| File name: | Minecraft Launcher.exe |
| Full analysis: | https://app.any.run/tasks/5a000aed-b402-478f-be37-5d640a07a5e8 |
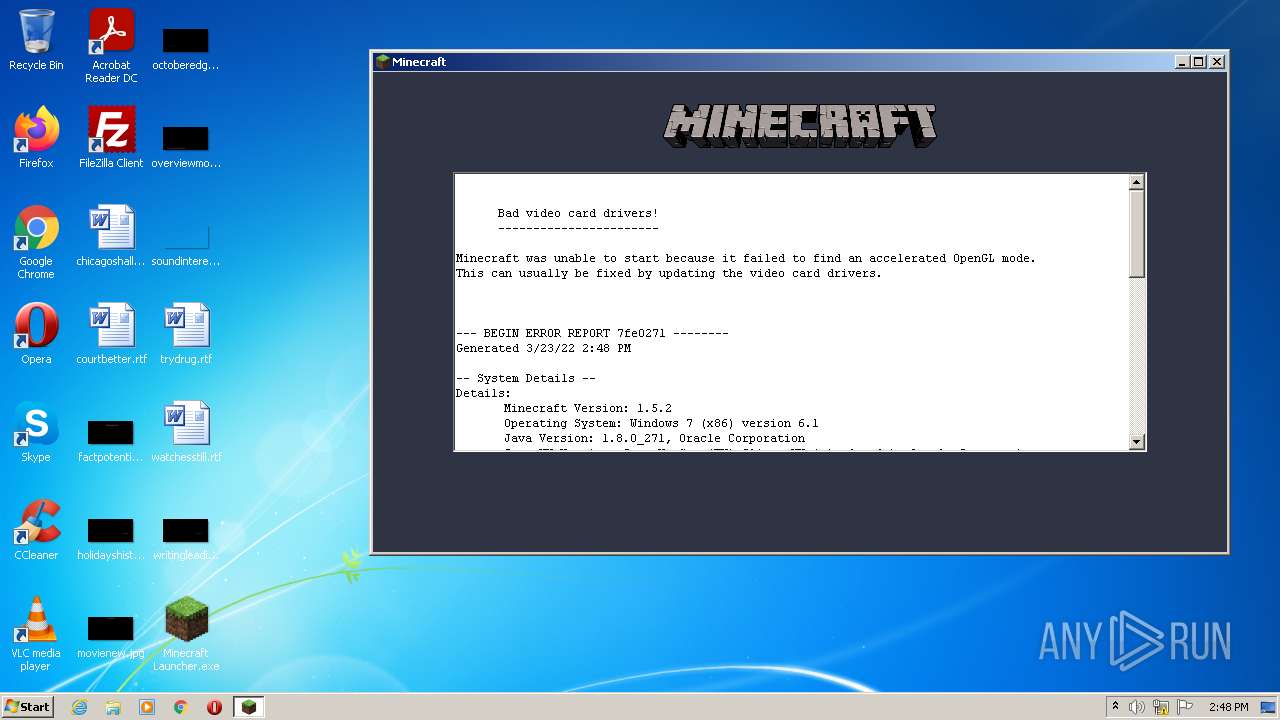
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2022, 14:47:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 605A171C61A0607BDCF6BE80ED07CF95 |
| SHA1: | 477D4391B0D84406127E43EAD289A3596AC1E5E5 |
| SHA256: | 09B78DC85713CA0F27F17D94C939CC606A59847C1F2B5CDD281B52A48CDAEAB9 |
| SSDEEP: | 6144:4mmx3k74XODG40zQG7NP0nuc6Hzp3wT66vlm4LbHL+pNn40yY7MmI2lP:ax3u9q400uB74fKL0m |
MALICIOUS
Drops executable file immediately after starts
- Minecraft Launcher.exe (PID: 3004)
Loads dropped or rewritten executable
- javaw.exe (PID: 3624)
Application was dropped or rewritten from another process
- i4jdel0.exe (PID: 3272)
SUSPICIOUS
Check for Java to be installed
- Minecraft Launcher.exe (PID: 3004)
- javaw.exe (PID: 3624)
Creates files in the program directory
- java.exe (PID: 3088)
Checks supported languages
- Minecraft Launcher.exe (PID: 3004)
- java.exe (PID: 3088)
- i4jdel0.exe (PID: 3272)
- javaw.exe (PID: 3624)
Uses ICACLS.EXE to modify access control list
- java.exe (PID: 3088)
Reads the computer name
- Minecraft Launcher.exe (PID: 3004)
- javaw.exe (PID: 3624)
Drops a file with too old compile date
- javaw.exe (PID: 3624)
Creates files in the user directory
- javaw.exe (PID: 3624)
Executable content was dropped or overwritten
- javaw.exe (PID: 3624)
- Minecraft Launcher.exe (PID: 3004)
Drops a file that was compiled in debug mode
- Minecraft Launcher.exe (PID: 3004)
INFO
Checks supported languages
- icacls.exe (PID: 2180)
Reads the computer name
- icacls.exe (PID: 2180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (30.9) |
| .scr | | | Windows screen saver (14.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
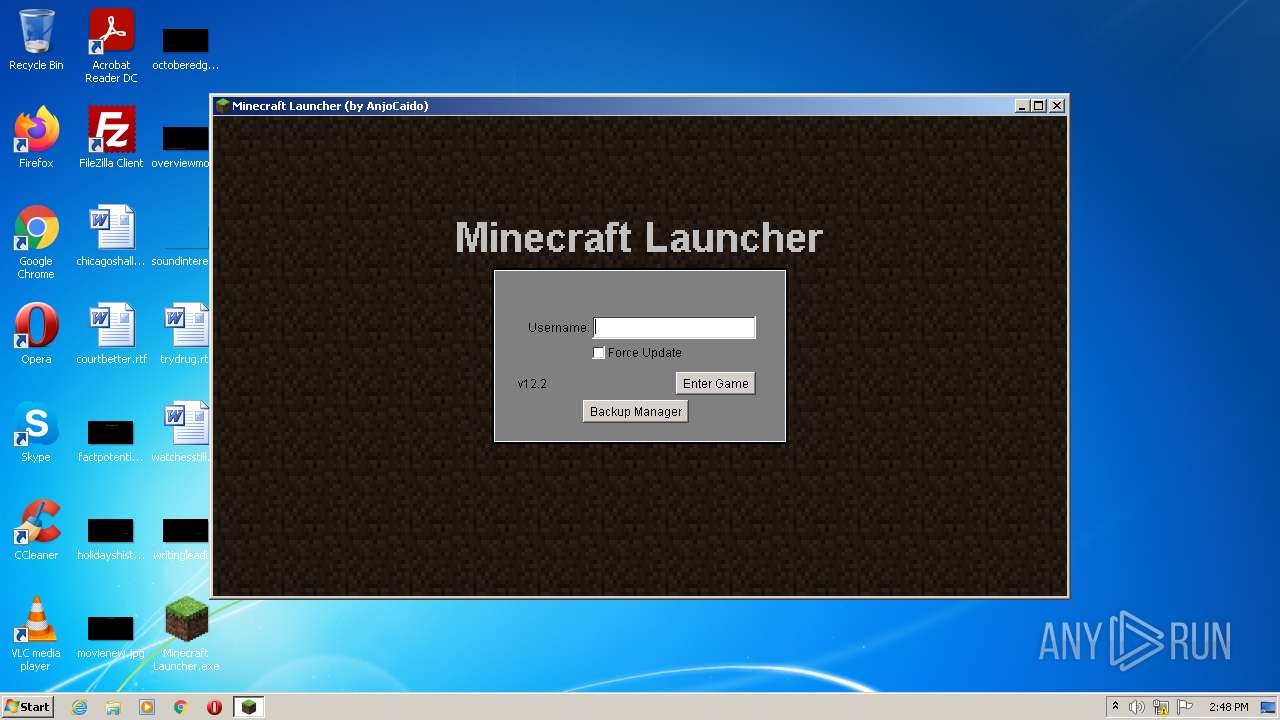
| InternalName: | MinecraftSP |
|---|---|
| OriginalFileName: | MinecraftSP.exe |
| ProductVersion: | 12.1.2.0 |
| ProductName: | MinecraftSP |
| LegalCopyright: | 2010 AnjoCaido (but Mojang have the rights over the game, you pirate!) |
| FileVersion: | 12.1.2.0 |
| FileDescription: | Free launcher for Minecraft Alpha |
| CompanyName: | AnjoCaido |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Win32 |
| FileFlags: | Debug |
| FileFlagsMask: | 0x0017 |
| ProductVersionNumber: | 12.1.2.0 |
| FileVersionNumber: | 12.1.2.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x11d8 |
| UninitializedDataSize: | 50688 |
| InitializedDataSize: | 494592 |
| CodeSize: | 128000 |
| LinkerVersion: | 2.56 |
| PEType: | PE32 |
| TimeStamp: | 2010:06:14 16:51:18+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2010 14:51:18 |
| CompanyName: | AnjoCaido |
| FileDescription: | Free launcher for Minecraft Alpha |
| FileVersion: | 12.1.2.0 |
| LegalCopyright: | 2010 AnjoCaido (but Mojang have the rights over the game, you pirate!) |
| ProductName: | MinecraftSP |
| ProductVersion: | 12.1.2.0 |
| OriginalFilename: | MinecraftSP.exe |
| InternalName: | MinecraftSP |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Jun-2010 14:51:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F2B8 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49943 |
.data | 0x00021000 | 0x000010B8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.32611 |
.bss | 0x00023000 | 0x0000C5F0 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00030000 | 0x000014CC | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8582 |
.rsrc | 0x00032000 | 0x00057000 | 0x00057000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.89004 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.95711 | 784 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.60877 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.97783 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.69194 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.0852 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 3.18197 | 302 | UNKNOWN | UNKNOWN | RT_DIALOG |
1001 | 2.6474 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2180 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\Desktop\Minecraft Launcher.exe" | C:\Users\admin\Desktop\Minecraft Launcher.exe | Explorer.EXE | ||||||||||||
User: admin Company: AnjoCaido Integrity Level: MEDIUM Description: Free launcher for Minecraft Alpha Exit code: 0 Version: 12.1.2.0 Modules
| |||||||||||||||
| 3088 | c:\PROGRA~1\java\JRE18~1.0_2\bin\java.exe -version | c:\PROGRA~1\java\JRE18~1.0_2\bin\java.exe | — | Minecraft Launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3272 | C:\Users\admin\AppData\Local\Temp\i4jdel0.exe i4j7726838632142626036.tmp | C:\Users\admin\AppData\Local\Temp\i4jdel0.exe | — | Minecraft Launcher.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
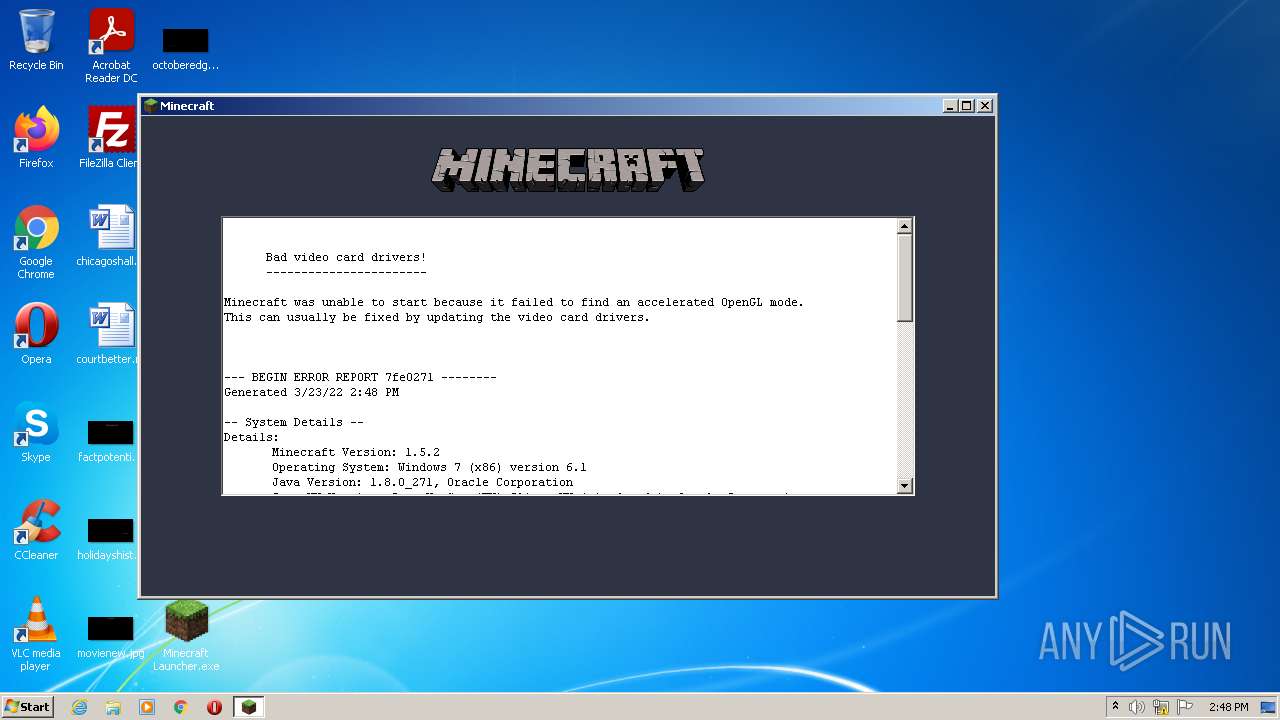
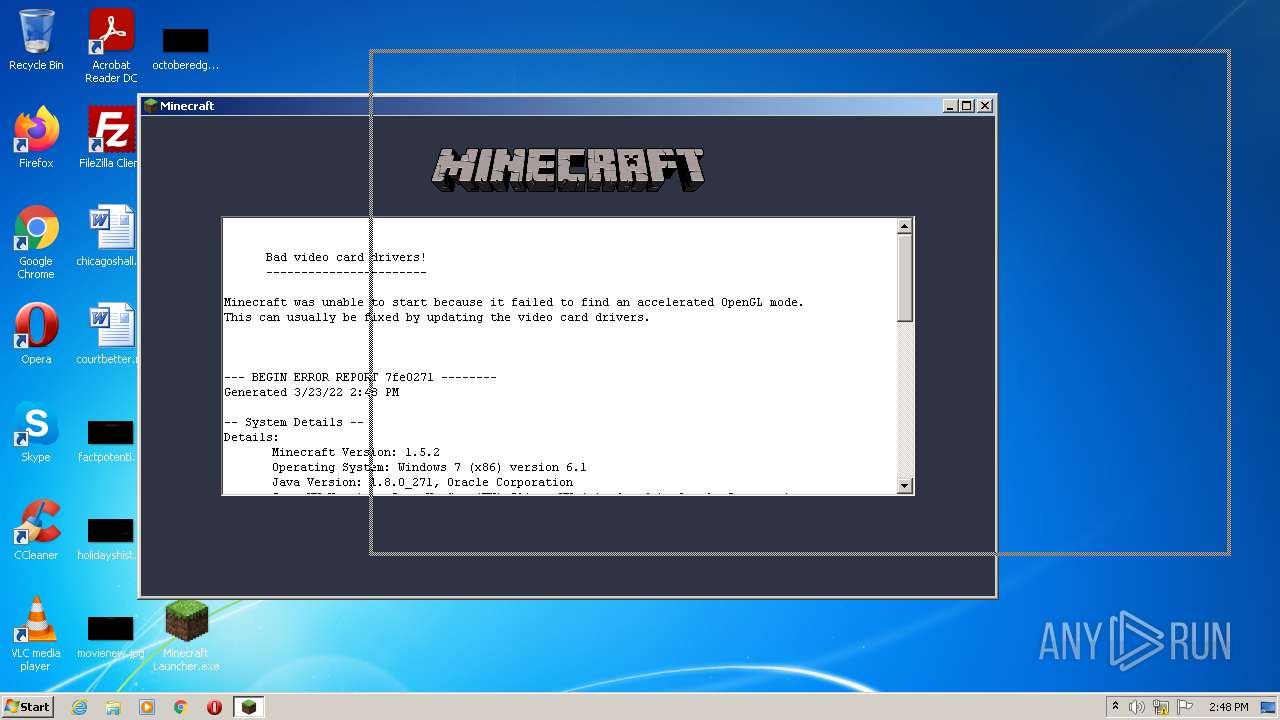
| 3624 | javaw -Xms512m -Xmx1024m -Dsun.java2d.noddraw=true -Dsun.java2d.d3d=false -Dsun.java2d.opengl=false -Dsun.java2d.pmoffscreen=false -classpath /C:/Users/admin/AppData/Local/Temp/e4jE543.tmp_dir/MinecraftSP.jar net.minecraft.LauncherFrame | C:\Program Files\Common Files\Oracle\Java\javapath\javaw.exe | Minecraft Launcher.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
Total events
1 282
Read events
1 280
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3004) Minecraft Launcher.exe | Key: | HKEY_CURRENT_USER\Software\ej-technologies\exe4j\jvms\c:/program files/java/jre1.8.0_271/bin/java.exe |
| Operation: | write | Name: | LastWriteTime |
Value: 7D3ADFE380B1D601 | |||
| (PID) Process: | (3004) Minecraft Launcher.exe | Key: | HKEY_CURRENT_USER\Software\ej-technologies\exe4j\jvms\c:/program files/java/jre1.8.0_271/bin/java.exe |
| Operation: | write | Name: | Version |
Value: 1.8.0_271 | |||
Executable files
12
Suspicious files
6
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | Minecraft Launcher.exe | C:\Users\admin\AppData\Local\Temp\i4j7726838632142626036.tmp | binary | |
MD5:— | SHA256:— | |||
| 3624 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\lastlogin | text | |
MD5:— | SHA256:— | |||
| 3088 | java.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 3004 | Minecraft Launcher.exe | C:\Users\admin\AppData\Local\Temp\e4jE543.tmp_dir\i4jdel.exe | executable | |
MD5:24F6D923EF6956ABD0449C879F36D7C7 | SHA256:B8FE41DD005BB309F2ED4B81300CE0FBE4DDFC2A379A5101C11ECE47462D1997 | |||
| 3004 | Minecraft Launcher.exe | C:\Users\admin\AppData\Local\Temp\e4jE543.tmp_dir\exe4jlib.jar | java | |
MD5:C97D4F24CE40002EBDCBEB9148617E44 | SHA256:411F86A58A889912D462EAD6BF382547476787AEC915BCC047CE7638608531B9 | |||
| 3624 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio5544601344768062243.tmp | image | |
MD5:91D3708A258E5F789E2AE888CF68F66F | SHA256:0AD2672561C2BA4E86C38702682BD84D720351F3E5C4CA232F0043AAB7FA8B28 | |||
| 3624 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\bin\lwjgl.jar | compressed | |
MD5:7A07C4285FA9A6B204BA59F011F1CD77 | SHA256:1B3258CE0F1091E6043D323B2980D0176C4D635B3A4F2AA7BEF178989093A12C | |||
| 3004 | Minecraft Launcher.exe | C:\Users\admin\AppData\Local\Temp\i4jdel0.exe | executable | |
MD5:24F6D923EF6956ABD0449C879F36D7C7 | SHA256:B8FE41DD005BB309F2ED4B81300CE0FBE4DDFC2A379A5101C11ECE47462D1997 | |||
| 3624 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\bin\jinput.jar | compressed | |
MD5:A7835A73A130656ABA23E34147A55367 | SHA256:E1B2F1E53F5B20768FA69DB7E61BC8E00A773D7B3B68E6E88E381DDC67F9DB17 | |||
| 3624 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio6141369392544589567.tmp | image | |
MD5:D141CC8E71A3351F1AACB88A74B45FA4 | SHA256:2788675E062E1111EAD50A9A05971A7C11FE6246A89F571CF9F59ED68C72BB17 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
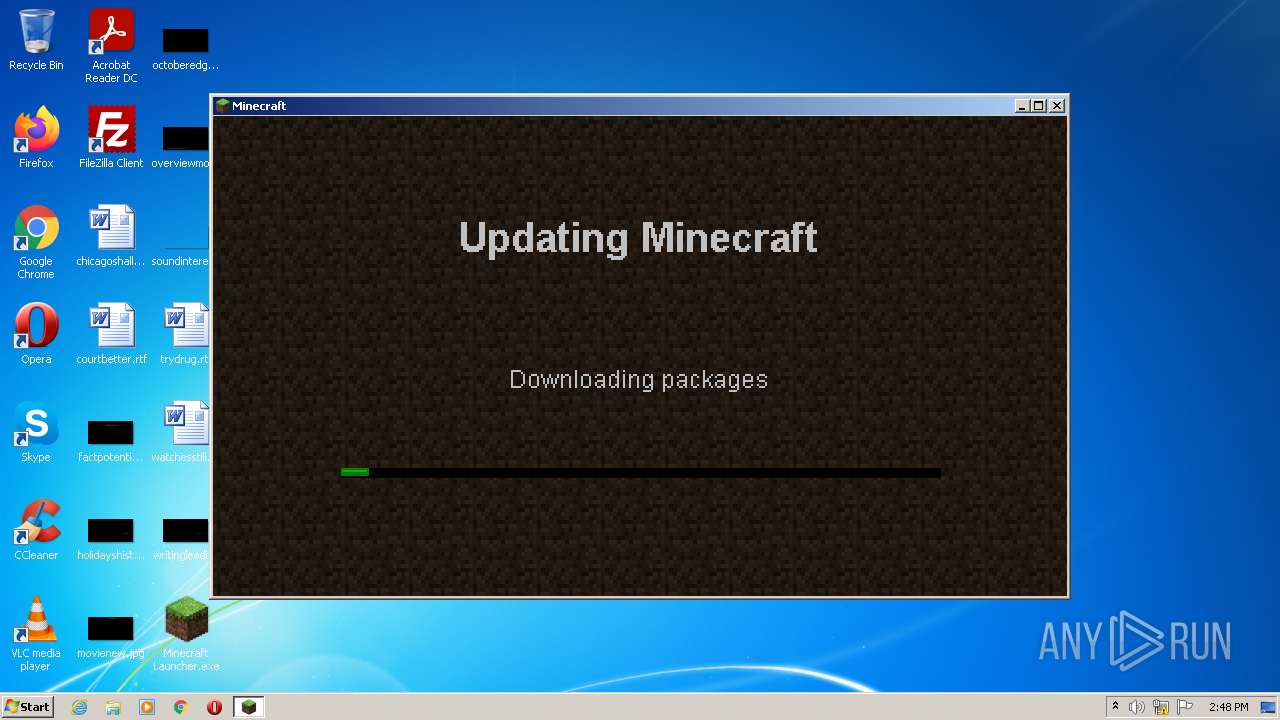
3624 | javaw.exe | HEAD | 200 | 52.217.198.88:80 | http://s3.amazonaws.com/MinecraftDownload/lwjgl_util.jar | US | — | — | shared |
3624 | javaw.exe | HEAD | — | 52.217.33.158:80 | http://s3.amazonaws.com/MinecraftDownload/jinput.jar | US | — | — | shared |
3624 | javaw.exe | HEAD | 200 | 52.217.198.88:80 | http://s3.amazonaws.com/MinecraftDownload/windows_natives.jar.lzma | US | — | — | shared |
3624 | javaw.exe | HEAD | 200 | 52.217.198.88:80 | http://s3.amazonaws.com/MinecraftDownload/minecraft.jar | US | — | — | shared |
3624 | javaw.exe | HEAD | 200 | 52.217.198.88:80 | http://s3.amazonaws.com/MinecraftDownload/jinput.jar | US | — | — | shared |
3624 | javaw.exe | GET | 200 | 52.217.198.88:80 | http://s3.amazonaws.com/MinecraftDownload/windows_natives.jar.lzma | US | lzma | 479 Kb | shared |
3624 | javaw.exe | GET | 200 | 52.217.198.88:80 | http://s3.amazonaws.com/MinecraftDownload/jinput.jar | US | compressed | 222 Kb | shared |
3624 | javaw.exe | GET | 200 | 52.217.198.88:80 | http://s3.amazonaws.com/MinecraftDownload/lwjgl_util.jar | US | compressed | 135 Kb | shared |
3624 | javaw.exe | GET | 200 | 52.217.198.88:80 | http://s3.amazonaws.com/MinecraftDownload/lwjgl.jar | US | compressed | 721 Kb | shared |
3624 | javaw.exe | HEAD | 200 | 52.217.33.158:80 | http://s3.amazonaws.com/MinecraftDownload/lwjgl.jar | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3624 | javaw.exe | 52.217.33.158:80 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
3624 | javaw.exe | 52.217.198.88:80 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s3.amazonaws.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3624 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
3624 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
3624 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download By Vulnerable Client |
3624 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download By Vulnerable Client |
3624 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download By Vulnerable Client |