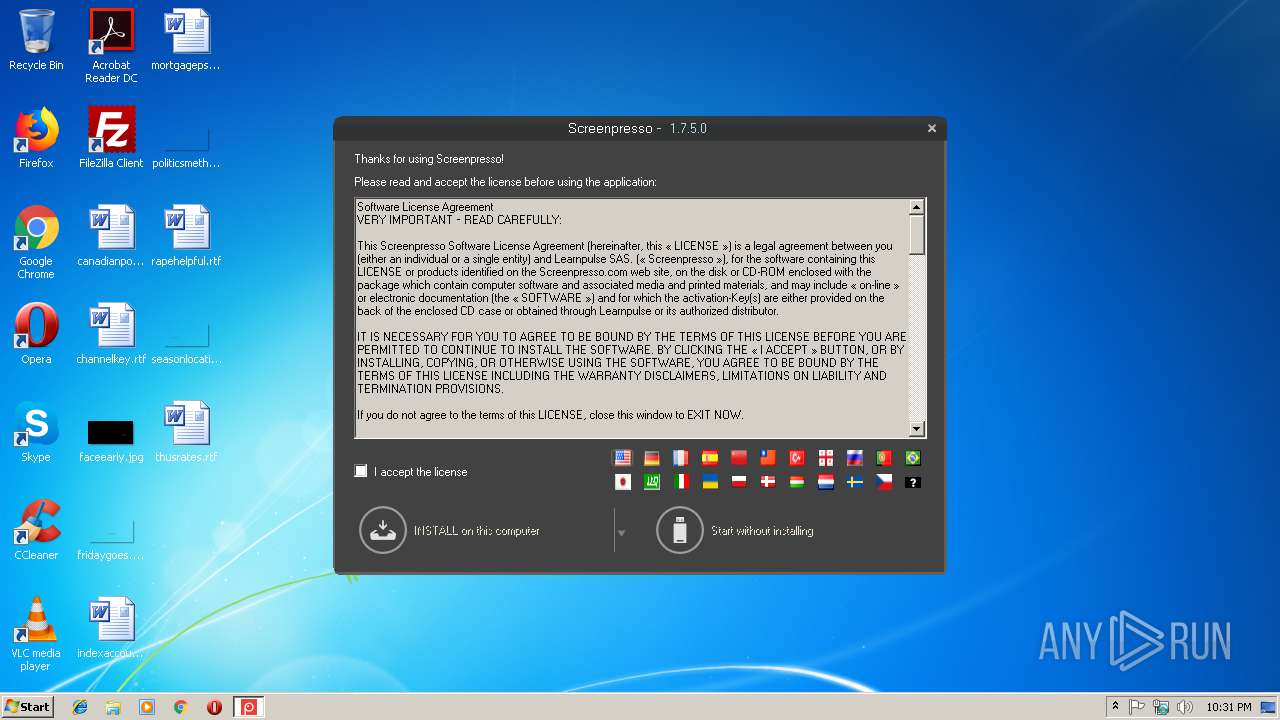
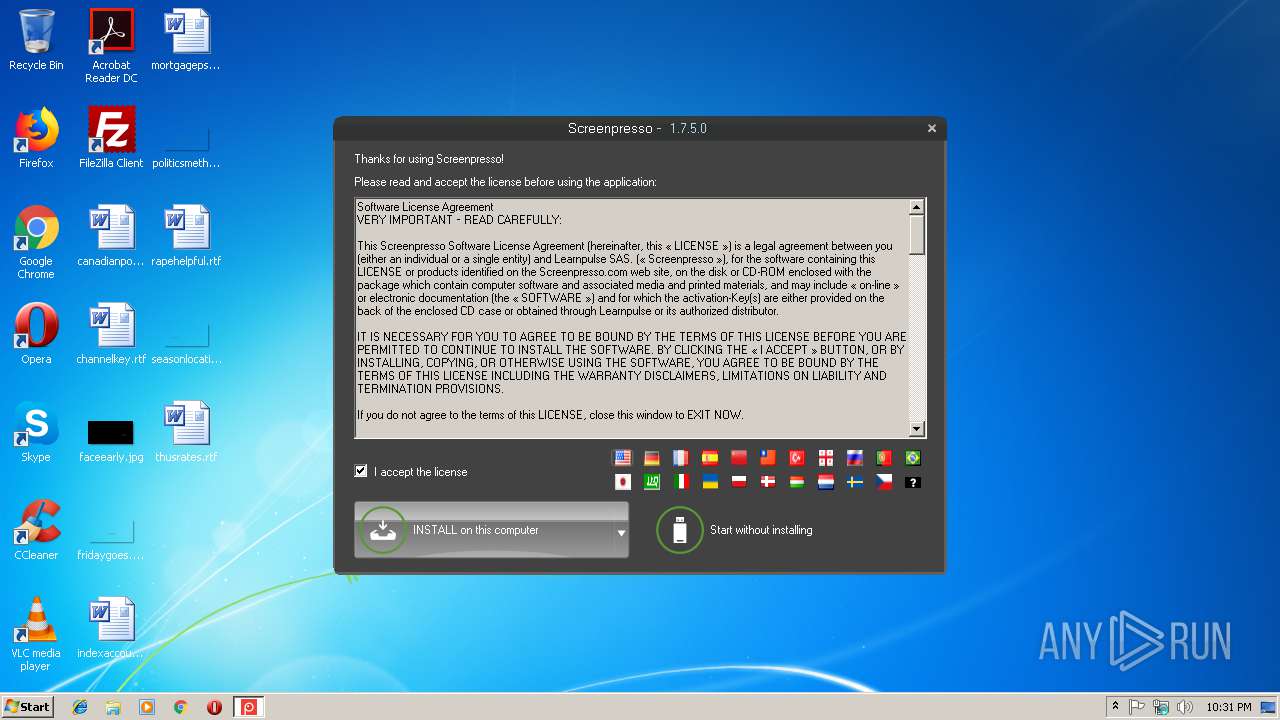
| File name: | Screenpresso.exe |
| Full analysis: | https://app.any.run/tasks/a65e4196-f535-4e69-9e31-0a9f8345b7a9 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2019, 22:30:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D26B6B1DAC08801DE525293CAD2E03E2 |
| SHA1: | 4E6C5B58E8F6E1897ED5D98202591345D0AD6A3E |
| SHA256: | 098392CA337FFFCF06E13ACFA931AB975F28268F054C2A77868560F2FCC826DA |
| SSDEEP: | 196608:TwBsQ+0d8/uhJZgeFC2Ncx0FXswgbAeYgk2yFi0FfTQ2uUnp:EkeFC2Ncxm5gbAeKlQ2Dp |
MALICIOUS
Changes the autorun value in the registry
- Screenpresso.exe (PID: 4092)
SUSPICIOUS
Modifies the open verb of a shell class
- Screenpresso.exe (PID: 4092)
Creates files in the user directory
- Screenpresso.exe (PID: 4092)
Executable content was dropped or overwritten
- Screenpresso.exe (PID: 4092)
Creates a software uninstall entry
- Screenpresso.exe (PID: 4092)
INFO
Dropped object may contain Bitcoin addresses
- Screenpresso.exe (PID: 4092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:15 18:35:53+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 12540416 |
| InitializedDataSize: | 12691456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbf786e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.5.0 |
| ProductVersionNumber: | 1.7.5.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Screen capture tool |
| CompanyName: | Learnpulse |
| FileDescription: | Screenpresso |
| FileVersion: | 1.7.5.0 |
| InternalName: | Screenpresso.exe |
| LegalCopyright: | Copyright © Learnpulse 2019 |
| OriginalFileName: | Screenpresso.exe |
| ProductName: | Screenpresso |
| ProductVersion: | 1.7.5.0 |
| AssemblyVersion: | 1.7.5.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jan-2019 17:35:53 |
| Debug artifacts: |
|
| Comments: | Screen capture tool |
| CompanyName: | Learnpulse |
| FileDescription: | Screenpresso |
| FileVersion: | 1.7.5.0 |
| InternalName: | Screenpresso.exe |
| LegalCopyright: | Copyright © Learnpulse 2019 |
| OriginalFilename: | Screenpresso.exe |
| ProductName: | Screenpresso |
| ProductVersion: | 1.7.5.0 |
| Assembly Version: | 1.7.5.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Jan-2019 17:35:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00BF5998 | 0x00BF5A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.96277 |
.rsrc | 0x00BF8000 | 0x00024DF0 | 0x00024E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.67521 |
.reloc | 0x00C1E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20044 | 2045 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 7.85823 | 7267 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.7086 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.78533 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.93589 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.82143 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.32302 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.5472 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.05029 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.99723 | 118 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
30
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4092 | "C:\Users\admin\AppData\Local\Temp\Screenpresso.exe" | C:\Users\admin\AppData\Local\Temp\Screenpresso.exe | explorer.exe | ||||||||||||
User: admin Company: Learnpulse Integrity Level: MEDIUM Description: Screenpresso Exit code: 0 Version: 1.7.5.0 Modules
| |||||||||||||||
Total events
439
Read events
397
Write events
42
Delete events
0
Modification events
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4092) Screenpresso.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Screenpresso_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
25
Suspicious files
1
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Roaming\Learnpulse\Screenpresso\settings.4092.xml | — | |
MD5:— | SHA256:— | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Roaming\Learnpulse\Screenpresso\settings.copy.xml | text | |
MD5:— | SHA256:— | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Roaming\LearnPulse\Screenpresso\fum.bin | binary | |
MD5:— | SHA256:— | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Screenpresso.lnk | lnk | |
MD5:— | SHA256:— | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Local\Learnpulse\Screenpresso\Screenpresso.exe | executable | |
MD5:— | SHA256:— | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Roaming\Learnpulse\Screenpresso\settings.xml | text | |
MD5:— | SHA256:— | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Local\Learnpulse\Screenpresso\ScreenpressoCapture.exe | executable | |
MD5:— | SHA256:— | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Local\Learnpulse\Screenpresso\References\Google.Apis.Auth.dll | executable | |
MD5:B3B34E55BF56AA150C14C371D77E47B3 | SHA256:B3B0AD91C2A4F1832D385CB105EAA532FE9121C0262FBE9673CCA7FE670B19F9 | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Local\Learnpulse\Screenpresso\ScreenpressoCodec.dll | executable | |
MD5:71F01FD1970303BBA7F5E80A24DEA8FB | SHA256:8D80CE82A4746233A2BB9D3EE64A11D7A34661C92AF3280151D2CC35FD557CF9 | |||
| 4092 | Screenpresso.exe | C:\Users\admin\AppData\Local\Learnpulse\Screenpresso\References\Google.Apis.dll | executable | |
MD5:012C9B842F2774D2A0D2200C273BD09F | SHA256:1D384837ECECBF7817A8C630F2D009F359D702CD24BB90099C58535D582FE7E7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4092 | Screenpresso.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
4092 | Screenpresso.exe | 213.186.33.17:443 | stats.screenpresso.com | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
stats.screenpresso.com |
| malicious |