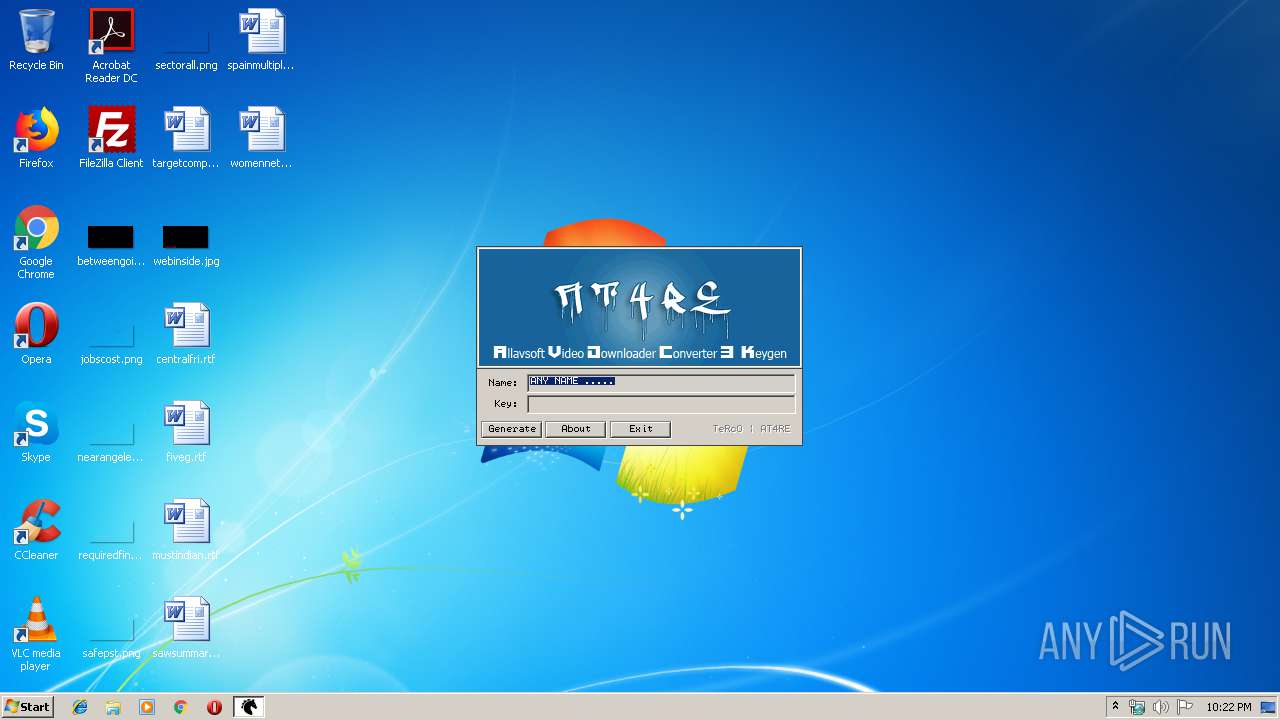
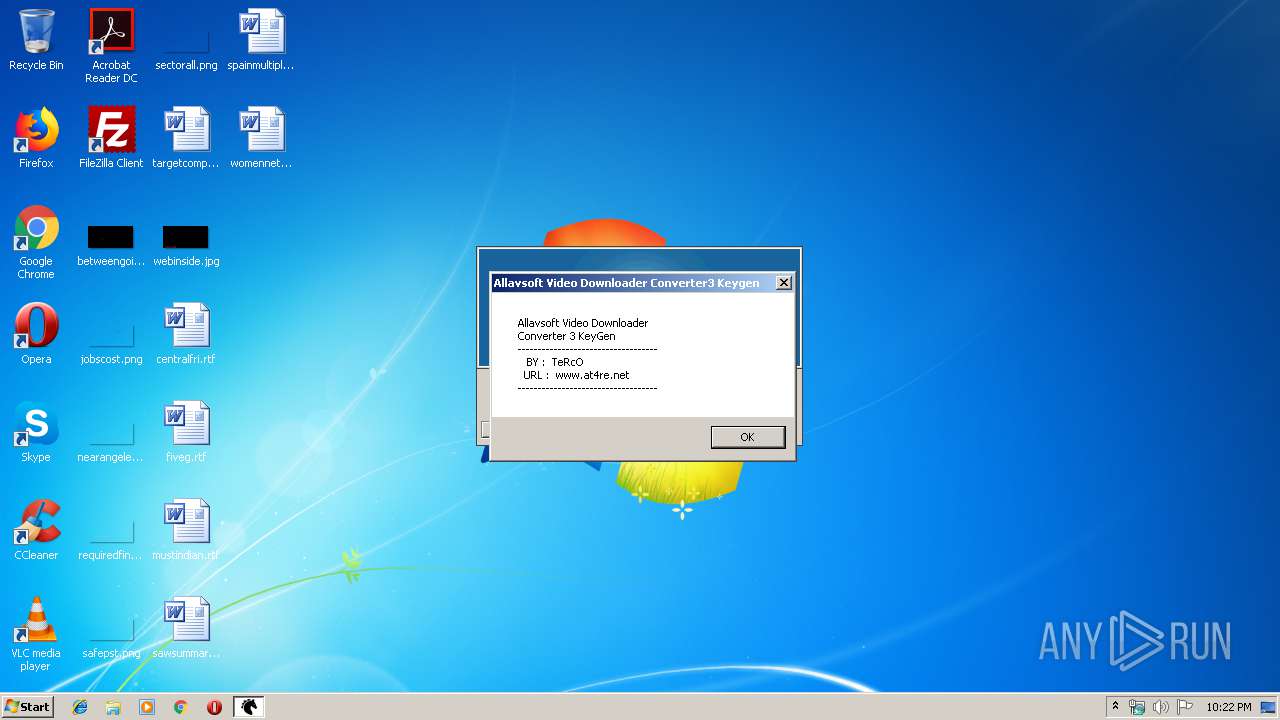
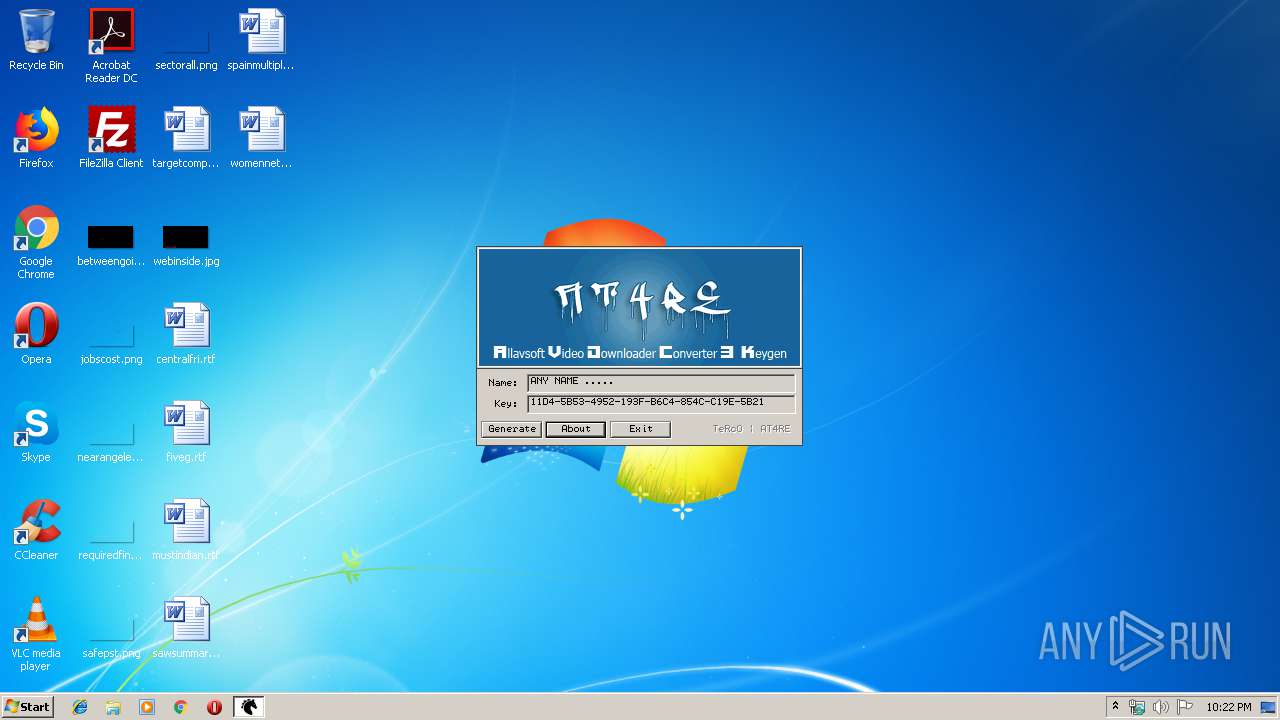
| File name: | Allavsoft.Video.Downloader.Converter.v3-Keygen-AT4RE.exe |
| Full analysis: | https://app.any.run/tasks/71f61a1a-ceba-40ae-9bb8-4c69a5633125 |
| Verdict: | No threats detected |
| Analysis date: | October 12, 2019, 21:21:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 70F8B52073121906E366B8C1368BBF1E |
| SHA1: | D5E2461F9076679E5DDC93EFA8547D96B3B04D61 |
| SHA256: | 09B1C92F2355C2B942B4018954D130C787FEADE4BDDA28E27289C21751E54C01 |
| SSDEEP: | 6144:VBmZCq518641FTlBabePrdKj/7SFN4UtrVultIGv2cfRfUG0wv:/GCq51tO9jd2/8xKzFnfRsG0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
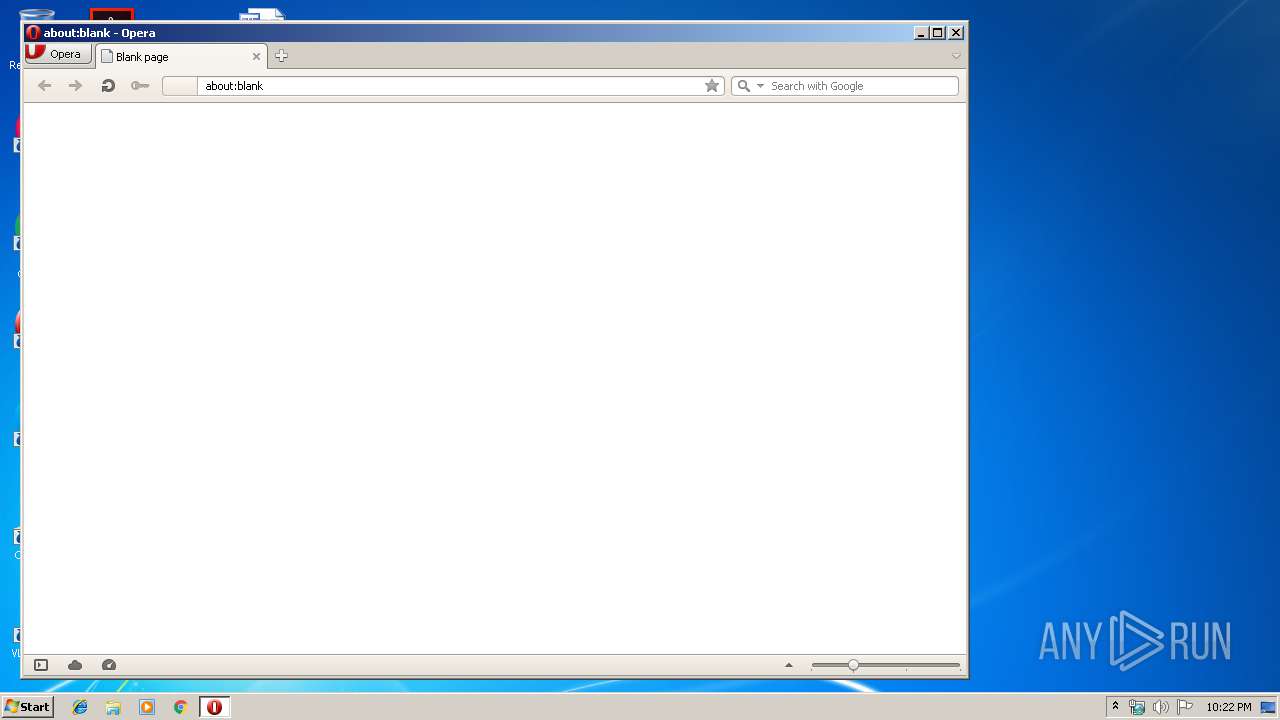
Manual execution by user
- opera.exe (PID: 3172)
Creates files in the user directory
- opera.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (94.6) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (2) |
| .scr | | | Windows screen saver (1.8) |
| .exe | | | Win32 Executable (generic) (0.6) |
| .exe | | | Win16/32 Executable Delphi generic (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 324096 |
| InitializedDataSize: | 180736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5002c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0004F05C | 0x0004F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54332 |
DATA | 0x00051000 | 0x00003954 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.36705 |
BSS | 0x00055000 | 0x00012E4D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00068000 | 0x00002170 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.99857 |
.tls | 0x0006B000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0006C000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.201539 |
.reloc | 0x0006D000 | 0x000056B8 | 0x00005800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00073000 | 0x00020B38 | 0x00020C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.24824 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
5 | 0.97565 | 16936 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
6 | 1.24702 | 9640 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
7 | 1.31393 | 4264 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
8 | 1.5157 | 2440 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
9 | 1.60266 | 1128 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
101 | 3.11403 | 540 | UNKNOWN | German - Germany | RT_DIALOG |
103 | 3.91415 | 77154 | UNKNOWN | German - Germany | RT_BITMAP |
4081 | 3.07549 | 244 | UNKNOWN | UNKNOWN | RT_STRING |
4082 | 3.22434 | 476 | UNKNOWN | UNKNOWN | RT_STRING |
4083 | 3.2356 | 340 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
winmm.dll |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2724 | "C:\Users\admin\AppData\Local\Temp\Allavsoft.Video.Downloader.Converter.v3-Keygen-AT4RE.exe" | C:\Users\admin\AppData\Local\Temp\Allavsoft.Video.Downloader.Converter.v3-Keygen-AT4RE.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
205
Read events
146
Write events
59
Delete events
0
Modification events
| (PID) Process: | (3172) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3172) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
33
Text files
9
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr44.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr83.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K6VPBXOUIYDIEKABEVQN.temp | — | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr98D.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr98E.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr98F.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3172 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3172 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3172 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3172 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |