| URL: | http://deliver.angelbroking.in/lt.pl?id=19783=IU8AUVQAAAAHTFRTBg4PUFcBAVMBUgcCAwIAUQdfAVdSAQMFAVoFW1JTBlECVVtSAQNOE0QER1UCTwoLQklcCgddWVVVAHdfWVFYCRxVV15NBARWBFwMAVZQUlEDDQRTVAFMCRFNRwIbH1UAXl9OVkMbUw1RAFhWFA4KDVxeGw0MHFwVS0lbB11UTRMB&fl=CkdEERYDGBddXgBLRV9CQV5WWQZCCFVdCk8PAUYWRw==&ext=ZT1LMjVxQUI4SUNXTjZiMnQlMkZEU1pqZUFzREJ3VmphQ3cxS1Mwc05Vd0JBZzFrYkdOJTJGWlNZU0MwRlZRa2MlMkJOVHdVTkRVOUlGdFZjWFFyYXk0dUlUODhQMDUlMkJYa0ElMkJQRHNvTmk0N0pGd1FjbGclMkJPVGt1TXlZcGFVVktRMThJTXpacGJYaGpmUWNEQVFGbmEyZDhDR2hpZVFBQUJBWm5lSDVwSUNBZ0lHMUFXRUk0TG5CeGRTMG9PVmx2VlZFeE95Y25JM2d2JnI9aHR0cHMlM0ElMkYlMkZ3d3cuYW5nZWxicm9raW5nLmNvbSUyRnBwYyUyRnJlZmVyLWEtZnJpZW5kLW5ldyUzRnV0bV9zb3VyY2UlM0RSbkVXZWJwYWdlJTI2dXRtX21lZGl1bSUzRFJuRSUyNTIwLSUyNTIwQ2xpZW50JTI2dXRtX2NhbXBhaWduJTNEUmVzdEIyQ01heTIyJmM9NTg4MTk4OTYwJnRva2VuPUdsVlFCZ05RQndRTUJBUSUzRCZ0cnk9MSYkZm9sbG93X3JlZGlyZWN0PXRydWU= |
| Full analysis: | https://app.any.run/tasks/25acd05e-623d-4cd1-90ed-13d9c54f3987 |
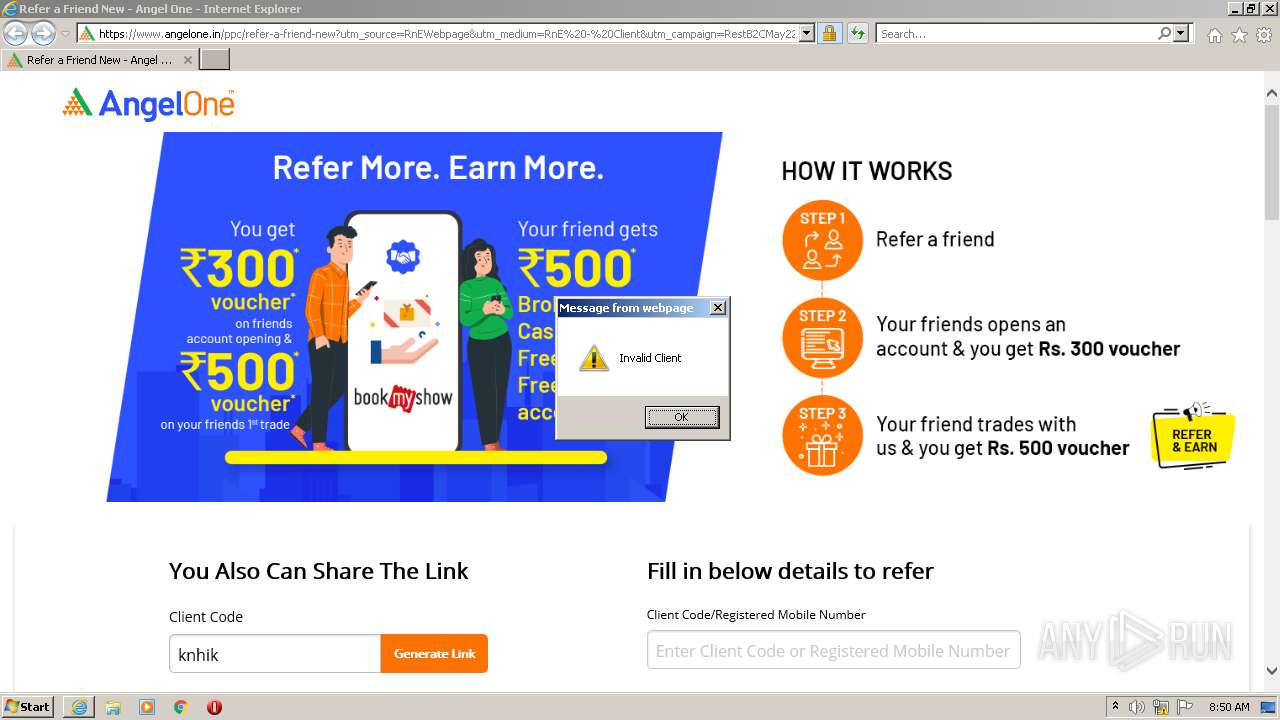
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 07:49:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7064C8F28355F23282DD44FBDA6FC68E |
| SHA1: | BC5562B4F72FAD50579D63A44824890EED8403C3 |
| SHA256: | 0947874514A1F75AE5713AC0D23AFD6442410A4DDD3D72BCC20C6E92F4853E34 |
| SSDEEP: | 12:TndUA7tWKcUyreofkslC1P7xLeFT8xhKubkzLac7lRSE6KV2Bp1EKA6mS12+zJIt:jdNW27oBAP7xCFY9ELaOkxKV+WbSz7nK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3248)
INFO
Checks supported languages
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 2264)
Reads the computer name
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 2264)
Checks Windows Trust Settings
- iexplore.exe (PID: 2264)
- iexplore.exe (PID: 3248)
Creates files in the user directory
- iexplore.exe (PID: 2264)
- iexplore.exe (PID: 3248)
Changes internet zones settings
- iexplore.exe (PID: 2264)
Reads settings of System Certificates
- iexplore.exe (PID: 3248)
- iexplore.exe (PID: 2264)
Application launched itself
- iexplore.exe (PID: 2264)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2264)
Reads internet explorer settings
- iexplore.exe (PID: 3248)
Changes settings of System certificates
- iexplore.exe (PID: 2264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2264 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://deliver.angelbroking.in/lt.pl?id=19783=IU8AUVQAAAAHTFRTBg4PUFcBAVMBUgcCAwIAUQdfAVdSAQMFAVoFW1JTBlECVVtSAQNOE0QER1UCTwoLQklcCgddWVVVAHdfWVFYCRxVV15NBARWBFwMAVZQUlEDDQRTVAFMCRFNRwIbH1UAXl9OVkMbUw1RAFhWFA4KDVxeGw0MHFwVS0lbB11UTRMB&fl=CkdEERYDGBddXgBLRV9CQV5WWQZCCFVdCk8PAUYWRw==&ext=ZT1LMjVxQUI4SUNXTjZiMnQlMkZEU1pqZUFzREJ3VmphQ3cxS1Mwc05Vd0JBZzFrYkdOJTJGWlNZU0MwRlZRa2MlMkJOVHdVTkRVOUlGdFZjWFFyYXk0dUlUODhQMDUlMkJYa0ElMkJQRHNvTmk0N0pGd1FjbGclMkJPVGt1TXlZcGFVVktRMThJTXpacGJYaGpmUWNEQVFGbmEyZDhDR2hpZVFBQUJBWm5lSDVwSUNBZ0lHMUFXRUk0TG5CeGRTMG9PVmx2VlZFeE95Y25JM2d2JnI9aHR0cHMlM0ElMkYlMkZ3d3cuYW5nZWxicm9raW5nLmNvbSUyRnBwYyUyRnJlZmVyLWEtZnJpZW5kLW5ldyUzRnV0bV9zb3VyY2UlM0RSbkVXZWJwYWdlJTI2dXRtX21lZGl1bSUzRFJuRSUyNTIwLSUyNTIwQ2xpZW50JTI2dXRtX2NhbXBhaWduJTNEUmVzdEIyQ01heTIyJmM9NTg4MTk4OTYwJnRva2VuPUdsVlFCZ05RQndRTUJBUSUzRCZ0cnk9MSYkZm9sbG93X3JlZGlyZWN0PXRydWU=" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3248 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2264 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 375
Read events
22 194
Write events
177
Delete events
4
Modification events
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960871 | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960871 | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
44
Text files
84
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7D6243C18F0F8F9AEC6638DD210F1984_C92B405182A6249C6589A0B8DA1DCFCE | der | |
MD5:— | SHA256:— | |||
| 2264 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | binary | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7D6243C18F0F8F9AEC6638DD210F1984_C92B405182A6249C6589A0B8DA1DCFCE | binary | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:— | SHA256:— | |||
| 2264 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
96
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3248 | iexplore.exe | GET | 302 | 35.197.220.123:80 | http://deliver.angelbroking.in/lt.pl?id=19783=IU8AUVQAAAAHTFRTBg4PUFcBAVMBUgcCAwIAUQdfAVdSAQMFAVoFW1JTBlECVVtSAQNOE0QER1UCTwoLQklcCgddWVVVAHdfWVFYCRxVV15NBARWBFwMAVZQUlEDDQRTVAFMCRFNRwIbH1UAXl9OVkMbUw1RAFhWFA4KDVxeGw0MHFwVS0lbB11UTRMB&fl=CkdEERYDGBddXgBLRV9CQV5WWQZCCFVdCk8PAUYWRw==&ext=ZT1LMjVxQUI4SUNXTjZiMnQlMkZEU1pqZUFzREJ3VmphQ3cxS1Mwc05Vd0JBZzFrYkdOJTJGWlNZU0MwRlZRa2MlMkJOVHdVTkRVOUlGdFZjWFFyYXk0dUlUODhQMDUlMkJYa0ElMkJQRHNvTmk0N0pGd1FjbGclMkJPVGt1TXlZcGFVVktRMThJTXpacGJYaGpmUWNEQVFGbmEyZDhDR2hpZVFBQUJBWm5lSDVwSUNBZ0lHMUFXRUk0TG5CeGRTMG9PVmx2VlZFeE95Y25JM2d2JnI9aHR0cHMlM0ElMkYlMkZ3d3cuYW5nZWxicm9raW5nLmNvbSUyRnBwYyUyRnJlZmVyLWEtZnJpZW5kLW5ldyUzRnV0bV9zb3VyY2UlM0RSbkVXZWJwYWdlJTI2dXRtX21lZGl1bSUzRFJuRSUyNTIwLSUyNTIwQ2xpZW50JTI2dXRtX2NhbXBhaWduJTNEUmVzdEIyQ01heTIyJmM9NTg4MTk4OTYwJnRva2VuPUdsVlFCZ05RQndRTUJBUSUzRCZ0cnk9MSYkZm9sbG93X3JlZGlyZWN0PXRydWU= | US | — | — | suspicious |
3248 | iexplore.exe | GET | 302 | 35.197.220.123:80 | http://deliver.angelbroking.in/lt.pl?id=19783=IU8AUVQAAAAHTFRTBg4PUFcBAVMBUgcCAwIAUQdfAVdSAQMFAVoFW1JTBlECVVtSAQNOE0QER1UCTwoLQklcCgddWVVVAHdfWVFYCRxVV15NBARWBFwMAVZQUlEDDQRTVAFMCRFNRwIbH1UAXl9OVkMbUw1RAFhWFA4KDVxeGw0MHFwVS0lbB11UTRMB&fl=CkdEERYDGBddXgBLRV9CQV5WWQZCCFVdCk8PAUYWRw==&ext=ZT1LMjVxQUI4SUNXTjZiMnQlMkZEU1pqZUFzREJ3VmphQ3cxS1Mwc05Vd0JBZzFrYkdOJTJGWlNZU0MwRlZRa2MlMkJOVHdVTkRVOUlGdFZjWFFyYXk0dUlUODhQMDUlMkJYa0ElMkJQRHNvTmk0N0pGd1FjbGclMkJPVGt1TXlZcGFVVktRMThJTXpacGJYaGpmUWNEQVFGbmEyZDhDR2hpZVFBQUJBWm5lSDVwSUNBZ0lHMUFXRUk0TG5CeGRTMG9PVmx2VlZFeE95Y25JM2d2JnI9aHR0cHMlM0ElMkYlMkZ3d3cuYW5nZWxicm9raW5nLmNvbSUyRnBwYyUyRnJlZmVyLWEtZnJpZW5kLW5ldyUzRnV0bV9zb3VyY2UlM0RSbkVXZWJwYWdlJTI2dXRtX21lZGl1bSUzRFJuRSUyNTIwLSUyNTIwQ2xpZW50JTI2dXRtX2NhbXBhaWduJTNEUmVzdEIyQ01heTIyJmM9NTg4MTk4OTYwJnRva2VuPUdsVlFCZ05RQndRTUJBUSUzRCZ0cnk9MSYkZm9sbG93X3JlZGlyZWN0PXRydWU= | US | — | — | suspicious |
3248 | iexplore.exe | GET | 200 | 184.24.77.48:80 | http://e1.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBTvkAFw3ViPKmUeIVEf3NC7b1ErqwQUWvPtK%2Fw2wjd5uVIw6lRvz1XLLqwCEgRlcVD5AzX4QmqWhppG4%2Fqyag%3D%3D | US | der | 344 b | whitelisted |
3248 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x2.c.lencr.org/ | US | der | 299 b | whitelisted |
3248 | iexplore.exe | GET | 200 | 18.64.100.199:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3248 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHr7M35ZTSPHb9t8TGKb2tY%3D | US | der | 1.40 Kb | whitelisted |
3248 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCdUrA%2FwvrytArhIvu6cF3d | US | der | 472 b | whitelisted |
3248 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?083ea7dff19e872e | US | compressed | 60.0 Kb | whitelisted |
3248 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDwQ9JNOs3IcArkp%2FBu7NbU | US | der | 472 b | whitelisted |
3248 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2264 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3248 | iexplore.exe | 18.66.242.58:80 | ocsp.rootg2.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
3248 | iexplore.exe | 35.197.220.123:80 | deliver.angelbroking.in | Google Inc. | US | unknown |
2264 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3248 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
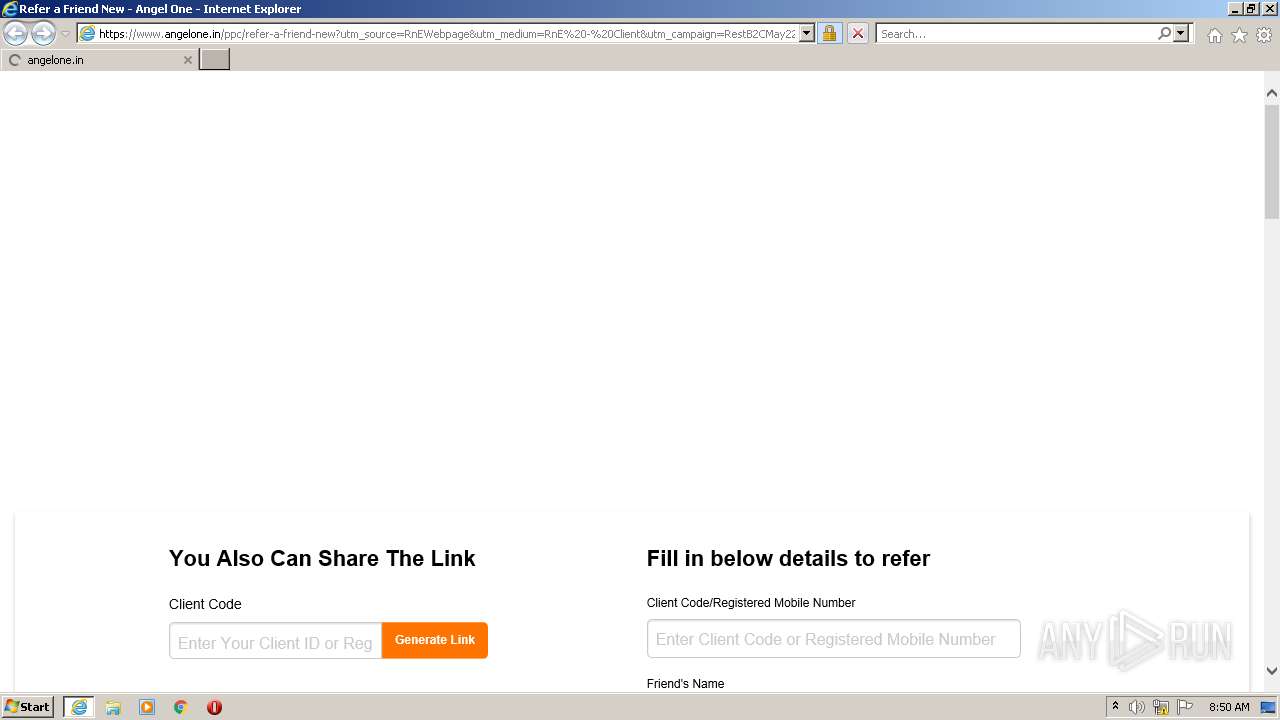
3248 | iexplore.exe | 104.21.85.142:443 | www.angelbroking.com | Cloudflare Inc | US | unknown |
3248 | iexplore.exe | 96.16.145.230:80 | x1.c.lencr.org | Akamai Technologies, Inc. | US | suspicious |
3248 | iexplore.exe | 18.66.242.45:80 | ocsp.rootg2.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
3248 | iexplore.exe | 108.156.253.131:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
3248 | iexplore.exe | 172.66.43.185:443 | www.angelone.in | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
deliver.angelbroking.in |
| unknown |
in1.wizrocketmail.net |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.digicert.com |
| whitelisted |
ocsp.sca1b.amazontrust.com |
| whitelisted |