| File name: | 最新非法滞留境外劝返名单.exe |
| Full analysis: | https://app.any.run/tasks/f6c03a0a-199b-467d-a7fa-3ff79883af13 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 05:04:00 |
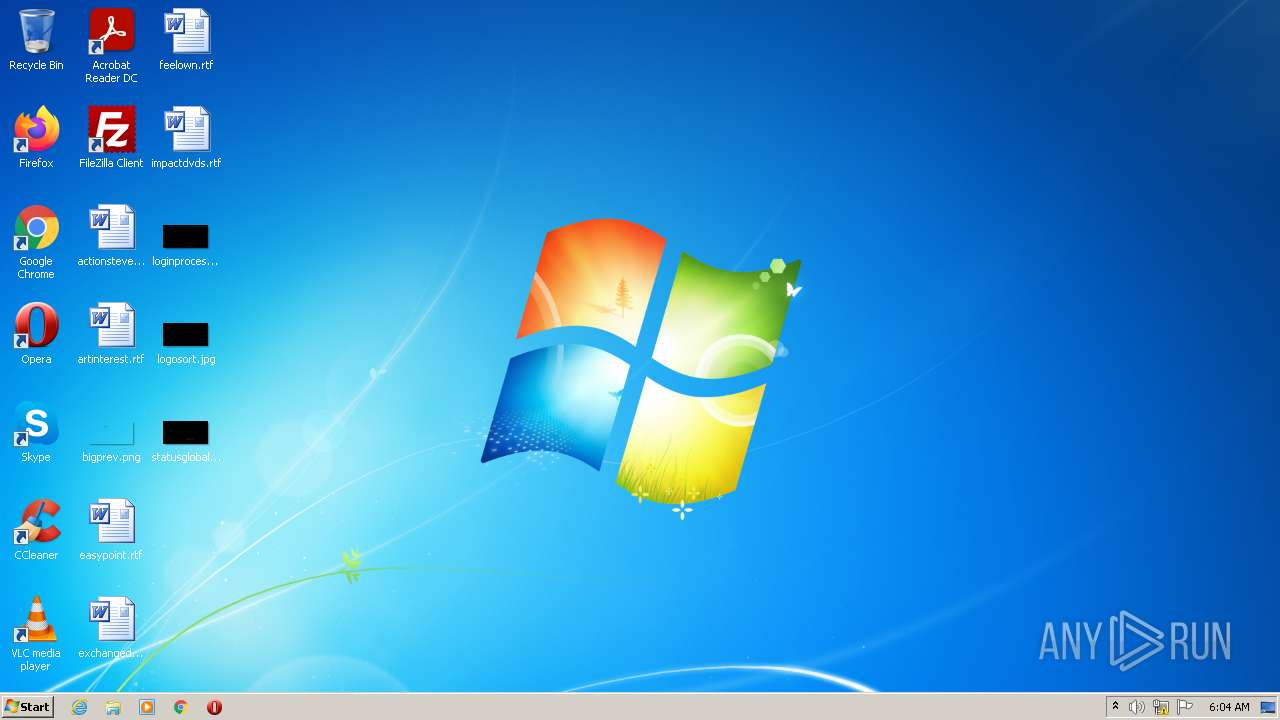
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EDF09F0C5DD060C50671F60C0FFABC23 |
| SHA1: | 7A46A9AB6C3729498CE18E3E033A4D9CA9170EFA |
| SHA256: | 09AB5D260BDE3B863B7705EC40C210B0E91BD49C10B04D6DD753EEF35C0B5782 |
| SSDEEP: | 24576:f4nXubIQGyxbPV0db26gL3Jl99iXH5TK9SRKpWu07TXu/icZTEwLbDKKl33C/9lG:fqe3f6ofiXH5TBiYfXyXo8PVUHlum0 |
MALICIOUS
Application was dropped or rewritten from another process
- UnRAR.exe (PID: 2336)
- FF_chrome.exe (PID: 3368)
- NNN_chrome.exe (PID: 3528)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 4016)
- NNN_chrome.exe (PID: 3528)
SUSPICIOUS
No suspicious indicators.INFO
Application was dropped or rewritten from another process
- 最新非法滞留境外劝返名单.tmp (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2020-Sep-13 09:00:51 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | https://www.a464ne6ae4b6a4.cc/ |
| FileDescription: | a464ne6ae4b6a4 Setup |
| FileVersion: | - |
| LegalCopyright: | a464ne6ae4b6a4 |
| OriginalFileName: | - |
| ProductName: | a464ne6ae4b6a4 |
| ProductVersion: | a464ne6ae4b6a4 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 80 |
| e_cp: | 2 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | 15 |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | 26 |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 256 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 10 |
| TimeDateStamp: | 2020-Sep-13 09:00:51 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 734748 | 735232 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 741376 | 5768 | 6144 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 749568 | 14244 | 14336 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 765952 | 28136 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.idata | 794624 | 3894 | 4096 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 798720 | 420 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 802816 | 154 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 806912 | 24 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rdata | 811008 | 93 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 815104 | 30088 | 30208 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41996 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.6421 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.15425 | 156 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.31895 | 884 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.28786 | 920 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 779836 |
__dbk_fcall_wrapper | 2 | 53408 |
TMethodImplementationIntercept | 3 | 344160 |
Total processes
54
Monitored processes
13
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1968 | "C:\Windows\System32\runas.exe" /trustlevel:0x20000 "cmd /c copy /b /y \"C:\Users\Public\Documents\NGLA\NNN_chrome.exe\" \"C:\Users\Public\Documents\NGLA\svchongl.exe\"" | C:\Windows\System32\runas.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1980 | "C:\Windows\System32\taskkill.exe" /f /IM 最新非法滞留境外劝返名单.exe | C:\Windows\System32\taskkill.exe | — | 最新非法滞留境外劝返名单.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | "C:\Windows\System32\runas.exe" /trustlevel:0x20000 "cmd /c reg add HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v NGLA /t REG_SZ /d \"C:\Users\Public\Documents\NGLA\svchongl.exe\" /f" | C:\Windows\System32\runas.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | cmd /c reg add HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v NGLA /t REG_SZ /d "C:\Users\Public\Documents\NGLA\svchongl.exe" /f | C:\Windows\System32\cmd.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2336 | "C:\Users\admin\Desktop\UnRAR.exe" x "C:\Users\Public\Documents\NGLA\bin.rar" "C:\Users\Public\Documents\NGLA\" -inul -y -o+ -pqwe123 | C:\Users\admin\Desktop\UnRAR.exe | — | cmd.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: Command line RAR Exit code: 0 Version: 6.2.0 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\is-DRSP4.tmp\最新非法滞留境外劝返名单.tmp" /SL5="$301AA,1347026,792576,C:\Users\admin\AppData\Local\Temp\最新非法滞留境外劝返名单.exe" | C:\Users\admin\AppData\Local\Temp\is-DRSP4.tmp\最新非法滞留境外劝返名单.tmp | — | 最新非法滞留境外劝返名单.exe | |||||||||||
User: admin Company: https://www.a464ne6ae4b6a4.cc/ Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3368 | "C:\Users\Public\Documents\NGLA\FF_chrome.exe" | C:\Users\Public\Documents\NGLA\FF_chrome.exe | 最新非法滞留境外劝返名单.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 46m6n4btaw Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3472 | "C:\Users\admin\AppData\Local\Temp\最新非法滞留境外劝返名单.exe" | C:\Users\admin\AppData\Local\Temp\最新非法滞留境外劝返名单.exe | — | Explorer.EXE | |||||||||||
User: admin Company: https://www.a464ne6ae4b6a4.cc/ Integrity Level: MEDIUM Description: a464ne6ae4b6a4 Setup Exit code: 1 Version: Modules
| |||||||||||||||
| 3528 | "C:\Users\Public\Documents\NGLA\NNN_chrome.exe" | C:\Users\Public\Documents\NGLA\NNN_chrome.exe | — | 最新非法滞留境外劝返名单.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3600 | cmd /c copy /b /y "C:\Users\Public\Documents\NGLA\NNN_chrome.exe" "C:\Users\Public\Documents\NGLA\svchongl.exe" | C:\Windows\System32\cmd.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 394
Read events
1 491
Write events
16
Delete events
887
Modification events
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: D4090000FA0F1CE677D8D801 | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 2FF4C2048F6994FCCBD7E5879A3F397AA6C7A72C66A2B751E8B6AEB702610323 | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\Desktop\UnRAR.exe | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: BC47E25BFFF0CF4CAC34F3680382C79D04FE9173BC69BD22C758F6F7A5A9B60E | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2516) 最新非法滞留境外劝返名单.tmp | Key: | HKEY_CURRENT_USER\Software |
| Operation: | write | Name: | USA |
Value: | |||
Executable files
8
Suspicious files
6
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | 最新非法滞留境外劝返名单.tmp | C:\Users\Public\Documents\NGLA\bin.rar | compressed | |
MD5:— | SHA256:— | |||
| 2516 | 最新非法滞留境外劝返名单.tmp | C:\Users\Public\Documents\NGLA\is-K2T3O.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2516 | 最新非法滞留境外劝返名单.tmp | C:\Users\Public\Documents\NGLA\AAAAAA\evqweqwe2.rar | compressed | |
MD5:— | SHA256:— | |||
| 2516 | 最新非法滞留境外劝返名单.tmp | C:\Users\Public\Documents\NGLA\is-9QESS.tmp | text | |
MD5:— | SHA256:— | |||
| 3472 | 最新非法滞留境外劝返名单.exe | C:\Users\admin\AppData\Local\Temp\is-DRSP4.tmp\最新非法滞留境外劝返名单.tmp | executable | |
MD5:— | SHA256:— | |||
| 2336 | UnRAR.exe | C:\Users\Public\Documents\NGLA\DLL_DLL.bin | binary | |
MD5:— | SHA256:— | |||
| 2516 | 最新非法滞留境外劝返名单.tmp | C:\Users\Public\Documents\NGLA\AAAAAA\is-JTRO0.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2516 | 最新非法滞留境外劝返名单.tmp | C:\Users\Public\Documents\NGLA\app.dat | text | |
MD5:— | SHA256:— | |||
| 2336 | UnRAR.exe | C:\Users\Public\Documents\NGLA\FF_chrome.exe | executable | |
MD5:— | SHA256:— | |||
| 2336 | UnRAR.exe | C:\Users\Public\Documents\NGLA\NNN_chrome.exe | executable | |
MD5:FFCB0336D59BD63E23E527D823289C8F | SHA256:E2FCCD0495E118A9C974C9454A86A4F810F6701BD19972C59F3F25F8105BA918 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3368 | FF_chrome.exe | 156.240.105.139:8001 | — | Hong Kong Communications International Co., Limited | HK | unknown |
DNS requests
Threats
Process | Message |
|---|---|
FF_chrome.exe | Sleep(1000) main |
FF_chrome.exe | 156.240.105.139 |
FF_chrome.exe | 156.240.105.139 |
FF_chrome.exe | Connect |
FF_chrome.exe | ³õ´Î£¬»ñÈ¡»î¶¯´°¿Ú |
FF_chrome.exe | sendLoginInfo |
FF_chrome.exe | send COMMAND_REPLAY_HEARTBEAT |