| File name: | ransomware.exe |
| Full analysis: | https://app.any.run/tasks/1722f215-1bde-4d12-bd8b-414fff8ca5a4 |
| Verdict: | Malicious activity |
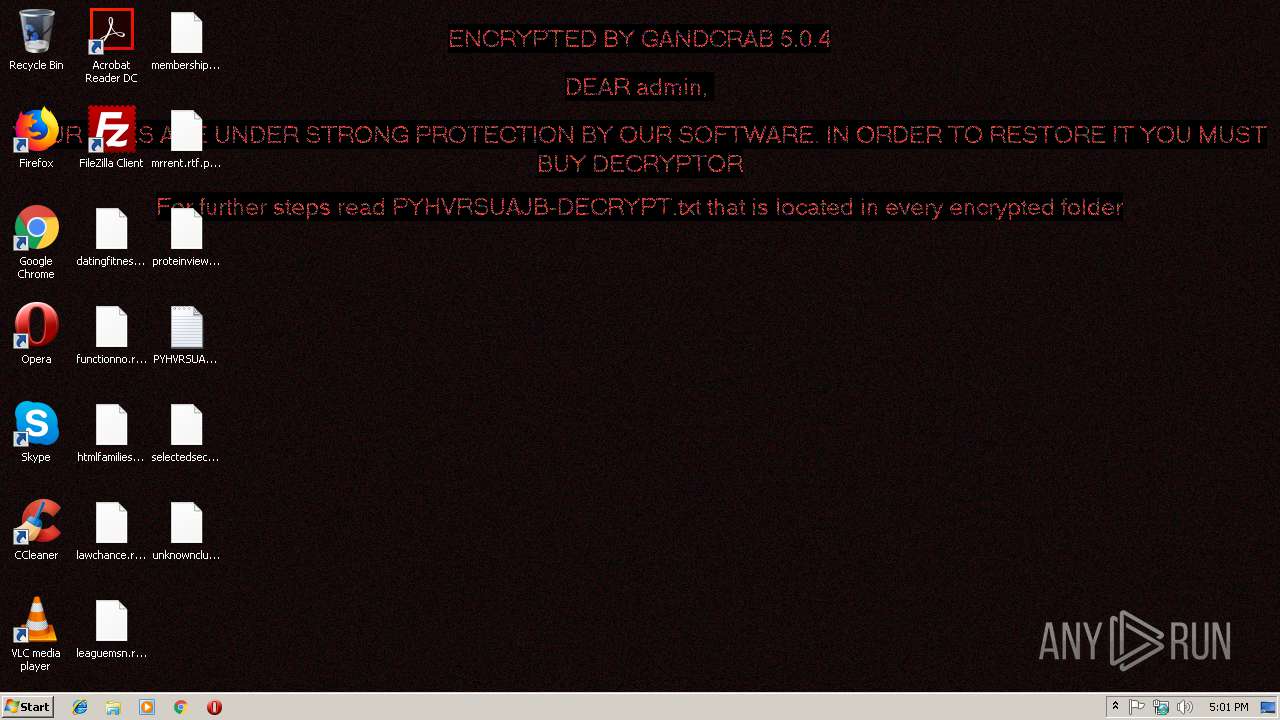
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 22, 2019, 17:00:52 |
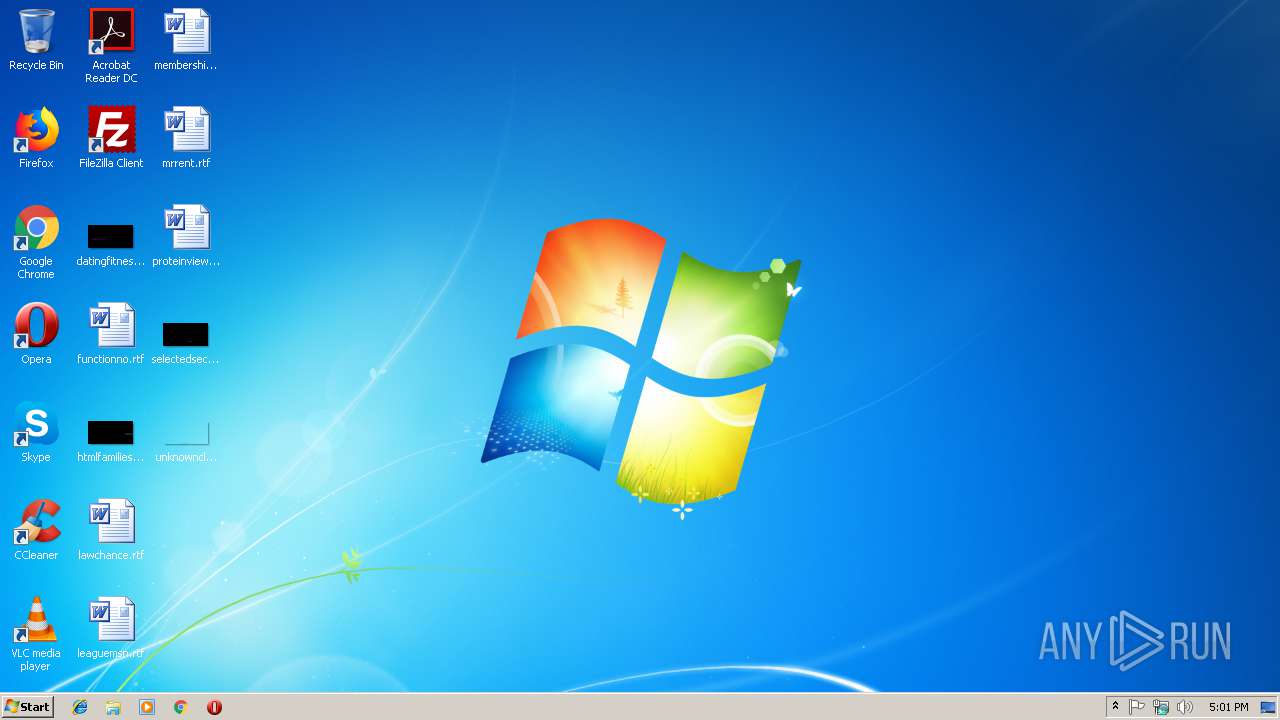
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DA66CBC9AE879173F9E38D51A2CFFDB8 |
| SHA1: | CE651B549E945FAB1FFBCED06C671C8F050B5018 |
| SHA256: | 098AAD386B0F549CEFDDF2001DBA9F31F40D88A3618CD3A8D5589B4B0B467342 |
| SSDEEP: | 1536:JLMVCWvZ8URtqOz3d+1Qs6H9Mk2e3E2avMWC3yMgYxf6+okbdWsWjcdpECaIxWzX:VM9ntZ3s1QJdnU2SQdf64ZZSCaIxWec |
MALICIOUS
Writes file to Word startup folder
- ransomware.exe (PID: 3104)
GandCrab keys found
- ransomware.exe (PID: 3104)
Actions looks like stealing of personal data
- ransomware.exe (PID: 3104)
Renames files like Ransomware
- ransomware.exe (PID: 3104)
Dropped file may contain instructions of ransomware
- ransomware.exe (PID: 3104)
Deletes shadow copies
- ransomware.exe (PID: 3104)
Connects to CnC server
- ransomware.exe (PID: 3104)
SUSPICIOUS
Creates files like Ransomware instruction
- ransomware.exe (PID: 3104)
Reads the cookies of Mozilla Firefox
- ransomware.exe (PID: 3104)
Creates files in the user directory
- ransomware.exe (PID: 3104)
INFO
Dropped object may contain TOR URL's
- ransomware.exe (PID: 3104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:26 10:47:08+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 80896 |
| InitializedDataSize: | 68096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6229 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Oct-2018 08:47:08 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Oct-2018 08:47:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013BE4 | 0x00013C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58693 |
.rdata | 0x00015000 | 0x00006B46 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59744 |
.data | 0x0001C000 | 0x000087F4 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.15553 |
.rsrc | 0x00025000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7123 |
.reloc | 0x00026000 | 0x000013A8 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64868 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
ole32.dll |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3104 | "C:\Users\admin\AppData\Local\Temp\ransomware.exe" | C:\Users\admin\AppData\Local\Temp\ransomware.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3220 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | ransomware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
127
Read events
96
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E00700079006800760072007300750061006A0062000000 | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A400005253413100080000010001001138D16B1968377DCF6560F678F874E115441DE0D032AC760B9AF36517D3E720F1C9CFC6652D175EBB9621E50CB2AE948161E63FA99D7B37BCD50C7D5D1E3DEF61F1B5899D79D96F3E1487FF4BE415531E4C1ADC0854DD902C06785D14CDE6EAAD671D8C4D88D765112A9BDF3AB7BDFC1C432D34F18DEFBFABA77F51E6F3390F0B77D16DD37CD8F52D13755EC05AEEA93AE1865536A4DE2D8C7E459B8893A8A3078D518BE55EC95C8147F1A09073C633F383481F8532793C4BCFD32CC81AA5CE5B5CBB5F1FF3EE8DD6EA329F9CA590AC859DE278BDCC87915971055BCC0D536695A1336DB0D3538726C4AF384CB476CA0D5F856B37290ACD7D2F59BF96DEB5C5 | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | private |
Value: 94040000F7E4318ED84570980CD4D70D67A9AAF1F079991619B28940332D395368D30E4D689A08EC5B1BD2406351B5A0243AF5D2814BD6A1AAE6E7F3CF787C470A3C0225842753E202DBF9BABFF32602685A2E7C8B02A59020868811DCA6F5FE26AB28406B9321B99EDC01BDEAE57C6CB67847DCDA59277B08F85C80B6EA14D3514DA52F2AEB56AF9B3F886AB8A383BEF48833524A739A2E17A56794F2259AC00943E0E47D88B0372B1F00BEDC5E40AFD784387F9BF80CCCE08AB9E859E9625F380C9D3C6586838A53549D43C8989140449210A01B0C7EE605DA519AD02169C197A8D0C80F904200273AA3056D7AA53DBB4D916ACF3F624A8B495D31D54C56D9064E0C3D46FECA5FAD18731BAF6D8AD93F1CA698CD543AFB211910037394182B3A330B960A0BBDA2AE2E17155374747E8A94946E01173332926C144C8B43E8BDB0BDBF4C91D2FEDC441477303322ED4627CD1EEA2D443713B4D6B1010BF085465655D18861E7E4460105B2310ED0C7C8D7F32B8B110CA89CA12E28D406764BB686C956A0F22D7E8151E6C678677BFE6D8D1327F79F4DE9105F56CD127749169FA79E5FF38A35B1F332B4B6E87A8BB7BA8E2B5F02800306473A63FDA9CA2A6AFD6AA50FEA230C48AE3538C9FF16BBD155F9DB4747495EC33ECCF3FFBFDBB136D552F67AA334E45AD5EAA0B6502EF1ADD38E4186241047382A22875EEADFB14499CDBB9A04B73AAD9AE6400DF94C1BFF343BBDA97D375AD5D87F2331B36CB130E4D2900247BEA0458A5C47C5ED63F9C23C27B16A06427F689A8F623DB4EEB7884578A99013412AAB1255478BE7A40B2C1BB01EC670D7104441AB3E0FD28E9331F7BF499B3B3FC7FCF1C3D64DD2F5C35023EABC185F7E27022104964CB6AC432B7315C273B2E3175108275B85BFBCBD0ED6E5D85EBAD8FB3D3FAEB8293E331A3EE091097EE13805806F6DD21FB2186C4485604FD475CAB1D65BB14110A66841A9D6214929236A3B152E7E10E28FA756045D26E02B2A0F094ECD504633ED7052AE382107D7598664E07BB90DA4012AA7BB6303982968234C40F4E483D36D946183FAF09371FAD07D61A41F321AE731B5383F072A0D3042237D4A2607F66BAF8C098E6A9144EF82D4C1A466A10E2AB09BF8CE258D02CA41DFEA5BD0E9D20382EA2D5865A016391E7129136A033C2A0A11ADAF7F25C52E78FE30C94C4A6E25BF86EB60376A8320E55974C3DA942943DD037393D21F1657340C84C48C0AEB2C40F92F95F486ABF8B60F705E92D5CB2FD7C395A3697715E7C0ED1FF0D43618AB13A35E1BE49494A4A8C80845400FA9B8BEC89B01807CB79B0E9B0A57C842F40A22EEA9445ED262EB4F2E347E50843D7B6F1BD97F12C796A1C1ADC45C8B6682BB06C6ED262BCBBEBCCC9DE6E5095C3D6B9B4015B5FDB95A965F7C45F3BCE9409AAFE55B5A145D96C510E685D6FDA50F6B15C4CF61121E9D11D3FBAF9316068D7B823848383AEBEC4D88C52B8E5B203F4849C2C69D134086F83398811182FC1B74B360142F0821241149AA6769614749BBA7C3D313601DE5C7AD22700724B929F9C51DC5DAC0C8302A7A8FCD0AB7EC7F6E544D6CB49F945C0EDF4895AC13EB9C68420C99442F0CE031F2C37CB112FEA602E34C2B7687D915B692D33790BCD5EEA78B04040A032B058B15B0B47CC3B03DC274EAE6F4A39B45A67B5FCCB0224C16F715F24E5A9A9BA4EED89B707CF5DC2F50C10C8F27BD980A7DCC29863CDE8AAF06AF90C8008F77FE98538F1A4F2DF14AEFB9A5071180BDD81FA2A89B87A6BA303F3EE13B654641A1D8189024D32B9A5BC802D60F4637979DBAA014B5A1AF78FACE21D316AF3F922961E060070A08880E1F99CC2E831AFF0C83B130A690A2130C2FA363D0DA3039E9557336592D71FC67C7F5A3B2680BFEF77842C889646AE81080FDDC40512F5D964312B86D7124DE786C3AA654328976F08EBAD53508F581DEEA578589E52132AE9C61CC574B4384931AFC48F94DF888F8C57BF64285B6685EE03AB334F6801E728C0A73FF2497DEFA95612E6D11FF015361192EA5CF90DFA9CDAB54A53350CEF24D275E1ECCFCF1606248664C300072FA6D00D688BC8F1B6E0ACAF522FD0C9F46CEA4B7E46A902C850E6ADABC18BB599040A25942766E325CCAE020B09B90ED6B38498807B186412ECFC11C4BA2407D5AB3A7CFFBB262CEC0B6F0D0001673D9B1569D271374C21F1222255C0D09B7E05B8E7A642797C6539E00F950D4B6289265B7EE6538157A6AA3182BA11114DDBECD22FD8420FEE69DAE98CFB67D4EF7AC2BE021C46214B616570DB5374BE0DDB6F8C9AE3F87FF00F6A9EB48DB3EE2BB08101E43E1A6550423365071D16F46289C88895103EF0A | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ransomware_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ransomware_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ransomware_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ransomware_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3104) ransomware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ransomware_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
284
Text files
208
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3104 | ransomware.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\PYHVRSUAJB-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\AppData\Roaming\Adobe\PYHVRSUAJB-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata.pyhvrsuajb | binary | |
MD5:— | SHA256:— | |||
| 3104 | ransomware.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\PYHVRSUAJB-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
39
DNS requests
20
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3104 | ransomware.exe | GET | 301 | 83.138.82.107:80 | http://www.swisswellness.com/ | DE | — | — | whitelisted |
3104 | ransomware.exe | GET | 301 | 104.24.23.22:80 | http://www.belvedere-locarno.com/ | US | — | — | shared |
3104 | ransomware.exe | GET | 301 | 83.166.138.7:80 | http://www.whitepod.com/ | CH | — | — | whitelisted |
3104 | ransomware.exe | GET | — | 212.59.186.61:80 | http://www.hotelweisshorn.com/ | CH | — | — | malicious |
3104 | ransomware.exe | GET | 302 | 192.185.159.253:80 | http://www.pizcam.com/ | US | — | — | malicious |
3104 | ransomware.exe | GET | 301 | 80.244.187.247:80 | http://www.hotelfarinet.com/ | GB | — | — | malicious |
3104 | ransomware.exe | GET | — | 217.26.53.37:80 | http://www.hrk-ramoz.com/ | CH | — | — | malicious |
3104 | ransomware.exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
3104 | ransomware.exe | GET | 200 | 74.220.215.73:80 | http://www.bizziniinfissi.com/ | US | html | 6.96 Kb | malicious |
3104 | ransomware.exe | POST | 510 | 136.243.13.215:80 | http://www.holzbock.biz/data/pics/methsedath.jpg | DE | html | 740 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3104 | ransomware.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
3104 | ransomware.exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
3104 | ransomware.exe | 138.201.162.99:443 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
3104 | ransomware.exe | 78.46.77.98:443 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3104 | ransomware.exe | 192.185.159.253:80 | www.pizcam.com | CyrusOne LLC | US | malicious |
3104 | ransomware.exe | 83.138.82.107:80 | www.swisswellness.com | hostNET Medien GmbH | DE | suspicious |
3104 | ransomware.exe | 138.201.162.99:80 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
3104 | ransomware.exe | 192.185.159.253:443 | www.pizcam.com | CyrusOne LLC | US | malicious |
3104 | ransomware.exe | 83.138.82.107:443 | www.swisswellness.com | hostNET Medien GmbH | DE | suspicious |
3104 | ransomware.exe | 212.59.186.61:80 | www.hotelweisshorn.com | green.ch AG | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
www.hotelweisshorn.com |
| unknown |
www.whitepod.com |
| whitelisted |
www.hardrockhoteldavos.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3104 | ransomware.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
3104 | ransomware.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3104 | ransomware.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |
3104 | ransomware.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
3104 | ransomware.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3104 | ransomware.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |
3104 | ransomware.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
3104 | ransomware.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3104 | ransomware.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |
3104 | ransomware.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |