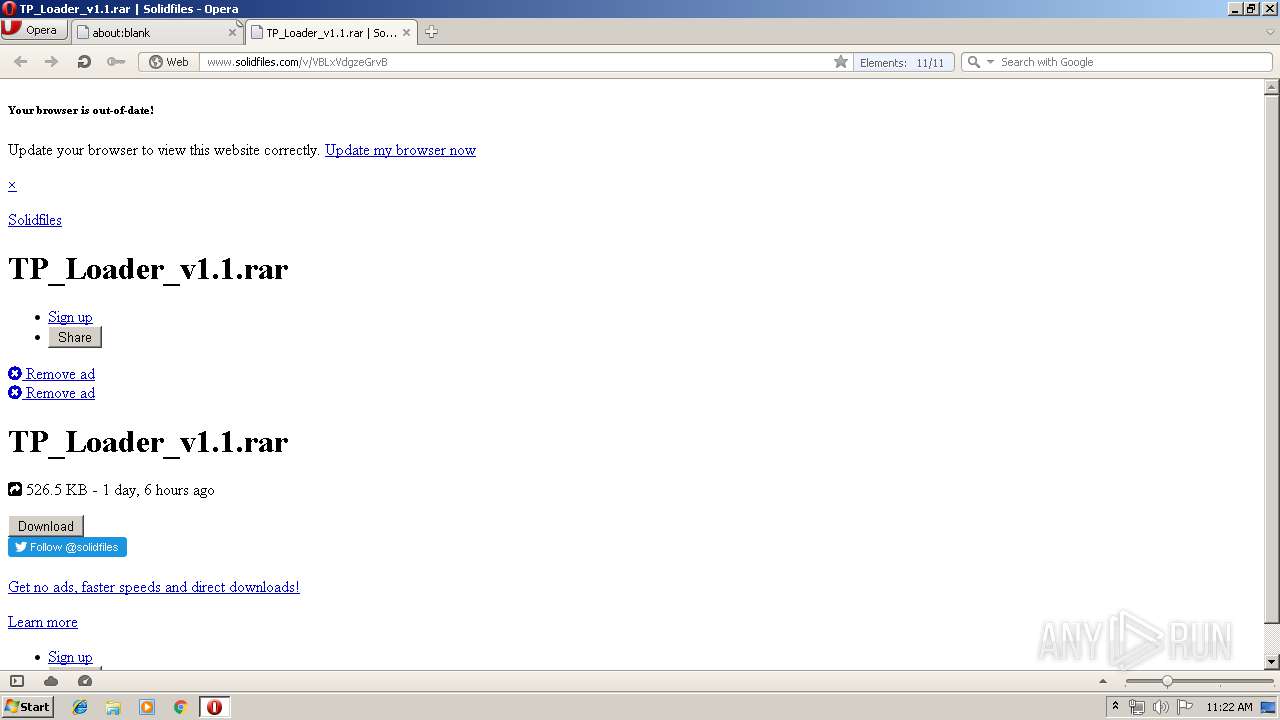
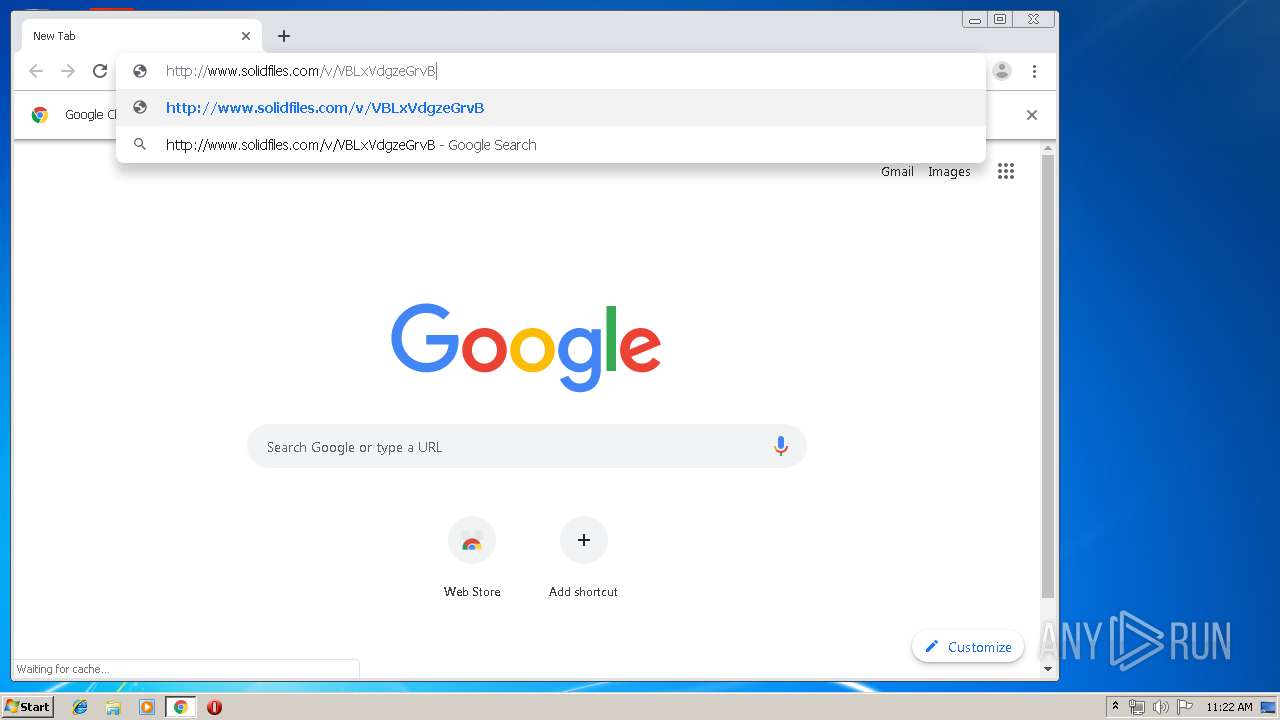
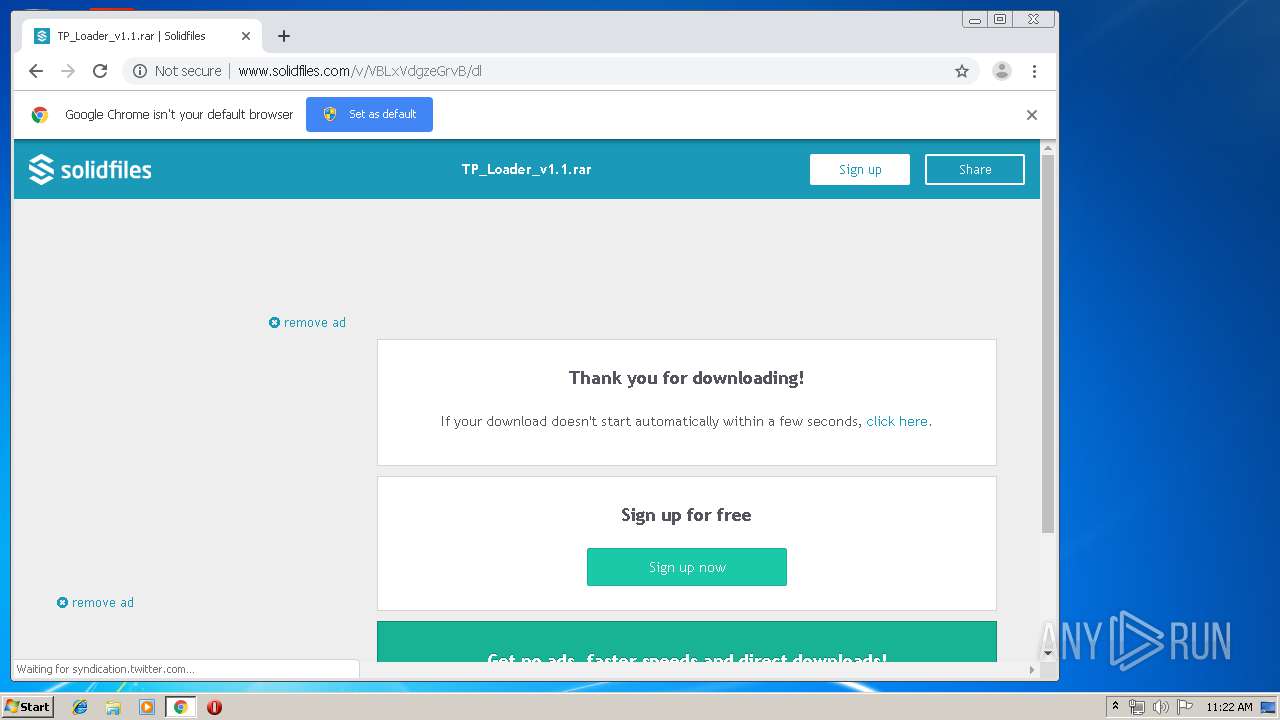
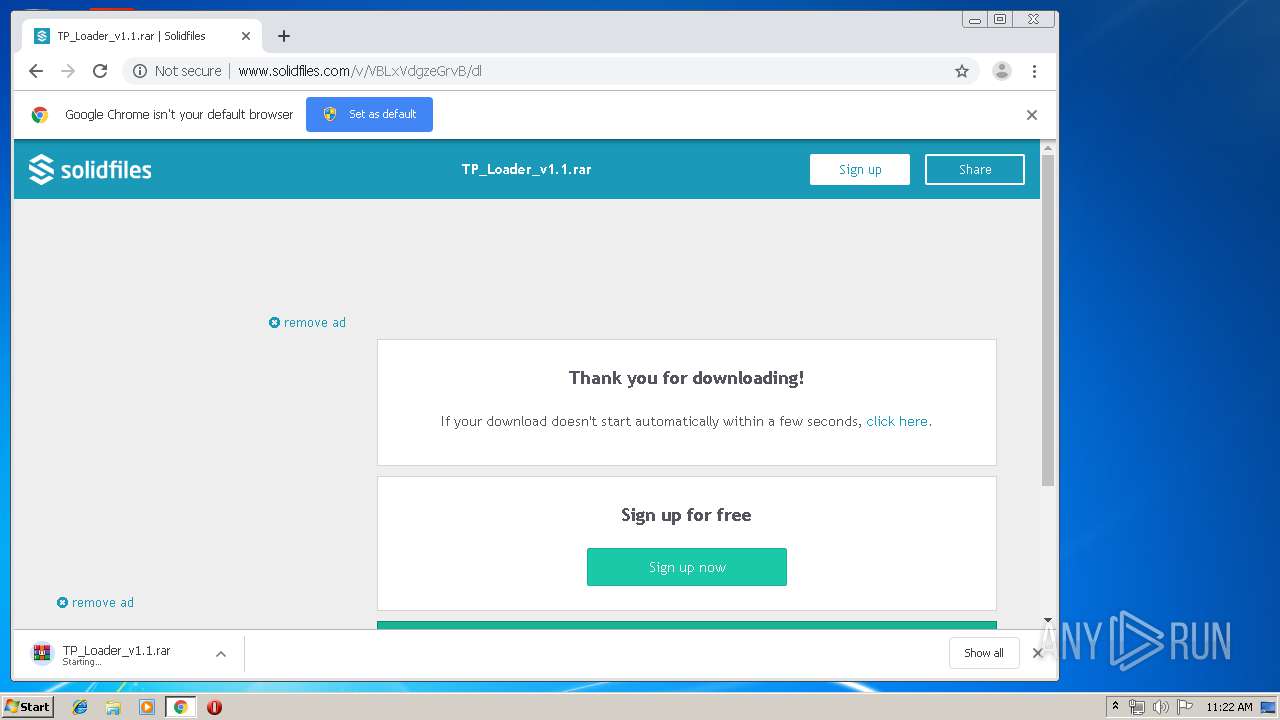
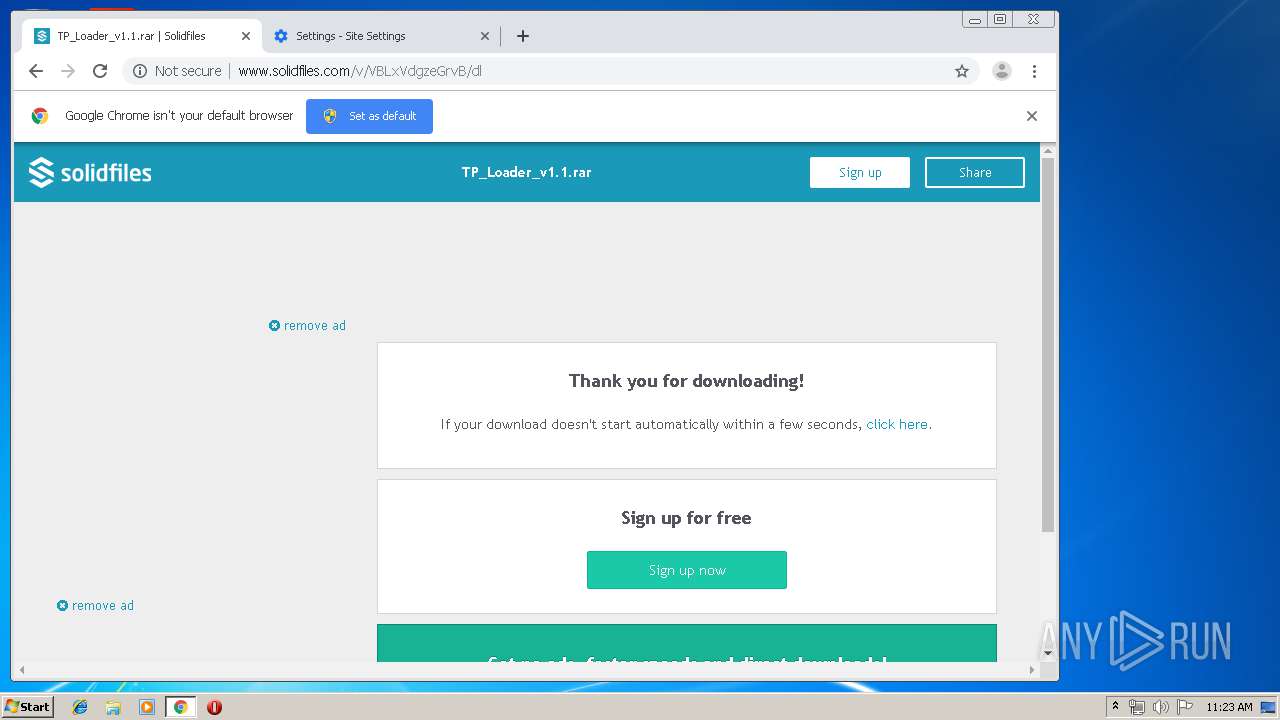
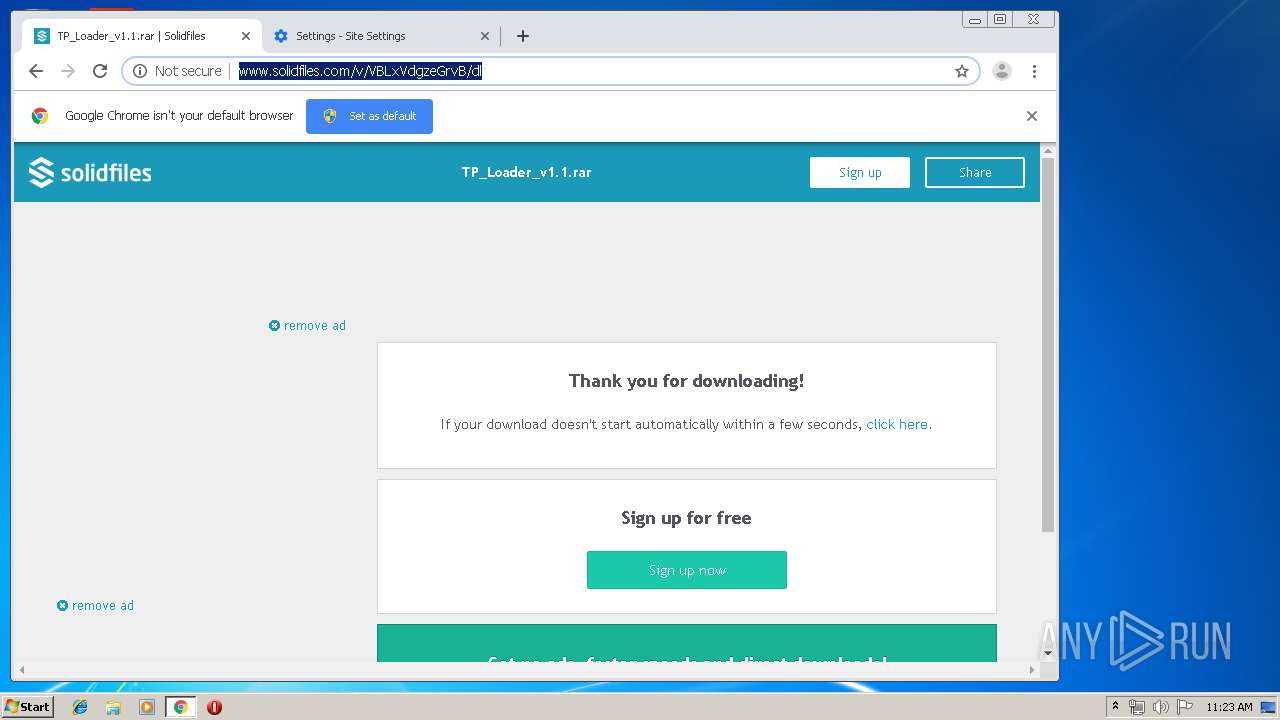
| URL: | http://www.solidfiles.com/v/VBLxVdgzeGrvB |
| Full analysis: | https://app.any.run/tasks/8390507b-969a-435f-b332-e252d4db90aa |
| Verdict: | No threats detected |
| Analysis date: | August 10, 2019, 10:21:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3F20C0E2D489DF7943216142A6DE9DA3 |
| SHA1: | 79E4FD356A3CC73CB04D0FB762E2D8275FBDB40A |
| SHA256: | 09B901377A43AD0479B4F381FE8C4963BF029EBBAA0D861A4D1EB087617E9EF8 |
| SSDEEP: | 3:N1KJS4kIKLzz30r:Cc4k3Lf30r |
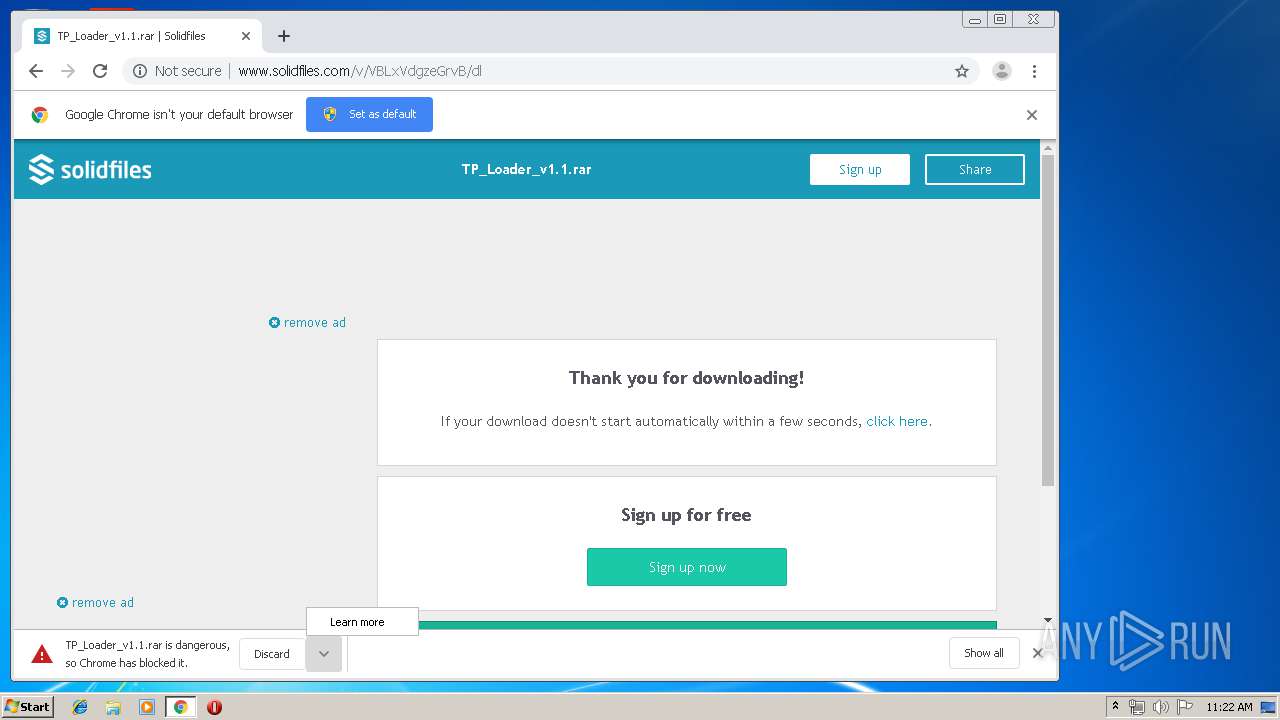
MALICIOUS
No malicious indicators.SUSPICIOUS
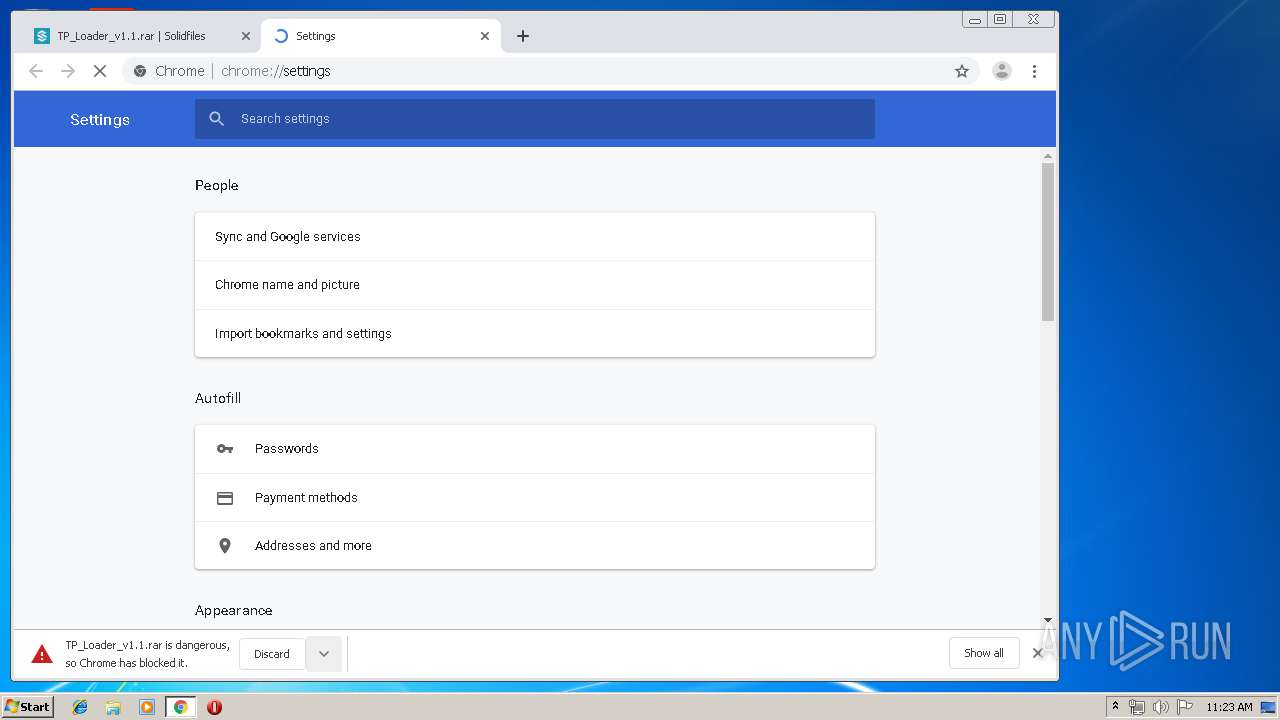
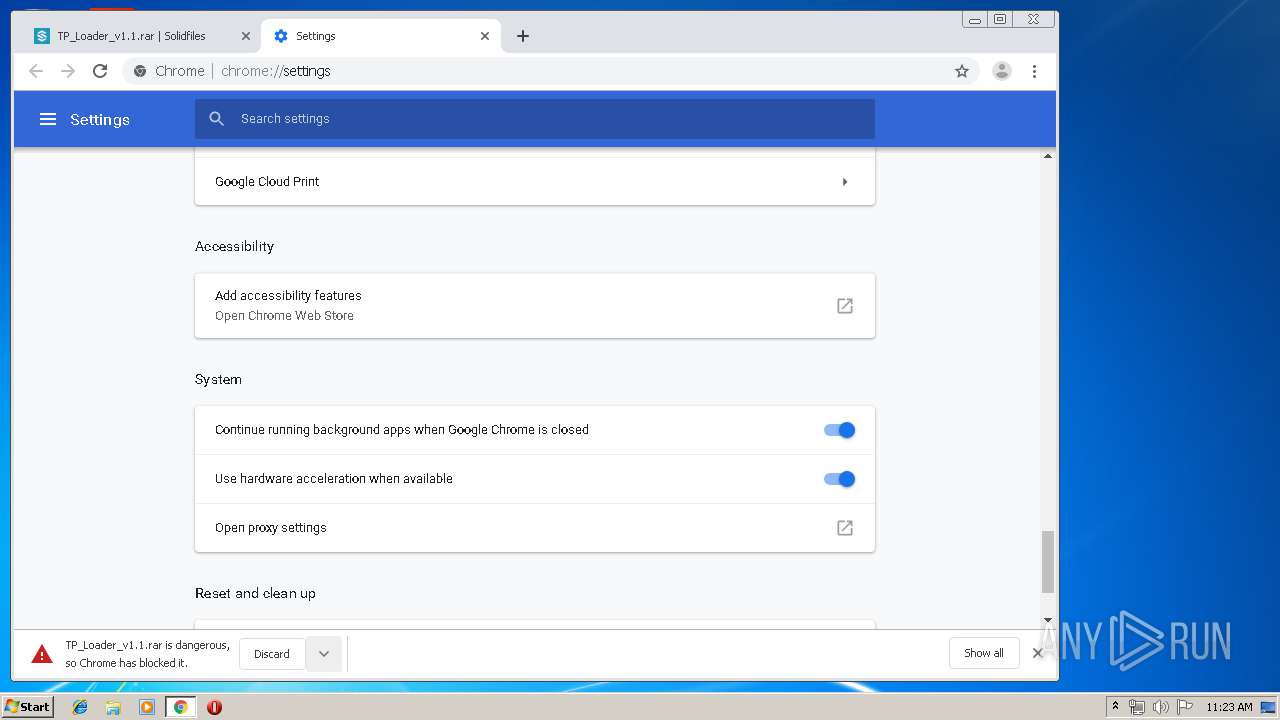
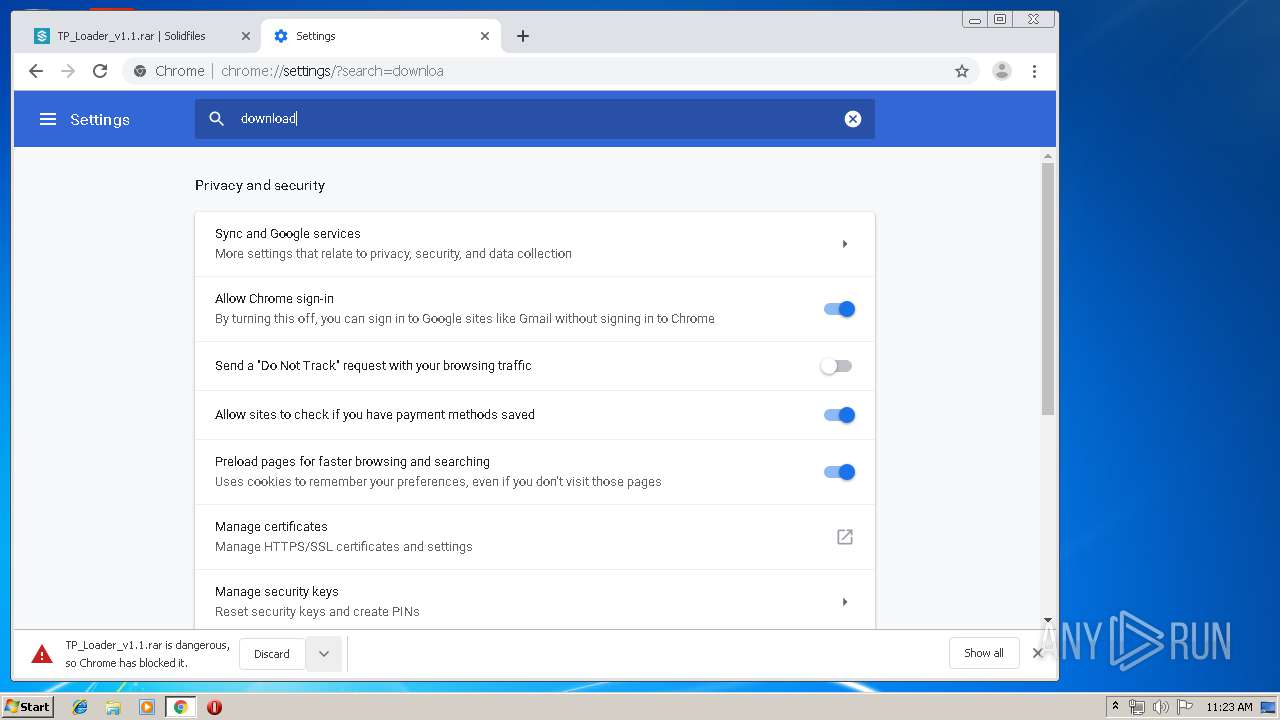
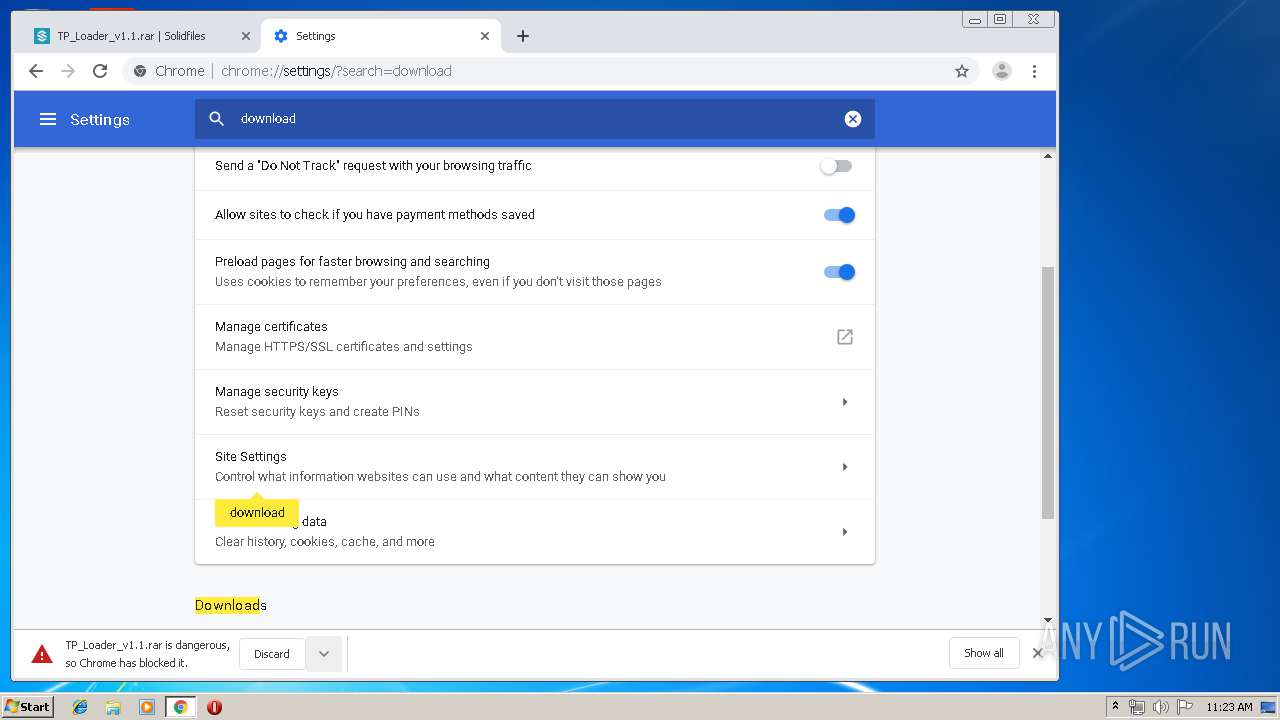
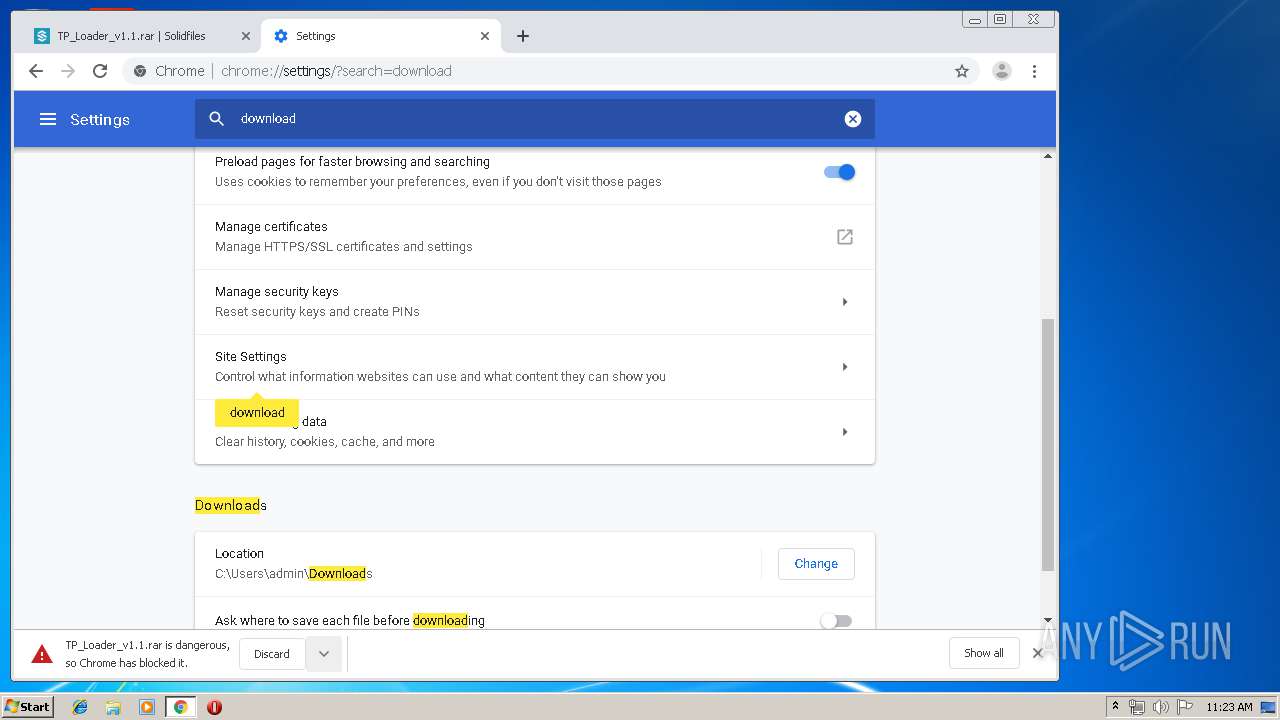
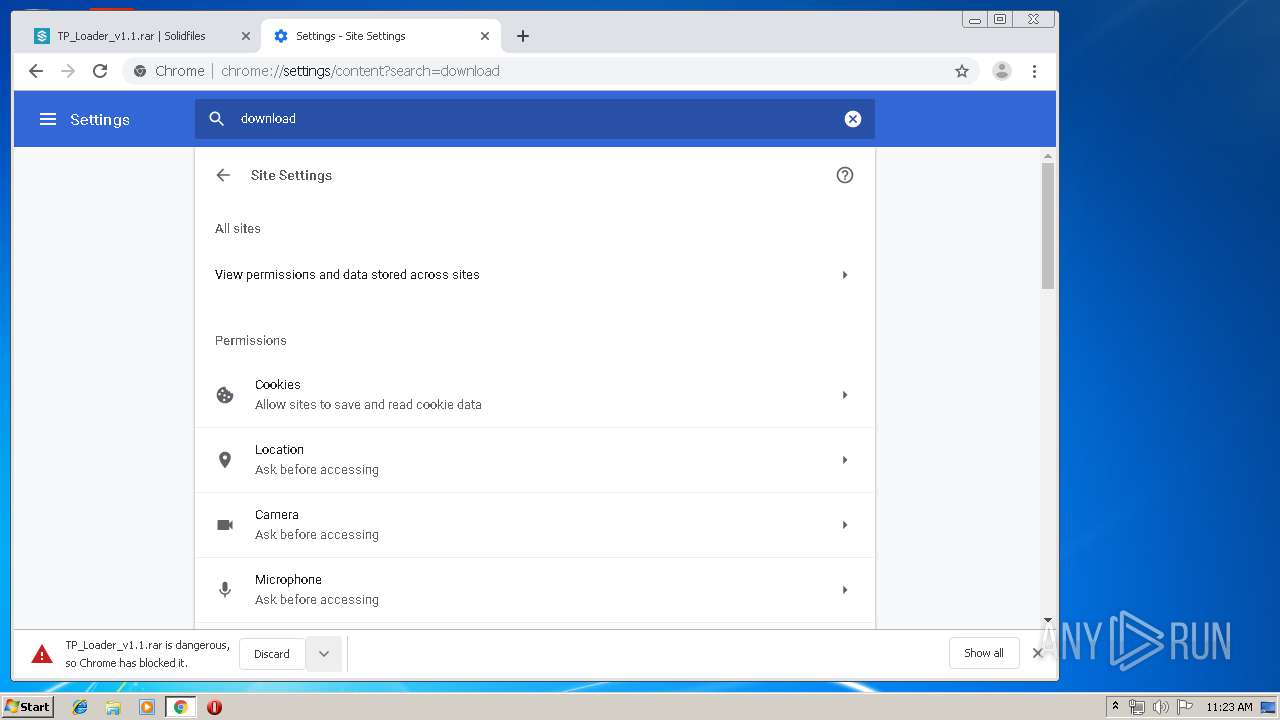
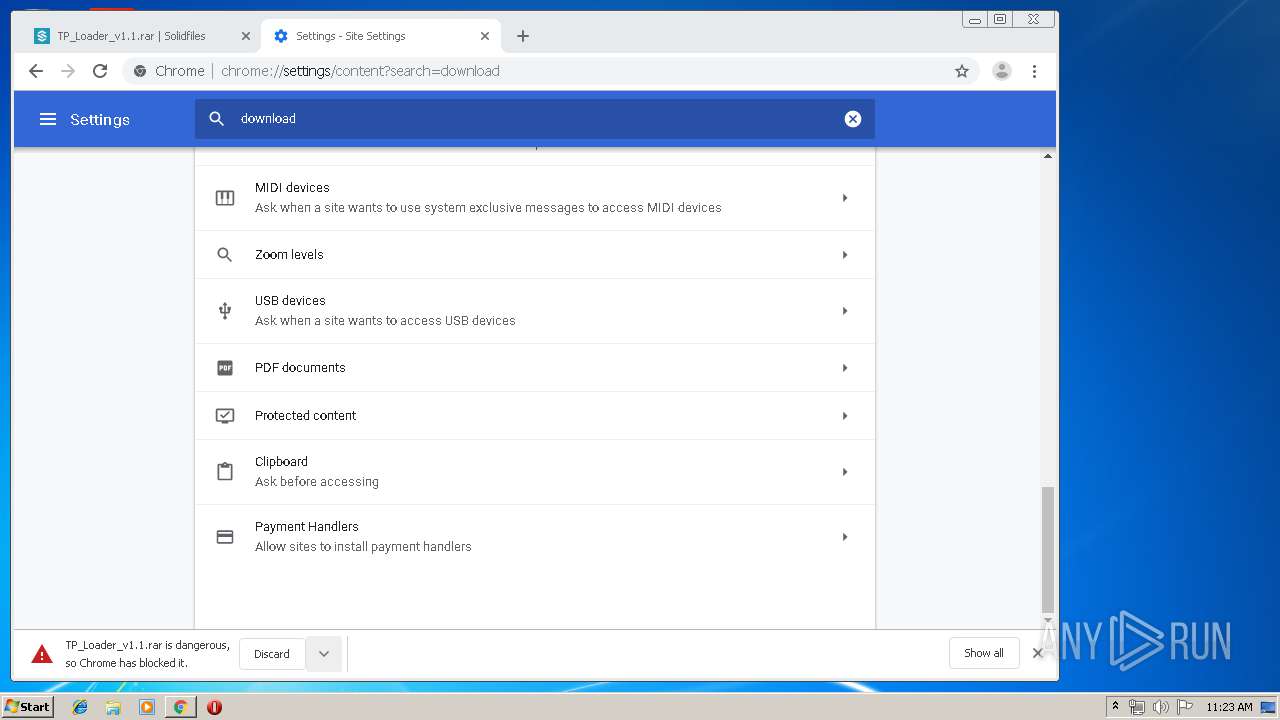
Modifies files in Chrome extension folder
- chrome.exe (PID: 3936)
INFO
Creates files in the user directory
- opera.exe (PID: 364)
- opera.exe (PID: 3668)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 3668)
Manual execution by user
- chrome.exe (PID: 3936)
- opera.exe (PID: 364)
Application launched itself
- chrome.exe (PID: 3936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9425468488611603187 --mojo-platform-channel-handle=4440 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=749969750904176441 --mojo-platform-channel-handle=3836 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
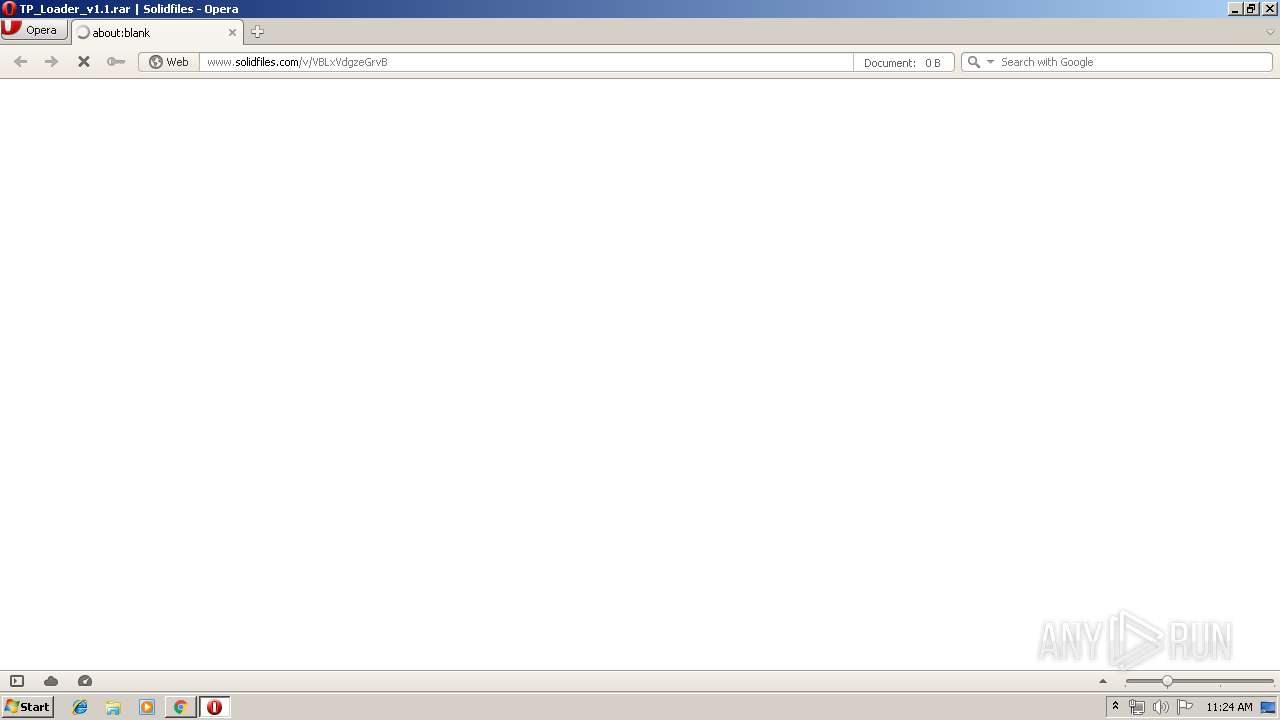
| 364 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14697019807475789355 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8093890163045662639 --mojo-platform-channel-handle=3732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17100109468779677312 --mojo-platform-channel-handle=568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13258366128233087157 --mojo-platform-channel-handle=3440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1193152236149821350 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8186893825503544460 --mojo-platform-channel-handle=3456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11096440941879705448,17569535329017258218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12218925086364540034 --mojo-platform-channel-handle=4516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 478
Read events
1 208
Write events
265
Delete events
5
Modification events
| (PID) Process: | (3668) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "http://www.solidfiles.com/v/VBLxVdgzeGrvB" | |||
| (PID) Process: | (3668) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3936-13209906154705156 |
Value: 259 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
0
Suspicious files
86
Text files
304
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprDBE2.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprDBF3.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprDC32.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EEQBSL4JIH9A0K1M4WGP.temp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprEA9B.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\00\0E\oprEB67.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\oprEB68.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
115
DNS requests
60
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3668 | opera.exe | GET | 200 | 216.58.207.67:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 546 b | whitelisted |
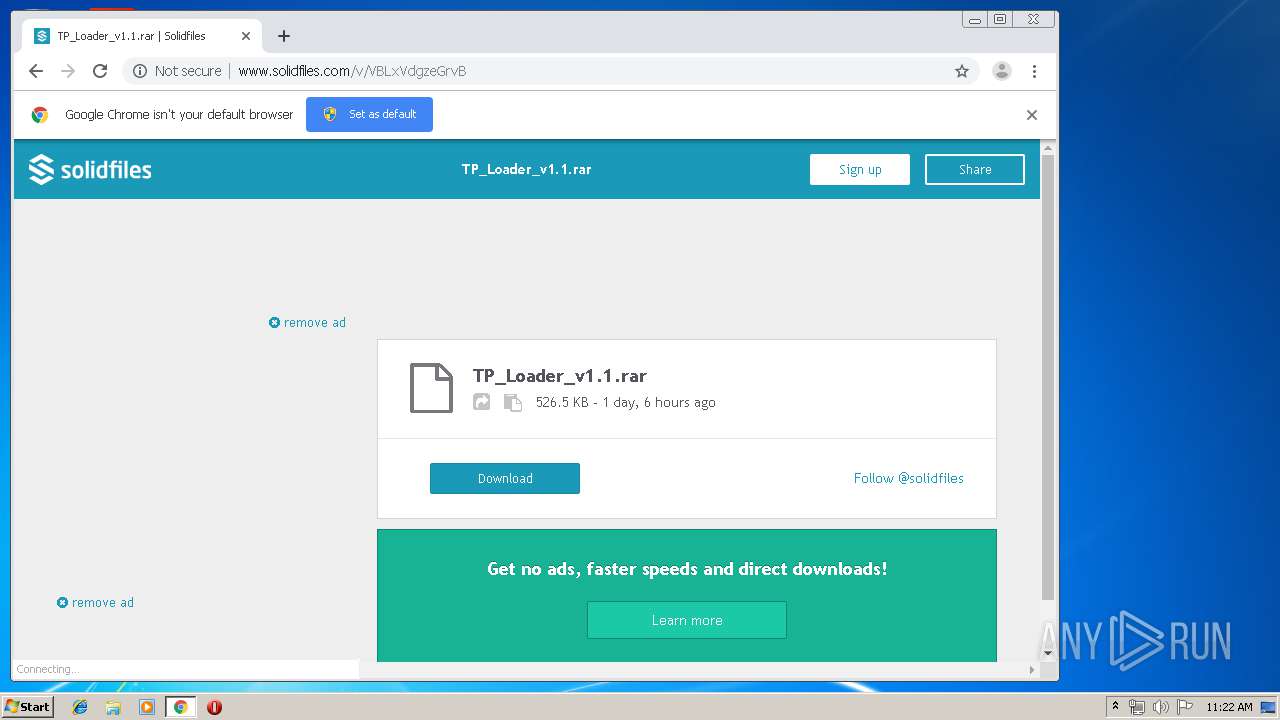
2392 | chrome.exe | GET | 200 | 37.221.163.214:80 | http://www.solidfiles.com/v/VBLxVdgzeGrvB | RO | html | 14.8 Kb | suspicious |
3668 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/COMODORSACertificationAuthority.crl | US | der | 812 b | whitelisted |
3668 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/AddTrustExternalCARoot.crl | US | der | 673 b | whitelisted |
3668 | opera.exe | GET | 200 | 185.60.216.19:80 | http://connect.facebook.net/en_US/all.js | IE | text | 1.74 Kb | whitelisted |
3668 | opera.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEFKcUKWn9UOD0NVZ4%2BltrUw%3D | US | der | 471 b | whitelisted |
3668 | opera.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDXyXxKNJJ7yggAAAAADcmt | US | der | 472 b | whitelisted |
3668 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
2392 | chrome.exe | POST | 200 | 37.221.163.214:80 | http://www.solidfiles.com/v/VBLxVdgzeGrvB/dl | RO | html | 13.8 Kb | suspicious |
2392 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3668 | opera.exe | 185.26.182.93:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
3668 | opera.exe | 37.221.163.214:80 | www.solidfiles.com | Voxility S.R.L. | RO | suspicious |
3668 | opera.exe | 104.27.129.228:443 | solidfilescdn.com | Cloudflare Inc | US | shared |
3668 | opera.exe | 185.26.182.93:80 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
3668 | opera.exe | 151.139.128.14:80 | crl.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
3668 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3668 | opera.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3668 | opera.exe | 216.58.207.74:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3668 | opera.exe | 185.60.216.19:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3668 | opera.exe | 93.184.220.66:80 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.solidfiles.com |
| suspicious |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
solidfilescdn.com |
| malicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
crl.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2392 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |