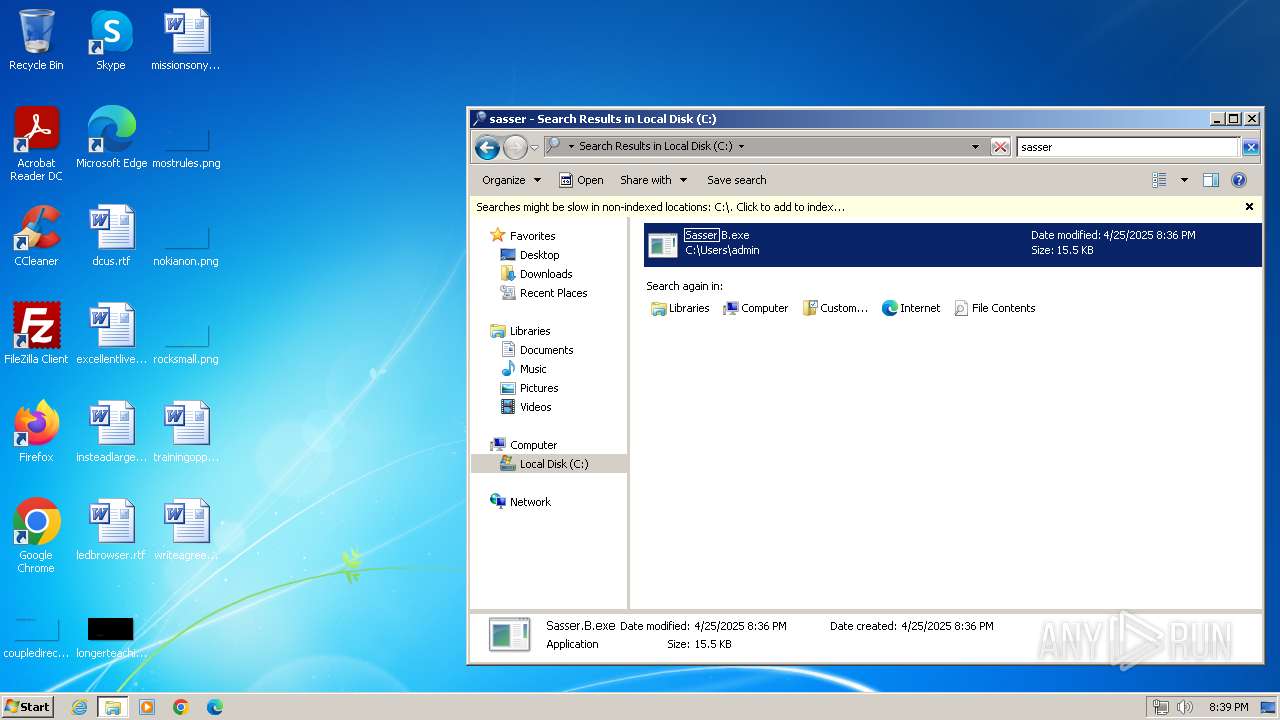
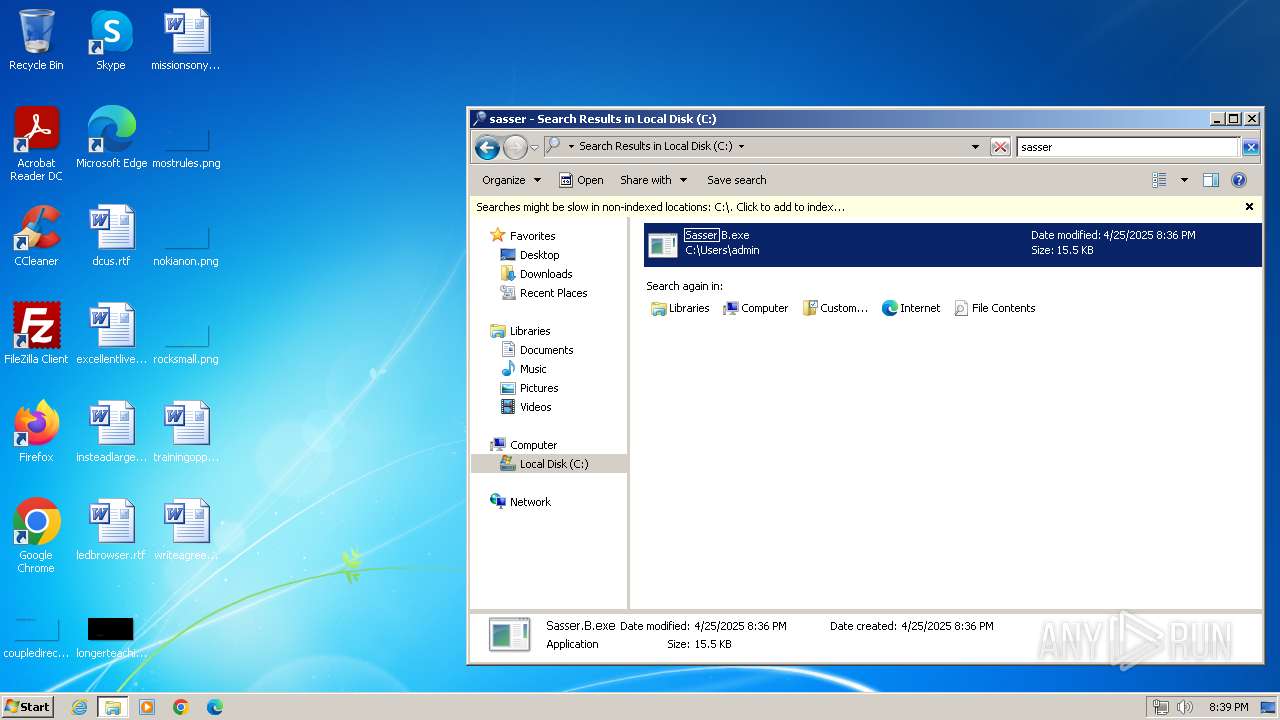
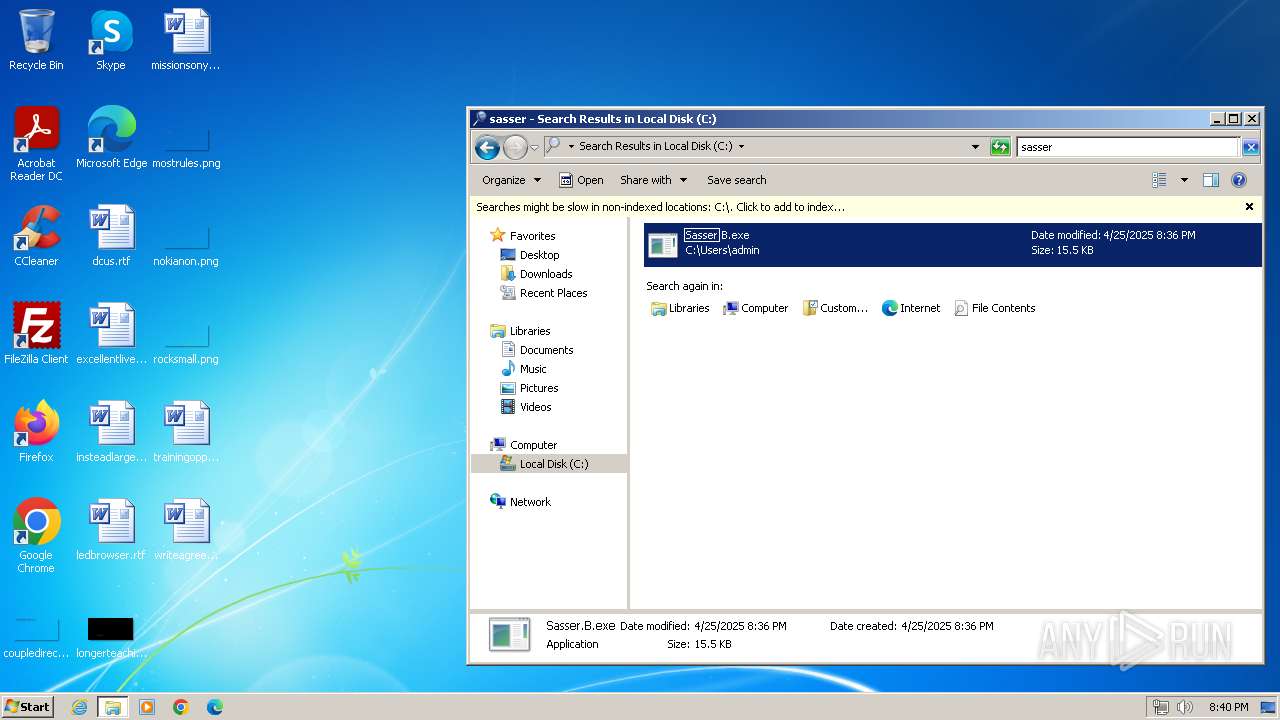
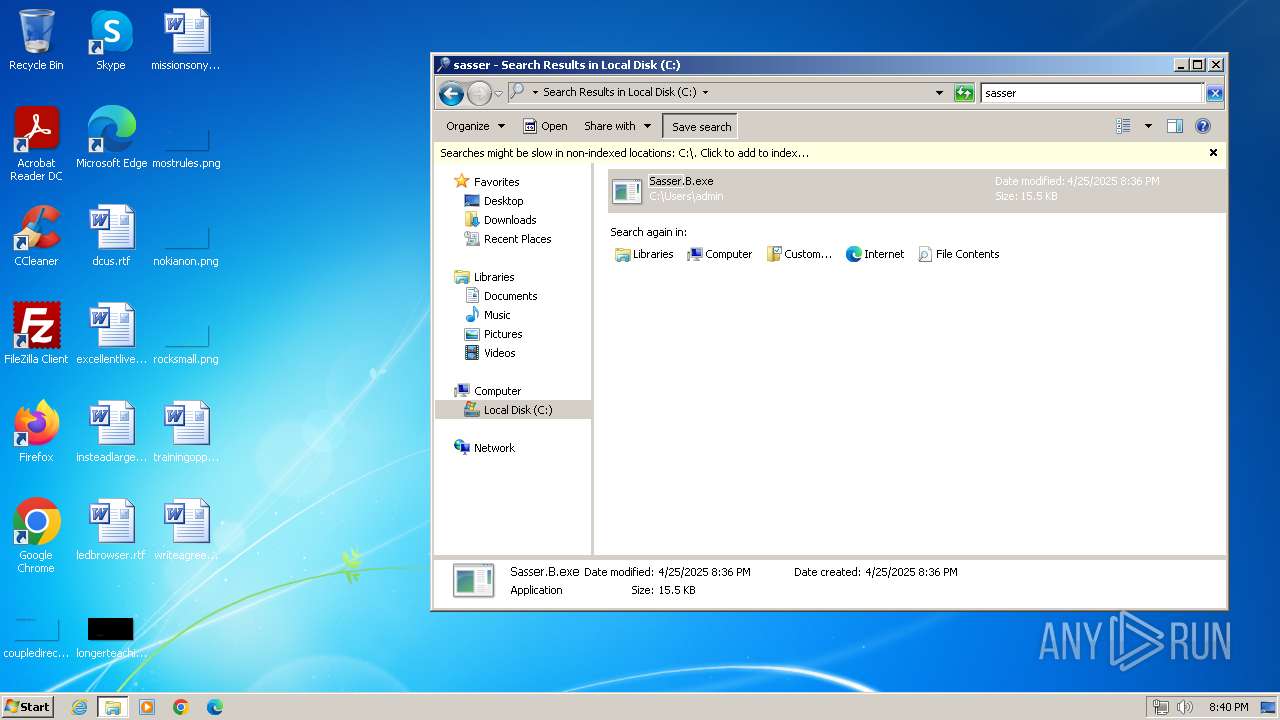
| File name: | Sasser.B.exe |
| Full analysis: | https://app.any.run/tasks/4b5406f7-828a-4a57-95b8-aa26a92f532b |
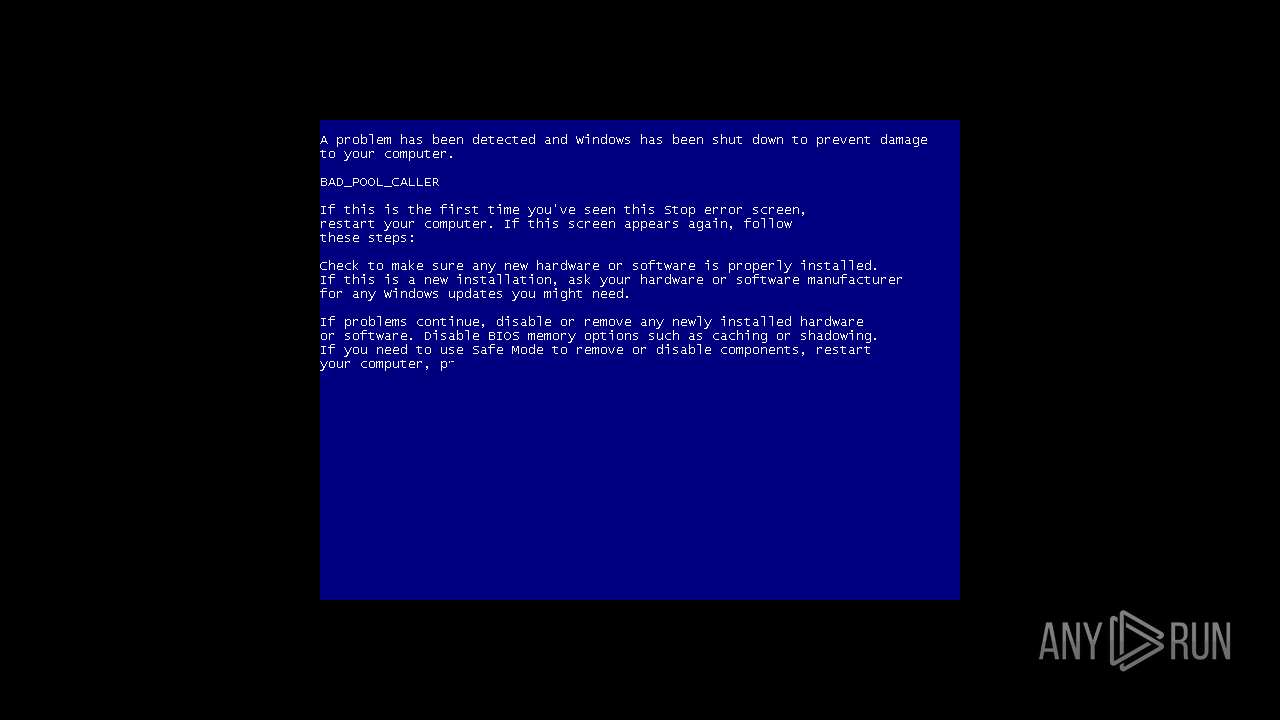
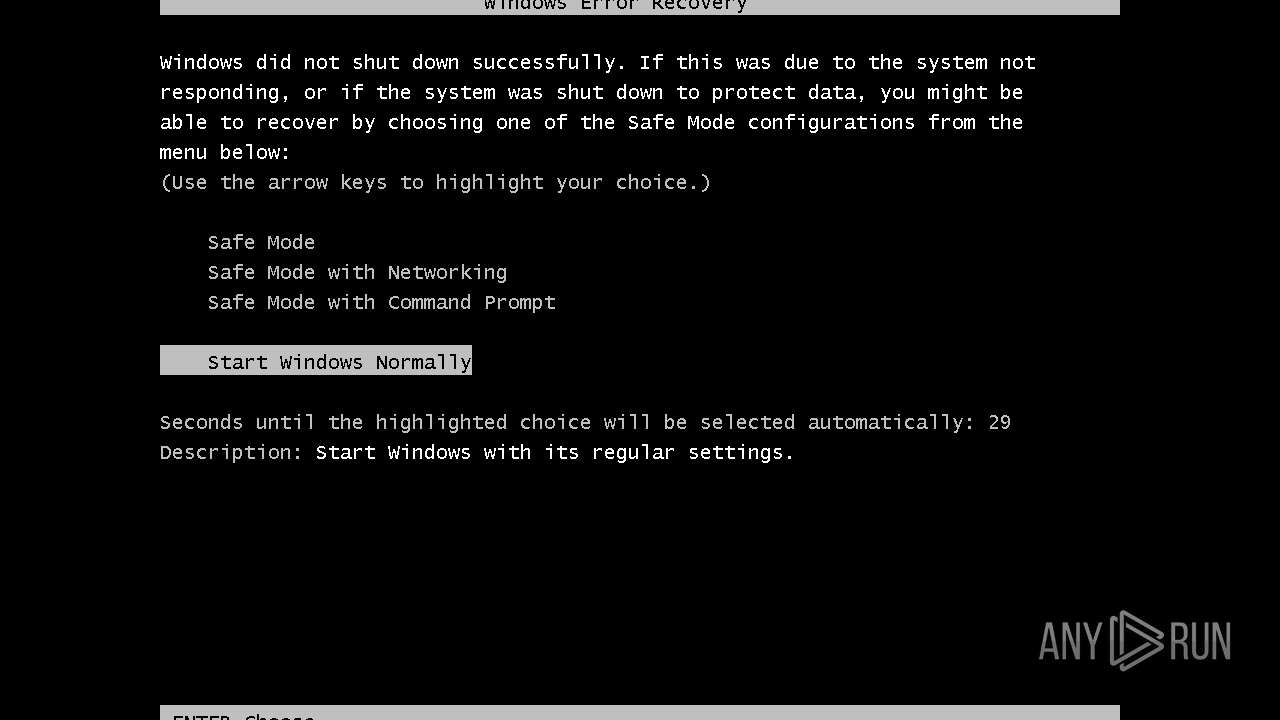
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2025, 19:36:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 2 sections |
| MD5: | 1A2C0E6130850F8FD9B9B5309413CD00 |
| SHA1: | D0DE44BCF3CA6553307C77DA8699DBC9B5E9D56A |
| SHA256: | 09398D3F5CC102F7D932B765036E1AC1FF5DC27405D7357B81EAF48CA8EC71B8 |
| SSDEEP: | 192:5LQQpqTnBW/OyBooSpbBdbnr9w/lhUYobpCtqOjVzg9ZsAXb1r5FSfhVWdzP5eOh:yQqTBNNrbSHhqONghZrGG5LWadp |
MALICIOUS
Changes the autorun value in the registry
- Sasser.B.exe (PID: 2848)
Attempt to connect to SMB server
- Sasser.B.exe (PID: 2848)
- Sasser.B.exe (PID: 3768)
Attempting to scan the network
- Sasser.B.exe (PID: 2848)
- Sasser.B.exe (PID: 3768)
SMBSCAN has been detected (SURICATA)
- Sasser.B.exe (PID: 2848)
- Sasser.B.exe (PID: 3768)
SUSPICIOUS
Application launched itself
- Sasser.B.exe (PID: 2848)
- WerFault.exe (PID: 2176)
The process executes via Task Scheduler
- sipnotify.exe (PID: 404)
- ctfmon.exe (PID: 1960)
Potential Corporate Privacy Violation
- Sasser.B.exe (PID: 2848)
- Sasser.B.exe (PID: 3768)
Reads the Internet Settings
- runonce.exe (PID: 2152)
- sipnotify.exe (PID: 404)
INFO
Checks supported languages
- Sasser.B.exe (PID: 2848)
- Sasser.B.exe (PID: 2844)
- IMEKLMG.EXE (PID: 2260)
- IMEKLMG.EXE (PID: 2272)
Reads the computer name
- Sasser.B.exe (PID: 2844)
- Sasser.B.exe (PID: 2848)
- IMEKLMG.EXE (PID: 2260)
- IMEKLMG.EXE (PID: 2272)
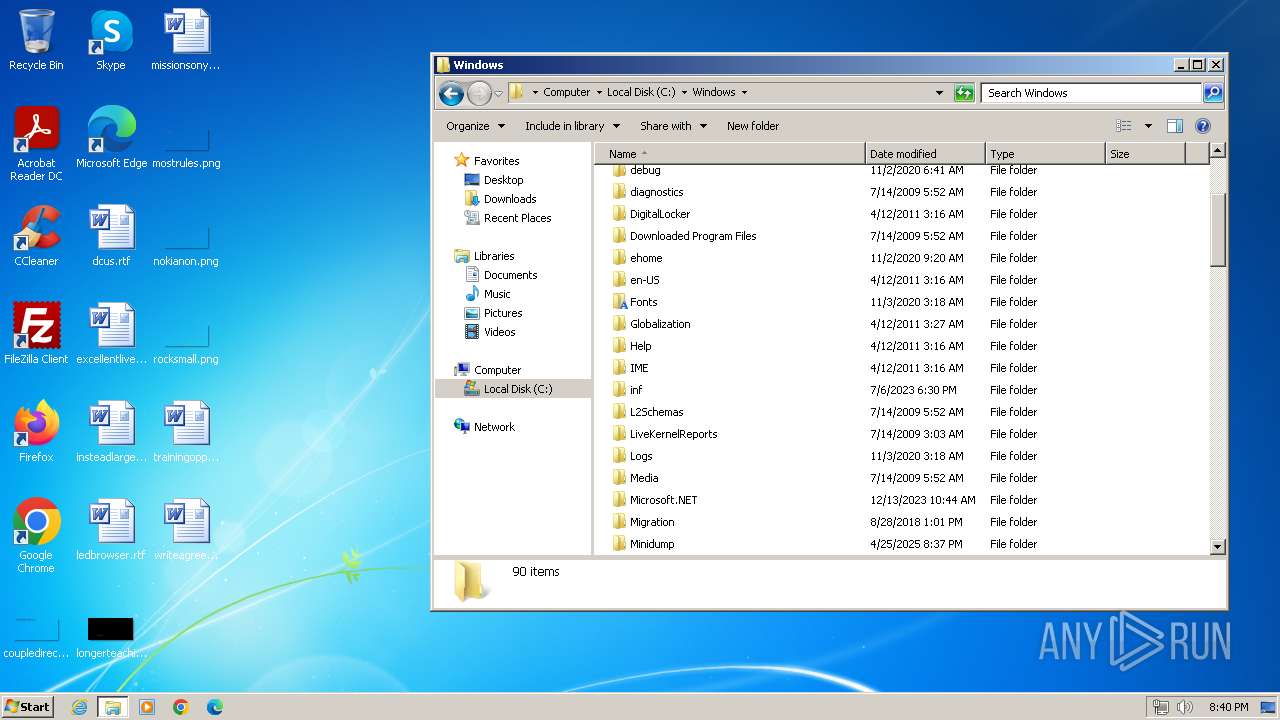
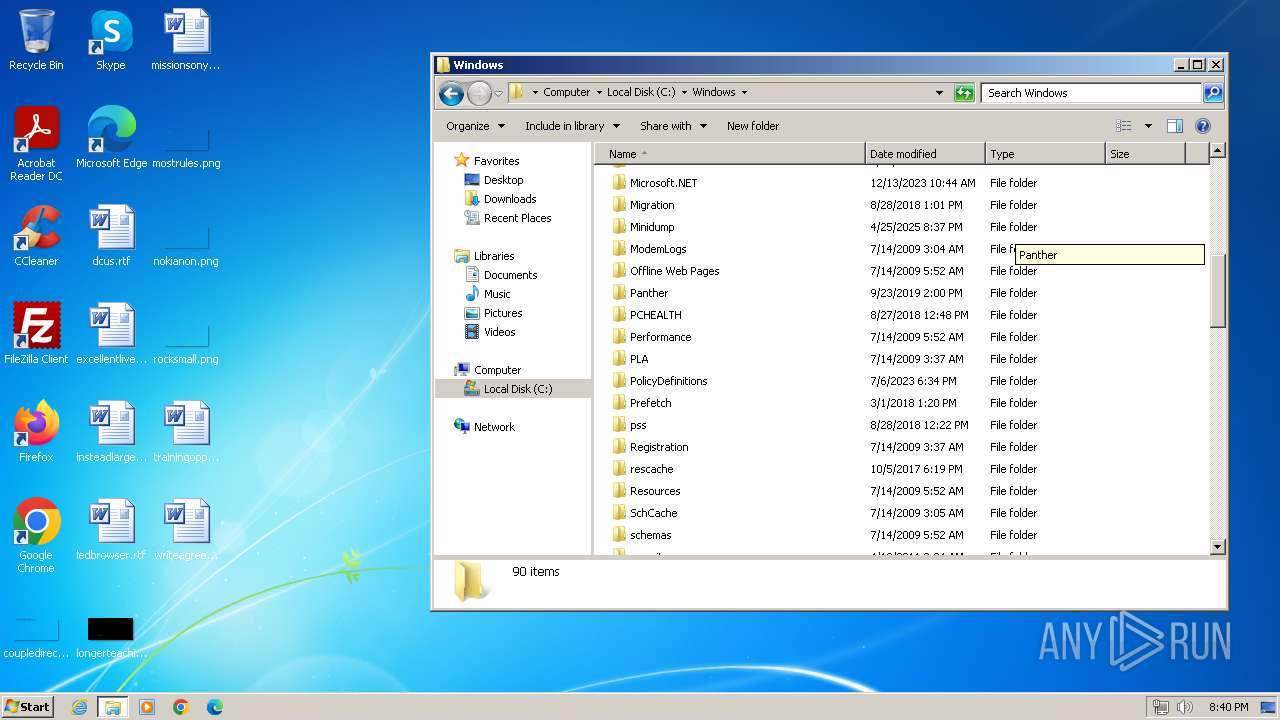
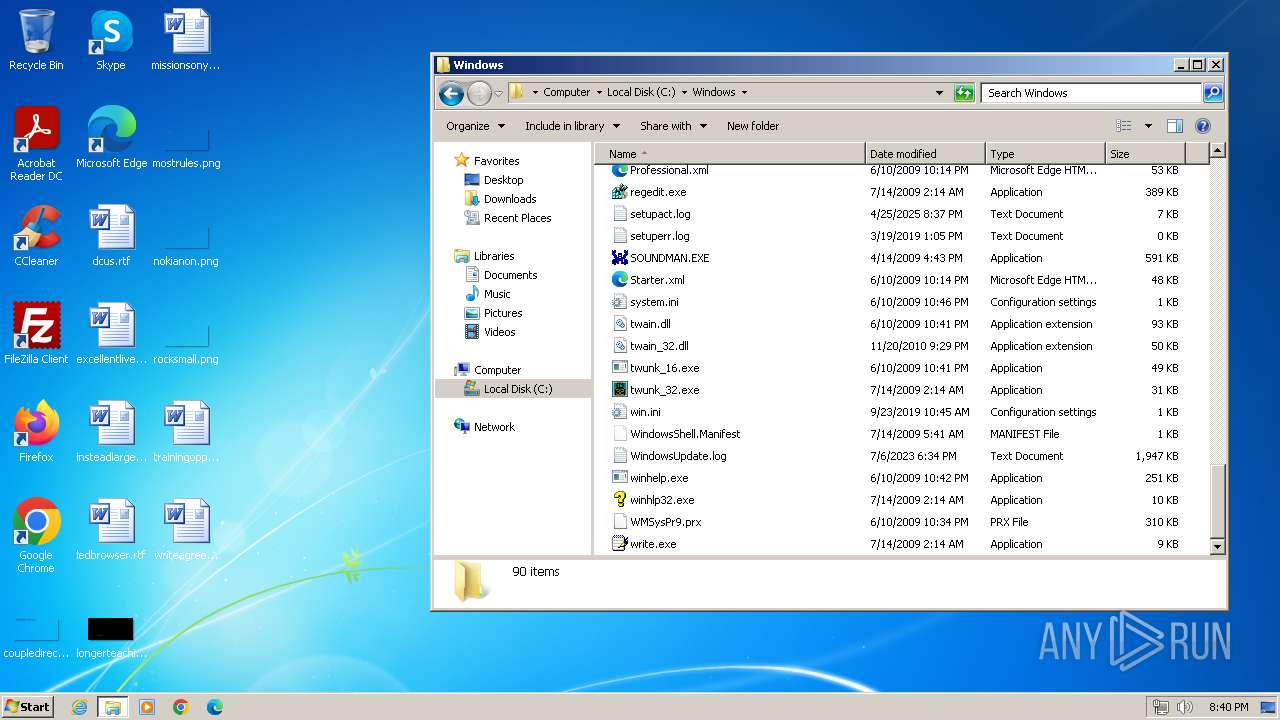
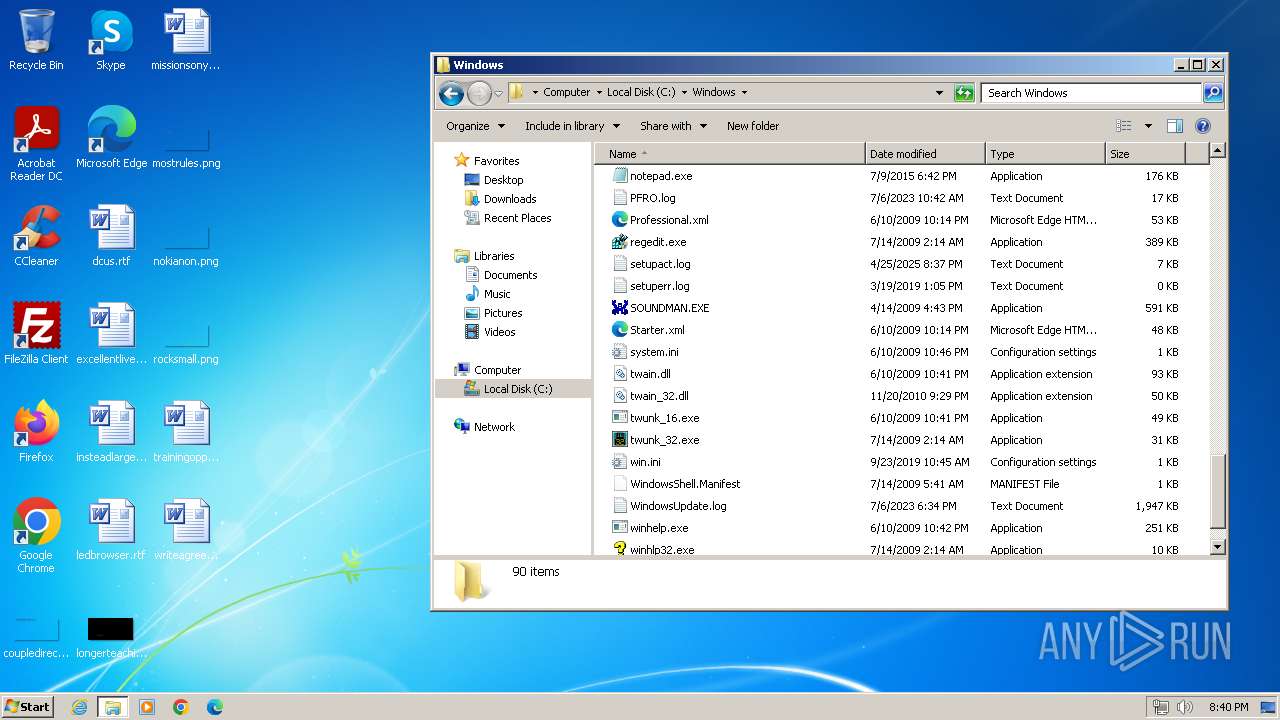
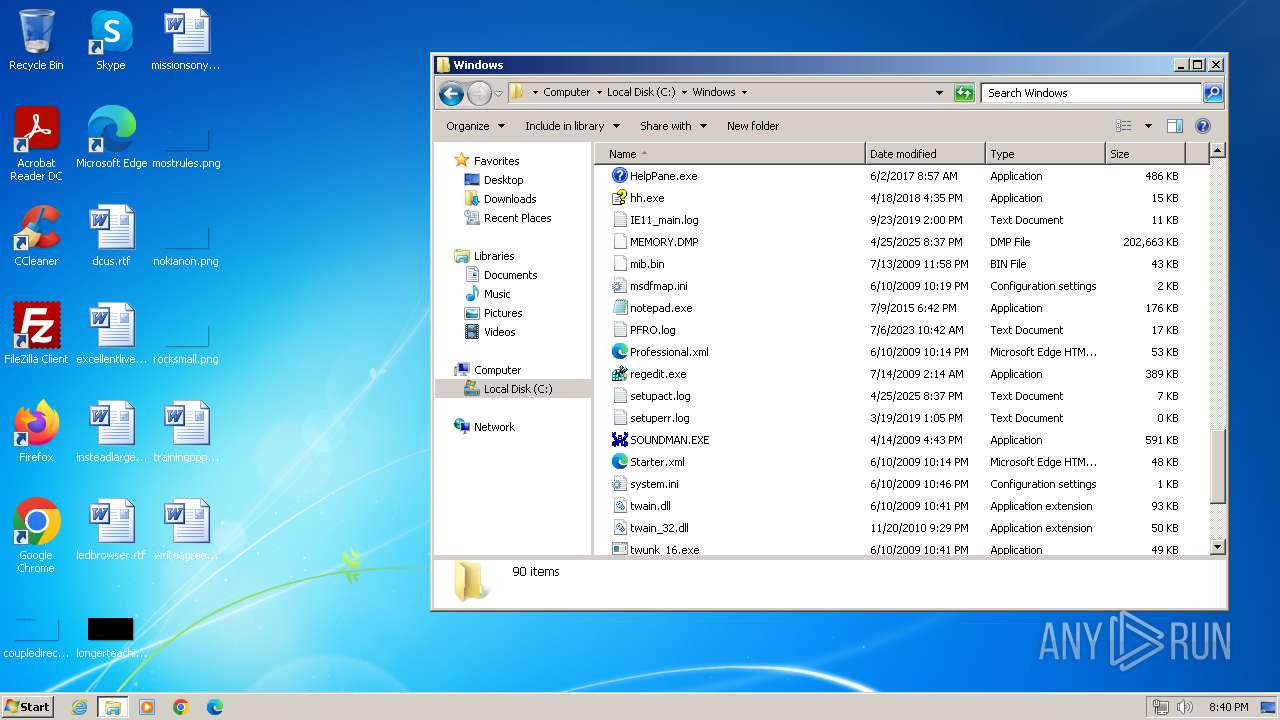
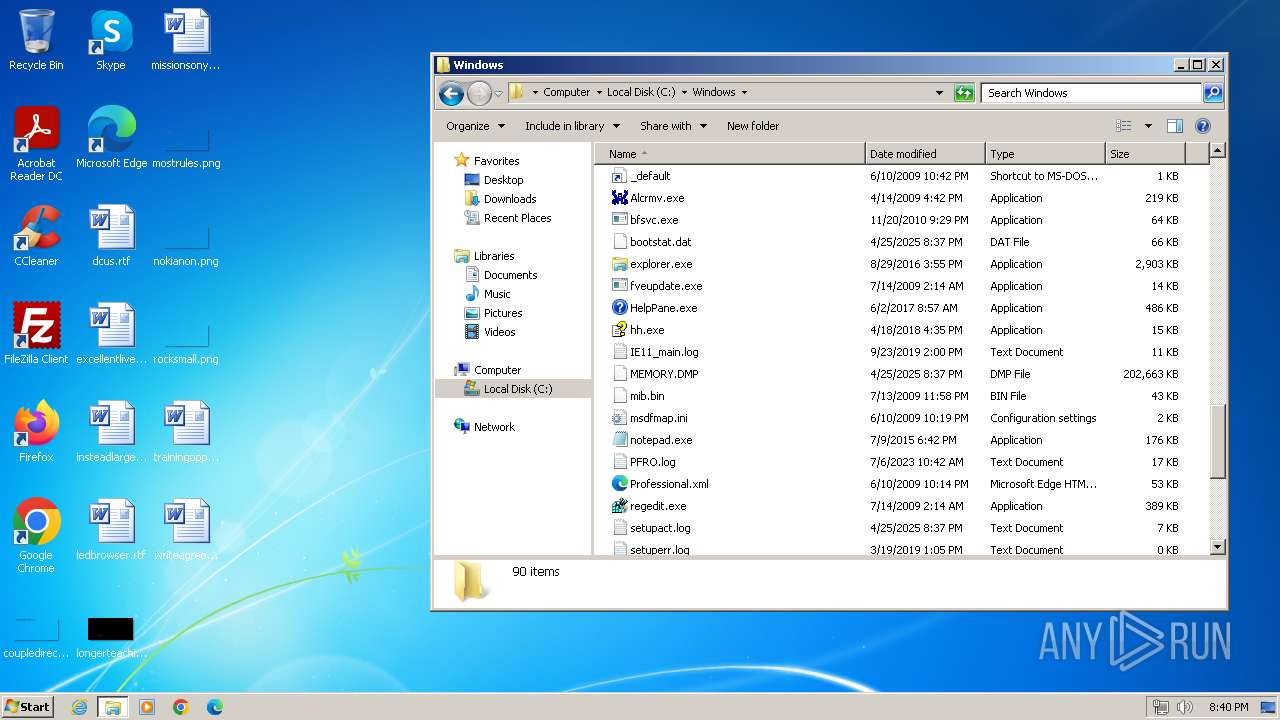
Failed to create an executable file in Windows directory
- Sasser.B.exe (PID: 2848)
Reads the time zone
- runonce.exe (PID: 2152)
Manual execution by a user
- runonce.exe (PID: 2152)
- IMEKLMG.EXE (PID: 2260)
- IMEKLMG.EXE (PID: 2272)
- explorer.exe (PID: 2740)
- Sasser.B.exe (PID: 3768)
Reads security settings of Internet Explorer
- runonce.exe (PID: 2152)
Create files in a temporary directory
- WerFault.exe (PID: 2184)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2272)
- IMEKLMG.EXE (PID: 2260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:05:01 11:39:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 15872 |
| InitializedDataSize: | 8704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x283e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
91
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1960 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | runonce.exe /Explorer | C:\Windows\System32\runonce.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Windows\System32\WerFault.exe" -k -rq | C:\Windows\System32\WerFault.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | C:\Windows\System32\WerFault.exe -k -q | C:\Windows\System32\WerFault.exe | — | WerFault.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2740 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | C:\Users\admin\Sasser.B.exe 127.124.239.122 | C:\Users\admin\Sasser.B.exe | — | Sasser.B.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\Sasser.B.exe" | C:\Users\admin\Sasser.B.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 118
Read events
4 097
Write events
14
Delete events
7
Modification events
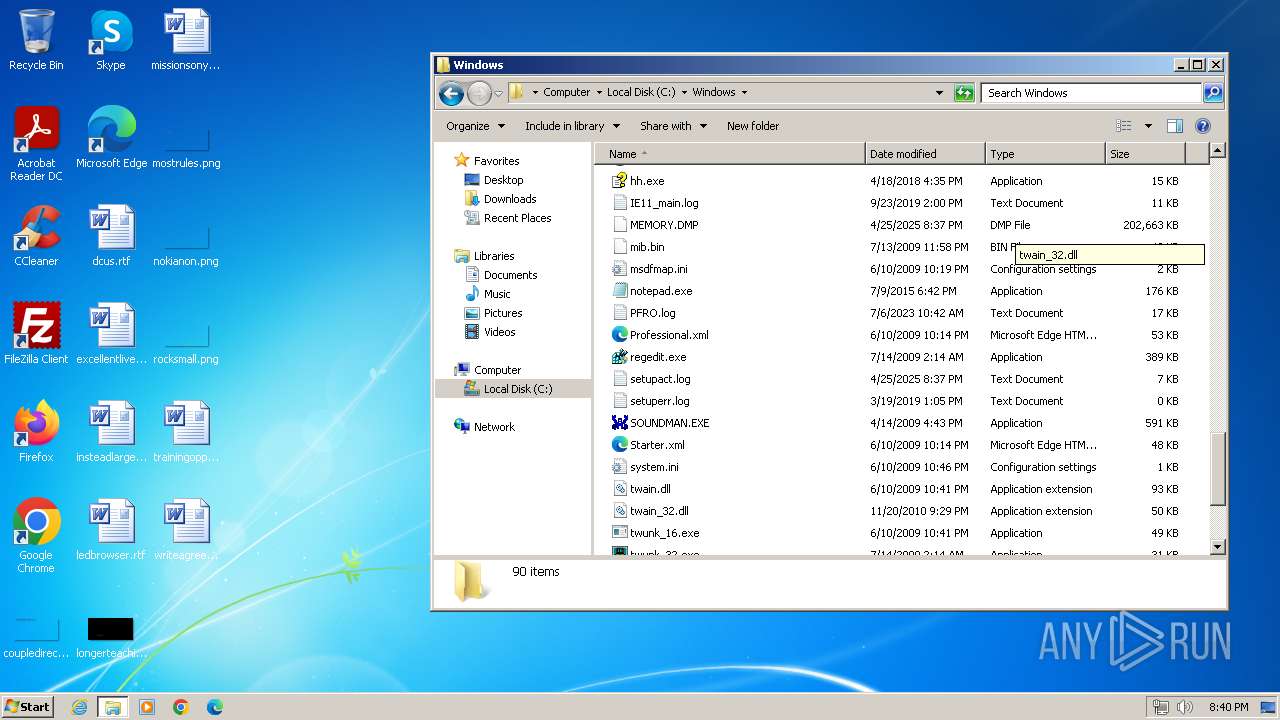
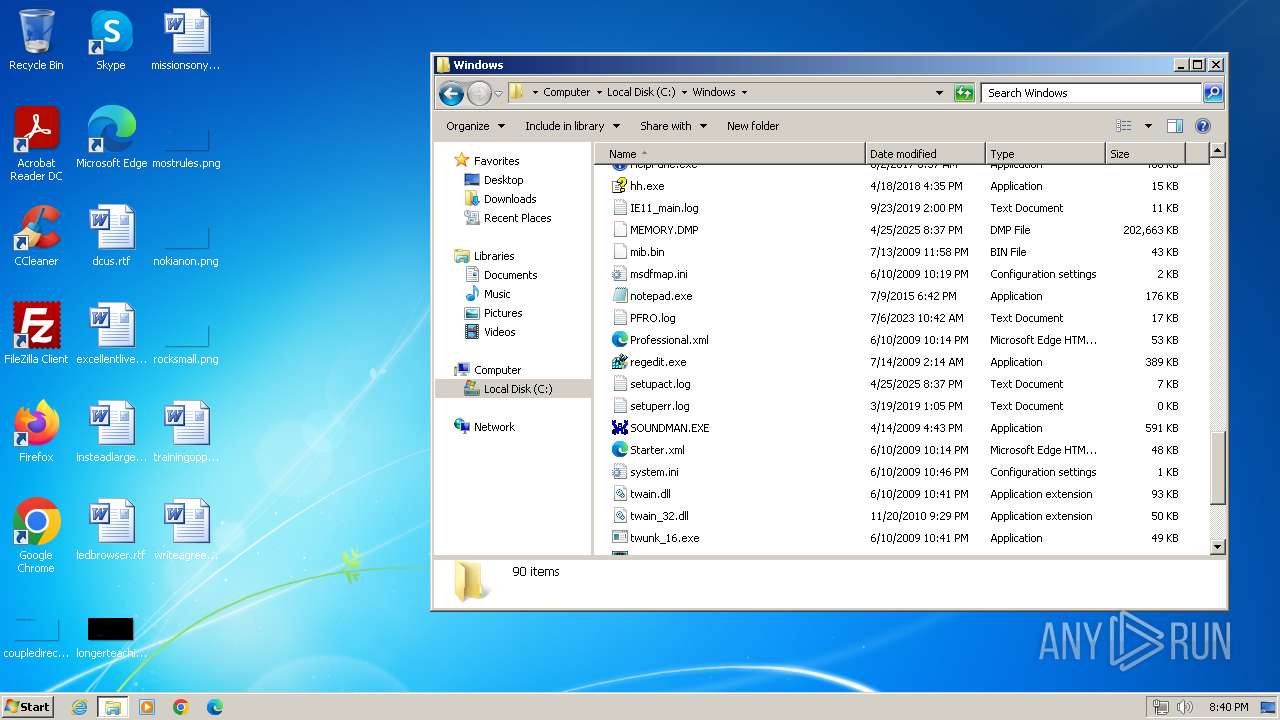
| (PID) Process: | (2848) Sasser.B.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | avserve2.exe |
Value: C:\Windows\avserve2.exe | |||
| (PID) Process: | (2152) runonce.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | *WerKernelReporting |
Value: %SYSTEMROOT%\SYSTEM32\WerFault.exe -k -rq | |||
| (PID) Process: | (1960) ctfmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | internat.exe |
Value: | |||
| (PID) Process: | (2184) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\KernelFaults\Queue |
| Operation: | delete value | Name: | C:\Windows\Minidump\042525-9406-01.dmp |
Value: �蓆똙Ǜ | |||
| (PID) Process: | (2272) IMEKLMG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\IMEKR\14.0 |
| Operation: | write | Name: | SetPreload |
Value: 1 | |||
| (PID) Process: | (2152) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2152) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2152) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2152) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2184) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\KernelFaults\Queue |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
9
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\Kernel_0_0_cab_08888e17\Report.wer | — | |
MD5:— | SHA256:— | |||
| 404 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\script.js | text | |
MD5:A2682382967C351F7ED21762F9E5DE9E | SHA256:36B1D26F1EC69685648C0528C2FCE95A3C2DBECF828CDFA4A8B4239A15B644A2 | |||
| 404 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\styles.css | text | |
MD5:3383EEF350240253D7C2C2564381B3CB | SHA256:85443493D86D6D7FB0E07BC9705DFC9C858086FBA1B0E508092AB328D5F145E8 | |||
| 2184 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER8D5B.tmp.cab | compressed | |
MD5:B52E512F33DF3D8C66BA49A9FA377D02 | SHA256:8930CC88F9B0E86FA34A0117713379A00EA51D74522C0CA800D28CE843C5C8CF | |||
| 2184 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER8D5C.tmp.cab.tmp | binary | |
MD5:FA2BB3AB19573AB5F774B842495EF5E2 | SHA256:DC63FB007785D76398F7D031C72AC9637FA999994CB7B569394AC375396F2D2C | |||
| 2184 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER8D5E.tmp.cab.tmp | binary | |
MD5:04AF6204931C65997FE4B9D705AB6336 | SHA256:75DFDD0FBE1E7E64384D95997BDF3BC7540AAA4E85E4A095B58531BFA8865E87 | |||
| 2184 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER8D60.tmp.cab.tmp | binary | |
MD5:8BA028678E2B812B0A124ADC1BAB3ECE | SHA256:9C43C0DF390C39D64F1E5E8E9E032029A634F0B5CE12B24DE2D20A38BF8A0CEC | |||
| 404 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\default.cab | compressed | |
MD5:340674F6A3D1562E28A011EC11E40D83 | SHA256:259880E2346D986ABEED46AA9C2917C53E969AAE6927F2CA0A2AD0967736DF98 | |||
| 404 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\metadata.json | binary | |
MD5:253EDC8EC7674BD78293FF3B21866074 | SHA256:51C3A033F0160A30C1773F1E5A9CD01AB018B151EDA1BB64D0226B2437106A56 | |||
| 404 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\main.jpg | image | |
MD5:C8BCC2041232DA45C1367F1FEED51370 | SHA256:C0EC6771F923E7B85F6E2E7AA58D6BA51D322E78F53CEE8108DBBFD352BE7B25 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
673
DNS requests
5
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
404 | sipnotify.exe | HEAD | 503 | 23.207.104.5:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133900870716250000 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
2848 | Sasser.B.exe | 57.220.243.203:445 | — | — | IE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2848 | Sasser.B.exe | 91.149.113.2:445 | — | T2 Mobile LLC | RU | unknown |
2848 | Sasser.B.exe | 35.203.98.90:445 | — | GOOGLE-CLOUD-PLATFORM | CA | unknown |
2848 | Sasser.B.exe | 192.168.220.135:445 | — | — | — | unknown |
2848 | Sasser.B.exe | 192.236.129.214:445 | — | HOSTWINDS | US | unknown |
2848 | Sasser.B.exe | 192.168.114.170:445 | — | — | — | unknown |
2848 | Sasser.B.exe | 169.161.212.50:445 | — | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2848 | Sasser.B.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |
2848 | Sasser.B.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
2848 | Sasser.B.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
3768 | Sasser.B.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |
3768 | Sasser.B.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
3768 | Sasser.B.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |
3768 | Sasser.B.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers inside a home network |
3768 | Sasser.B.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempting to scan SMB servers outside a home network |