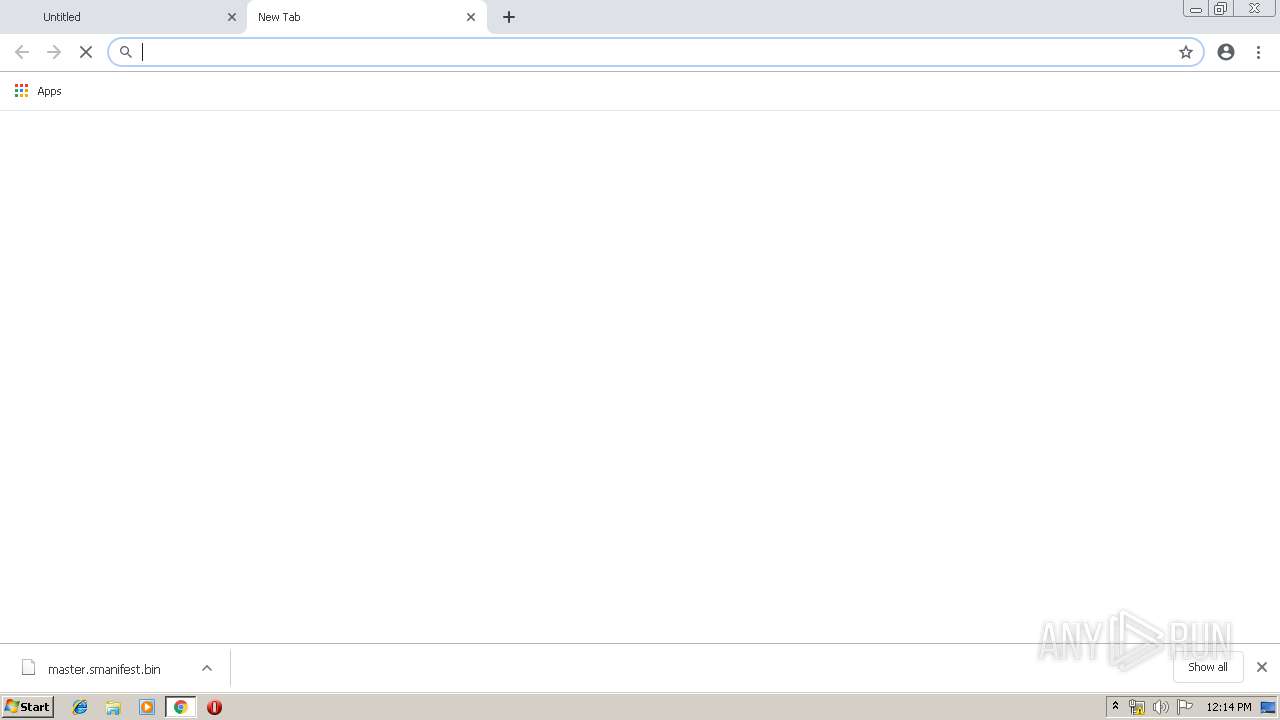
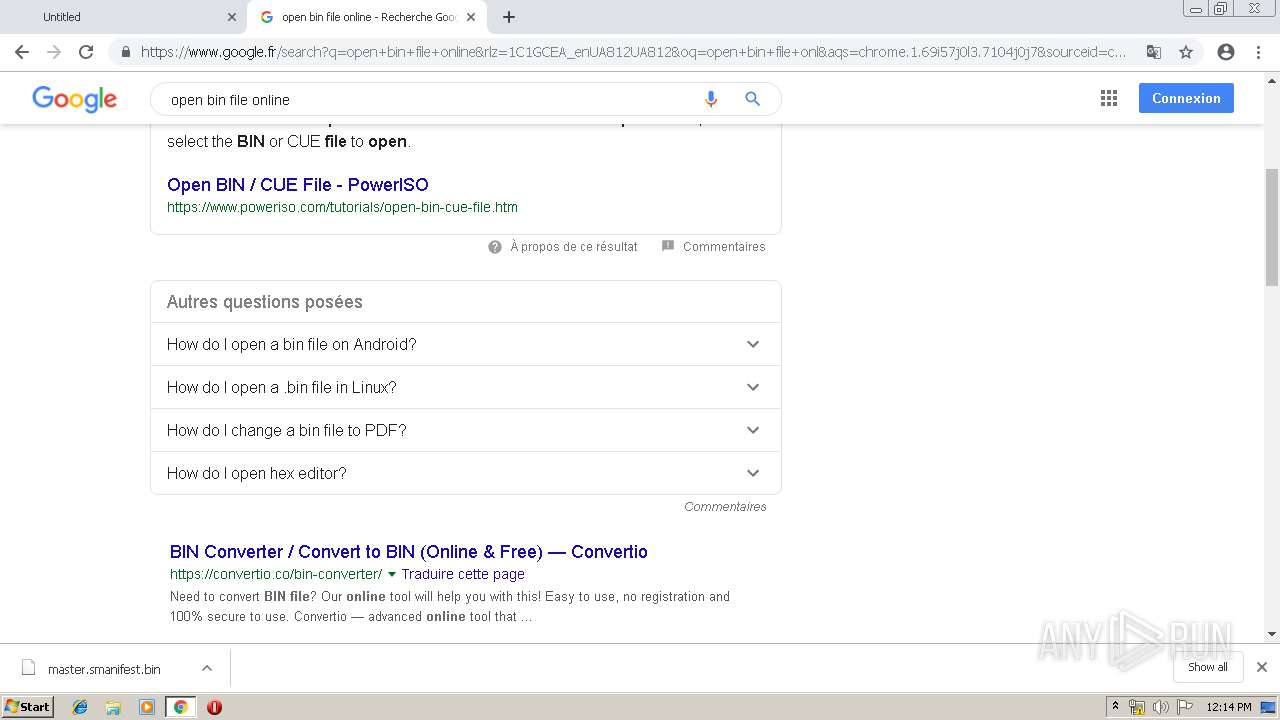
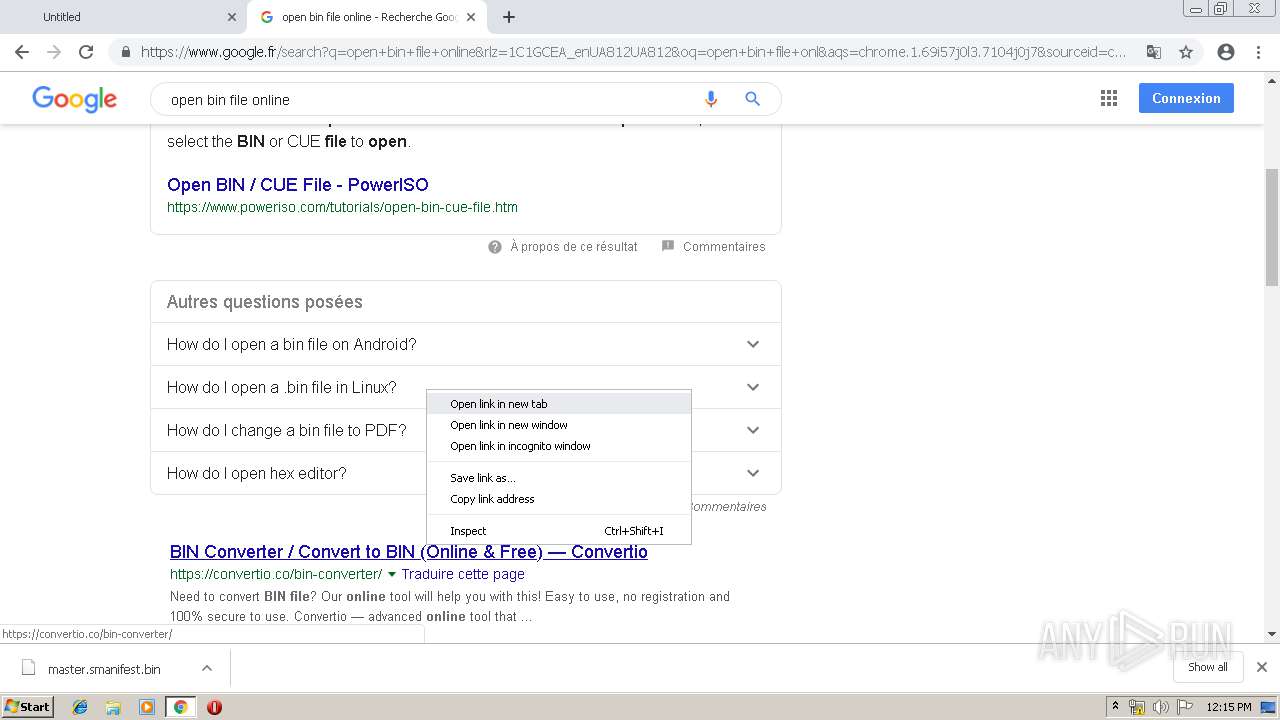
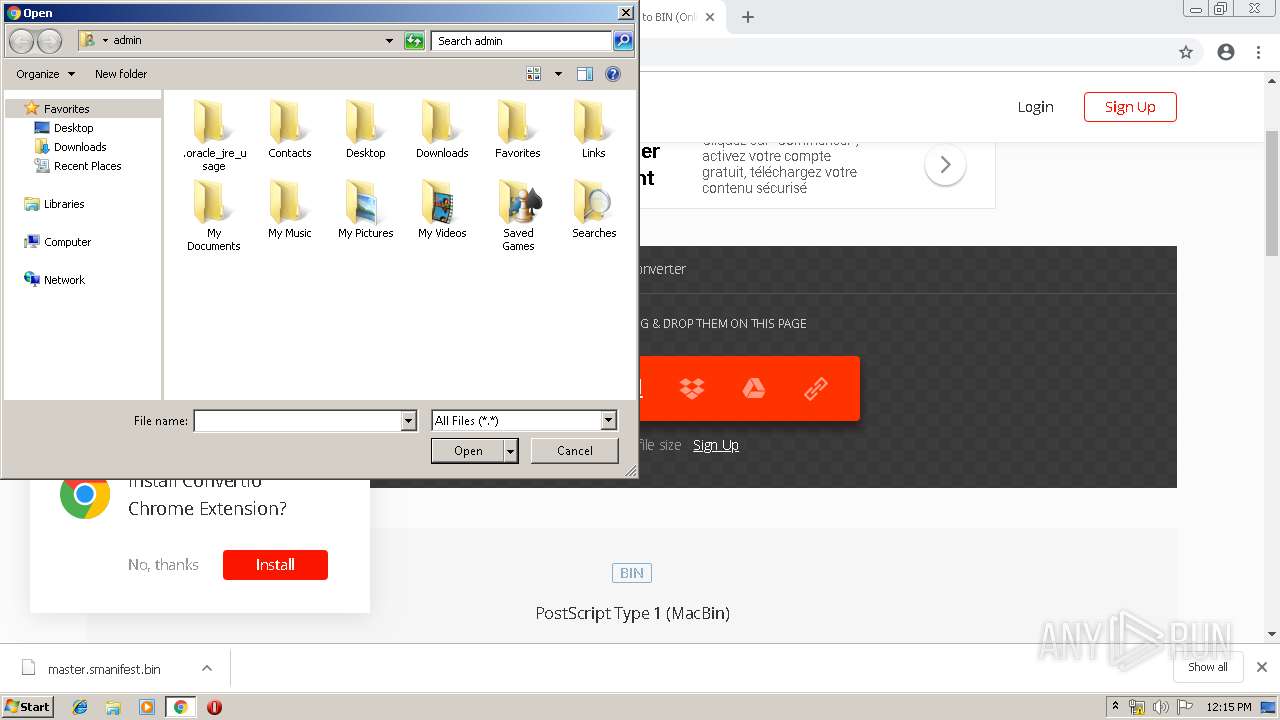
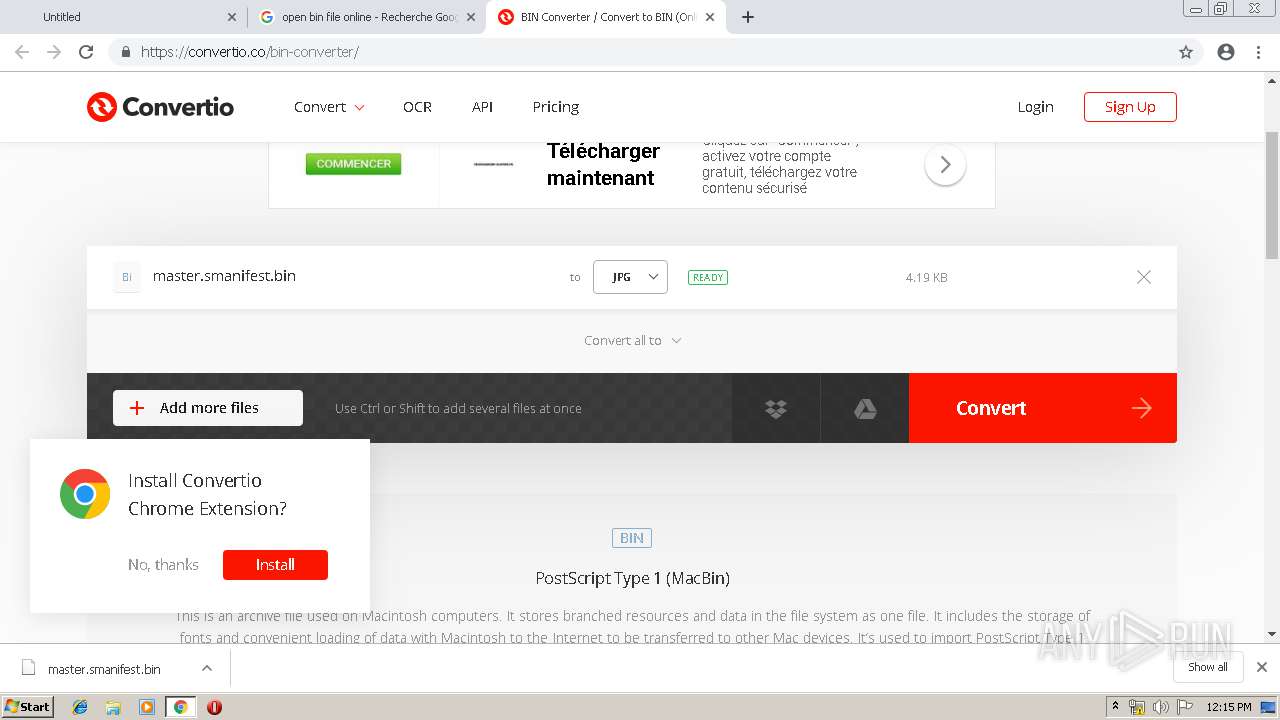
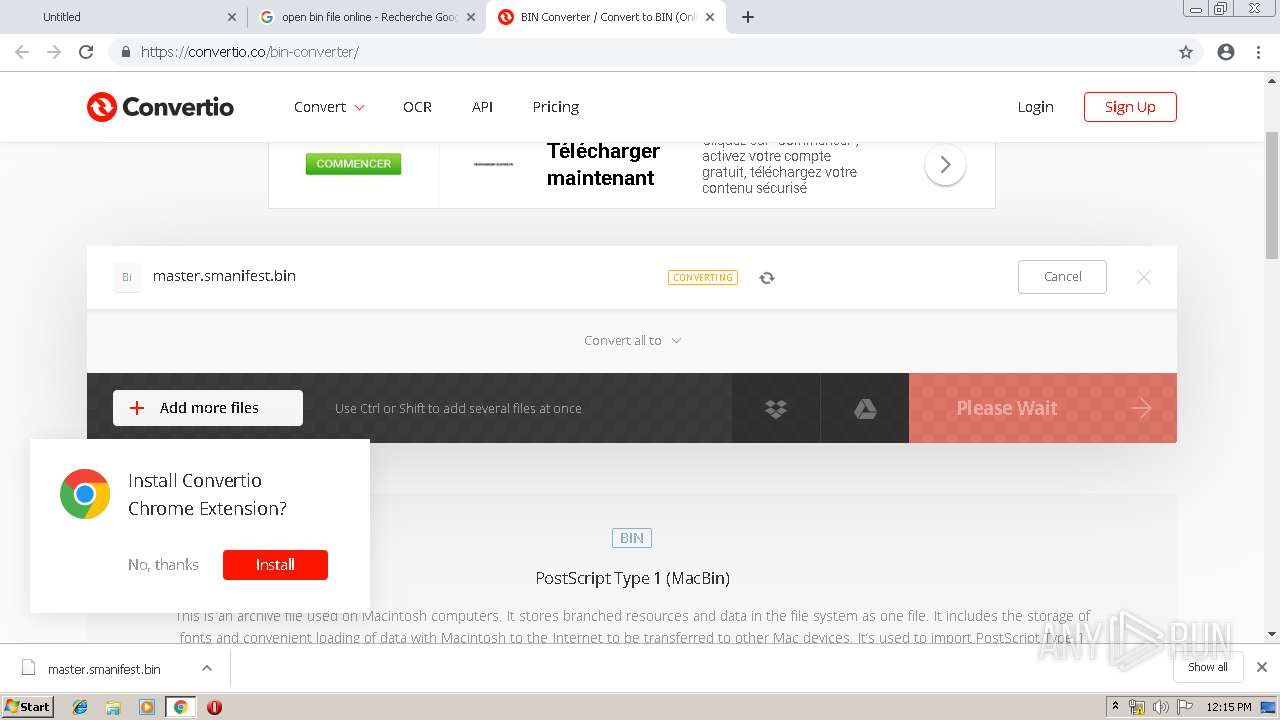
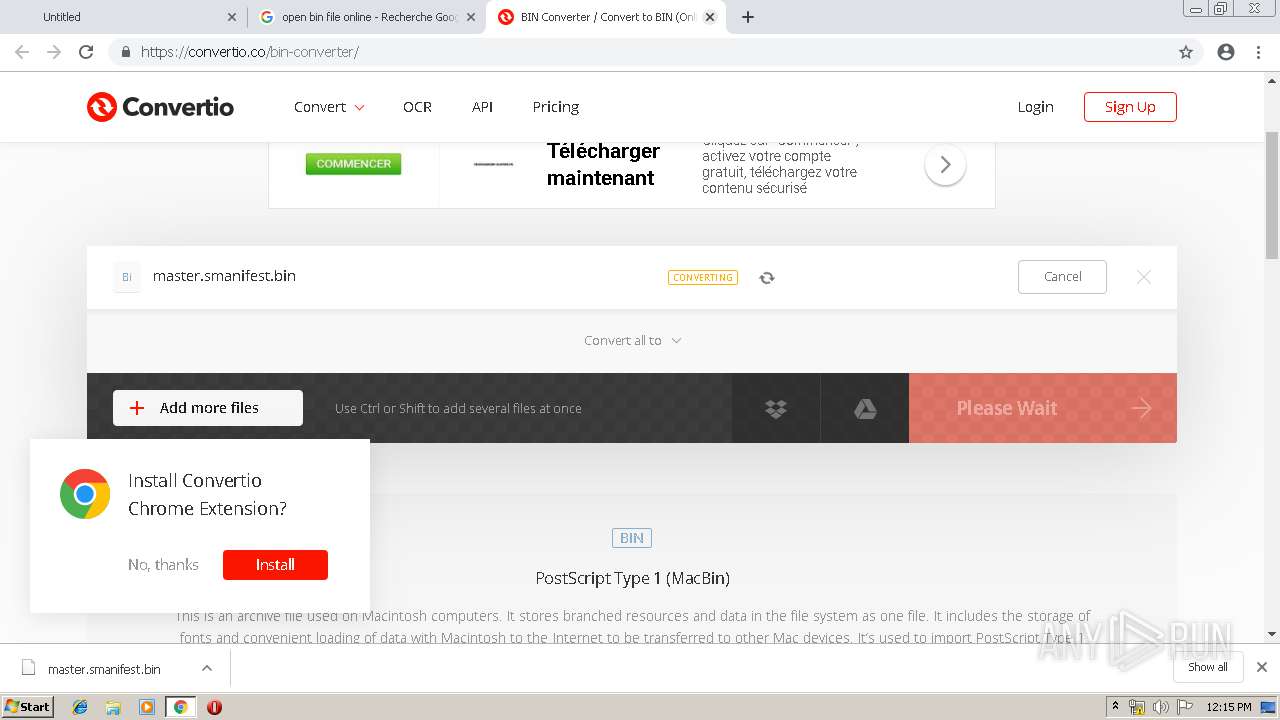
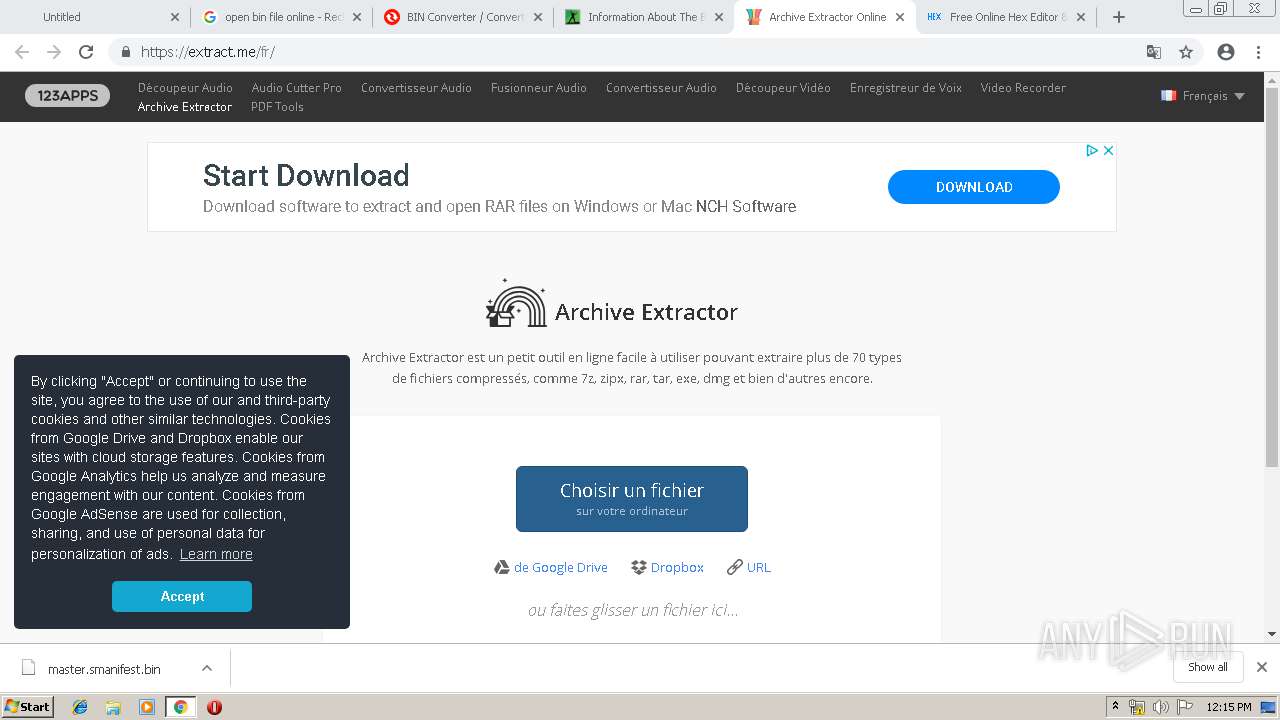
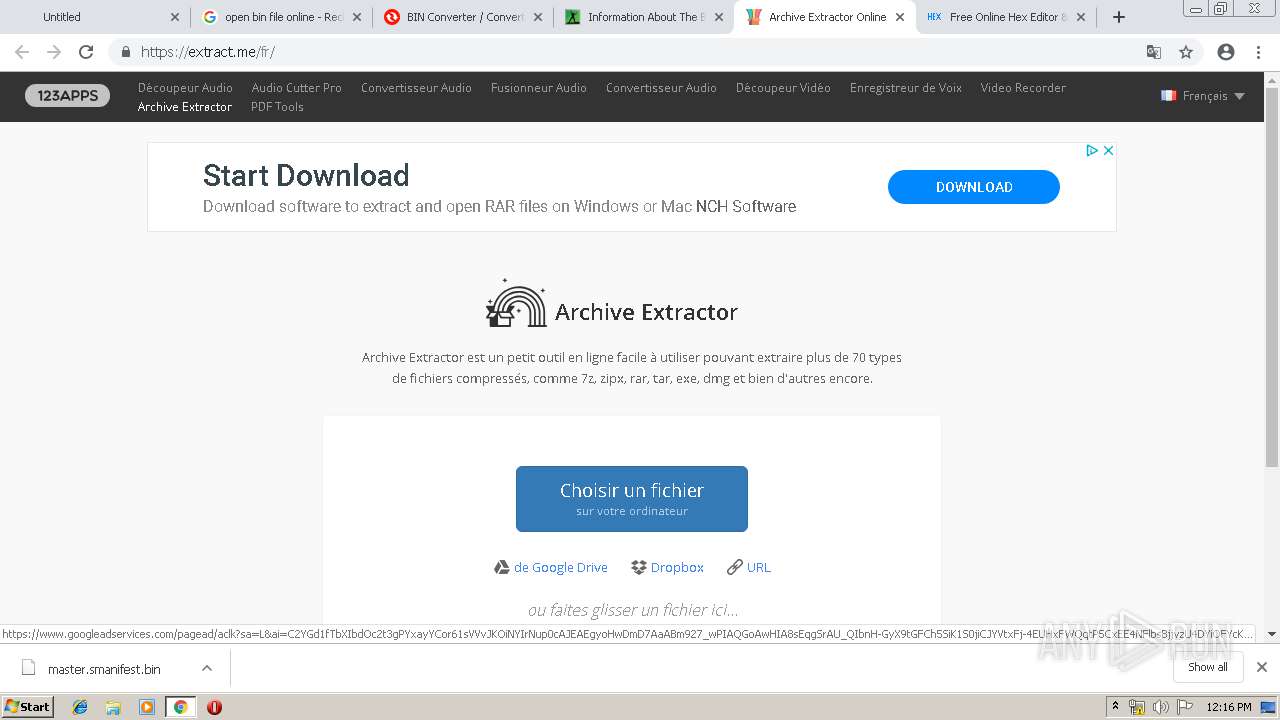
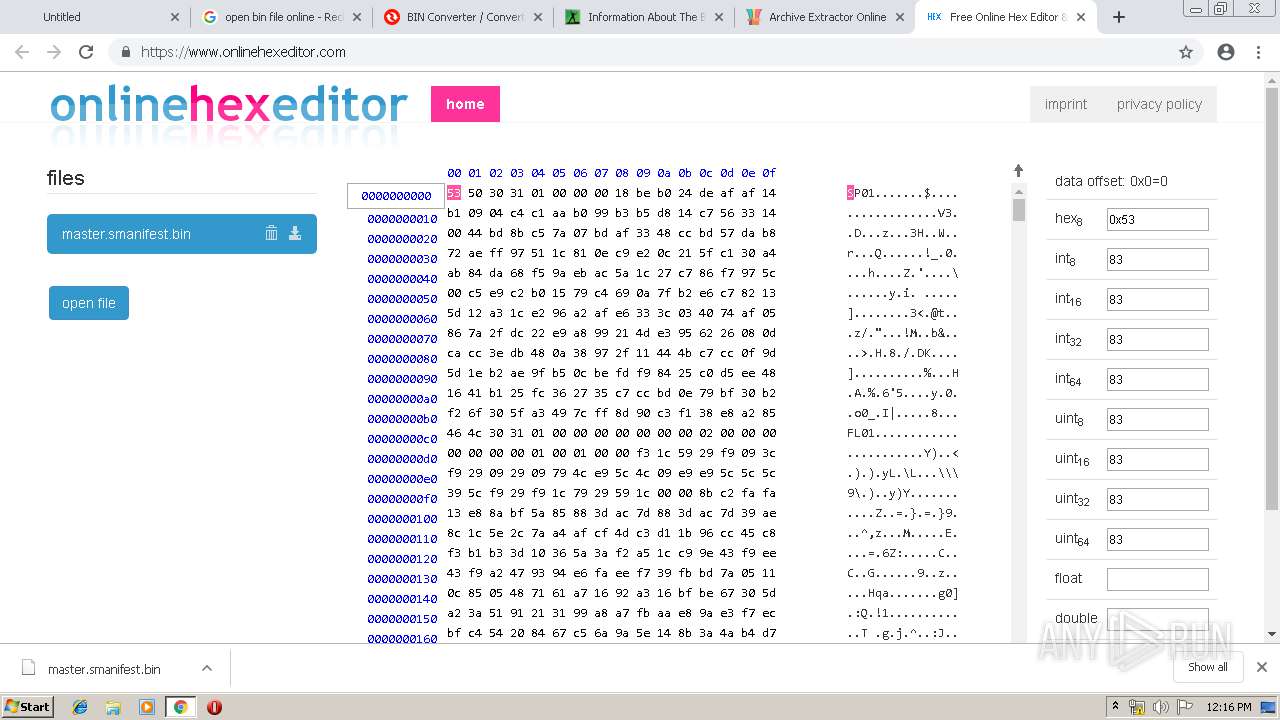
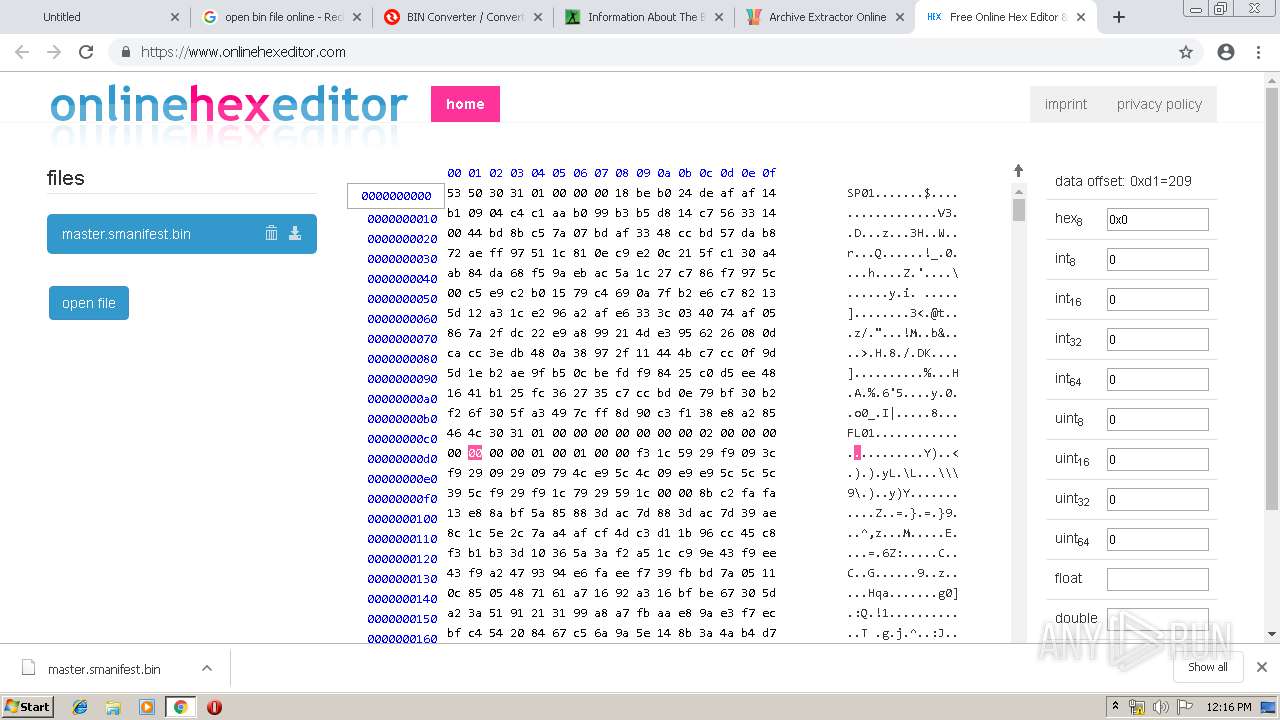
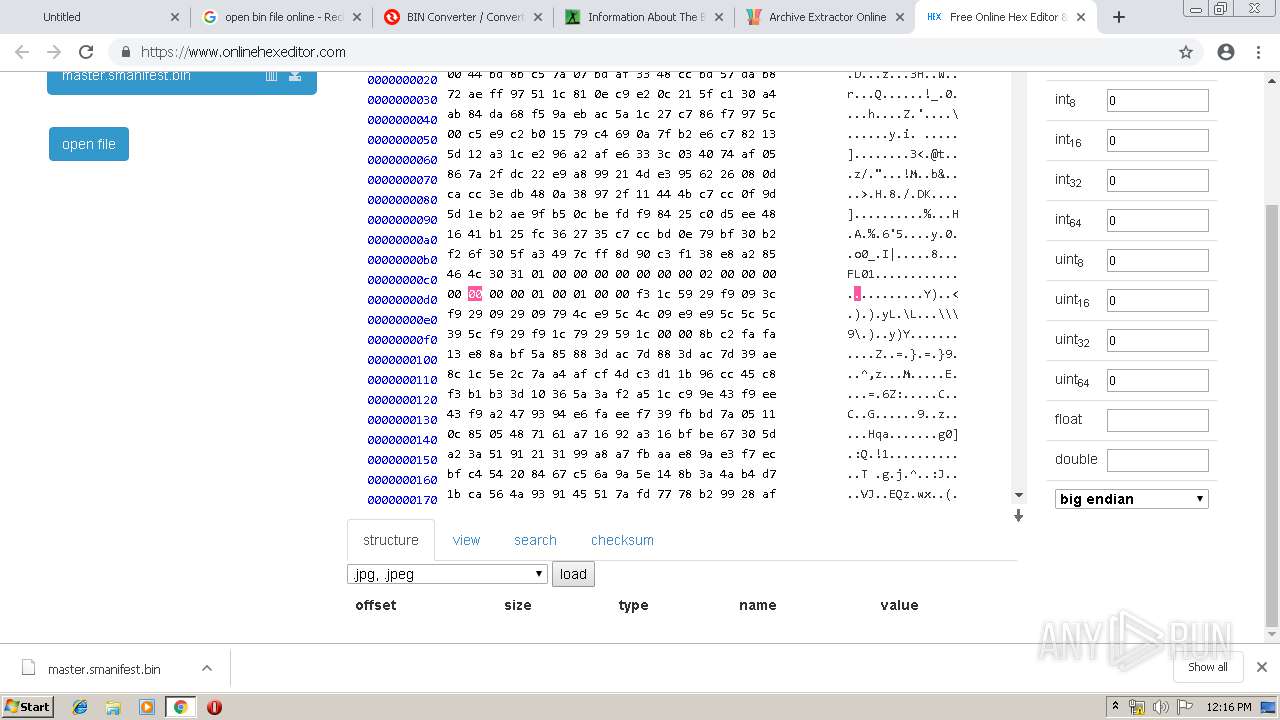
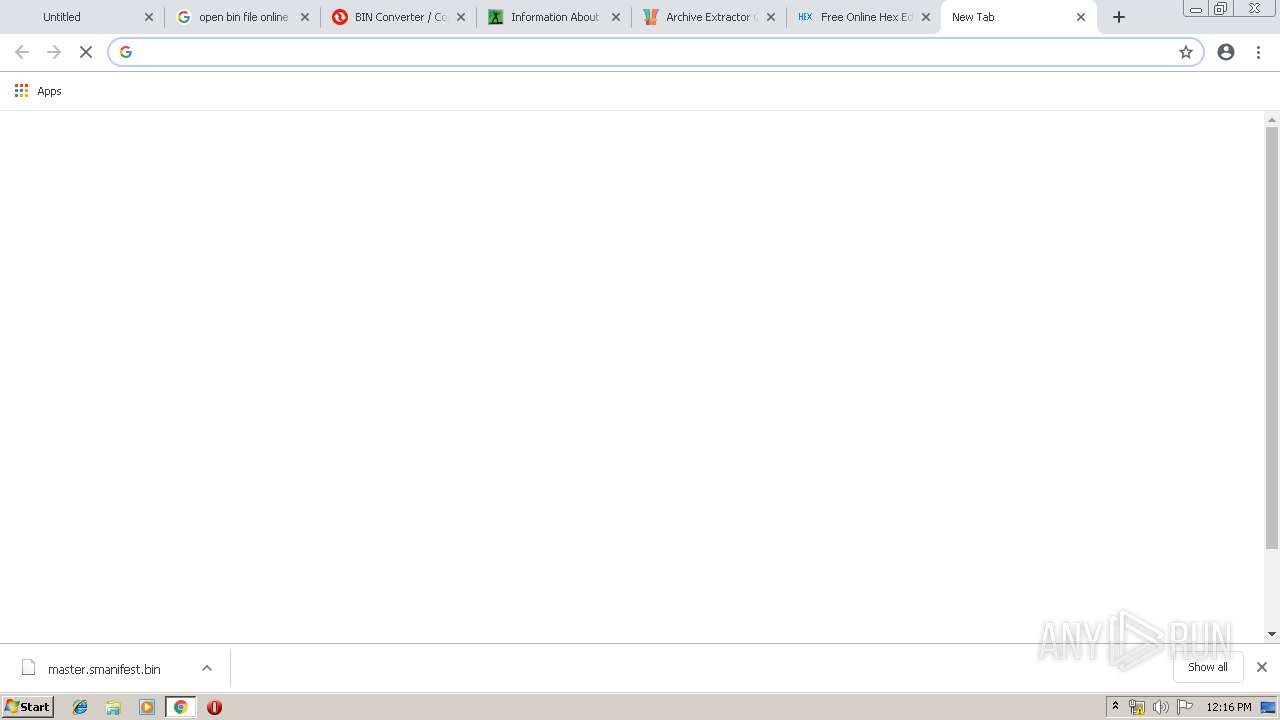
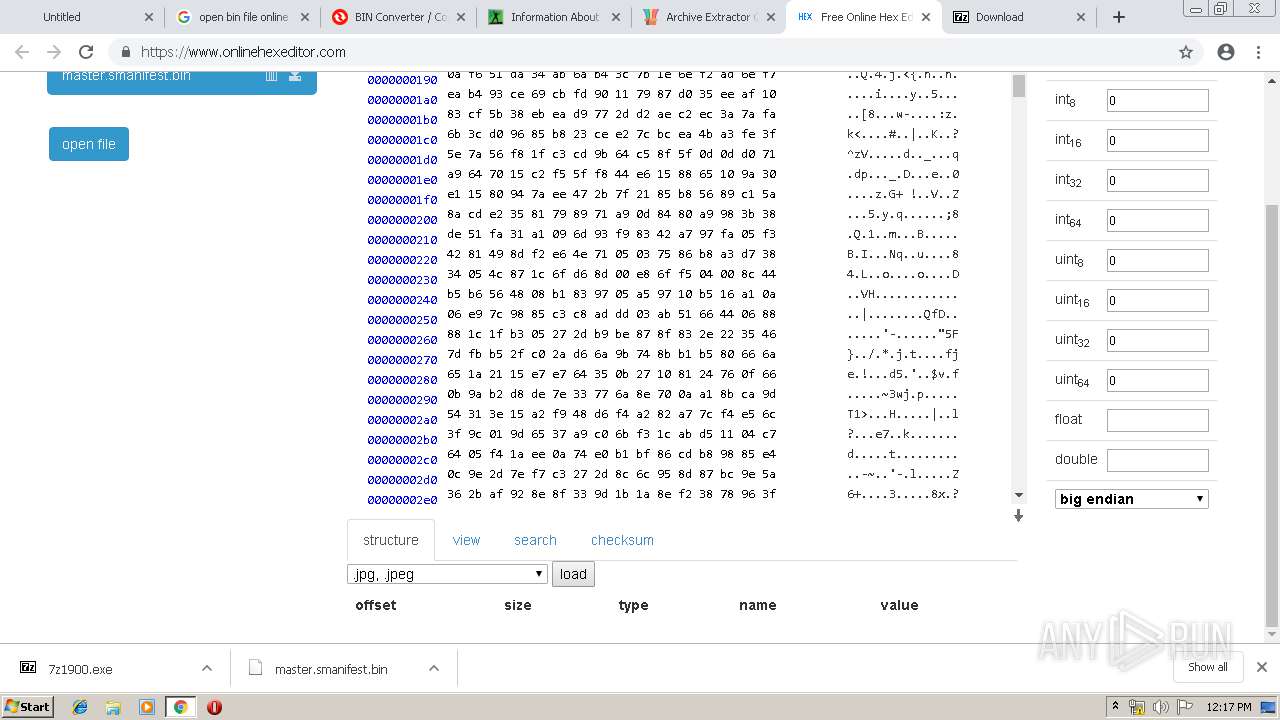
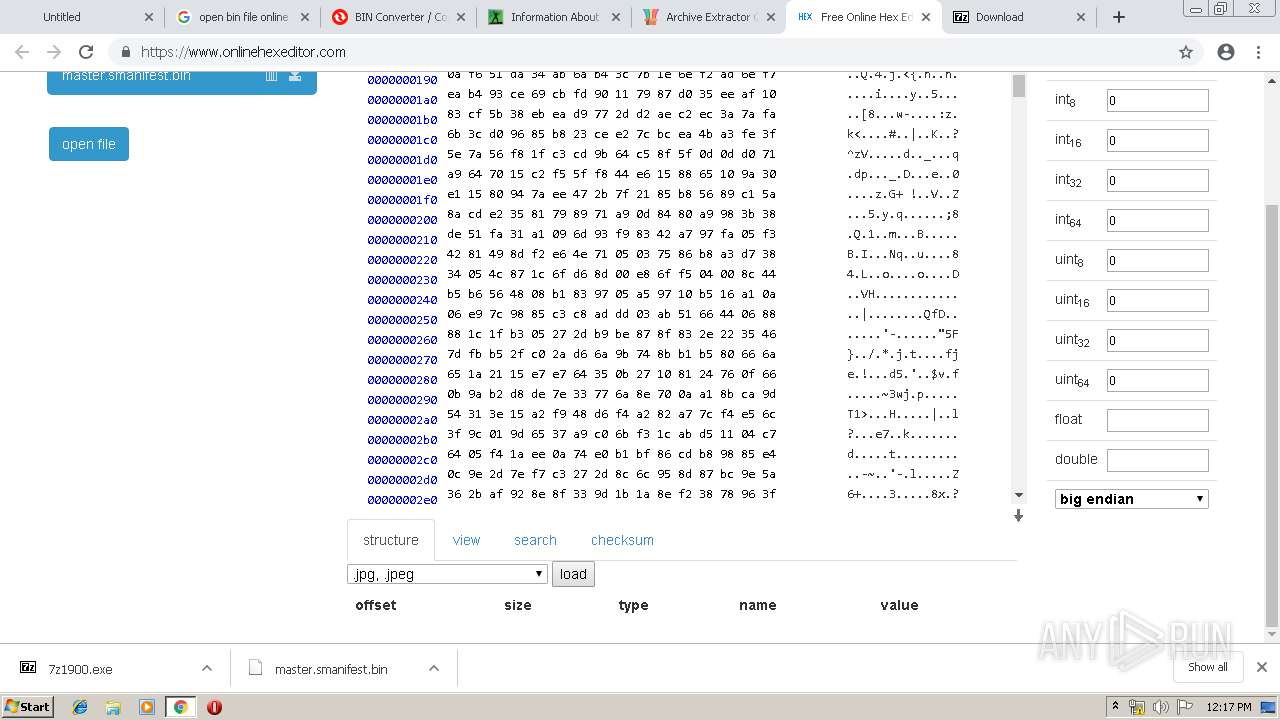
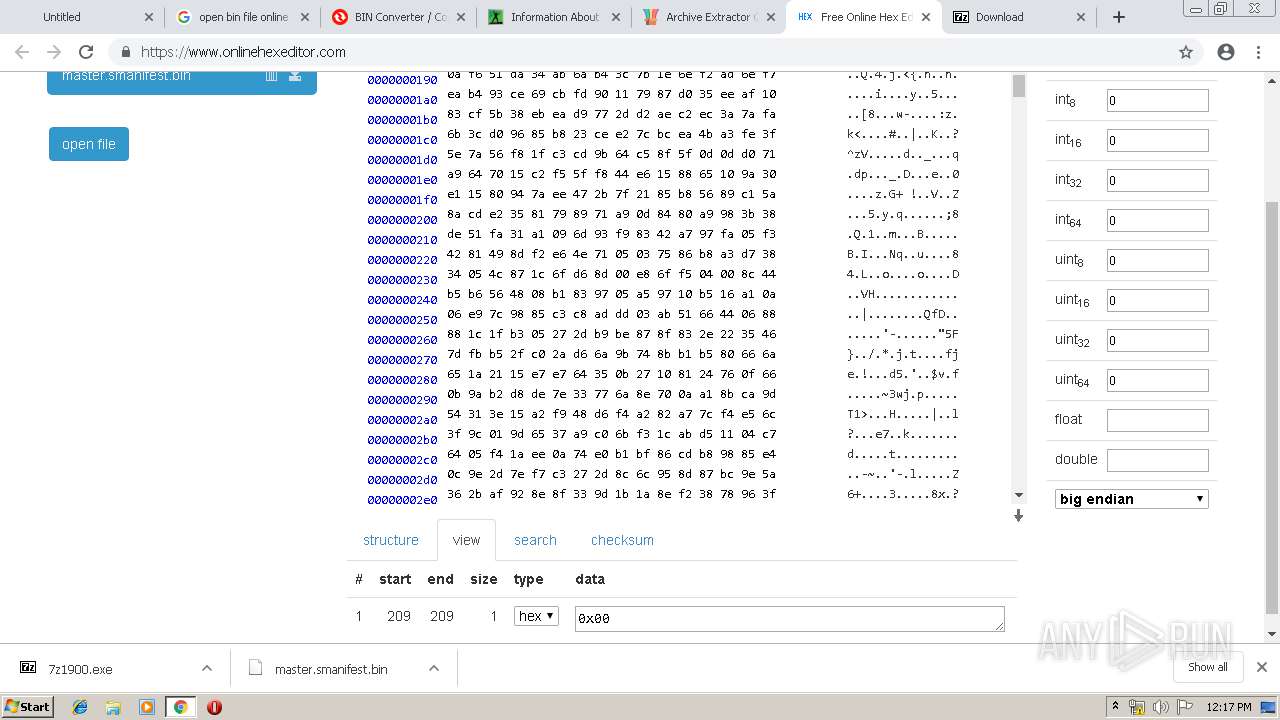
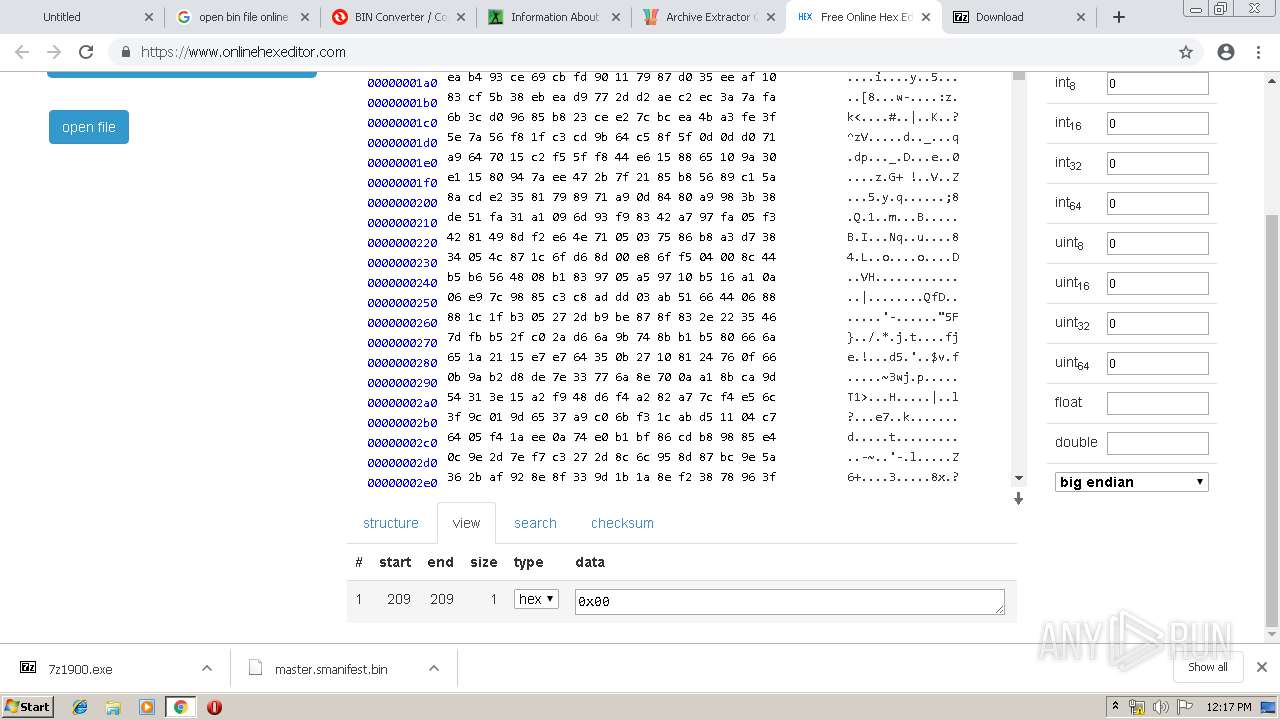
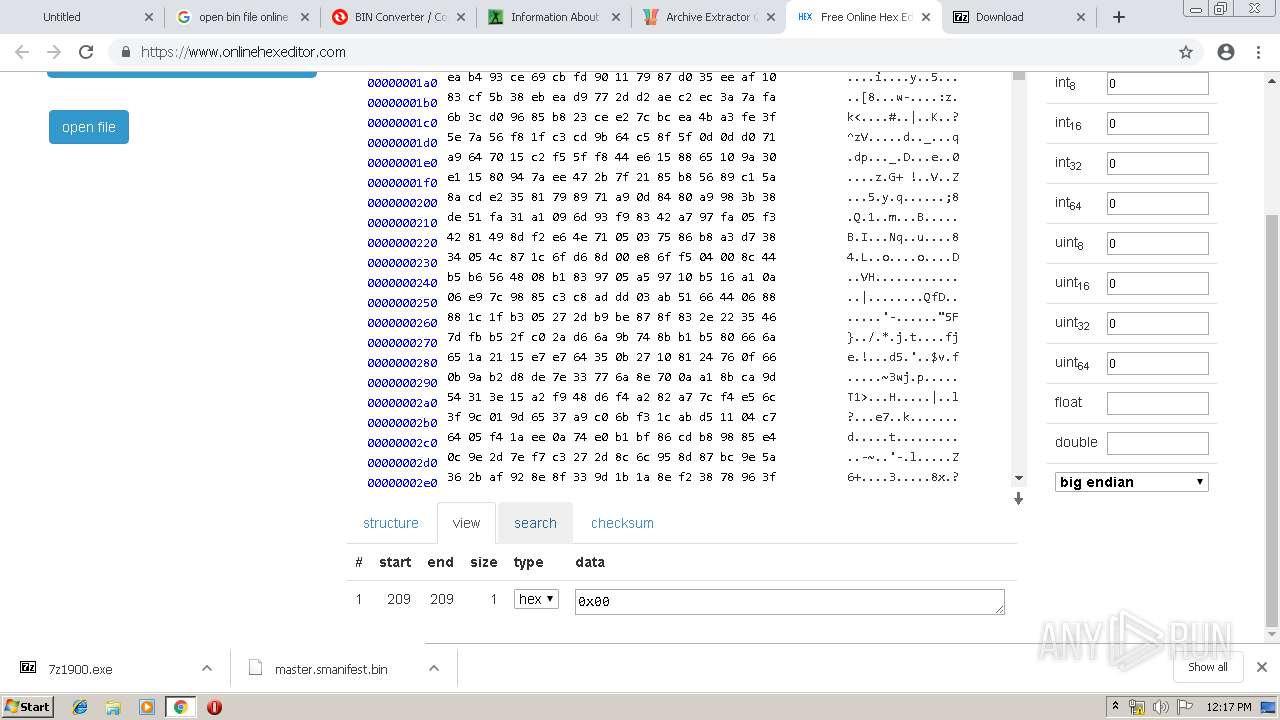
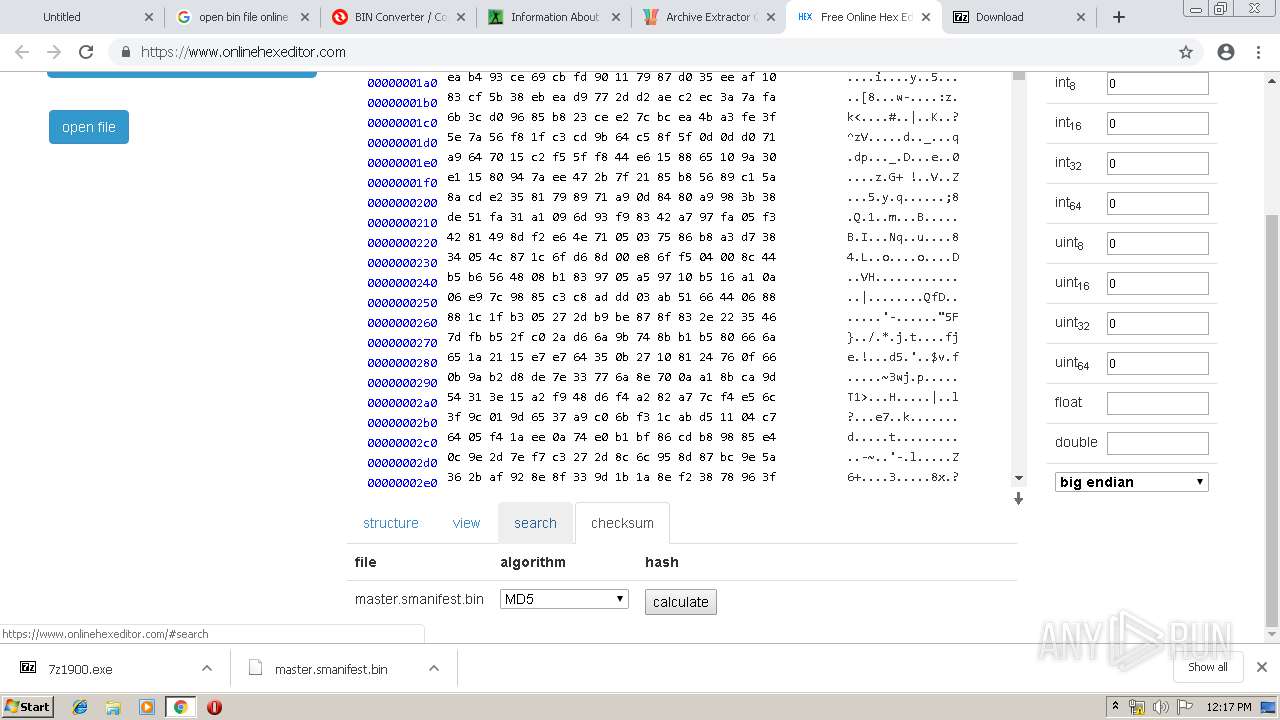
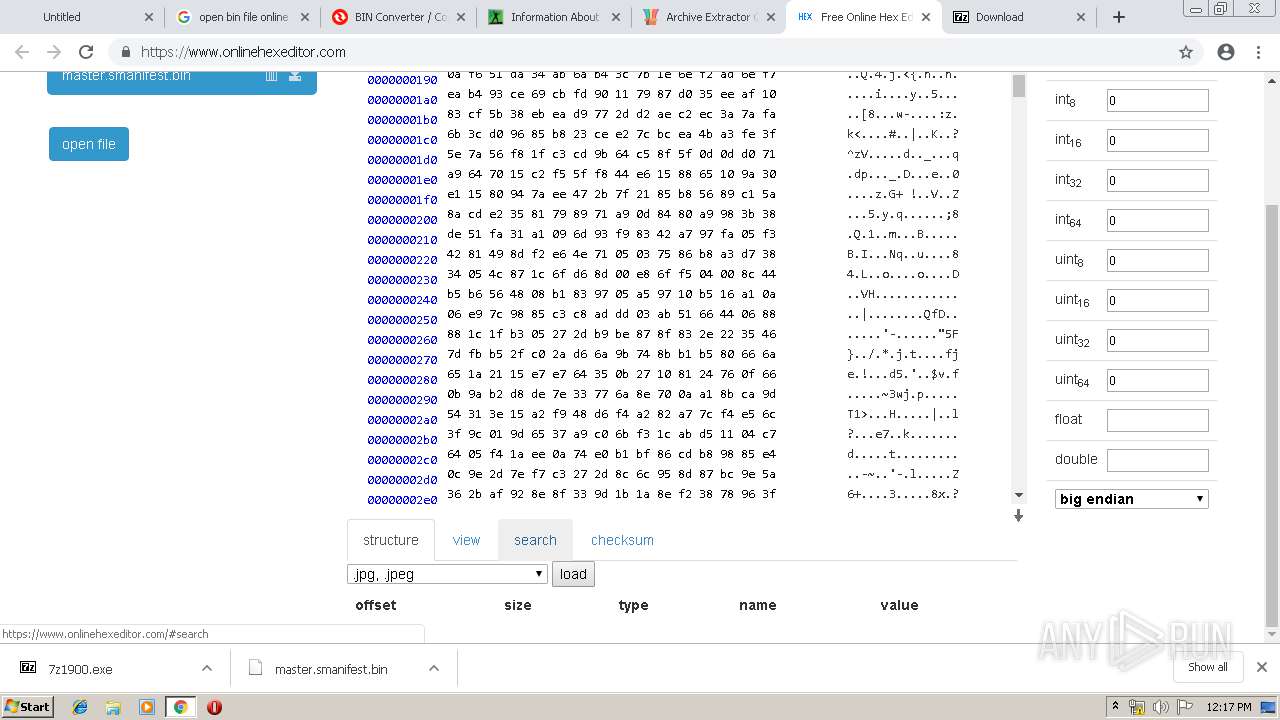
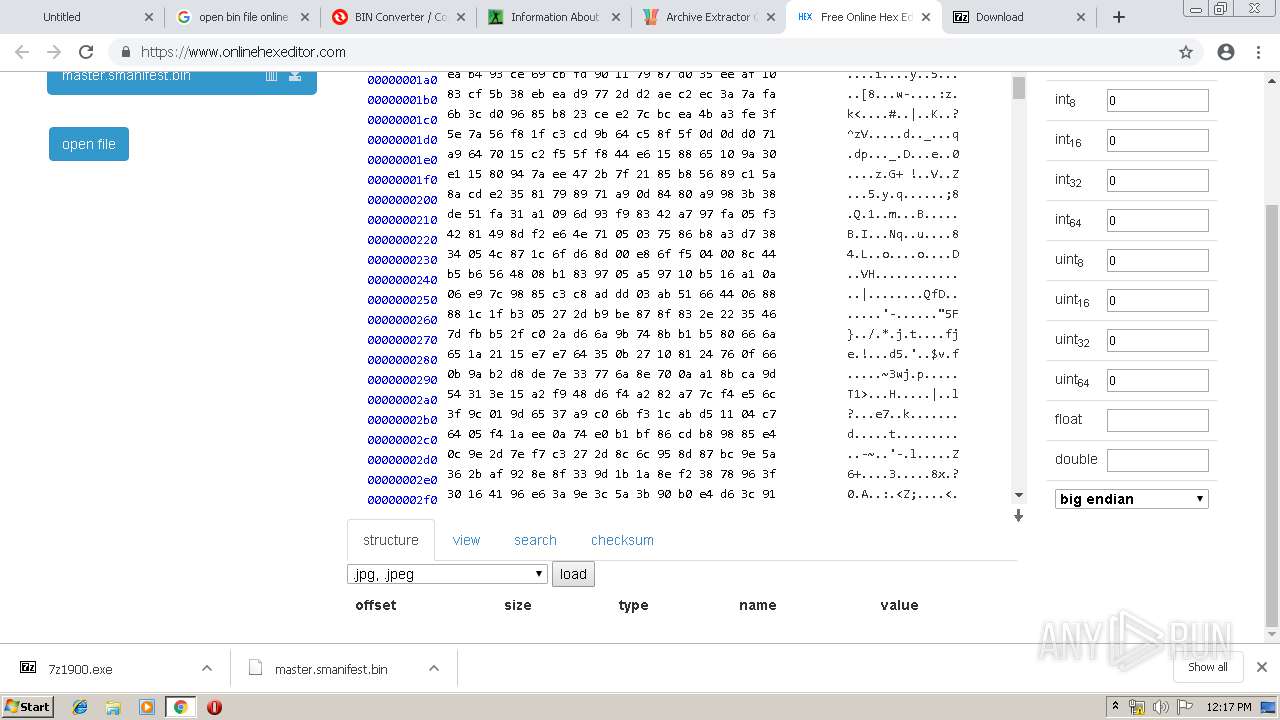
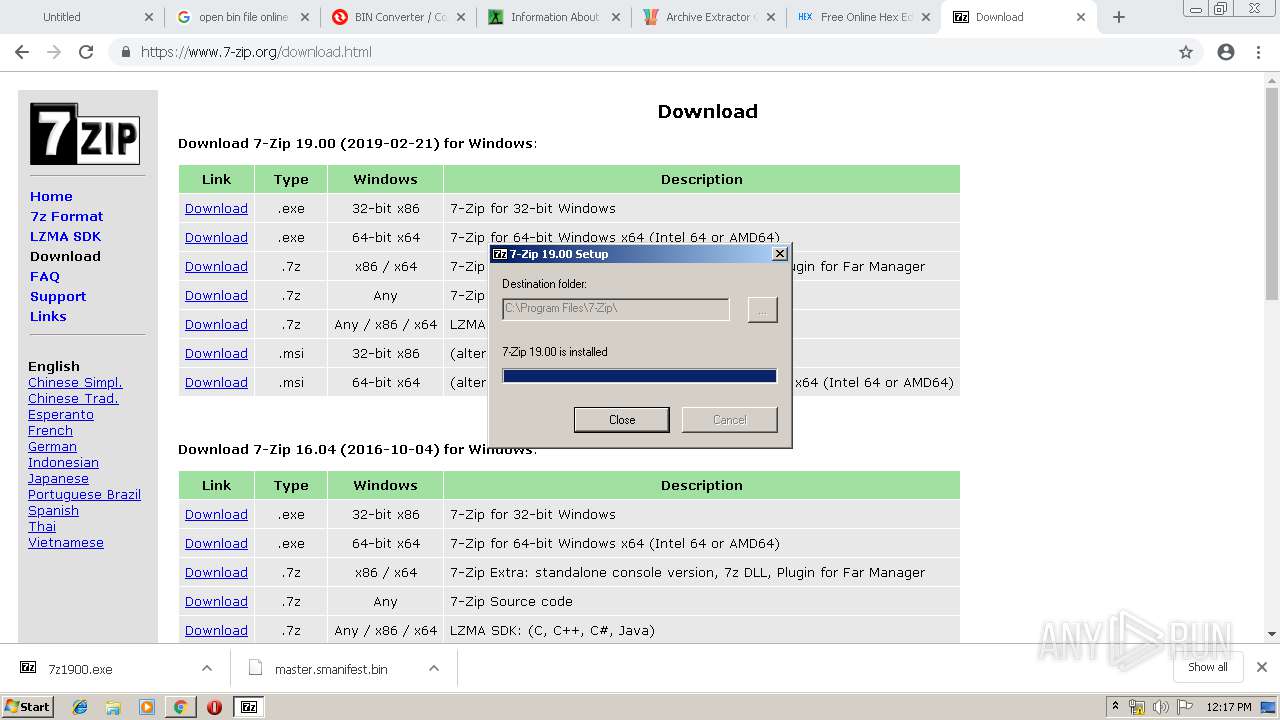
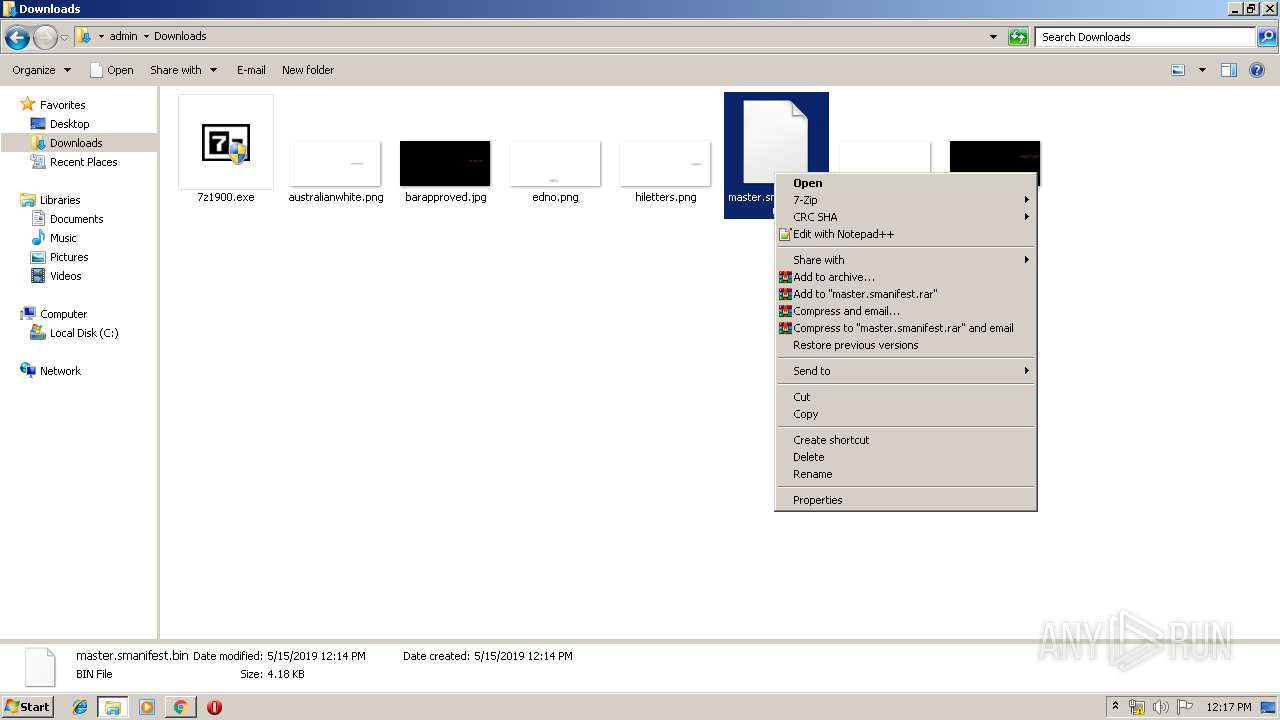
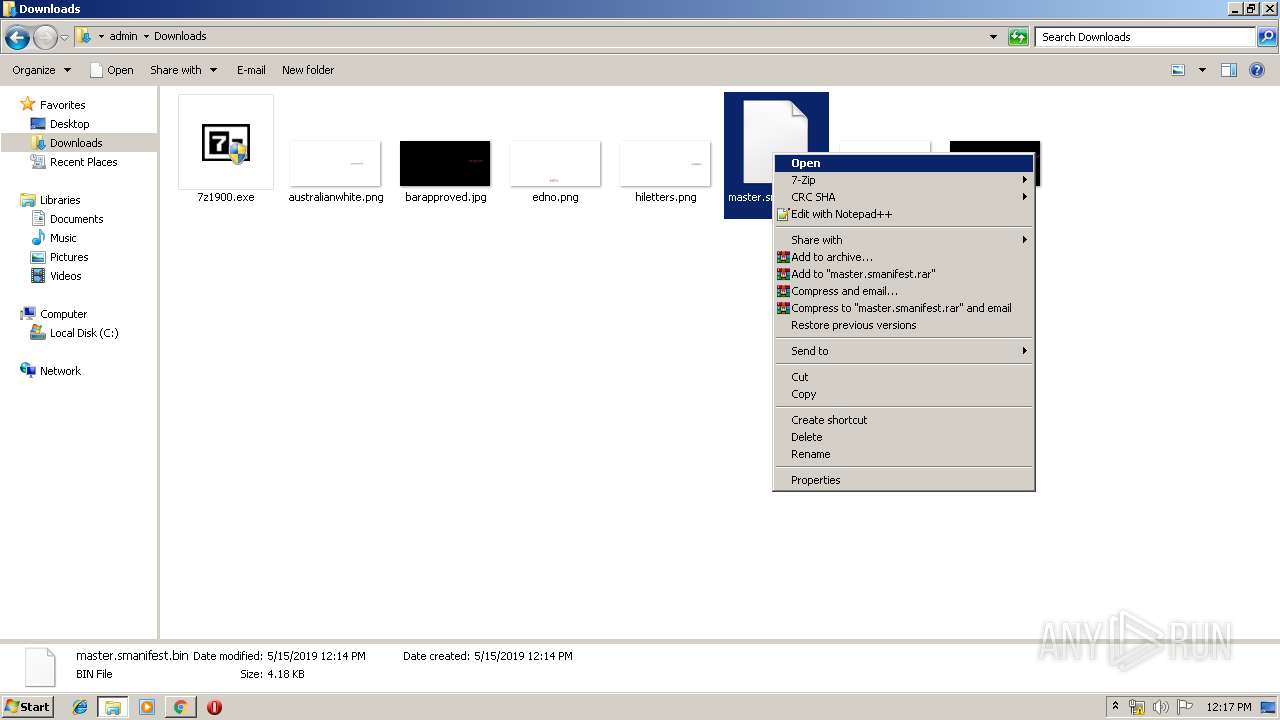
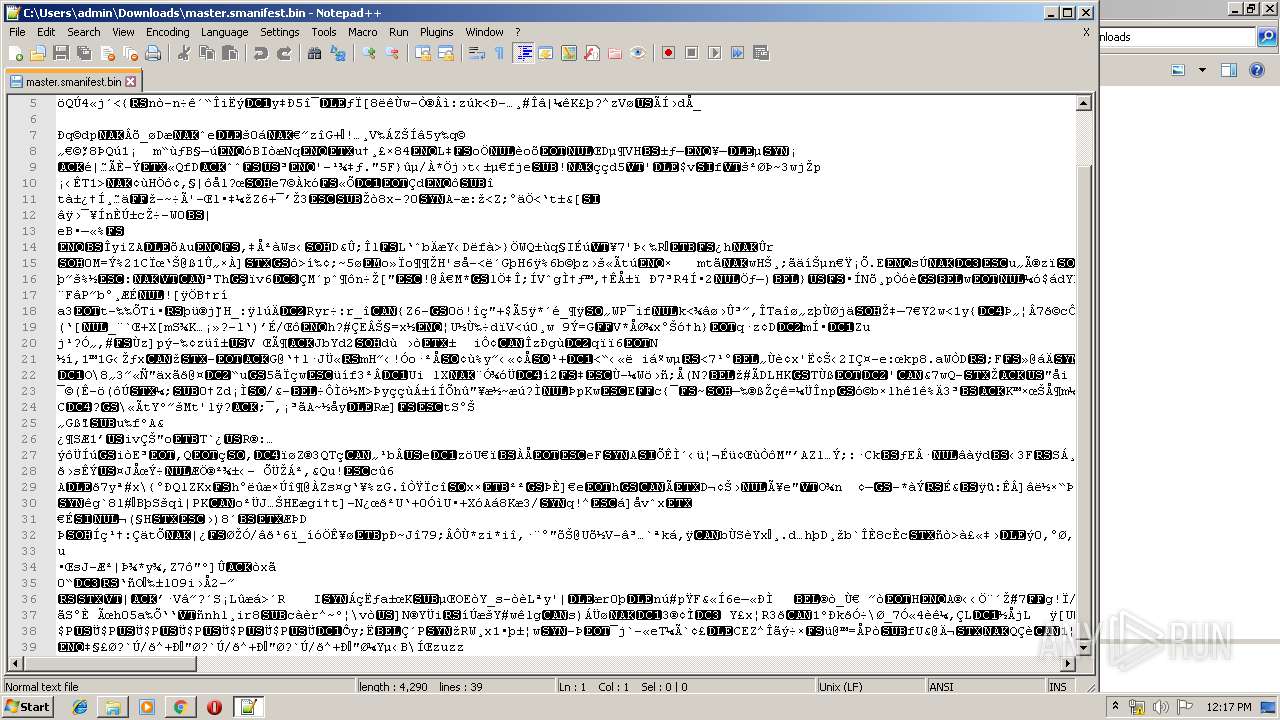
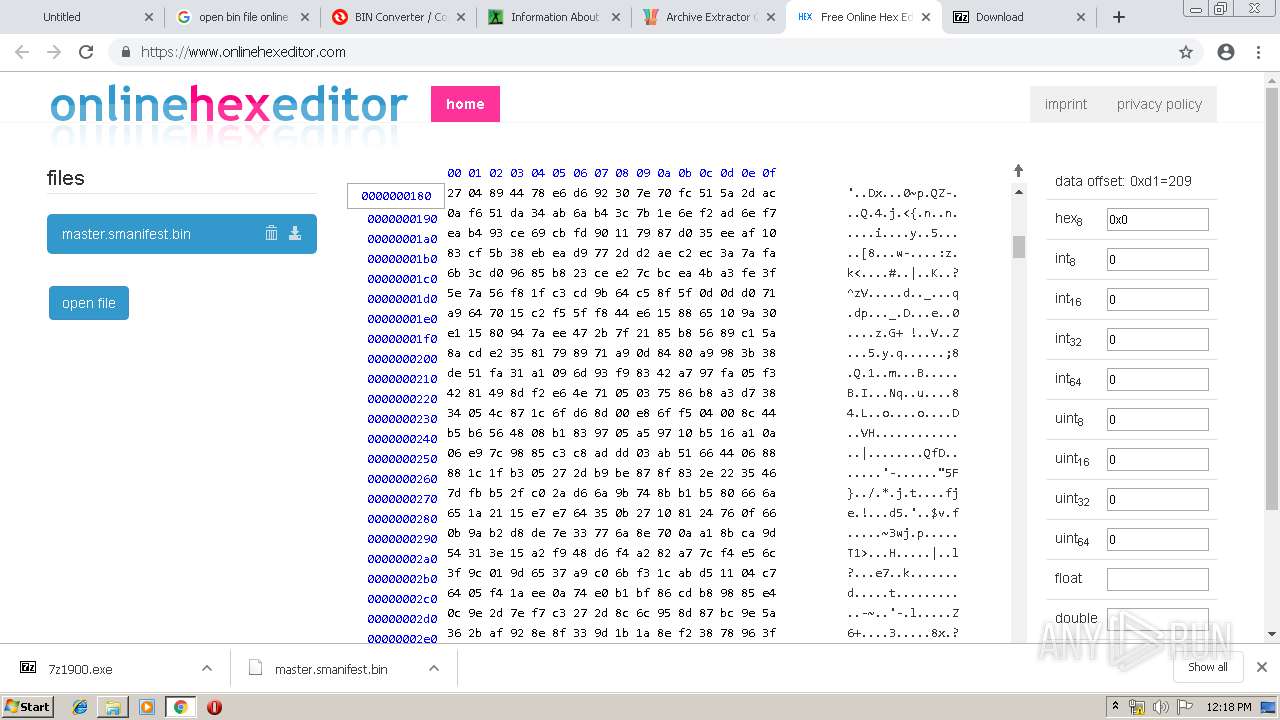
| URL: | http://s3.amazonaws.com/contentpack/manifests/e0a816f3815189e3dd8664fcd43c93df/master.smanifest.bin |
| Full analysis: | https://app.any.run/tasks/8eb4fd16-a760-4cec-9a46-595642c6b6ea |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 11:14:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F163BF1D257563ECEFE3321D073A6E55 |
| SHA1: | 0125CE11B4E70E95142D7C272F0AAE75EDC24004 |
| SHA256: | 09E93FE5863194D5A45E8ED731F143379F17E8F6FDC5721954DEB786ECD38D52 |
| SSDEEP: | 3:N1KNY7WtGKL8zPORWCWTDaUQUeA+lGnB1IWRMbAWRLqn:CatQwGWnGJHcAWy9O |
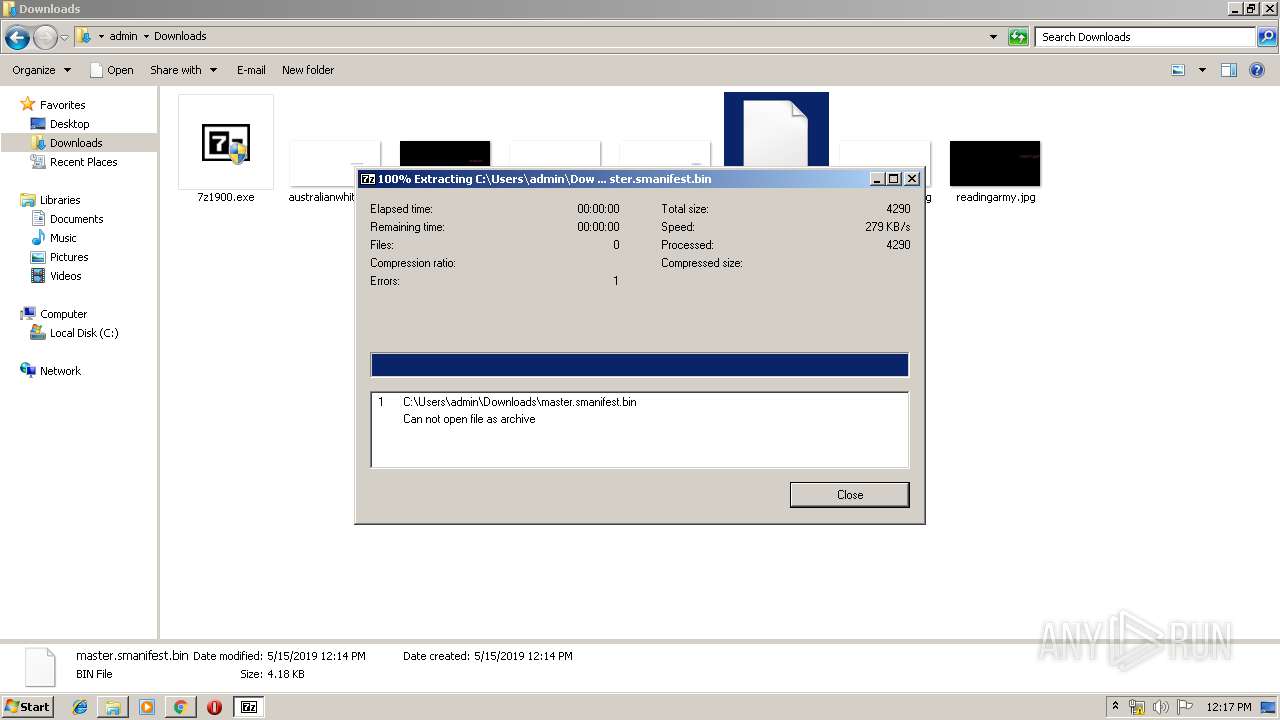
MALICIOUS
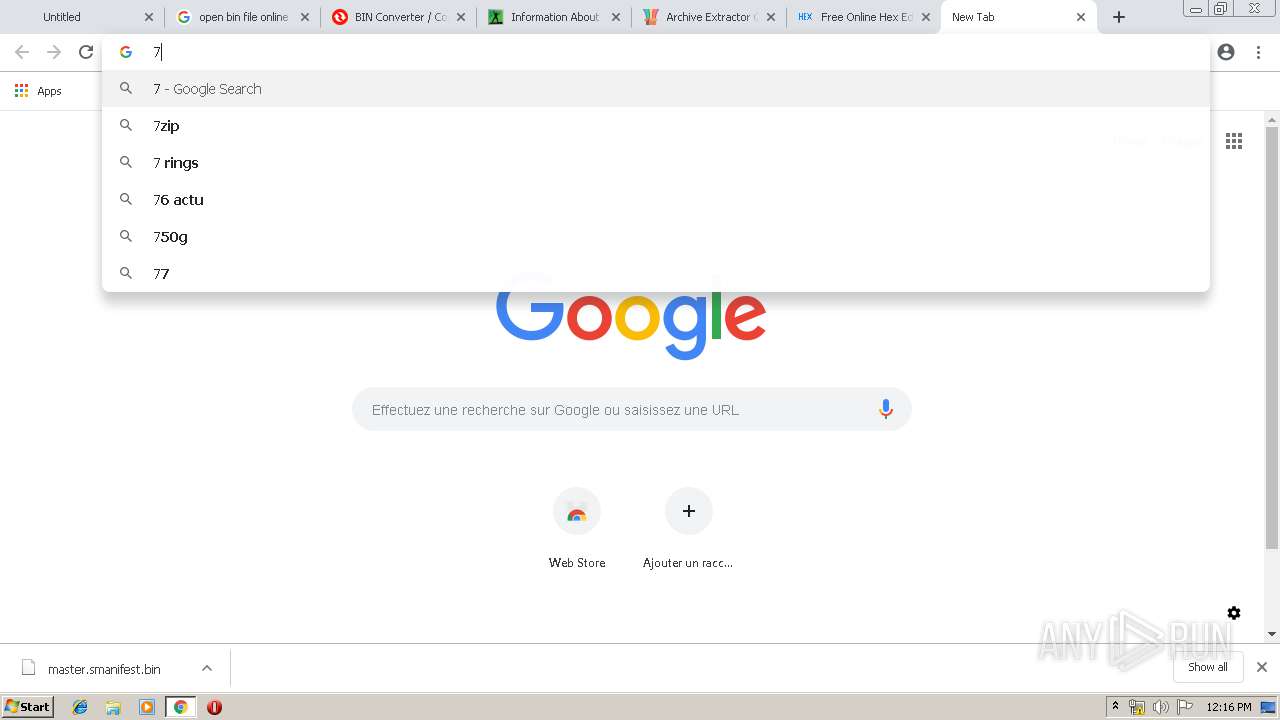
Loads dropped or rewritten executable
- explorer.exe (PID: 252)
- 7zG.exe (PID: 2900)
- svchost.exe (PID: 848)
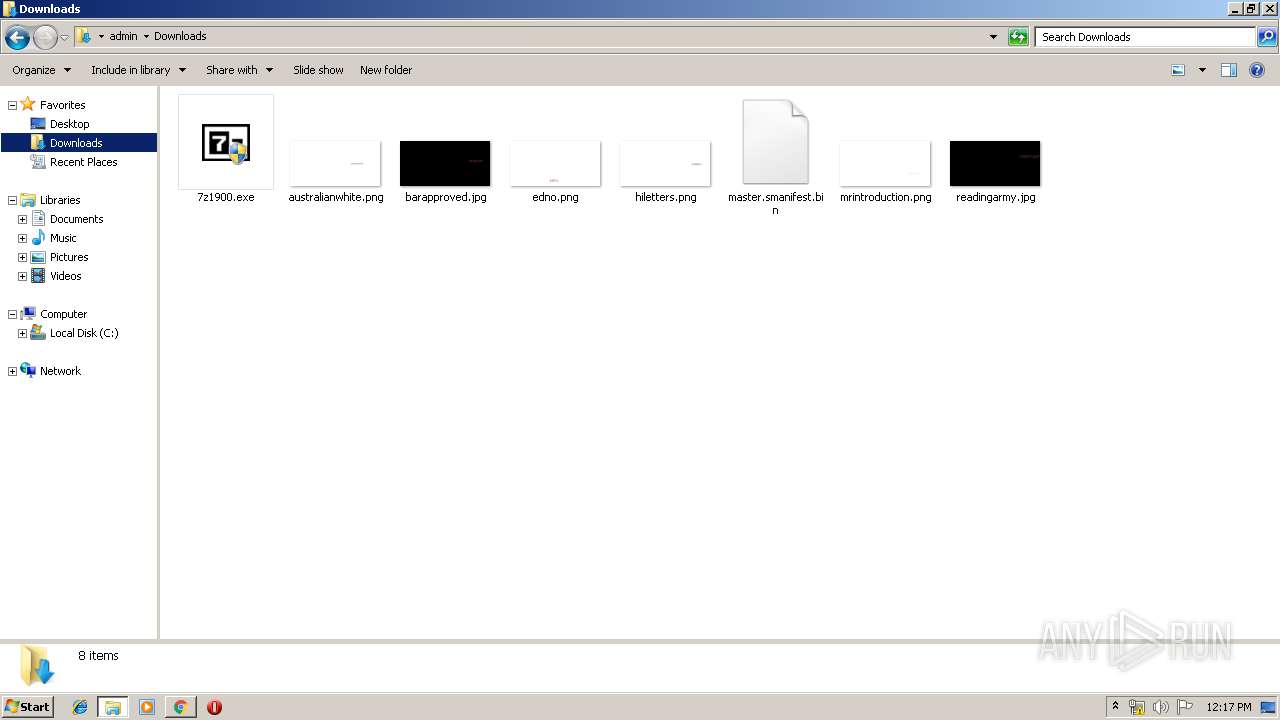
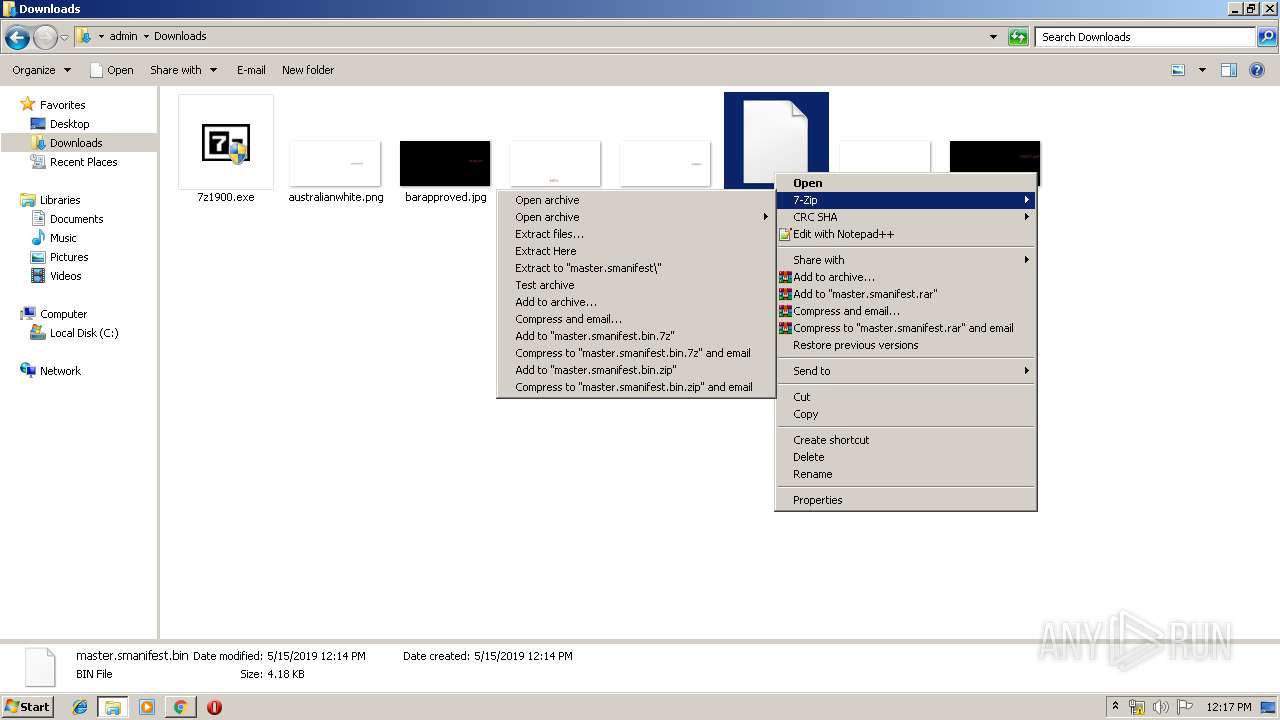
Application was dropped or rewritten from another process
- 7zG.exe (PID: 2900)
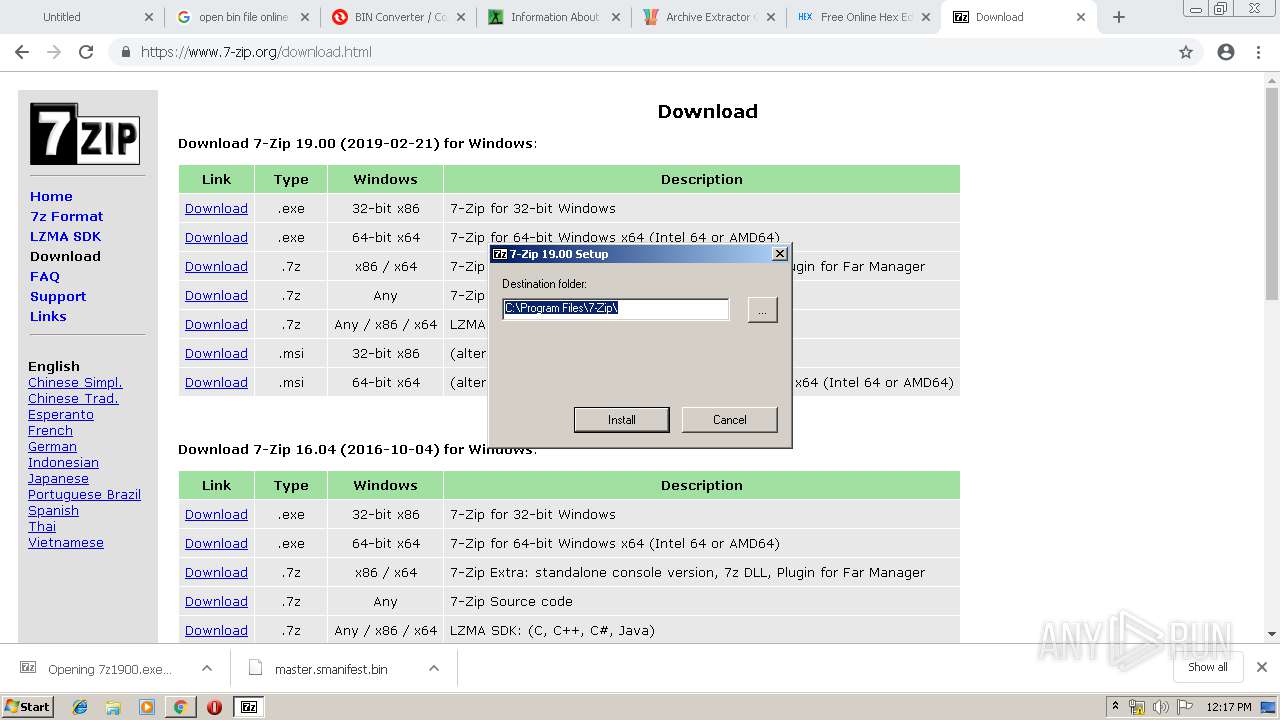
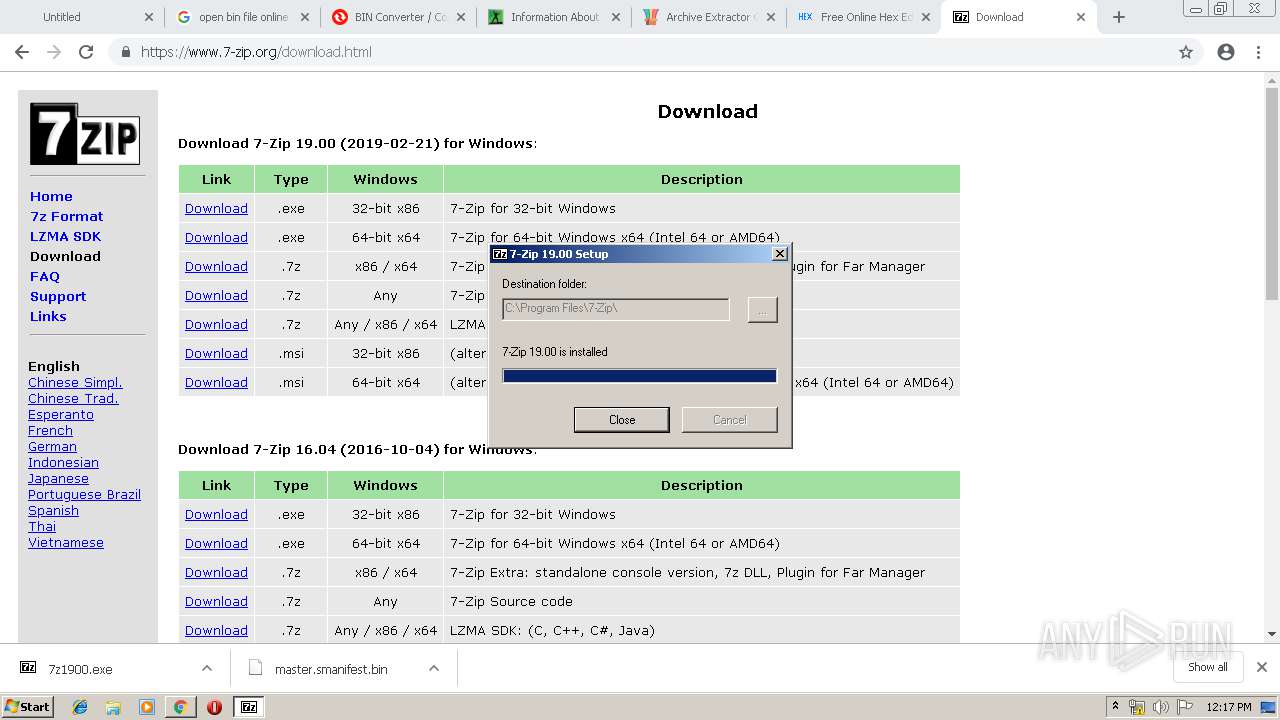
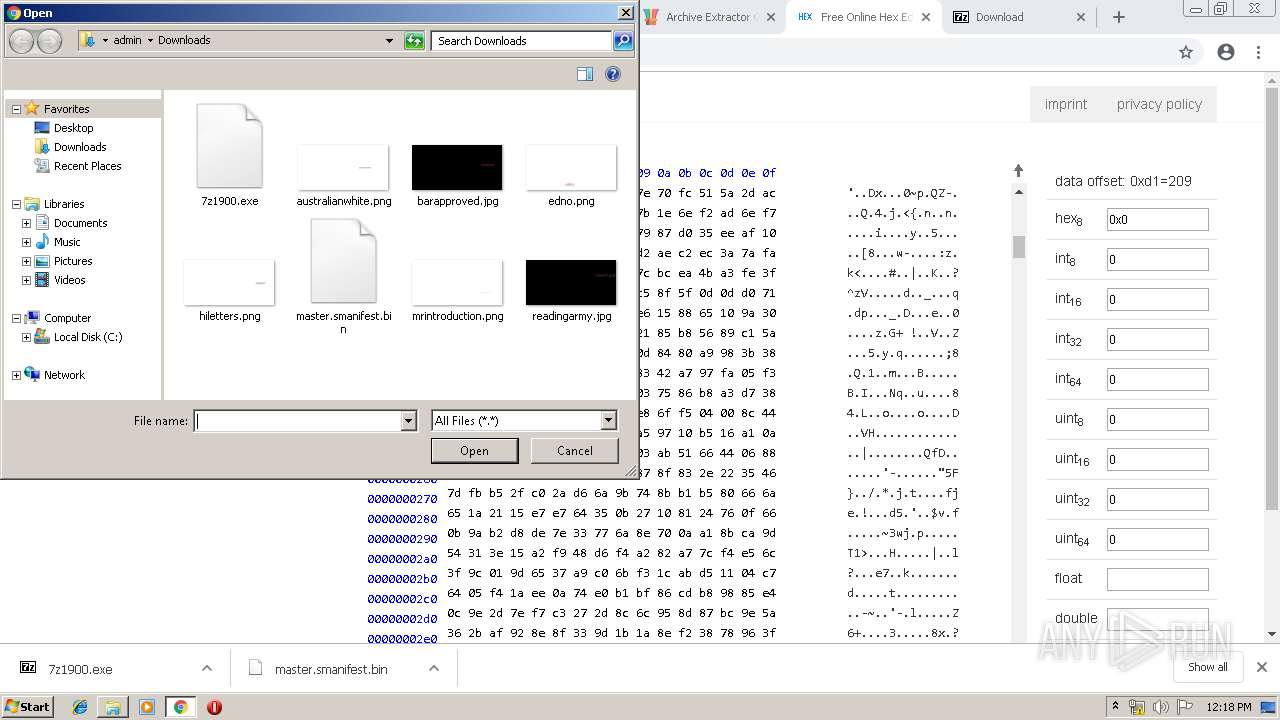
- 7z1900.exe (PID: 2180)
- 7z1900.exe (PID: 2052)
SUSPICIOUS
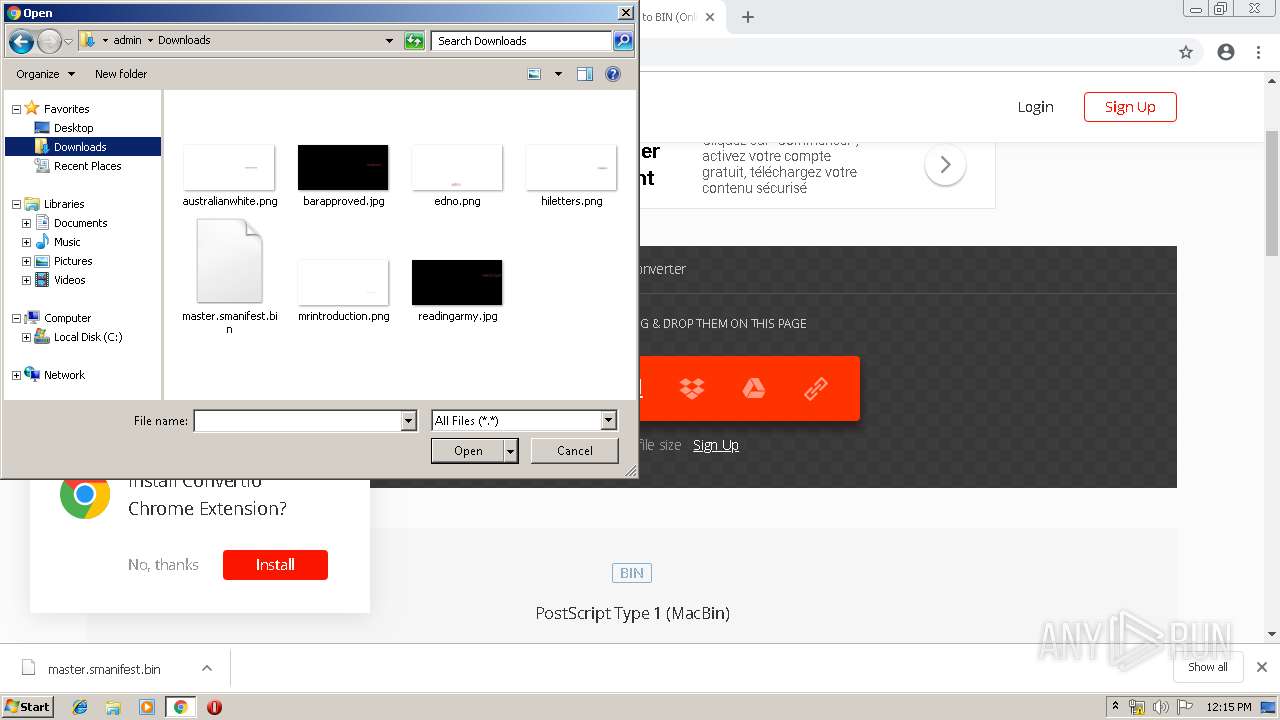
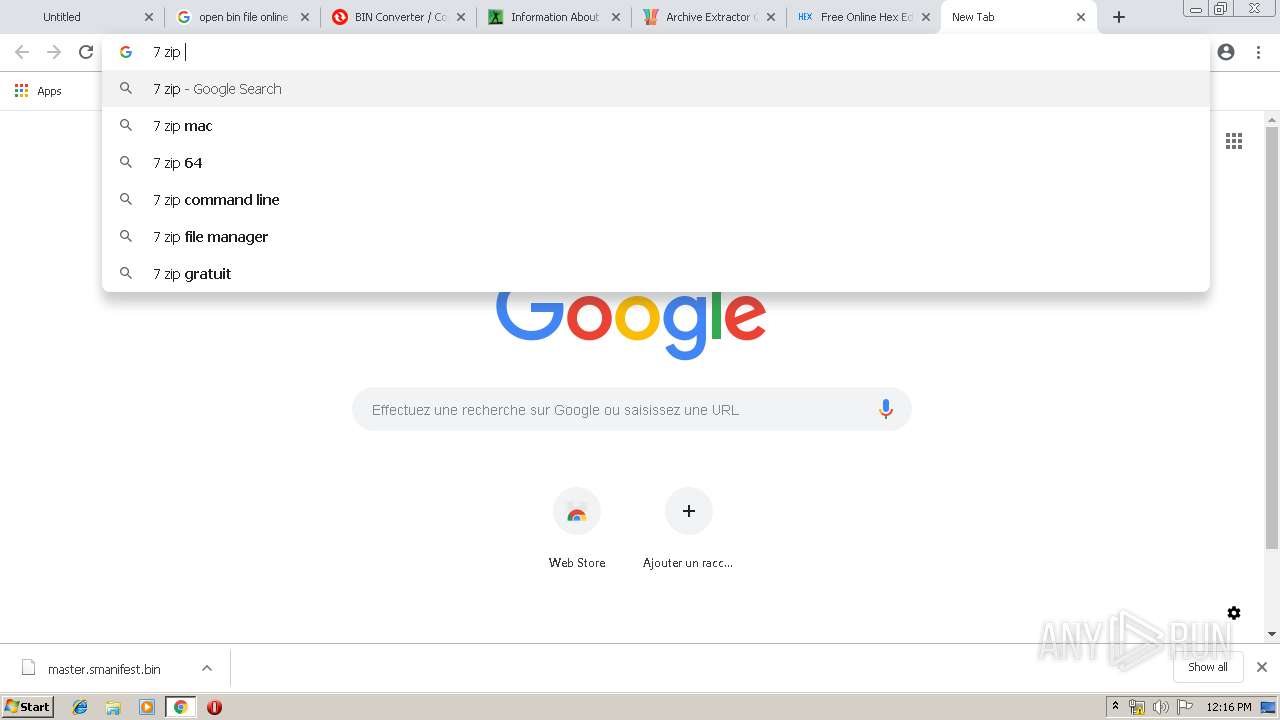
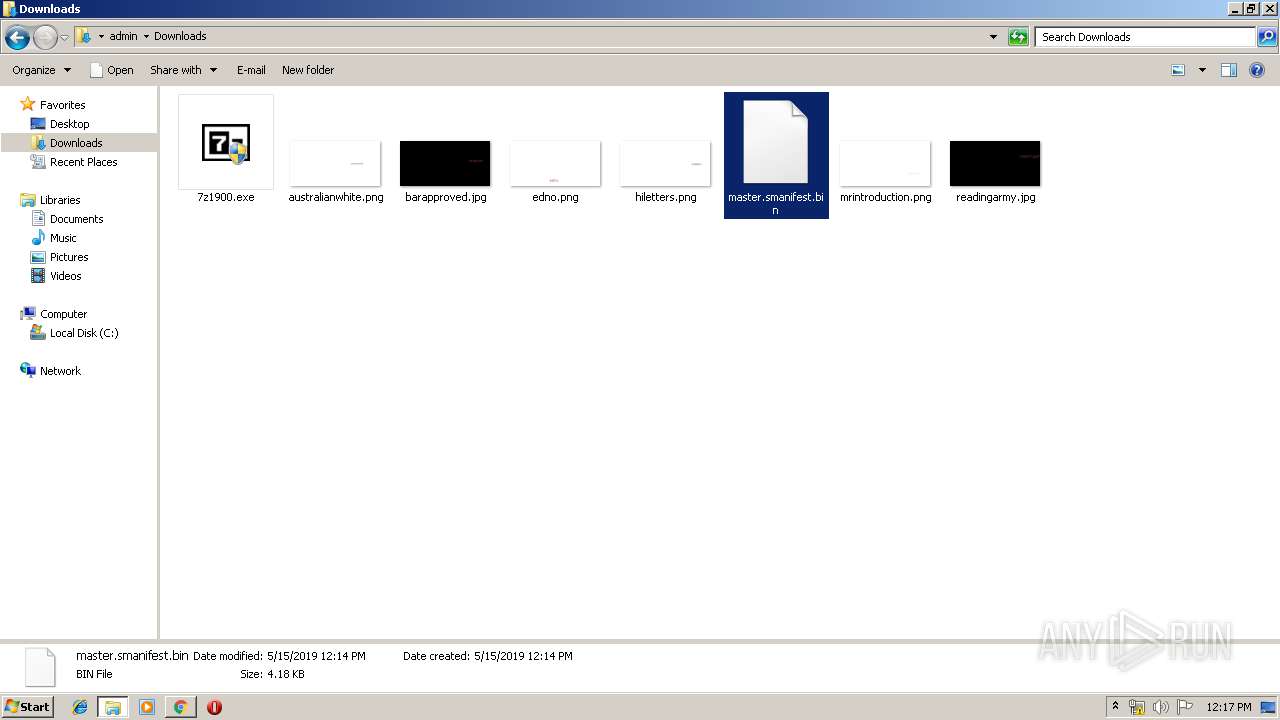
Creates files in the user directory
- explorer.exe (PID: 252)
- notepad++.exe (PID: 3596)
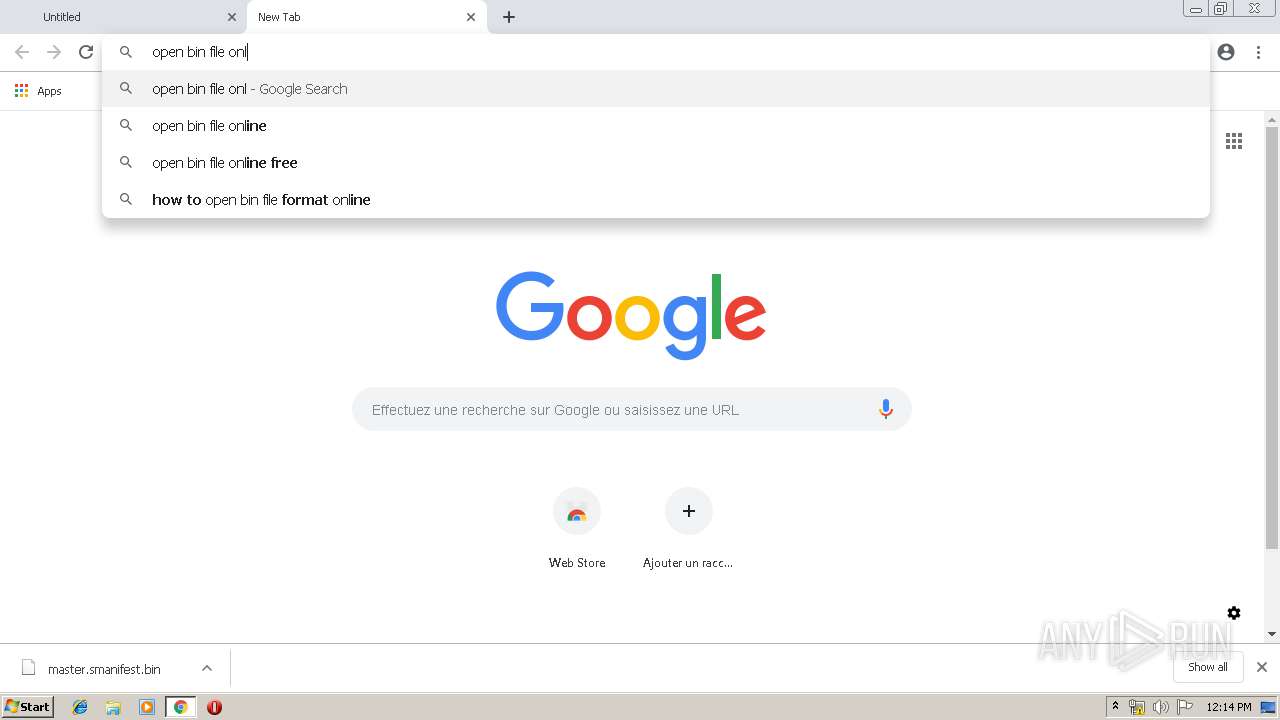
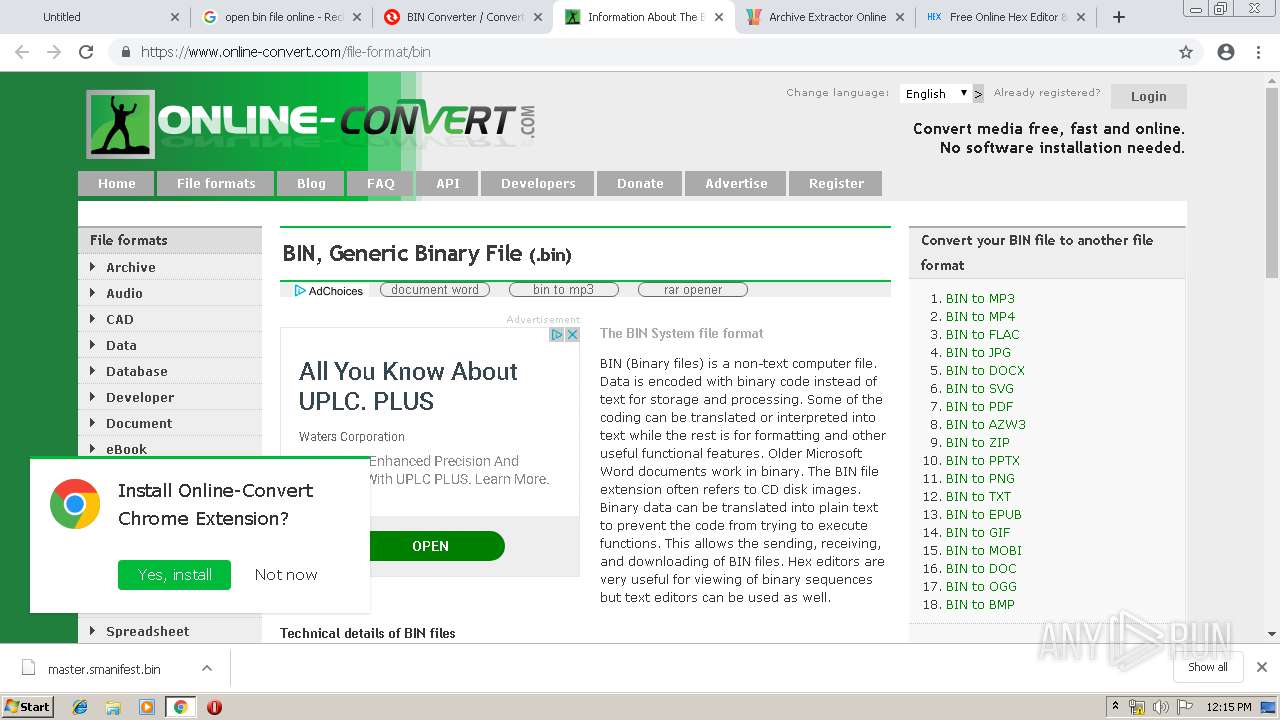
Executable content was dropped or overwritten
- chrome.exe (PID: 2992)
- 7z1900.exe (PID: 2180)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2992)
Reads Internet Cache Settings
- explorer.exe (PID: 252)
Creates COM task schedule object
- 7z1900.exe (PID: 2180)
Creates a software uninstall entry
- 7z1900.exe (PID: 2180)
Creates files in the program directory
- 7z1900.exe (PID: 2180)
INFO
Application launched itself
- chrome.exe (PID: 2992)
Reads Internet Cache Settings
- chrome.exe (PID: 2992)
Reads settings of System Certificates
- chrome.exe (PID: 2992)
Changes settings of System certificates
- chrome.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
51
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ctfmon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3431860298787652815 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3431860298787652815 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 848 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=900323055437454127 --mojo-platform-channel-handle=7508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5188678728085855193 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5188678728085855193 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11379873890864730353 --mojo-platform-channel-handle=8164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
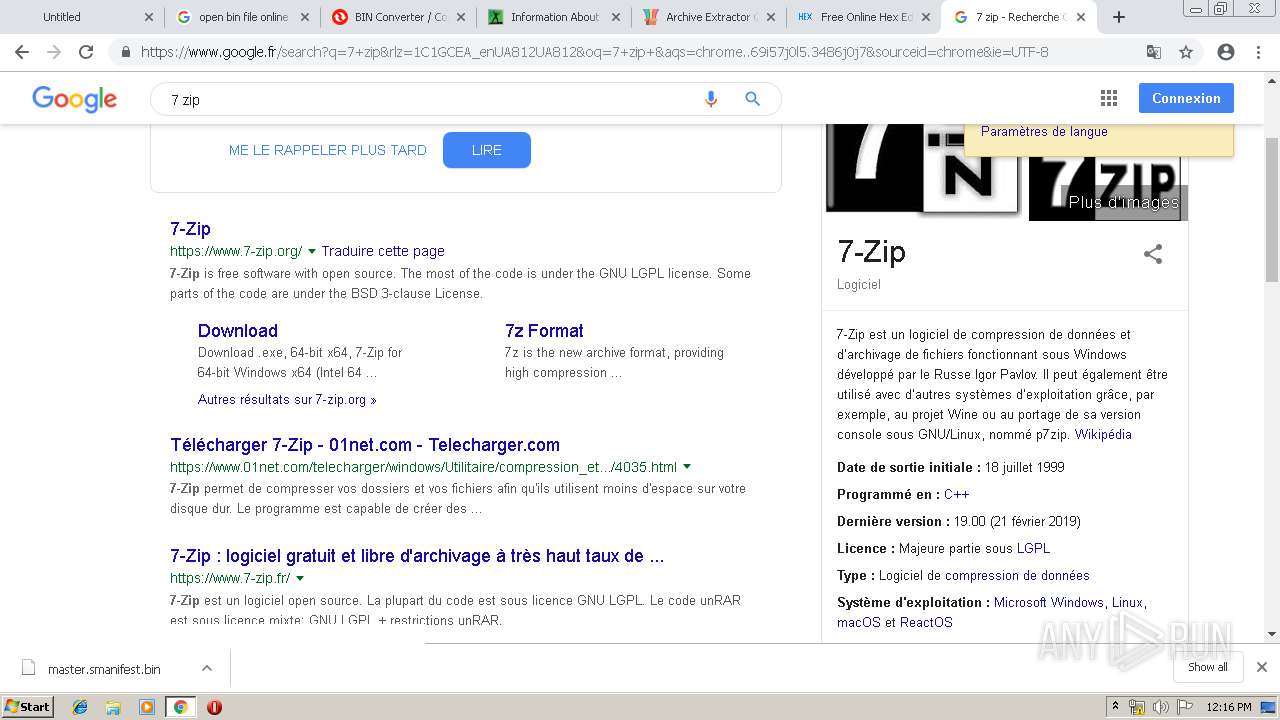
| 2052 | "C:\Users\admin\Downloads\7z1900.exe" | C:\Users\admin\Downloads\7z1900.exe | — | chrome.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Installer Exit code: 3221226540 Version: 19.00 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15513028437310704501 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15513028437310704501 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=995004208448385255 --mojo-platform-channel-handle=1088 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2180 | "C:\Users\admin\Downloads\7z1900.exe" | C:\Users\admin\Downloads\7z1900.exe | chrome.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
Total events
3 017
Read events
2 484
Write events
512
Delete events
21
Modification events
| (PID) Process: | (848) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | BD |
Value: BD00000000000000 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2992-13202392466886375 |
Value: 259 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
Executable files
10
Suspicious files
261
Text files
355
Unknown types
27
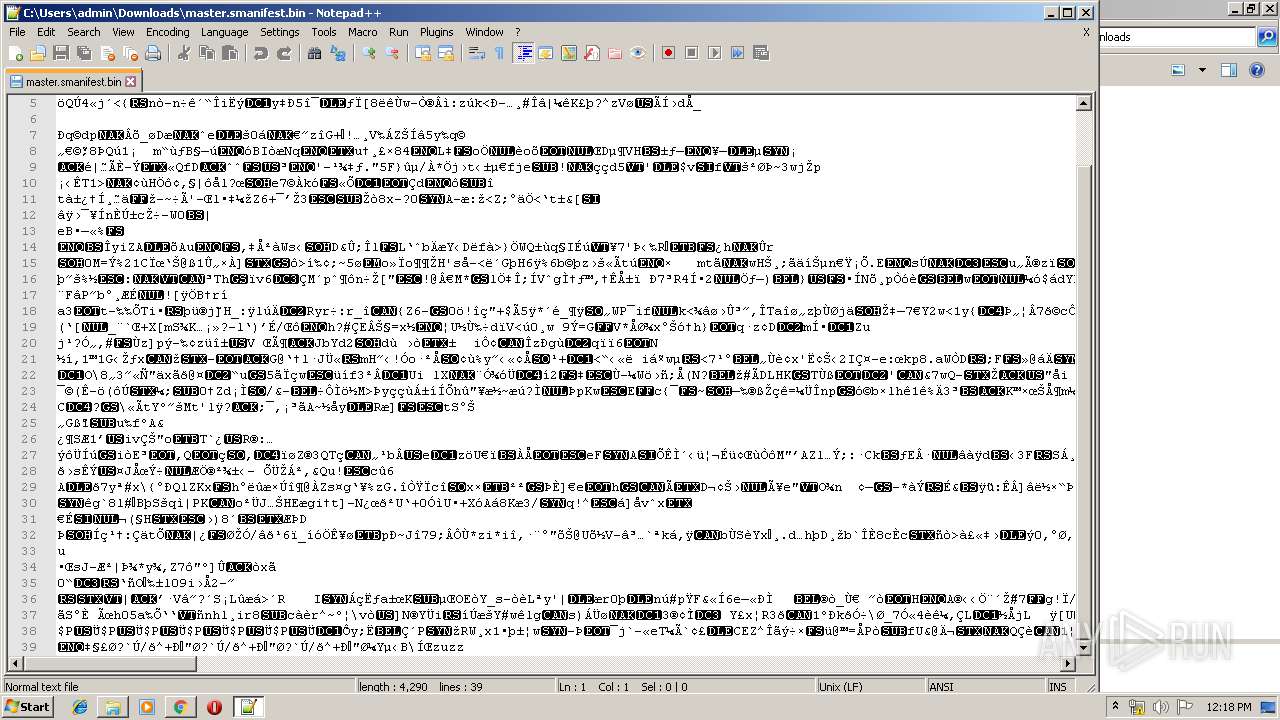
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bba3b1ae-e562-4241-8ad6-5251d14aeb71.tmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
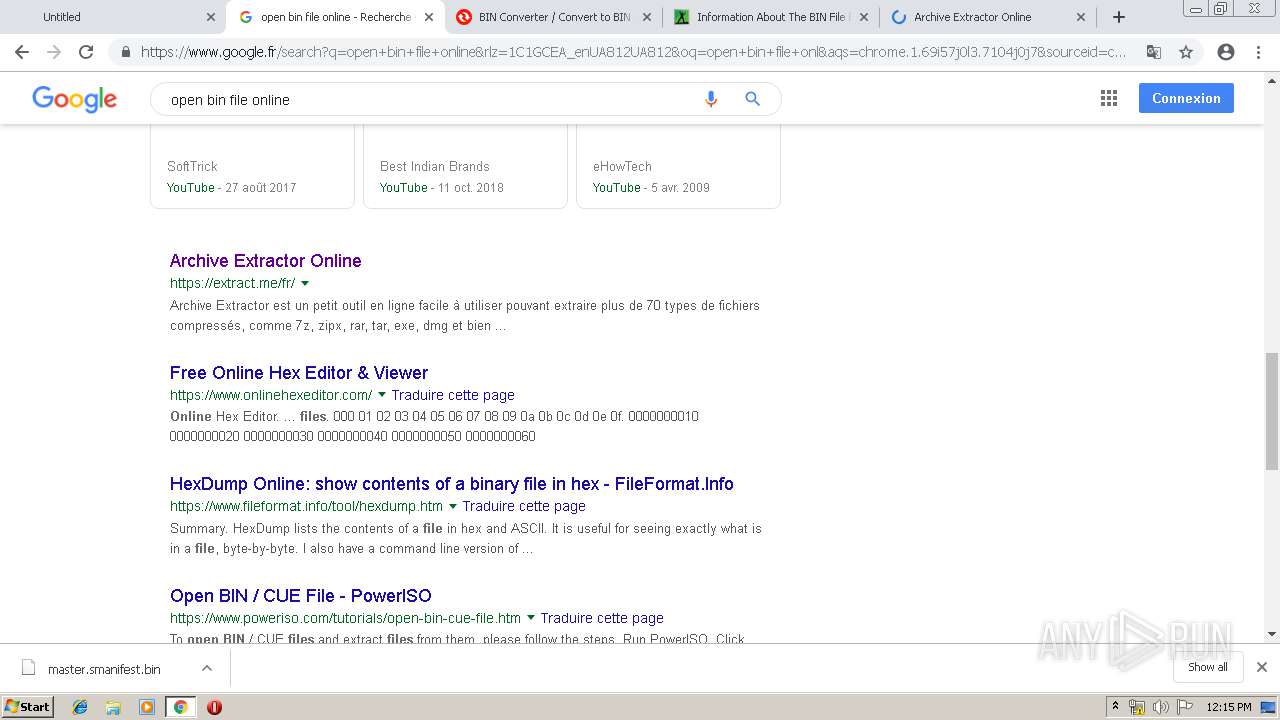
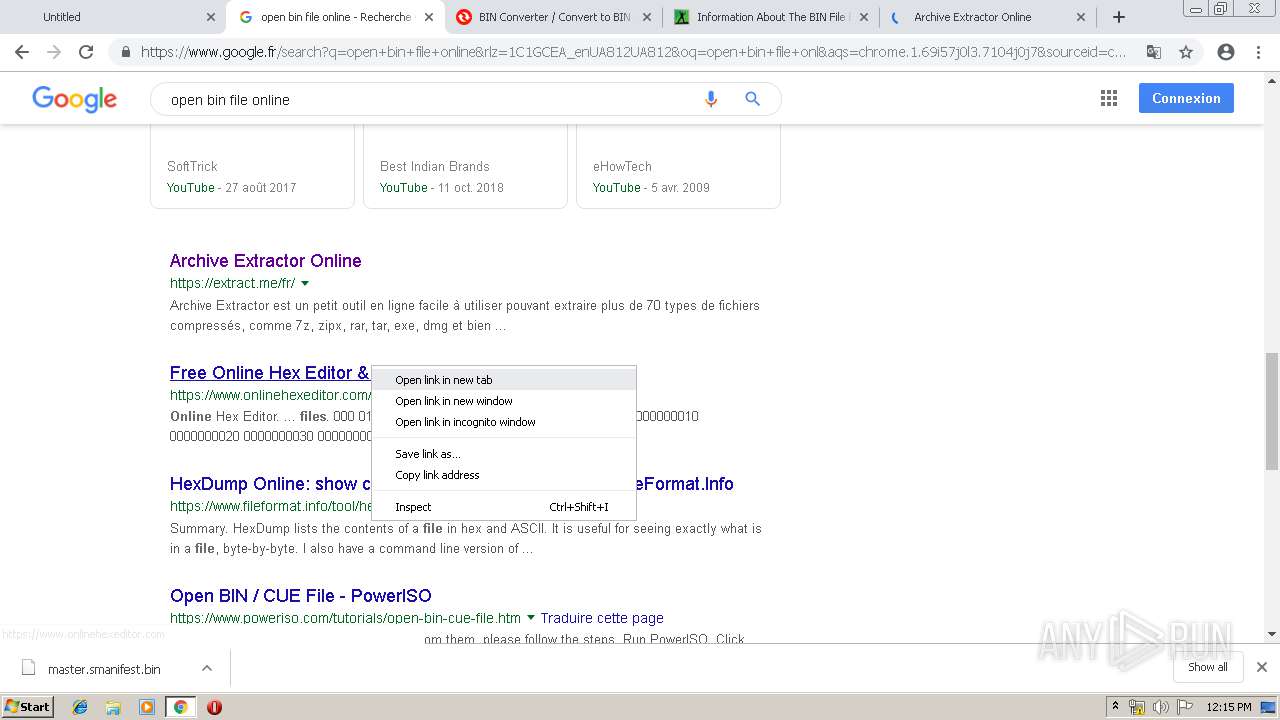
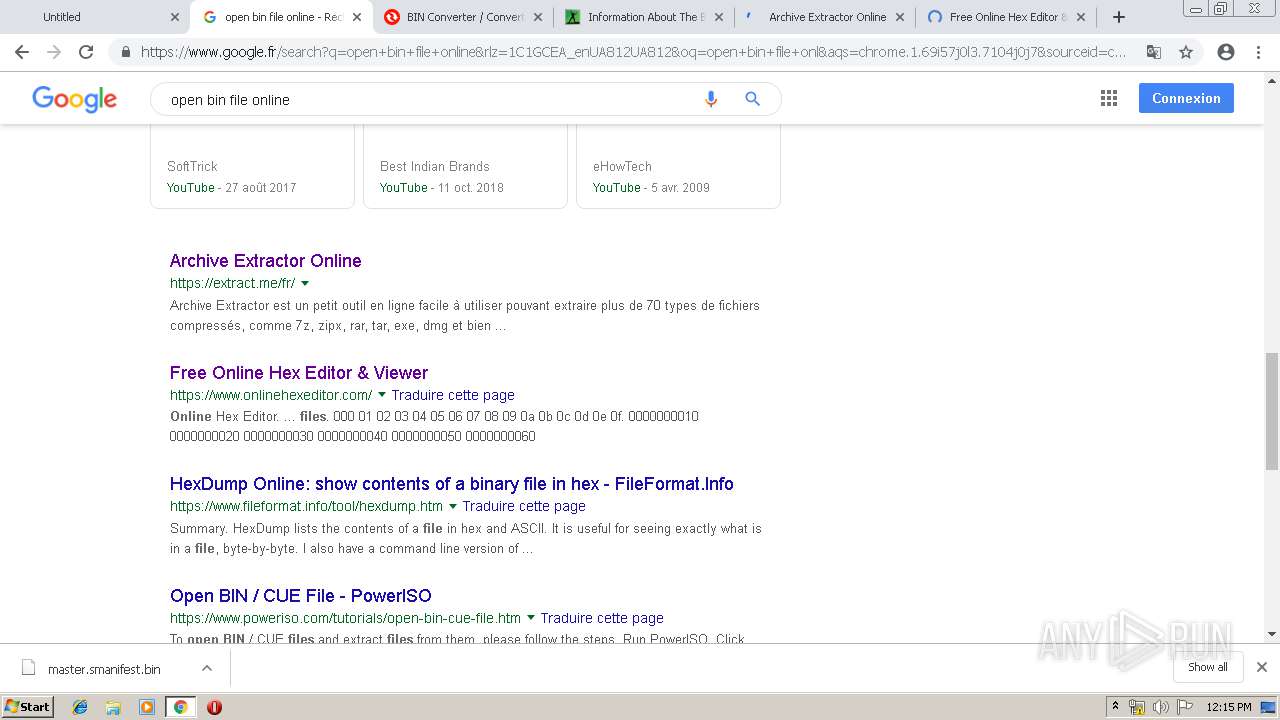
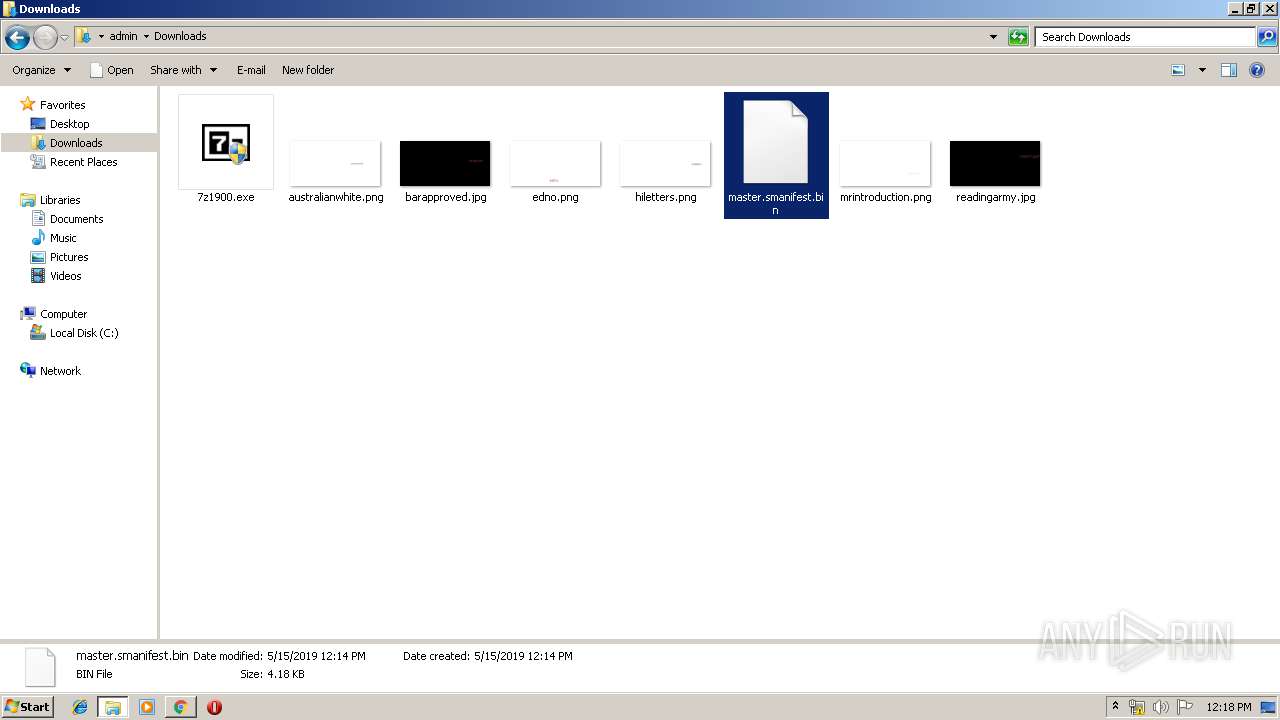
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
141
DNS requests
98
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2992 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2992 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2992 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
— | — | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
2992 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAU5fm3dSuY9dJCdoTinHgw%3D | US | der | 471 b | whitelisted |
2992 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
2992 | chrome.exe | GET | 200 | 52.216.109.141:80 | http://s3.amazonaws.com/contentpack/manifests/e0a816f3815189e3dd8664fcd43c93df/master.smanifest.bin | US | sp | 4.19 Kb | shared |
2992 | chrome.exe | GET | 200 | 52.222.146.213:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2992 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
2992 | chrome.exe | GET | 200 | 74.125.173.138:80 | http://r5---sn-4g5ednsy.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.119.8&mm=28&mn=sn-4g5ednsy&ms=nvh&mt=1557918987&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 172.217.23.142:443 | clients4.google.com | Google Inc. | US | whitelisted |
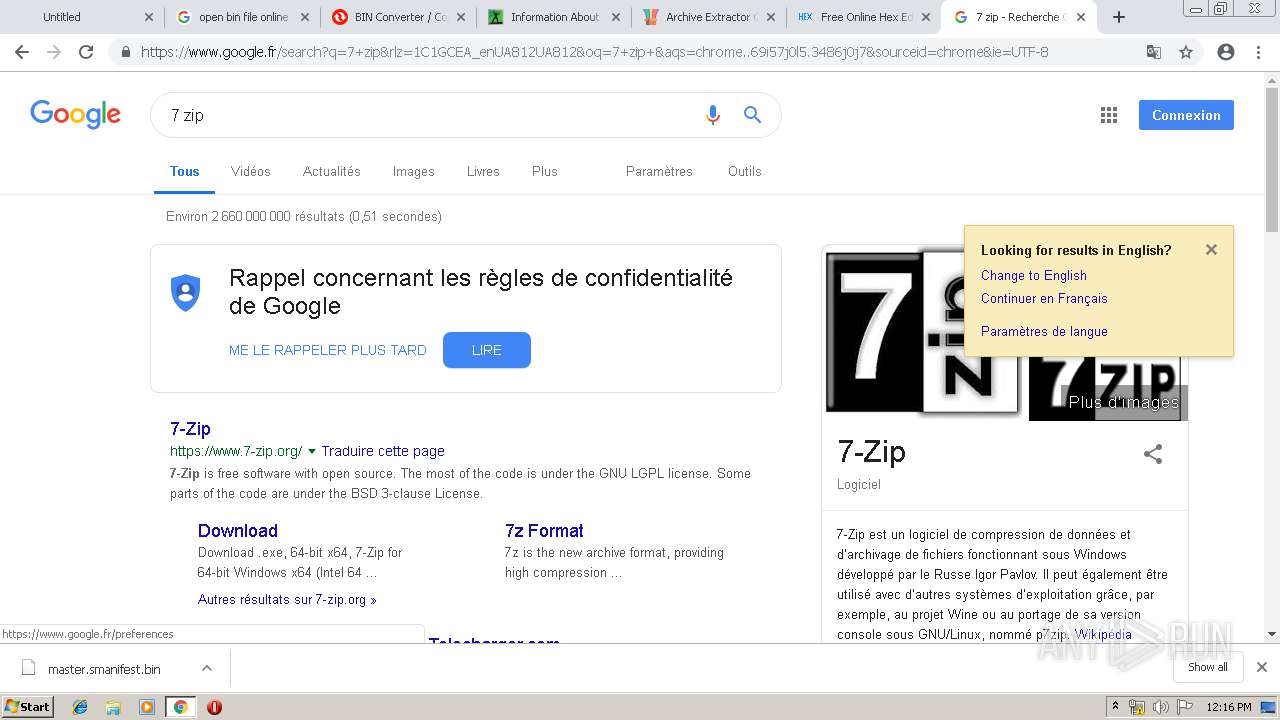
2992 | chrome.exe | 172.217.21.227:443 | www.google.fr | Google Inc. | US | whitelisted |
— | — | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 52.216.109.141:80 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
2992 | chrome.exe | 172.217.18.14:443 | consent.google.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 172.217.21.194:443 | adservice.google.fr | Google Inc. | US | whitelisted |
2992 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
s3.amazonaws.com |
| shared |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients4.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.fr |
| whitelisted |
clients1.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
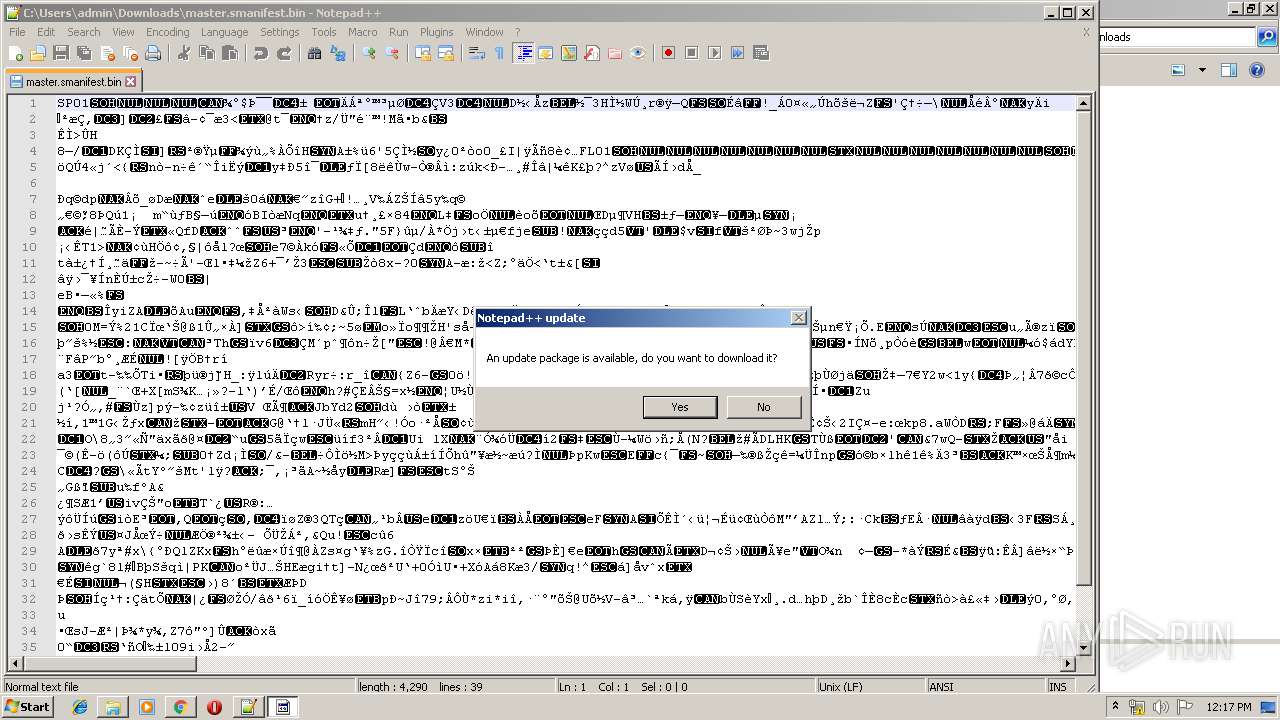
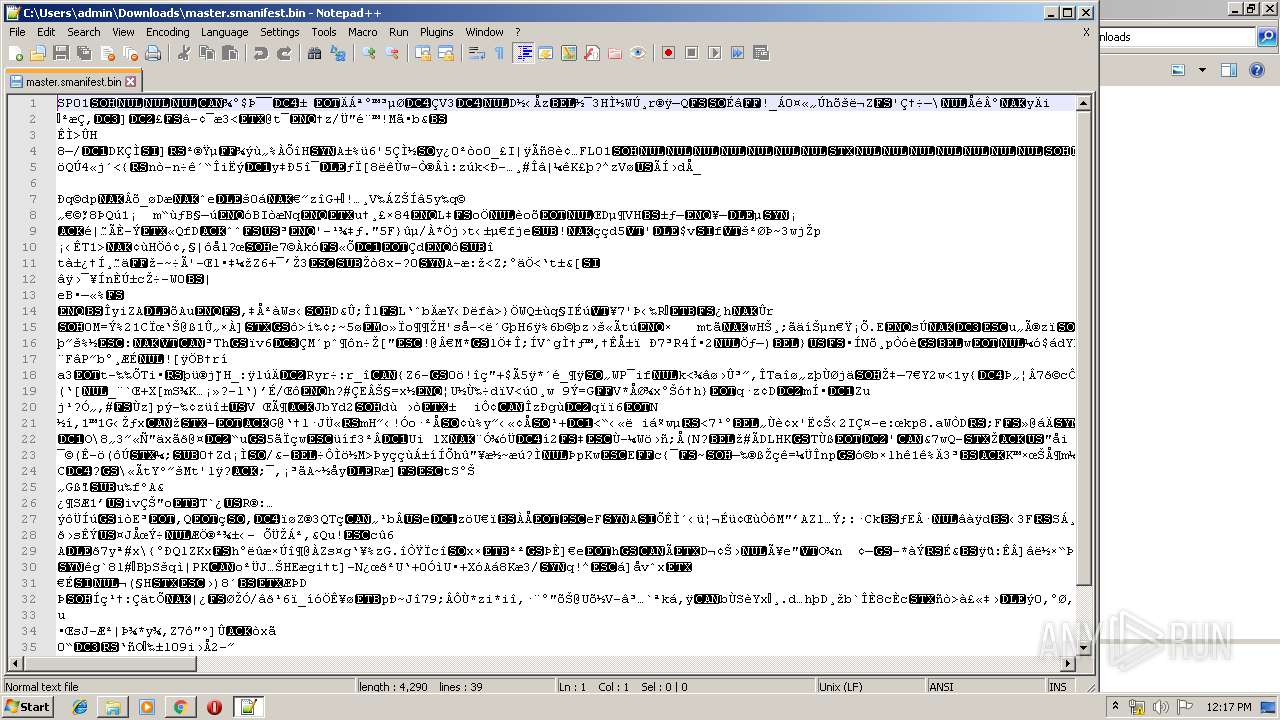
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|