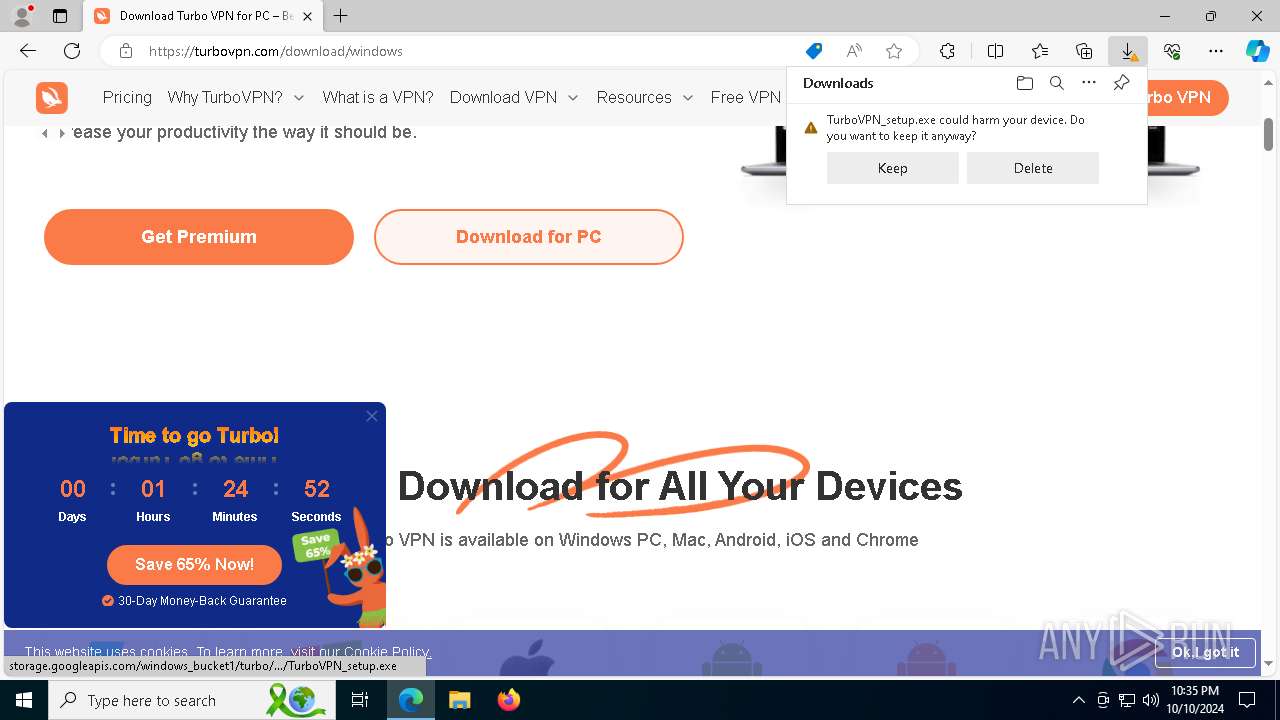
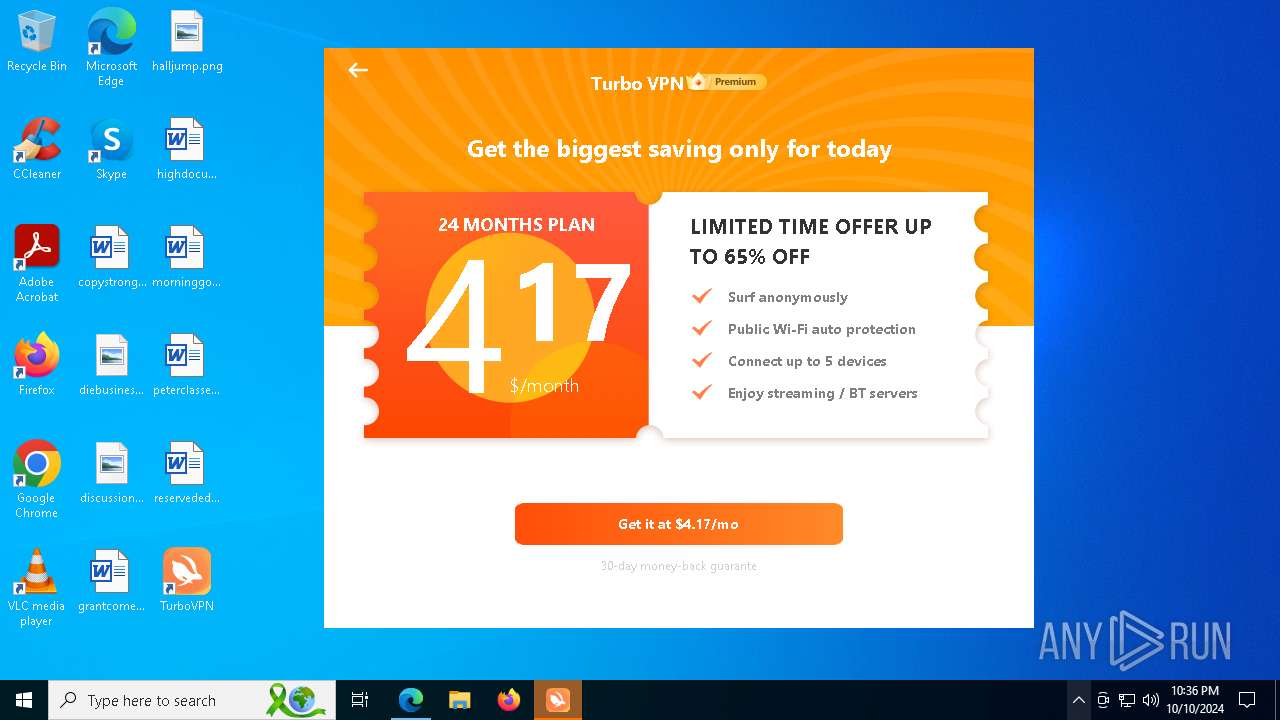
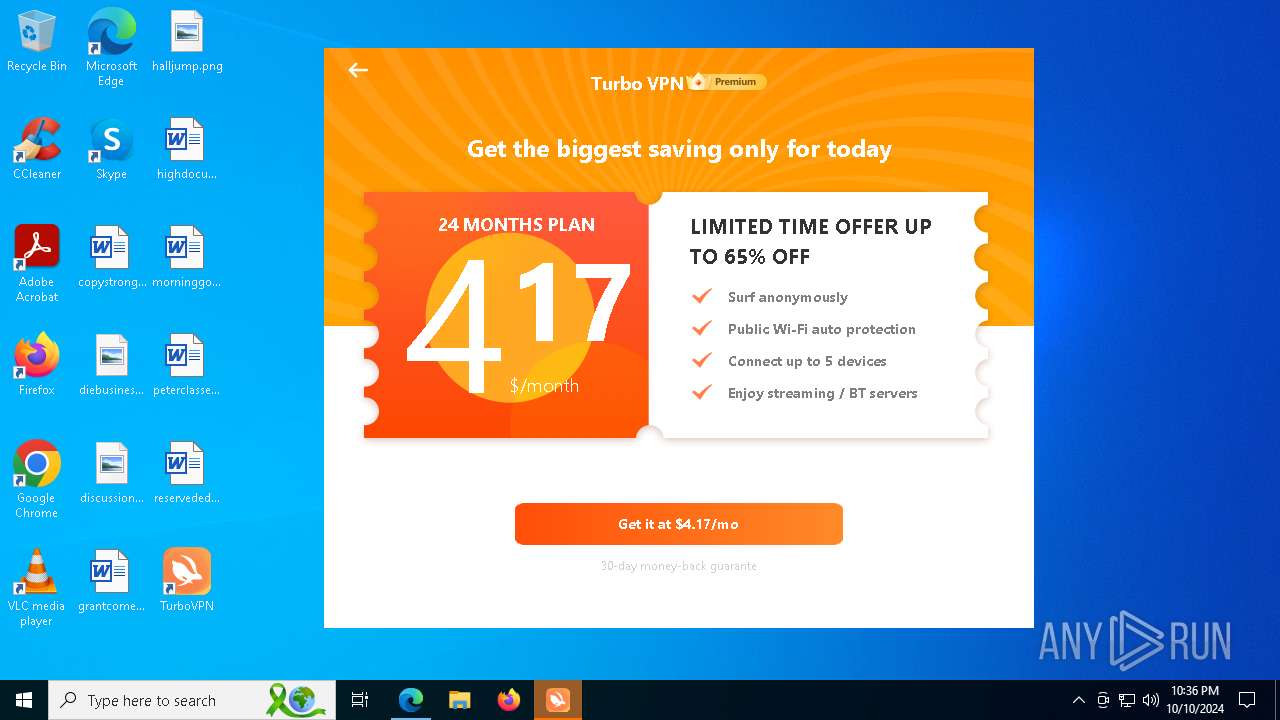
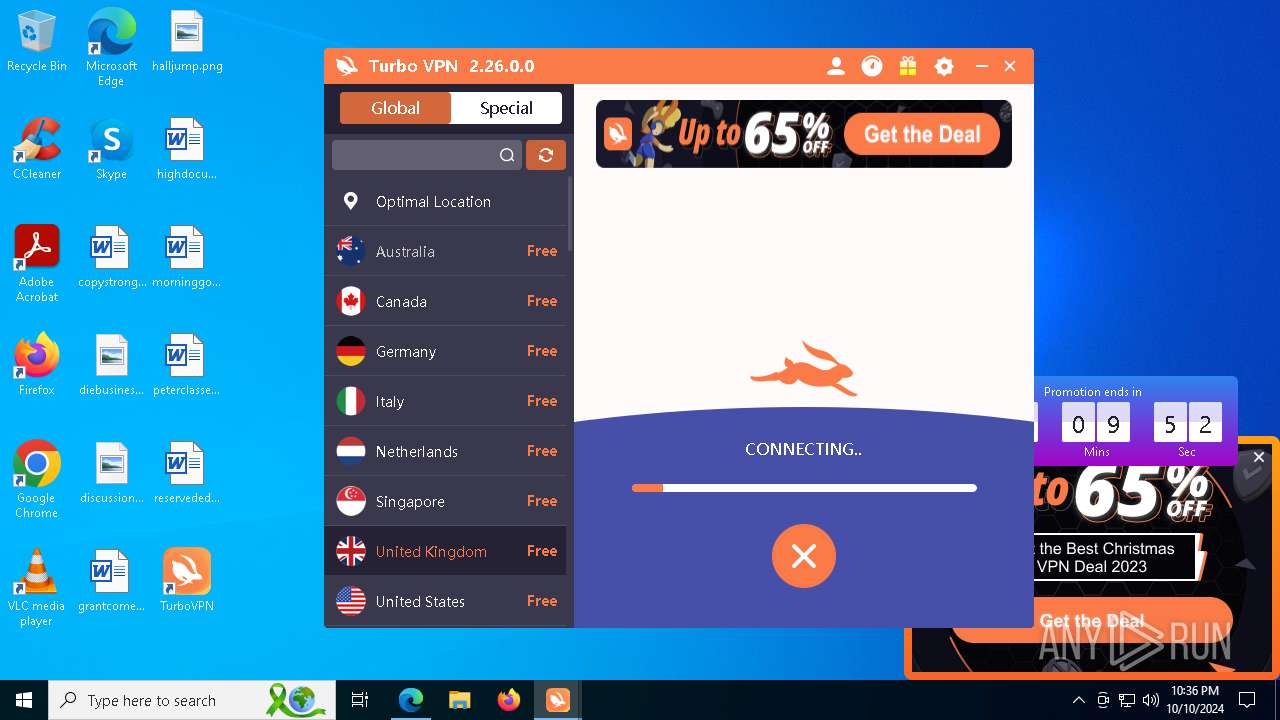
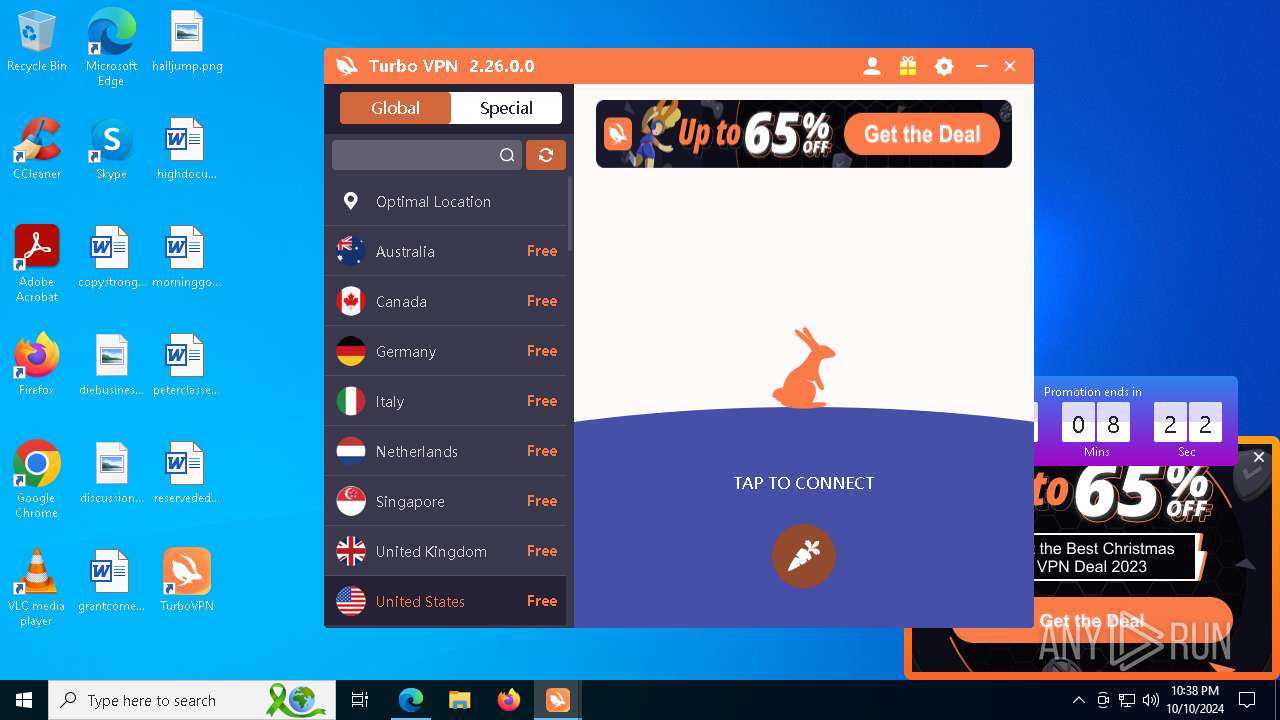
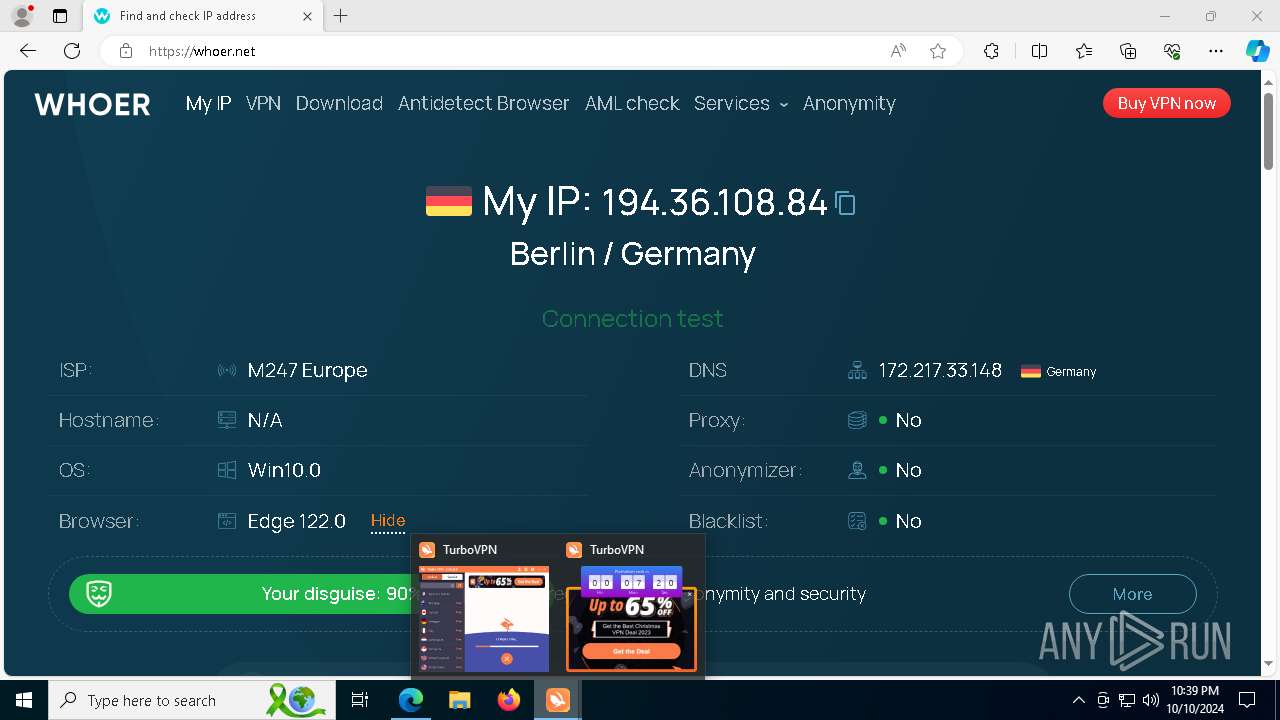
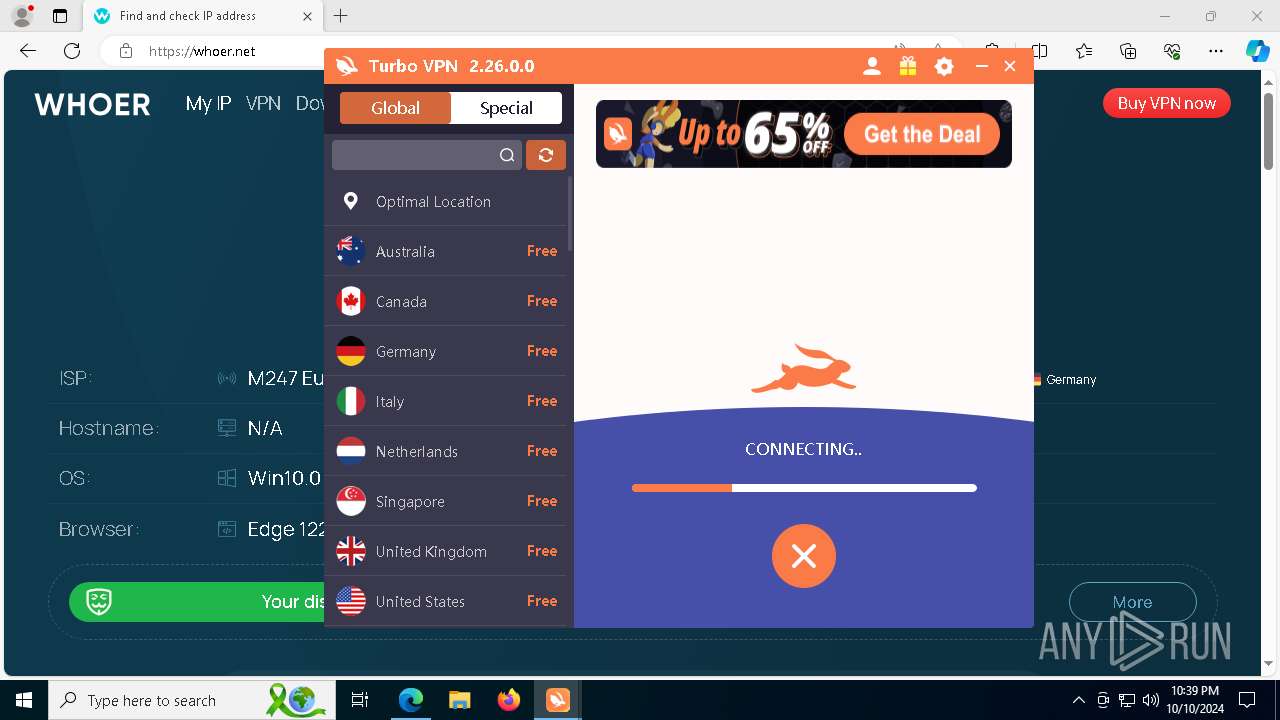
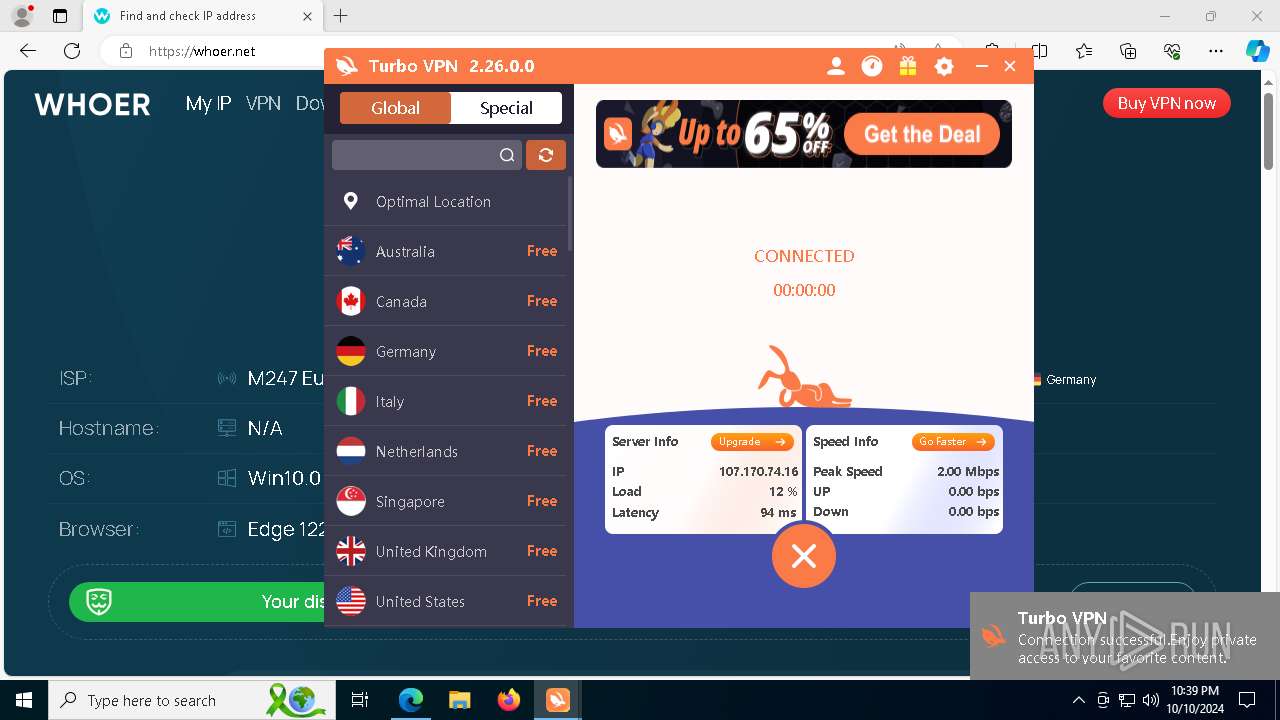
| URL: | https://turbovpn.com/download |
| Full analysis: | https://app.any.run/tasks/4fc0207b-c5e1-4d82-b54f-1f02ed935bc6 |
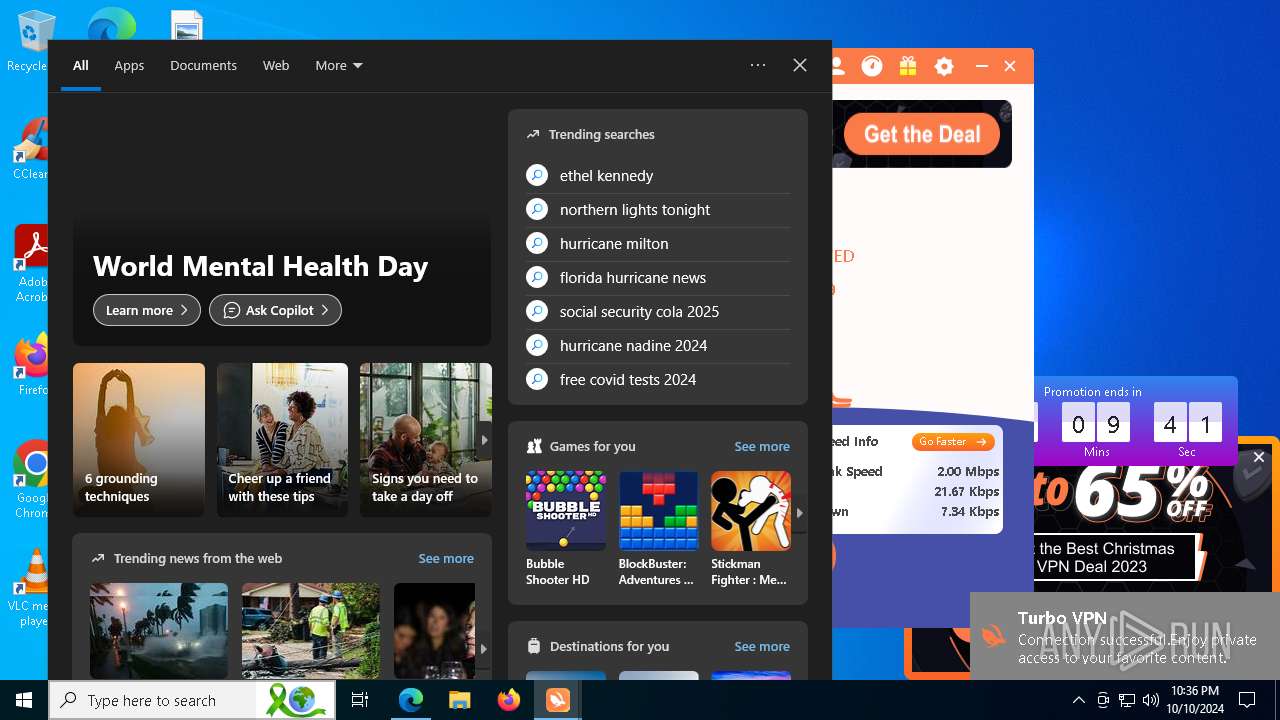
| Verdict: | Malicious activity |
| Analysis date: | October 10, 2024, 22:34:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A894FF3C92DDD0C95487C561E85D4301 |
| SHA1: | 1812259E69326B491A4BD7BF9049EF3C7B01CDA0 |
| SHA256: | 0977F515B4758CB7BDD576653BBE95EB440EDD1B768DD2452222EEDD0739F6B1 |
| SSDEEP: | 3:N8YY0aKM:2YY4M |
MALICIOUS
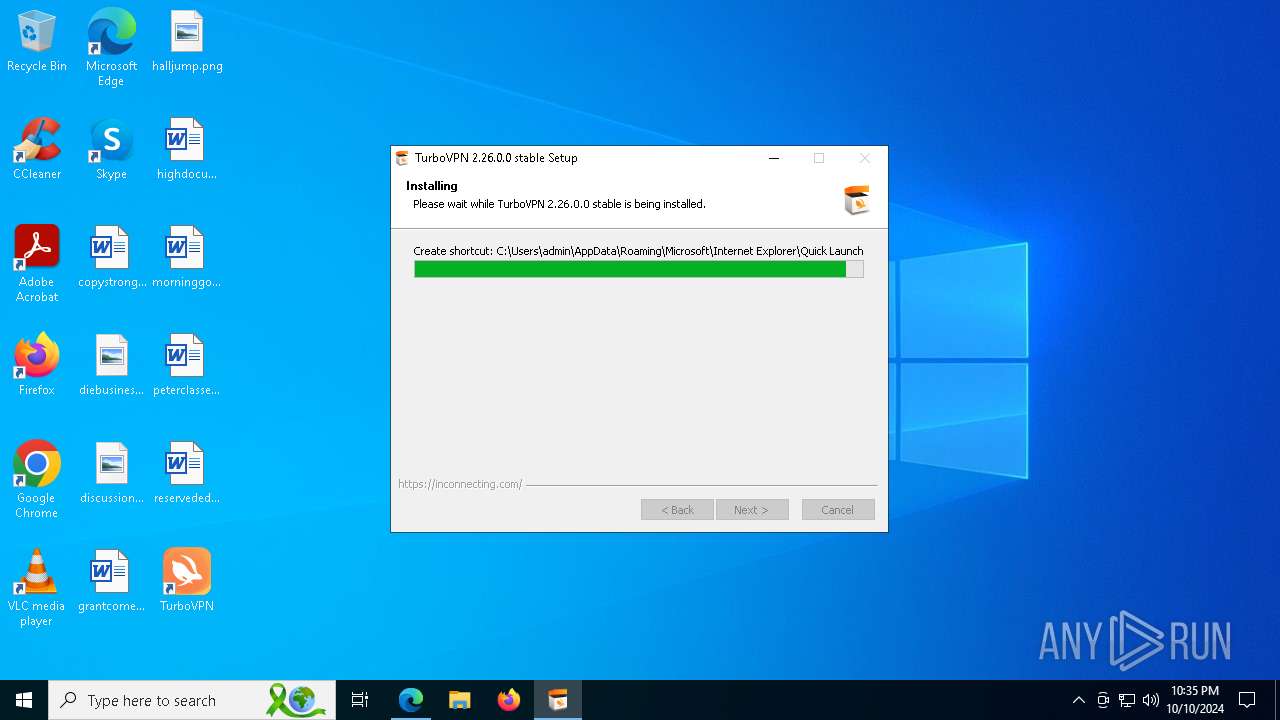
Changes the autorun value in the registry
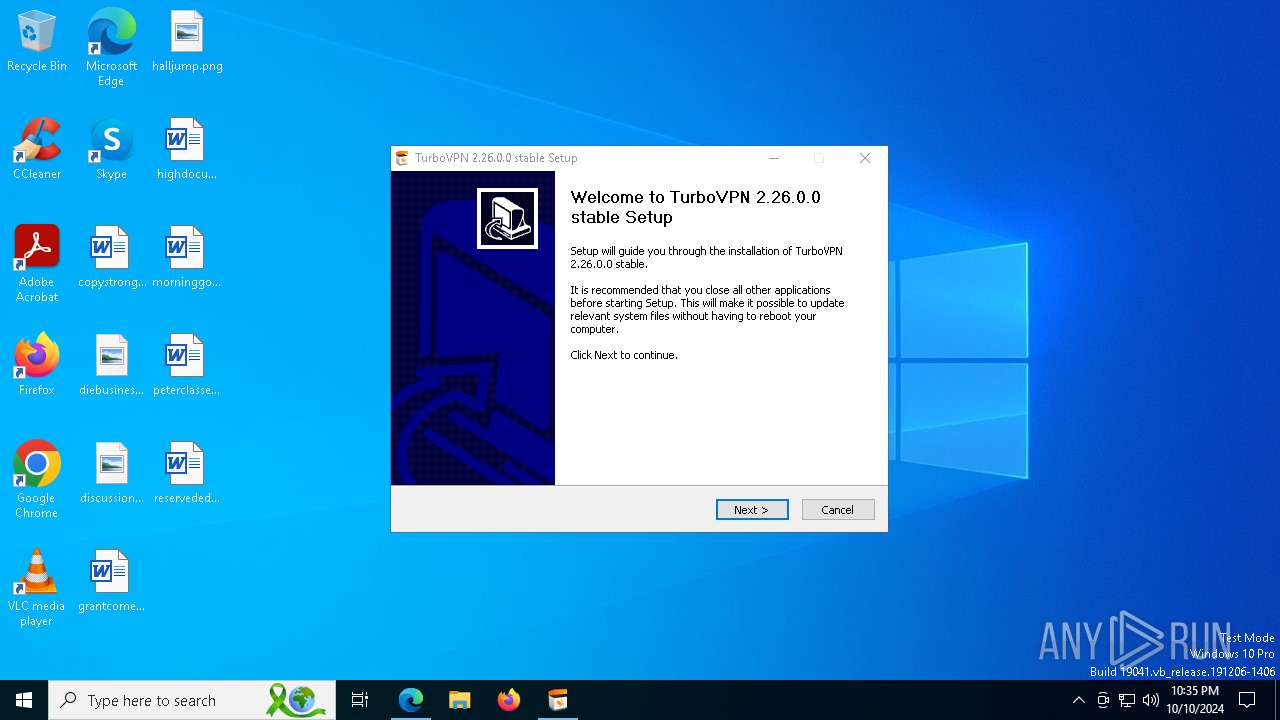
- TurboVPN_setup.exe (PID: 7256)
SUSPICIOUS
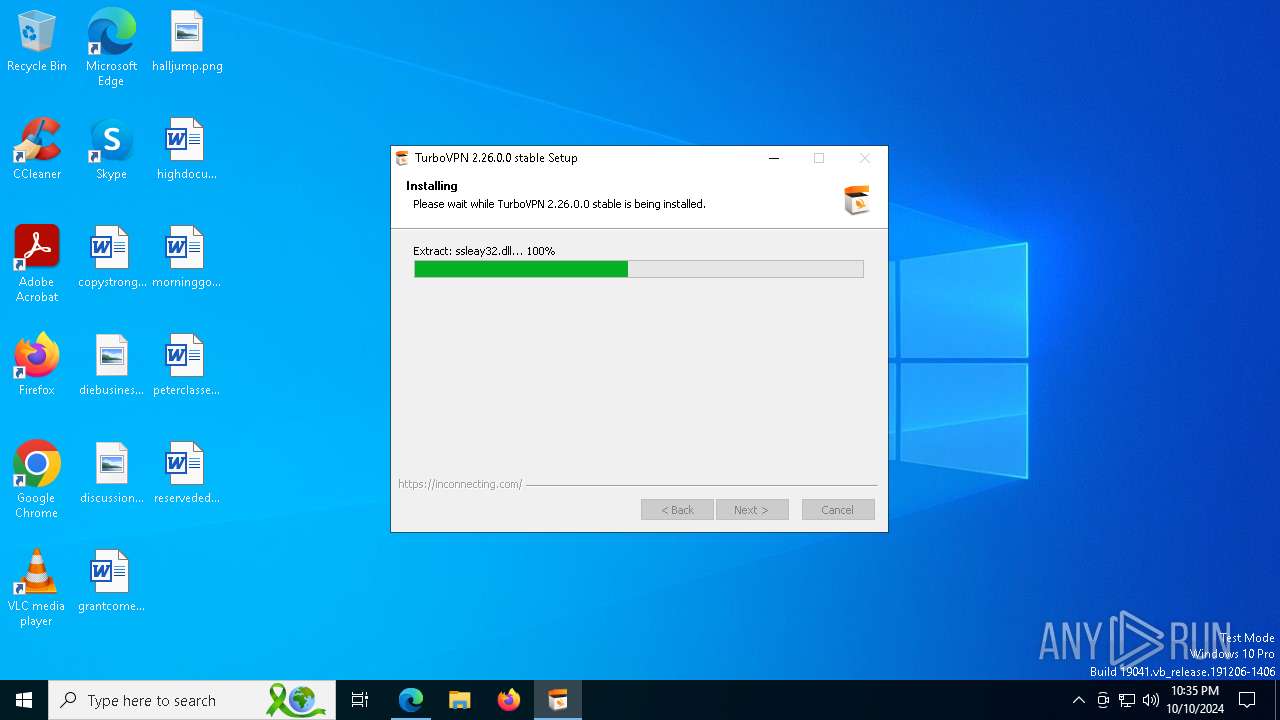
Executable content was dropped or overwritten
- TurboVPN_setup.exe (PID: 7256)
- installtapx64.exe (PID: 6196)
- drvinst.exe (PID: 6496)
- drvinst.exe (PID: 6804)
- TurboVPN.exe (PID: 6444)
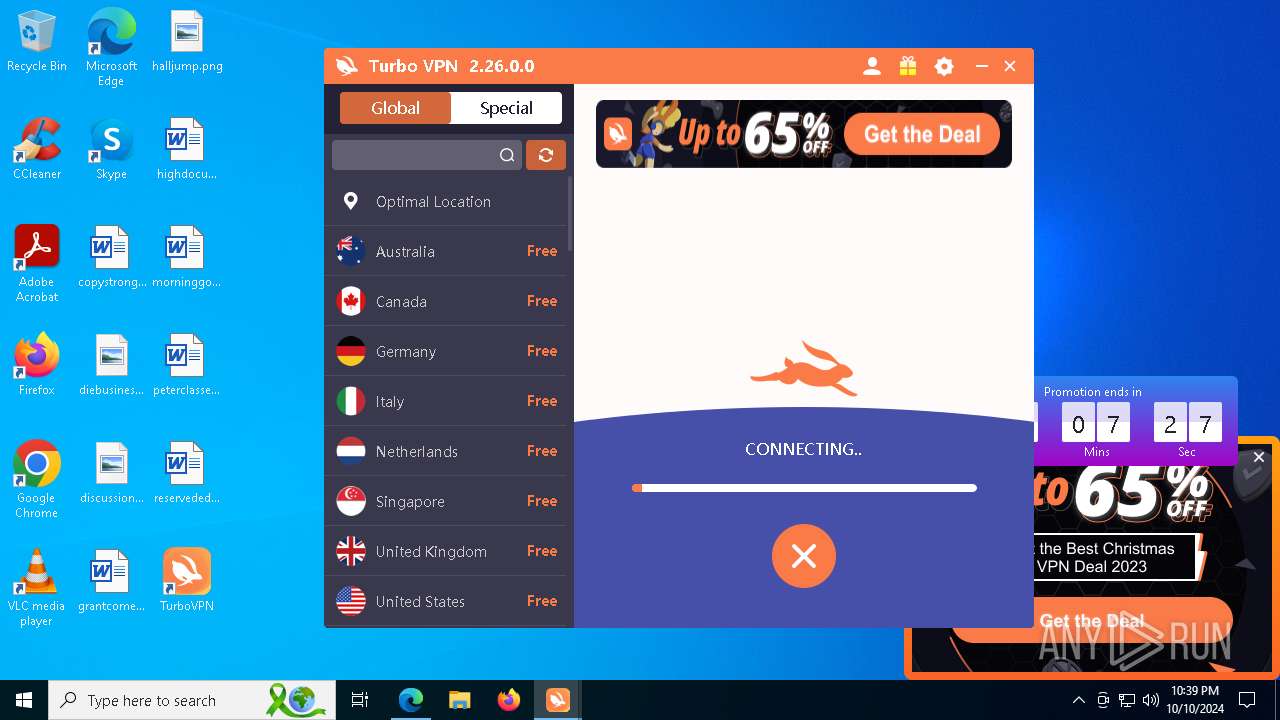
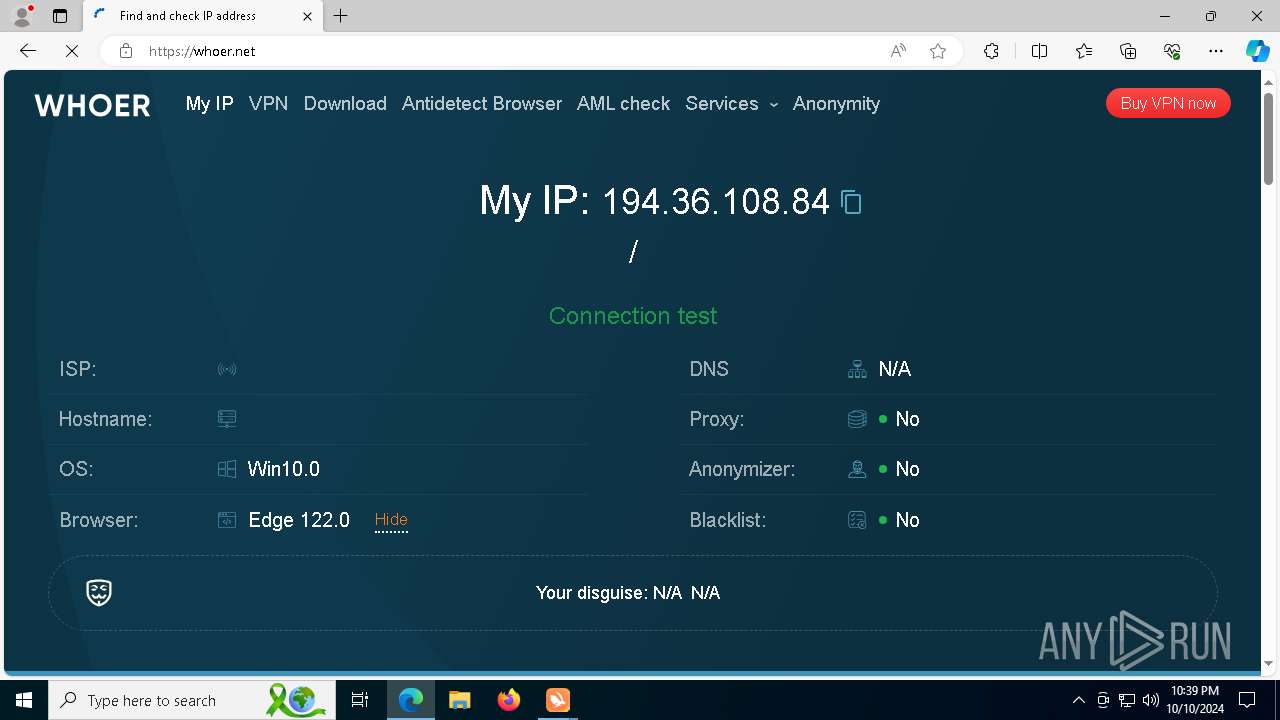
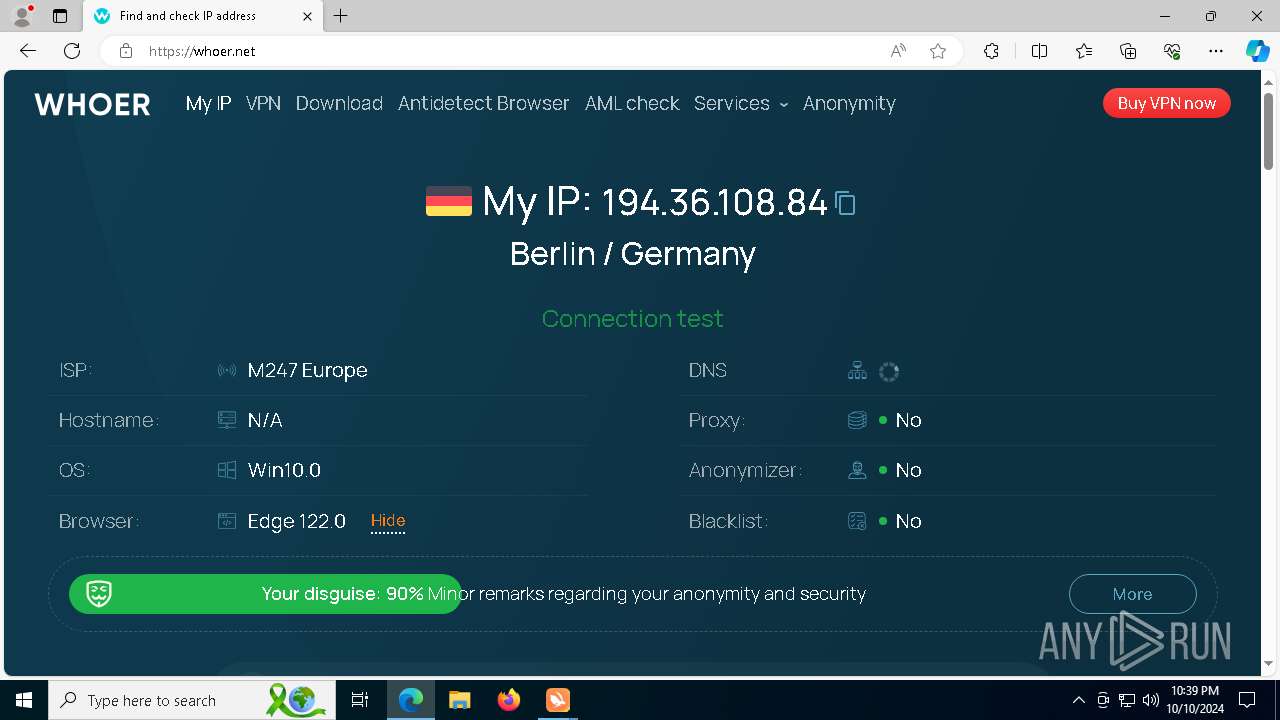
Checks for external IP
- svchost.exe (PID: 2172)
- TurboVPN_setup.exe (PID: 7256)
- TurboVPN.exe (PID: 6444)
Malware-specific behavior (creating "System.dll" in Temp)
- TurboVPN_setup.exe (PID: 7256)
Uses TASKKILL.EXE to kill process
- TurboVPN_setup.exe (PID: 7256)
Process drops legitimate windows executable
- TurboVPN_setup.exe (PID: 7256)
The process drops C-runtime libraries
- TurboVPN_setup.exe (PID: 7256)
Checks Windows Trust Settings
- installtapx64.exe (PID: 6196)
- drvinst.exe (PID: 6496)
- TurboVPN.exe (PID: 6444)
Reads security settings of Internet Explorer
- installtapx64.exe (PID: 6196)
- TurboVPN.exe (PID: 6444)
Drops a system driver (possible attempt to evade defenses)
- drvinst.exe (PID: 6496)
- TurboVPN_setup.exe (PID: 7256)
- drvinst.exe (PID: 6804)
- installtapx64.exe (PID: 6196)
The process creates files with name similar to system file names
- TurboVPN_setup.exe (PID: 7256)
Creates or modifies Windows services
- drvinst.exe (PID: 6804)
- TurboVPN.exe (PID: 6444)
Creates files in the driver directory
- drvinst.exe (PID: 6804)
- drvinst.exe (PID: 6496)
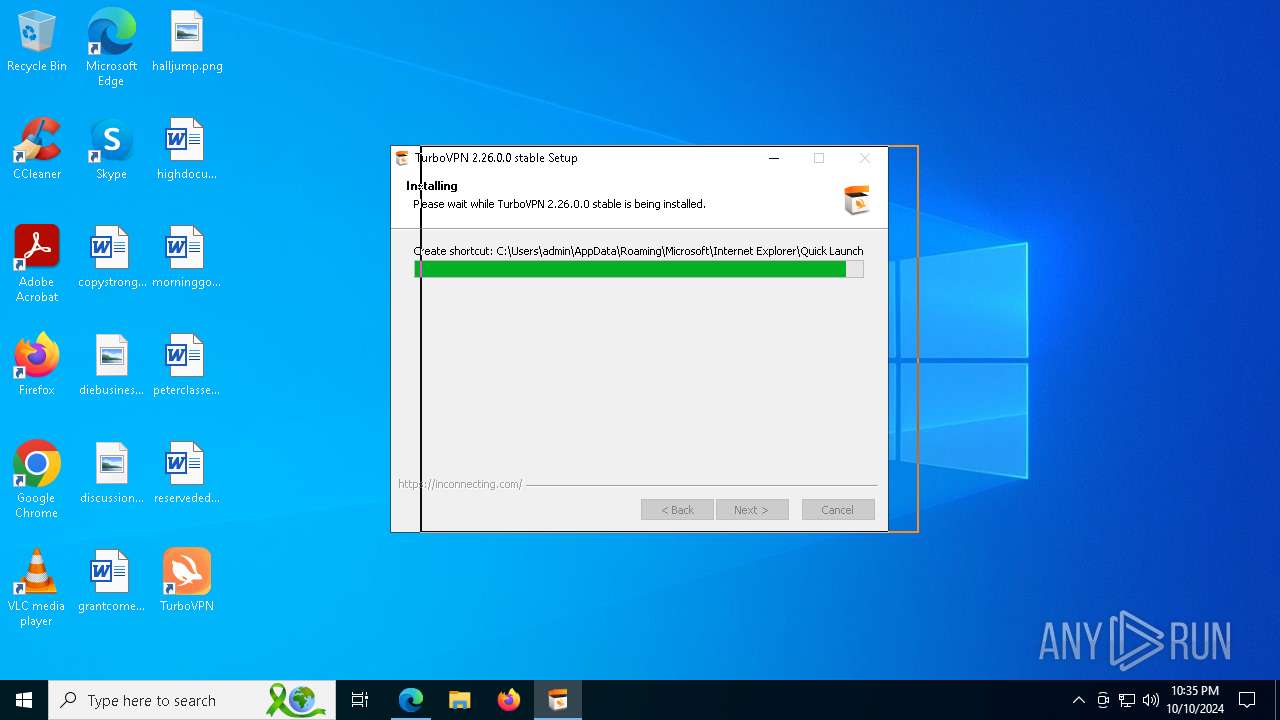
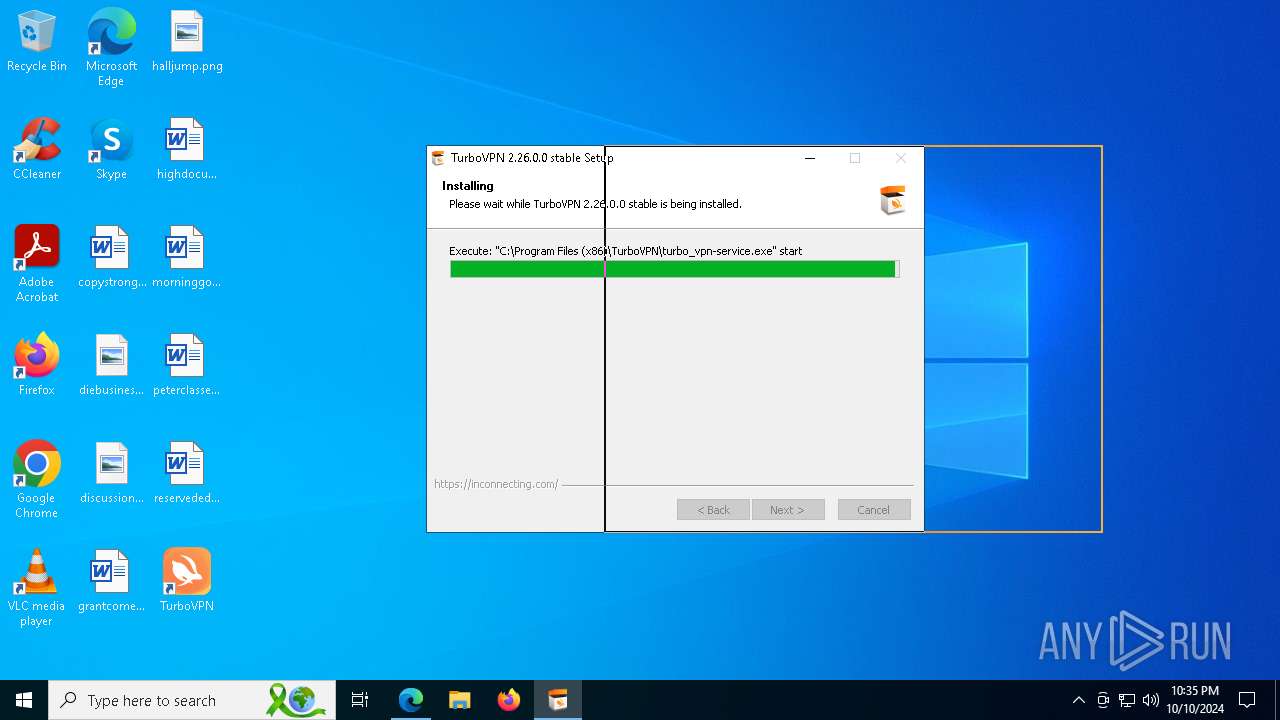
Executes as Windows Service
- turbo_vpn-service.exe (PID: 6336)
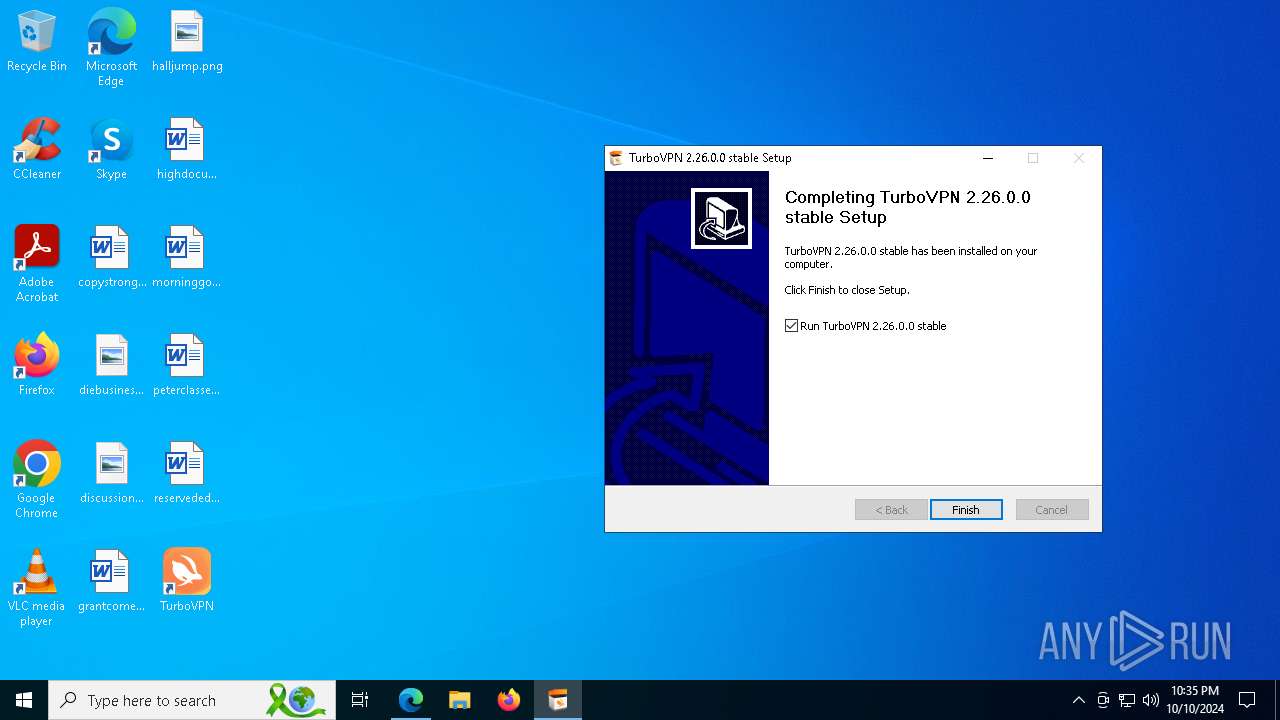
Creates a software uninstall entry
- TurboVPN_setup.exe (PID: 7256)
Adds/modifies Windows certificates
- TurboVPN.exe (PID: 6444)
Uses ROUTE.EXE to obtain the routing table information
- TurboVPN.exe (PID: 6444)
Suspicious use of NETSH.EXE
- tun2socks.exe (PID: 6168)
- tun2socks.exe (PID: 7792)
- tun2socks.exe (PID: 7572)
- tun2socks.exe (PID: 7600)
- tun2socks.exe (PID: 7952)
- tun2socks.exe (PID: 7924)
- tun2socks.exe (PID: 2132)
- tun2socks.exe (PID: 7908)
- tun2socks.exe (PID: 1568)
- tun2socks.exe (PID: 8052)
Connects to unusual port
- ssr.exe (PID: 7196)
- TurboVPN.exe (PID: 6444)
- ssr.exe (PID: 7088)
- ssr.exe (PID: 7668)
Process uses IPCONFIG to clear DNS cache
- TurboVPN.exe (PID: 6444)
INFO
Reads Environment values
- identity_helper.exe (PID: 7376)
Checks supported languages
- identity_helper.exe (PID: 7376)
- TurboVPN_setup.exe (PID: 7256)
- drvinst.exe (PID: 6496)
- installtapx64.exe (PID: 6196)
- drvinst.exe (PID: 6804)
- turbo_vpn-service.exe (PID: 2736)
- turbo_vpn-service.exe (PID: 6336)
- TurboVPNLauncher.exe (PID: 920)
- TurboVPN.exe (PID: 6444)
- turboconfig.exe (PID: 4016)
- turbo_vpn-service.exe (PID: 2724)
- ssr.exe (PID: 7196)
- tun2socks.exe (PID: 6168)
- tun2socks.exe (PID: 7792)
- tun2socks.exe (PID: 7600)
- tun2socks.exe (PID: 7572)
- ssr.exe (PID: 7668)
- tun2socks.exe (PID: 7952)
- ssr.exe (PID: 7088)
- tun2socks.exe (PID: 7924)
- tun2socks.exe (PID: 7908)
- tun2socks.exe (PID: 2132)
- tun2socks.exe (PID: 1568)
- tun2socks.exe (PID: 7288)
- tun2socks.exe (PID: 8052)
Reads the computer name
- identity_helper.exe (PID: 7376)
- installtapx64.exe (PID: 6196)
- TurboVPN_setup.exe (PID: 7256)
- drvinst.exe (PID: 6496)
- turbo_vpn-service.exe (PID: 2736)
- TurboVPNLauncher.exe (PID: 920)
- turbo_vpn-service.exe (PID: 2724)
- turbo_vpn-service.exe (PID: 6336)
- TurboVPN.exe (PID: 6444)
- turboconfig.exe (PID: 4016)
- ssr.exe (PID: 7196)
- tun2socks.exe (PID: 6168)
- tun2socks.exe (PID: 7792)
- drvinst.exe (PID: 6804)
- tun2socks.exe (PID: 7572)
- tun2socks.exe (PID: 7600)
- tun2socks.exe (PID: 7952)
- tun2socks.exe (PID: 7924)
- tun2socks.exe (PID: 2132)
- tun2socks.exe (PID: 7908)
- tun2socks.exe (PID: 1568)
- tun2socks.exe (PID: 7288)
- tun2socks.exe (PID: 8052)
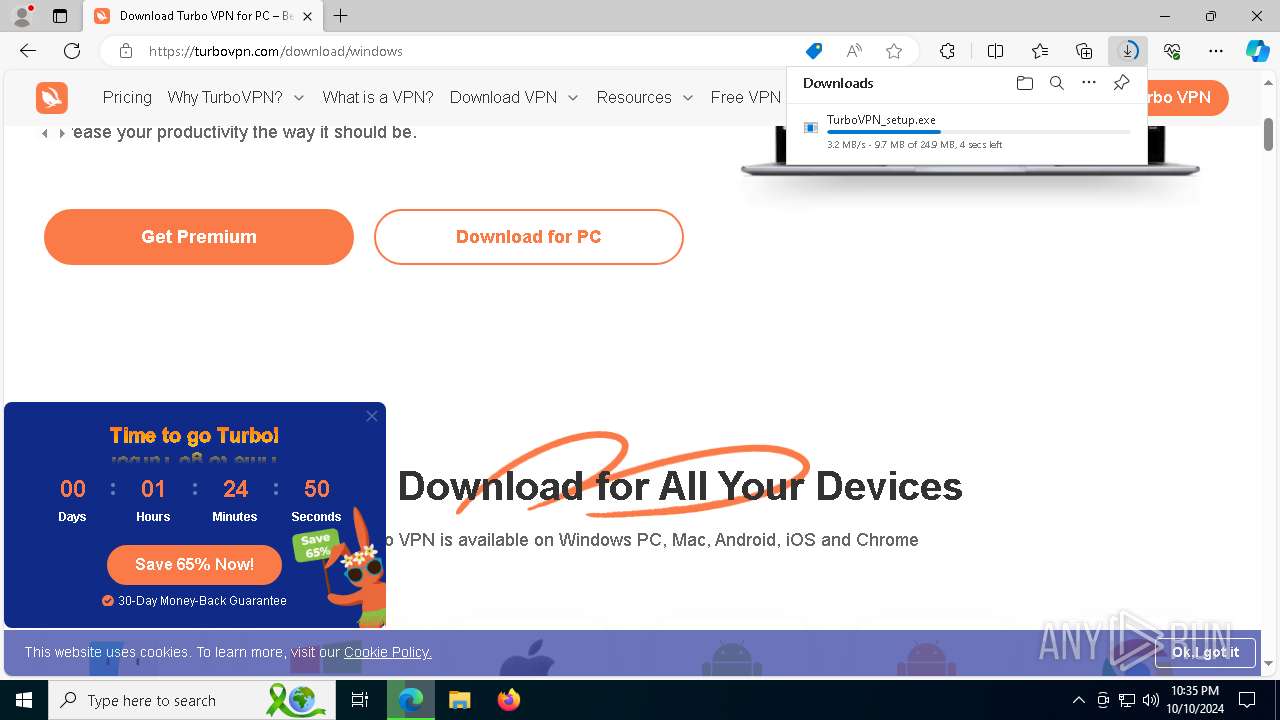
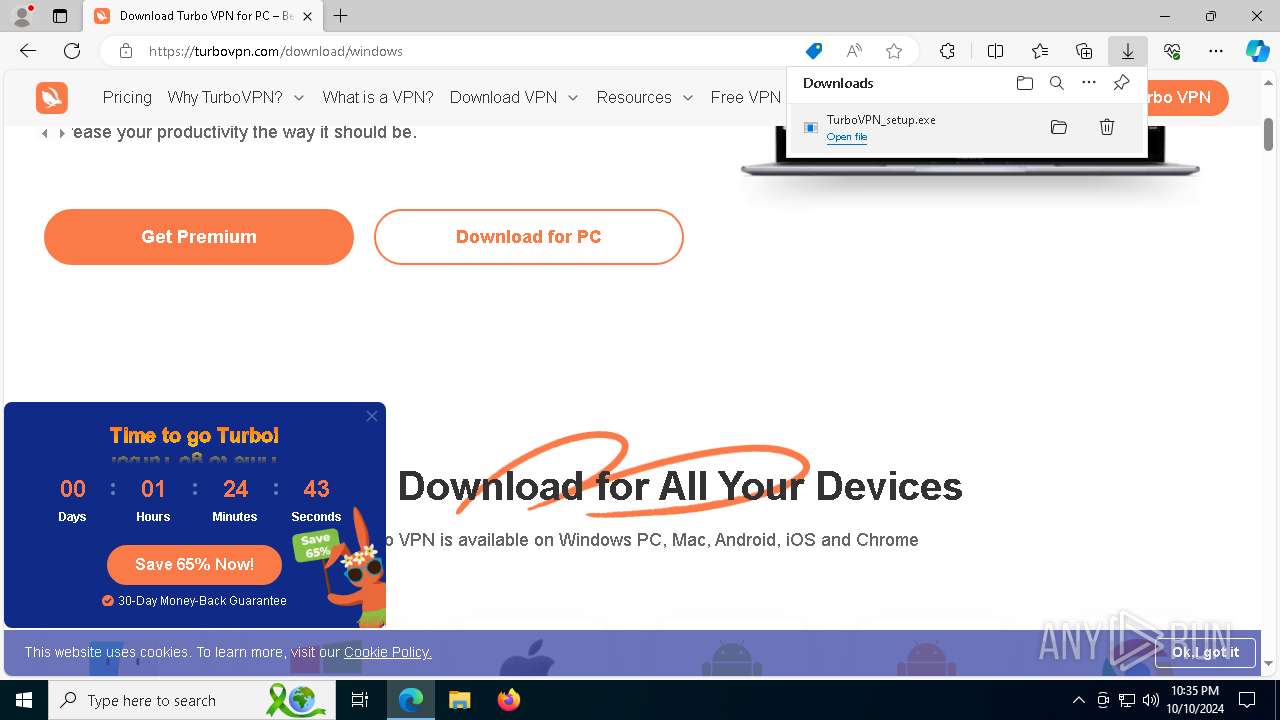
The process uses the downloaded file
- msedge.exe (PID: 7968)
- msedge.exe (PID: 6028)
Create files in a temporary directory
- TurboVPN_setup.exe (PID: 7256)
- installtapx64.exe (PID: 6196)
Executable content was dropped or overwritten
- msedge.exe (PID: 6820)
- msedge.exe (PID: 6028)
- msedge.exe (PID: 2084)
Application launched itself
- msedge.exe (PID: 6028)
Creates files in the program directory
- TurboVPN_setup.exe (PID: 7256)
- turbo_vpn-service.exe (PID: 2736)
- turbo_vpn-service.exe (PID: 2724)
- TurboVPNLauncher.exe (PID: 920)
- TurboVPN.exe (PID: 6444)
Reads the machine GUID from the registry
- installtapx64.exe (PID: 6196)
- drvinst.exe (PID: 6496)
- TurboVPN.exe (PID: 6444)
- tun2socks.exe (PID: 6168)
- tun2socks.exe (PID: 7792)
- tun2socks.exe (PID: 7600)
- tun2socks.exe (PID: 7572)
- tun2socks.exe (PID: 7952)
- tun2socks.exe (PID: 7924)
- tun2socks.exe (PID: 2132)
- tun2socks.exe (PID: 7908)
- tun2socks.exe (PID: 1568)
- tun2socks.exe (PID: 8052)
- tun2socks.exe (PID: 7288)
Sends debugging messages
- installtapx64.exe (PID: 6196)
- TurboVPN.exe (PID: 6444)
Reads the software policy settings
- installtapx64.exe (PID: 6196)
- drvinst.exe (PID: 6496)
- TurboVPN.exe (PID: 6444)
- slui.exe (PID: 3860)
- slui.exe (PID: 8188)
Creates files or folders in the user directory
- TurboVPN_setup.exe (PID: 7256)
- TurboVPN.exe (PID: 6444)
Checks proxy server information
- TurboVPN.exe (PID: 6444)
- slui.exe (PID: 3860)
Deletes a route via ROUTE.EXE
- ROUTE.EXE (PID: 7840)
- ROUTE.EXE (PID: 6864)
- ROUTE.EXE (PID: 6368)
- ROUTE.EXE (PID: 6276)
- ROUTE.EXE (PID: 7100)
- ROUTE.EXE (PID: 2928)
- ROUTE.EXE (PID: 7712)
- ROUTE.EXE (PID: 7000)
- ROUTE.EXE (PID: 7520)
- ROUTE.EXE (PID: 6192)
- ROUTE.EXE (PID: 7836)
- ROUTE.EXE (PID: 7648)
- ROUTE.EXE (PID: 6904)
- ROUTE.EXE (PID: 784)
- ROUTE.EXE (PID: 7596)
- ROUTE.EXE (PID: 7556)
- ROUTE.EXE (PID: 3008)
- ROUTE.EXE (PID: 7712)
- ROUTE.EXE (PID: 4836)
- ROUTE.EXE (PID: 6644)
- ROUTE.EXE (PID: 7792)
- ROUTE.EXE (PID: 7956)
- ROUTE.EXE (PID: 6896)
- ROUTE.EXE (PID: 7192)
- ROUTE.EXE (PID: 6480)
Disables trace logs
- netsh.exe (PID: 8052)
- netsh.exe (PID: 6276)
- netsh.exe (PID: 6936)
- netsh.exe (PID: 4408)
- netsh.exe (PID: 1376)
- netsh.exe (PID: 7004)
- netsh.exe (PID: 7436)
- netsh.exe (PID: 7524)
- netsh.exe (PID: 7428)
- netsh.exe (PID: 3924)
- netsh.exe (PID: 1432)
- netsh.exe (PID: 6860)
- netsh.exe (PID: 6480)
- netsh.exe (PID: 1376)
- netsh.exe (PID: 6852)
- netsh.exe (PID: 7056)
- netsh.exe (PID: 7364)
- netsh.exe (PID: 7552)
- netsh.exe (PID: 7932)
- netsh.exe (PID: 7072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
369
Monitored processes
212
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 784 | C:\WINDOWS\system32\route delete 192.241.236.8 mask 255.255.255.255 | C:\Windows\SysWOW64\ROUTE.EXE | — | TurboVPN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Route Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
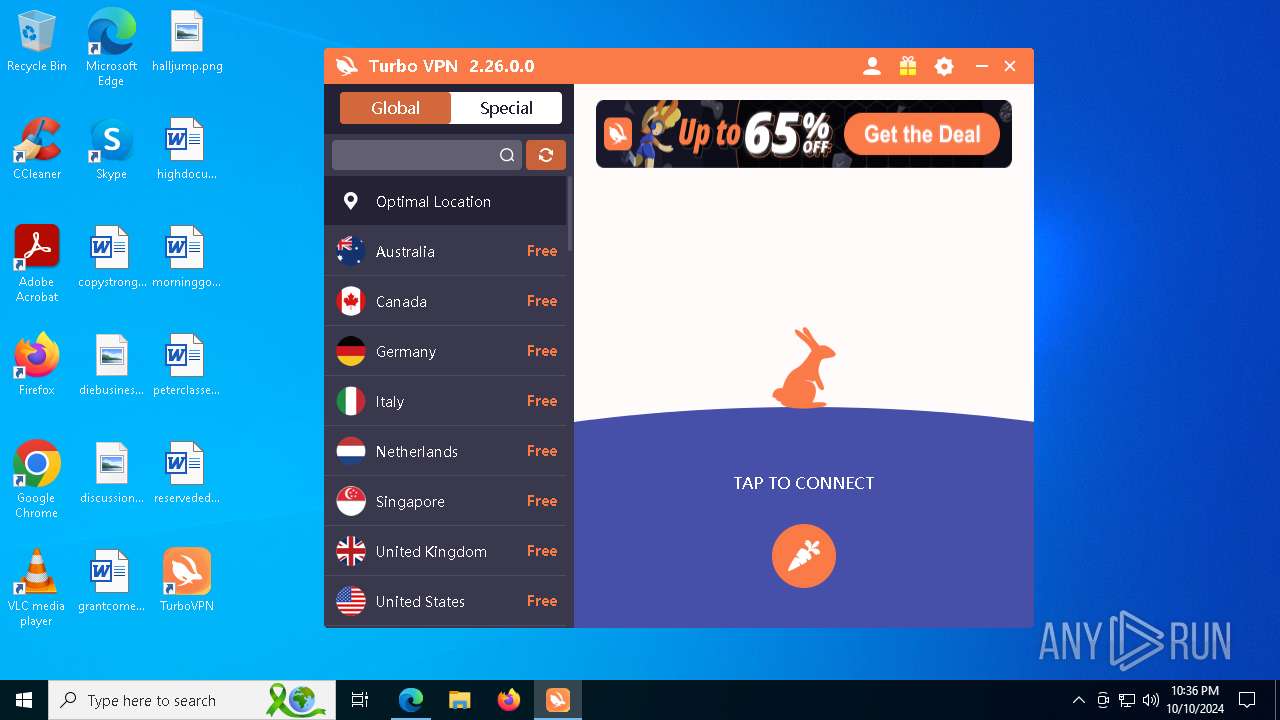
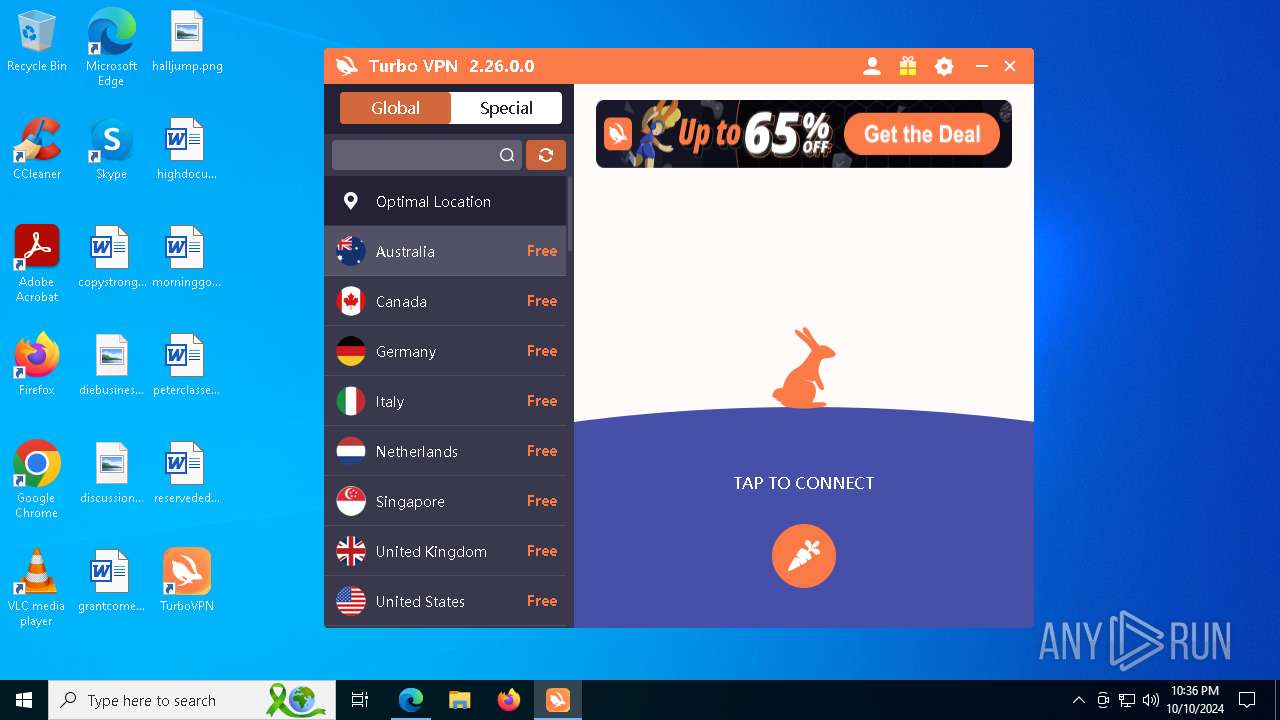
| 920 | "C:\Program Files (x86)\TurboVPN\TurboVPNLauncher.exe" | C:\Program Files (x86)\TurboVPN\TurboVPNLauncher.exe | — | TurboVPN_setup.exe | |||||||||||
User: admin Company: Innovative Connecting Integrity Level: HIGH Description: Startup Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1112 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2364 --field-trial-handle=2368,i,657857238940183092,11175774173721801278,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ROUTE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=NetworkAvailable | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3704 --field-trial-handle=2368,i,657857238940183092,11175774173721801278,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=5568 --field-trial-handle=2368,i,657857238940183092,11175774173721801278,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1376 | netsh interface ip set dns "Local Area Connection" dhcp | C:\Windows\SysWOW64\netsh.exe | — | tun2socks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1376 | netsh interface ip set dns "Local Area Connection" dhcp | C:\Windows\SysWOW64\netsh.exe | — | tun2socks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
163 600
Read events
163 457
Write events
134
Delete events
9
Modification events
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 04922641BD822F00 | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 113D2D41BD822F00 | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721516 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CD6E0C36-C024-4ABF-AD4E-BC44FDB62B22} | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721516 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4228108E-79C6-4728-A802-CCB369B1EAFE} | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721516 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3C531269-7FAB-4F27-9A21-3DAEFFC52A5F} | |||
| (PID) Process: | (6028) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721516 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CFF2C731-F8A9-4F65-9924-E4A50303BC35} | |||
Executable files
75
Suspicious files
482
Text files
181
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8a67a.TMP | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8a67a.TMP | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8a67a.TMP | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8a689.TMP | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8a689.TMP | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
2 446
DNS requests
310
Threats
54
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7480 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
824 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7256 | TurboVPN_setup.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json | unknown | — | — | shared |
7340 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1728651739&P2=404&P3=2&P4=AEjJIuHUG%2f%2fO4IuTnCTy6ki7X16fmm1TNoqvUGjy4NzJ%2brg%2f%2fA6sGbPKELH%2b%2buAj7yNYHxsJ3iGh3h%2bL47NrRQ%3d%3d | unknown | — | — | whitelisted |
7340 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1728651739&P2=404&P3=2&P4=AEjJIuHUG%2f%2fO4IuTnCTy6ki7X16fmm1TNoqvUGjy4NzJ%2brg%2f%2fA6sGbPKELH%2b%2buAj7yNYHxsJ3iGh3h%2bL47NrRQ%3d%3d | unknown | — | — | whitelisted |
7340 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c12dff9-696d-48d4-bbe8-7d8bdad98e65?P1=1728651739&P2=404&P3=2&P4=AEjJIuHUG%2f%2fO4IuTnCTy6ki7X16fmm1TNoqvUGjy4NzJ%2brg%2f%2fA6sGbPKELH%2b%2buAj7yNYHxsJ3iGh3h%2bL47NrRQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7044 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6820 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6028 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6820 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6820 | msedge.exe | 54.230.228.4:443 | turbovpn.com | AMAZON-02 | US | whitelisted |
6820 | msedge.exe | 13.107.246.64:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6820 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
turbovpn.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7256 | TurboVPN_setup.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
7256 | TurboVPN_setup.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
7256 | TurboVPN_setup.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
7256 | TurboVPN_setup.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6444 | TurboVPN.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6444 | TurboVPN.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
7196 | ssr.exe | Generic Protocol Command Decode | SURICATA TLS invalid SNI length |
7196 | ssr.exe | Generic Protocol Command Decode | SURICATA TLS invalid SNI length |
Process | Message |
|---|---|
installtapx64.exe | 3 |
installtapx64.exe | C:\Program Files (x86)\TurboVPN\installtapx64.exe |
installtapx64.exe | C:\Program Files (x86)\TurboVPN |
installtapx64.exe | /S |
installtapx64.exe | C:\Program Files (x86)\TurboVPN\installtapx64.exe C:\Program Files (x86)\TurboVPN /S |
installtapx64.exe | C:\Program Files (x86)\TurboVPN |
installtapx64.exe | C:\Program Files (x86)\TurboVPN\installtapx64.exe |
installtapx64.exe | strCmdType |
installtapx64.exe | |
installtapx64.exe | Unknow Cmd xxx |