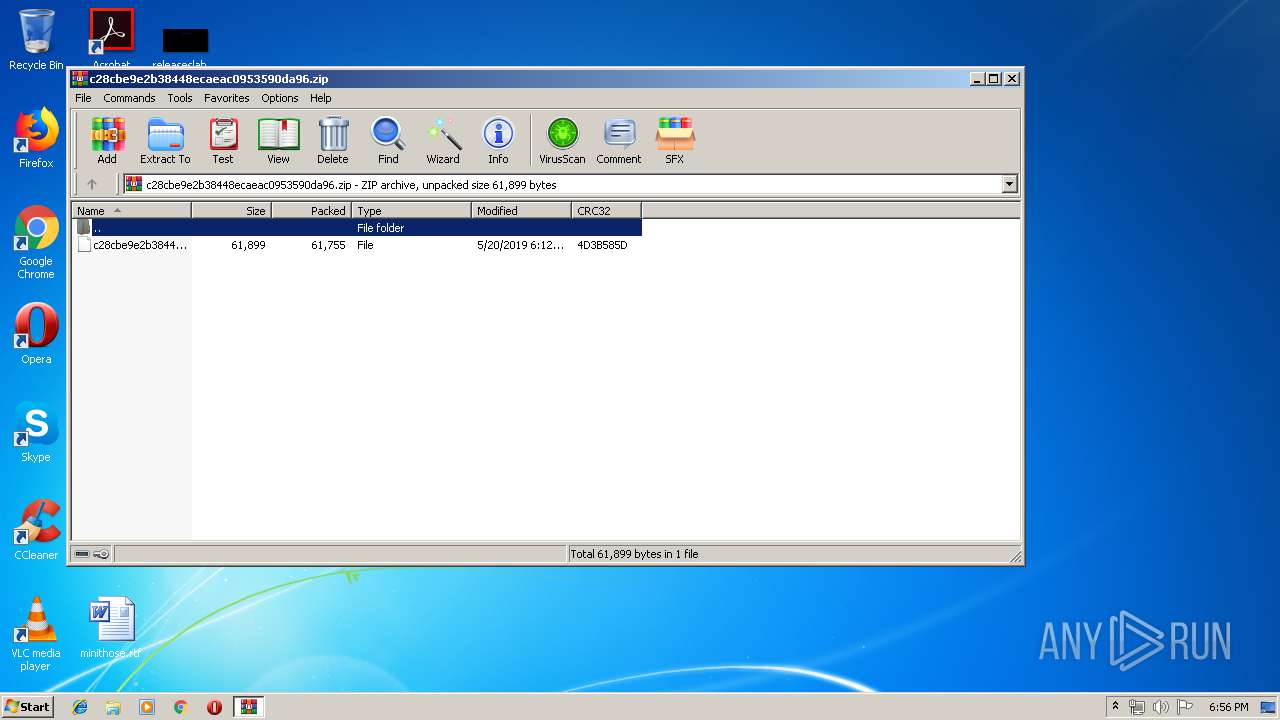
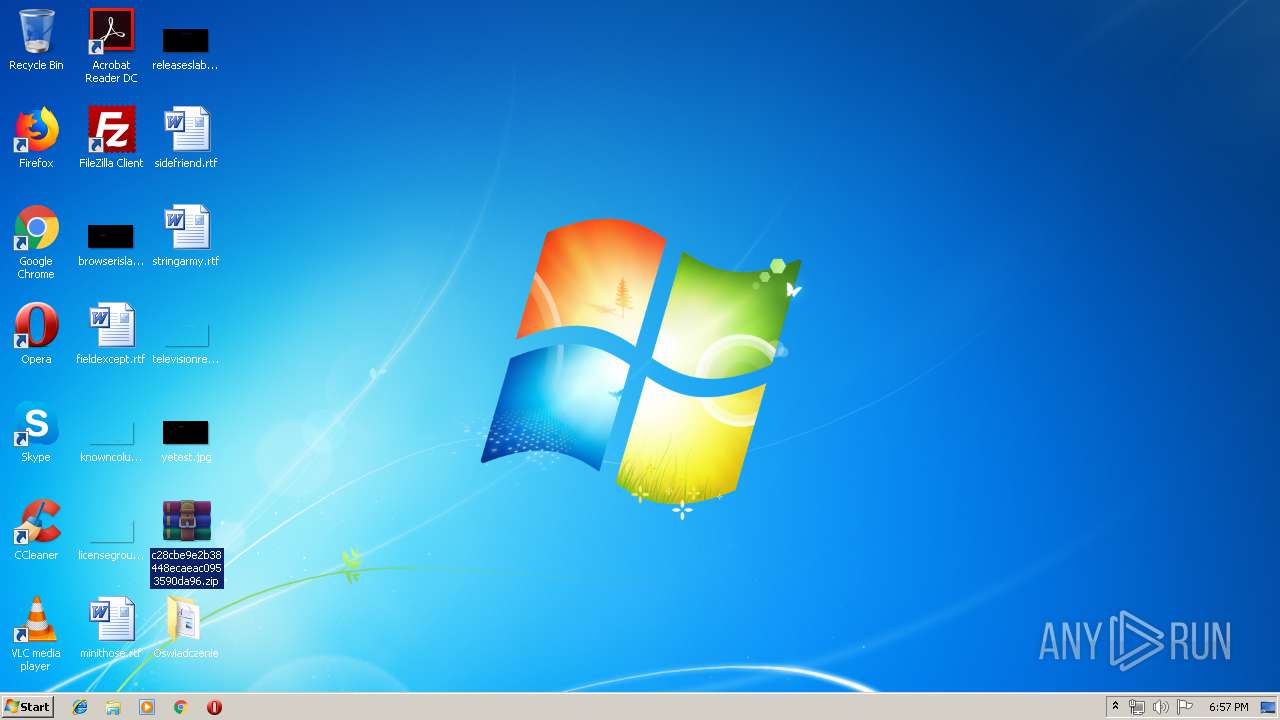
| File name: | c28cbe9e2b38448ecaeac0953590da96.zip |
| Full analysis: | https://app.any.run/tasks/7bde9a79-e189-4f22-a088-9e82451a601f |
| Verdict: | Malicious activity |
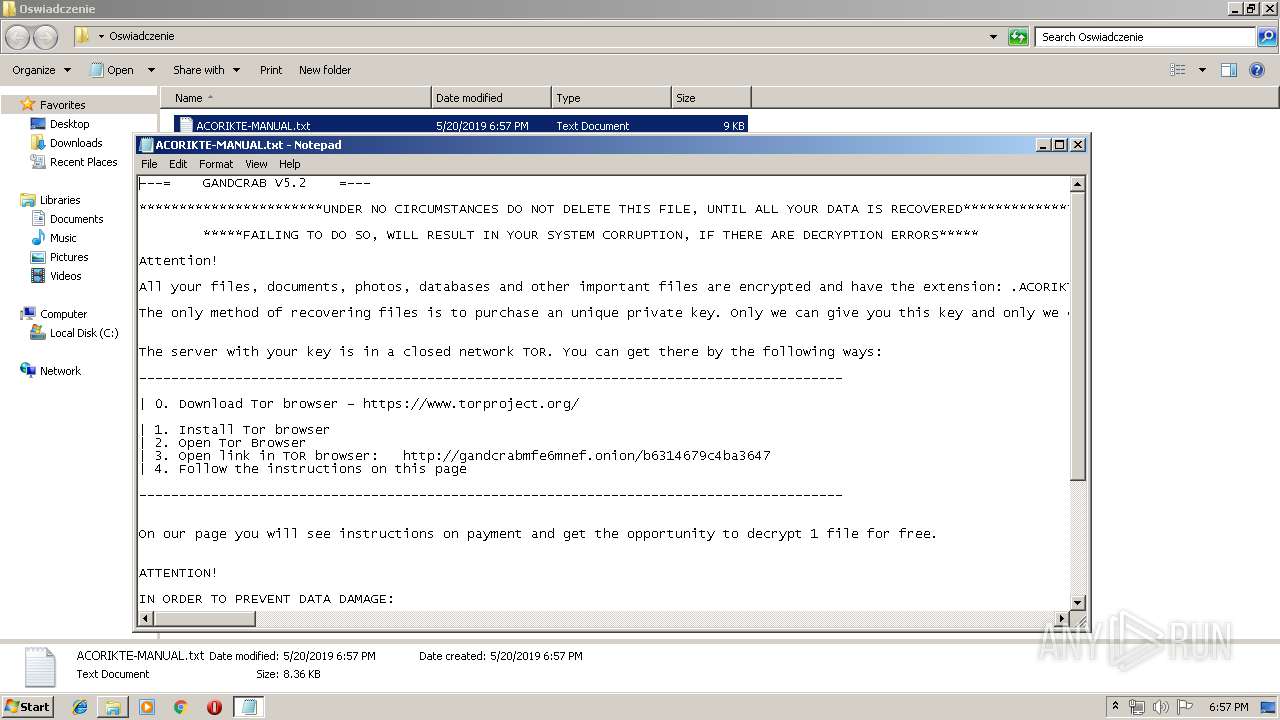
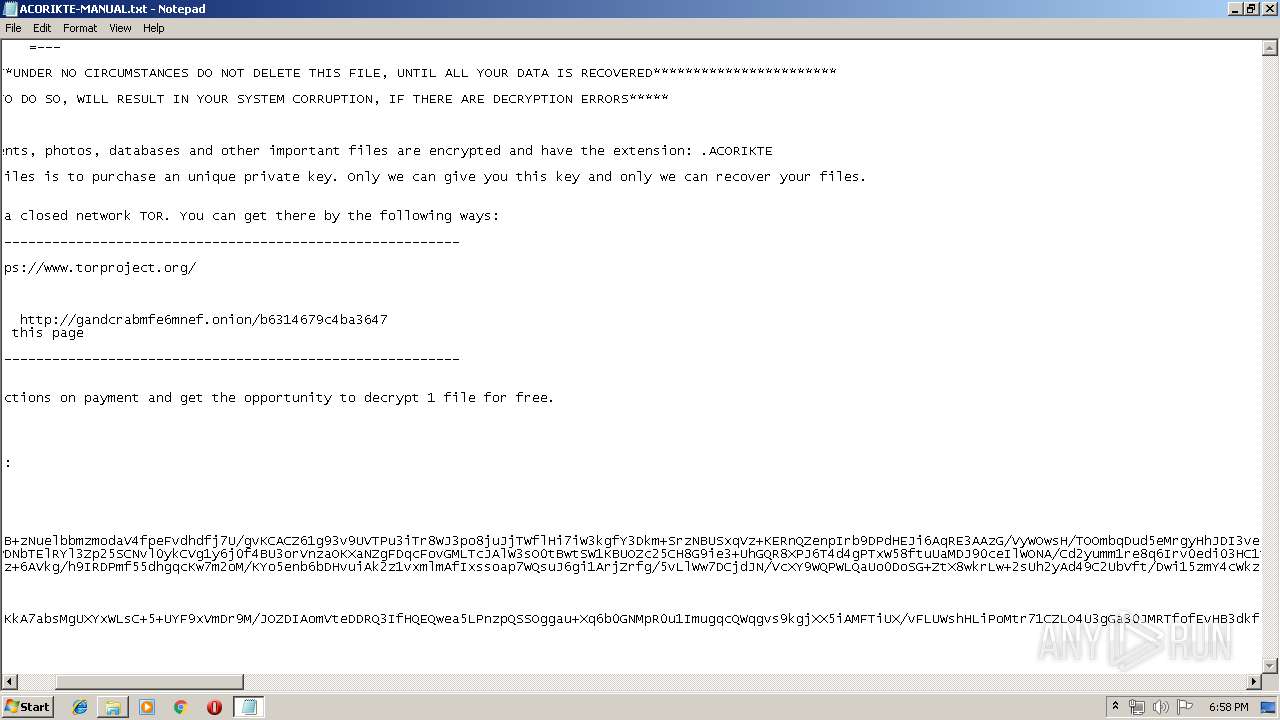
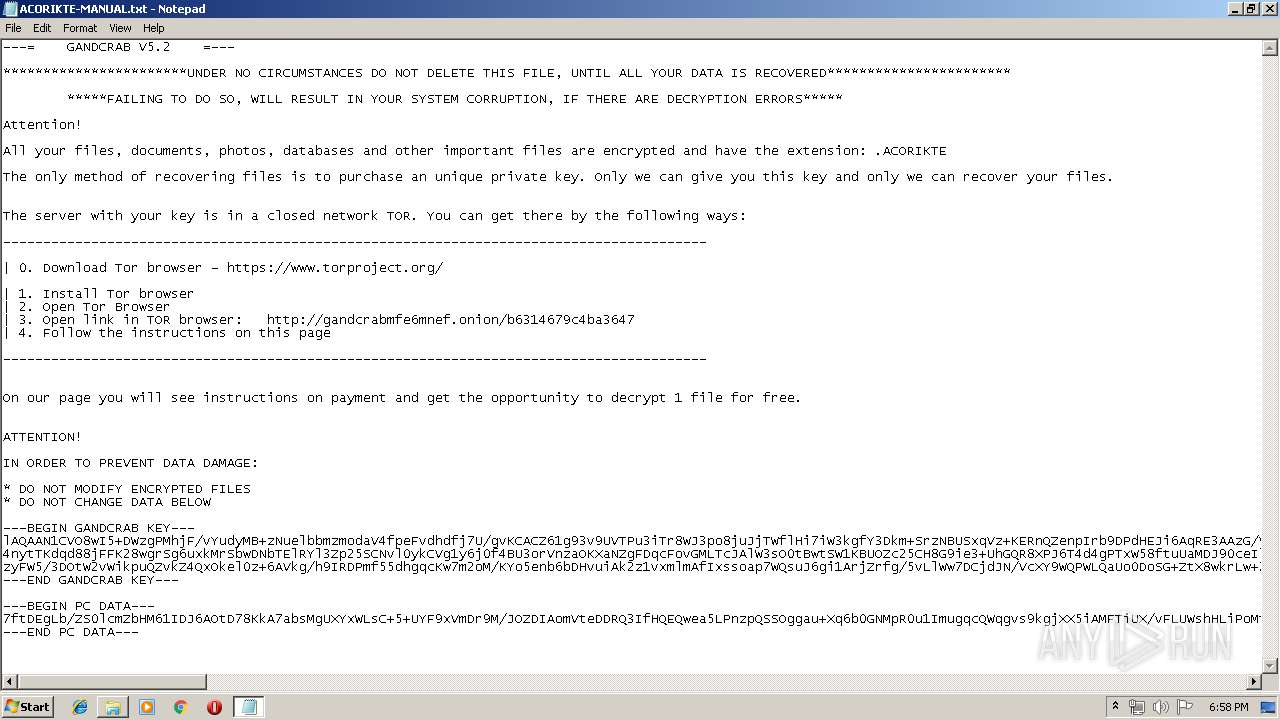
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | May 20, 2019, 17:55:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 894AC39E74D206028F98318C83458036 |
| SHA1: | 1AFC945BEF79D79979900622DAF918B83D9E7020 |
| SHA256: | 09426C2EE9309B2BAA78658AB4883F334EB54EED2C079C45664101015496656C |
| SSDEEP: | 1536:WnIKbOdaKhjMfAqpgZETLGGOwnACp65I9t5:F3VhJXZ4ipCpX |
MALICIOUS
Application was dropped or rewritten from another process
- log.txt (PID: 3224)
Actions looks like stealing of personal data
- log.txt (PID: 3224)
Writes file to Word startup folder
- log.txt (PID: 3224)
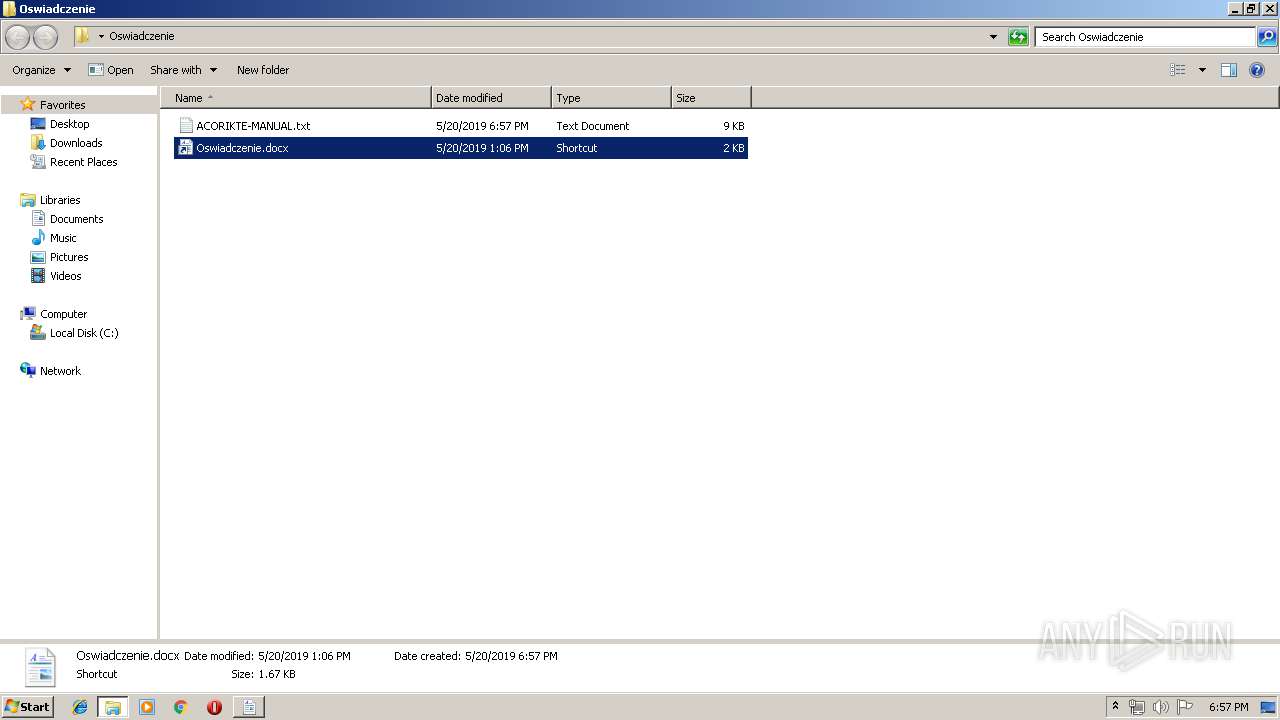
Renames files like Ransomware
- log.txt (PID: 3224)
Deletes shadow copies
- cmd.exe (PID: 1716)
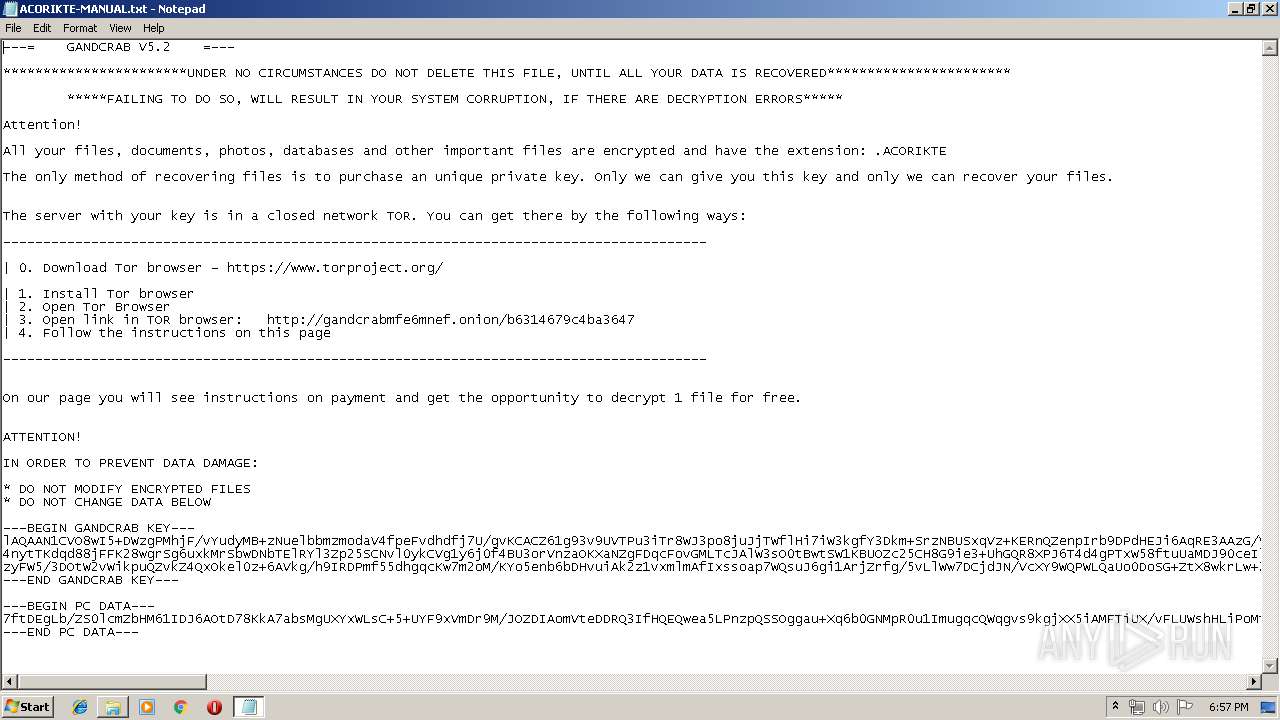
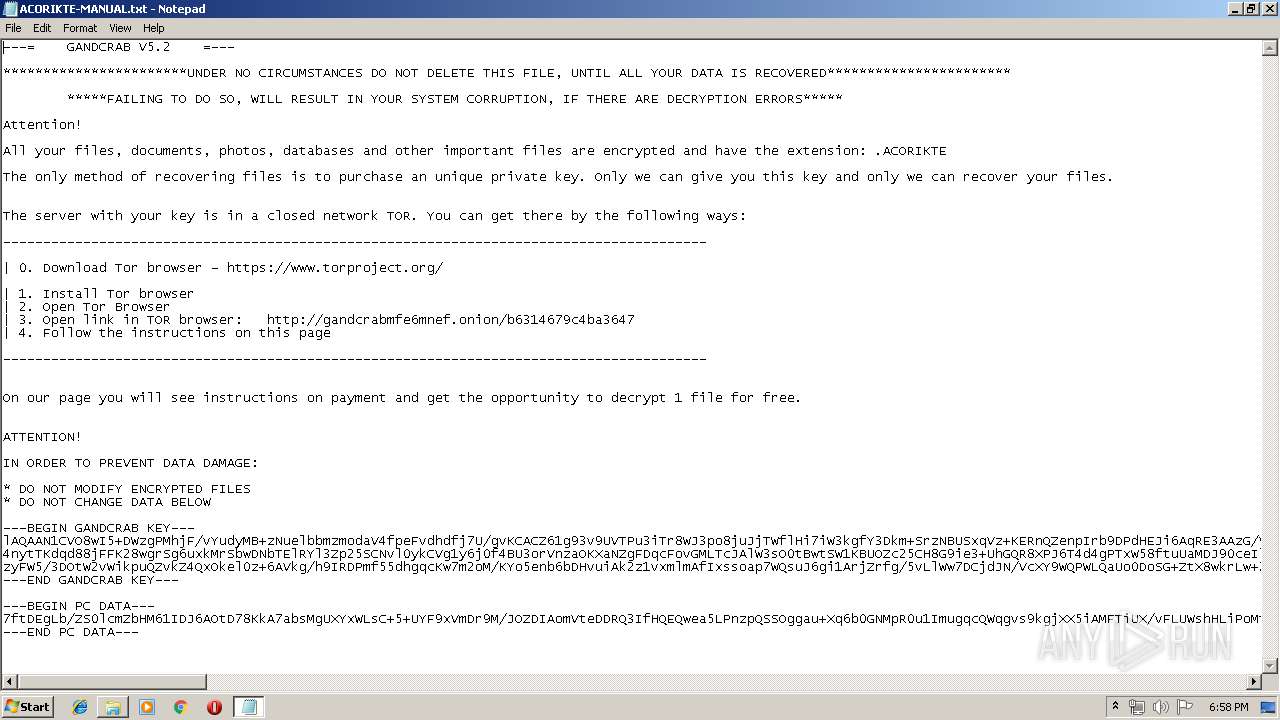
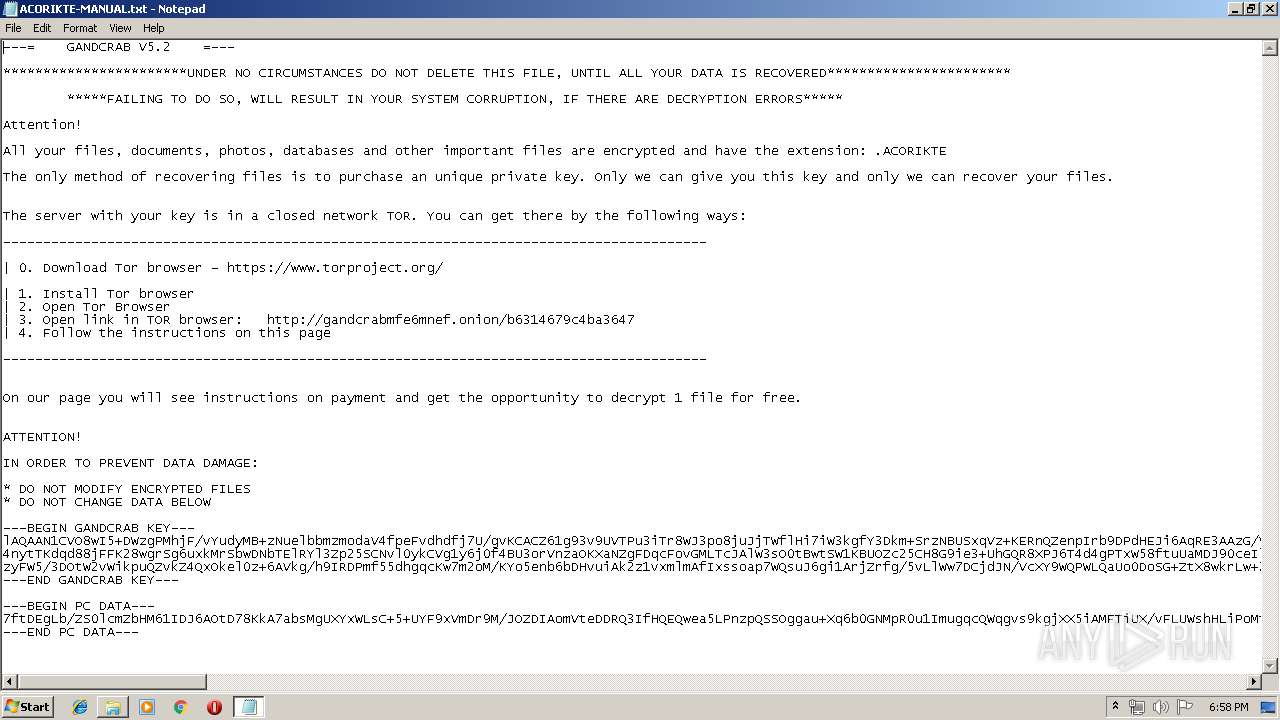
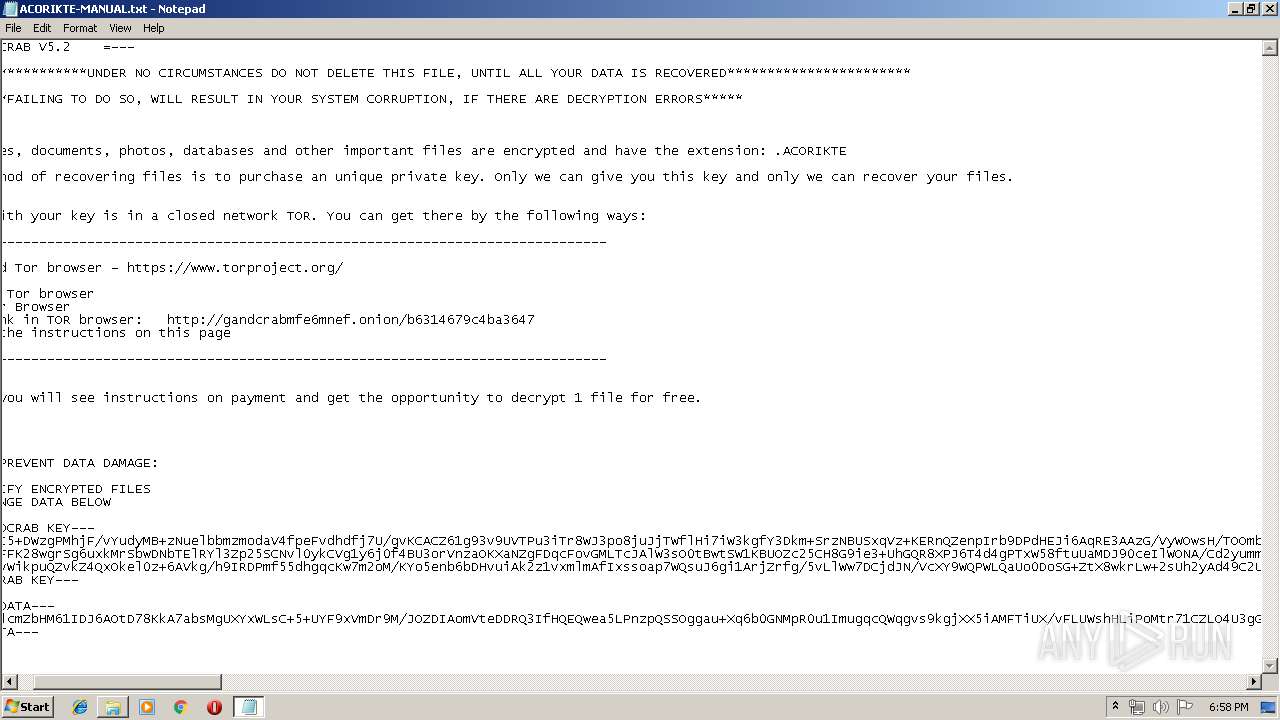
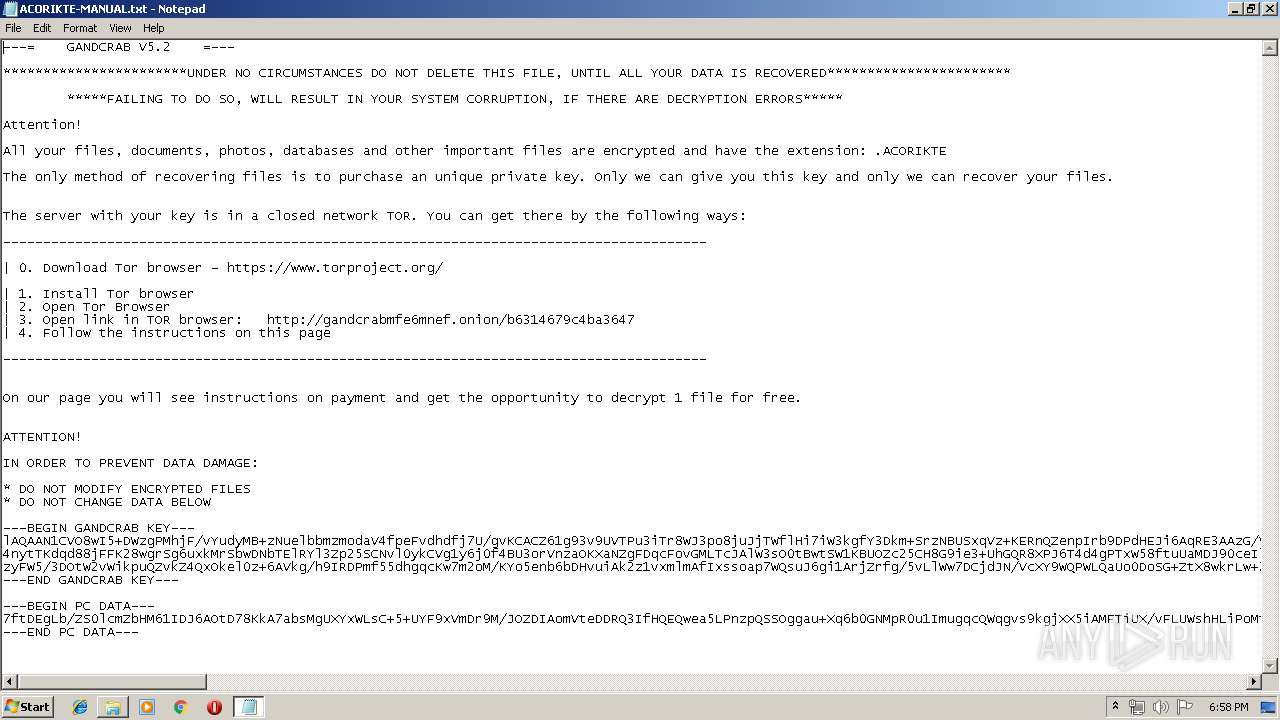
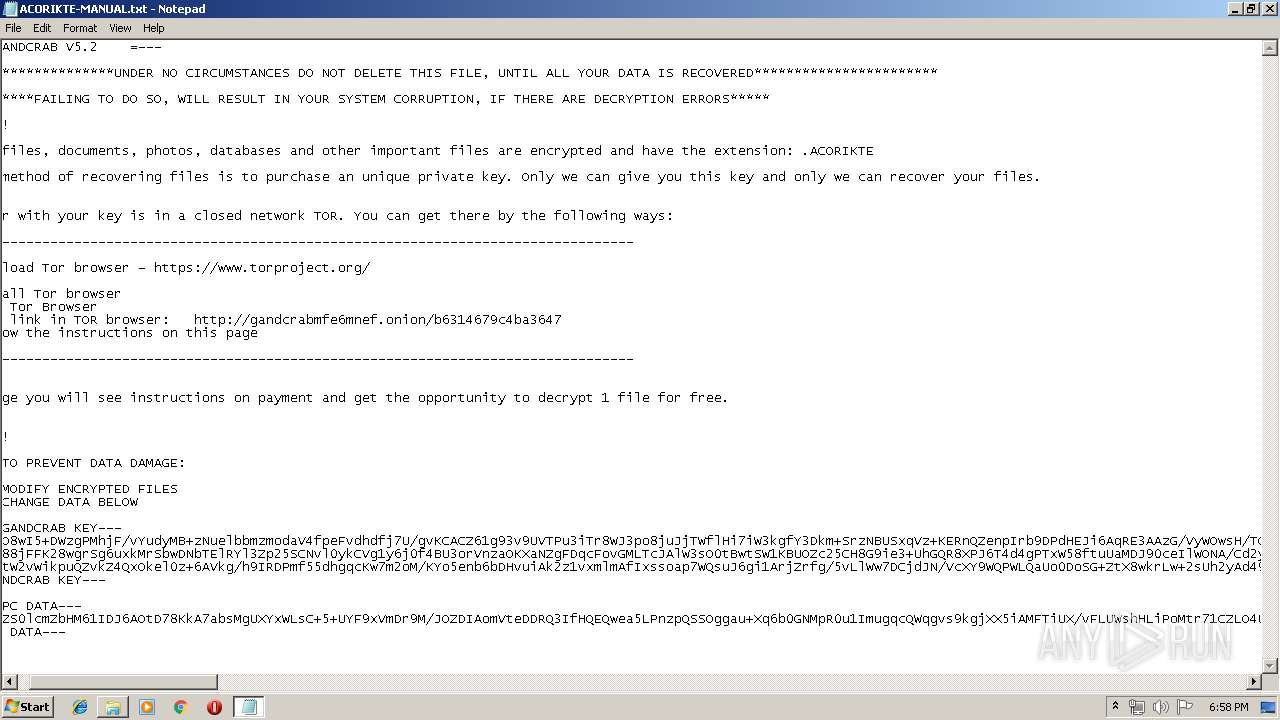
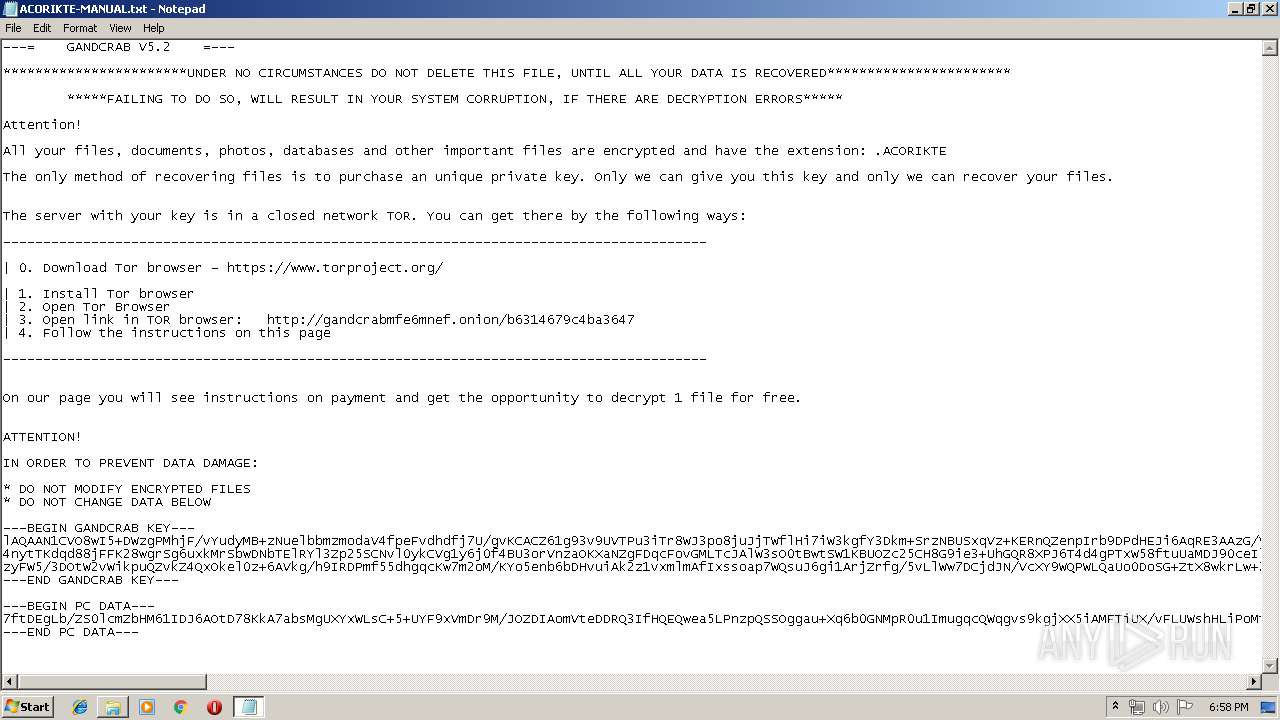
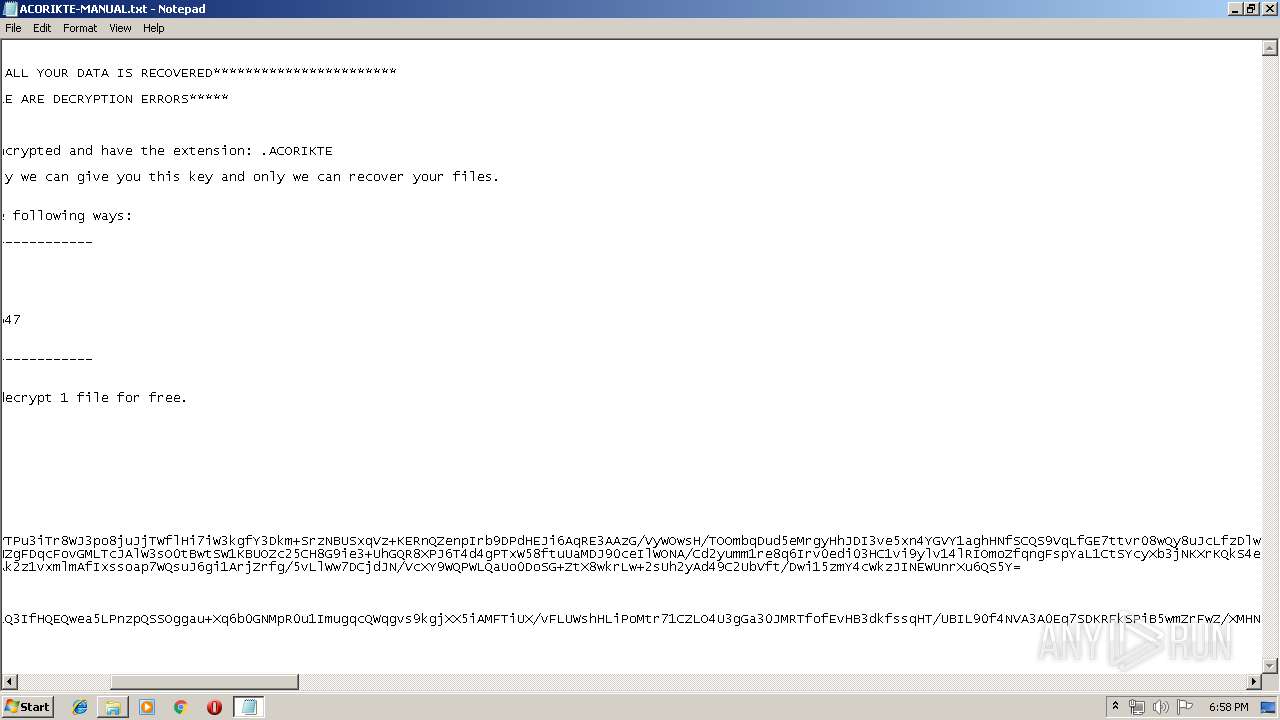
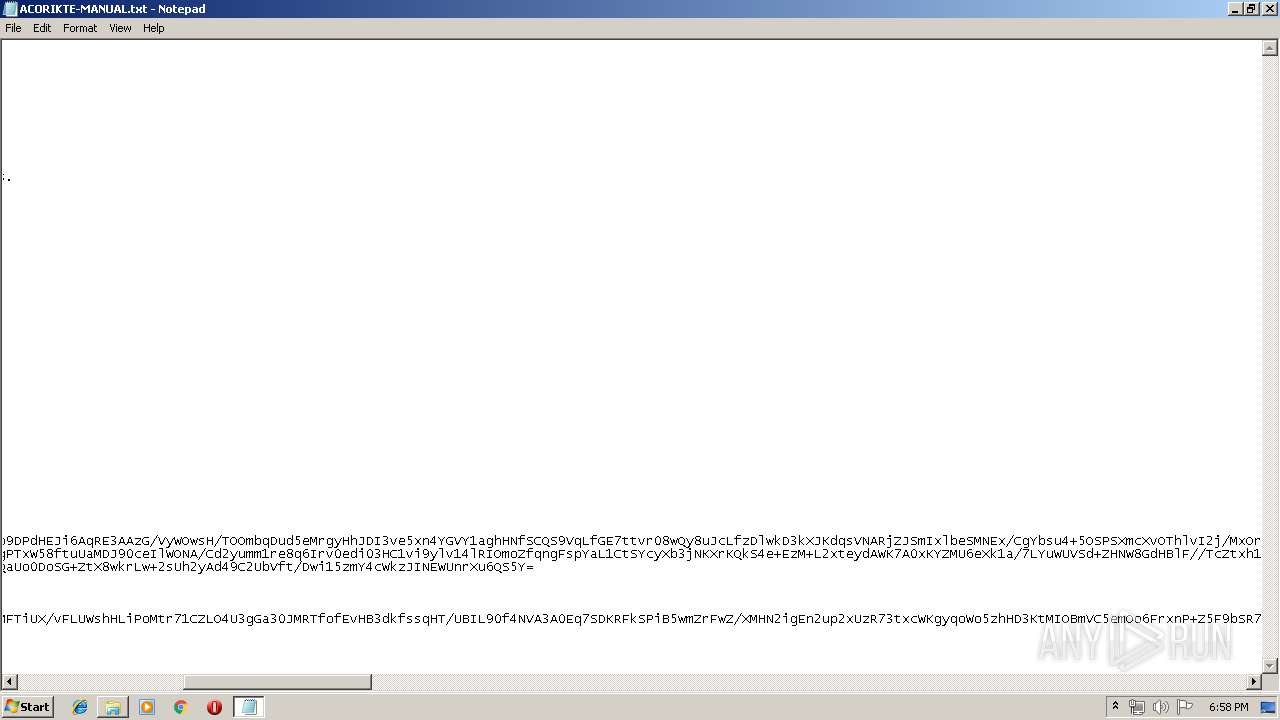
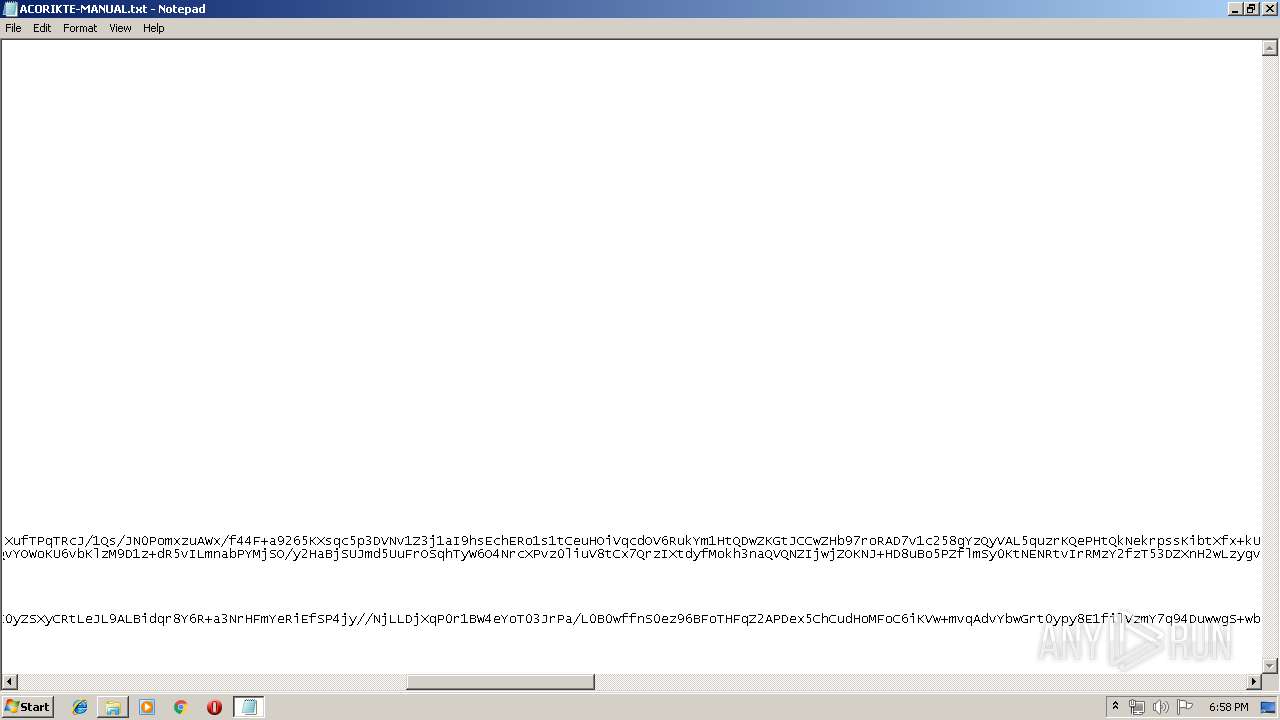
Dropped file may contain instructions of ransomware
- log.txt (PID: 3224)
GANDCRAB detected
- log.txt (PID: 3224)
SUSPICIOUS
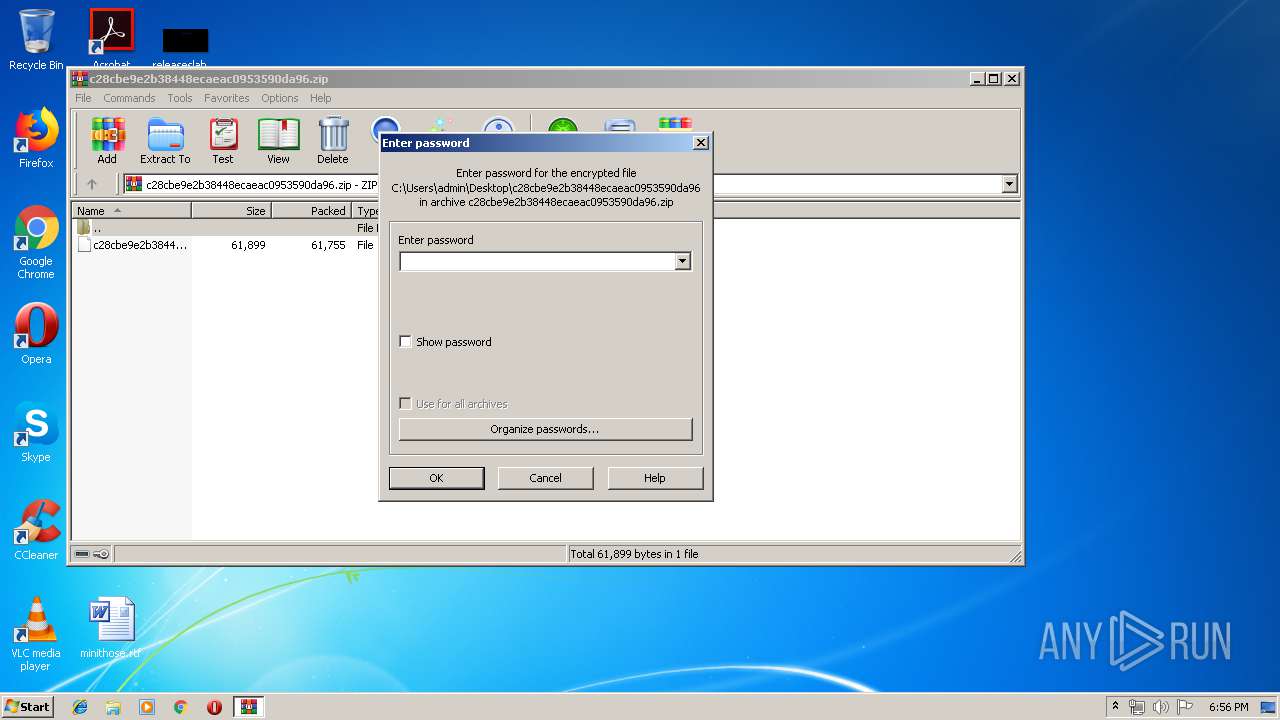
Starts application with an unusual extension
- cmd.exe (PID: 3448)
Executable content was dropped or overwritten
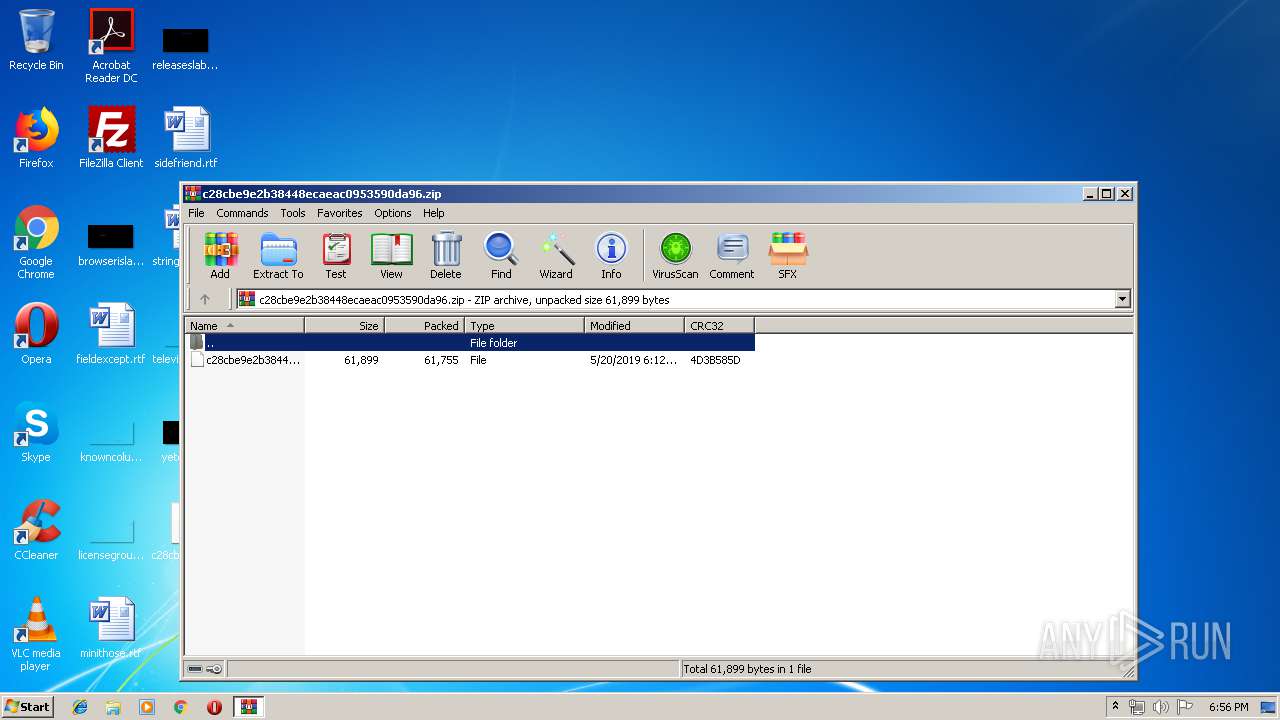
- WinRAR.exe (PID: 3436)
Creates files in the program directory
- log.txt (PID: 3224)
Reads the cookies of Mozilla Firefox
- log.txt (PID: 3224)
Executed as Windows Service
- vssvc.exe (PID: 3872)
Starts CMD.EXE for commands execution
- log.txt (PID: 3224)
Creates files in the user directory
- log.txt (PID: 3224)
INFO
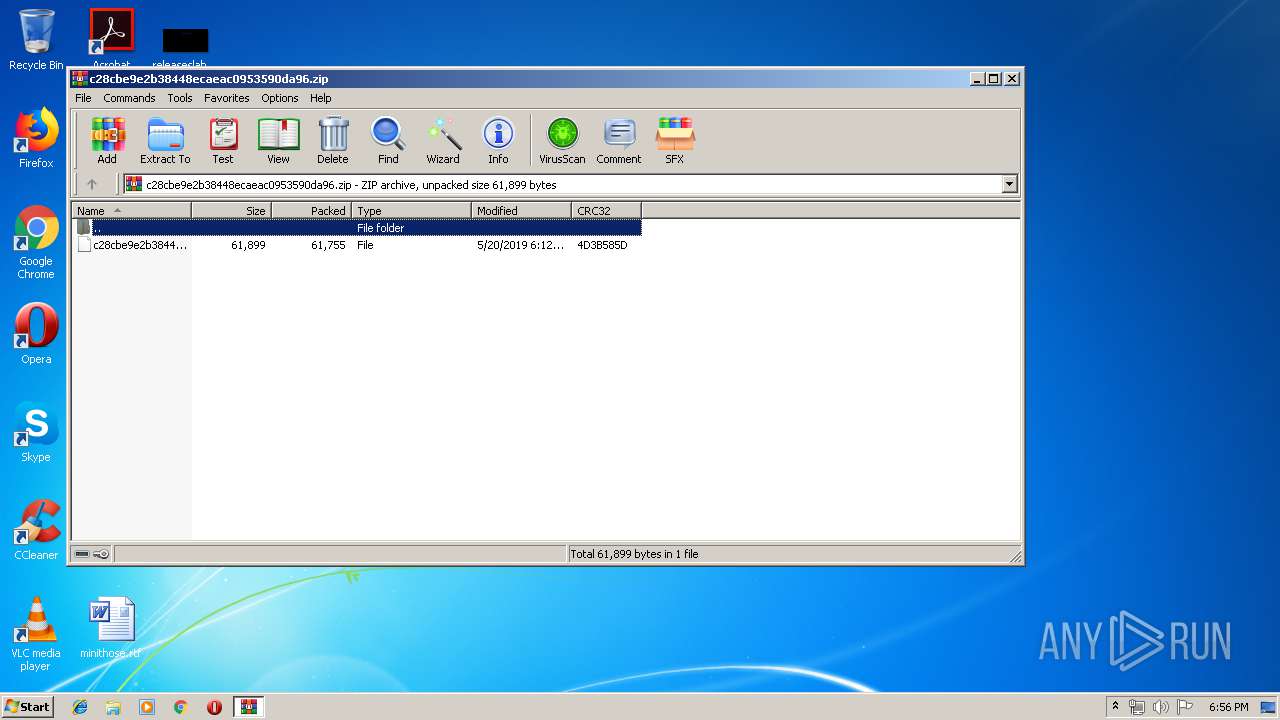
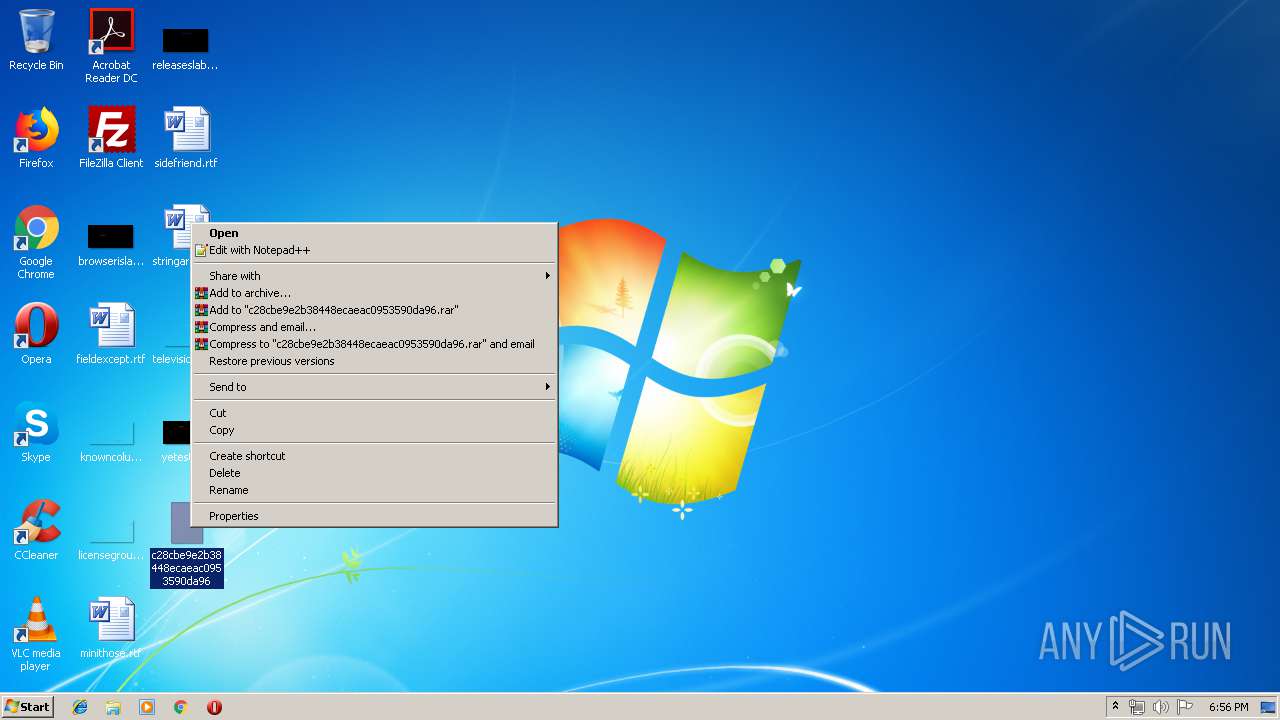
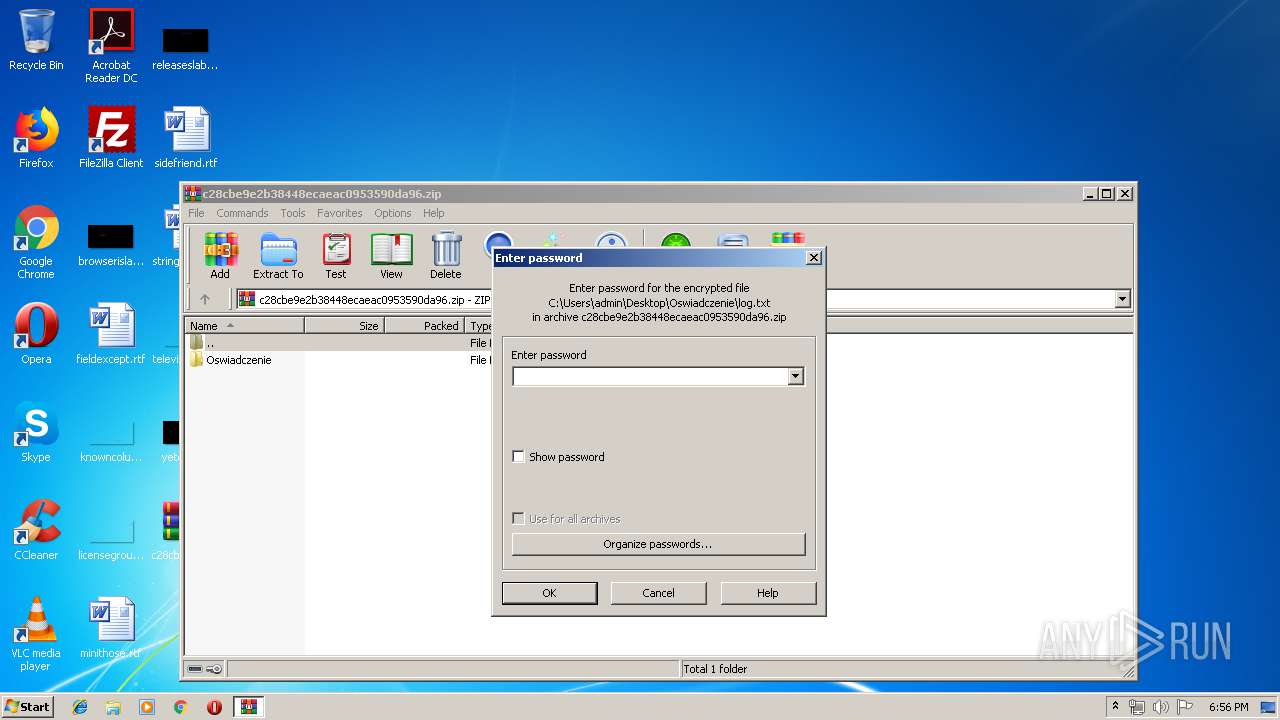
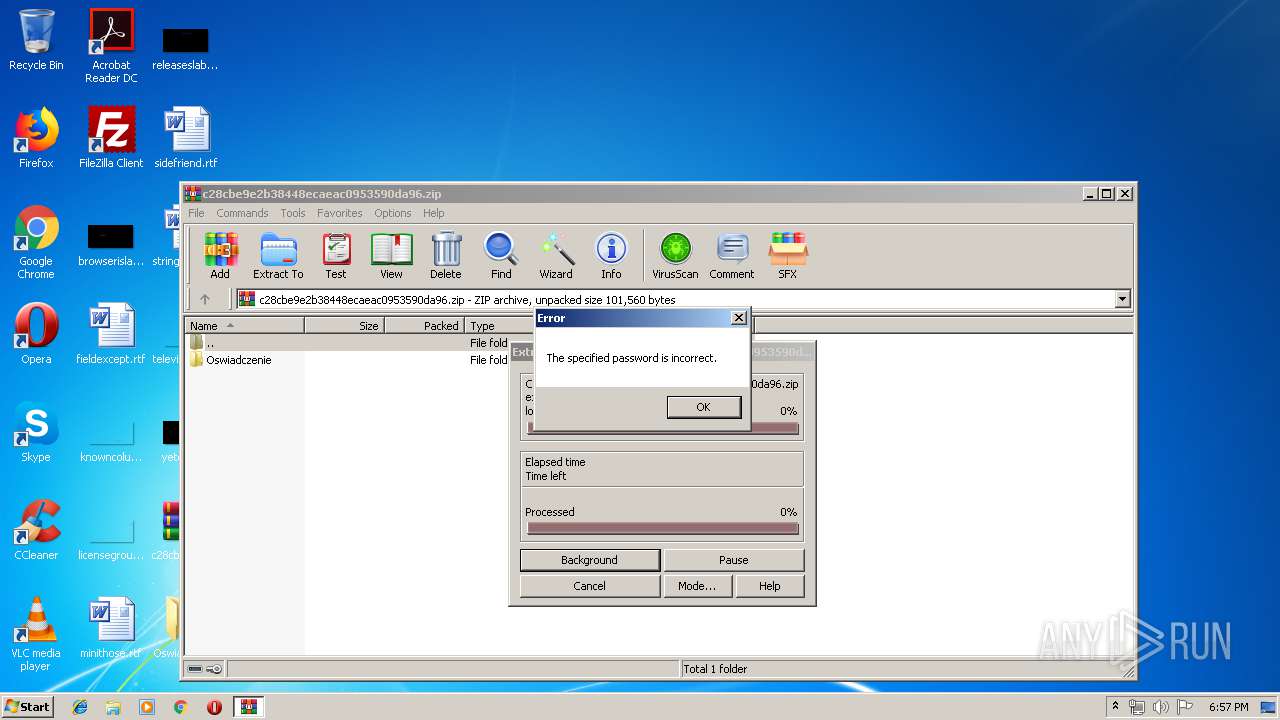
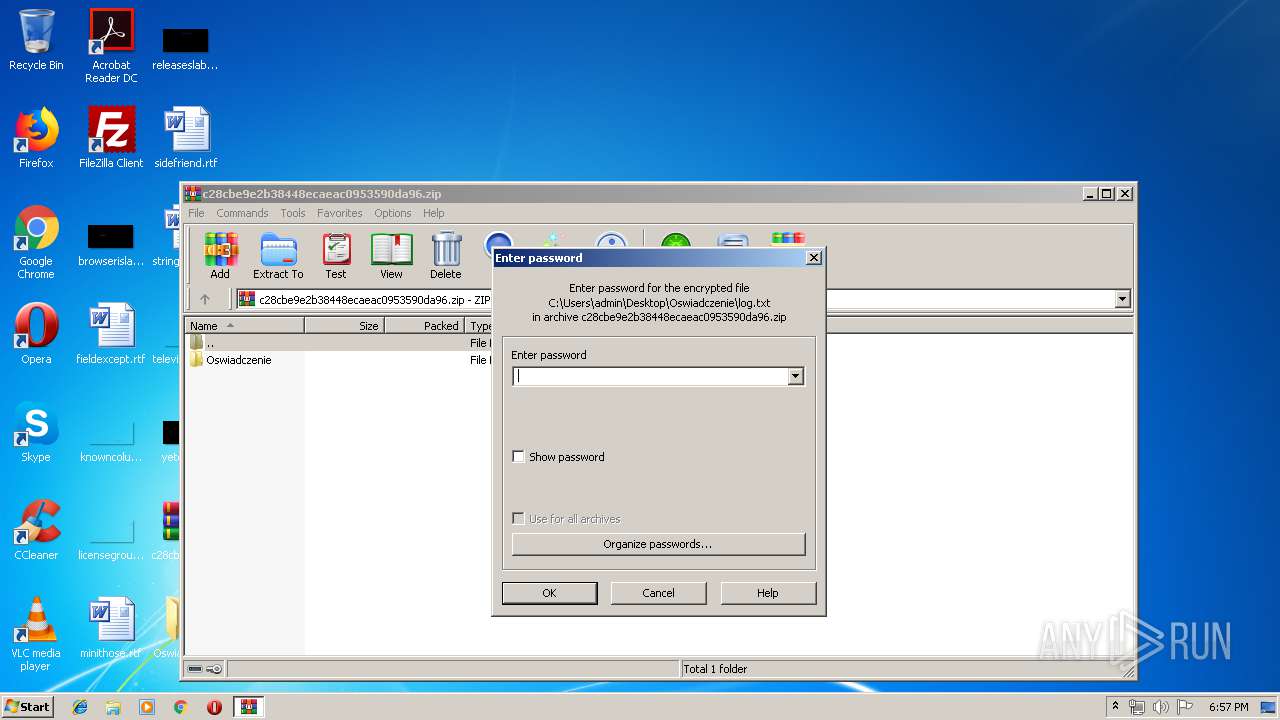
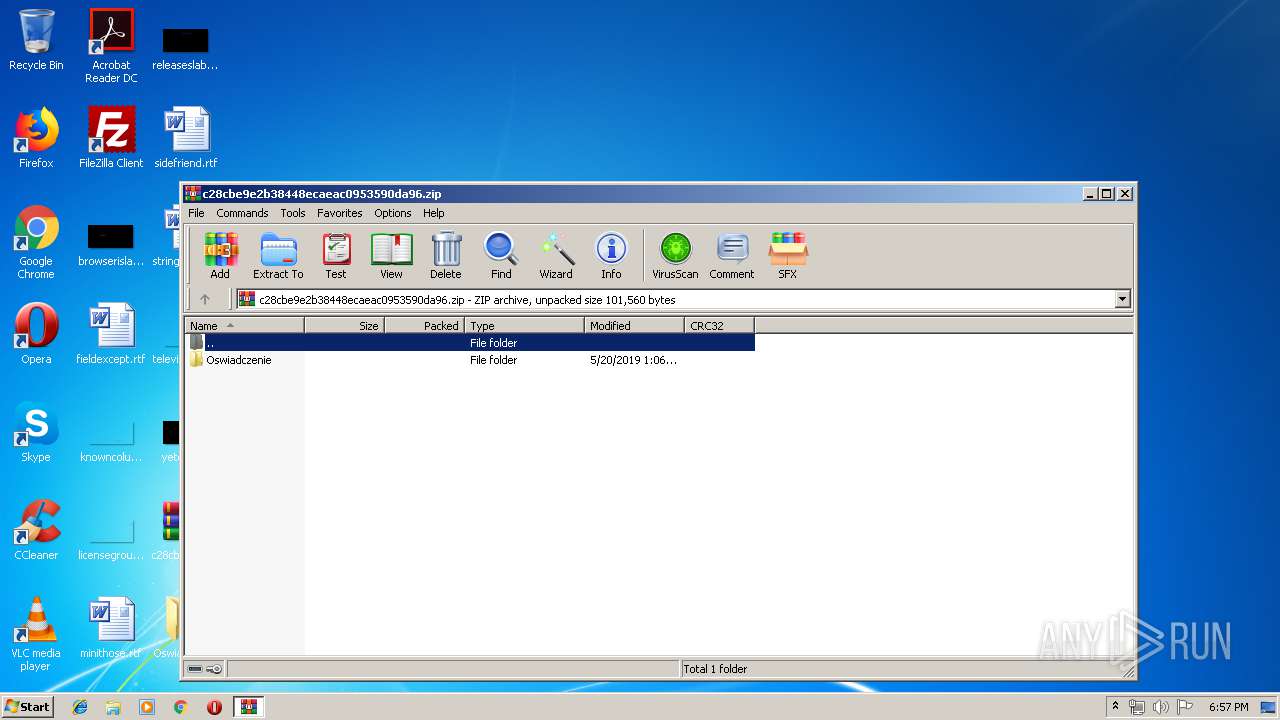
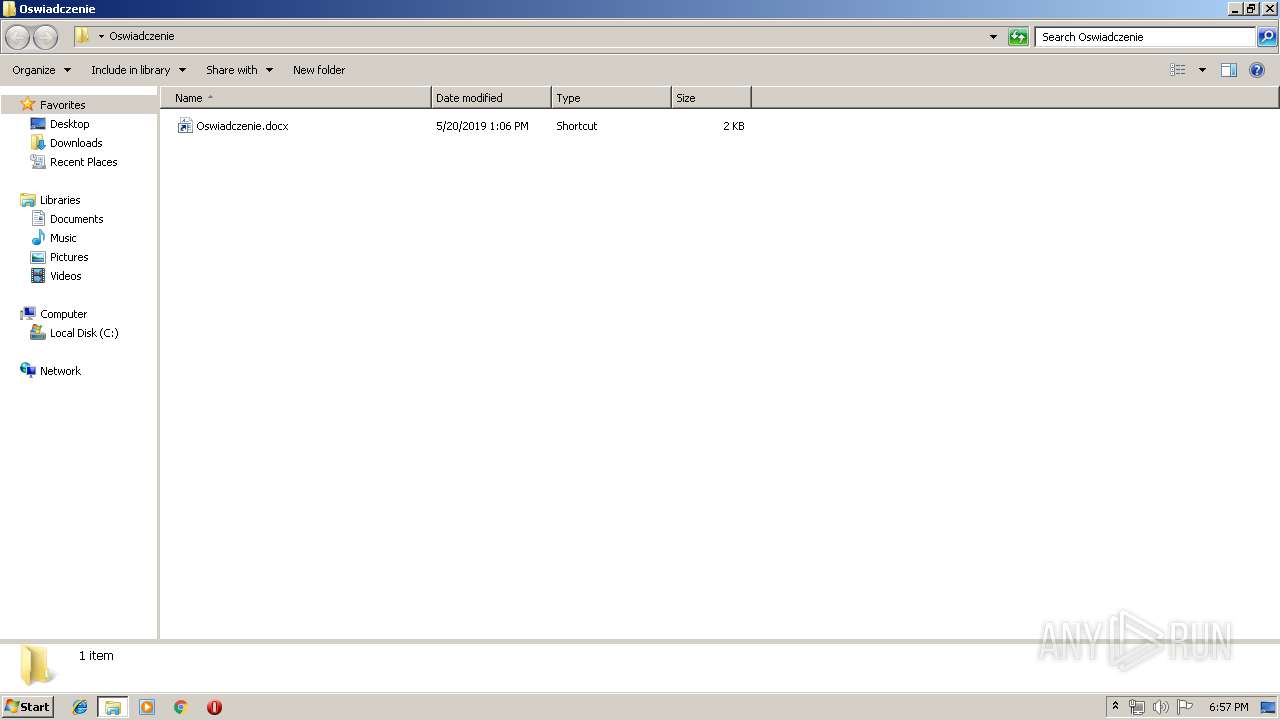
Manual execution by user
- WinRAR.exe (PID: 3436)
- cmd.exe (PID: 3448)
- NOTEPAD.EXE (PID: 1484)
Dropped object may contain Bitcoin addresses
- log.txt (PID: 3224)
Application was crashed
- log.txt (PID: 3224)
Dropped object may contain TOR URL's
- log.txt (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:20 19:12:05 |
| ZipCRC: | 0x4d3b585d |
| ZipCompressedSize: | 61755 |
| ZipUncompressedSize: | 61899 |
| ZipFileName: | c28cbe9e2b38448ecaeac0953590da96 |
Total processes
51
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
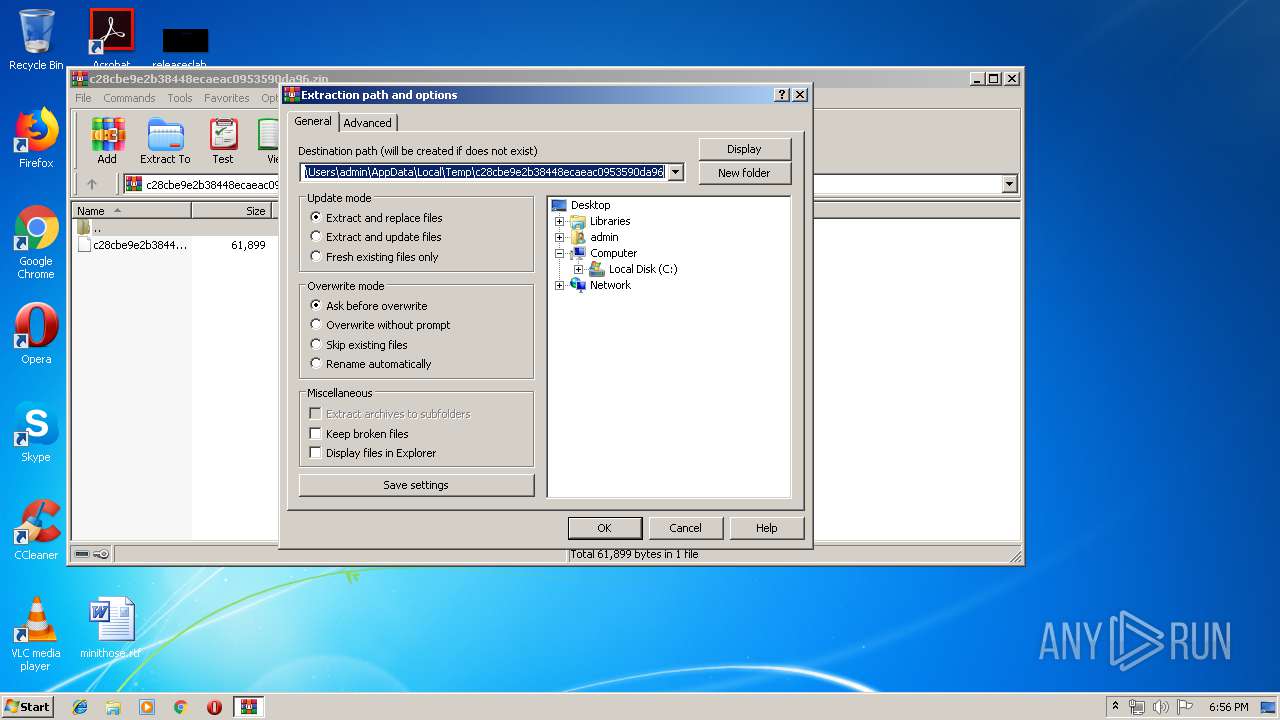
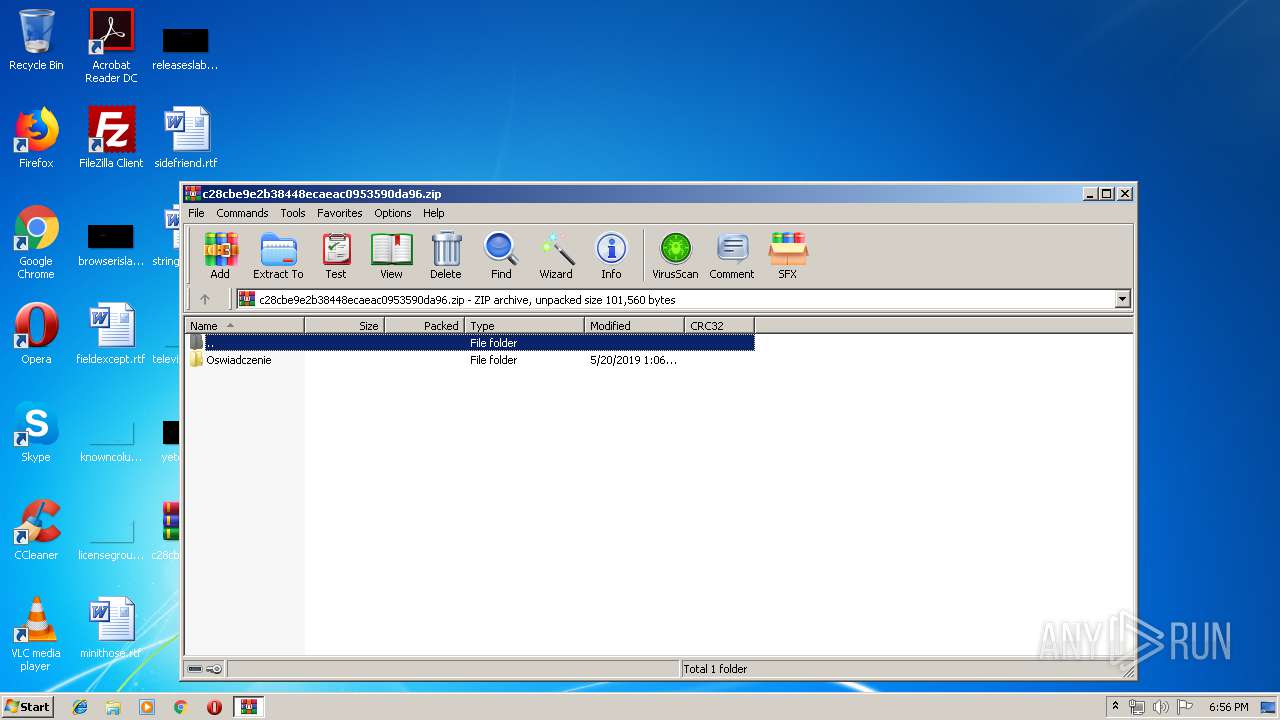
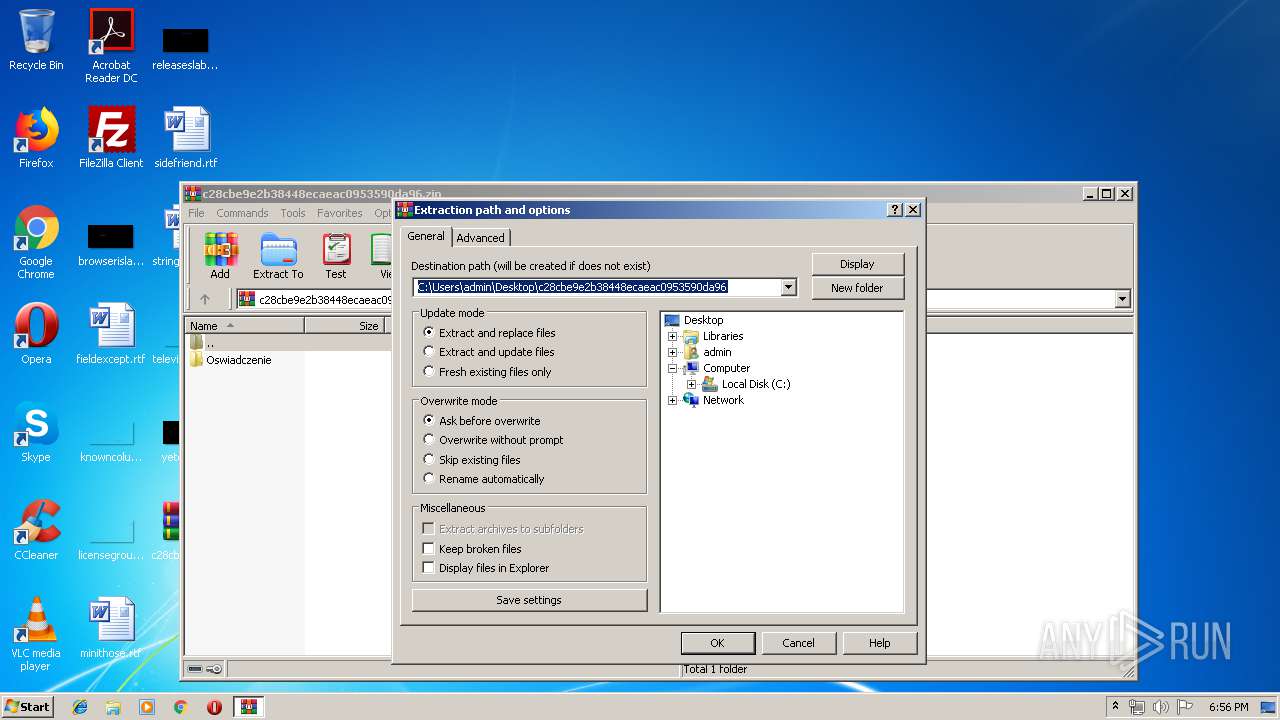
| 116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\c28cbe9e2b38448ecaeac0953590da96.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1104 | vssadmin delete shadows /all /quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
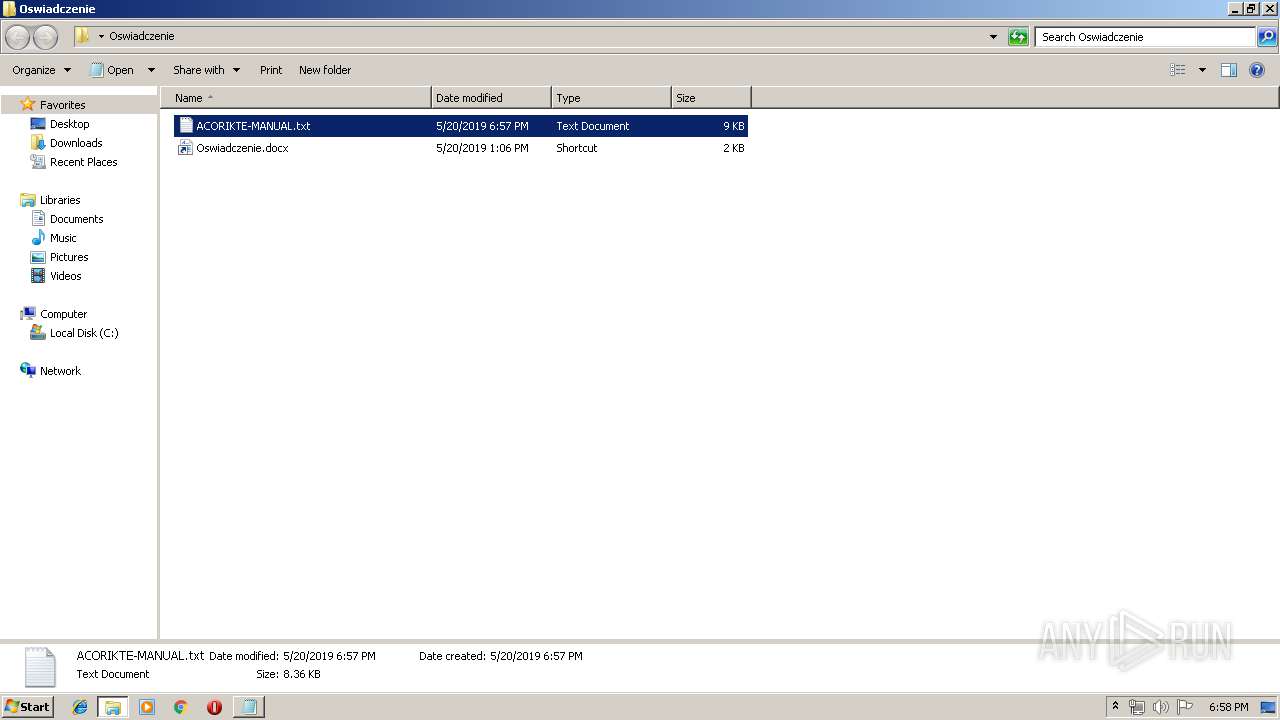
| 1484 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Oswiadczenie\ACORIKTE-MANUAL.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1716 | "C:\Windows\system32\cmd.exe" /c vssadmin delete shadows /all /quiet | C:\Windows\system32\cmd.exe | log.txt | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3224 | log.txt | C:\Users\admin\Desktop\Oswiadczenie\log.txt | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 255 Modules
| |||||||||||||||
| 3436 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\c28cbe9e2b38448ecaeac0953590da96.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3448 | "C:\Windows\System32\cmd.exe" /c log.txt | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3872 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
878
Read events
828
Write events
50
Delete events
0
Modification events
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\c28cbe9e2b38448ecaeac0953590da96.zip | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
428
Text files
318
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | log.txt | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3224 | log.txt | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 3224 | log.txt | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.acorikte | — | |
MD5:— | SHA256:— | |||
| 3224 | log.txt | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3224 | log.txt | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3436 | WinRAR.exe | C:\Users\admin\Desktop\Oswiadczenie\log.txt | executable | |
MD5:— | SHA256:— | |||
| 3224 | log.txt | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3224 | log.txt | C:\PerfLogs\ACORIKTE-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
| 3224 | log.txt | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3436 | WinRAR.exe | C:\Users\admin\Desktop\Oswiadczenie\Oswiadczenie.docx.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report