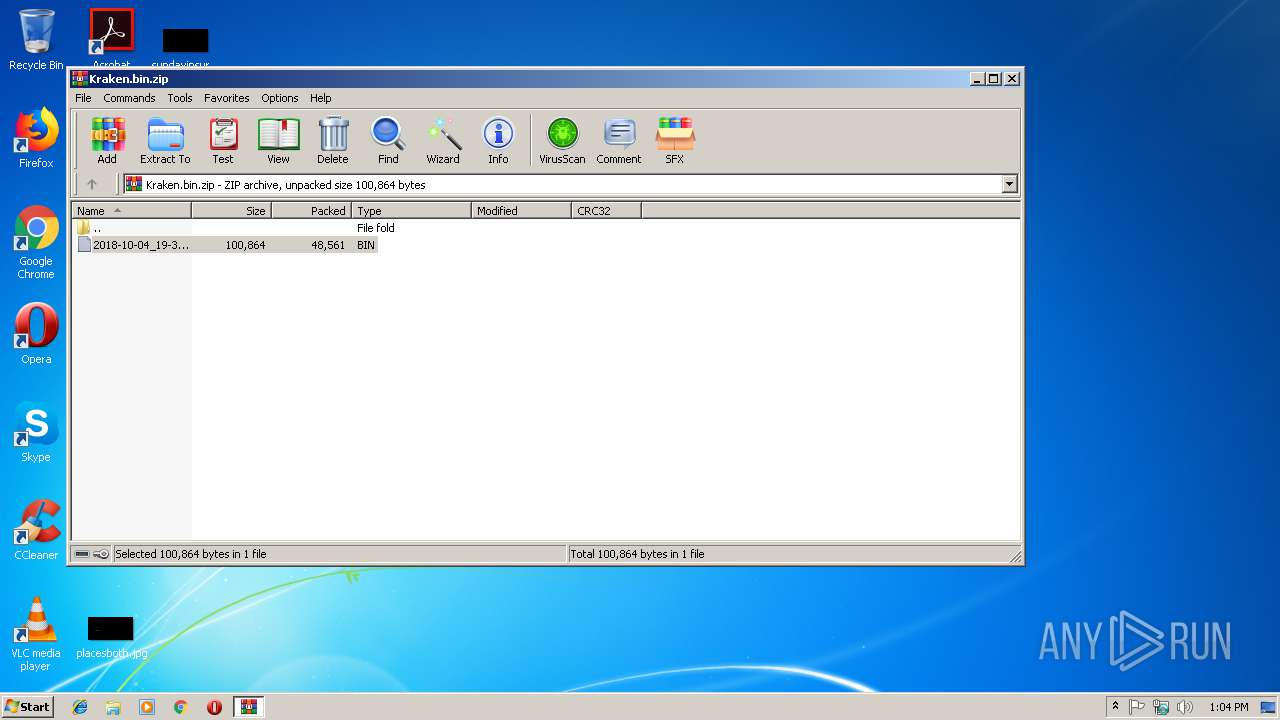
| File name: | Kraken.bin.zip |
| Full analysis: | https://app.any.run/tasks/80061f0d-7c14-4579-a93c-882604caad14 |
| Verdict: | Malicious activity |
| Threats: | Kraken is a trojan malware with infostealing capabilities that was first spotted in May of 2023. The malware can perform a wide range of malicious activities, including logging users’ keystrokes. The data then can be sent to the attacker using several protocols. The operators behind the Kraken stealer usually distribute it via phishing emails. |
| Analysis date: | January 11, 2019, 13:03:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2A31FC84EBA675C8AA74673FD7EFFD9D |
| SHA1: | 40479BCBDB8D3791B7DFA38381923412BC988E20 |
| SHA256: | 094922019198988CA8554CDD1D9C29D72E1DD5A4FBF3F665AEBC454B7F02ECA9 |
| SSDEEP: | 768:nfQfXA9MPEXvLFYcVBm7Lu166D1NR/aJYvmsBx/zn+y8pSyc+4enfLWu6whg4:nIfX0MPaBkLufDnAJur/8cA4nc |
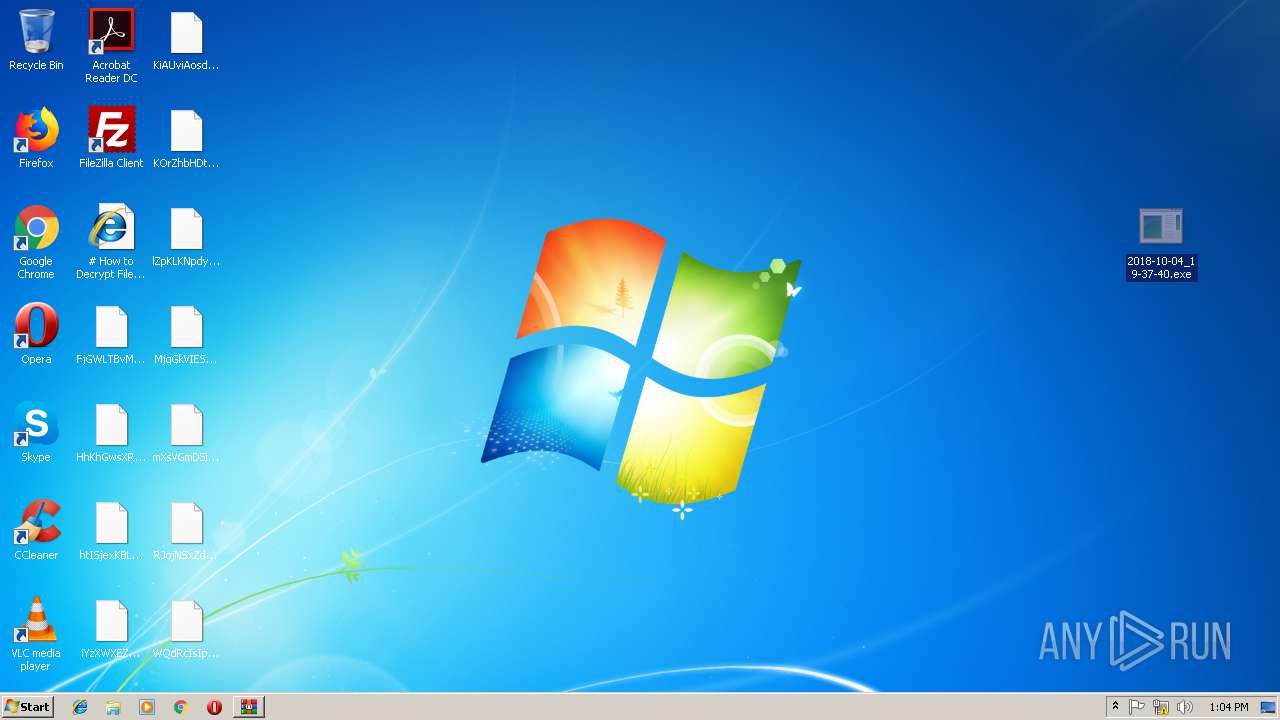
MALICIOUS
Kraken Ransomware was detected
- 2018-10-04_19-37-40.exe (PID: 2832)
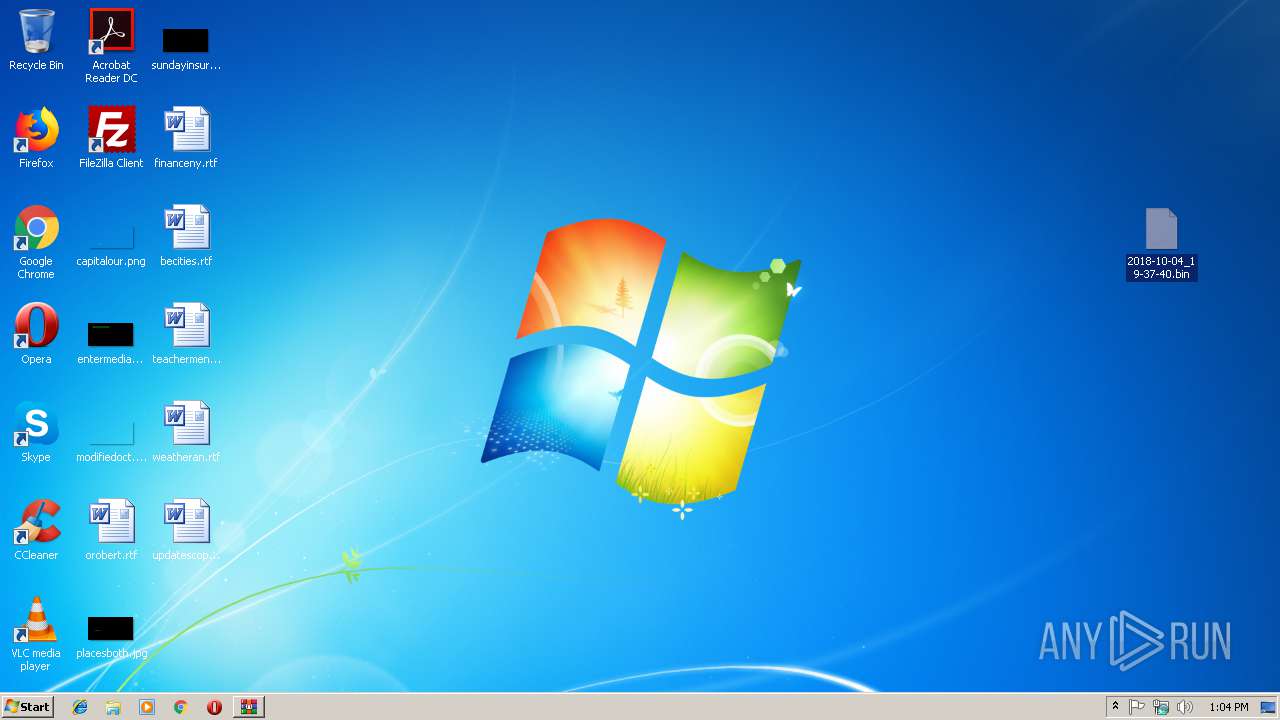
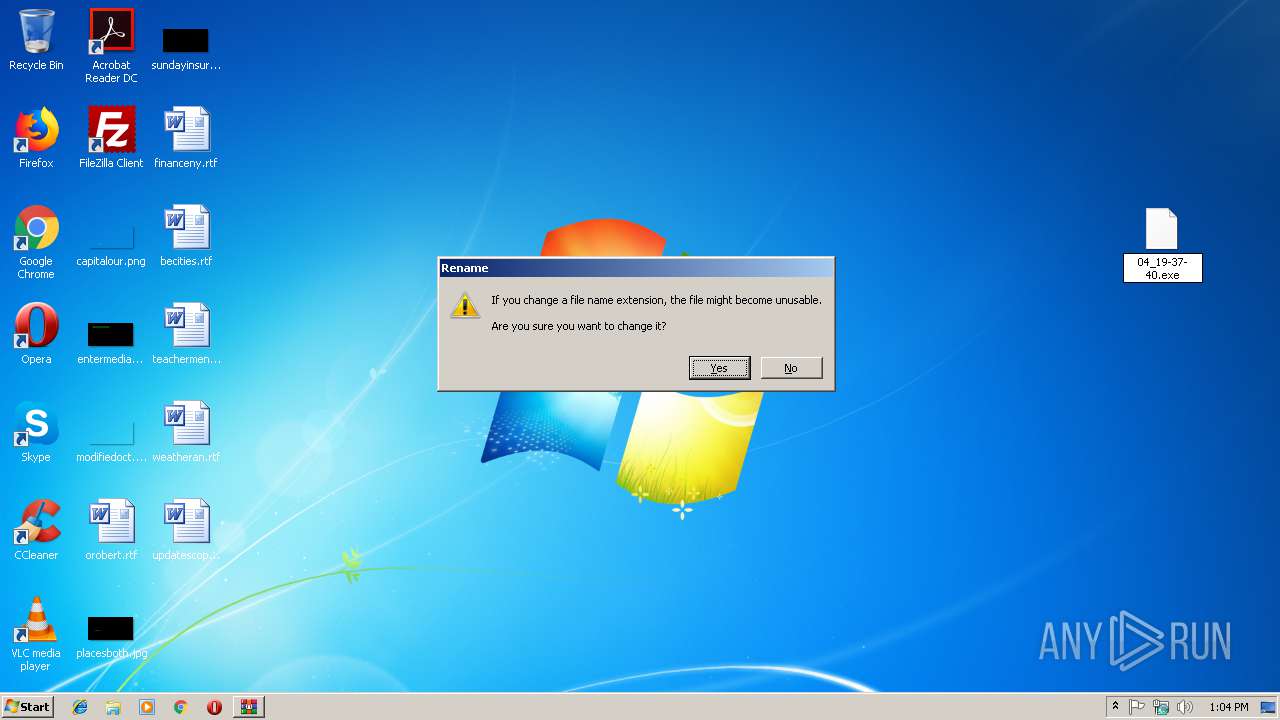
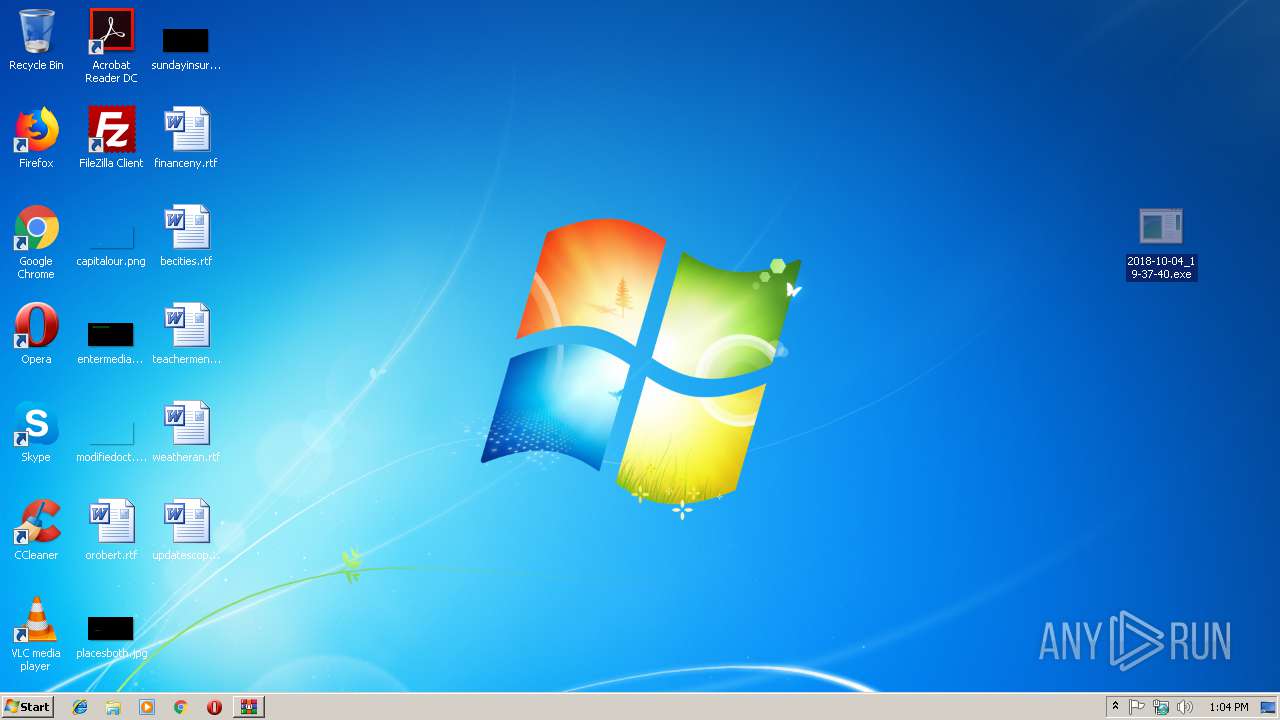
Application was dropped or rewritten from another process
- 2018-10-04_19-37-40.exe (PID: 2832)
- krakentemp0000.exe (PID: 2316)
- sdelete.exe (PID: 3452)
Known privilege escalation attack
- 2018-10-04_19-37-40.exe (PID: 2832)
Changes the autorun value in the registry
- 2018-10-04_19-37-40.exe (PID: 2832)
Application was injected by another process
- dllhost.exe (PID: 308)
Runs injected code in another process
- 2018-10-04_19-37-40.exe (PID: 2832)
Changes settings of System certificates
- krakentemp0000.exe (PID: 2316)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 4000)
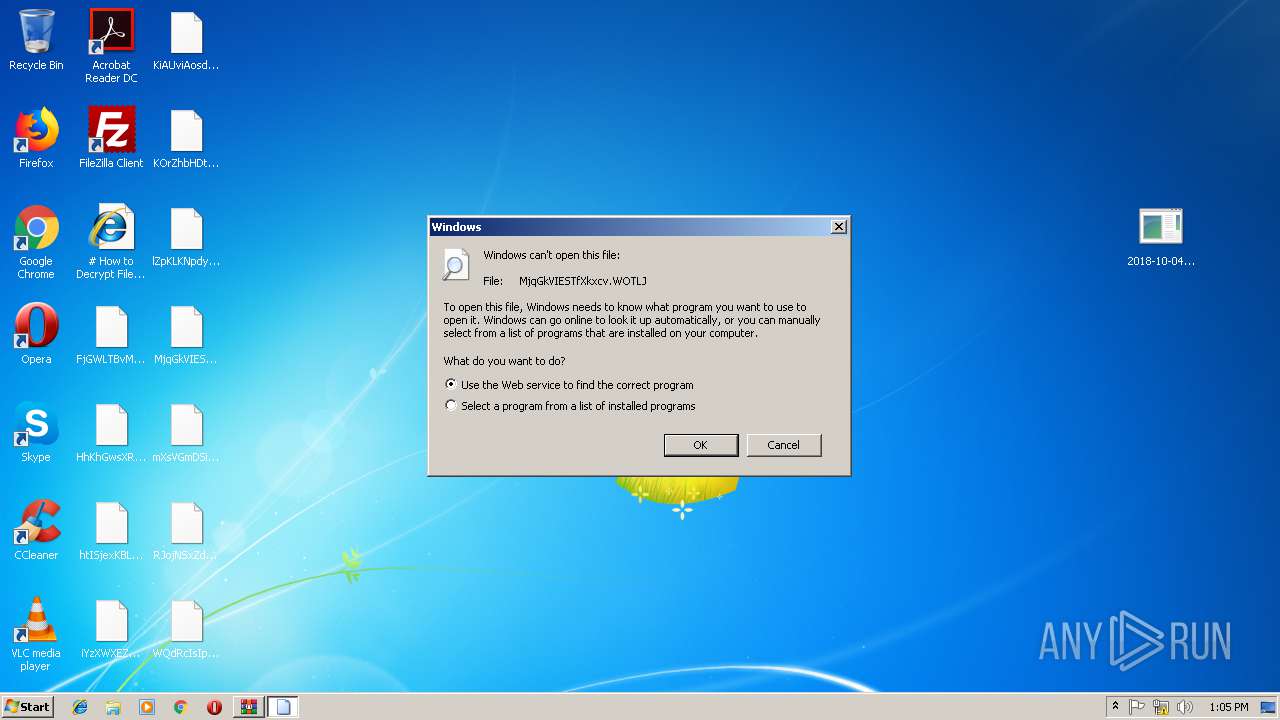
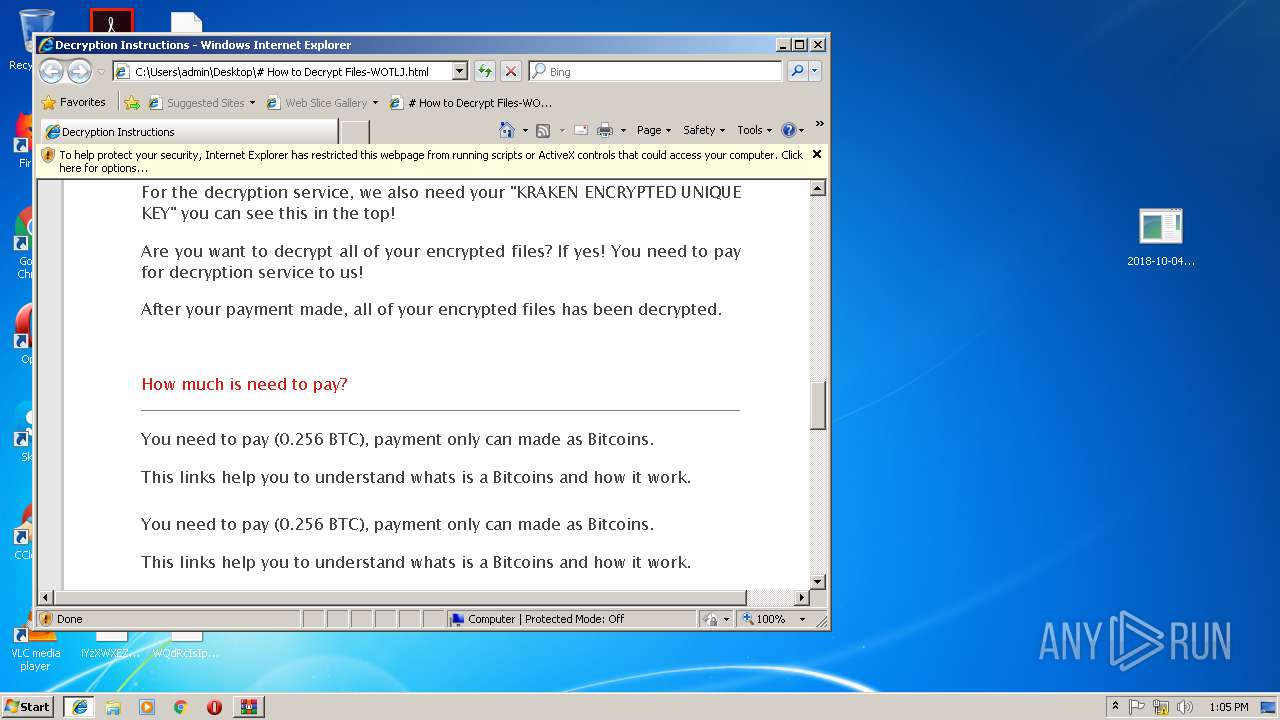
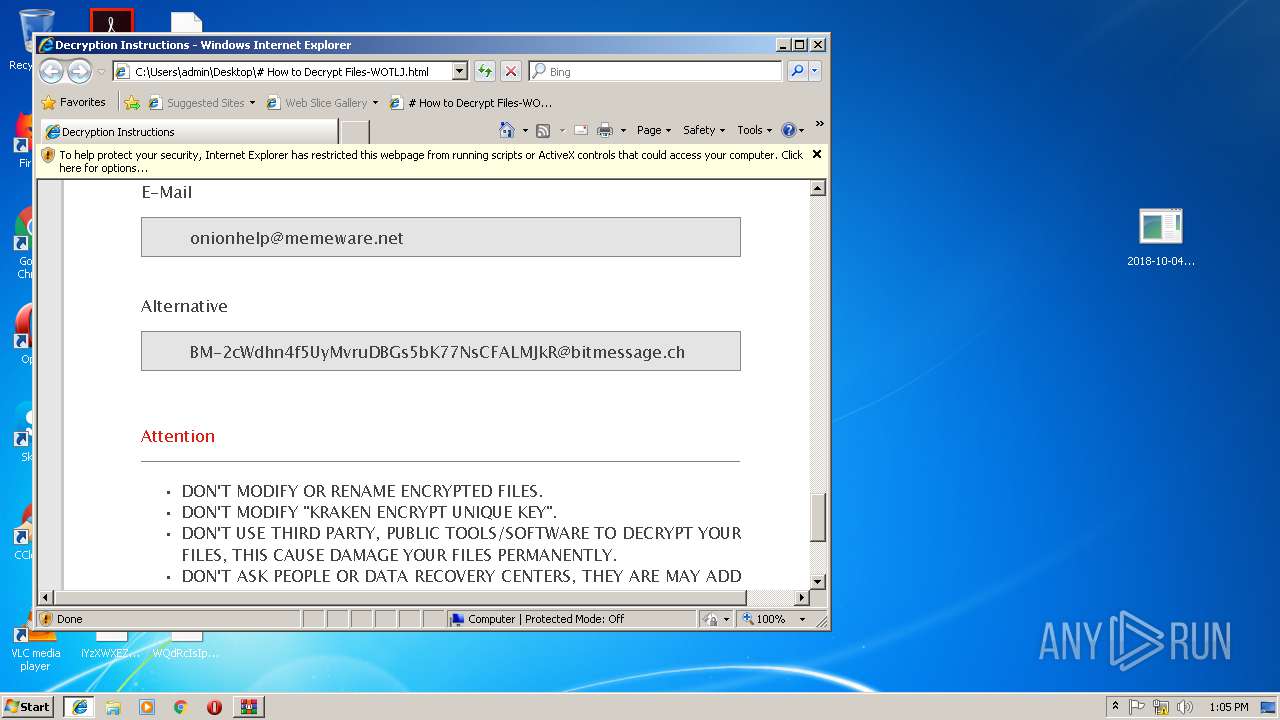
Detected Kraken's note (Ransomware)
- krakentemp0000.exe (PID: 2316)
SUSPICIOUS
Modifies the open verb of a shell class
- 2018-10-04_19-37-40.exe (PID: 2832)
Executable content was dropped or overwritten
- 2018-10-04_19-37-40.exe (PID: 2832)
- krakentemp0000.exe (PID: 2316)
Creates files in the program directory
- krakentemp0000.exe (PID: 2316)
Adds / modifies Windows certificates
- krakentemp0000.exe (PID: 2316)
Creates files like Ransomware instruction
- krakentemp0000.exe (PID: 2316)
Checks for external IP
- krakentemp0000.exe (PID: 2316)
Uses TASKLIST.EXE to query information about running processes
- krakentemp0000.exe (PID: 2316)
Creates files in the Windows directory
- krakentemp0000.exe (PID: 2316)
Starts CMD.EXE for commands execution
- krakentemp0000.exe (PID: 2316)
- cmd.exe (PID: 3820)
Removes files from Windows directory
- krakentemp0000.exe (PID: 2316)
Application launched itself
- cmd.exe (PID: 3820)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3820)
INFO
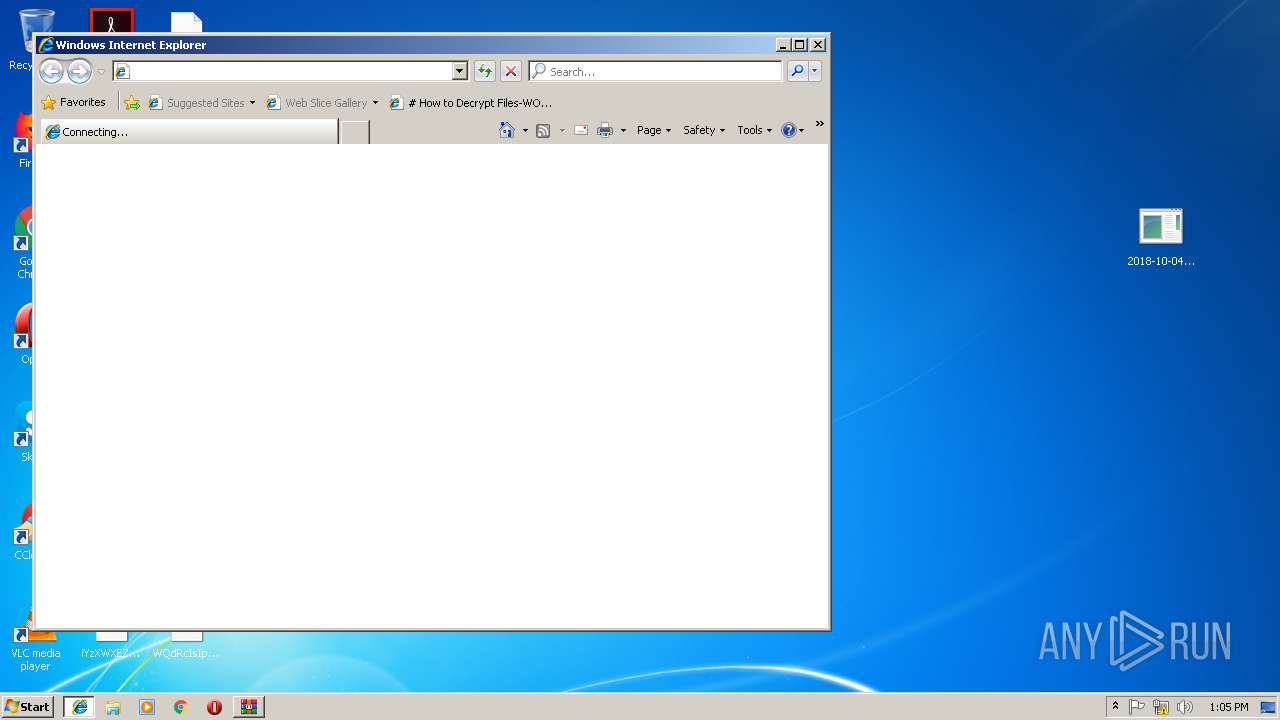
Reads Microsoft Office registry keys
- iexplore.exe (PID: 2104)
Application launched itself
- iexplore.exe (PID: 2104)
Reads internet explorer settings
- iexplore.exe (PID: 2752)
Changes internet zones settings
- iexplore.exe (PID: 2104)
Creates files in the user directory
- iexplore.exe (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
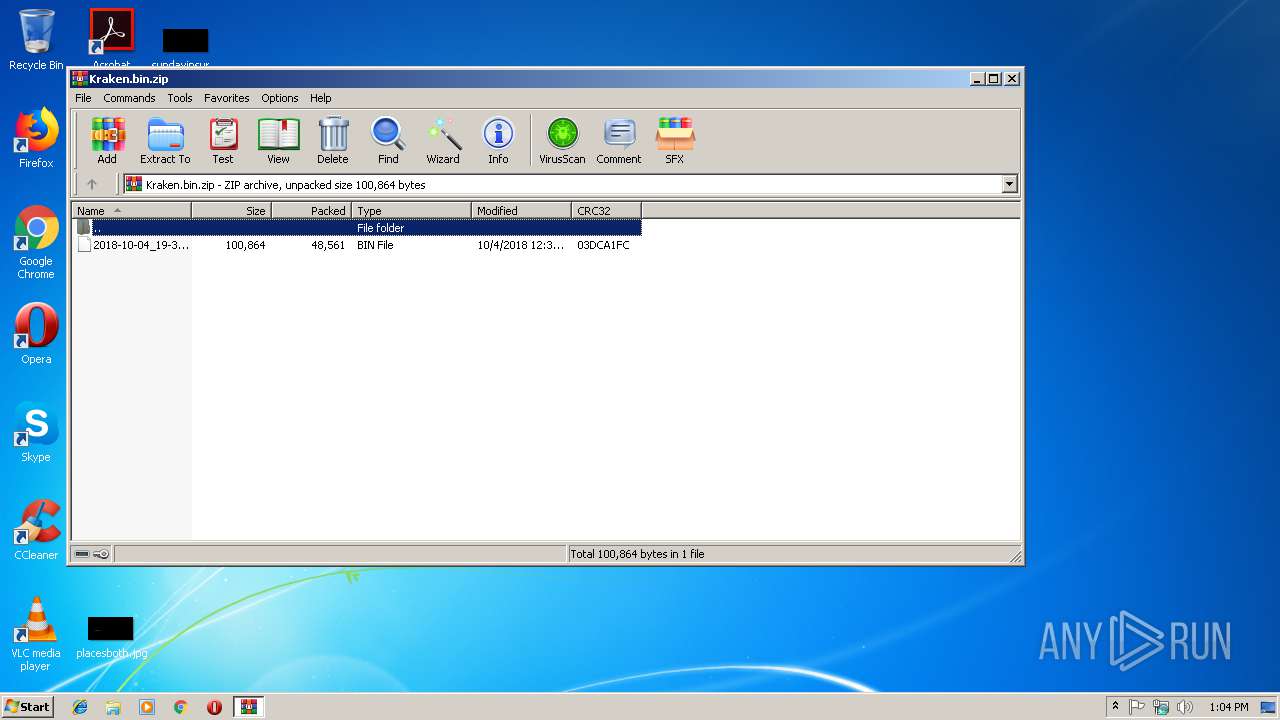
| ZipRequiredVersion: | 788 |
|---|---|
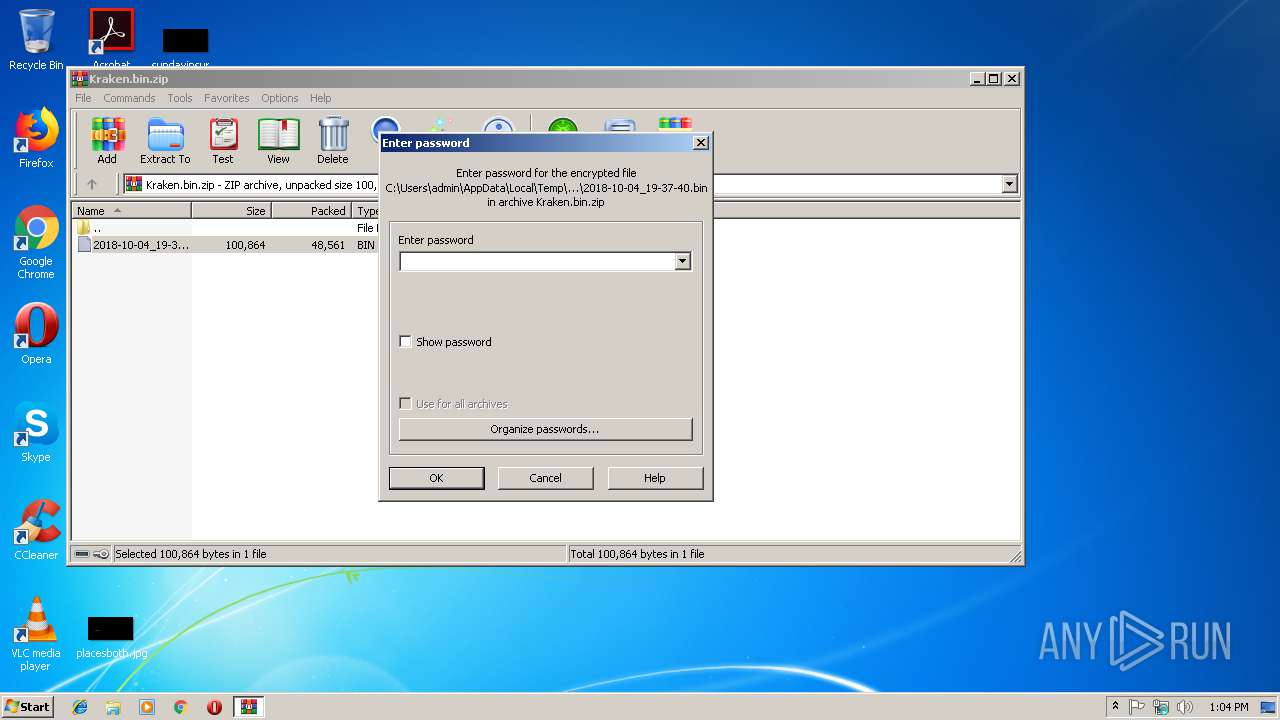
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:10:04 13:36:26 |
| ZipCRC: | 0x03dca1fc |
| ZipCompressedSize: | 48561 |
| ZipUncompressedSize: | 100864 |
| ZipFileName: | 2018-10-04_19-37-40.bin |
Total processes
57
Monitored processes
17
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | dllhost.exe | svchost.exe | |||||||||||||
Integrity Level: UNKNOWN Exit code: 0 | |||||||||||||||
| 308 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | — | 2018-10-04_19-37-40.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Event Viewer Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | REG ADD "HKEY_CURRENT_USER\Software\Sysinternals\SDelete" /v EulaAccepted /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | cmd.exe /c C:\ProgramData\sdelete.exe -c -z C: | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Desktop\# How to Decrypt Files-WOTLJ.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Local\Temp\krakentemp0000.exe" | C:\Users\admin\AppData\Local\Temp\krakentemp0000.exe | eventvwr.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.1.7.9 Modules
| |||||||||||||||
| 2356 | "tasklist" /V /FO CSV | C:\Windows\system32\tasklist.exe | — | krakentemp0000.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2644 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\MjqGkVIESTfXkxcv.WOTLJ | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2104 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
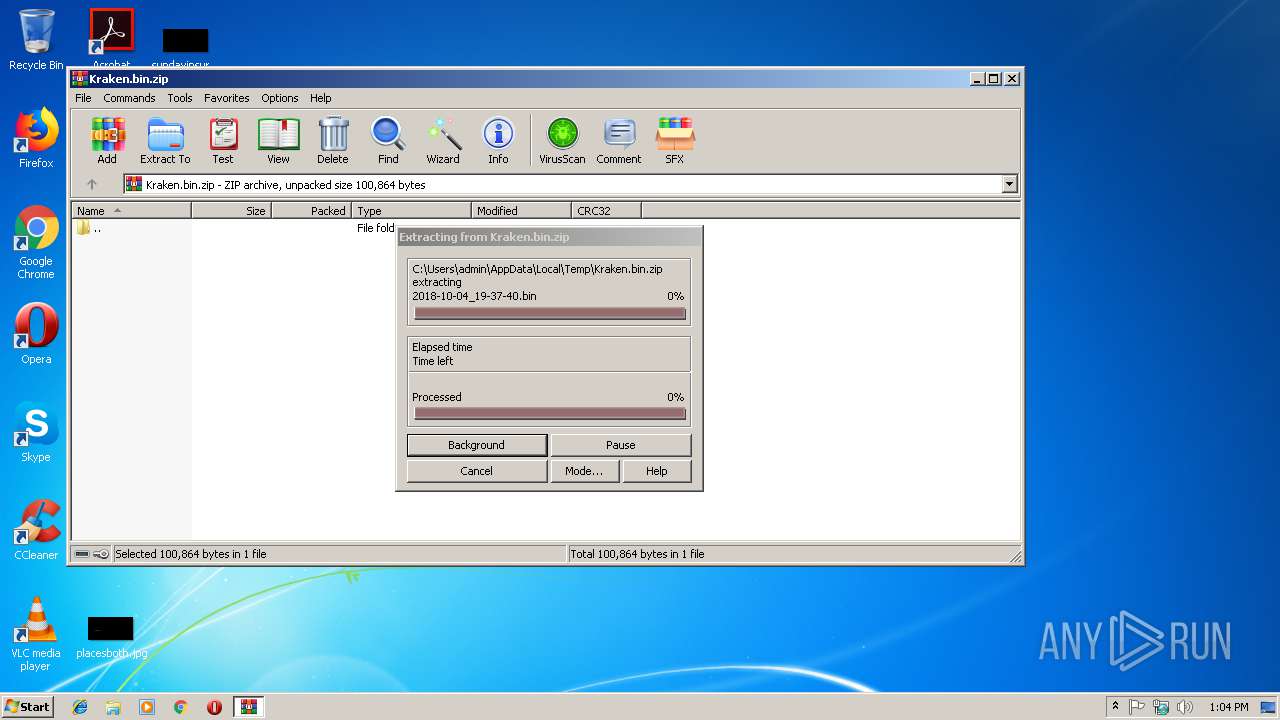
| 2800 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Kraken.bin.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 277
Read events
1 173
Write events
104
Delete events
0
Modification events
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Kraken.bin.zip | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2832) 2018-10-04_19-37-40.exe | Key: | HKEY_CLASSES_ROOT\mscfile\shell\open\command |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\krakentemp0000.exe | |||
Executable files
2
Suspicious files
36
Text files
52
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2800.35988\2018-10-04_19-37-40.bin | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Contacts\admin.contact | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Desktop\becities.rtf | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Desktop\capitalour.png | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Desktop\entermedia.jpg | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Desktop\financeny.rtf | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Desktop\modifiedoct.png | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Desktop\orobert.rtf | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Desktop\placesboth.jpg | — | |
MD5:— | SHA256:— | |||
| 2316 | krakentemp0000.exe | C:\Users\admin\Desktop\sundayinsurance.jpg | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
5
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2316 | krakentemp0000.exe | GET | — | 104.28.13.103:80 | http://blasze.tk/CN18R3 | US | — | — | malicious |
2316 | krakentemp0000.exe | GET | 302 | 104.28.13.103:80 | http://blasze.tk/CN18R3 | US | text | 51 b | malicious |
2316 | krakentemp0000.exe | GET | 301 | 172.217.22.46:80 | http://google.com/ | US | html | 219 b | whitelisted |
2316 | krakentemp0000.exe | GET | 200 | 108.177.127.103:80 | http://www.google.com/ | US | html | 12.1 Kb | malicious |
2104 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2316 | krakentemp0000.exe | 108.177.127.103:80 | www.google.com | Google Inc. | US | whitelisted |
2316 | krakentemp0000.exe | 152.199.19.160:443 | download.sysinternals.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2104 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2316 | krakentemp0000.exe | 172.217.22.46:80 | — | Google Inc. | US | whitelisted |
2316 | krakentemp0000.exe | 216.239.32.21:443 | ipinfo.io | Google Inc. | US | whitelisted |
2316 | krakentemp0000.exe | 104.28.13.103:80 | blasze.tk | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipinfo.io |
| shared |
blasze.tk |
| malicious |
www.google.com |
| malicious |
download.sysinternals.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2316 | krakentemp0000.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2316 | krakentemp0000.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2316 | krakentemp0000.exe | A Network Trojan was detected | ET TROJAN [PTsecurity] Kraken Ransomware Start Activity 2 |
2316 | krakentemp0000.exe | A Network Trojan was detected | SC RANSOMWARE Ransomware Kraken Win32 |
2316 | krakentemp0000.exe | A Network Trojan was detected | MALWARE [PTsecurity] Kraken Cryptor |
2316 | krakentemp0000.exe | A Network Trojan was detected | MALWARE [PTsecurity] Ransomware.Kraken_Cryptor UA |
2316 | krakentemp0000.exe | A Network Trojan was detected | MALWARE [PTsecurity] Ransomware.Kraken_Cryptor URL |
2316 | krakentemp0000.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2316 | krakentemp0000.exe | A Network Trojan was detected | ET TROJAN Kraken Ransomware End Activity |
2316 | krakentemp0000.exe | A Network Trojan was detected | SC RANSOMWARE Ransomware Kraken Win32 |