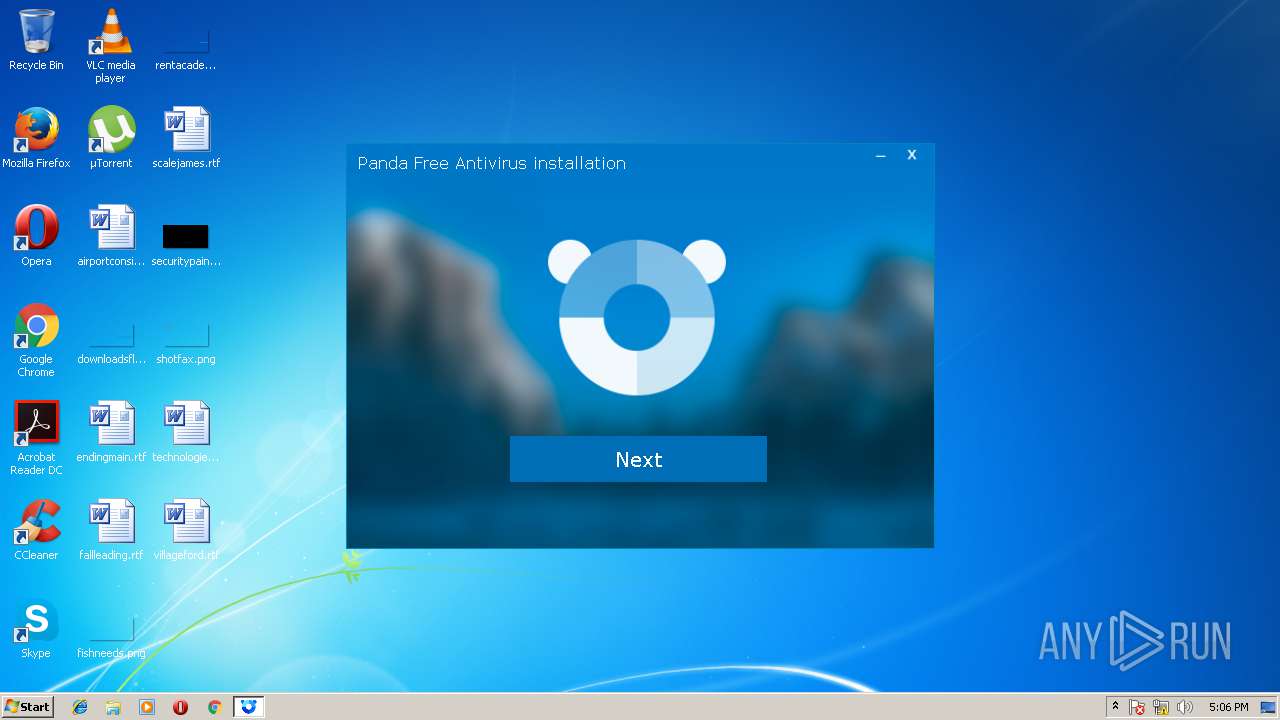
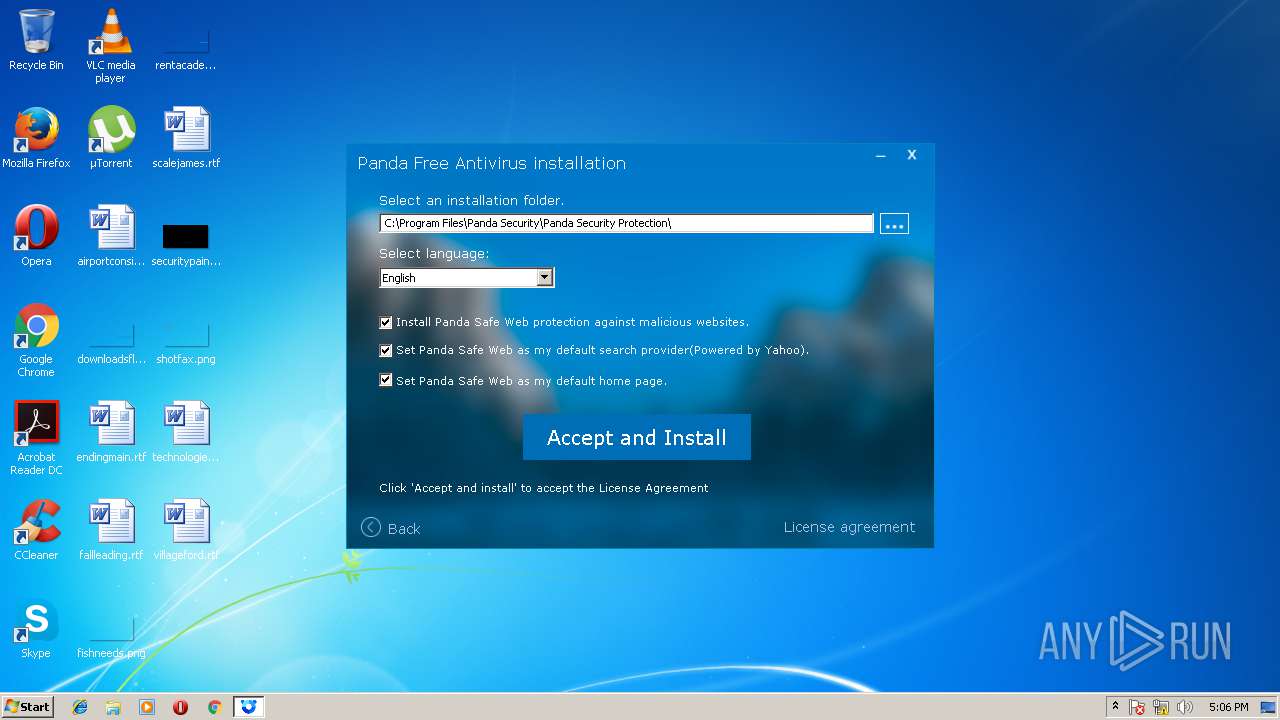
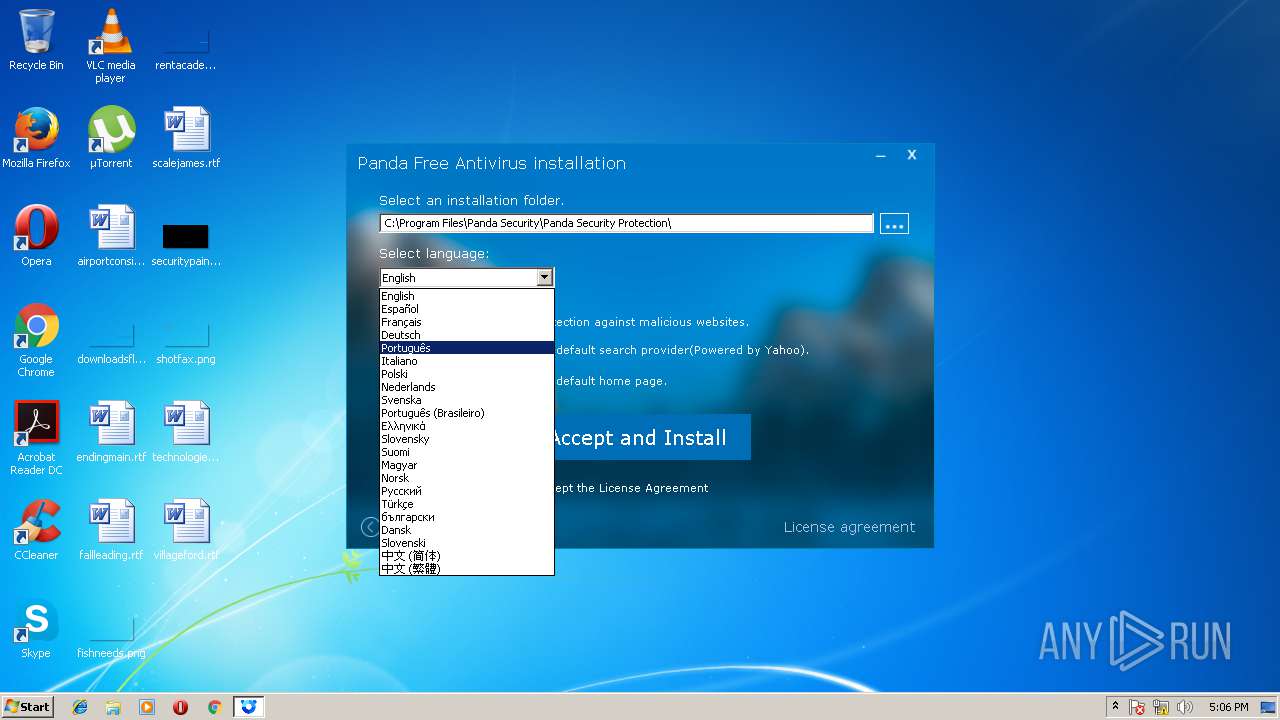
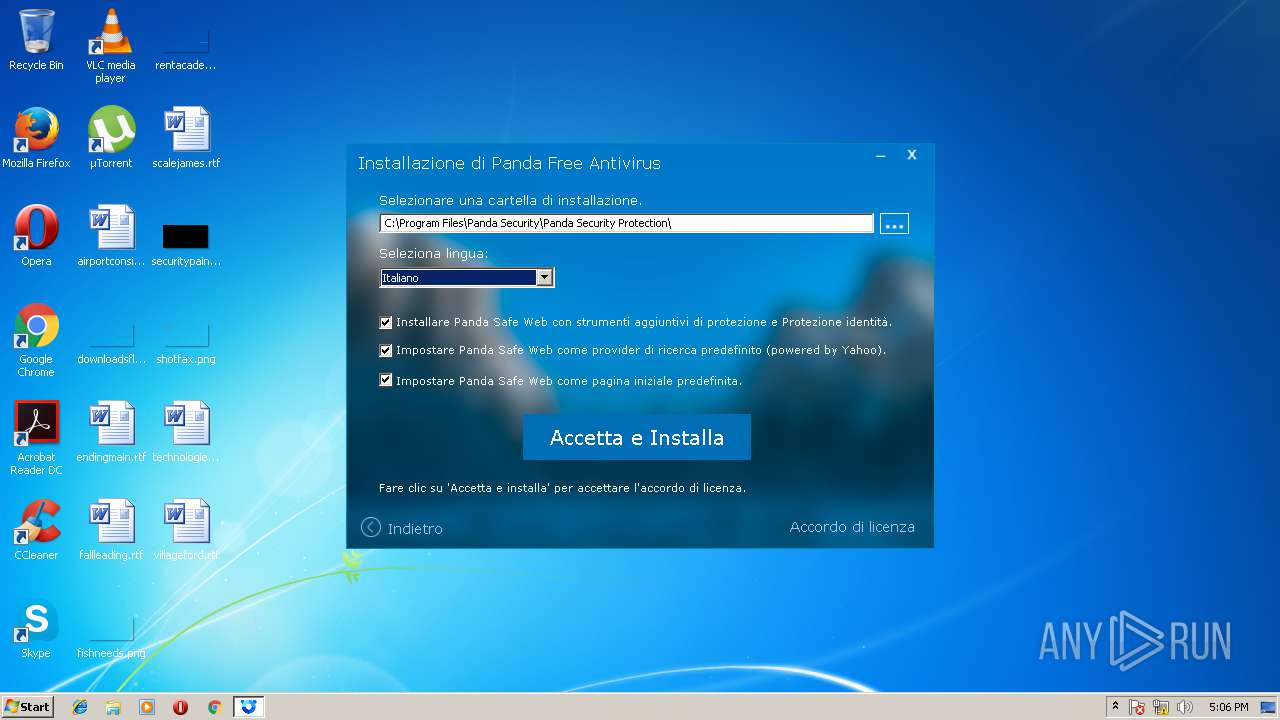
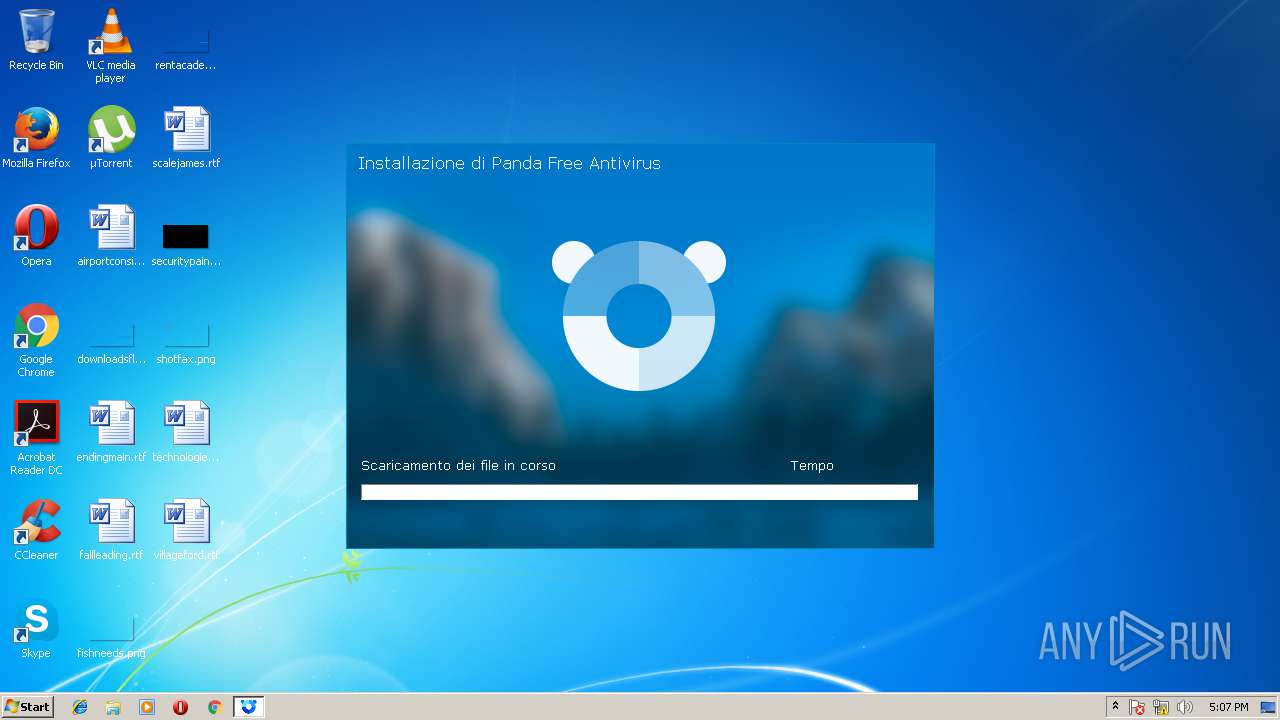
| File name: | PANDAFREEAV.exe |
| Full analysis: | https://app.any.run/tasks/0f32bed5-db17-4724-8666-efb5d12aeb1a |
| Verdict: | No threats detected |
| Analysis date: | March 08, 2018, 17:06:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BFFE6879A728B8E416AF76EF402DCE51 |
| SHA1: | 4BD9C70E75DB2E21C4BA958F0E366576E1994D5D |
| SHA256: | 095D93E4FC30AB9D53536FF3DAB69BBA67ADC1A54E391BCE60BF5371526C00E3 |
| SSDEEP: | 49152:qar2cZCM1lulIWLyOjdogjzygQGNJ1qSxfuceB:XSPM1NFOji2JQGNJ1quucK |
MALICIOUS
Application loaded dropped or rewritten executable
- Stub.exe (PID: 2352)
Application was dropped or rewritten from another process
- Stub.exe (PID: 2352)
SUSPICIOUS
Creates files in the program directory
- Stub.exe (PID: 2352)
INFO
Dropped object may contain URL's
- PANDAFREEAV.exe (PID: 3556)
- Stub.exe (PID: 2352)
Loads rich edit control libraries
- Stub.exe (PID: 2352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:28 10:47:25+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 130048 |
| InitializedDataSize: | 379392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19702 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 15.14.3.0 |
| ProductVersionNumber: | 15.14.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Panda Security, S.L. |
| FileDescription: | Panda Security SFX |
| FileVersion: | 15.14.3.0 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | © Panda 2016 |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | Panda Security SelfExtrator |
| ProductVersion: | 15.14 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Apr-2016 08:47:25 |
| Detected languages: |
|
| CompanyName: | Panda Security, S.L. |
| FileDescription: | Panda Security SFX |
| FileVersion: | 15.14.3.0 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | © Panda 2016 |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | Panda Security SelfExtrator |
| ProductVersion: | 15.14 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 28-Apr-2016 08:47:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001FB61 | 0x0001FC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62376 |
.rdata | 0x00021000 | 0x000076B6 | 0x00007800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.65546 |
.data | 0x00029000 | 0x000045A4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.98703 |
.rsrc | 0x0002E000 | 0x00053868 | 0x00053A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.93947 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21494 | 1429 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.24448 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.72936 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.48017 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.5553 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.29066 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.80136 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 1.9242 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 2.59555 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 3.23577 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2352 | ".\Stub.exe" /c "181305" /u "http://acs.pandasoftware.com/Panda/FREEAV/181305/FREEAV.exe" /a "CNTPZFPR1M1016" /p "4252" | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\Stub.exe | — | PANDAFREEAV.exe | |||||||||||
User: admin Company: Panda Security, S.L. Integrity Level: HIGH Exit code: 0 Version: 5.0.15.0 Modules
| |||||||||||||||
| 3012 | "C:\Users\admin\AppData\Local\Temp\PANDAFREEAV.exe" | C:\Users\admin\AppData\Local\Temp\PANDAFREEAV.exe | — | explorer.exe | |||||||||||
User: admin Company: Panda Security, S.L. Integrity Level: MEDIUM Description: Panda Security SFX Exit code: 3221226540 Version: 15.14.3.0 Modules
| |||||||||||||||
| 3556 | "C:\Users\admin\AppData\Local\Temp\PANDAFREEAV.exe" | C:\Users\admin\AppData\Local\Temp\PANDAFREEAV.exe | explorer.exe | ||||||||||||
User: admin Company: Panda Security, S.L. Integrity Level: HIGH Description: Panda Security SFX Exit code: 0 Version: 15.14.3.0 Modules
| |||||||||||||||
Total events
40
Read events
22
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2352) Stub.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stub_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
8
Suspicious files
1
Text files
259
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\res\final_img.png | image | |
MD5:— | SHA256:— | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\res\img_product2.png | image | |
MD5:— | SHA256:— | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\res\img_product1.png | image | |
MD5:— | SHA256:— | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\Stubinstaller.ini | text | |
MD5:— | SHA256:— | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\res\background.png | image | |
MD5:— | SHA256:— | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\InstallRes.dll | executable | |
MD5:— | SHA256:— | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\recorte_cloud.png | image | |
MD5:F037258F333D7967D5CB7672AE0DD4CA | SHA256:226928BD446DBF9542DBDE8D38367194DCCA65C18A552F4F26DAF30520E41822 | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\avDetect.dat | gpg | |
MD5:9A17B5AC44705CC4BC3608C6232E1F16 | SHA256:4AD849F737B18084B060828C7CCA48BCF512CC2ADA2A937F5CFBAB79F1B29677 | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\StubInstaller.dat | binary | |
MD5:238DCAB1CB4709A2CB212A4ACF1944D2 | SHA256:17B5F3D0697F2B41CF09D65F595E030B90DE23B2AFCDFB85BE1969B57C9A4B72 | |||
| 3556 | PANDAFREEAV.exe | C:\Users\admin\AppData\Local\Temp\7zS4ED235F1\CommsWrapper.dll | executable | |
MD5:DE835B63304969AAB279FD08FF927A8D | SHA256:A474A520C9DAC0E66678A967E9B94923FCBD084E449403399F96B1F0879CF0E6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
11
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_1_it.png | AT | — | — | whitelisted |
— | — | GET | — | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_1_en.png | AT | — | — | whitelisted |
— | — | GET | — | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_3_it.png | AT | — | — | whitelisted |
— | — | GET | 200 | 137.135.129.175:80 | http://eventtrack.pandasecurity.com/track/install/details.html?ProductID=4252&Stub_Event=Start&_ei=4139ABCA-B9D9-43C4-83F7-14197C3809FF&_es=1&_et=Stub&_lt=20180308170635 | IE | — | — | whitelisted |
— | — | GET | — | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_3_it.png | AT | — | — | whitelisted |
— | — | GET | — | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_4_it.png | AT | — | — | whitelisted |
— | — | GET | 200 | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_4_it.png | AT | image | 170 Kb | whitelisted |
— | — | GET | 200 | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_4_it.png | AT | image | 170 Kb | whitelisted |
— | — | GET | — | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_2_it.png | AT | — | — | whitelisted |
— | — | GET | — | 2.21.246.64:80 | http://acs.pandasoftware.com/Panda/FREEAV/img_pp/Page_2_it.png | AT | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 137.135.129.175:80 | eventtrack.pandasecurity.com | Microsoft Corporation | IE | whitelisted |
— | — | 2.21.246.64:80 | acs.pandasoftware.com | Akamai International B.V. | AT | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eventtrack.pandasecurity.com |
| unknown |
acs.pandasoftware.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |