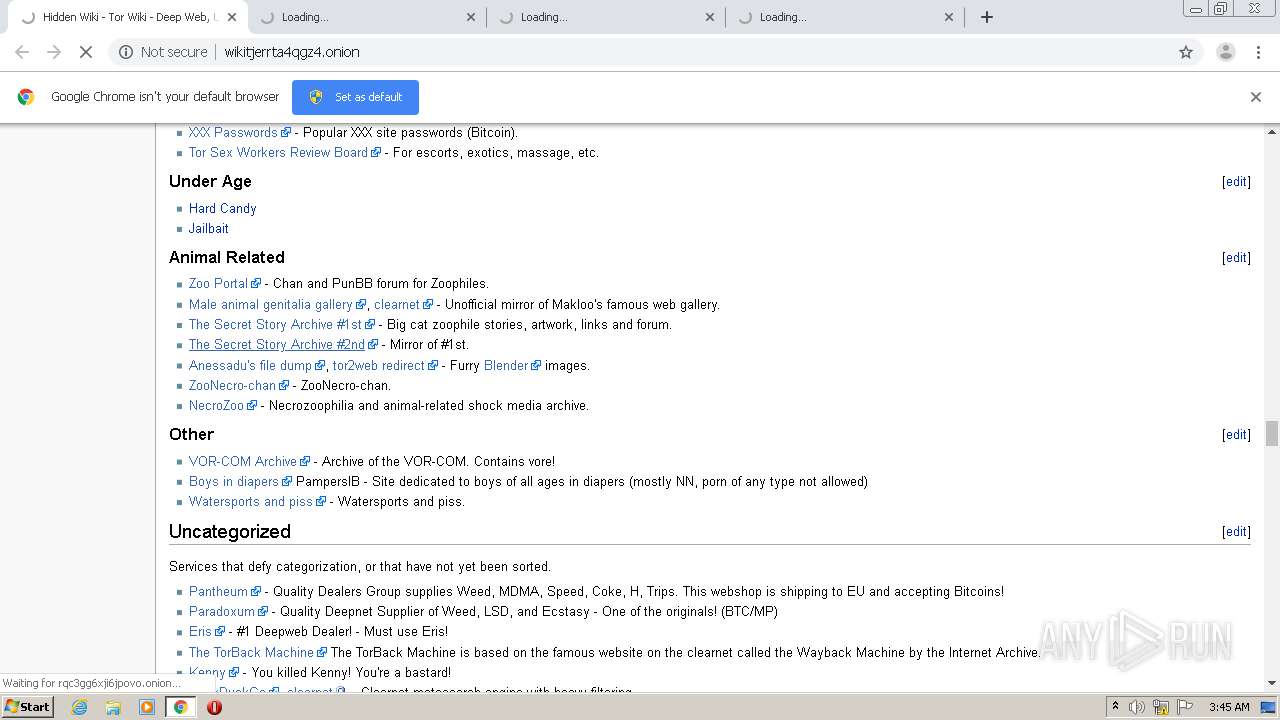
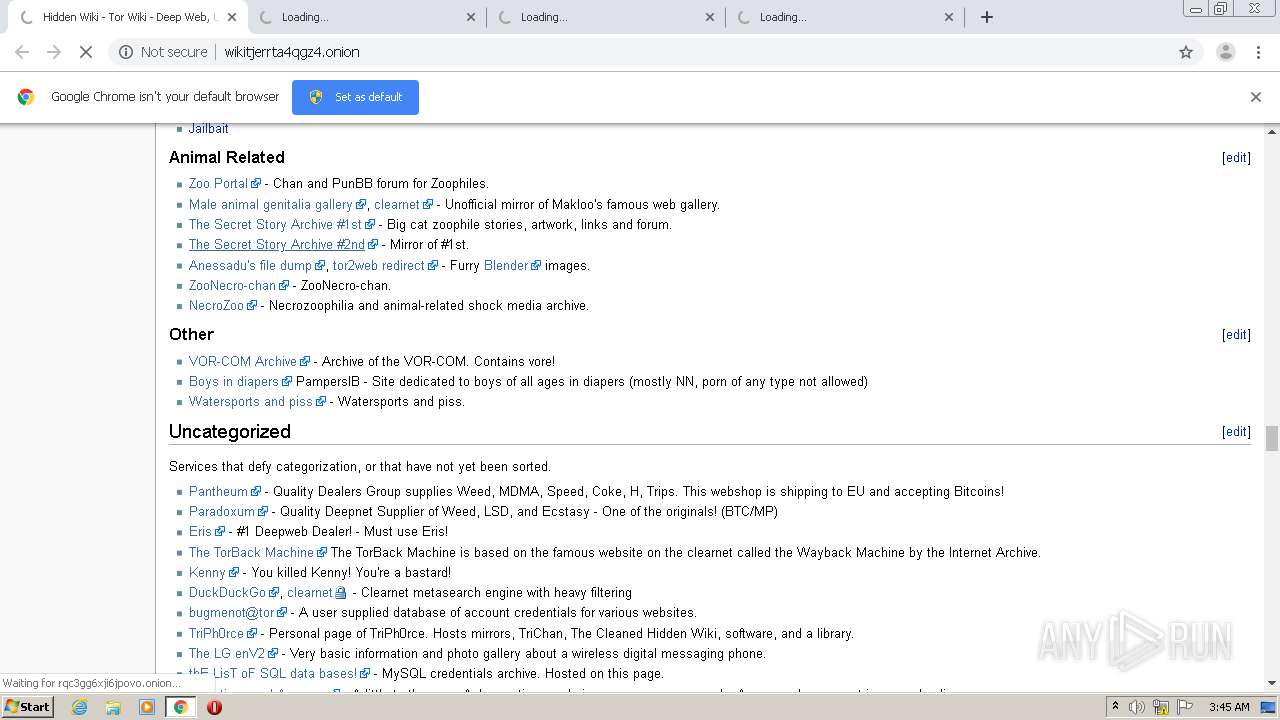
1720 | chrome.exe | GET | 200 | 10.209.254.99:80 | http://wikitjerrta4qgz4.onion/ | unknown | html | 107 Kb | unknown |
1720 | chrome.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.7 Kb | whitelisted |
1720 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1720 | chrome.exe | 10.209.254.99:80 | wikitjerrta4qgz4.onion | — | — | unknown |
1720 | chrome.exe | 216.58.211.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.17.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 172.217.20.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 216.58.214.13:443 | accounts.google.com | Google Inc. | US | suspicious |
1720 | chrome.exe | 10.229.12.88:80 | s7nbvdbky4xqim7h.onion | — | — | unknown |
1720 | chrome.exe | 64.233.185.113:443 | clients1.google.com | Google Inc. | US | whitelisted |
1720 | chrome.exe | 10.193.94.171:80 | odduuqnxvzqftyfh.onion | — | — | unknown |
1720 | chrome.exe | 10.217.47.118:80 | hb4pm4eznzhd6mts.onion | — | — | unknown |
1720 | chrome.exe | 10.245.151.119:80 | gante6n6fjopy6sf.onion | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wikitjerrta4qgz4.onion |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ow24et3tetp6tvmk.onion |
| unknown |
torlinkbgs6aabns.onion |
| unknown |
easycoinsayj7p5l.onion |
| unknown |
3dbr5t4pygahedms.onion |
| suspicious |
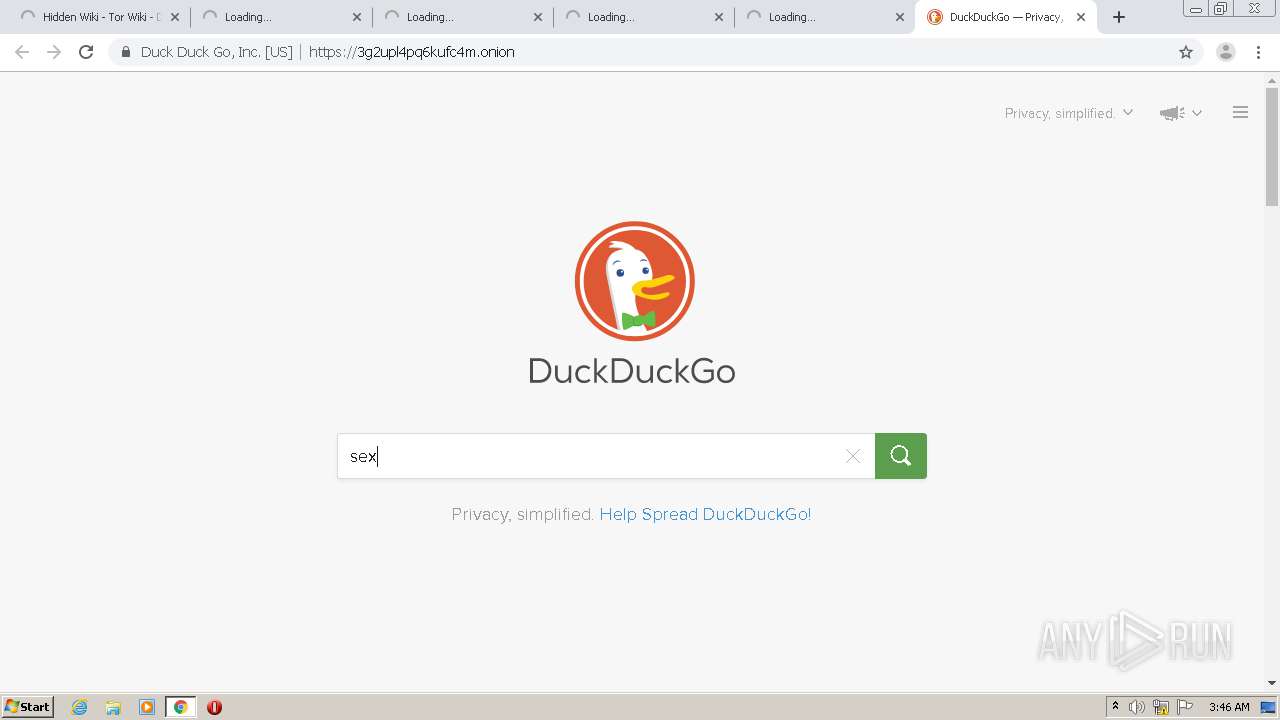
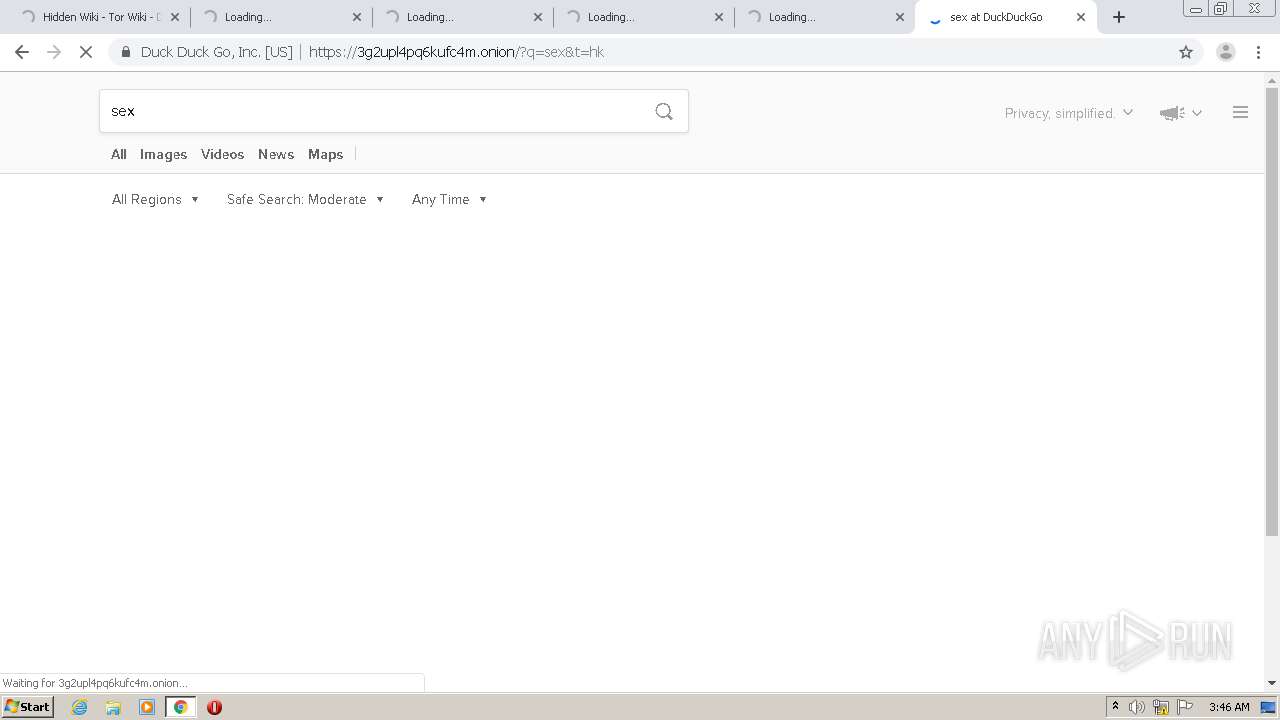
3g2upl4pq6kufc4m.onion |
| unknown |
6dyi4t72u7y6g763.onion |
| unknown |
ahmia.fi |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1048 | svchost.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
1048 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1048 | svchost.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
1048 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1048 | svchost.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
1048 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1048 | svchost.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
1048 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1048 | svchost.exe | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |