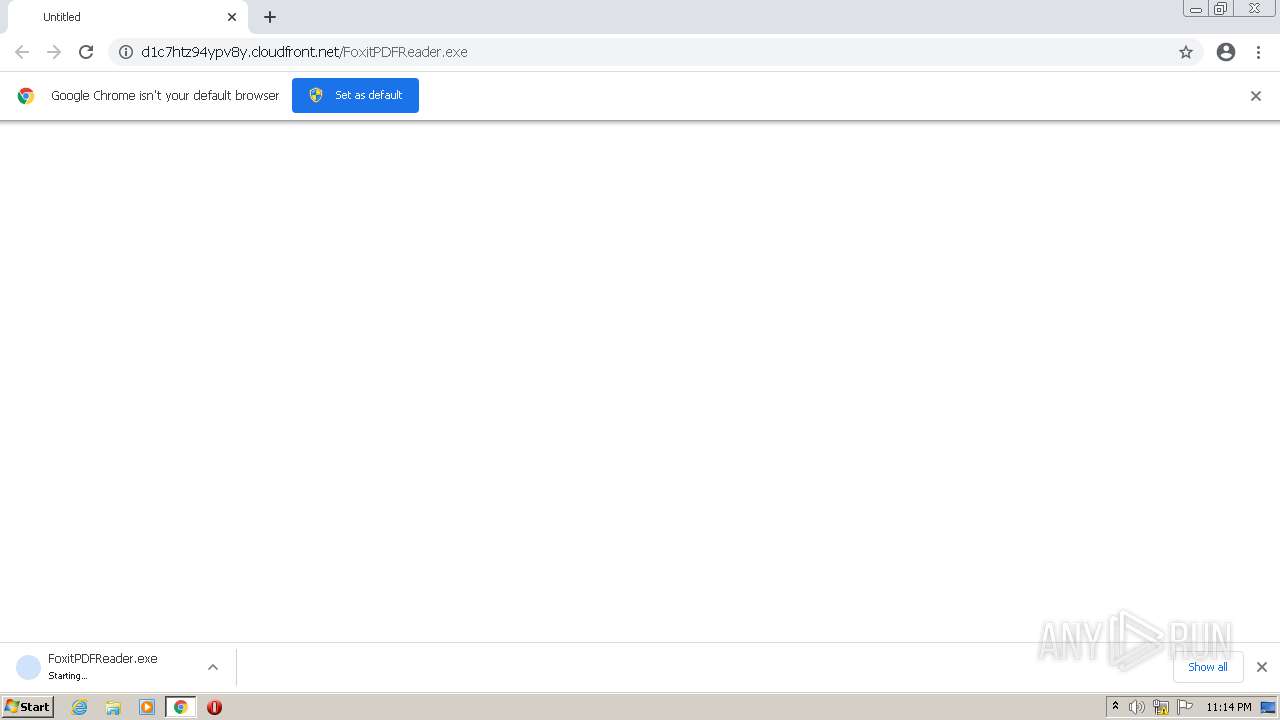
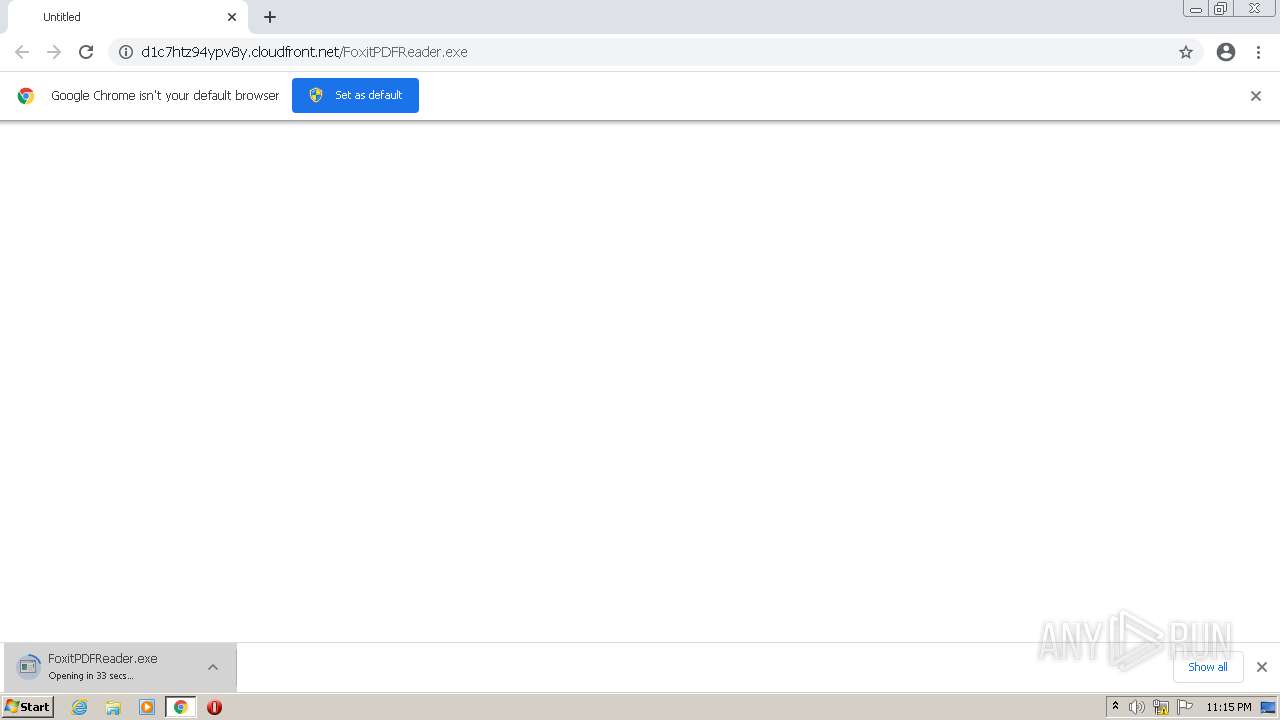
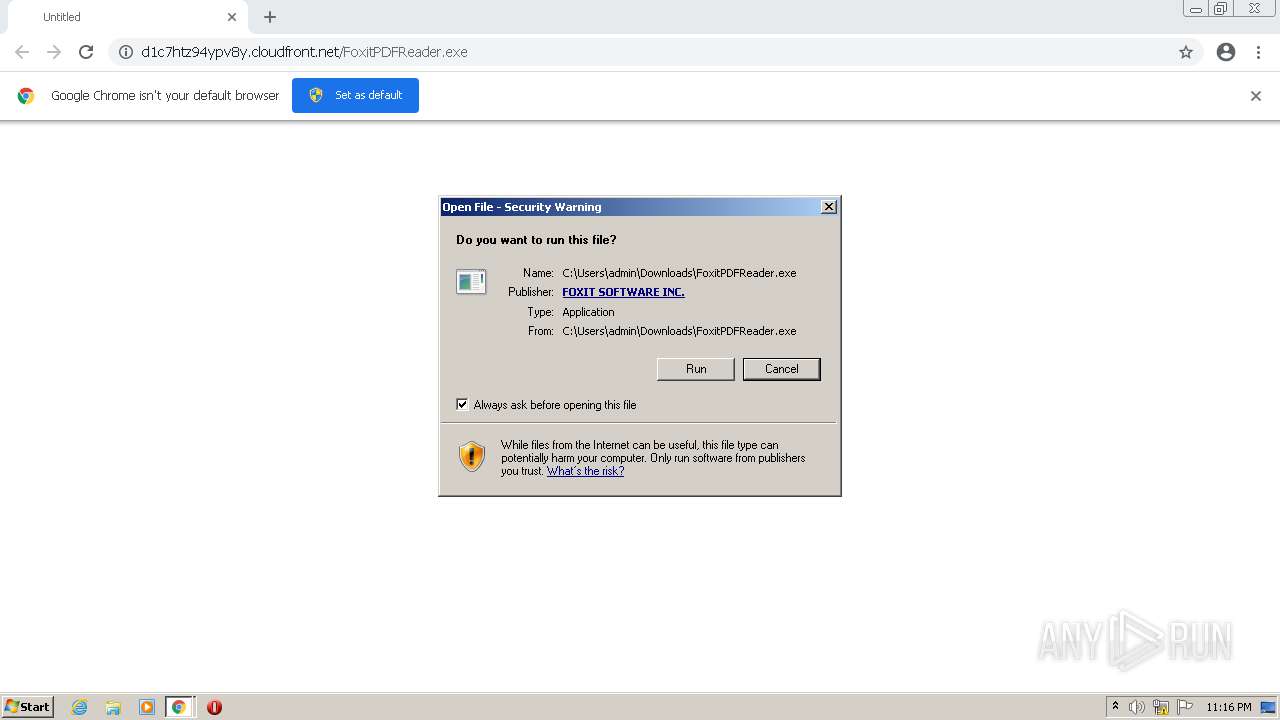
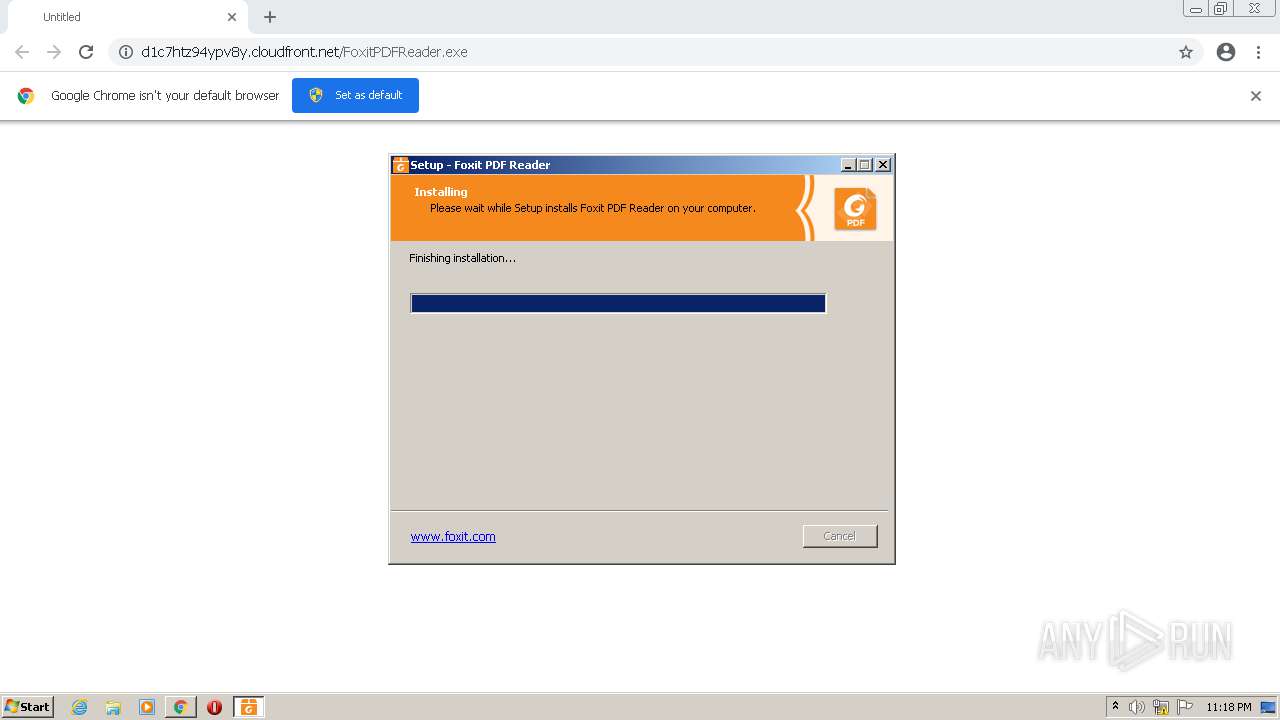
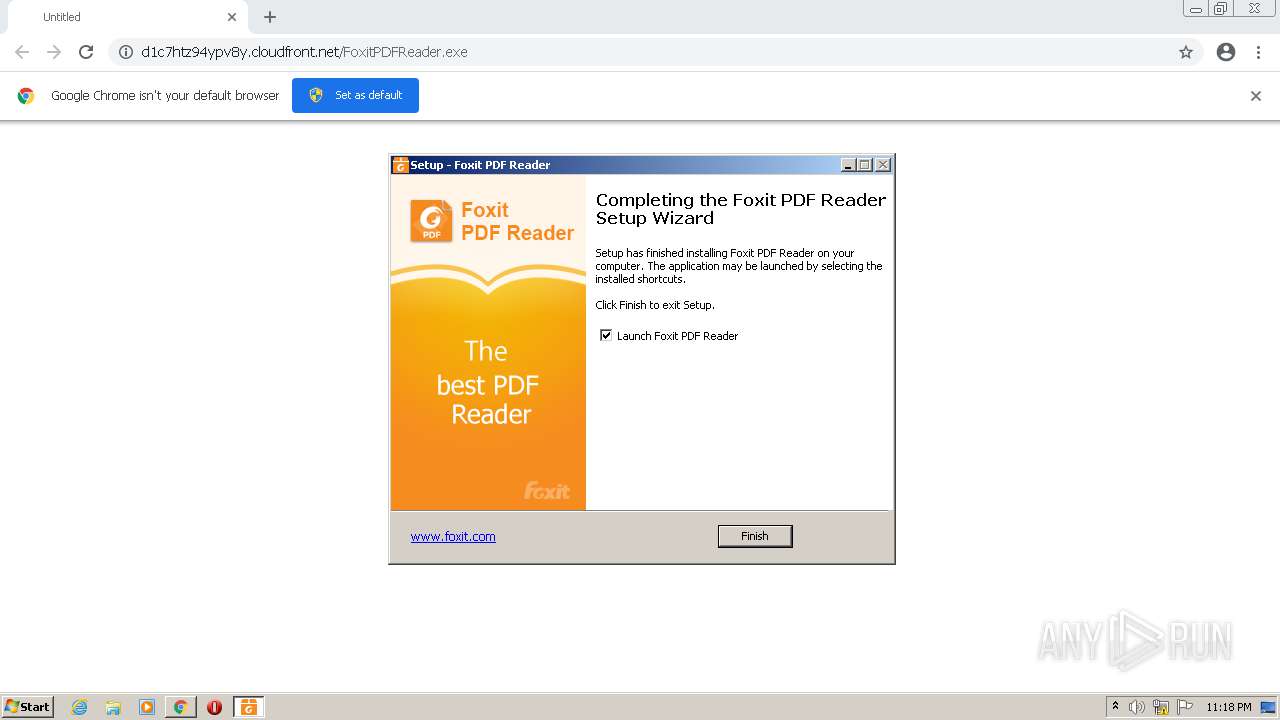
| URL: | https://d1c7htz94ypv8y.cloudfront.net/FoxitPDFReader.exe |
| Full analysis: | https://app.any.run/tasks/61d9624d-762b-4696-ac1d-a7e8e156b775 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2021, 22:14:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A818AFD197602F69B90D5D6D5C3D80FD |
| SHA1: | EAA0F394BA01985F8026EF1F577419654C01C380 |
| SHA256: | 09C31856956C00824CE886DBCA49B8F6BF3FBC4DD9FE6CA1DB1CC97E9D106CEE |
| SSDEEP: | 3:N8MdR70l/04KI3QX0C:2MJHK9C |
MALICIOUS
Application was dropped or rewritten from another process
- FoxitPDFReader.exe (PID: 1596)
- FoxitPDFReader.exe (PID: 2332)
- FoxitPreviewhost.exe (PID: 2296)
- FoxitPDFReaderUpdateService.exe (PID: 1844)
- FoxitPDFReaderUpdateService.exe (PID: 2952)
- FoxitUpdater.exe (PID: 2264)
Drops executable file immediately after starts
- FoxitPDFReader.exe (PID: 1596)
- FoxitPDFReader.exe (PID: 2332)
- chrome.exe (PID: 2984)
Registers / Runs the DLL via REGSVR32.EXE
- FoxitPDFReader.tmp (PID: 2736)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 1532)
- regsvr32.exe (PID: 4056)
- regsvr32.exe (PID: 1588)
- FoxitPDFReader.exe (PID: 3760)
- FoxitPDFReader.exe (PID: 1204)
- FoxitPDFReader.exe (PID: 3812)
- FoxitUpdater.exe (PID: 2264)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3448)
- FoxitPDFReader.exe (PID: 1596)
- FoxitPDFReader.exe (PID: 2332)
- chrome.exe (PID: 2984)
- FoxitPDFReader.tmp (PID: 2736)
Reads the computer name
- FoxitPDFReader.tmp (PID: 588)
- FoxitPDFReader.tmp (PID: 2736)
- FoxitPDFReader.exe (PID: 3812)
- FoxitPDFReader.exe (PID: 3760)
- FoxitPDFReader.exe (PID: 1204)
- FoxitPDFReaderUpdateService.exe (PID: 1844)
- FoxitPDFReaderUpdateService.exe (PID: 2952)
- FoxitUpdater.exe (PID: 2264)
- CountInstallation.exe (PID: 3656)
- Foxit_PhantomPDF_Setup.exe (PID: 2624)
Checks supported languages
- FoxitPDFReader.tmp (PID: 2736)
- FoxitPDFReader.exe (PID: 1596)
- FoxitPDFReader.tmp (PID: 588)
- FoxitPDFReader.exe (PID: 2332)
- FoxitPDFReader.exe (PID: 3760)
- FoxitPDFReader.exe (PID: 1204)
- FoxitPDFReader.exe (PID: 3812)
- FoxitPDFReaderUpdateService.exe (PID: 2952)
- FoxitUpdater.exe (PID: 2264)
- FoxitPDFReaderUpdateService.exe (PID: 1844)
- CountInstallation.exe (PID: 3656)
- Foxit_PhantomPDF_Setup.exe (PID: 2624)
- FoxitPreviewhost.exe (PID: 2296)
Reads Windows owner or organization settings
- FoxitPDFReader.tmp (PID: 2736)
Reads the Windows organization settings
- FoxitPDFReader.tmp (PID: 2736)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2984)
- FoxitPDFReader.tmp (PID: 2736)
Creates a directory in Program Files
- FoxitPDFReader.tmp (PID: 2736)
Creates files in the user directory
- FoxitPDFReader.tmp (PID: 2736)
- FoxitPDFReader.exe (PID: 3760)
- FoxitUpdater.exe (PID: 2264)
- Foxit_PhantomPDF_Setup.exe (PID: 2624)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1532)
- regsvr32.exe (PID: 1588)
- regsvr32.exe (PID: 4056)
- FoxitPDFReader.exe (PID: 3760)
Drops a file with too old compile date
- FoxitPDFReader.tmp (PID: 2736)
Changes default file association
- FoxitPDFReader.tmp (PID: 2736)
- FoxitPDFReader.exe (PID: 3812)
Drops a file with a compile date too recent
- FoxitPDFReader.tmp (PID: 2736)
Changes IE settings (feature browser emulation)
- FoxitPDFReader.tmp (PID: 2736)
Executed as Windows Service
- FoxitPDFReaderUpdateService.exe (PID: 2952)
Creates files in the program directory
- FoxitUpdater.exe (PID: 2264)
INFO
Checks supported languages
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 1820)
- chrome.exe (PID: 980)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 1232)
- chrome.exe (PID: 1020)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 688)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 2560)
- regsvr32.exe (PID: 1532)
- regsvr32.exe (PID: 4056)
- regsvr32.exe (PID: 1588)
- chrome.exe (PID: 2036)
- chrome.exe (PID: 1684)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 1860)
Reads the computer name
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 980)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 1232)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 2040)
- regsvr32.exe (PID: 1532)
Reads the hosts file
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2664)
Application launched itself
- chrome.exe (PID: 3448)
Reads settings of System Certificates
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3448)
- FoxitUpdater.exe (PID: 2264)
- CountInstallation.exe (PID: 3656)
- Foxit_PhantomPDF_Setup.exe (PID: 2624)
Checks Windows Trust Settings
- chrome.exe (PID: 3448)
- CountInstallation.exe (PID: 3656)
- Foxit_PhantomPDF_Setup.exe (PID: 2624)
Reads the date of Windows installation
- chrome.exe (PID: 2508)
Application was dropped or rewritten from another process
- FoxitPDFReader.tmp (PID: 588)
- FoxitPDFReader.tmp (PID: 2736)
- CountInstallation.exe (PID: 3656)
- Foxit_PhantomPDF_Setup.exe (PID: 2624)
Loads dropped or rewritten executable
- FoxitPDFReader.tmp (PID: 2736)
Creates files in the program directory
- FoxitPDFReader.tmp (PID: 2736)
Creates a software uninstall entry
- FoxitPDFReader.tmp (PID: 2736)
Dropped object may contain Bitcoin addresses
- FoxitPDFReader.tmp (PID: 2736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
46
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | "C:\Users\admin\AppData\Local\Temp\is-C7OAT.tmp\FoxitPDFReader.tmp" /SL5="$4015C,165014486,421376,C:\Users\admin\Downloads\FoxitPDFReader.exe" | C:\Users\admin\AppData\Local\Temp\is-C7OAT.tmp\FoxitPDFReader.tmp | — | FoxitPDFReader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,2443242465150822972,16946575011082428722,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,2443242465150822972,16946575011082428722,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2443242465150822972,16946575011082428722,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Foxit Software\Foxit PDF Reader\FoxitPDFReader.exe" /FirstRun | C:\Program Files\Foxit Software\Foxit PDF Reader\FoxitPDFReader.exe | — | FoxitPDFReader.tmp | |||||||||||
User: admin Company: Foxit Software Inc. Integrity Level: HIGH Description: Foxit PDF Reader 11.1 Exit code: 0 Version: 11.1.0.52543 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,2443242465150822972,16946575011082428722,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1340 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1532 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\Foxit Software\Foxit PDF Reader\plugins\FoxitPDFReaderBrowserAx.dll" | C:\Windows\system32\regsvr32.exe | — | FoxitPDFReader.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,2443242465150822972,16946575011082428722,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2912 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1588 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\Foxit Software\Foxit PDF Reader\Shell Extensions\FoxitPrevHndlr.dll" | C:\Windows\system32\regsvr32.exe | — | FoxitPDFReader.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | "C:\Users\admin\Downloads\FoxitPDFReader.exe" | C:\Users\admin\Downloads\FoxitPDFReader.exe | chrome.exe | ||||||||||||
User: admin Company: Foxit Software Inc. Integrity Level: MEDIUM Description: Foxit PDF Reader Setup Exit code: 0 Version: 11.1.0.52543 Modules
| |||||||||||||||
Total events
27 231
Read events
26 495
Write events
696
Delete events
40
Modification events
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
584
Suspicious files
167
Text files
479
Unknown types
134
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6168ABBF-D78.pma | — | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1525c1.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF15269c.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1524f6.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9c7bc009-aaff-42b9-a574-635c48157872.tmp | text | |
MD5:— | SHA256:— | |||
| 1820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF152bbd.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
32
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 173.194.163.103:80 | http://r1---sn-5go7yne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODZmQUFYS2VOaGowdjdSeVBvWFBSTDIxdw/1.0.0.9_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=3e&mip=45.92.228.20&mm=28&mn=sn-5go7yne6&ms=nvh&mt=1634249295&mv=m&mvi=1&pl=24&rmhost=r3---sn-5go7yne6.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
— | — | HEAD | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODZmQUFYS2VOaGowdjdSeVBvWFBSTDIxdw/1.0.0.9_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
— | — | GET | 200 | 173.194.163.103:80 | http://r1---sn-5go7yne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODZmQUFYS2VOaGowdjdSeVBvWFBSTDIxdw/1.0.0.9_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=3e&mip=45.92.228.20&mm=28&mn=sn-5go7yne6&ms=nvh&mt=1634249295&mv=m&mvi=1&pl=24&rmhost=r3---sn-5go7yne6.gvt1.com&shardbypass=yes | US | crx | 2.81 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 596 b | whitelisted |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 596 b | whitelisted |
— | — | GET | 206 | 74.125.110.168:80 | http://r3---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=1M&mip=45.92.228.20&mm=28&mn=sn-5go7yner&ms=nvh&mt=1634249295&mv=m&mvi=3&pl=24&rmhost=r5---sn-5go7yner.gvt1.com&shardbypass=yes&smhost=r5---sn-5go7yne6.gvt1.com | US | binary | 9.48 Kb | whitelisted |
— | — | GET | 206 | 74.125.110.168:80 | http://r3---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=1M&mip=45.92.228.20&mm=28&mn=sn-5go7yner&ms=nvh&mt=1634249295&mv=m&mvi=3&pl=24&rmhost=r5---sn-5go7yner.gvt1.com&shardbypass=yes&smhost=r5---sn-5go7yne6.gvt1.com | US | binary | 43.3 Kb | whitelisted |
— | — | HEAD | 200 | 74.125.110.168:80 | http://r3---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=1M&mip=45.92.228.20&mm=28&mn=sn-5go7yner&ms=nvh&mt=1634249295&mv=m&mvi=3&pl=24&rmhost=r5---sn-5go7yner.gvt1.com&shardbypass=yes&smhost=r5---sn-5go7yne6.gvt1.com | US | — | — | whitelisted |
— | — | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 596 b | whitelisted |
— | — | GET | 206 | 74.125.110.168:80 | http://r3---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=1M&mip=45.92.228.20&mm=28&mn=sn-5go7yner&ms=nvh&mt=1634249295&mv=m&mvi=3&pl=24&rmhost=r5---sn-5go7yner.gvt1.com&shardbypass=yes&smhost=r5---sn-5go7yne6.gvt1.com | US | binary | 7.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.250.184.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2664 | chrome.exe | 143.204.101.126:443 | d1c7htz94ypv8y.cloudfront.net | — | US | suspicious |
2664 | chrome.exe | 142.250.184.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2664 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
2664 | chrome.exe | 142.250.186.163:443 | update.googleapis.com | Google Inc. | US | whitelisted |
— | — | 173.194.150.183:80 | r1---sn-5goeen7d.gvt1.com | Google Inc. | US | whitelisted |
— | — | 74.125.110.168:80 | r3---sn-5go7yner.gvt1.com | Google Inc. | US | whitelisted |
2664 | chrome.exe | 142.250.186.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
2664 | chrome.exe | 142.250.181.238:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 173.194.150.185:80 | r3---sn-5goeen7d.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
d1c7htz94ypv8y.cloudfront.net |
| suspicious |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-5go7yne6.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
r3---sn-5go7yner.gvt1.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
FoxitUpdater.exe | StopRequest |