| File name: | iCal-2019120.ics |
| Full analysis: | https://app.any.run/tasks/9d827e2c-9422-4961-8767-d3f1c943e04f |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 14:04:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/calendar |
| File info: | vCalendar calendar file |
| MD5: | F1997C34BA0818BDD5ED1B135BCB86C0 |
| SHA1: | F6D1635F99B7DE4891999689DCFD12921BEABE6D |
| SHA256: | 09E023C85A3BBBE89CDAE761BF726EA1293524061BDCD77103E4285AF9D0BA0B |
| SSDEEP: | 96:E4ofb3J9qpiH5Dg7anxkLgO5blYuLDUgMC04ZzbtgVYn4q/NO8ahjeiwVDfLUx94:7Cb3J9LZgasAta9XmnnGn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- OUTLOOK.EXE (PID: 2940)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2940)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2940)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ics/vcs | | | iCalendar - vCalendar (100) |
|---|
EXIF
VCard
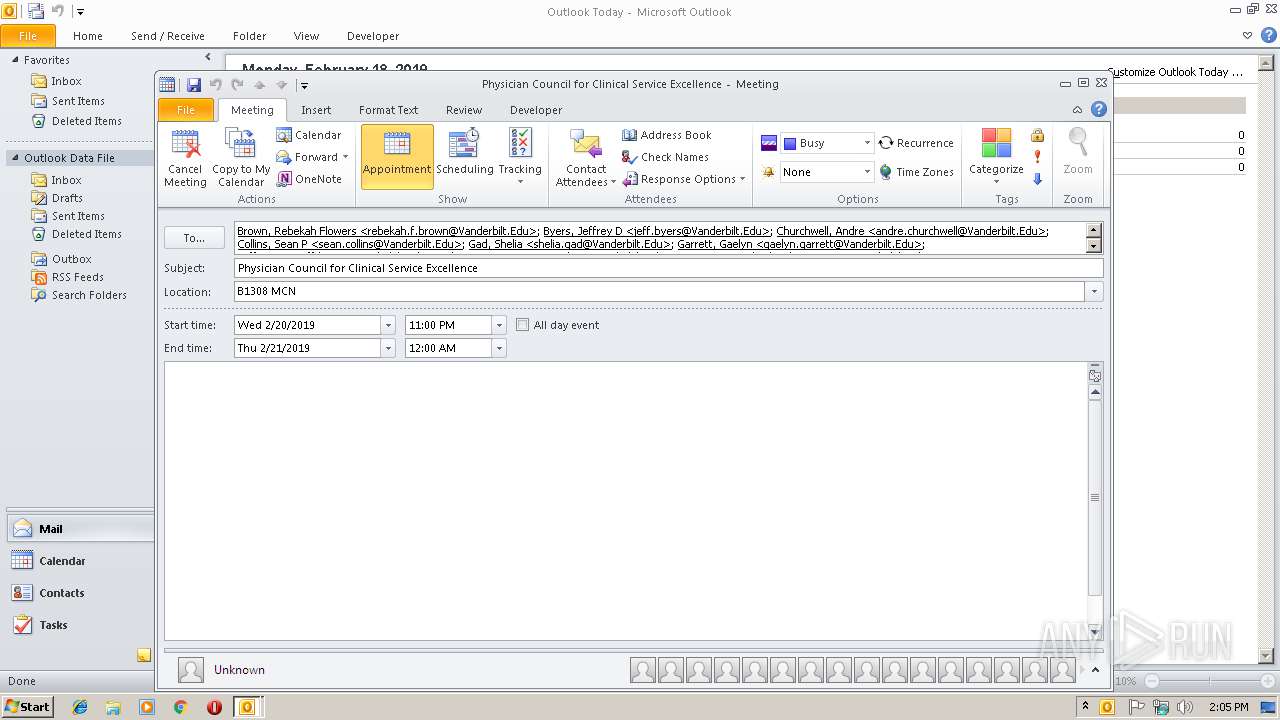
| CalendarScale: | GREGORIAN |
|---|---|
| Software: | -//Apple Inc.//iOS 12.1.2//EN |
| VCalendarVersion: | 2 |
| DateCreated: | 2019:02:17 23:28:13Z |
| DateTimeEnd: | 2019:02:20 18:00:00 |
| DateTimeEndTimezoneID: | America/Chicago |
| DateTimeStamp: | 2019:02:17 23:28:17Z |
| DateTimeStart: | 2019:02:20 17:00:00 |
| DateTimeStartTimezoneID: | America/Chicago |
| ModifyDate: | 2019:02:17 23:28:13Z |
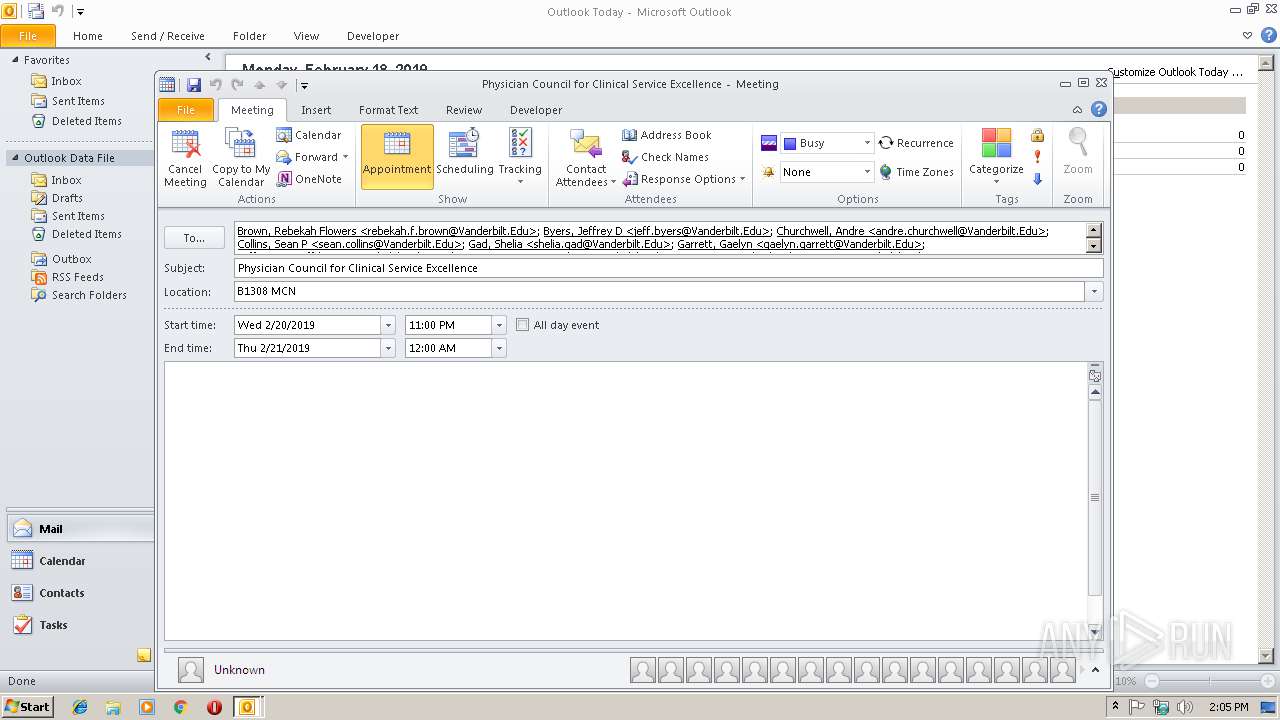
| Location: | B1308 MCN |
| Organizer: | /aNDM3NjQxNjIxNDM3NjQxNtrf2OzYkUvf0v7F5dBVh14Qcq0OE_ioClcyOZtHe66k/principal/ |
| SequenceNumber: | - |
| Summary: | Physician Council for Clinical Service Excellence |
| URL: | - |
| Attendee: | mailto:daniel.h.biller@Vanderbilt.Edu |
| Icloud-peruser-uid: | 438341468 |
| Begin: | X-ICLOUD-PERINSTANCE |
| TimeTransparency: | OPAQUE |
| Action: | DISPLAY |
| Description: | Reminder |
| Trigger: | -PT15M |
| UID: | C5BF60C9-83C7-48B4-B671-70325C0CBD3B |
| Wr-alarmuid: | C5BF60C9-83C7-48B4-B671-70325C0CBD3B |
| End: | X-ICLOUD-PERUSER |
Total processes
32
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2940 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /ical "C:\Users\admin\AppData\Local\Temp\iCal-2019120.ics" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
1 498
Read events
1 040
Write events
422
Delete events
36
Modification events
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | xf/ |
Value: 78662F007C0B0000010000000000000000000000 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 7C0B0000DA75BFF192C7D40100000000 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219915360 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2940) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1313996821 | |||
Executable files
0
Suspicious files
0
Text files
26
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR66E8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF0B3D9A4D258A6B56.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF9DE9EB93744BB3AA.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\mso6A54.tmp | html | |
MD5:A8934077843220A8E31367C7BBE15E6C | SHA256:A2DB0201D36F07F3F99D1ADF8B8EAFB9CF9BB803D024FCC9327B77AF56346861 | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_5D05CDBC1778574F8B2BA70DD43CE7D8.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{26671A2D-CD50-4DCF-A4D9-51C1448CAF46}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\gap[1] | image | |
MD5:96C4C871750D7CA05DFA18CE6A85D369 | SHA256:74441313BB1FB62500484443C4937E90D4E335351A4FCD12A9AC48448500E33E | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019021820190219\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2940 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_A50670C7C347C64EBD735F898E6A6EB7.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2940 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2940 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |