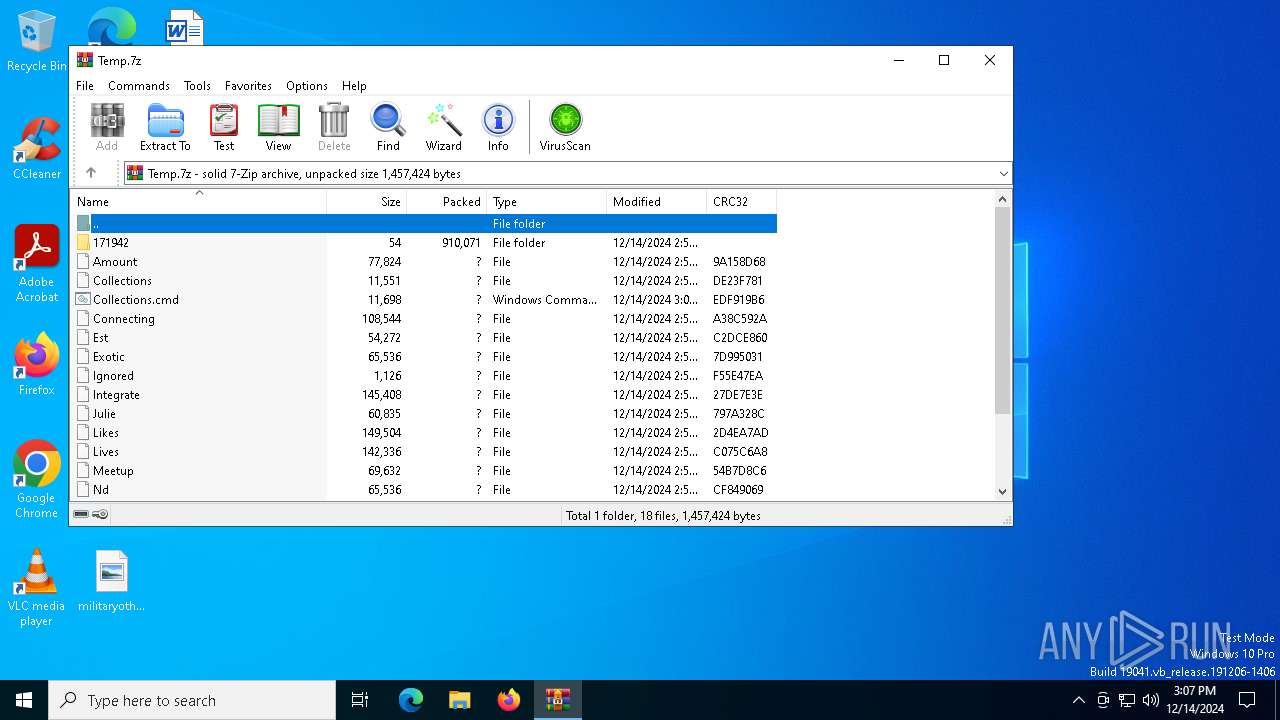
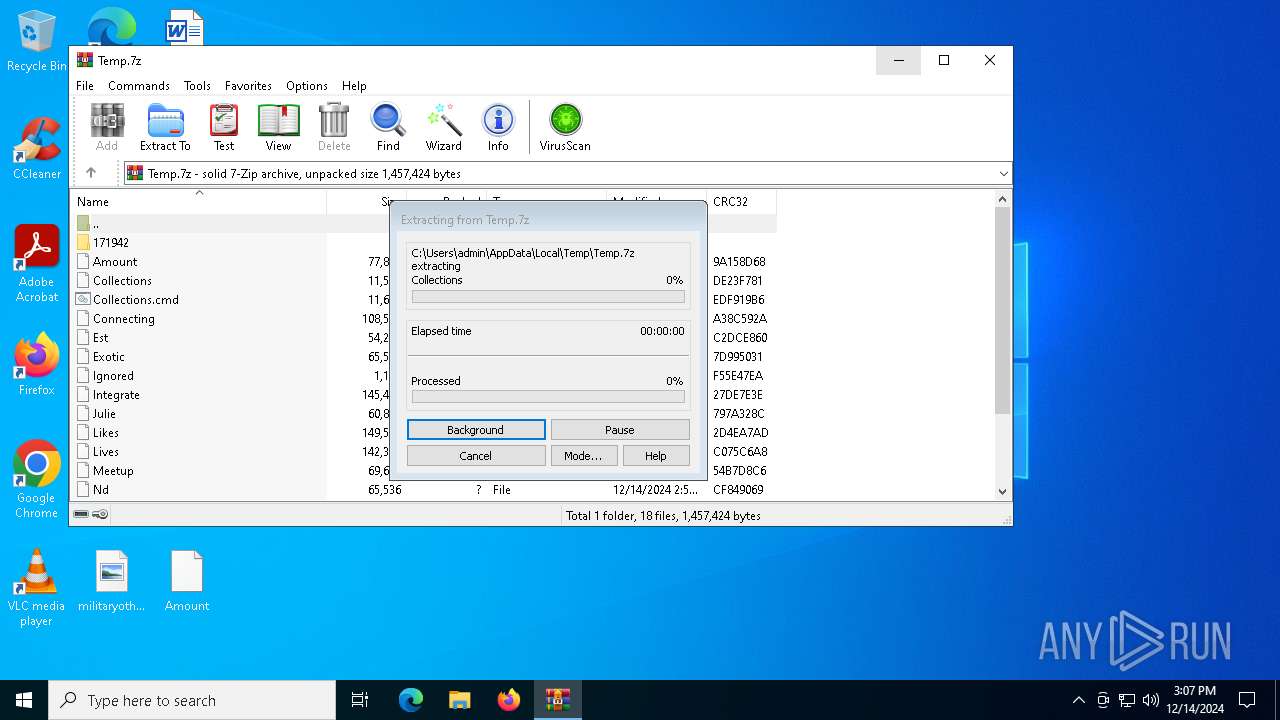
| File name: | Temp.7z |
| Full analysis: | https://app.any.run/tasks/b90b7721-7901-4260-85af-29c7385ba7b8 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 15:06:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 533993A25CB3F0F1A76EDD00EAB735A6 |
| SHA1: | 63DEA19C3BE2F2E30F7CAEA34607625F97DEA895 |
| SHA256: | 09767BF3ADAA3EDECA603FBC73E9D1654748E70D6B0F9133C476558A830ED39F |
| SSDEEP: | 49152:/c0A610x3ebdNjjjZ3HD5xlQ0nY+bGHVuPzKHpQ/qXG50VIc9Uhh0WfErmlIUHoQ:/c0A6OWdlZ3j5x60YHHVurUWjOqc9Uhb |
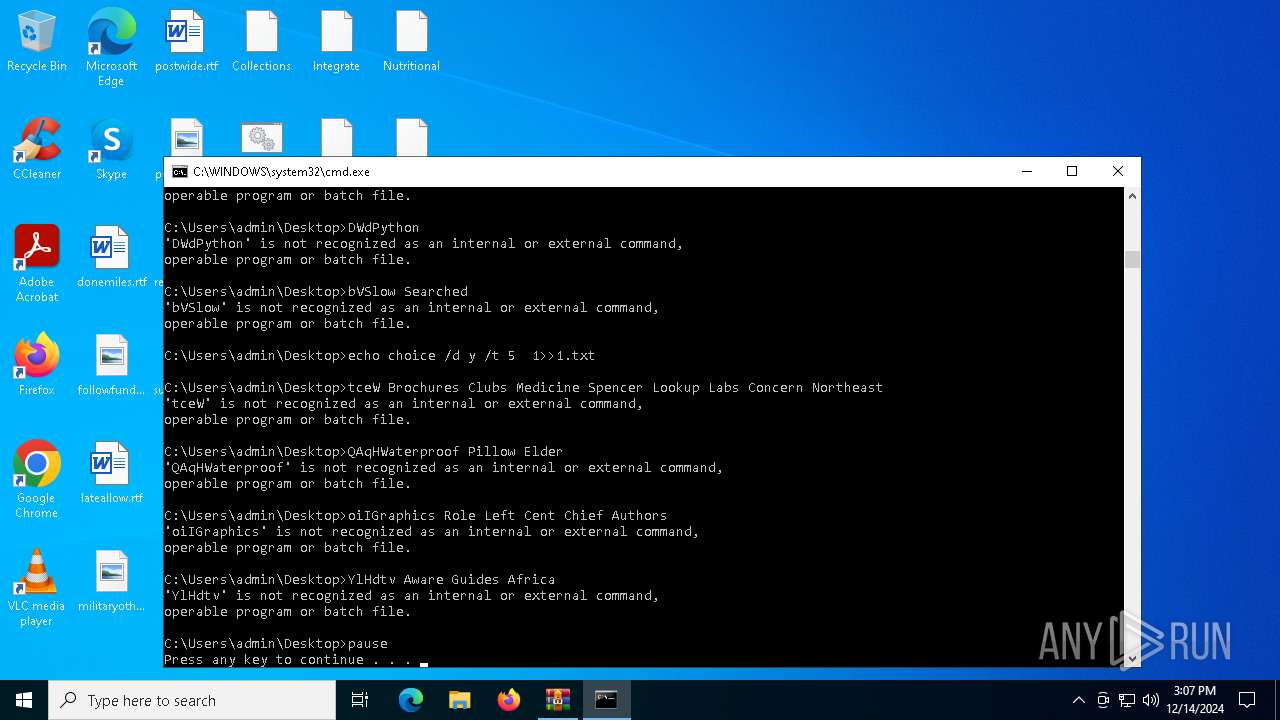
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 848)
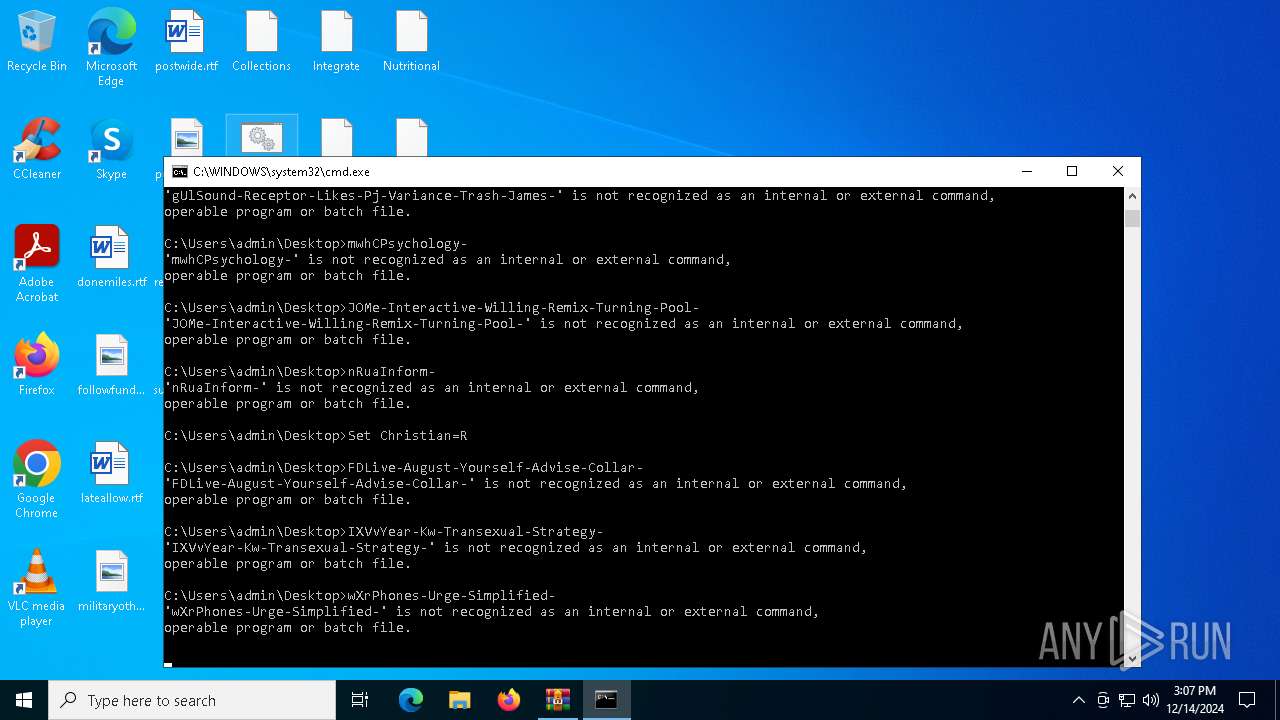
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 6832)
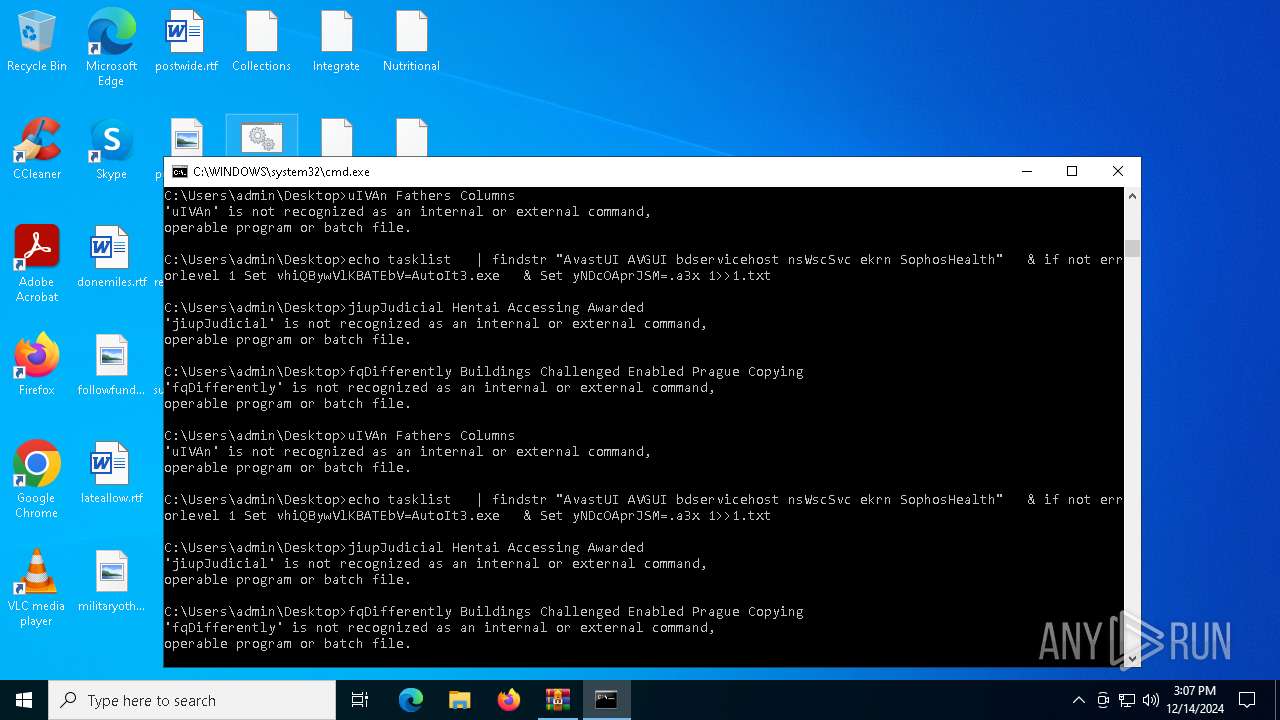
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6832)
Get information on the list of running processes
- cmd.exe (PID: 6832)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6832)
INFO
Manual execution by a user
- cmd.exe (PID: 6832)
The process uses the downloaded file
- WinRAR.exe (PID: 848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2024:12:14 14:56:27+00:00 |
| ArchivedFileName: | 171942 |
Total processes
134
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
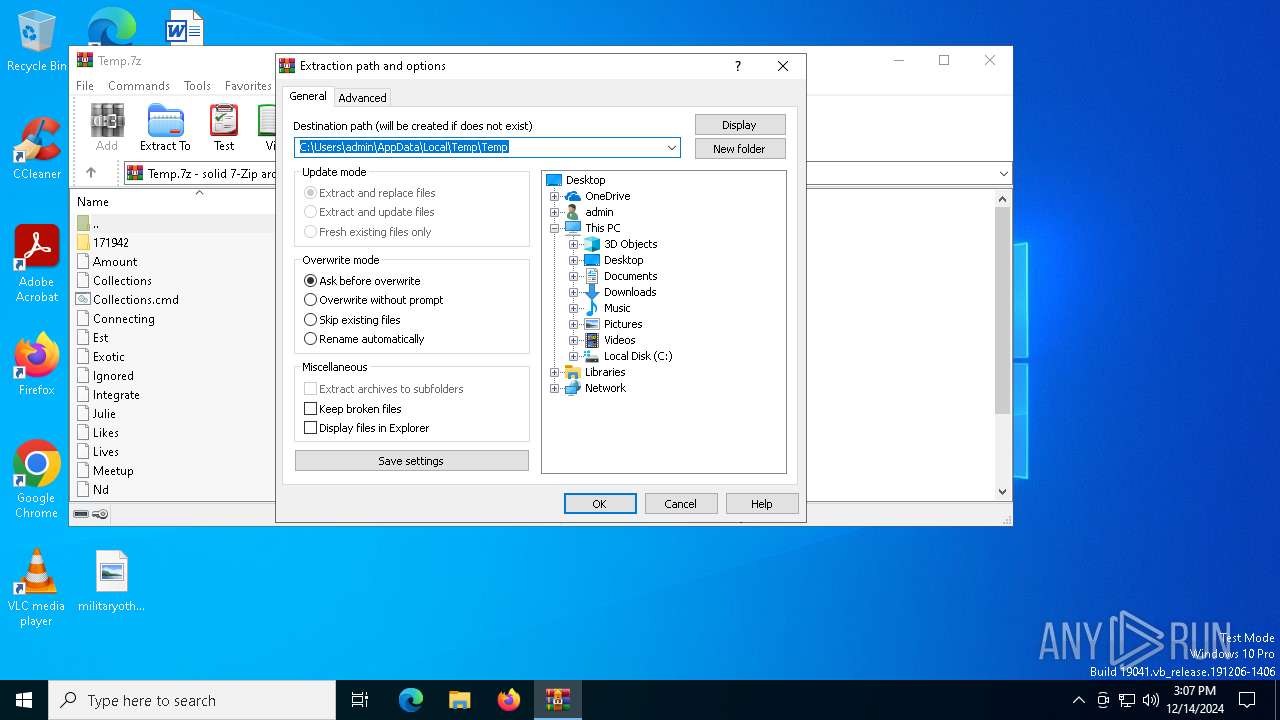
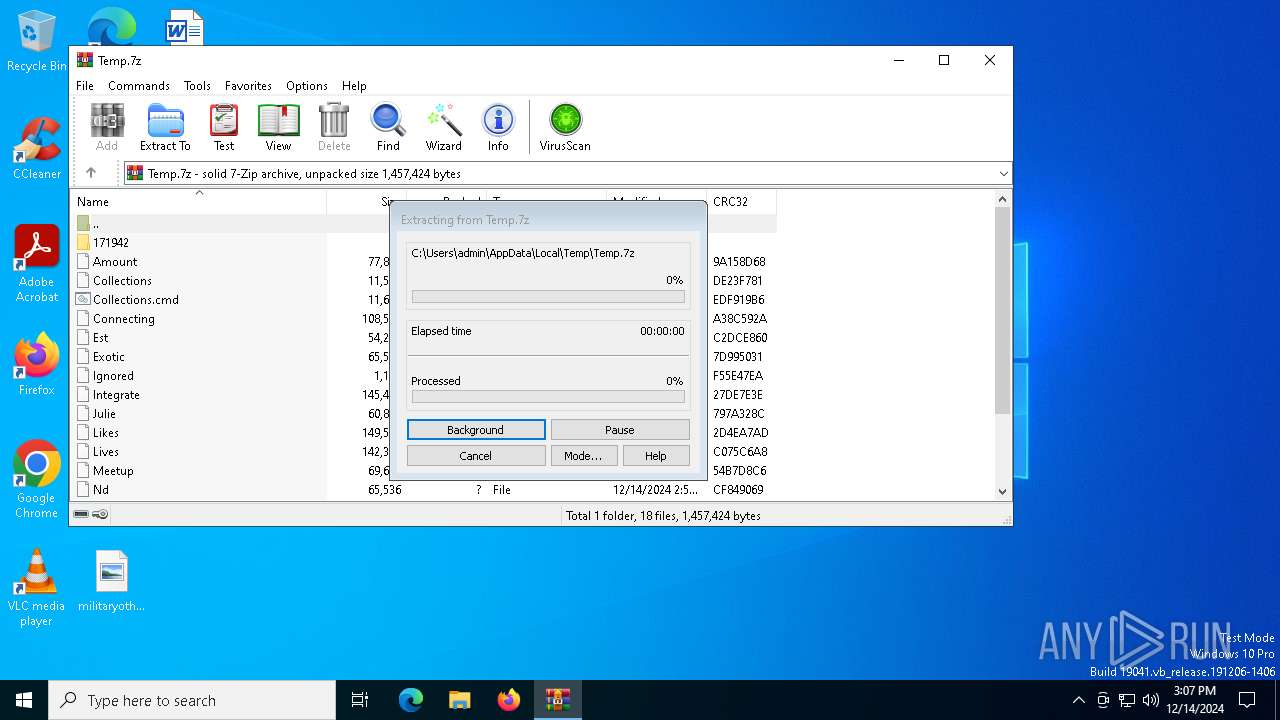
| 848 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Temp.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6832 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Collections.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6840 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6932 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo tasklist " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6940 | findstr /I "opssvc wrsa" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6976 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo tasklist " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6984 | findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 200
Read events
2 176
Write events
11
Delete events
13
Modification events
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Temp.7z | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 4 |
Value: | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 3 |
Value: | |||
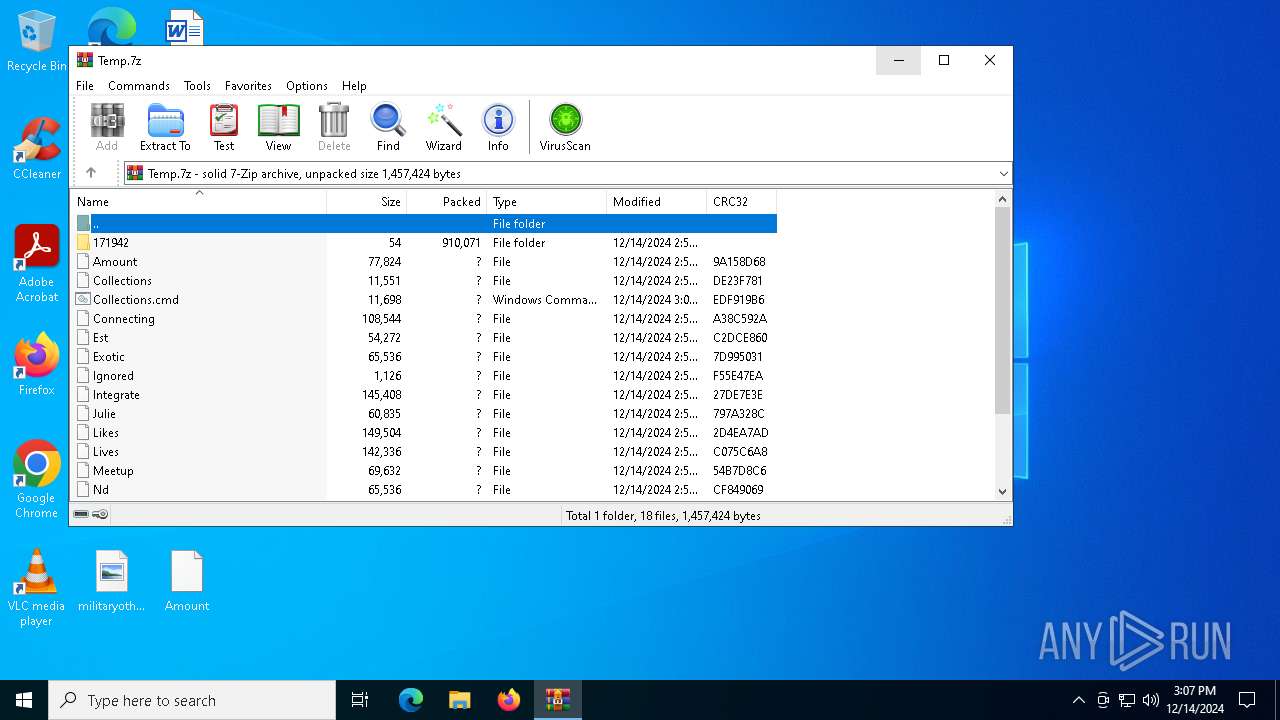
Executable files
0
Suspicious files
16
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 848 | WinRAR.exe | C:\Users\admin\Desktop\171942\San.com | text | |
MD5:E887EE1A0D4D6C9259E9FBB80FD9C037 | SHA256:136E46BD9EA401C05E275ECEFEAAABEC85D33F69AB67CDB278011BFB6E7727B4 | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Julie | binary | |
MD5:3D24BE0D9369F3DD0548DC07BD5F18D1 | SHA256:9AFA79582AC6230EE9C59CB2A25EE25C9A1343E8F93EF4A6D39373545DAC83EC | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Collections | text | |
MD5:B3C238B7E47A251ACCC1745B0A0D61A6 | SHA256:5E0CFAE4B29B000CA3F9929A82DC4D53531116A5B1D8B019FA539D0C612696C8 | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Integrate | binary | |
MD5:D6F490FF5BA765BD10DE9813B6945ABF | SHA256:CABBC9151C20B926819086B4CC7621CD57003549BBE81C8899D52A229B6752D4 | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Est | binary | |
MD5:3F22D6A8AA725F84141C970B4B7A1D9F | SHA256:E3FE85D90BD5ACFC60D88923EFA0EE8E206552BBD8A732C6FF7480FFEA5E5251 | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Exotic | binary | |
MD5:8EC7B49145758ACDBE52BA63E790E560 | SHA256:CBCC4A791D90BE6F6FBDA08234993E630F84A82E2B817F6FDDFE7AD88D794AA0 | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Likes | binary | |
MD5:B59E0FE24DFA3A7326D29B7EBFFA6736 | SHA256:2CEC9B111D68CD730158F6A82AD1F3D90205E3A3ADE21BF5B9247A9C01FCE67B | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Lives | binary | |
MD5:8E742197F01F0DCA5D0237B967DA77BB | SHA256:45A411A63D6F99768E0B8AA76062095E6E14B1DAFFA0889A5F525BD713C8676A | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Amount | binary | |
MD5:99FDECBC55D8785374EA17615D48DDF5 | SHA256:3F82F9DF19639E68E8C8D4E98A7BC8029FC81EC2F0CAAB9CFE2539D70BAD7568 | |||
| 848 | WinRAR.exe | C:\Users\admin\Desktop\Collections.cmd | text | |
MD5:0C122A1741A44C16A06671E45ED72F35 | SHA256:644CDD6C9398126153ED446D9785064C5286D6EA0556C45E61D20F752A9DEB69 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6256 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4944 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4944 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6068 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |