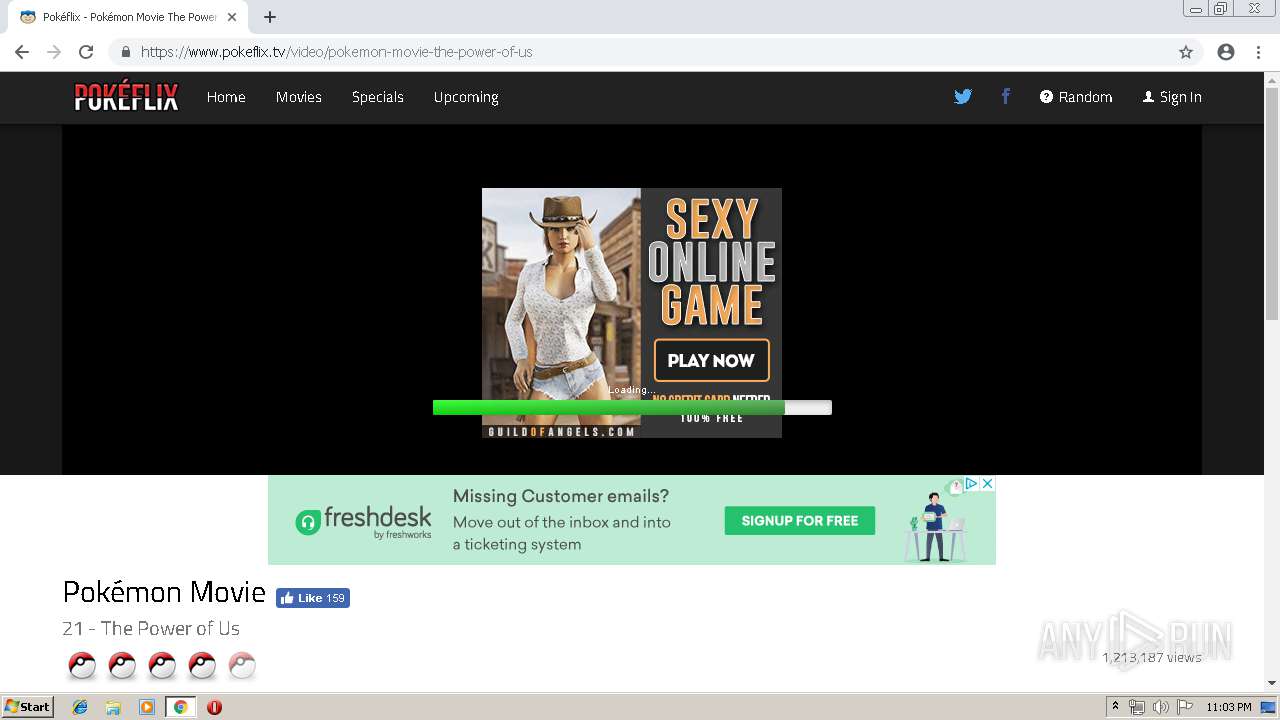
| URL: | https://www.pokeflix.tv/movies/ |
| Full analysis: | https://app.any.run/tasks/877bcd06-8fd0-4452-91ac-48490443ee54 |
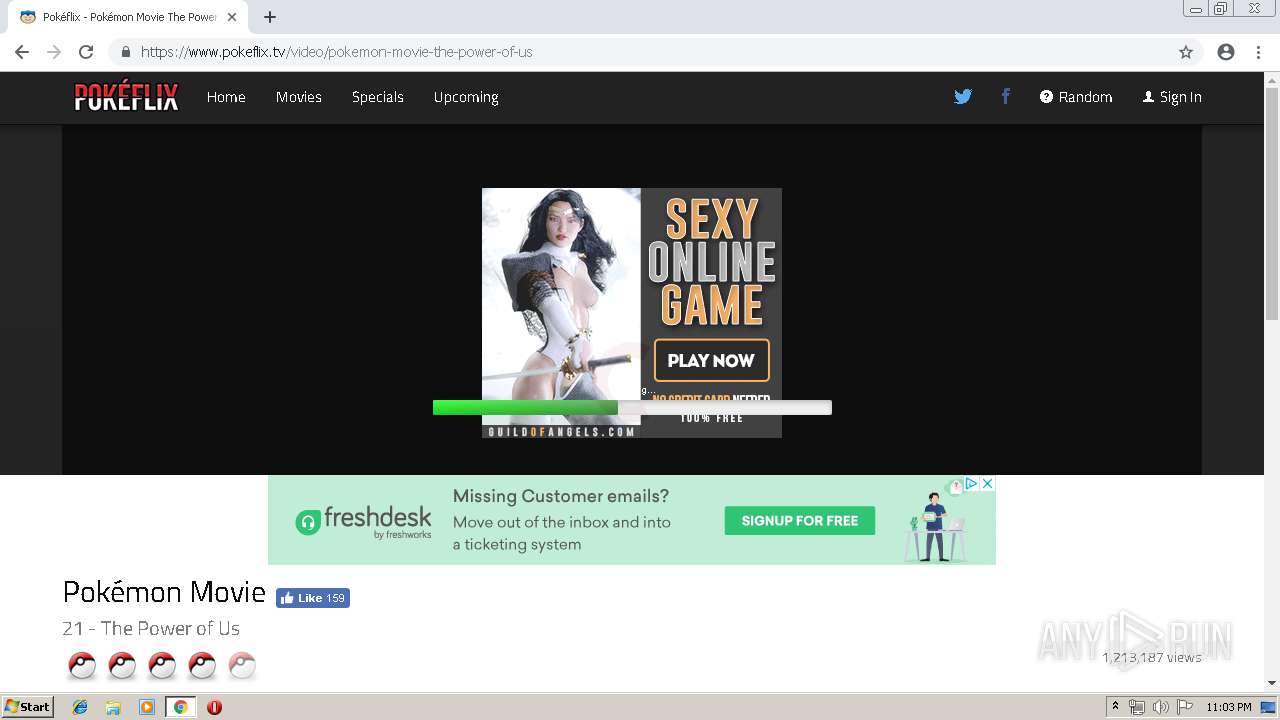
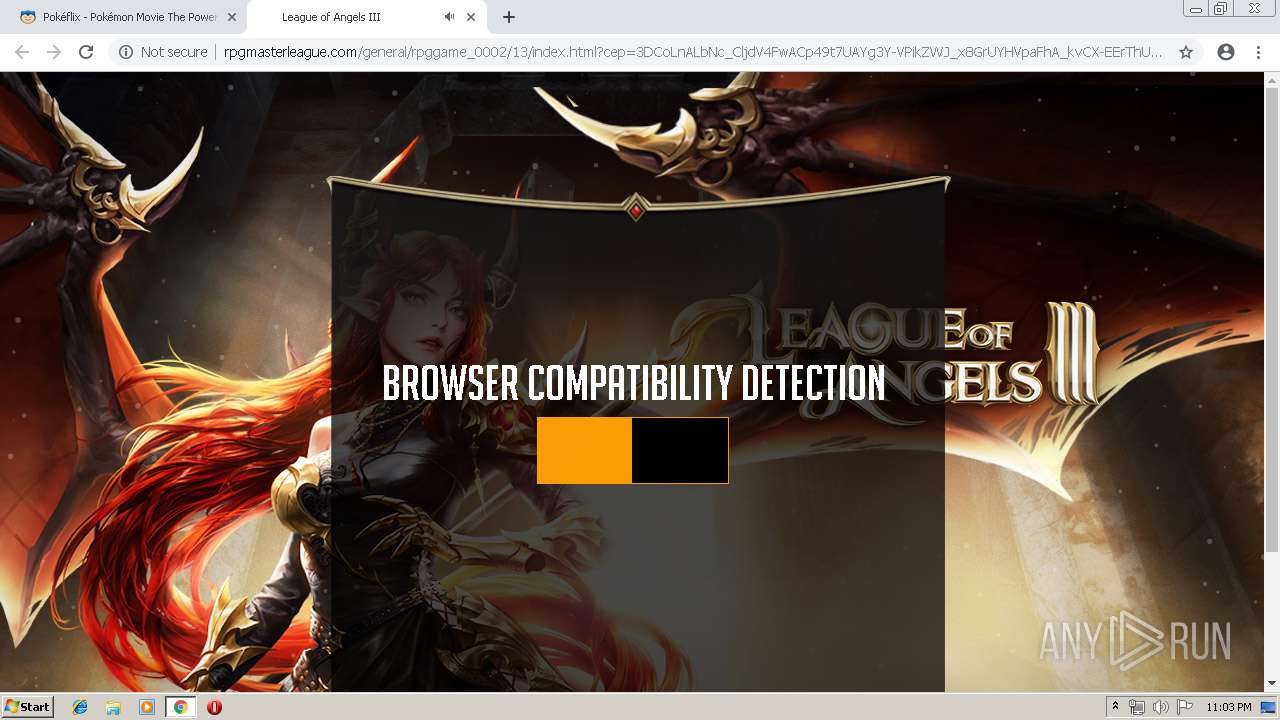
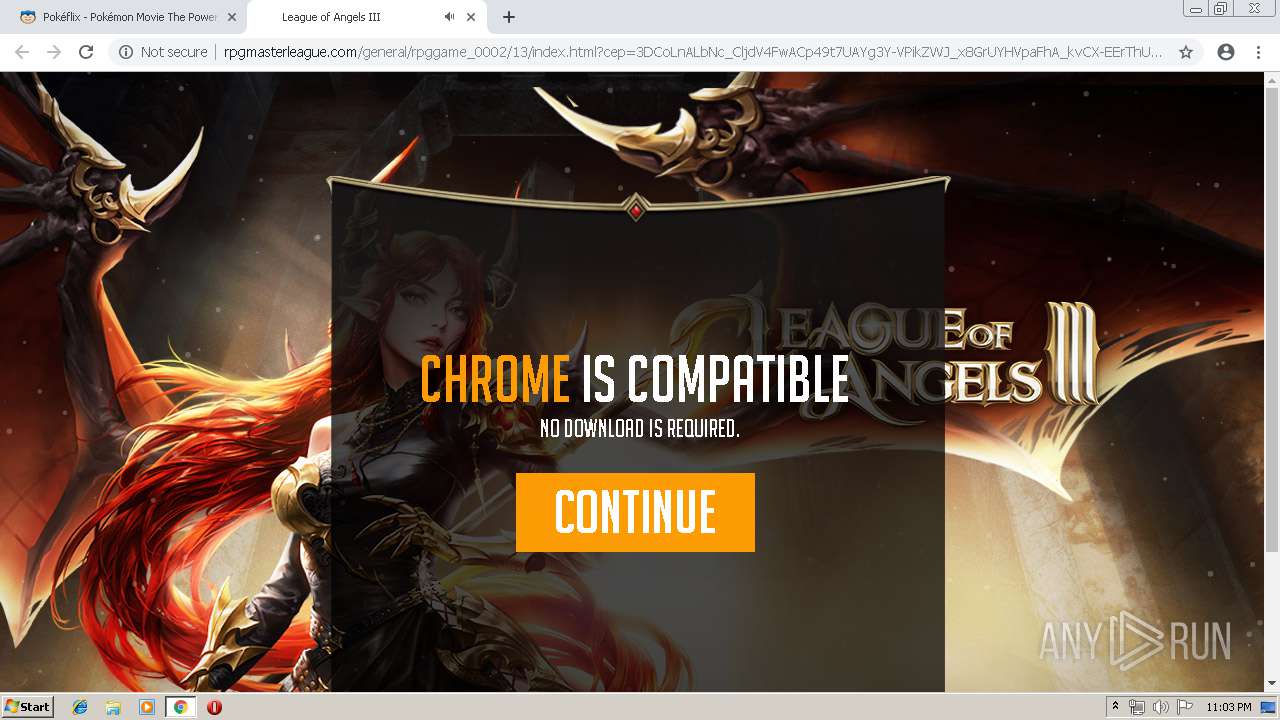
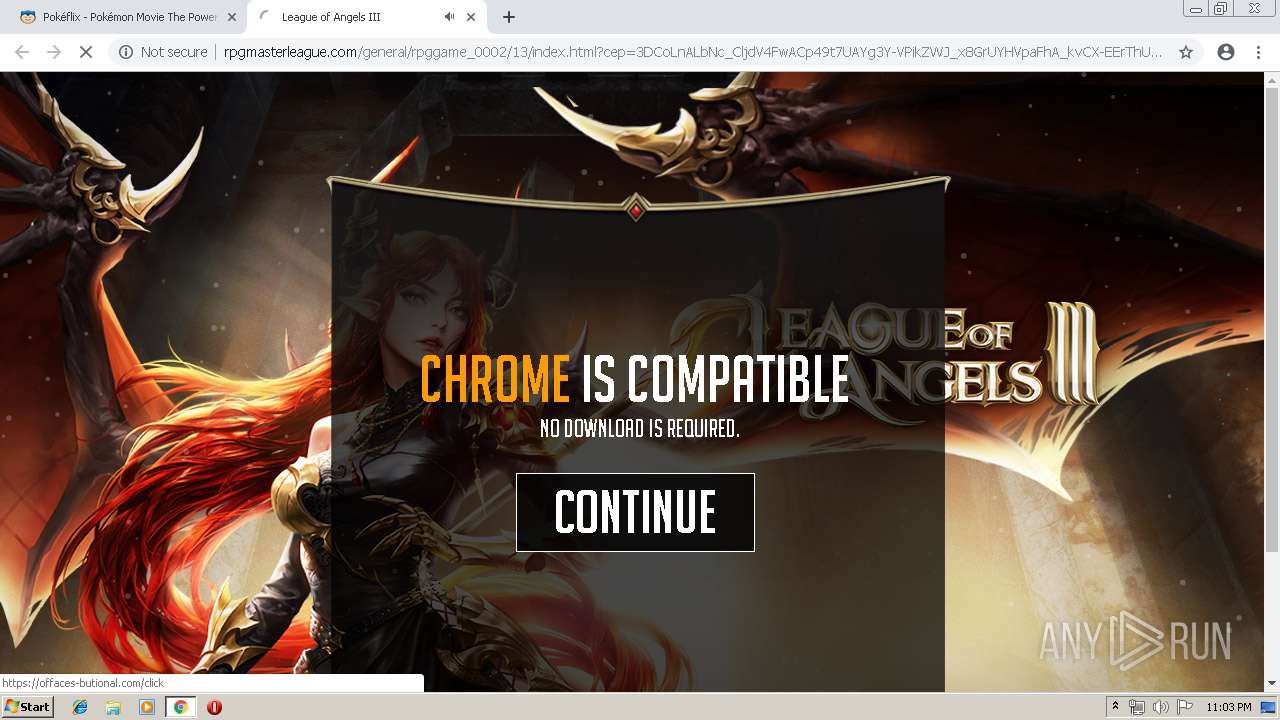
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2019, 22:02:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F0C6C6EF52DE9722A0985ED633F7AEC4 |
| SHA1: | 5B273D428E5C8B86E39D89194A88153F9B5BCE17 |
| SHA256: | 096529511881F5DE7CB047F3A5E0CFAFEB074F5BDC610B250D4AF6082BFA2717 |
| SSDEEP: | 3:N8DSL6J4lm:2OLib |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3040)
INFO
Application launched itself
- chrome.exe (PID: 3040)
Reads settings of System Certificates
- chrome.exe (PID: 2420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
31
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1028209968923288126 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1028209968923288126 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa10f18,0x6fa10f28,0x6fa10f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11712245969348023633 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17178344355861402813 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17178344355861402813 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7001129769703531439 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7001129769703531439 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6552396231026770309 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6552396231026770309 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8324786270415231242 --mojo-platform-channel-handle=2532 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13458979464860854711 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13458979464860854711 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4664 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2517409576668401881 --mojo-platform-channel-handle=1464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13572677733993323321 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13572677733993323321 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
613
Read events
517
Write events
92
Delete events
4
Modification events
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3352) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3040-13199407367539750 |
Value: 259 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3040-13199407367539750 |
Value: 259 | |||
Executable files
0
Suspicious files
153
Text files
168
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1fd514b2-b2df-43fa-8582-359af64ed3a4.tmp | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
177
DNS requests
97
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
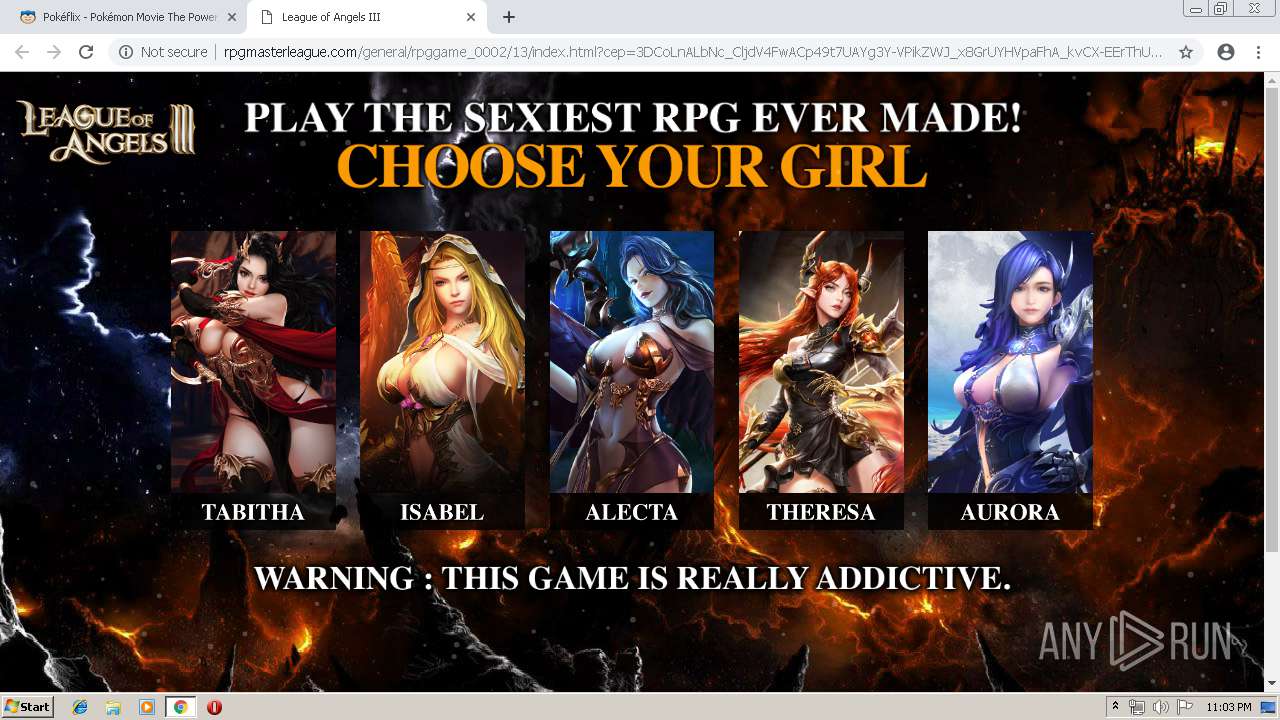
2420 | chrome.exe | GET | — | 198.24.162.123:80 | http://server.cpmstar.com/click.aspx?poolid=76839&subpoolid=0&campaignid=428139&creativeid=1128420&url= | US | — | — | suspicious |
2420 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
2420 | chrome.exe | GET | 200 | 104.28.19.102:80 | http://rpgmasterleague.com/js/push/push.js | US | text | 1.18 Kb | suspicious |
2420 | chrome.exe | GET | 200 | 104.28.19.102:80 | http://rpgmasterleague.com/general/rpggame_0002/13/index_files/img/v1/en/lg.css | US | text | 188 b | suspicious |
2420 | chrome.exe | GET | 200 | 104.28.19.102:80 | http://rpgmasterleague.com/general/rpggame_0002/13/index_files/validation.css | US | text | 853 b | suspicious |
2420 | chrome.exe | GET | 200 | 176.126.58.208:80 | http://r5---sn-x2pm-3ufk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=31.204.150.72&mm=28&mn=sn-x2pm-3ufk&ms=nvh&mt=1554933682&mv=m&pcm2cms=yes&pl=22&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
2420 | chrome.exe | GET | 200 | 104.28.19.102:80 | http://rpgmasterleague.com/general/rpggame_0002/13/index_files/img/girl-1-thumb.jpg | US | image | 110 Kb | suspicious |
2420 | chrome.exe | GET | 200 | 104.28.19.102:80 | http://rpgmasterleague.com/general/rpggame_0002/13/index_files/html5lightbox.js | US | text | 20.3 Kb | suspicious |
2420 | chrome.exe | GET | 200 | 104.28.19.102:80 | http://rpgmasterleague.com/general/rpggame_0002/13/index_files/animate.css | US | text | 4.27 Kb | suspicious |
2420 | chrome.exe | GET | 200 | 104.28.19.102:80 | http://rpgmasterleague.com/general/rpggame_0002/13/index_files/img/girl-2-thumb.jpg | US | image | 113 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | chrome.exe | 216.58.207.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 216.58.205.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 46.19.139.18:443 | www.pokeflix.tv | Private Layer INC | CH | unknown |
2420 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 216.58.206.13:443 | — | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.22.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 104.25.124.99:443 | code.ionicframework.com | Cloudflare Inc | US | shared |
2420 | chrome.exe | 104.25.80.5:443 | static.pokemon-vortex.com | Cloudflare Inc | US | shared |
2420 | chrome.exe | 172.217.22.34:443 | adservice.google.nl | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.18.98:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.pokeflix.tv |
| unknown |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
code.ionicframework.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
certify-js.alexametrics.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2420 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2420 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2420 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |