| download: | t.exe |
| Full analysis: | https://app.any.run/tasks/f6b2dfab-c193-480e-9fcd-acbbfef5065d |
| Verdict: | Malicious activity |
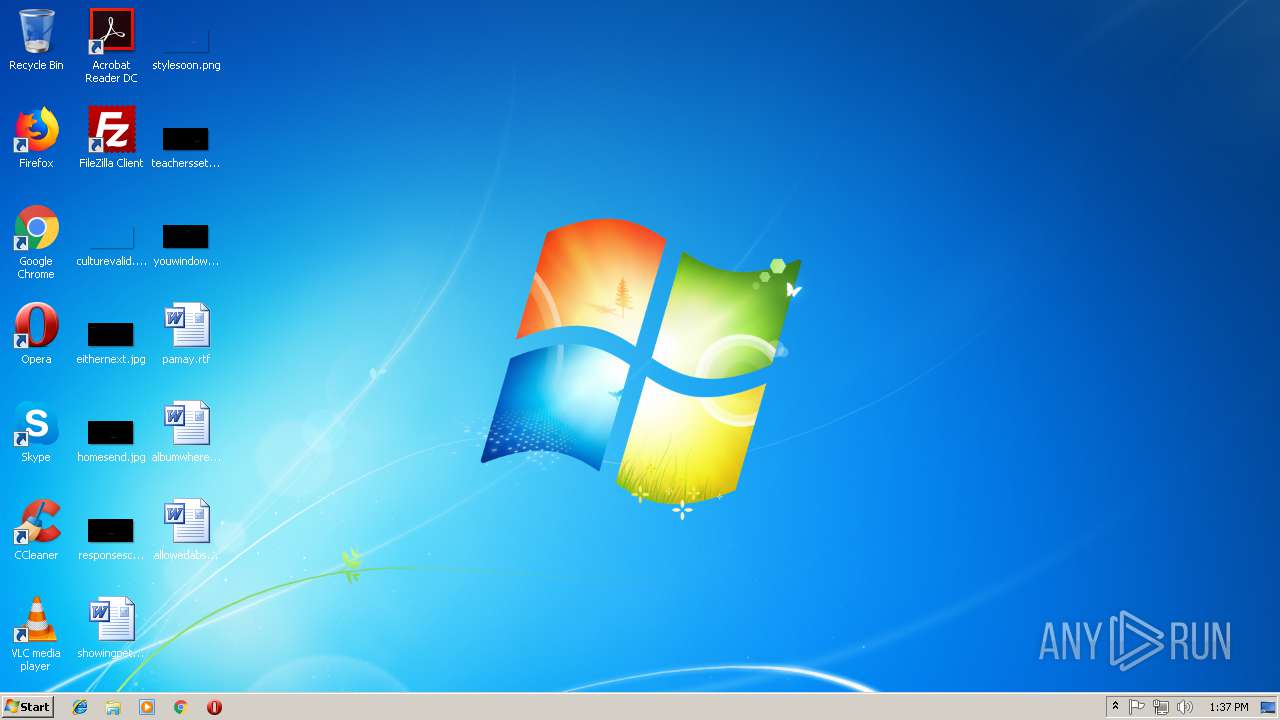
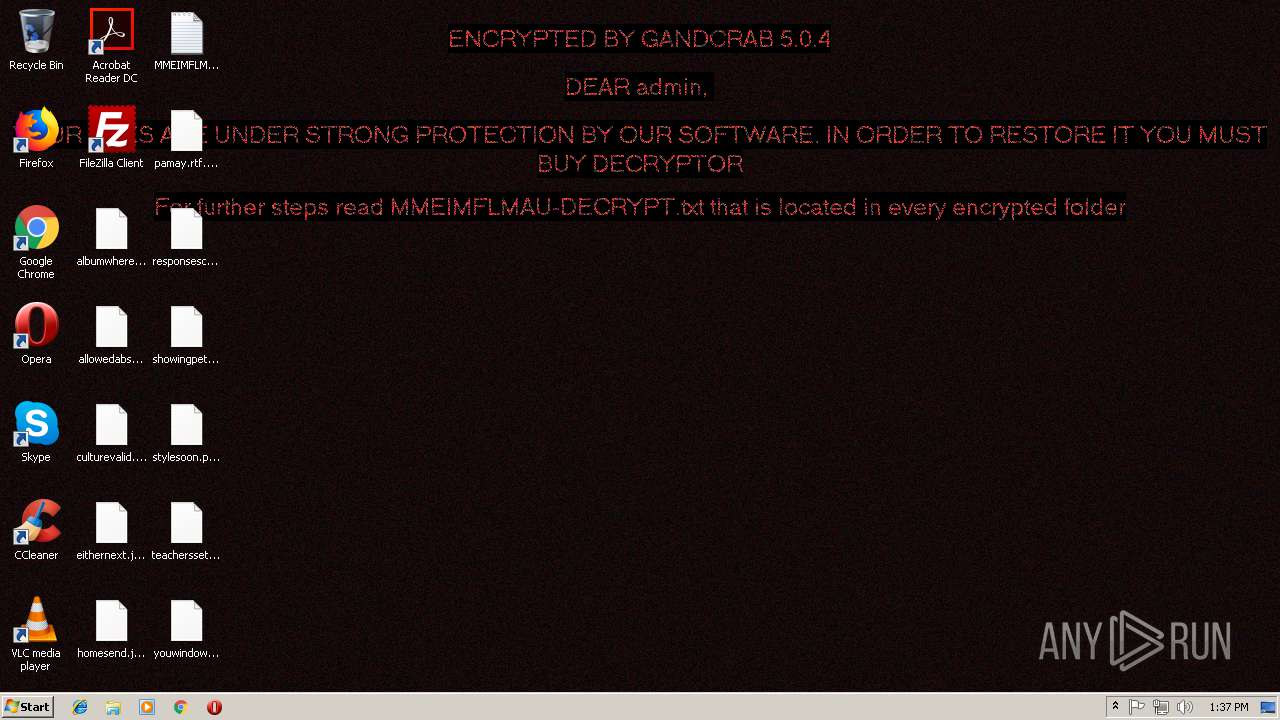
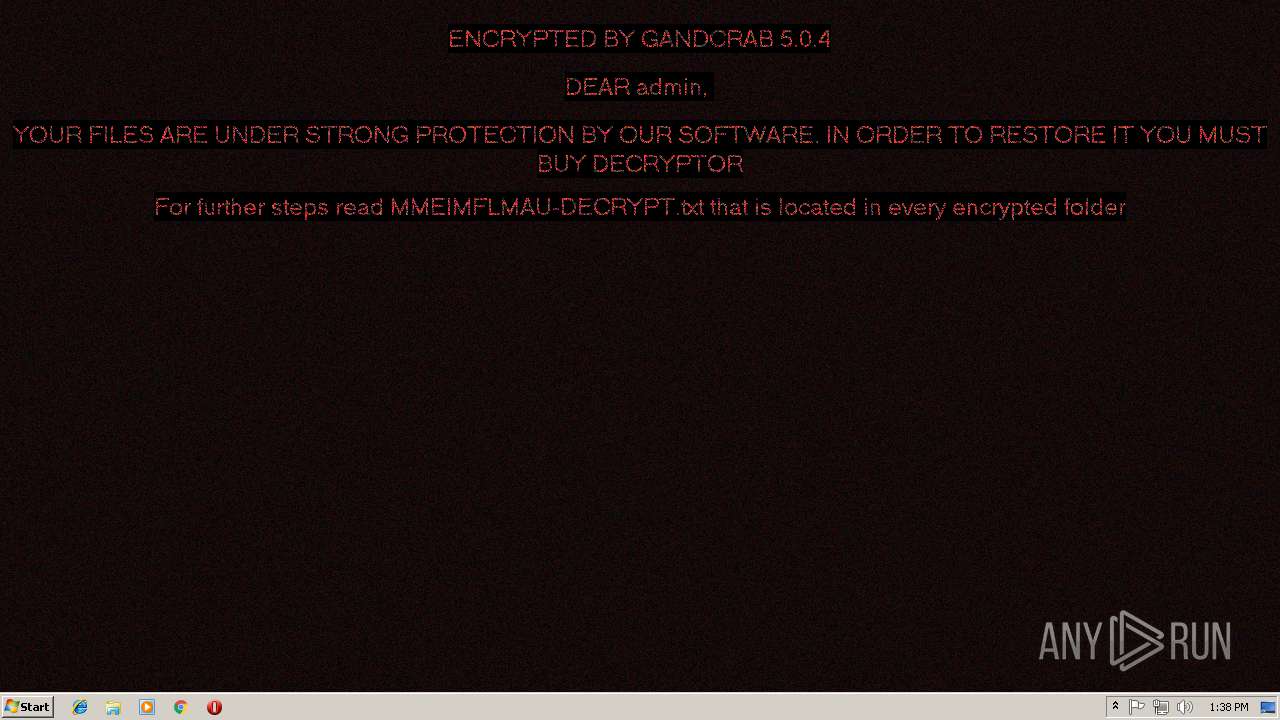
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | November 14, 2018, 13:37:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DA66CBC9AE879173F9E38D51A2CFFDB8 |
| SHA1: | CE651B549E945FAB1FFBCED06C671C8F050B5018 |
| SHA256: | 098AAD386B0F549CEFDDF2001DBA9F31F40D88A3618CD3A8D5589B4B0B467342 |
| SSDEEP: | 1536:JLMVCWvZ8URtqOz3d+1Qs6H9Mk2e3E2avMWC3yMgYxf6+okbdWsWjcdpECaIxWzX:VM9ntZ3s1QJdnU2SQdf64ZZSCaIxWec |
MALICIOUS
GandCrab keys found
- t.exe (PID: 3728)
Connects to CnC server
- t.exe (PID: 3728)
Actions looks like stealing of personal data
- t.exe (PID: 3728)
Writes file to Word startup folder
- t.exe (PID: 3728)
Deletes shadow copies
- t.exe (PID: 3728)
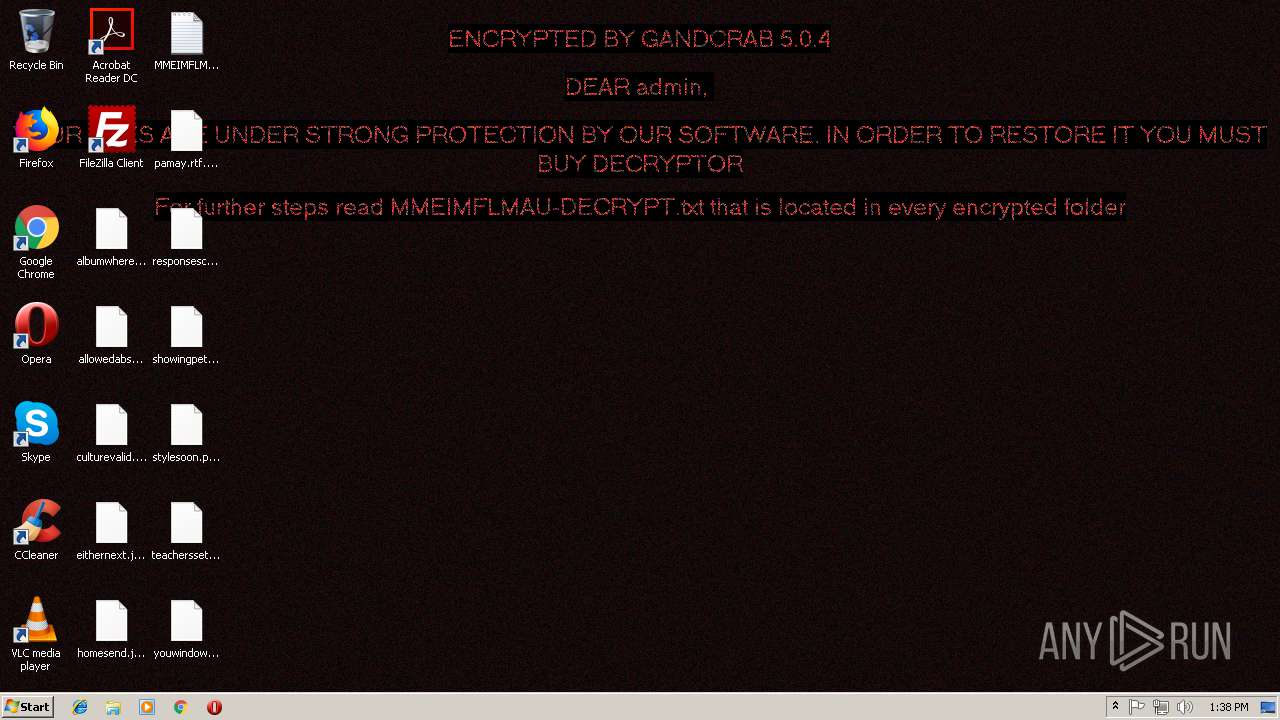
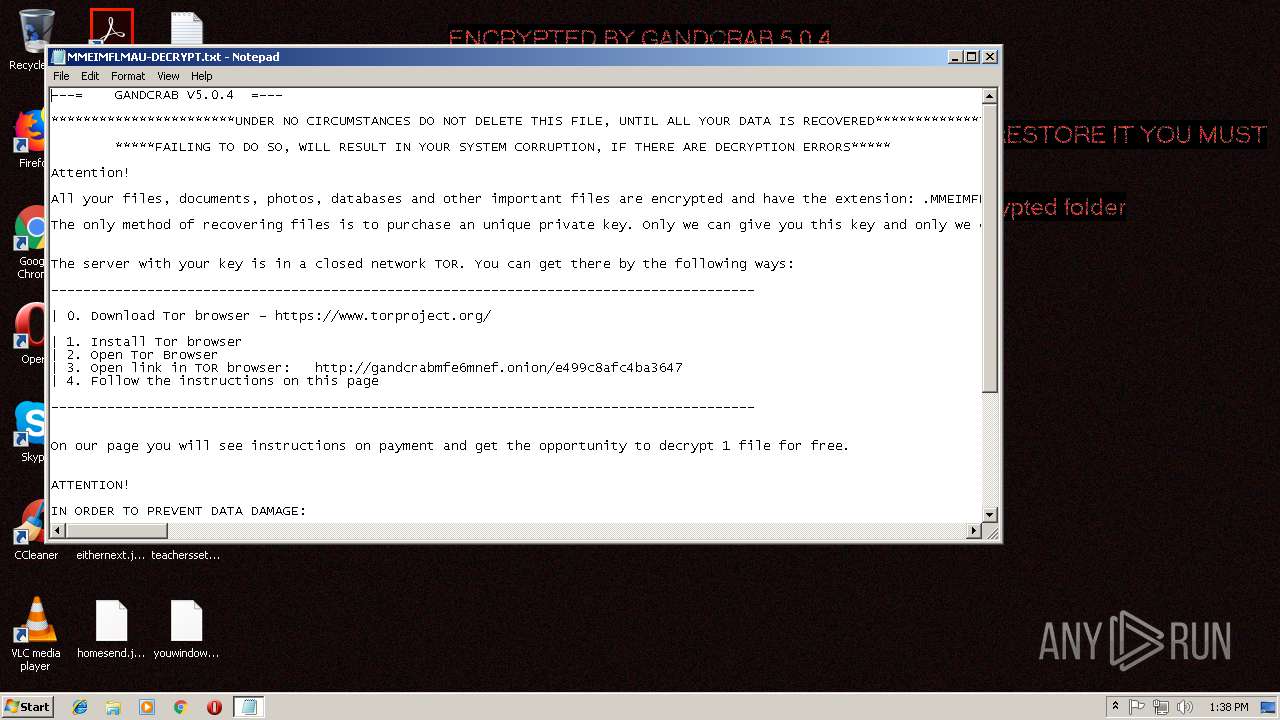
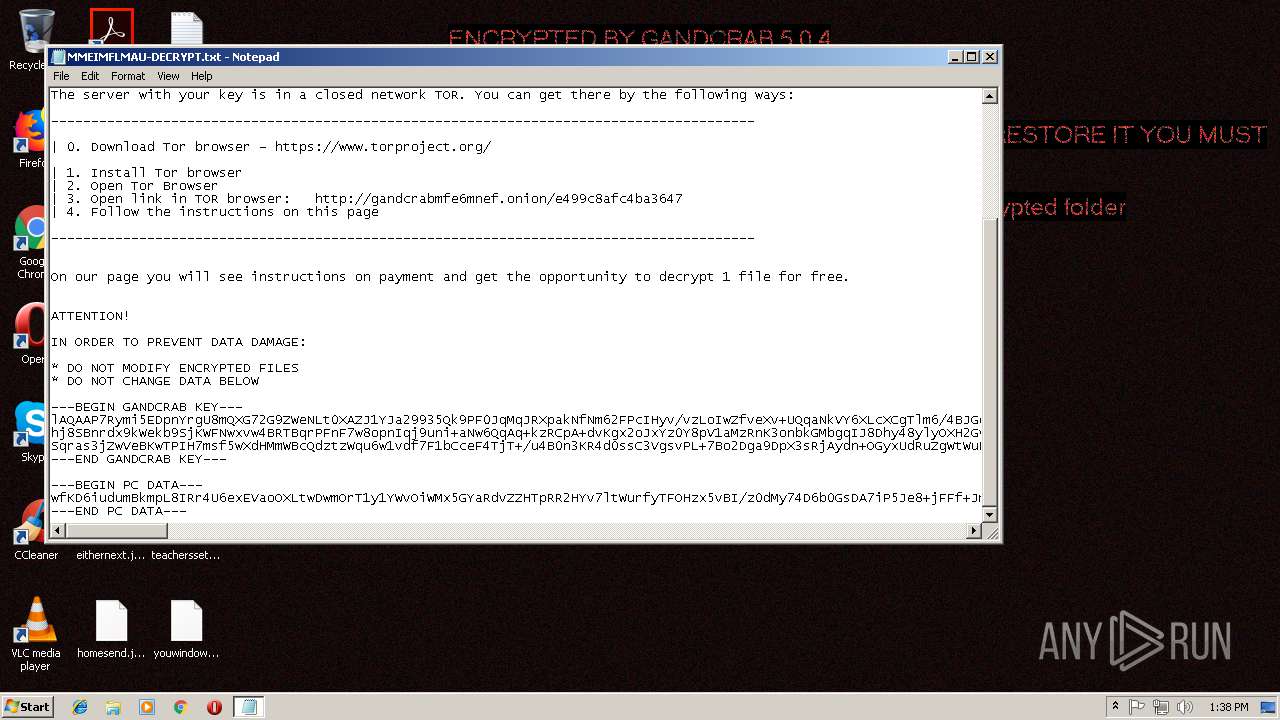
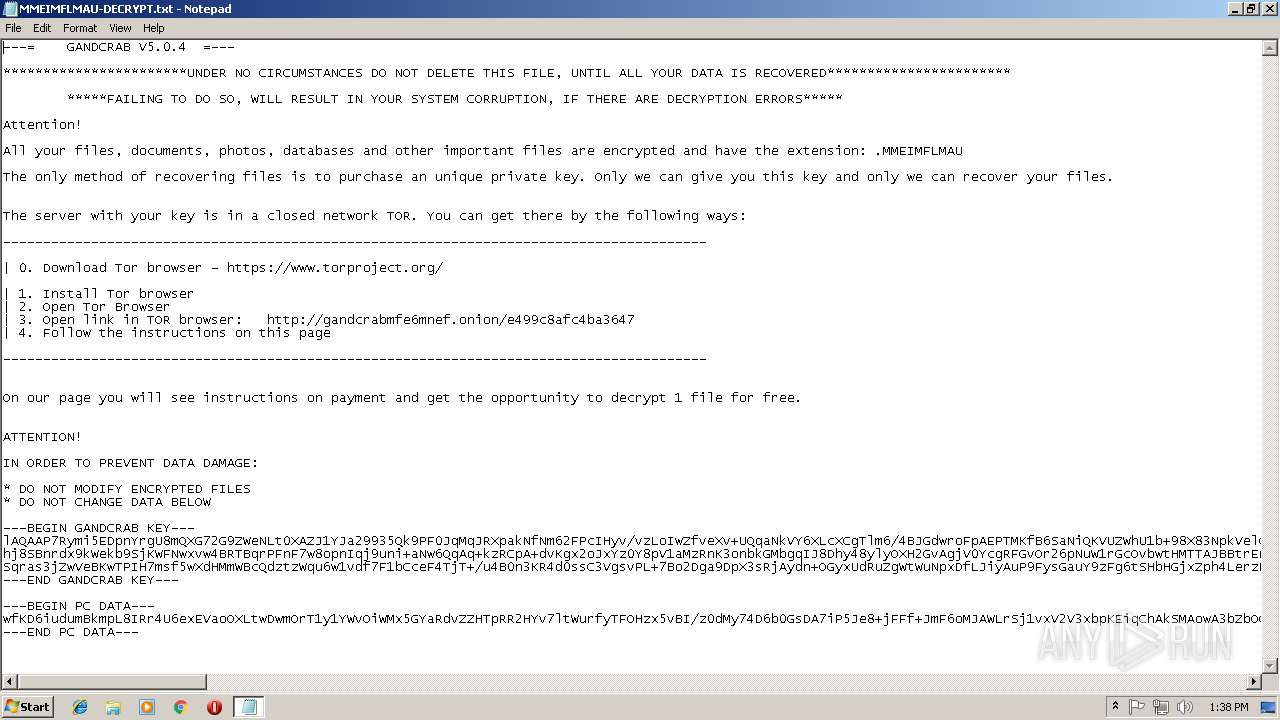
Dropped file may contain instructions of ransomware
- t.exe (PID: 3728)
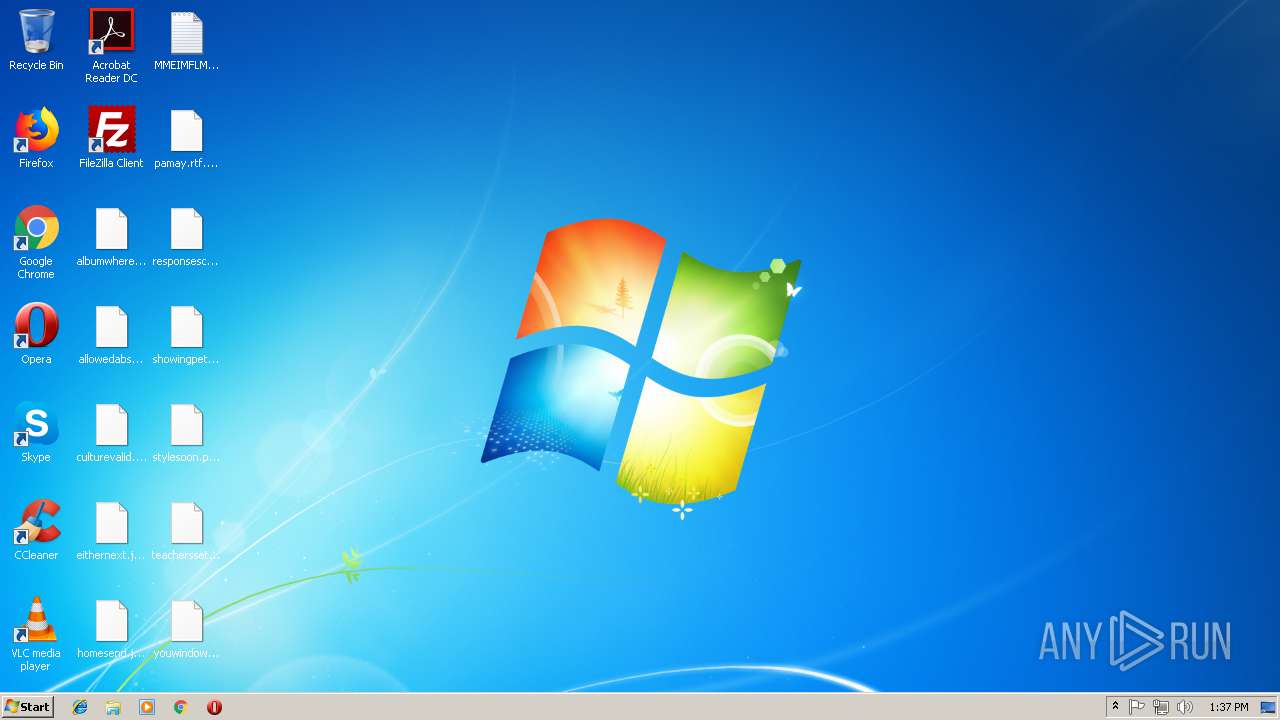
Renames files like Ransomware
- t.exe (PID: 3728)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- t.exe (PID: 3728)
Creates files like Ransomware instruction
- t.exe (PID: 3728)
Creates files in the user directory
- t.exe (PID: 3728)
INFO
Dropped object may contain TOR URL's
- t.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:26 10:47:08+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 80896 |
| InitializedDataSize: | 68096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6229 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Oct-2018 08:47:08 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Oct-2018 08:47:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013BE4 | 0x00013C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58693 |
.rdata | 0x00015000 | 0x00006B46 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59744 |
.data | 0x0001C000 | 0x000087F4 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.15553 |
.rsrc | 0x00025000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7123 |
.reloc | 0x00026000 | 0x000013A8 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64868 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
ole32.dll |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2824 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\MMEIMFLMAU-DECRYPT.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3588 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | t.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\t.exe" | C:\Users\admin\AppData\Local\Temp\t.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
135
Read events
104
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3728) t.exe | Key: | HKEY_CURRENT_USER\Software\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E006D006D00650069006D0066006C006D00610075000000 | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A400005253413100080000010001008FEFF657DC5F30E330A4D4BDC42CB5ED7BC0FAFD08080D16BC942B58671C9BE97CD529CCDF93FD82A29225554D60E5B7EB35EE5A8905A33798298E07075A63DC2F2076A8EE7EA4F064A1DEC2B4CDA92CE859F3DA669276D66AEAFCB4D99DEA897F78753C5F656571001EE878AB305212D77578AA6B695674E48A4C19BA4E57160183A89D334C2D6C99F4D0A963149F46D3314030FA25FB84155CD33B2E642FC44DEA69D9296F3E41CDDCB2CE6F8746B86428E02B4E997C6DF5275A14EC242691646A67E7DDB8438F90E870B70EBA7FC488DDEF109B2769EB9F2F2EC15B3F7E94374244C35D1F5A88A7E5E9ACFAEF53DAA8DCBCF59D65CAAEC5E20DFE9CC4A8AD | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | private |
Value: 94040000FED1CA68B9103A6762B814F264171BBD86F5959E34BB745C0649D5825ADBDF77E5093D3C5D09A8CA89457A5A90D7CD9BAD853DC207CAFFEFCCBA08C197EF797BFE510A9A364558E972DC5C2813966EBFE01246770AE81690043D330A7C1E9268D8902955195A15356FEF7C5FCDCDA6455E94EF69CA527824A9403F5EE3B547B53AA8F9CFE5003478323F2A95D1A2F150E18D3BCAE956AF94CE199BC2B8B8753EE572591460FE25C99D880AAD84E2700C6AE232588B3EC630B80C46093D5C1EDFAC93D930F6C415EA5825F4C902B86EEF4D0D1875747BC6F90F1D46ED55869A30F06A6E447AF55B3E410658B98448BD16BD9CB296E6FA3B87449B591871E8B174E632E571C976F670618A30B4BCF4B3742072D03EB3AEEFFA5B413FDF35AC553C6CF9DBFFD99303A040A76862F0CB084B32B2807C5FCA1929AA03E309C755437D1D32B893267F67755C301E93E60BF29EAB52950FC4B7DFAC7080EDA493939058CF5EB7E1590823FA93F100F4346AFF4537B9DF82E3623290EAC2AFF8D39C277765F5AF90D37CD75F979B303B12D776896B0D0F17C092C882503AFC10FD668C3205C0C7B1925B71F8B09B2F77FD3E1BF7ADF3CA642EE2D36B53E7660C277D8E2CC7C050B531BC67BE2A0C576DFE5D4F5E1AFF607C5C924EC0769E9D70E10324B818F4265B7FF403863F9352F1131285598A7E9C988FADF0C6AC0C8EAE38A1966F474542D527A144C6EF37DEDB5301A9D11353A3200F6707674D9D6CABB9E186E6E3B8F1A81639E4865D474B3E049D8743796FAA05C9F9111B36CA5C4EA0CB781602BFBBDE9FD1094662864A6B489C7C5645A5495E2F308D15F388B1183416F4205B14CE7B2D4277140BFC69B4560E2864265B0F95D69782067D73084EC33A19F2E2D6D2CD030167C943492DC11BF88637B68BAF06470B5571540620B15AD25C557DBF3EA830FBCC4258EBFB885A0C54A103AEDA131EFB2D0B63DA73F6CCE58A7C54368954267816A59C808FBD4F6B463B49F6AD53572E6A11E9023DDD816C1A0D8D85A1EA2CF256E620EDC37B92B86D3212A7A1A433F8EF389EEA5EB5863F12067ADDC7D9167A46FD4A329614DC31BF0E0145306AACF16717BC3CA299C8AA3F6E9E2F9A370E90A80ABE933442A40F9DBCA831DA8271633D18F2957568CCD19CADE89DB90631B82A209F03872E3CCA5C8E5C7D86BC082357461C811146BCEAF6EA936E5B5AC670EBDBC2D1CC4D3009041B6B12B13C15F0E1196B81D97559C964166A755C4BD61BEC031620F1F7B6C92B99605FC450567F10ADDC3E1DBB1EF63258469963C4DB35765CFA61A3F09C02B204B8E5054211C29284F25CC8D79CF347DFF7DFDBEB1FFD47BF69D74BFBD73497F824D3E68819CAE6E342E9A690C9102C587C2C758B04D895DAEADBF06F39108FC3F9938614E915EE8E165D906B12FD904D88F1E6FCE6DD297EC5ACF4D223911347C89B20B10B735EF6543E90FE5C1B63813E9B22A55BC76BB858EA737004C284C456D3018A4B866E70D48D341E1BA16157D77C37000F1DA4DDDBC392DC618237E17BB961BCCC01451D948F6665777A800782F7F6E545A57B654C9A09445F9C94F3681858F4B3F23328059E7DAC5360049699C8372A7A069F1C45B07B2B5578DB3007D2F9A91ADFCDEF529308AB1C076BC032F5A583201936527AA57C77EB6FAB1FC3AA08A48BD7BEDBFD925D088C120F8B2BEE0D1C96E977C45EB6803A7286E1BBE9AE109C99F3DDF961D8ADDFE611650508CC6DA595684648D2C6F3308DBEA678D2512AAC7E4690BFCA167081CD87F0667565652DB917F563E32CF804708BA1DF5489F0D7D3D3FEDE9DF1A73C9800E9C30B048D08F8E4603FEAB509DE6668C4AB04CC9DC2EE10426AD1A702636674AE68965561224F41F8DAE4A5BBFD42CCD9DE0D36C97EC65C7FCB52F5BB1535E933FB2D09D7C010D321DF5393F72F34AD9E592B93411741F022B27D477A1CAFC8EEC64697ACC8D0AAC2C9B865275106C26E089AC5100B376BE31ACCCDDCDBB08794EE365F5D269BEF4915AAF2663DACE9231220B34D7811A5C9C0AE8002B29944F4F0AC2852B9D18954F07349CED1B4B470AA3E6C2E55B5823BD427D476C25EB95F07B0F5120CA5B698BAA0C1C1F42BB871AF47296B34988850D105BFE2D74AAADAB378D9C157812B04CF207EE6B1FE705DD1CC99605C41DCEDCD6AAEEB0D6F75FEC5D5B09C785E138D3FBFBB80749F7291E1DD2CB02DD582CBCF2FEEC1A360E06BD0E95F7B118C0C9D9FE386CB151D46E6605AD5AE369C437CB262C80B8FF45CAC19AB98F73160EAD4876C71A3C59A61E0B7ABCCD5DB2184520C4CC81A170EDC94C119C4D3A66B92623262A674C6800D426593668BEB | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\t_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\t_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\t_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\t_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3728) t.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\t_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
273
Text files
204
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | t.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\MMEIMFLMAU-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\Users\admin\MMEIMFLMAU-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\Users\admin\.oracle_jre_usage\MMEIMFLMAU-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3728 | t.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.mmeimflmau | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
5
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3728 | t.exe | GET | — | 136.243.13.215:80 | http://www.holzbock.biz/ | DE | — | — | suspicious |
3728 | t.exe | GET | — | 138.201.162.99:80 | http://www.fliptray.biz/ | DE | — | — | malicious |
3728 | t.exe | GET | 200 | 217.26.53.161:80 | http://www.haargenau.biz/ | CH | html | 13.3 Kb | malicious |
3728 | t.exe | POST | 510 | 136.243.13.215:80 | http://www.holzbock.biz/uploads/imgs/thamru.bmp | DE | html | 740 b | suspicious |
3728 | t.exe | POST | 404 | 74.220.215.73:80 | http://www.bizziniinfissi.com/includes/pictures/zumehe.gif | US | html | 2.61 Kb | malicious |
3728 | t.exe | POST | — | 217.26.53.161:80 | http://www.haargenau.biz/data/graphic/eskethmo.png | CH | — | — | malicious |
3728 | t.exe | GET | 200 | 74.220.215.73:80 | http://www.bizziniinfissi.com/ | US | html | 6.96 Kb | malicious |
3728 | t.exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3728 | t.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3728 | t.exe | 78.46.77.98:443 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3728 | t.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
3728 | t.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
3728 | t.exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
3728 | t.exe | 138.201.162.99:80 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3728 | t.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
3728 | t.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3728 | t.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
3728 | t.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3728 | t.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |