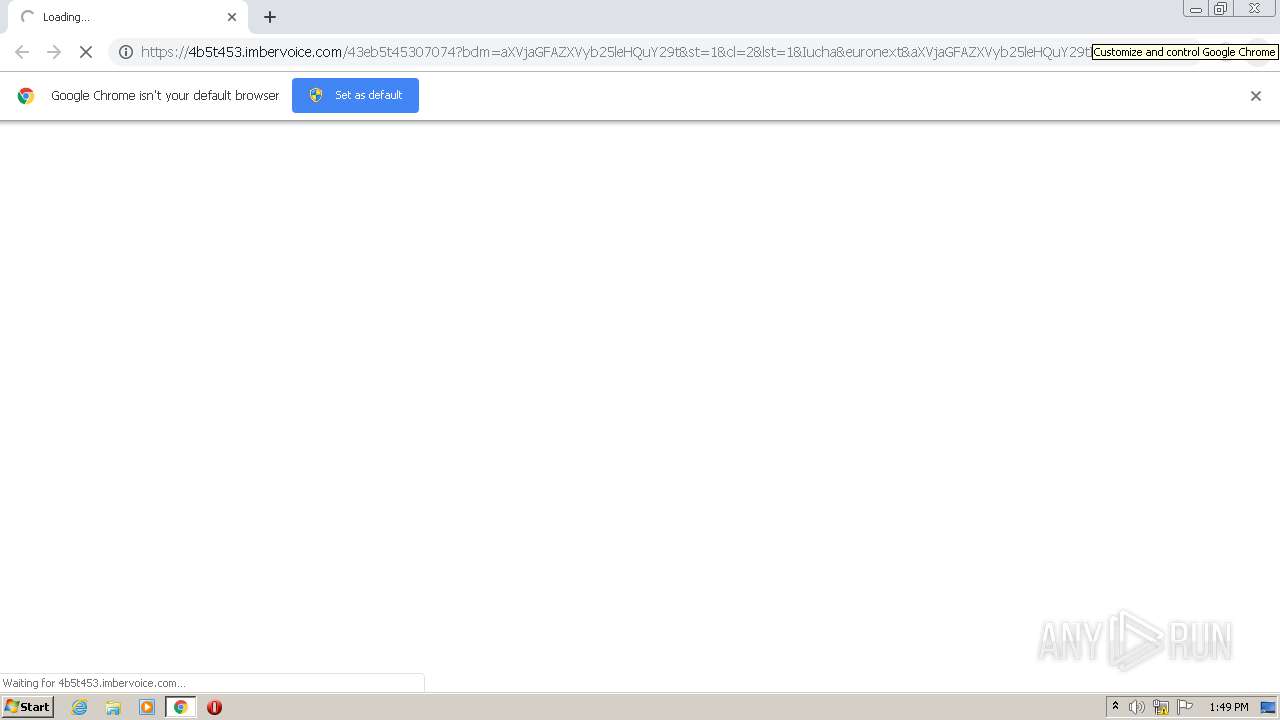
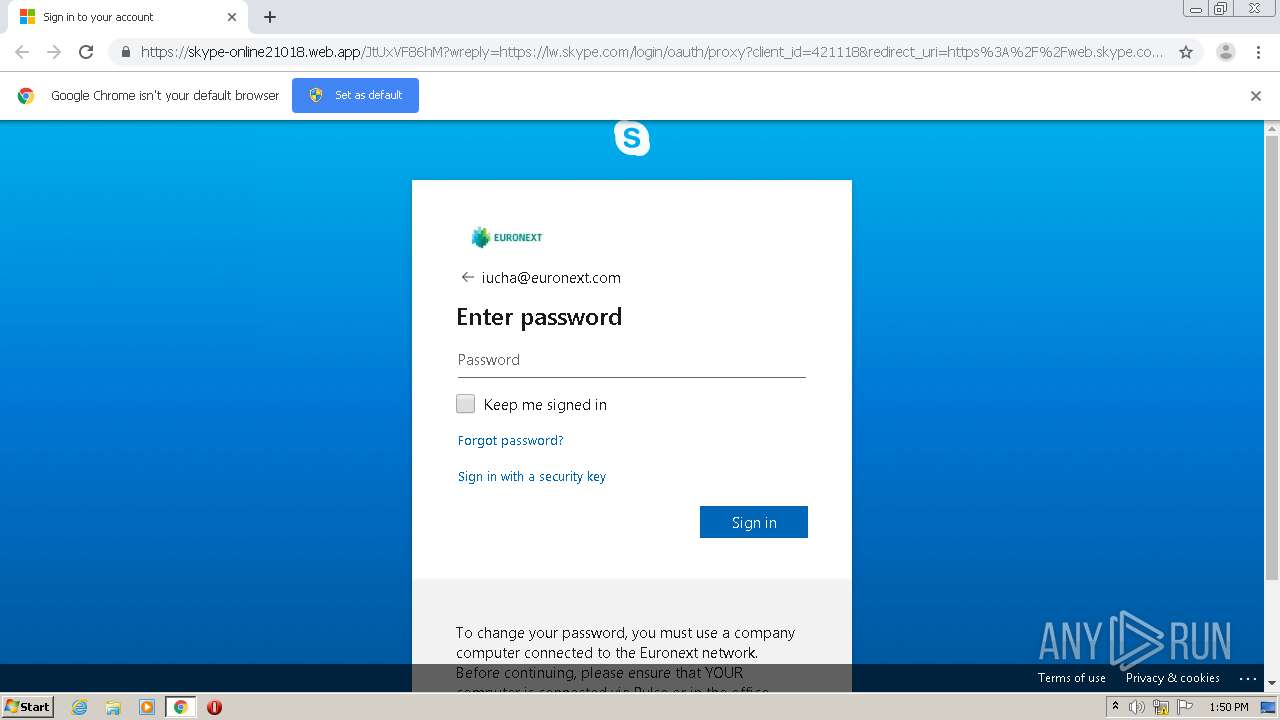
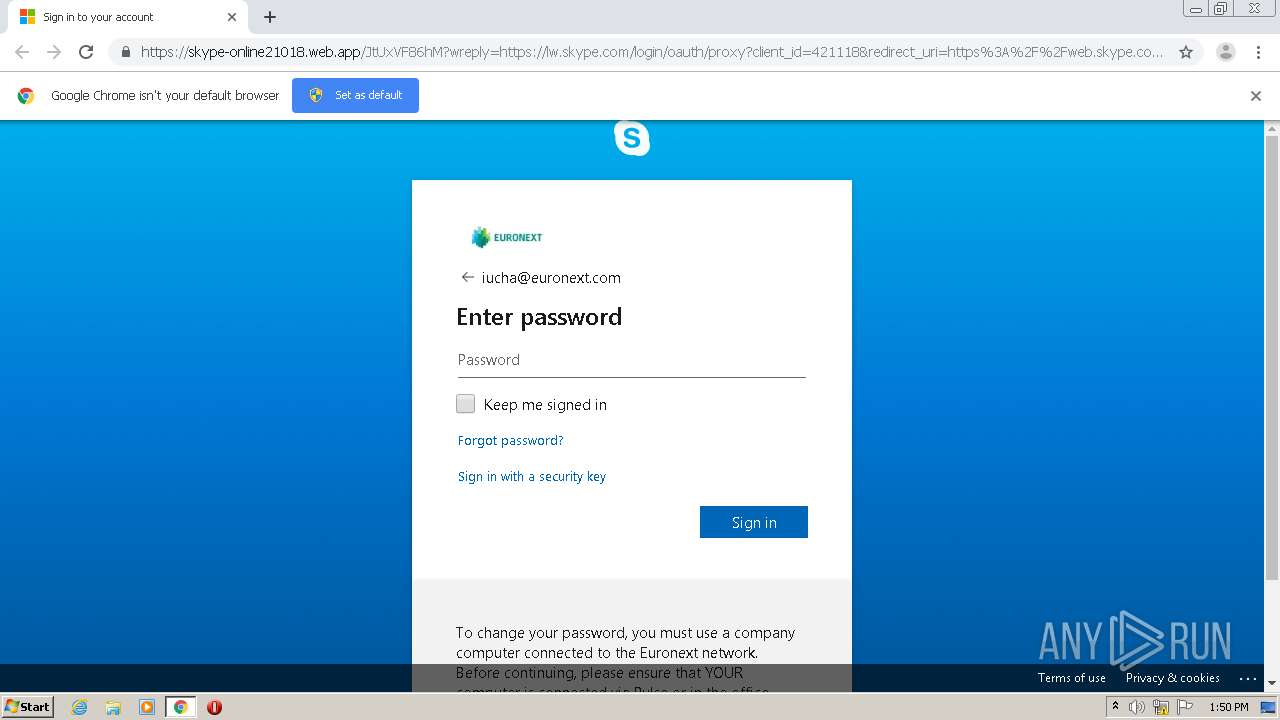
| URL: | https://4b5t453.imbervoice.com/43eb5t45307074?bdm=aXVjaGFAZXVyb25leHQuY29t&st=1&cl=2&lst=1&Iucha&euronext&aXVjaGFAZXVyb25leHQuY29tIucha&euronextaXVjaGFAZXVyb25leHQuY29t&Iucha&euronext&aXVjaGFAZXVyb25leHQuY29tIucha&euronextaXVjaGFAZXVyb25leHQuY29t&Iucha&euronext&aXVjaGFAZXVyb25leHQuY29tIucha&euronextaXVjaGFAZXVyb25leHQuY29t |
| Full analysis: | https://app.any.run/tasks/b631a9b6-f934-439c-a4b2-d082440cab0f |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 12:49:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B33D7E93194E8D79608BD25FD2654D9D |
| SHA1: | 55288AFEB09918EAA909E10C9CA8E3B1040C0C79 |
| SHA256: | 098AEB36B17657FCDB322367DBE9FA8F310C1C8C71E1DC2B21959881C01F3341 |
| SSDEEP: | 6:2byJ4qzq5n5DGLI295hpRzq5cI295hpRzq5cI295hpRzq5g:2a4lIIwhpRzKcIwhpRzKcIwhpRzKg |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2472)
- chrome.exe (PID: 1796)
Application launched itself
- chrome.exe (PID: 2472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5598430634528194385,17610400112902361332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8464074567861587212 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,5598430634528194385,17610400112902361332,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4184740451648915299 --mojo-platform-channel-handle=3204 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5598430634528194385,17610400112902361332,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6657995090602980707 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c57a9d0,0x6c57a9e0,0x6c57a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,5598430634528194385,17610400112902361332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3770223311198104696 --mojo-platform-channel-handle=1504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,5598430634528194385,17610400112902361332,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2423551152541564414 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,5598430634528194385,17610400112902361332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14266749036159174415 --mojo-platform-channel-handle=2852 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,5598430634528194385,17610400112902361332,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14045317500703120545 --mojo-platform-channel-handle=2004 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,5598430634528194385,17610400112902361332,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15116681073806143587 --mojo-platform-channel-handle=3496 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://4b5t453.imbervoice.com/43eb5t45307074?bdm=aXVjaGFAZXVyb25leHQuY29t&st=1&cl=2&lst=1&Iucha&euronext&aXVjaGFAZXVyb25leHQuY29tIucha&euronextaXVjaGFAZXVyb25leHQuY29t&Iucha&euronext&aXVjaGFAZXVyb25leHQuY29tIucha&euronextaXVjaGFAZXVyb25leHQuY29t&Iucha&euronext&aXVjaGFAZXVyb25leHQuY29tIucha&euronextaXVjaGFAZXVyb25leHQuY29t" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
580
Read events
515
Write events
61
Delete events
4
Modification events
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2472-13247671796612750 |
Value: 259 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
13
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8EDCF5-9A8.pma | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d0f28965-efc9-4b7b-92c3-39a8ba305805.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF2d429b.TMP | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
25
DNS requests
13
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1796 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 45.12.32.188:443 | 4b5t453.imbervoice.com | — | — | unknown |
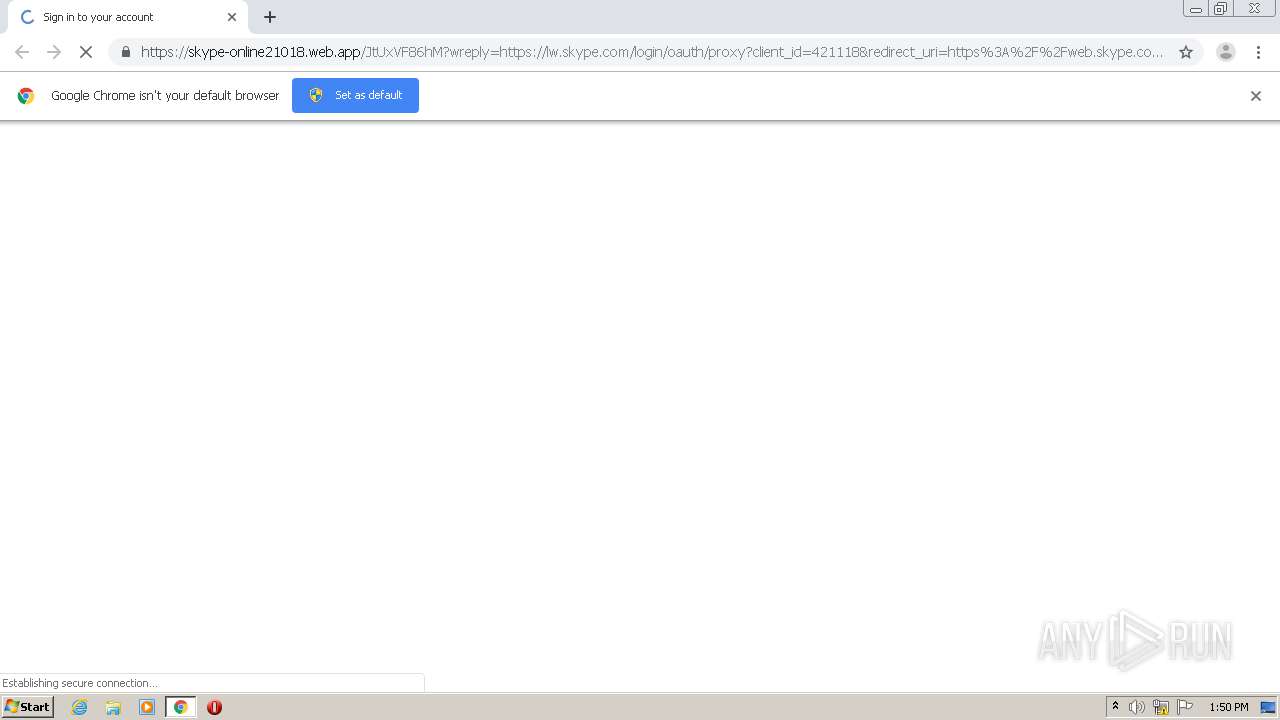
1796 | chrome.exe | 151.101.65.195:443 | skype-online21018.web.app | Fastly | US | malicious |
1796 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
1796 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 151.101.1.195:443 | skype-online21018.web.app | Fastly | US | malicious |
1796 | chrome.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
1796 | chrome.exe | 23.62.132.180:443 | secure.aadcdn.microsoftonline-p.com | Akamai Technologies, Inc. | NL | whitelisted |
1796 | chrome.exe | 185.212.129.195:443 | jgmfhdgthrh4y546uy7jret.duckdns.org | Virtual Trade Ltd | NL | malicious |
1796 | chrome.exe | 192.229.221.185:443 | logincdn.msauth.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
4b5t453.imbervoice.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
skype-online21018.web.app |
| malicious |
ssl.gstatic.com |
| whitelisted |
code.jquery.com |
| whitelisted |
jgmfhdgthrh4y546uy7jret.duckdns.org |
| malicious |
secure.aadcdn.microsoftonline-p.com |
| whitelisted |
logincdn.msauth.net |
| malicious |
bck-aqswdefrgt.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |