| download: | home |
| Full analysis: | https://app.any.run/tasks/203e3ca0-f363-4b29-b857-c1f2aaf505d9 |
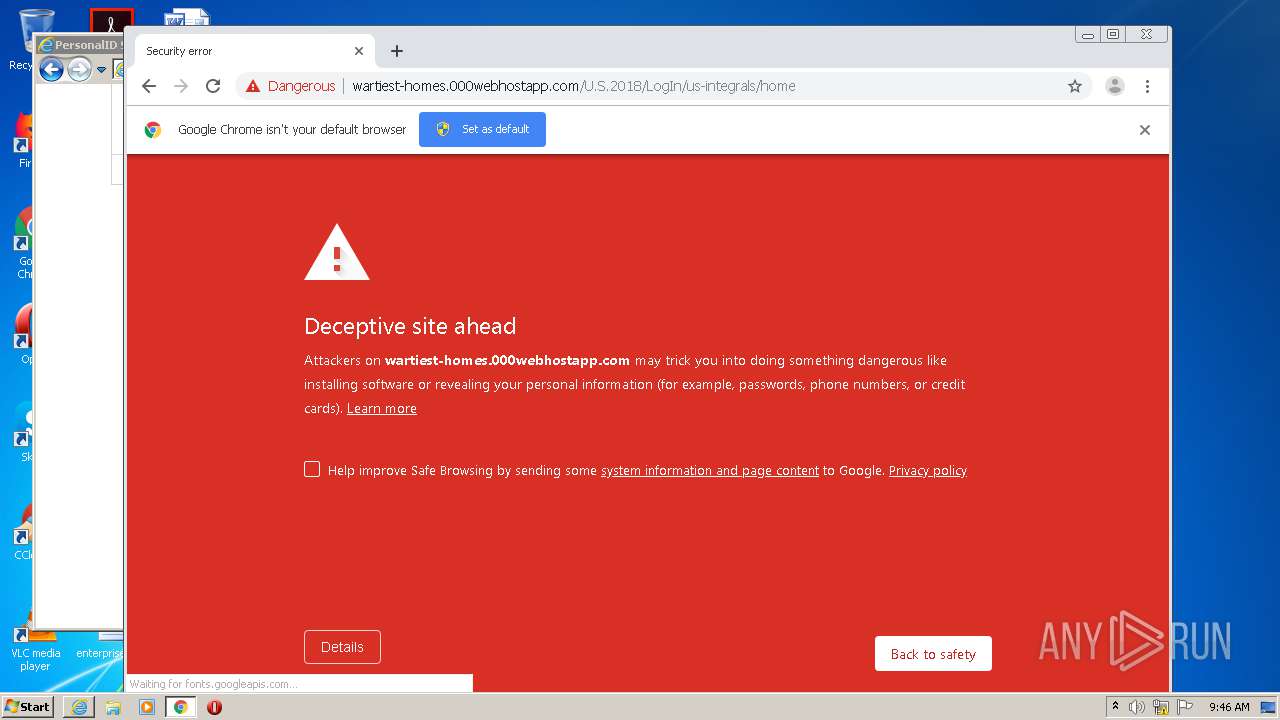
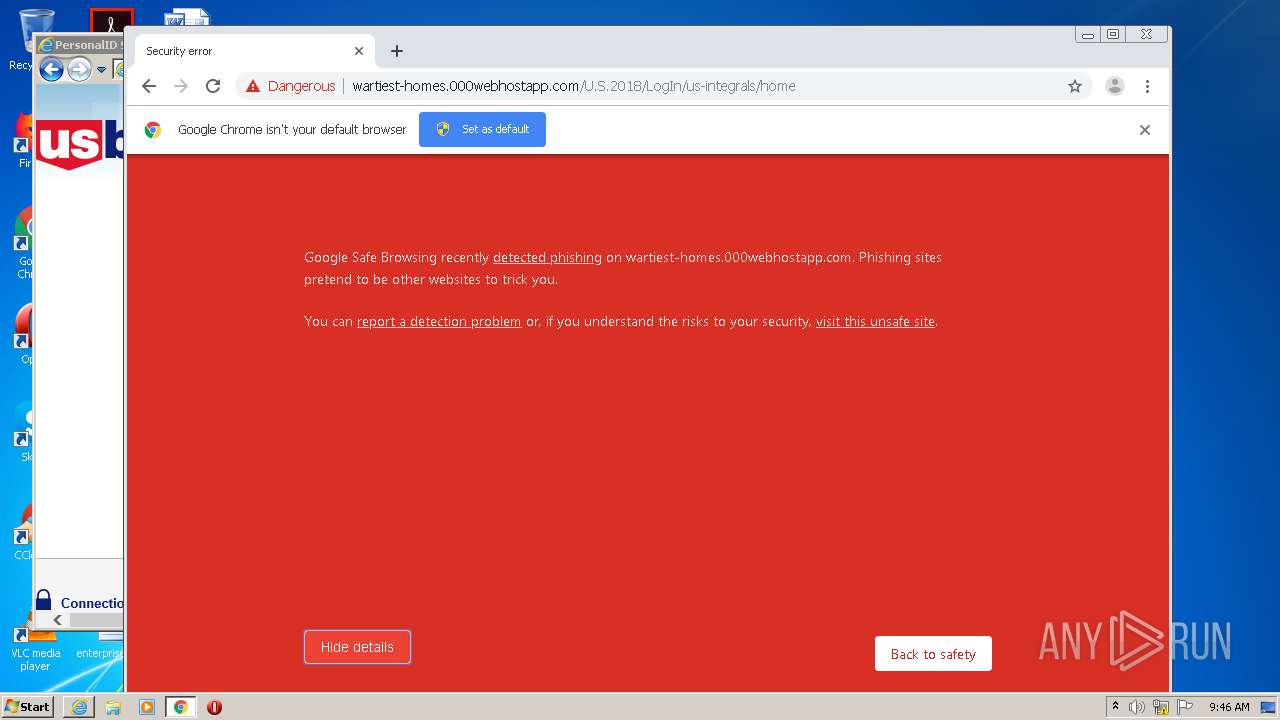
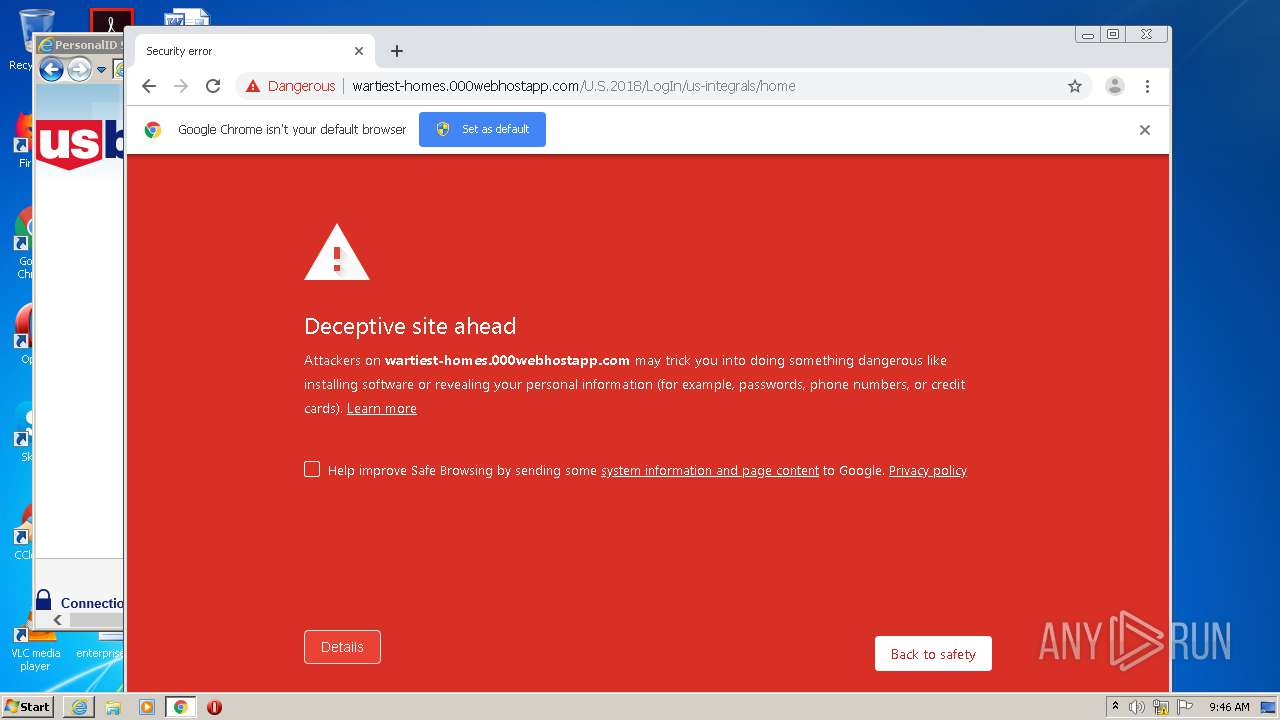
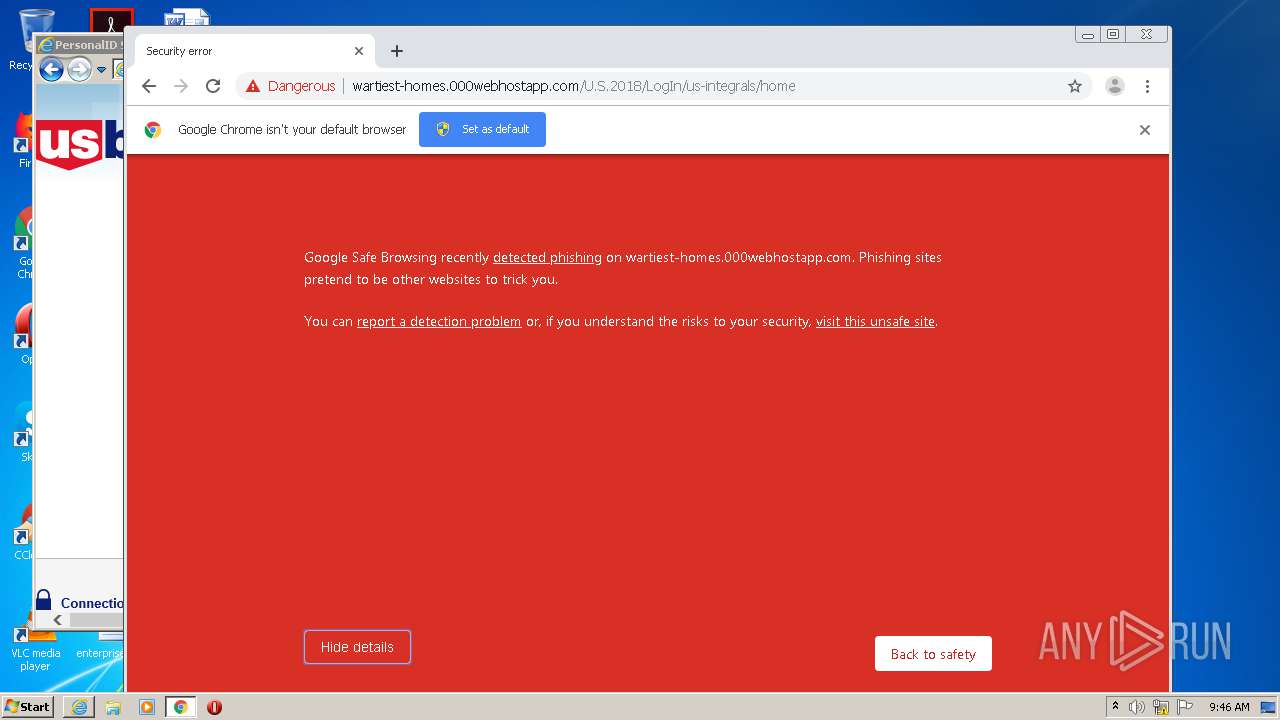
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 08:45:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | A7A359A3267C347767BD8035A0658671 |
| SHA1: | A658465400210D10D75A8A78C80EF3E2649325A6 |
| SHA256: | 093764FA1E62570A1019033F95BA142748FE317C79BD1320A0D4F97B44C51CFF |
| SSDEEP: | 192:w23N0NWcMztS015kc1T2cjugR9aPjMPbPcIhYO6gvufh6wWpZnStOrX:w23CINtSylScSo9arMDEIhYfgmZ8AOrX |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3448)
Changes settings of System certificates
- iexplore.exe (PID: 916)
- iexplore.exe (PID: 3388)
Adds / modifies Windows certificates
- iexplore.exe (PID: 916)
- iexplore.exe (PID: 3388)
Reads settings of System Certificates
- iexplore.exe (PID: 916)
- iexplore.exe (PID: 3388)
- chrome.exe (PID: 3340)
Application launched itself
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 916)
- chrome.exe (PID: 444)
Changes internet zones settings
- iexplore.exe (PID: 3388)
Creates files in the user directory
- iexplore.exe (PID: 3448)
Reads internet explorer settings
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 916)
Reads the hosts file
- chrome.exe (PID: 444)
- chrome.exe (PID: 3340)
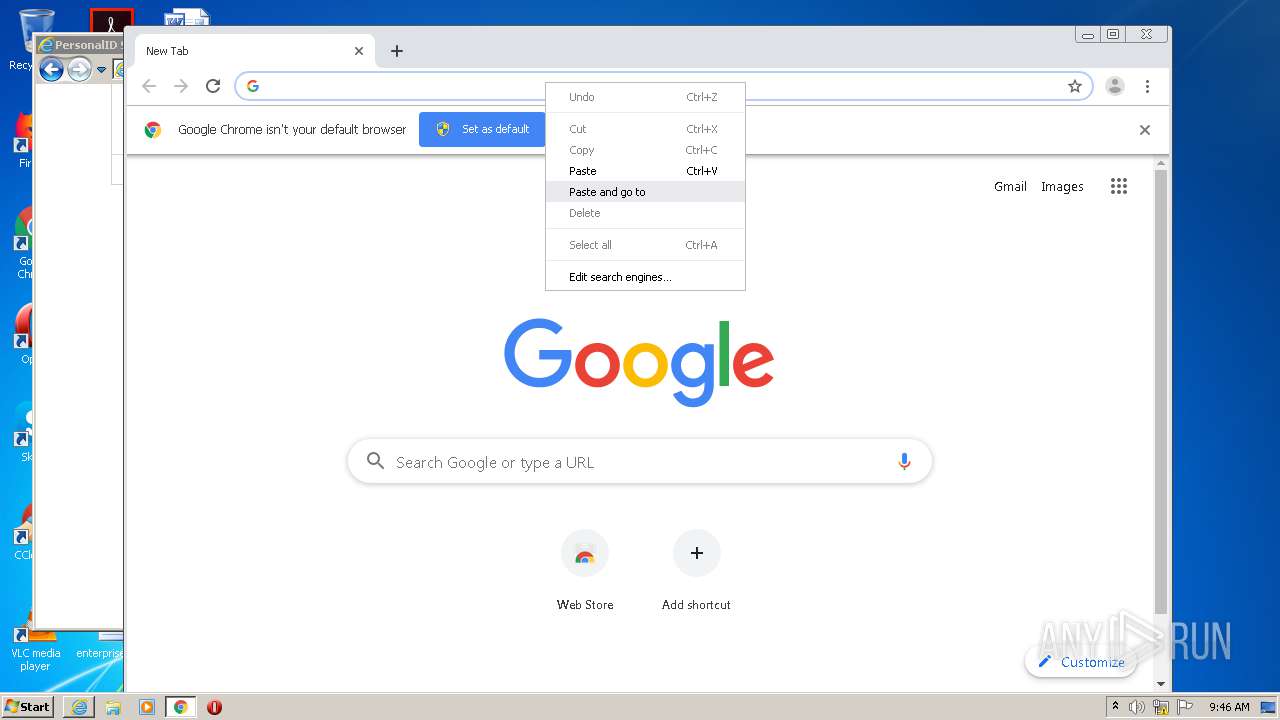
Manual execution by user
- chrome.exe (PID: 444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=UTF-8 |
|---|---|
| CacheControl: | private,no-cache, no-store, must-revalidate |
| Expires: | -1 |
| Pragma: | private,no-cache |
Total processes
58
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3388 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,10926449927433433197,12459359197308450940,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=905751831425795980 --mojo-platform-channel-handle=3292 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,10926449927433433197,12459359197308450940,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18184066658852092746 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,10926449927433433197,12459359197308450940,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11492339311436012595 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,10926449927433433197,12459359197308450940,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16062748743475711963 --mojo-platform-channel-handle=4036 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,10926449927433433197,12459359197308450940,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12676371022110742747 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,10926449927433433197,12459359197308450940,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6302003189179804228 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,10926449927433433197,12459359197308450940,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7897058073945688091 --mojo-platform-channel-handle=3368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,10926449927433433197,12459359197308450940,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14884826269517603585 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 588
Read events
1 373
Write events
208
Delete events
7
Modification events
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 600736228 | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30840582 | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
27
Text files
87
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2BLPY5V1.txt | — | |
MD5:— | SHA256:— | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\CEL6NS54.txt | — | |
MD5:— | SHA256:— | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7445D6-1BC.pma | — | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3237.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar3238.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bde44820-456c-4b29-a801-cfa6f9cc3f14.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_D9817BD5013875AD517DA73475345203 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
52
DNS requests
31
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
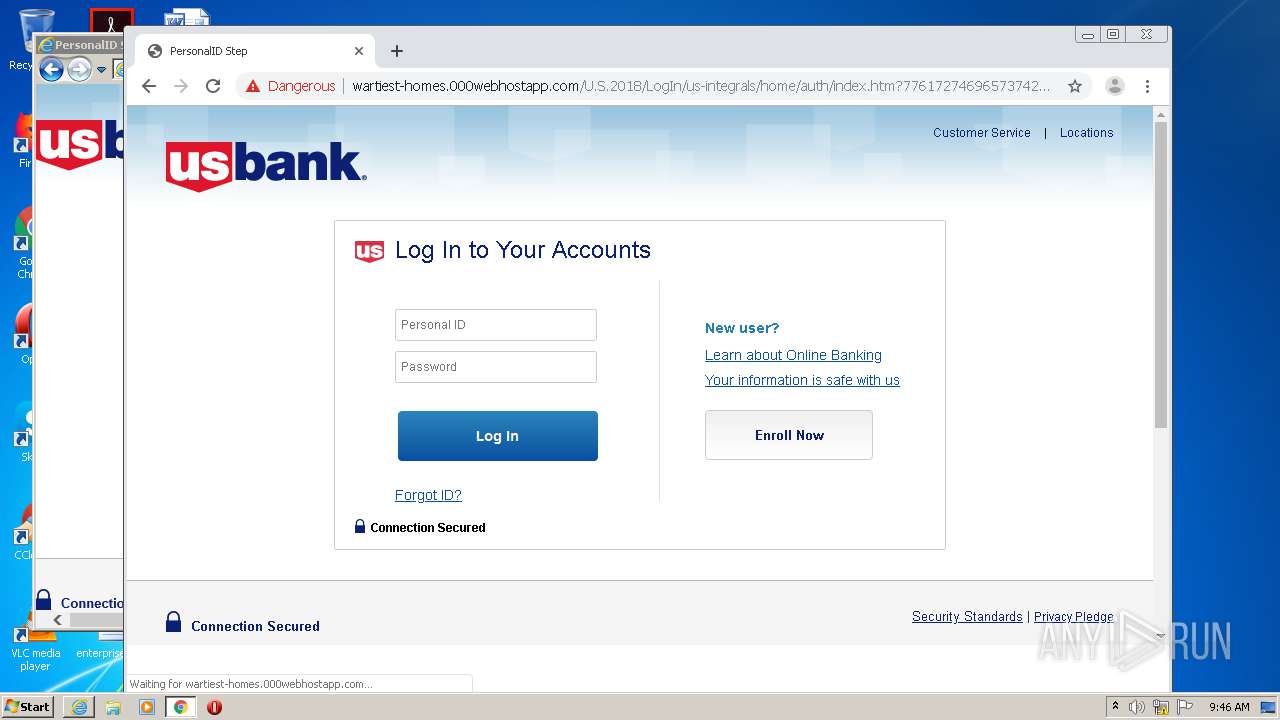
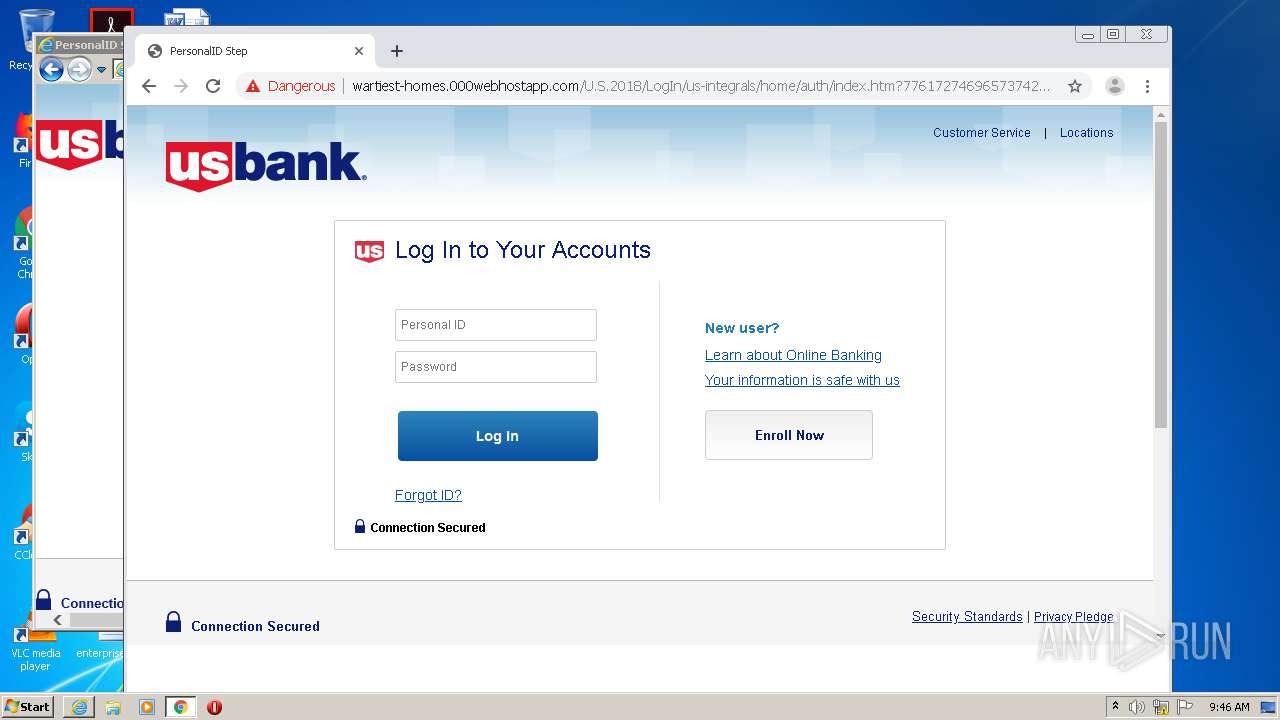
3448 | iexplore.exe | GET | — | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/U.S.2018/LogIn/us-integrals/home | US | — | — | shared |
3448 | iexplore.exe | GET | 302 | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/U.S.2018/LogIn/us-integrals/home/ | US | — | — | shared |
3388 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3448 | iexplore.exe | GET | 404 | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/U.S.2018/LogIn/us-integrals/home/auth/index%5D_files/gen_validatorv4.js | US | html | 3.69 Kb | shared |
3340 | chrome.exe | GET | 301 | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/U.S.2018/LogIn/us-integrals/home | US | html | 281 b | shared |
3448 | iexplore.exe | GET | 200 | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/U.S.2018/LogIn/us-integrals/home/auth/index%5D_files/17.png | US | image | 772 b | shared |
3388 | iexplore.exe | GET | 404 | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/favicon.ico | US | html | 3.69 Kb | shared |
3448 | iexplore.exe | GET | 200 | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/U.S.2018/LogIn/us-integrals/home/auth/index.htm?77617274696573742d686f6d65732e303030776562686f73746170702e636f6d | US | html | 3.25 Kb | shared |
3340 | chrome.exe | GET | 200 | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/U.S.2018/LogIn/us-integrals/home/auth/index.htm?77617274696573742d686f6d65732e303030776562686f73746170702e636f6d | US | html | 3.25 Kb | shared |
3448 | iexplore.exe | GET | 200 | 145.14.145.227:80 | http://wartiest-homes.000webhostapp.com/U.S.2018/LogIn/us-integrals/home/auth/index%5D_files/23.png | US | image | 1.70 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3388 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3448 | iexplore.exe | 13.107.13.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
3388 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3448 | iexplore.exe | 145.14.145.227:80 | wartiest-homes.000webhostapp.com | Hostinger International Limited | US | shared |
3340 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3340 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3340 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3388 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3340 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
wartiest-homes.000webhostapp.com |
| shared |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
3448 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS US Bank Phishing Landing |
1056 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
3340 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS US Bank Phishing Landing |