| File name: | newILY.ps1 |
| Full analysis: | https://app.any.run/tasks/85c0c25d-e73c-460b-abbc-3b38e7a4d0b4 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2024, 23:03:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (7460), with CRLF line terminators |
| MD5: | FF4627D5247A84643BE462EA8AB64FEF |
| SHA1: | 0002757ED5D8DB1422F18CA35D6D1702C3C6149A |
| SHA256: | 094DD036E6DA7A8D04943DD1EFEA9A48A7730FF61E8FB1E22FE4950BBFB4CD76 |
| SSDEEP: | 192:d9QJ6LH6vI2MMgucnCU+PcEE/5AR3XumFaMay:DQJ6LH6w2MVrycEE/uR3+mF |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6684)
Drops known malicious image
- powershell.exe (PID: 6684)
SUSPICIOUS
Group Policy Discovery via Microsoft GPResult Utility
- powershell.exe (PID: 6684)
Uses NLTEST.EXE to test domain trust
- powershell.exe (PID: 6684)
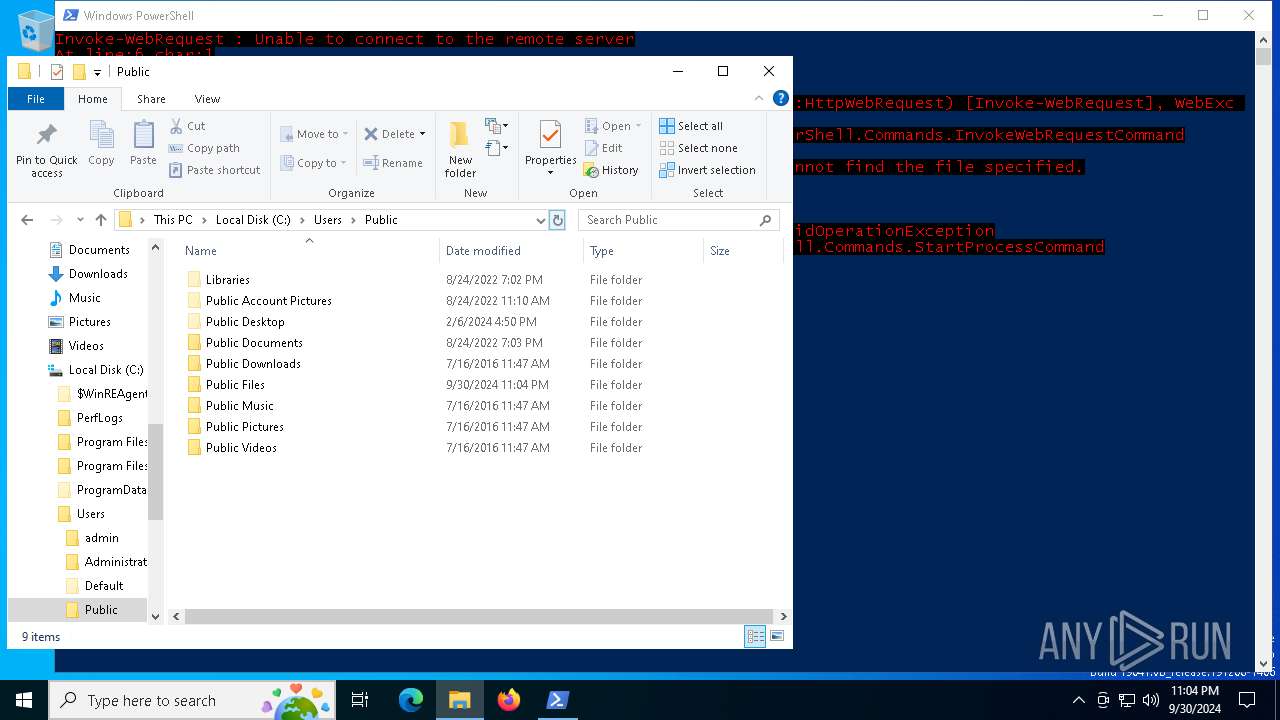
Executable content was dropped or overwritten
- powershell.exe (PID: 6684)
Uses WMIC.EXE to obtain Windows Installer data
- powershell.exe (PID: 6684)
Connects to unusual port
- powershell.exe (PID: 6684)
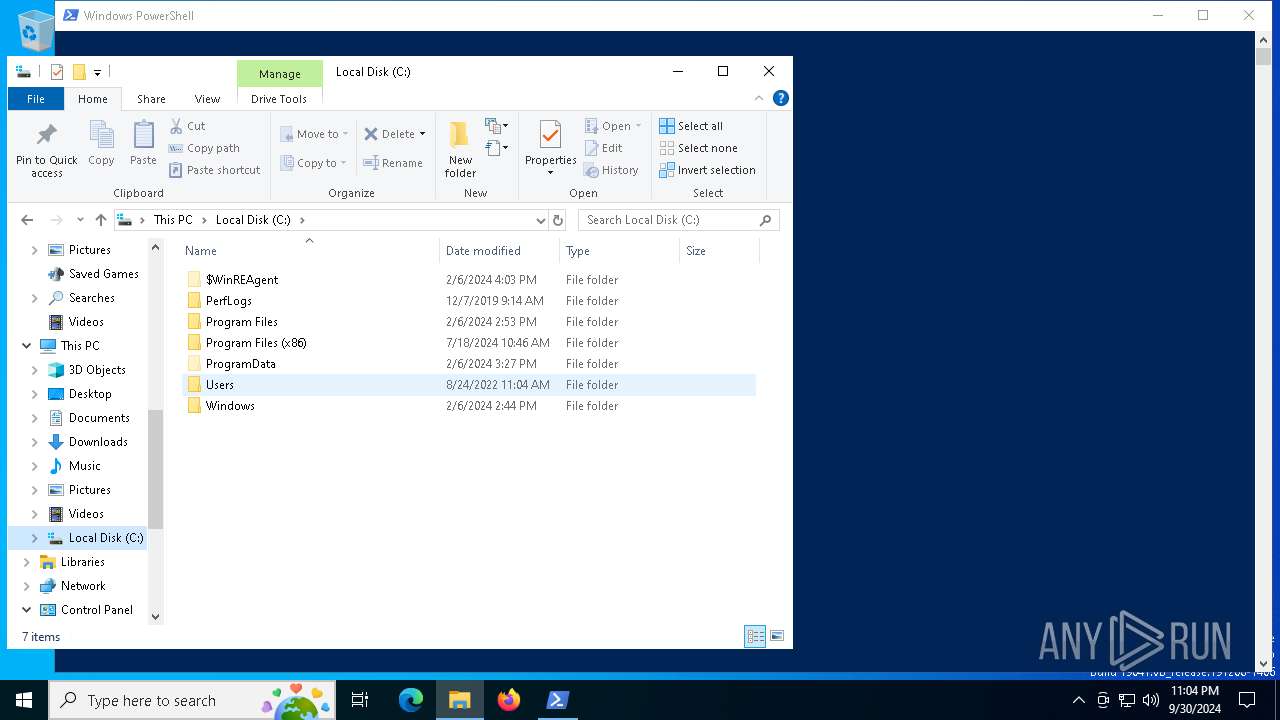
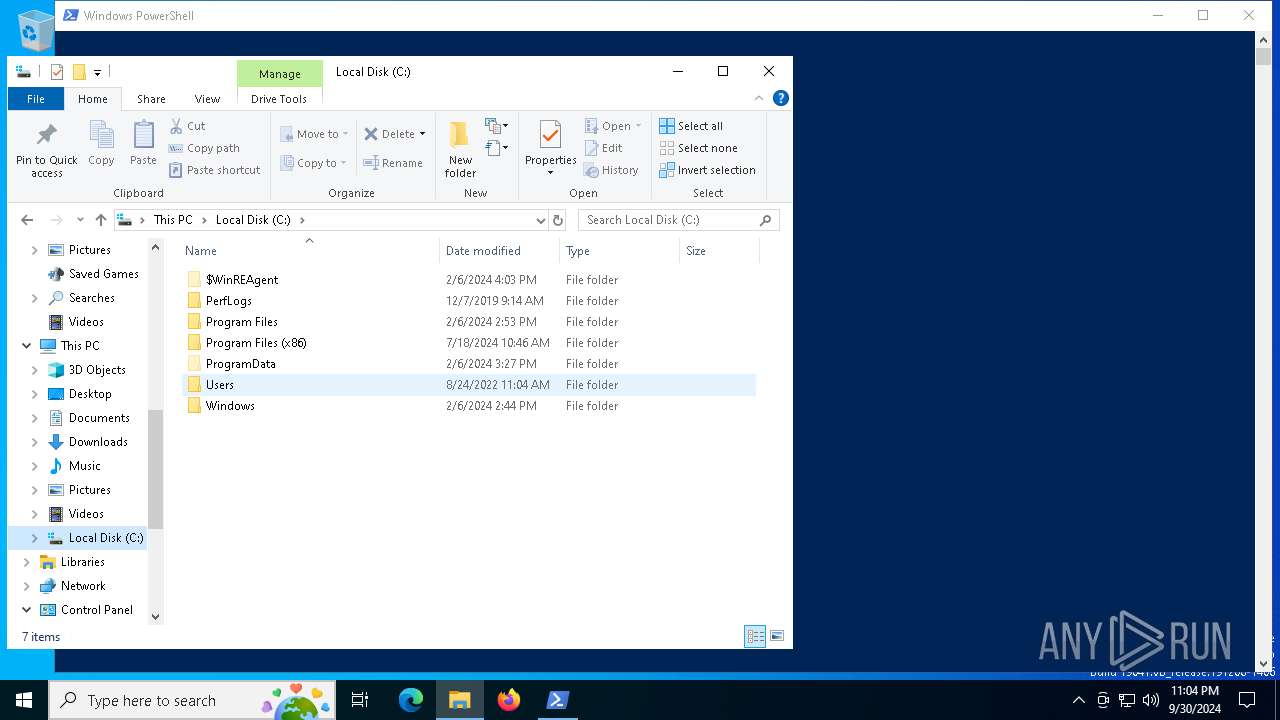
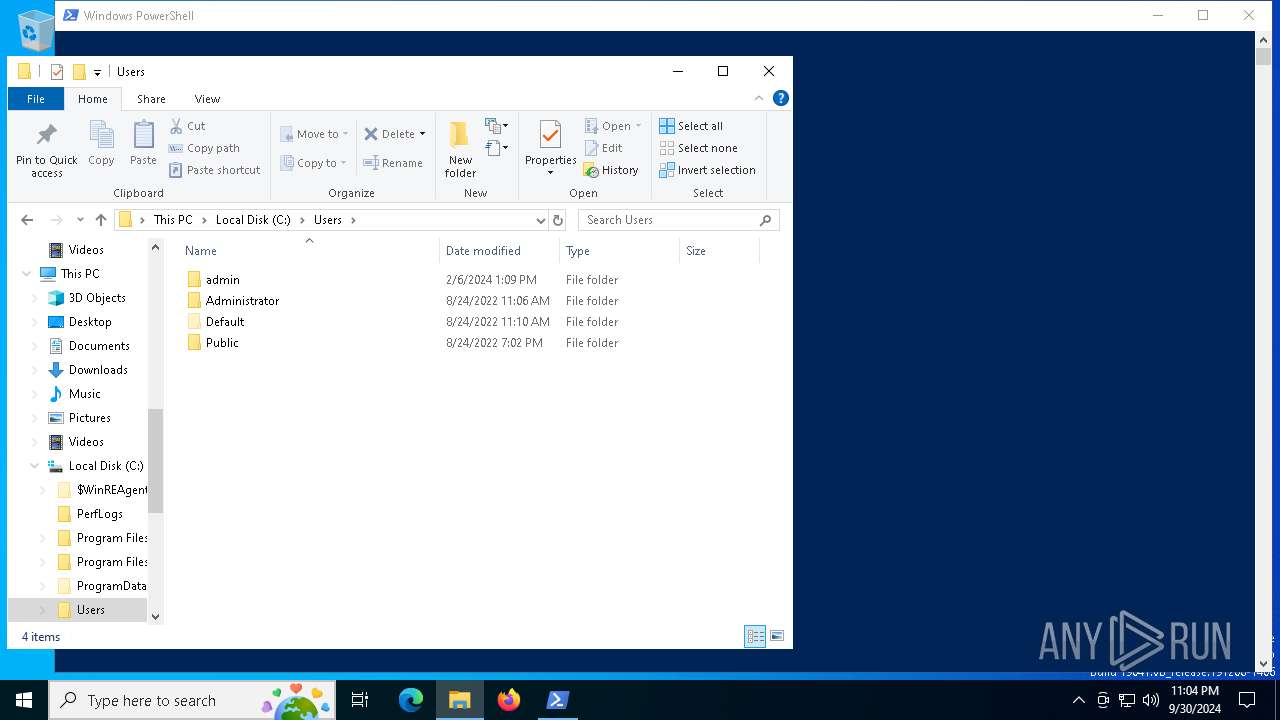
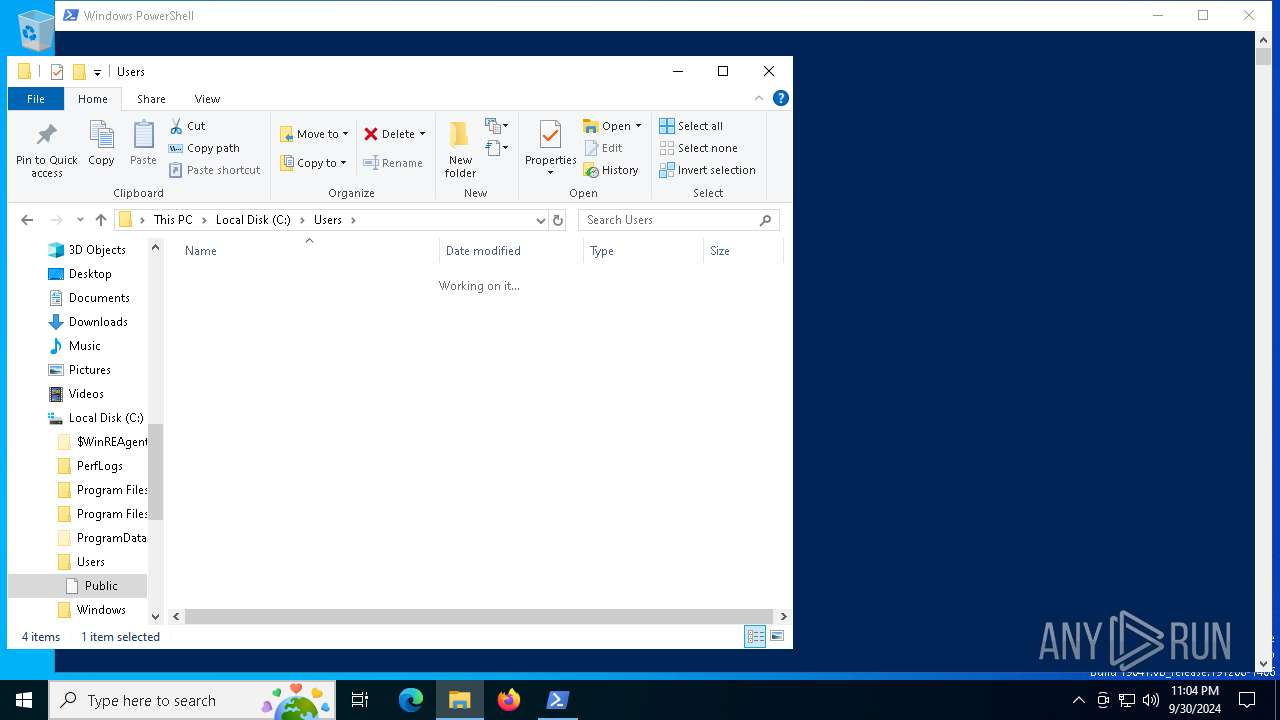
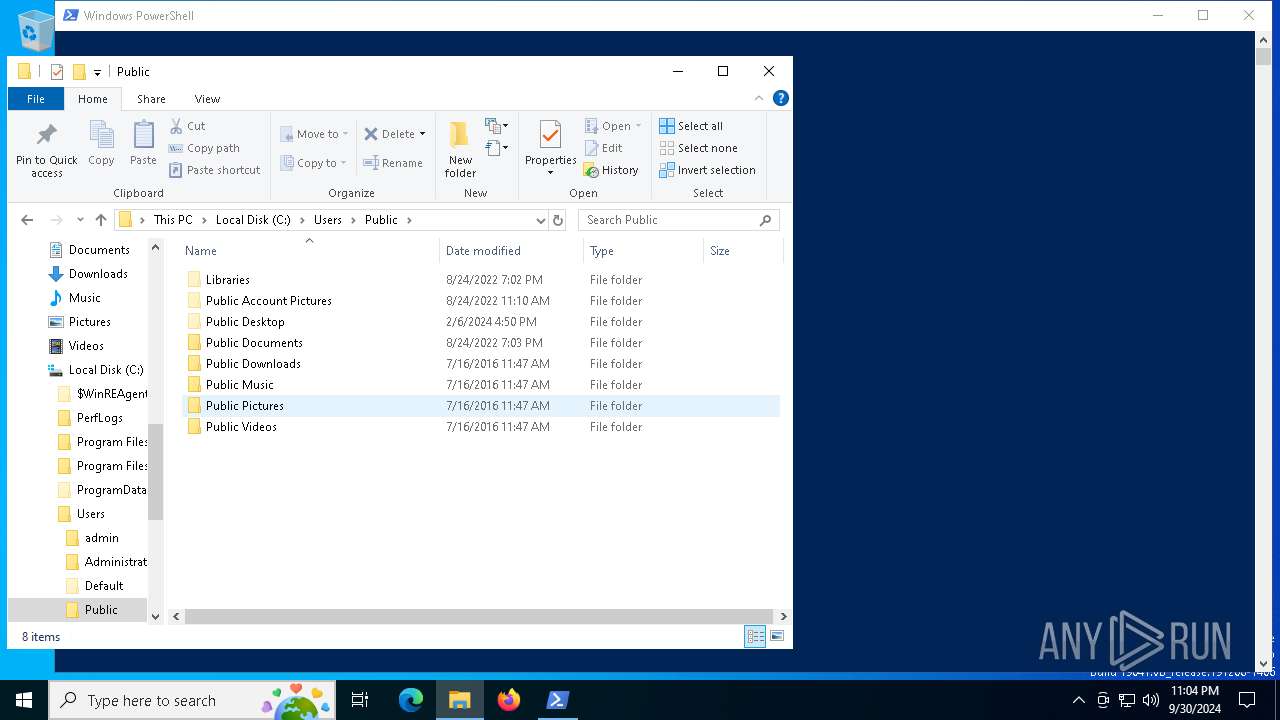
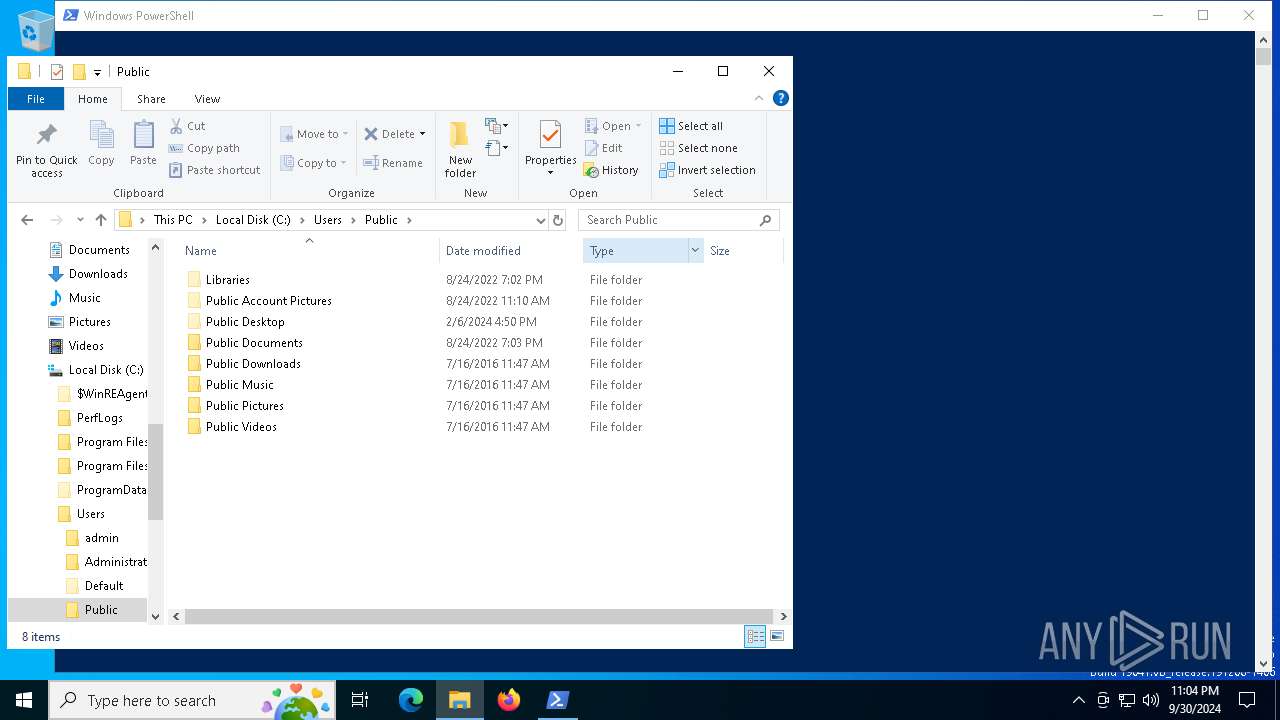
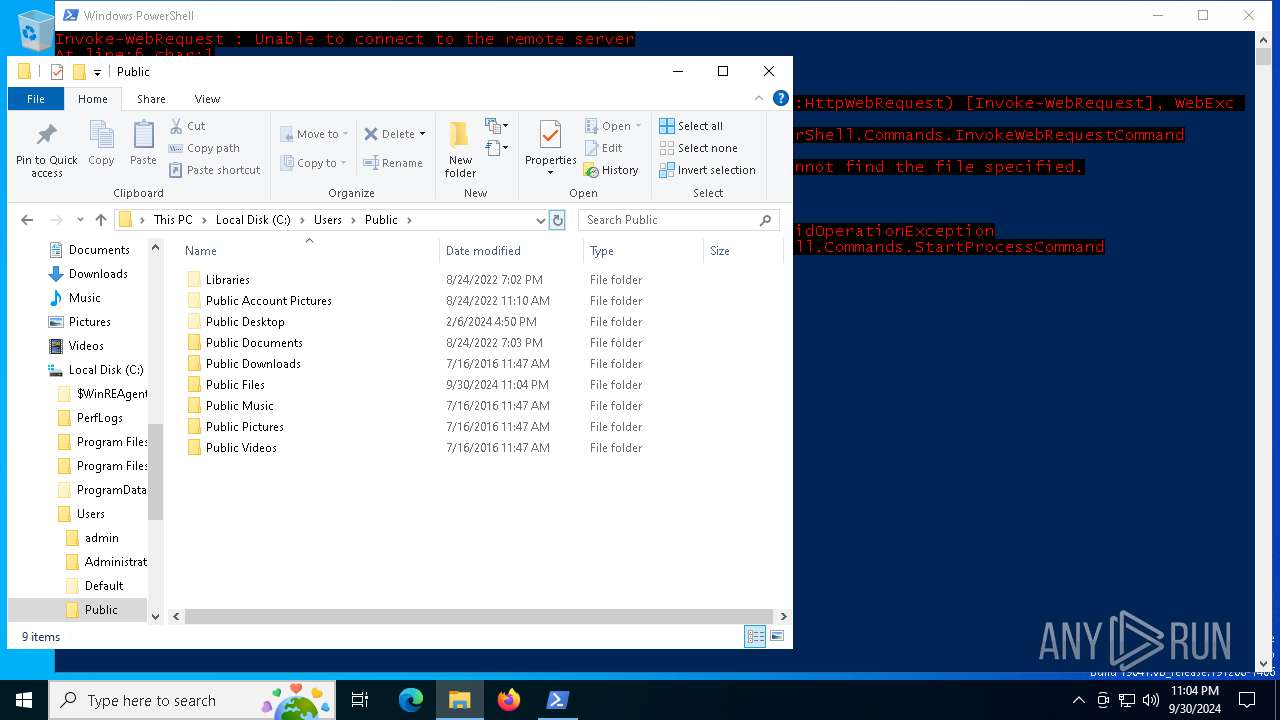
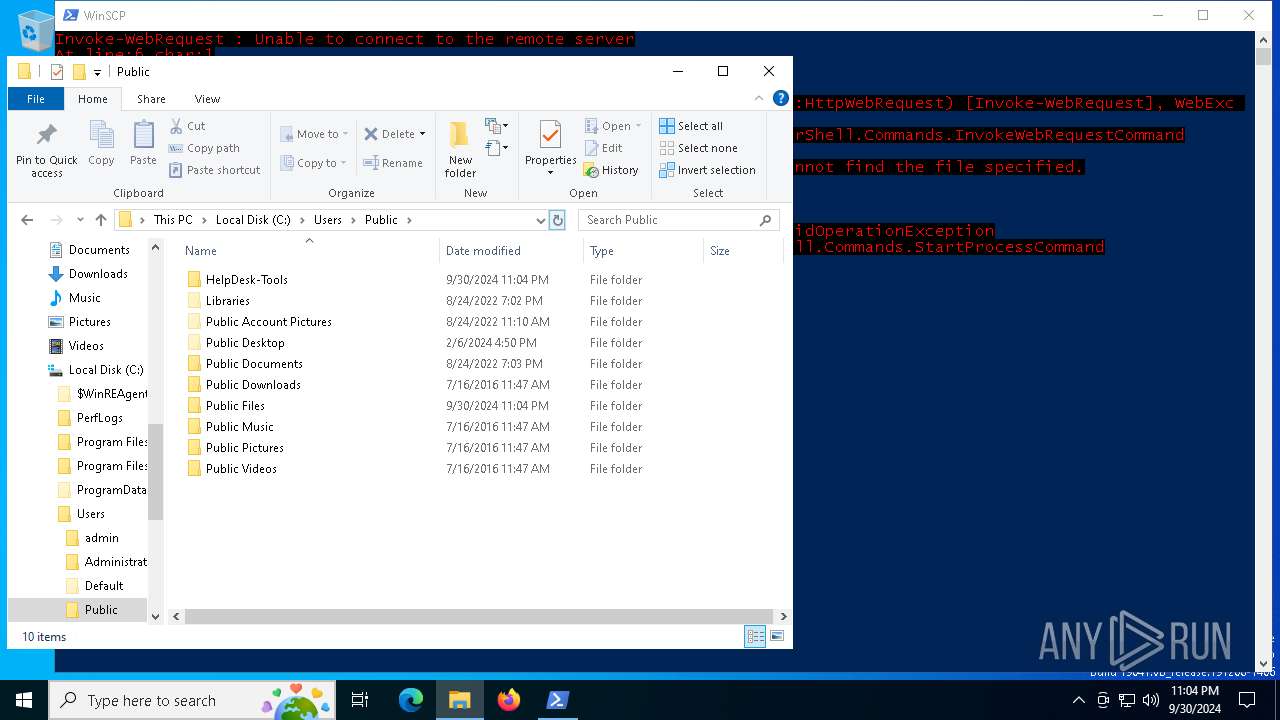
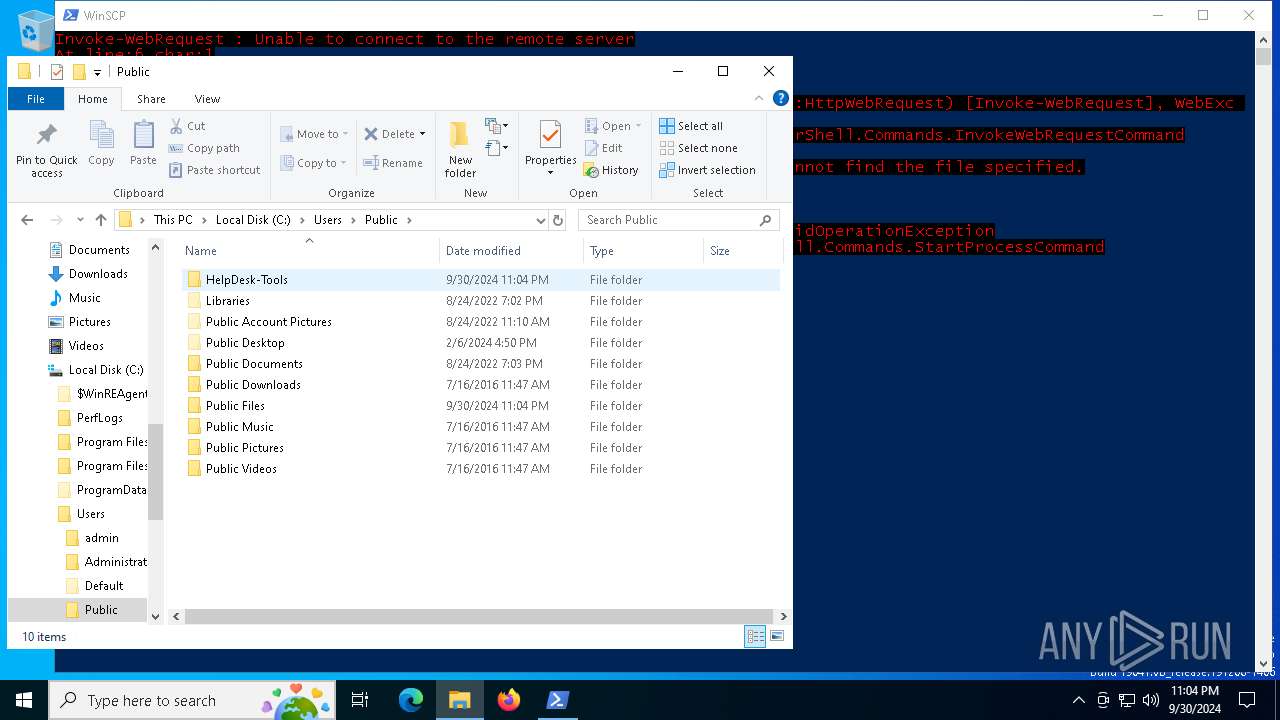
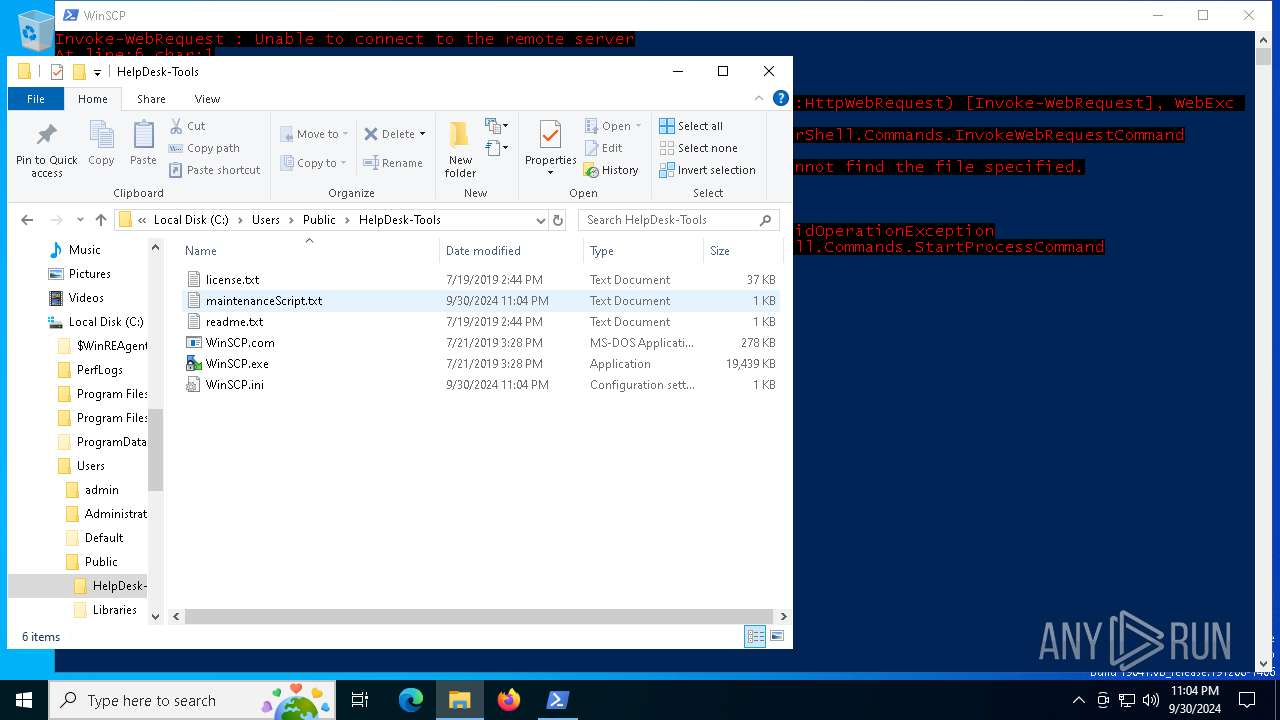
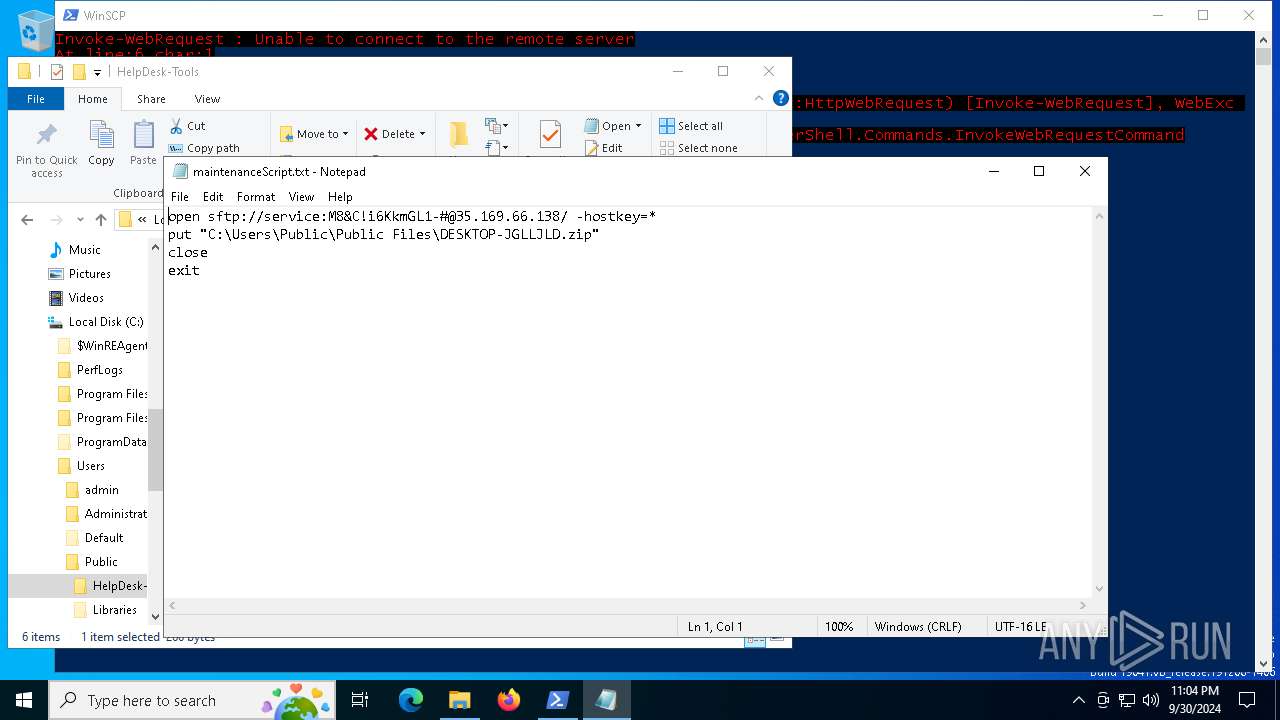
Likely accesses (executes) a file from the Public directory
- WinSCP.com (PID: 5916)
- WinSCP.exe (PID: 5584)
- notepad.exe (PID: 3688)
Connects to SSH
- WinSCP.exe (PID: 5584)
Starts application with an unusual extension
- powershell.exe (PID: 6684)
INFO
Found Base64 encoded network access via PowerShell (YARA)
- powershell.exe (PID: 6684)
Found Base64 encoded reference to AntiVirus WMI classes (YARA)
- powershell.exe (PID: 6684)
Found Base64 encoded access to processes via PowerShell (YARA)
- powershell.exe (PID: 6684)
Found Base64 encoded reference to WMI classes (YARA)
- powershell.exe (PID: 6684)
Manual execution by a user
- notepad.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
137
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2620 | "C:\WINDOWS\system32\nltest.exe" /dsgetdc:DESKTOP-JGLLJLD | C:\Windows\System32\nltest.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Logon Server Test Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3444 | "C:\WINDOWS\system32\gpresult.exe" /r | C:\Windows\System32\gpresult.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Query Group Policy RSOP Data Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
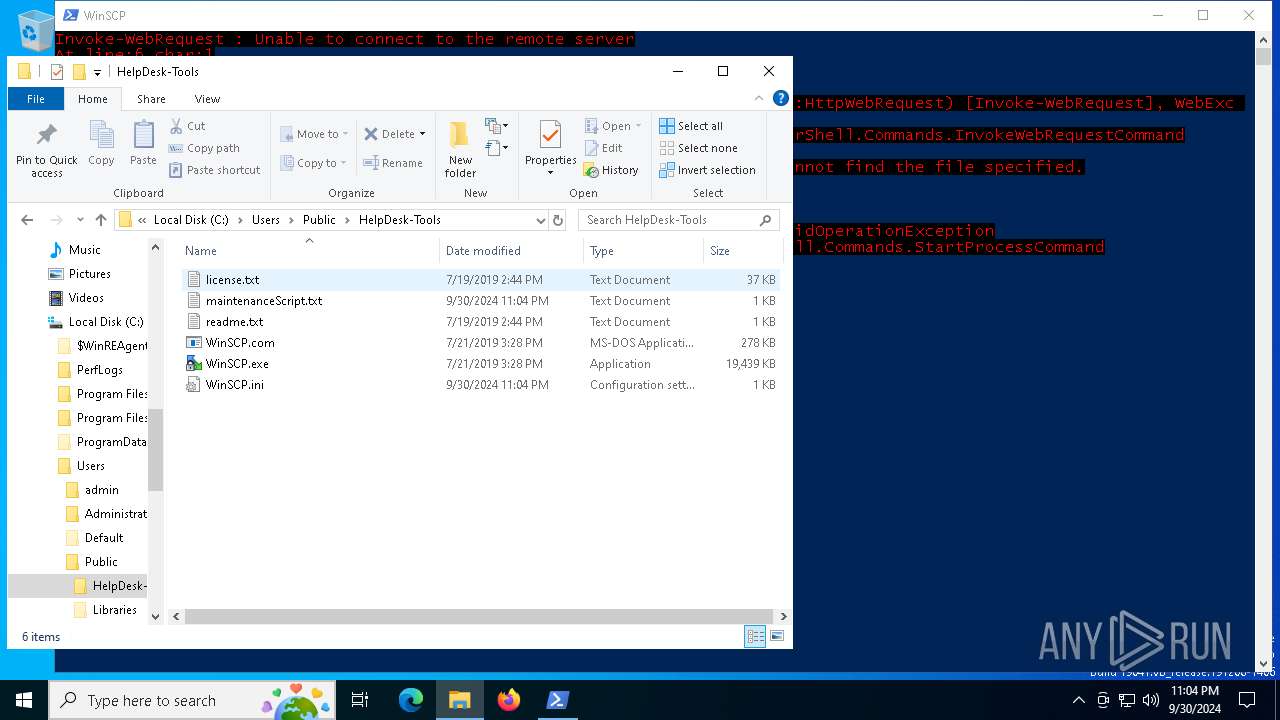
| 3688 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\Public\HelpDesk-Tools\maintenanceScript.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5164 | "C:\WINDOWS\System32\Wbem\WMIC.exe" /NAMESPACE:\\root\SecurityCenter2 PATH AntiVirusProduct GET /value | C:\Windows\System32\wbem\WMIC.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5584 | "C:\Users\Public\HelpDesk-Tools\WinSCP.exe" /console=5.15.3 /consoleinstance=_5916_558 "/script=C:\Users\Public\HelpDesk-Tools\maintenanceScript.txt" | C:\Users\Public\HelpDesk-Tools\WinSCP.exe | WinSCP.com | ||||||||||||
User: admin Company: Martin Prikryl Integrity Level: MEDIUM Description: WinSCP: SFTP, FTP, WebDAV, S3 and SCP client Version: 5.15.3.9730 Modules
| |||||||||||||||
| 5916 | "C:\Users\Public\HelpDesk-Tools\WinSCP.com" /script="C:\Users\Public\HelpDesk-Tools\maintenanceScript.txt" | C:\Users\Public\HelpDesk-Tools\WinSCP.com | — | powershell.exe | |||||||||||
User: admin Company: Martin Prikryl Integrity Level: MEDIUM Description: Console interface for WinSCP Version: 5.0.1.9730 Modules
| |||||||||||||||
| 6124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6684 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\newILY.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 142
Read events
11 142
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
19
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6684 | powershell.exe | C:\Users\Public\Public Files\AVinfo.txt | text | |
MD5:E16D80E0C0842B3845562B8ACA960DD0 | SHA256:D2D4CADF6390D0ADBDC2ABA49701463D24F06FAD15B6C4531AAF1AFDF19914A4 | |||
| 6684 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XB23RYKWOOW86KDJ7V1N.temp | binary | |
MD5:256214E1C71187EC44672E481EBBDB6B | SHA256:3D50799E7A35DED1D8181FD1AFE0694C1B1DB528BB04D35C3A9CA86A3391DB4D | |||
| 6684 | powershell.exe | C:\Users\Public\Public Files\Built-In Building Blocks.dotx | document | |
MD5:45B3206B0A14EB850F21A52116F021EA | SHA256:C6407F48BAE9FF72044F64B06622076A84D9E8F36A9E0F4F0632A5E644ADB6AA | |||
| 6684 | powershell.exe | C:\Users\Public\Public Files\username.txt | text | |
MD5:B862A883A1AD2D03F78677F0FA3B532B | SHA256:F77ADB49175BC4312D14ADB711BC540E7CE045BF7C277DBFAC4B9D62CCE37E79 | |||
| 6684 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_esx5mbpp.axc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6684 | powershell.exe | C:\Users\Public\Public Files\Get more out of PivotTables.xltx | document | |
MD5:27BFFEADAA58B2D2560AAC8024225189 | SHA256:FF191450AA1894B99B0608355C744EBA8F441A548F9BD8FFBC6BD4B33A437EA3 | |||
| 6684 | powershell.exe | C:\Users\Public\Public Files\PivotTable tutorial(2).xltx | document | |
MD5:3ECC3580E61A7FFDDE237CA70BAD202D | SHA256:91B30C8346A857DA000B129C06F8A0B146FBA13B96E03C3E49E15B7E28223875 | |||
| 6684 | powershell.exe | C:\Users\Public\Public Files\localusers.txt | text | |
MD5:A8EA1765F76DD21736ACE3460F60F725 | SHA256:7D3C4B6115BA8CB2F378BA19267AB0B6982593EF008AB0BAD1F3BF07B87F6355 | |||
| 6684 | powershell.exe | C:\Users\Public\Public Files\UserProcesses.txt | text | |
MD5:88642C22954A81789640A78AED819E8F | SHA256:368786DBF5B1FFB8D938C0DA1754A79EE11353ECFE6412F61C357F178D3ECA99 | |||
| 6684 | powershell.exe | C:\Users\Public\Public Files\Formula tutorial(2).xltx | document | |
MD5:1A732175C6E0343D9A7C403BD0C65A6D | SHA256:DABDF3DDCB019C9AA34218F550A99E3CD0FB0594ECDA24FADE32299419B2F43A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
45
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1928 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5664 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1928 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3972 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7108 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6684 | powershell.exe | 44.206.187.144:9000 | — | AMAZON-AES | US | unknown |
7108 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5664 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5584 | WinSCP.exe | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |