| File name: | Adobe Download Manager |
| Full analysis: | https://app.any.run/tasks/a6f9191e-89f2-4e59-af90-e9cc870947c1 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2025, 12:48:44 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | AE3158C94D6BB744991E0320F74770D6 |
| SHA1: | EB7B05F055AD2F443D7F8D9F02812BCDB57B1603 |
| SHA256: | 0966555BD577A1A3D45655422D0D41DF77EB1834B93A56288ED336593B402D0E |
| SSDEEP: | 196608:dIskkv4HikWy3xKB9XBXuHC8a7wX/QCaTUJmQwVAJqvg6qESvLxmm/hZmhqaiaTJ:gSTZCMX0Y3OCfOKDrzQXz54d |
MALICIOUS
Changes Windows Defender settings
- Adobe Download Manager.exe (PID: 1204)
- chrome.exe (PID: 1248)
Adds path to the Windows Defender exclusion list
- Adobe Download Manager.exe (PID: 1204)
- chrome.exe (PID: 1248)
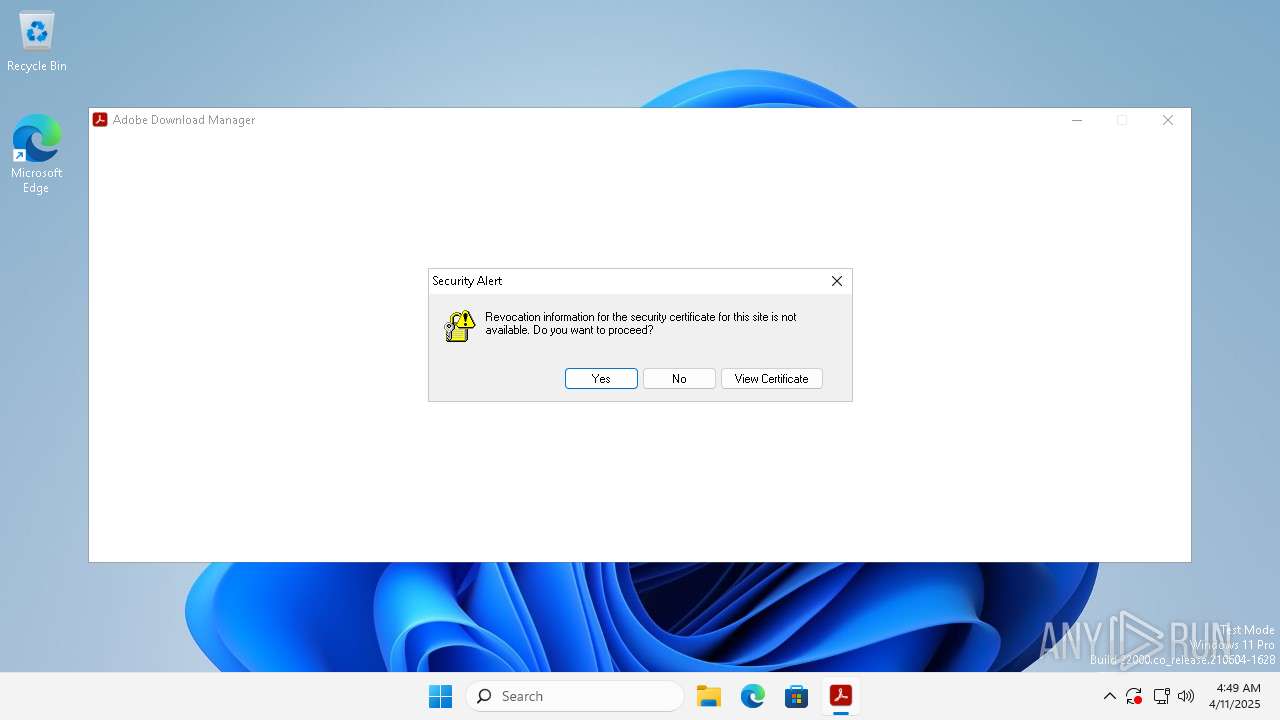
Executing a file with an untrusted certificate
- chrome.exe (PID: 2268)
- chrome.exe (PID: 1248)
- chrome.exe (PID: 5600)
Uses Task Scheduler to run other applications
- chrome.exe (PID: 2268)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- Adobe Download Manager.exe (PID: 1204)
- chrome.exe (PID: 1248)
Script adds exclusion path to Windows Defender
- Adobe Download Manager.exe (PID: 1204)
- chrome.exe (PID: 1248)
Reads security settings of Internet Explorer
- Adobe Download Manager.exe (PID: 436)
- Reader_br_install.exe (PID: 2660)
Starts CMD.EXE for commands execution
- chrome.exe (PID: 5600)
Checks for external IP
- svchost.exe (PID: 1660)
- Adobe Download Manager.exe (PID: 1204)
- Adobe Download Manager.exe (PID: 436)
- chrome.exe (PID: 5600)
Executable content was dropped or overwritten
- Adobe Download Manager.exe (PID: 1204)
- Adobe Download Manager.exe (PID: 436)
Reads the Internet Settings
- Reader_br_install.exe (PID: 2660)
- Adobe Download Manager.exe (PID: 436)
Reads settings of System Certificates
- Reader_br_install.exe (PID: 2660)
Reads the date of Windows installation
- Adobe Download Manager.exe (PID: 436)
Application launched itself
- Adobe Download Manager.exe (PID: 436)
Executes as Windows Service
- SecurityHealthService.exe (PID: 3188)
Reads Internet Explorer settings
- Reader_br_install.exe (PID: 2660)
INFO
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5720)
- powershell.exe (PID: 3028)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5720)
- powershell.exe (PID: 3028)
The sample compiled with english language support
- chrome.exe (PID: 2268)
- Adobe Download Manager.exe (PID: 1204)
Node.js compiler has been detected
- chrome.exe (PID: 2268)
Reads Environment values
- Adobe Download Manager.exe (PID: 436)
- Adobe Download Manager.exe (PID: 1204)
Checks supported languages
- Adobe Download Manager.exe (PID: 1204)
- Adobe Download Manager.exe (PID: 436)
- Reader_br_install.exe (PID: 2660)
Reads product name
- Adobe Download Manager.exe (PID: 1204)
- Adobe Download Manager.exe (PID: 436)
Reads the computer name
- Adobe Download Manager.exe (PID: 1204)
- Reader_br_install.exe (PID: 2660)
- Adobe Download Manager.exe (PID: 436)
Create files in a temporary directory
- Adobe Download Manager.exe (PID: 1204)
- Reader_br_install.exe (PID: 2660)
- Adobe Download Manager.exe (PID: 436)
Checks proxy server information
- Reader_br_install.exe (PID: 2660)
Creates files or folders in the user directory
- Reader_br_install.exe (PID: 2660)
Creates files in the program directory
- SecurityHealthService.exe (PID: 3188)
Reads security settings of Internet Explorer
- SecurityHealthService.exe (PID: 3188)
UPX packer has been detected
- Reader_br_install.exe (PID: 2660)
Reads the machine GUID from the registry
- Reader_br_install.exe (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:03 13:00:31+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 28081664 |
| InitializedDataSize: | 24252416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a84a3c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.790 |
| ProductVersionNumber: | 2.0.0.790 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Special build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft |
| ProductName: | Adobe Download Manager |
| FileDescription: | Adobe Download Manager |
| FileVersion: | 2.0.0.790 |
| ProductVersion: | 2.0.0.790 |
| OriginalFileName: | Adobe Download Manager |
| InternalName: | Microsoft |
| LegalCopyright: | Copyright 2019 Adobe Inc. All rights reserved. |
Total processes
133
Monitored processes
13
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Users\admin\AppData\Local\Temp\Adobe Download Manager.exe" | C:\Users\admin\AppData\Local\Temp\Adobe Download Manager.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Adobe Download Manager Exit code: 0 Version: 2.0.0.790 Modules
| |||||||||||||||
| 1204 | "C:\Users\admin\AppData\Local\Temp\Adobe Download Manager.exe" C:\Users\admin\AppData\Local\Temp\Adobe Download Manager.exe | C:\Users\admin\AppData\Local\Temp\Adobe Download Manager.exe | Adobe Download Manager.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Adobe Download Manager Exit code: 0 Version: 2.0.0.790 Modules
| |||||||||||||||
| 1248 | C:\Users\admin\AppData\Roaming\ChromeApplication\chrome.exe --own=799056 | C:\Users\admin\AppData\Roaming\ChromeApplication\chrome.exe | Adobe Download Manager.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 134.0.6998.167 Modules
| |||||||||||||||
| 1660 | C:\Windows\system32\svchost.exe -k NetworkService -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | C:\Users\admin\AppData\Roaming\ChromeApplication\chrome.exe --type=utility | C:\Users\admin\AppData\Roaming\ChromeApplication\chrome.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Chrome Version: 134.0.6998.167 Modules
| |||||||||||||||
| 2660 | C:\Users\admin\AppData\Local\Temp\Reader_br_install.exe | C:\Users\admin\AppData\Local\Temp\Reader_br_install.exe | Adobe Download Manager.exe | ||||||||||||
User: admin Company: Adobe Inc Integrity Level: HIGH Description: Adobe Download Manager Version: 2.0.0.790s Modules
| |||||||||||||||
| 3028 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe "Add-MpPreference -ExclusionPath C:\Users\admin\AppData\Roaming\ChromeApplication -Force" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3188 | C:\Windows\system32\SecurityHealthService.exe | C:\Windows\System32\SecurityHealthService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Security Health Service Version: 10.0.22000.1042 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3248 | \\?\C:\Windows\System32\SecurityHealthHost.exe {08728914-3F57-4D52-9E31-49DAECA5A80A} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 10.0.22000.1042 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3748 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 965
Read events
2 945
Write events
20
Delete events
0
Modification events
| (PID) Process: | (436) Adobe Download Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (436) Adobe Download Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (436) Adobe Download Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (436) Adobe Download Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2660) Reader_br_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2660) Reader_br_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2660) Reader_br_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2660) Reader_br_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2660) Reader_br_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2660) Reader_br_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
7
Suspicious files
15
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1204 | Adobe Download Manager.exe | C:\Users\admin\AppData\Roaming\ChromeApplication\chrome.exe | — | |
MD5:— | SHA256:— | |||
| 1204 | Adobe Download Manager.exe | C:\Users\admin\AppData\Local\Temp\cb1b8060.bak | — | |
MD5:— | SHA256:— | |||
| 3028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nv2acmch.0n2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5600 | chrome.exe | C:\Users\admin\AppData\Roaming\ChromeApplication\temp\00d31e0f4e | binary | |
MD5:14CCC9293153DEACBB9A20EE8F6FF1B7 | SHA256:3195CE0F7AA2EAE2B21C447F264E2BD4E1DC5208353AC72D964A750DE9A83511 | |||
| 3028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_q21ajegc.vml.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5600 | chrome.exe | C:\Users\admin\AppData\Roaming\ChromeApplication\bwdat\enc_flag | text | |
MD5:B326B5062B2F0E69046810717534CB09 | SHA256:B5BEA41B6C623F7C09F1BF24DCAE58EBAB3C0CDD90AD966BC43A45B44867E12B | |||
| 5600 | chrome.exe | C:\Users\admin\AppData\Roaming\ChromeApplication\temp\4297844ccf | binary | |
MD5:35AE56ED9518BF63EC530650FA3A493A | SHA256:341D0FF4FA34FB5E77FD3616DECD680A78CF9873915E59B659C43BA6AEB343C8 | |||
| 2268 | chrome.exe | C:\Windows\Temp\amd_64_browser.inf.resources_pi905f2cs0550a3a_7.2.22992.0_none_21yyw11db43e3187k\d1f6e50334a50a3f1f8e35e02d788ad9.node | executable | |
MD5:0014FBE11B52C2BA8E25A66398245A22 | SHA256:DF856226949D7749D87F6376A0F3391B597C4EDC214E0BA2523DB24D4BF3D554 | |||
| 5720 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:10E2A201FED254AEC04F615E1CFC8959 | SHA256:4DEDBCBCD0DE6935525F52308A216BF85DA498413F191D87BC6B8ABF2B170F90 | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Roaming\ChromeApplication\library\dxcompiler.dll | executable | |
MD5:1C0C56F2C5B473DF1D4EE170DFFDEB18 | SHA256:6C0BDFC146319EA414C00818A69E8E630C7AE5642310E43D8A4CEEF83603A20F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
149
DNS requests
30
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1568 | svchost.exe | GET | 200 | 23.50.131.200:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8f8099286902d6c5 | unknown | — | — | whitelisted |
1568 | svchost.exe | GET | 200 | 23.50.131.200:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7a1b9bad01c53fa7 | unknown | — | — | whitelisted |
1204 | Adobe Download Manager.exe | GET | 200 | 208.95.112.1:80 | http://208.95.112.1:80/json | unknown | — | — | unknown |
436 | Adobe Download Manager.exe | GET | 200 | 208.95.112.1:80 | http://208.95.112.1:80/json | unknown | — | — | unknown |
5600 | chrome.exe | GET | 200 | 208.95.112.1:80 | http://208.95.112.1:80/json | unknown | — | — | unknown |
3828 | MoUsoCoreWorker.exe | GET | 200 | 95.101.54.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?136d07a8c7673d05 | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.146:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
5600 | chrome.exe | GET | 200 | 208.95.112.1:80 | http://208.95.112.1:80/json | unknown | — | — | unknown |
3828 | MoUsoCoreWorker.exe | GET | 200 | 95.101.54.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?05c39ed7a099fae8 | unknown | — | — | whitelisted |
— | — | GET | 101 | 31.220.98.29:443 | https://floravirtual.com.br/socket.io/?EIO=4&transport=websocket&sid=yslyOKxK60SfFE0zAGOO | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1568 | svchost.exe | 23.50.131.200:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
5752 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 23.53.40.146:80 | www.msftconnecttest.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.36.5.94:443 | geo.prod.do.dsp.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
www.msftconnecttest.com |
| whitelisted |
geo.prod.do.dsp.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ip-api.com |
| whitelisted |
tunneloop.com.br |
| unknown |
use.typekit.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
1660 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
1660 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
436 | Adobe Download Manager.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
1204 | Adobe Download Manager.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
— | — | Unknown Traffic | ET USER_AGENTS Node XMLHTTP User-Agent |
— | — | Unknown Traffic | ET USER_AGENTS Node XMLHTTP User-Agent |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Socket.IO requests event-based bidirectional communication via HTTP |
— | — | Unknown Traffic | ET USER_AGENTS Node XMLHTTP User-Agent |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |