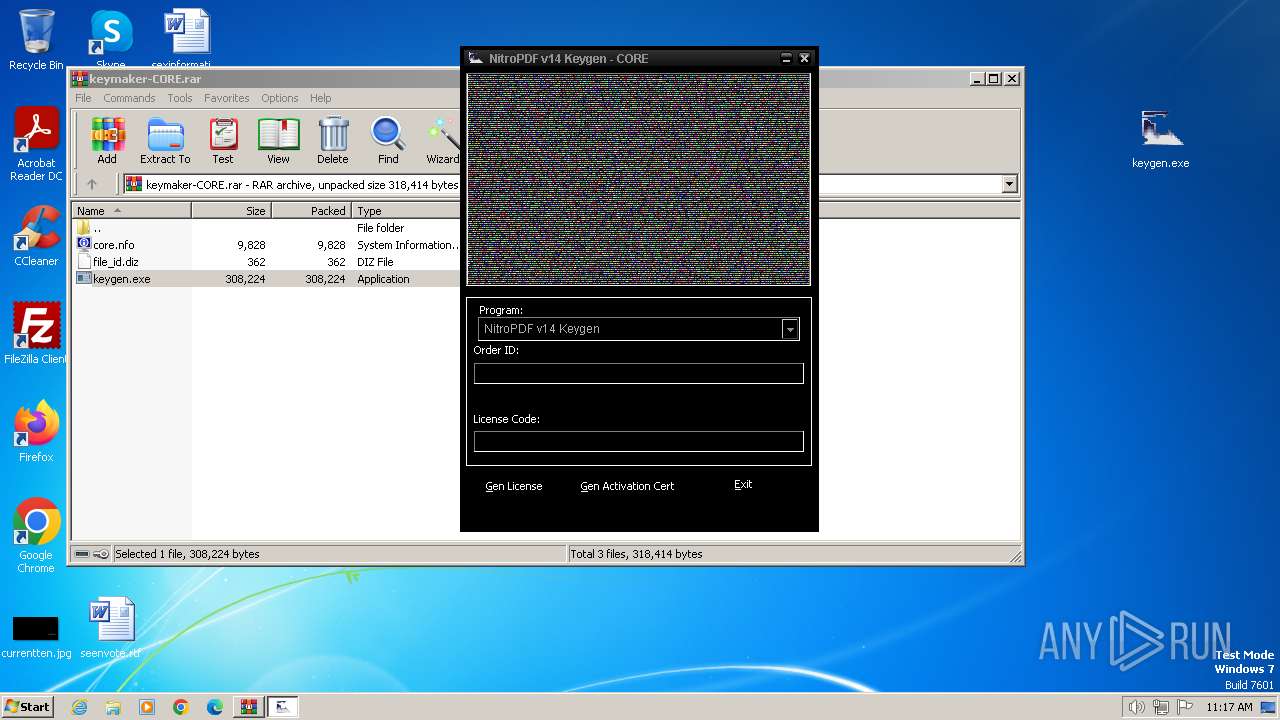
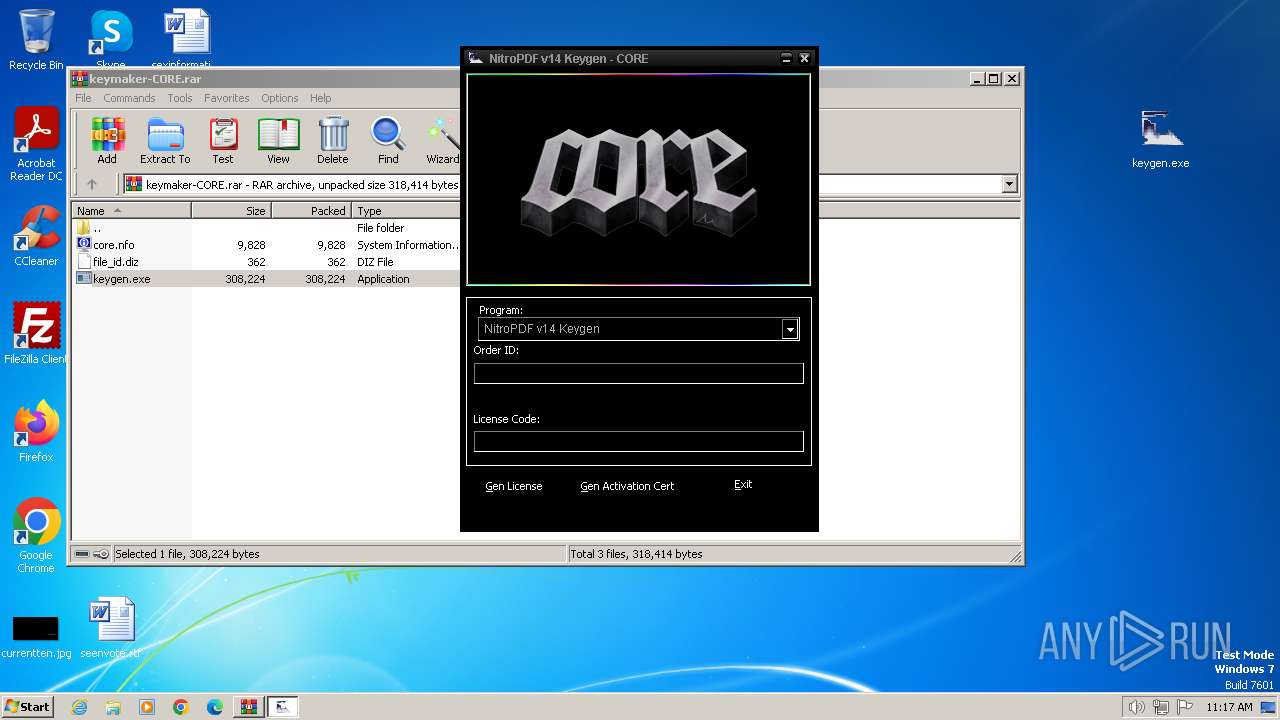
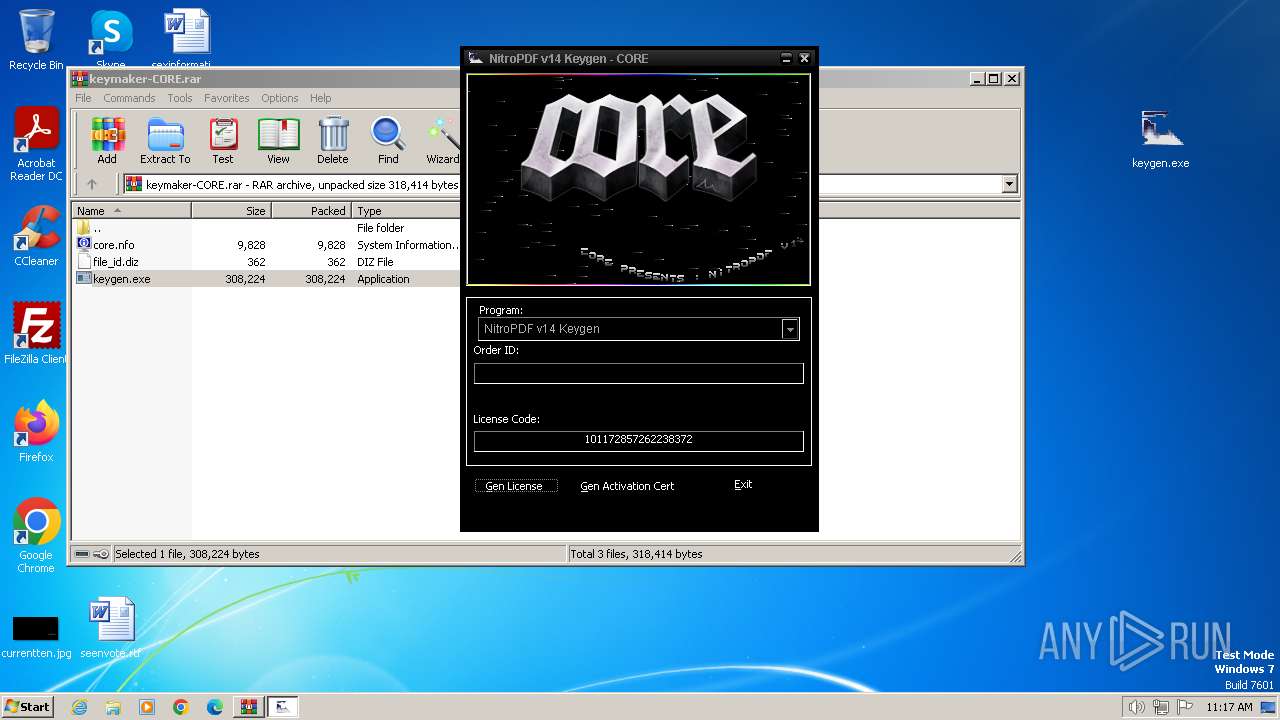
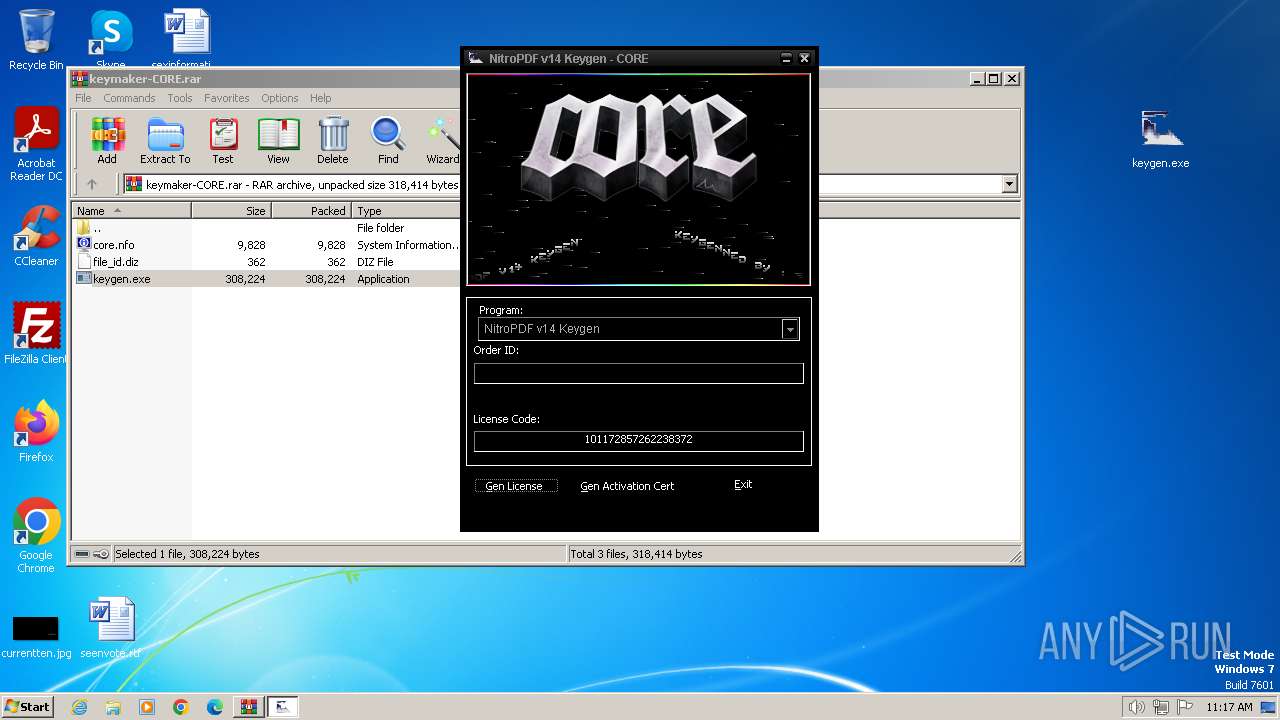
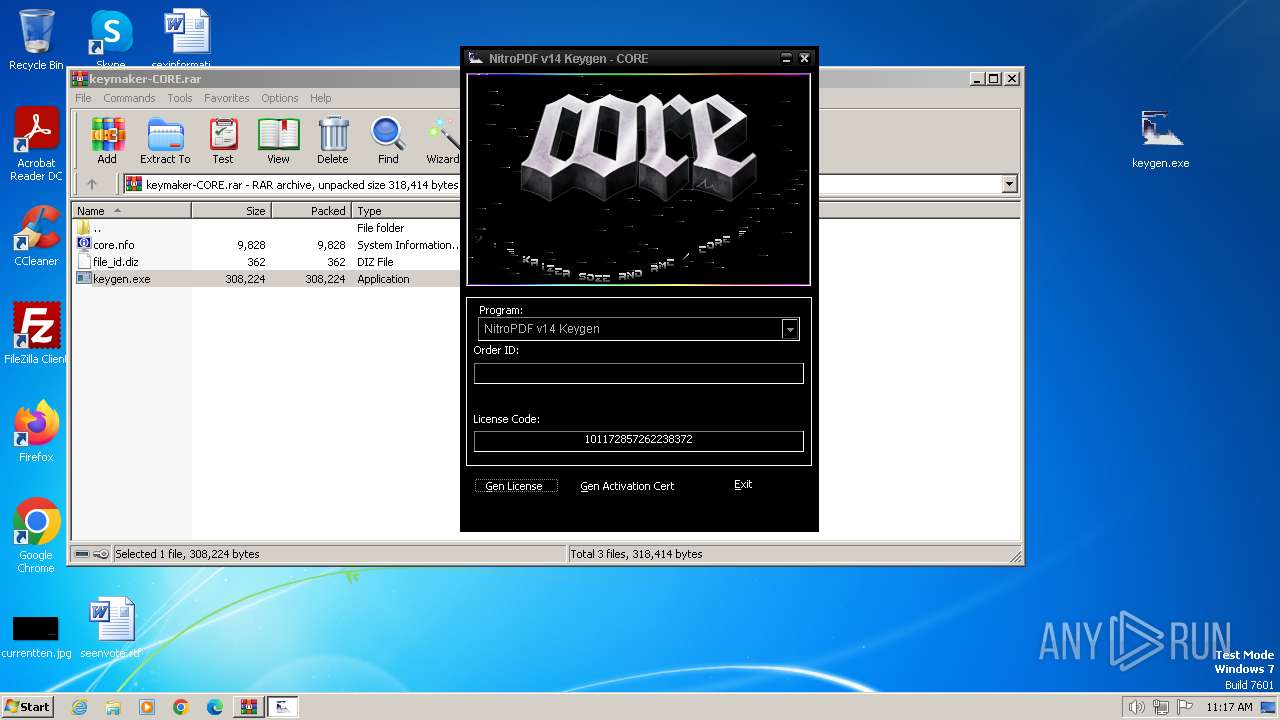
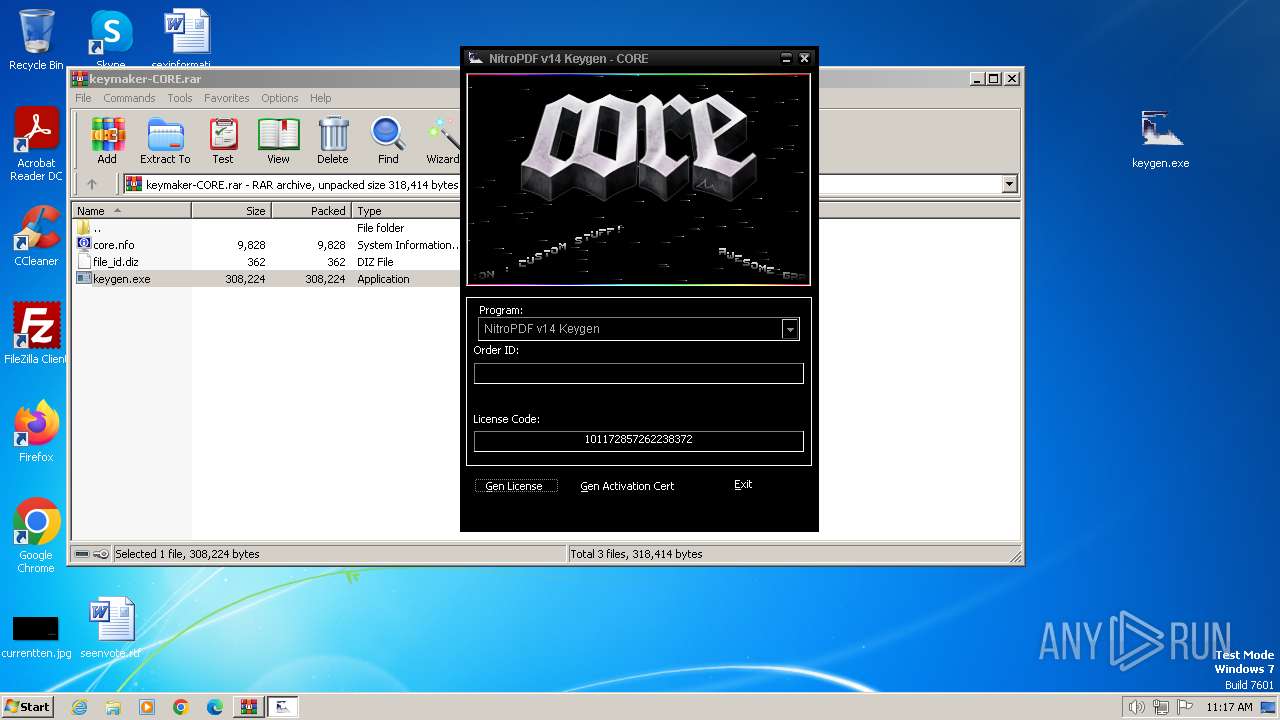
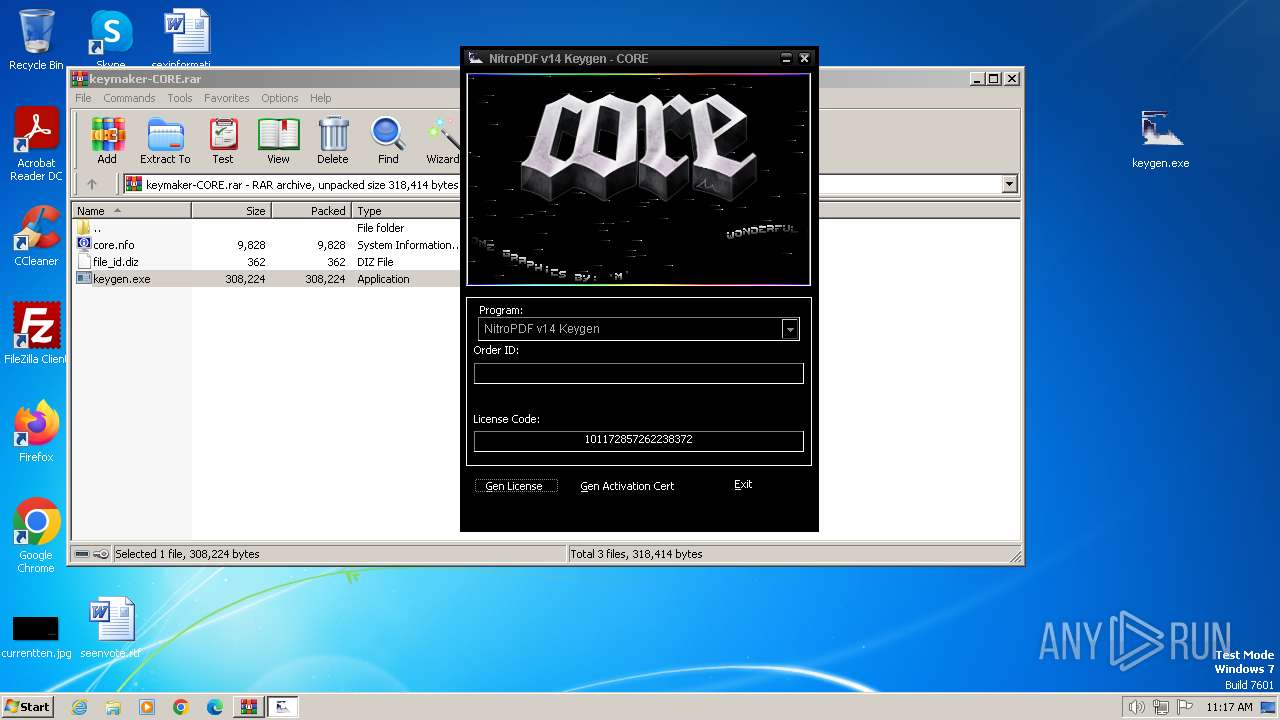
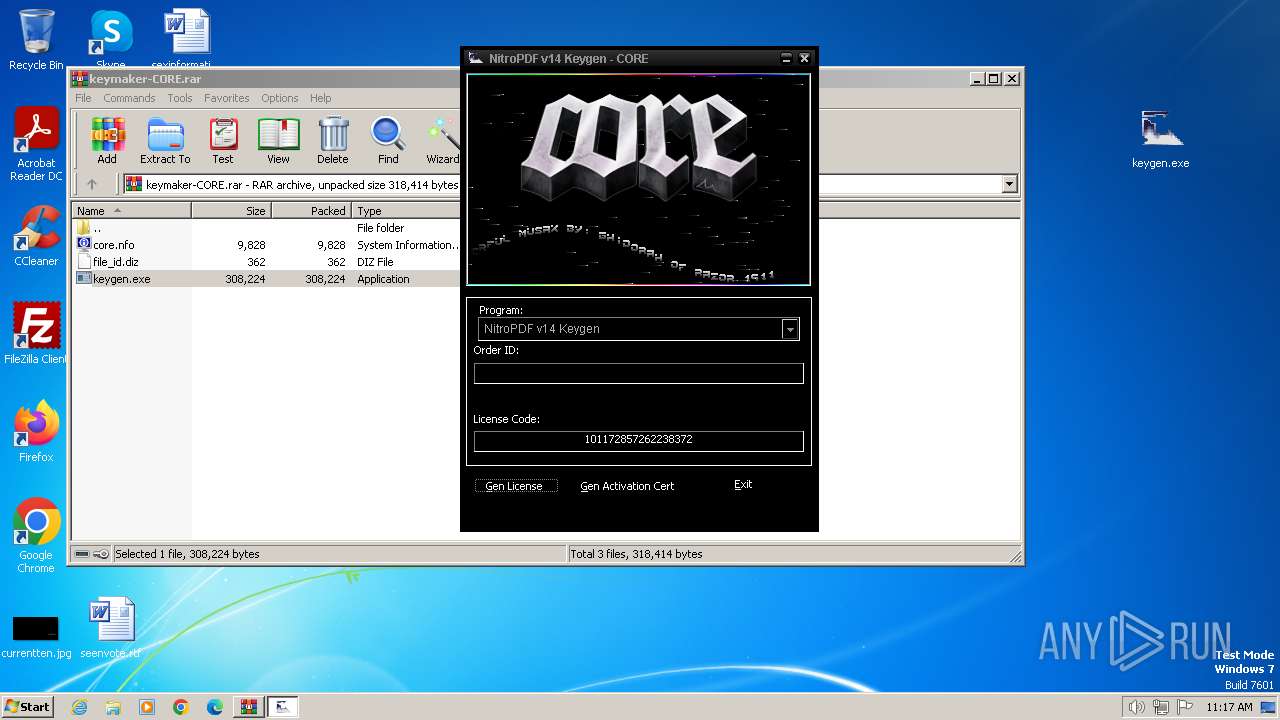
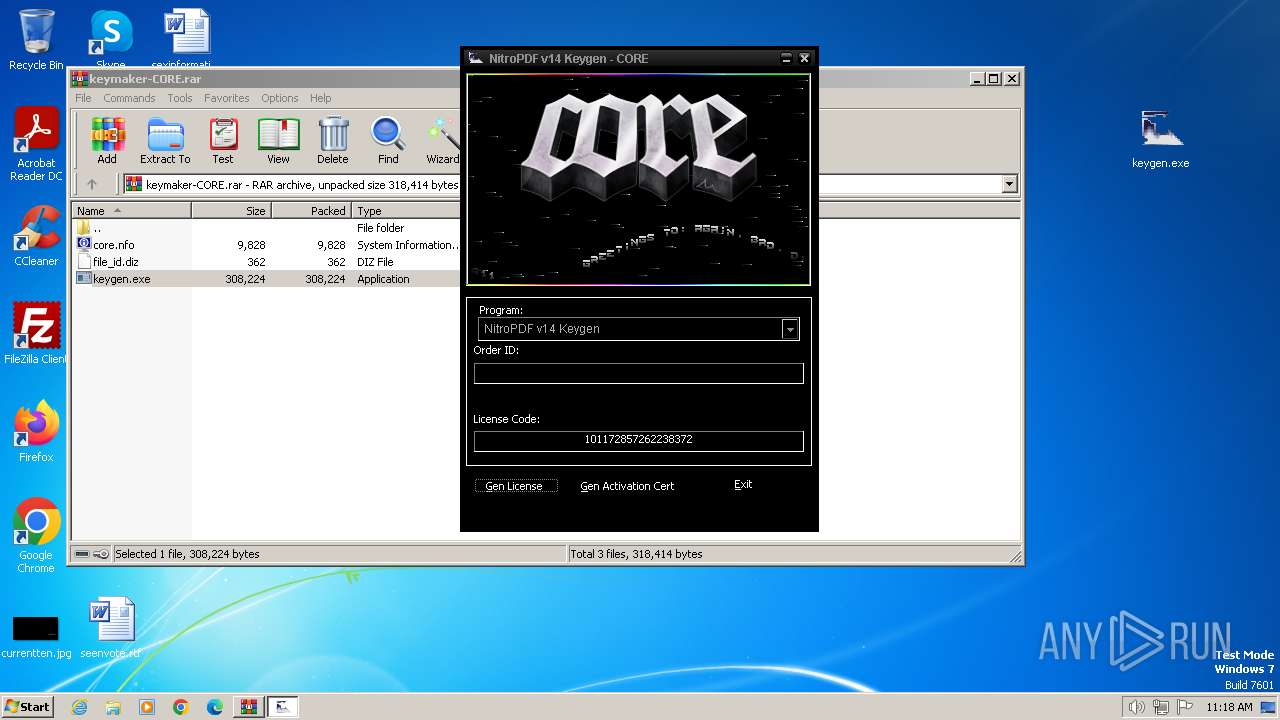
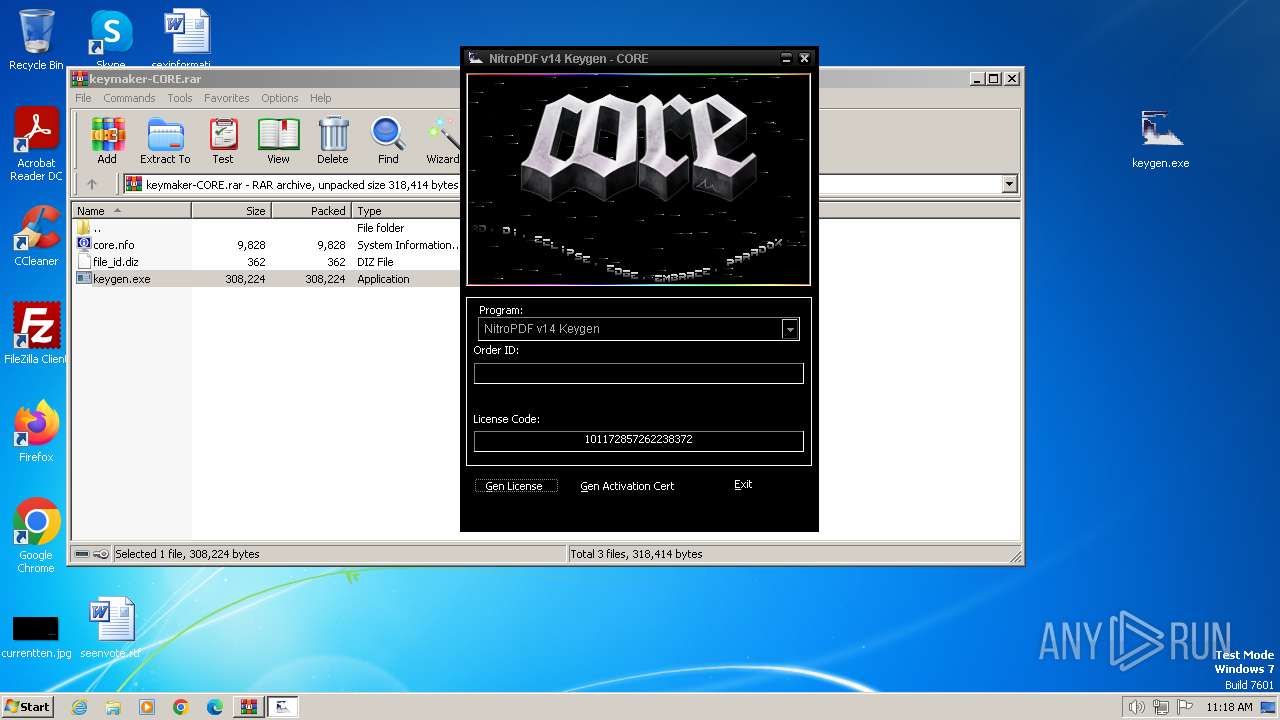
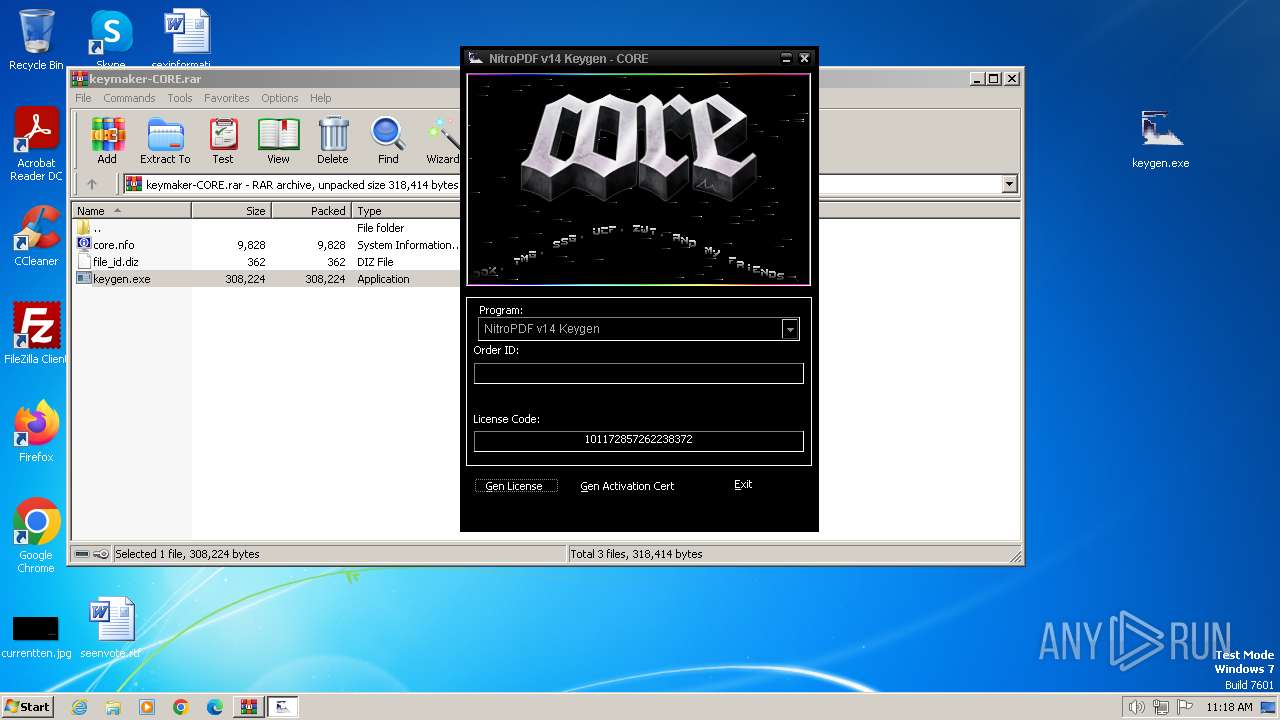
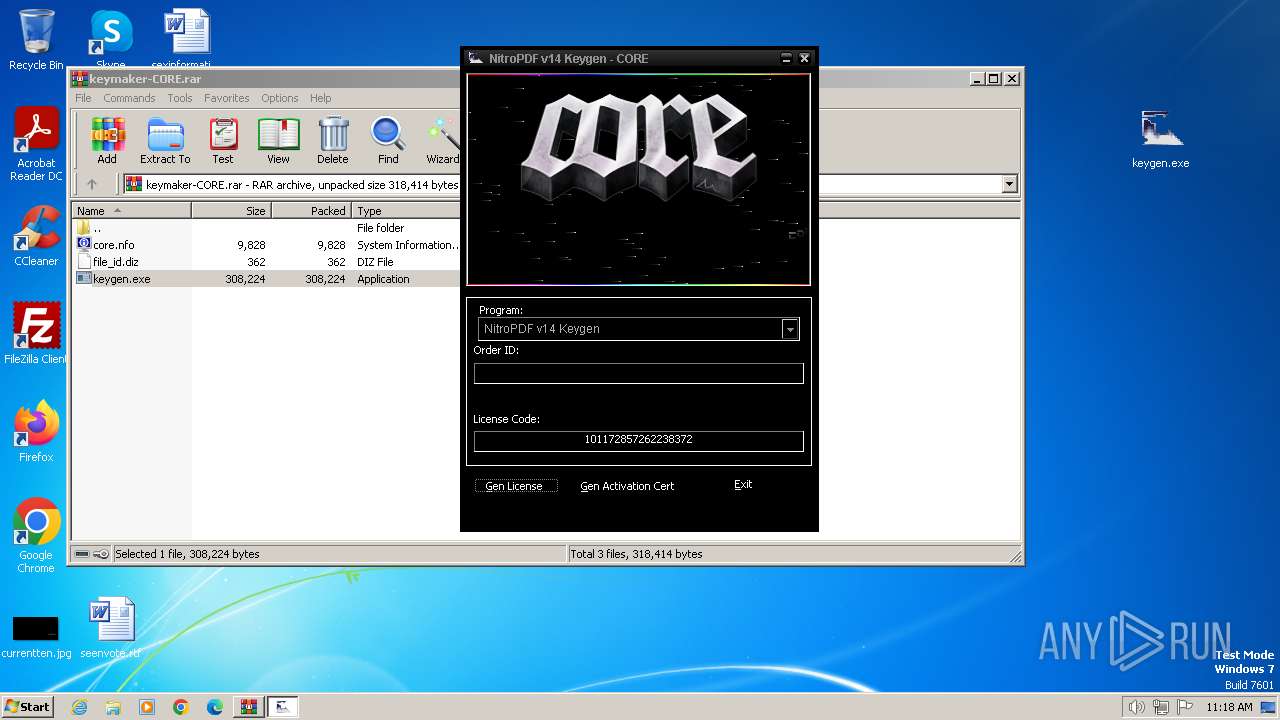
| File name: | keymaker-CORE.rar |
| Full analysis: | https://app.any.run/tasks/9957256a-c798-4242-9005-89d66ed33173 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2024, 10:17:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
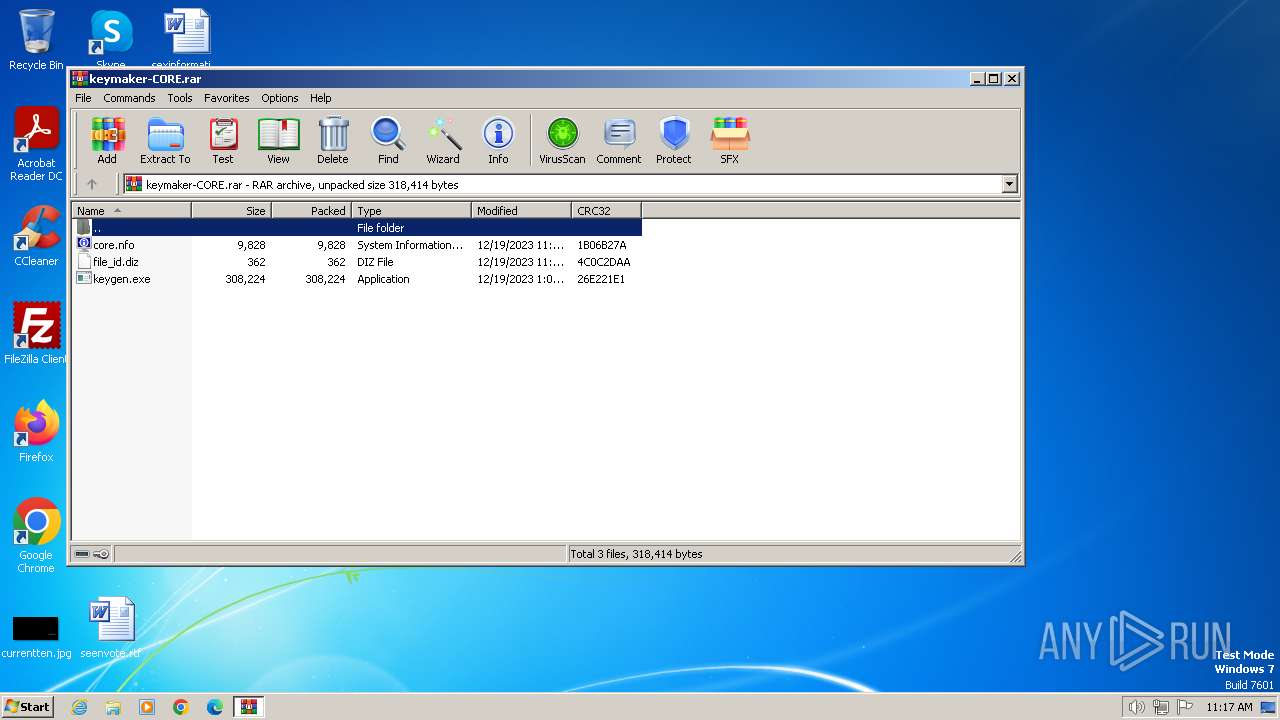
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5FF069E8423C6396EAF93A64844155C6 |
| SHA1: | 3211388DBF62C82EAABACE87CB5A9842219F805A |
| SHA256: | 093153A252DA53F2684CDE8ABC026AEFFA25C560E2AEEA5AD22E6D3BE5A952A7 |
| SSDEEP: | 12288:SquzImxolCXQUbewRp3F7WaMFfl66Wp7T6:SquzImxo4gOewRp3F7WaKfl66WpS |
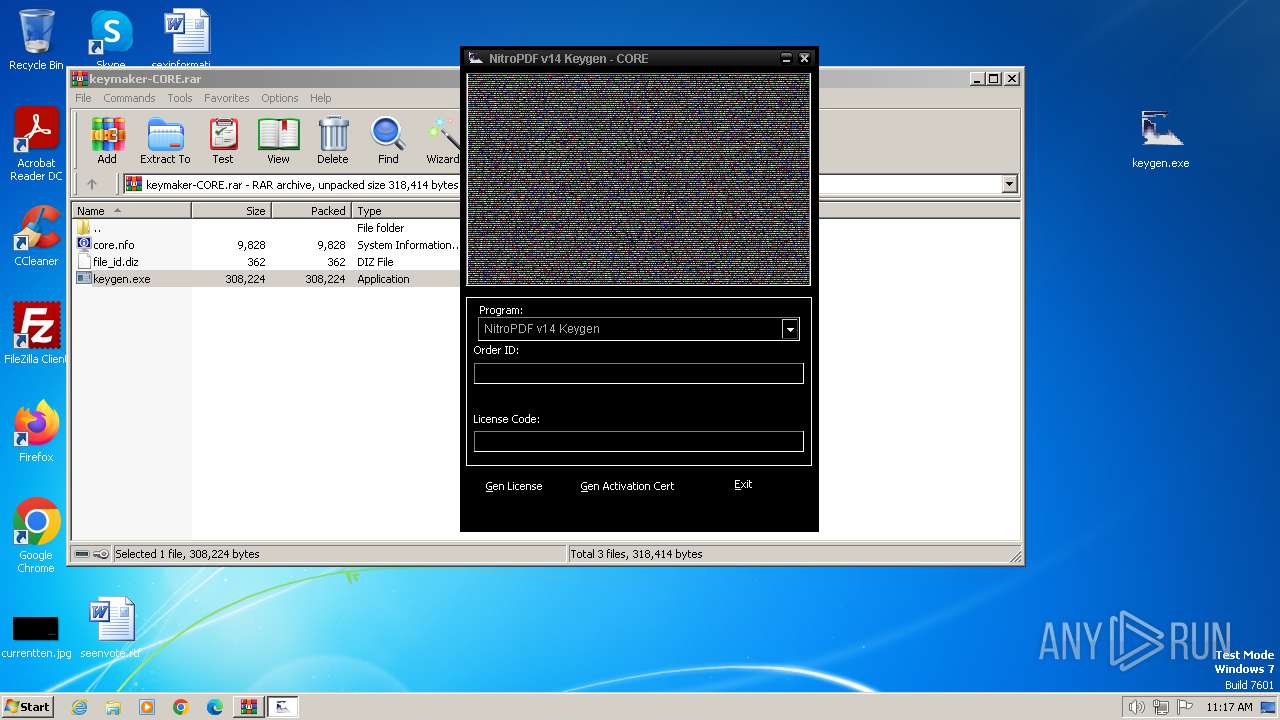
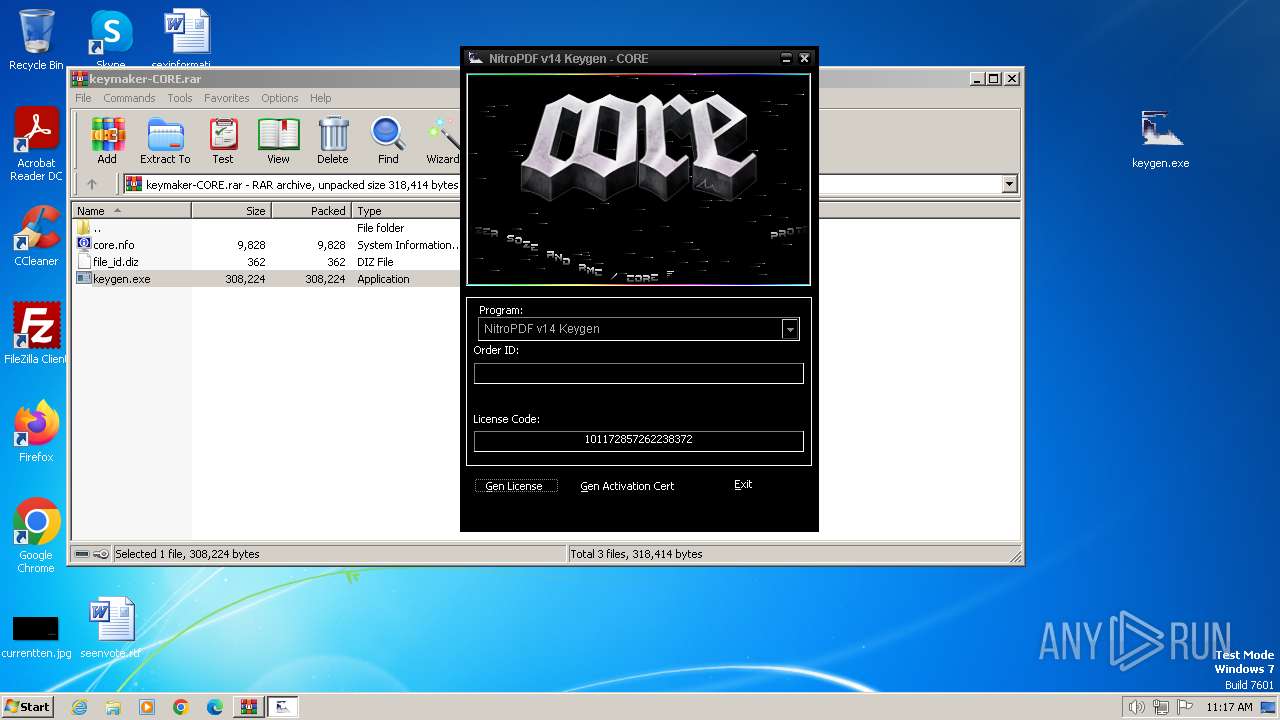
MALICIOUS
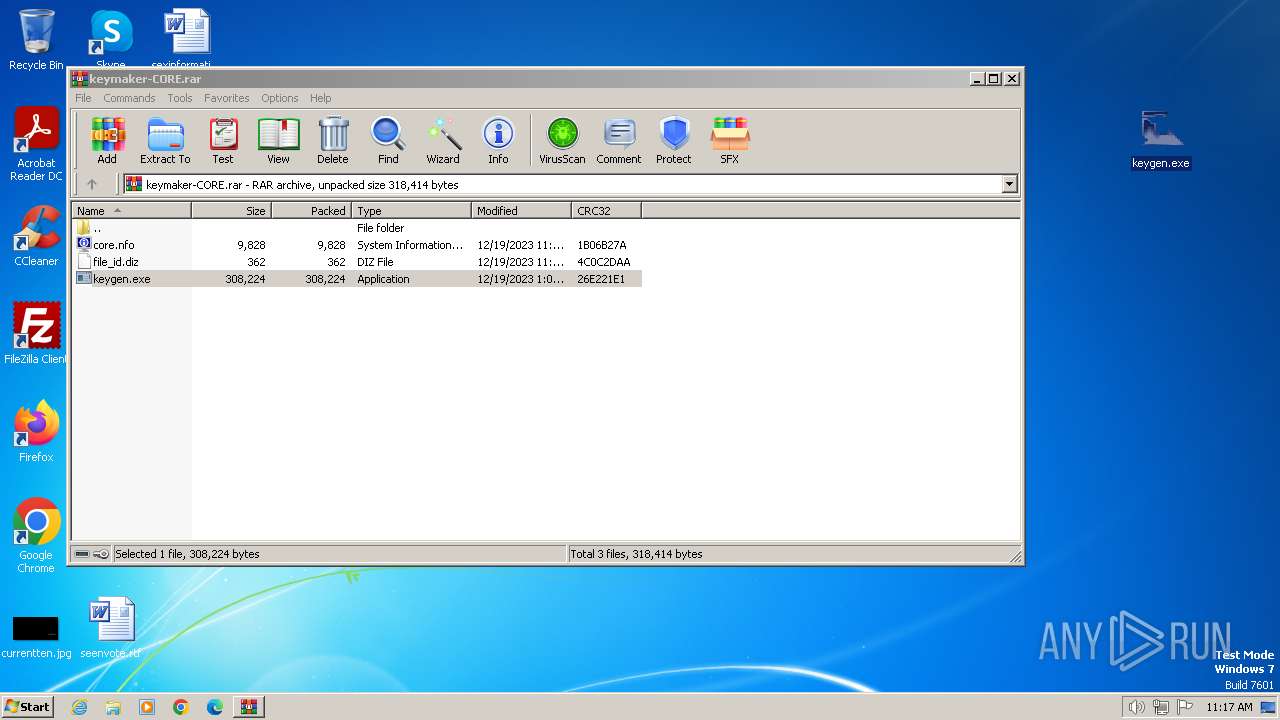
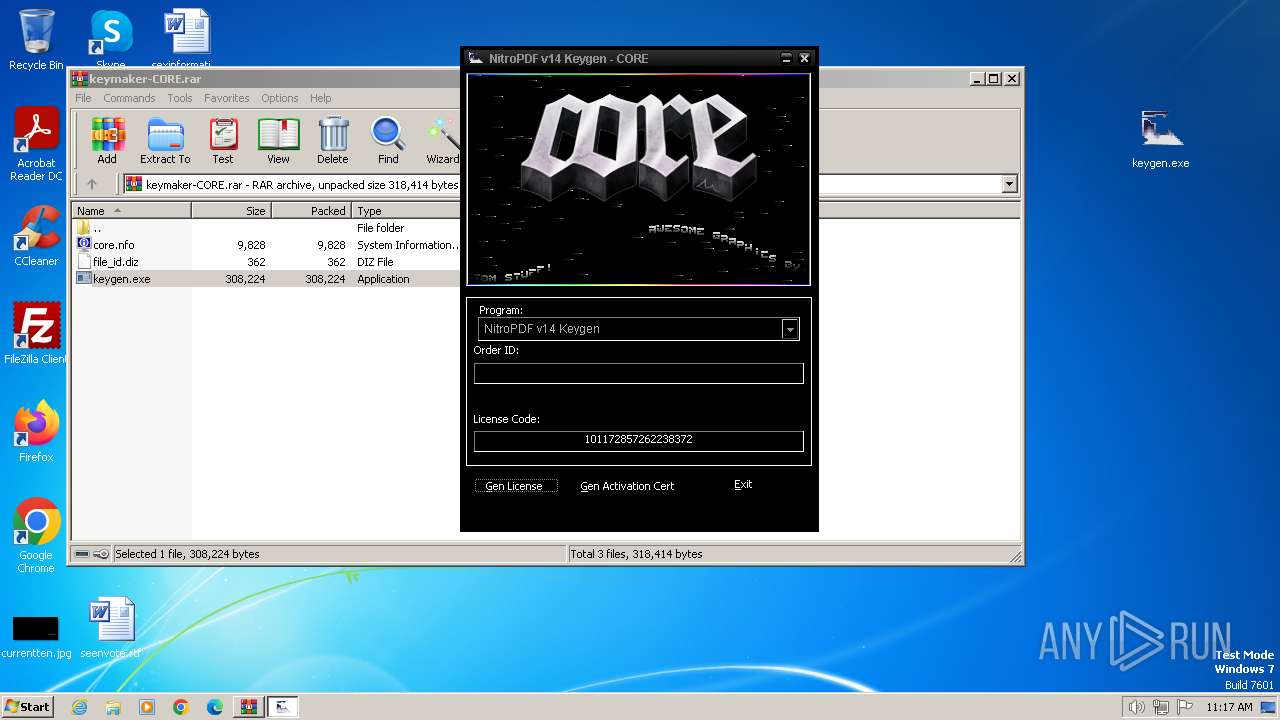
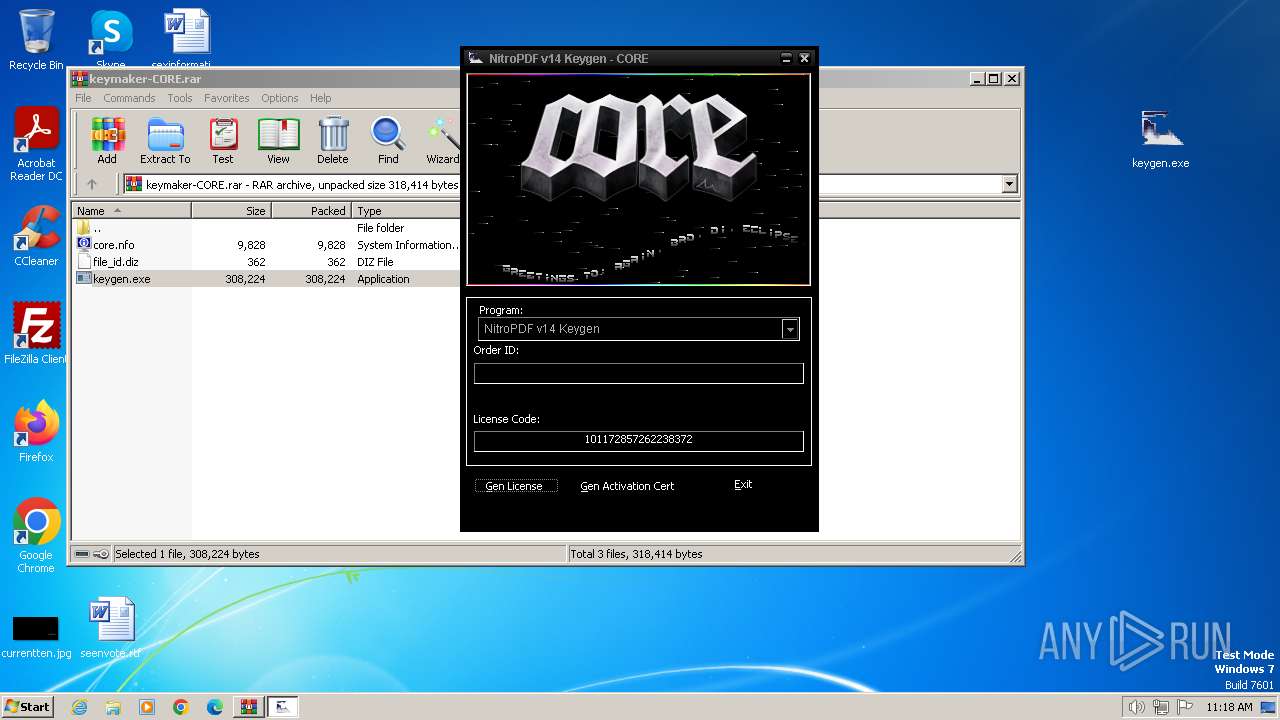
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3432)
- keygen.exe (PID: 680)
SUSPICIOUS
Executable content was dropped or overwritten
- keygen.exe (PID: 680)
There is functionality for taking screenshot (YARA)
- keygen.exe (PID: 680)
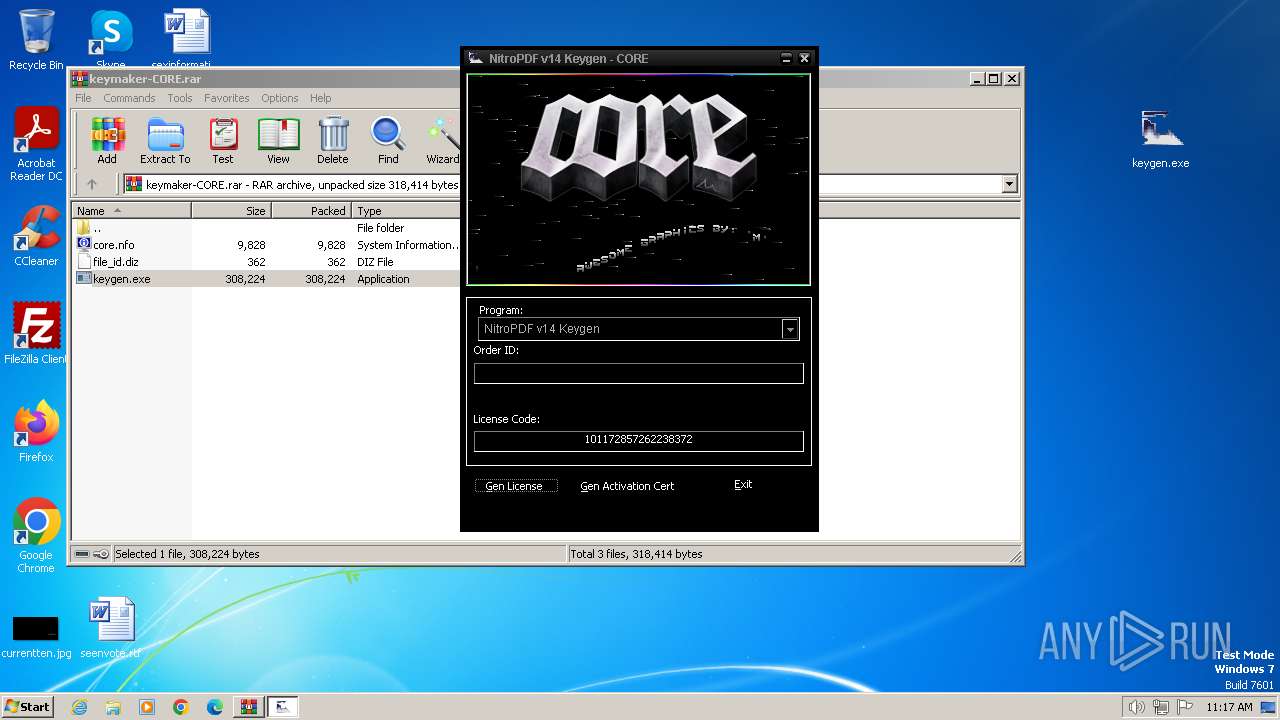
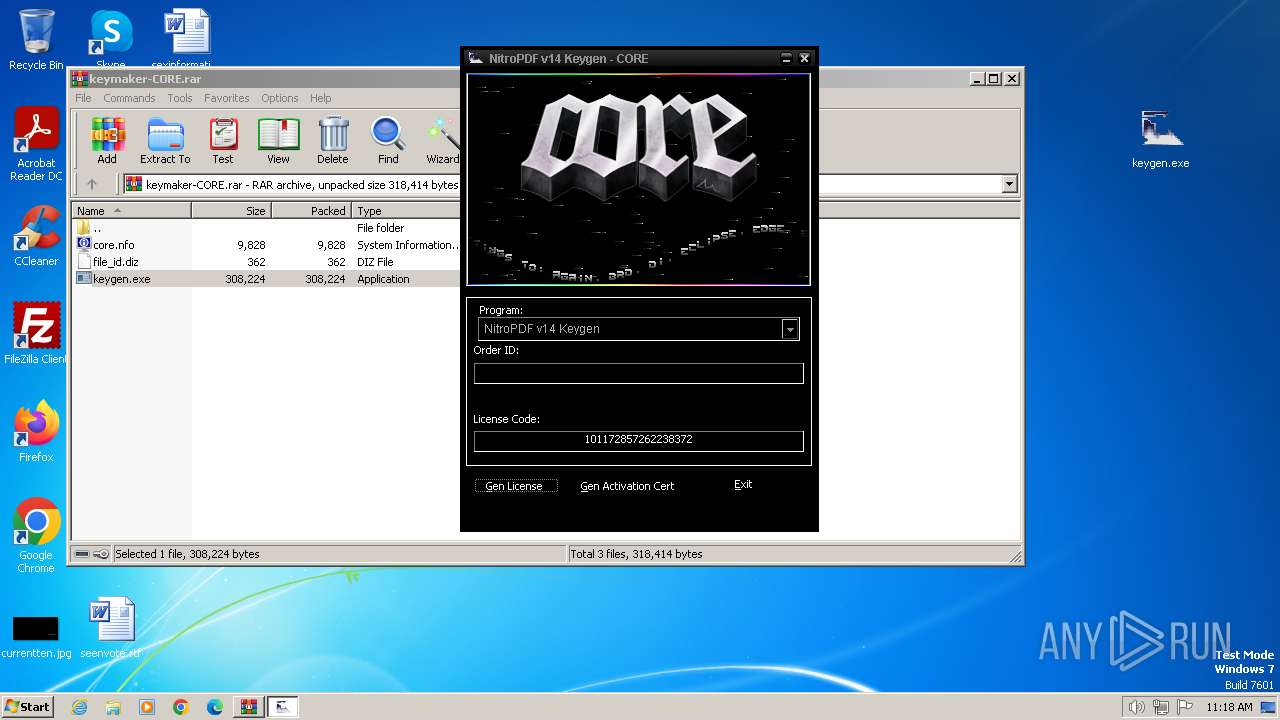
INFO
Checks supported languages
- keygen.exe (PID: 680)
Create files in a temporary directory
- keygen.exe (PID: 680)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3432)
Manual execution by a user
- keygen.exe (PID: 680)
Reads the computer name
- keygen.exe (PID: 680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Users\admin\Desktop\keygen.exe" | C:\Users\admin\Desktop\keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3416 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3432 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\keymaker-CORE.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 672
Read events
3 659
Write events
13
Delete events
0
Modification events
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\keymaker-CORE.rar | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3432) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
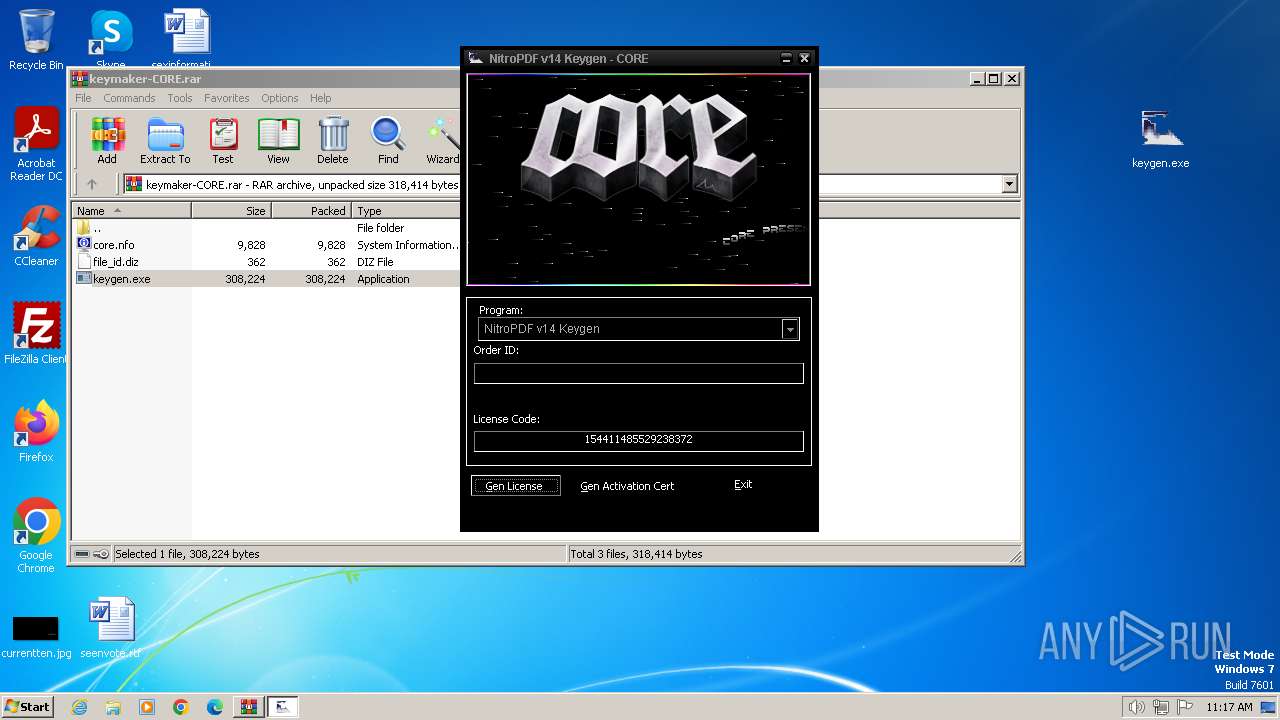
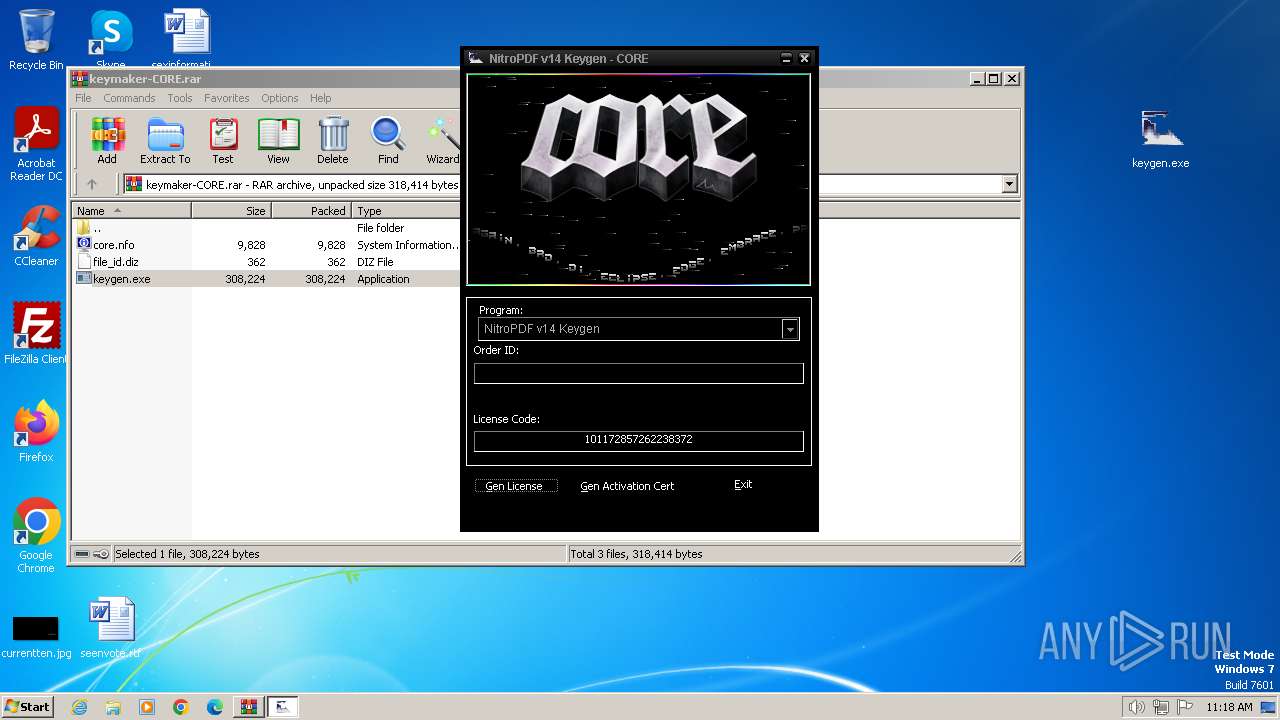
Executable files
4
Suspicious files
0
Text files
3
Unknown types
0
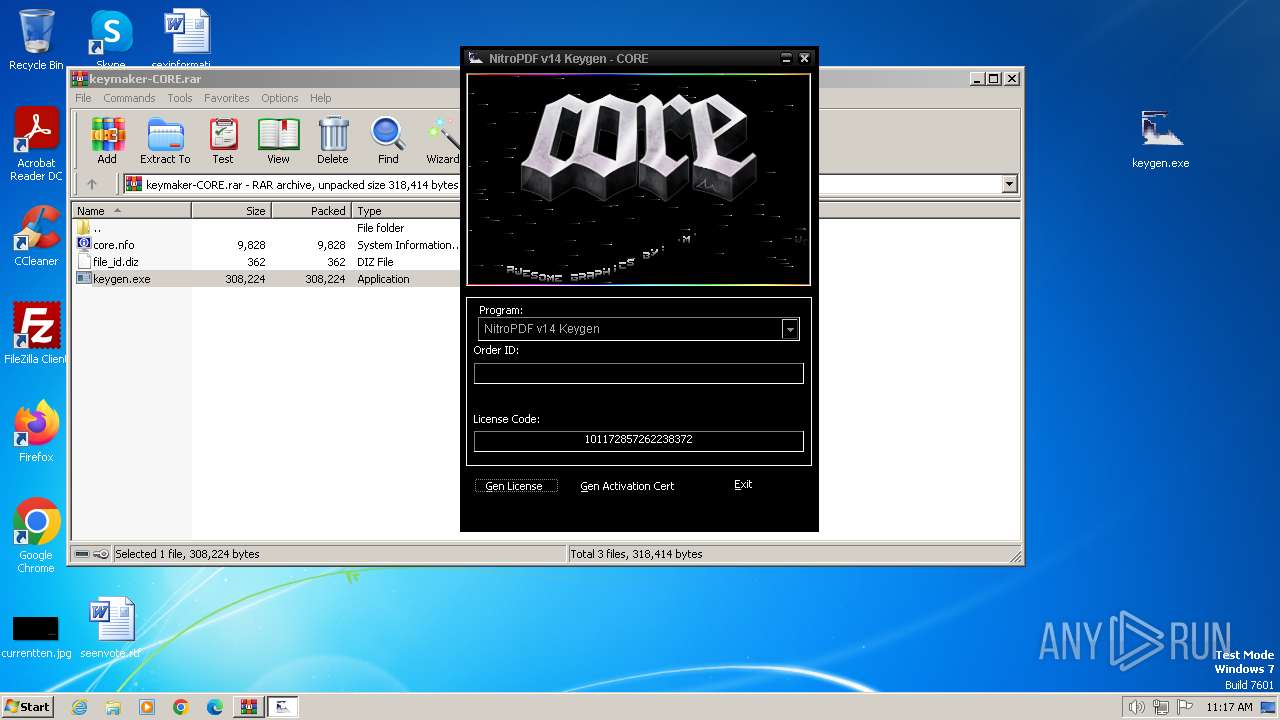
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 680 | keygen.exe | C:\Users\admin\AppData\Local\Temp\Test.dat | text | |
MD5:0CBC6611F5540BD0809A388DC95A615B | SHA256:532EAABD9574880DBF76B9B8CC00832C20A6EC113D682299550D7A6E0F345E25 | |||
| 680 | keygen.exe | C:\Users\admin\AppData\Local\Temp\wqcmWZdxfvhUNcRSBkHT.DLL | executable | |
MD5:E6144FB36C1FDC6BA1D1AFA9632588F8 | SHA256:B141412D0611571DF381C26186B3FC438C725D6E45AD66FD76413322C17A9AC6 | |||
| 3432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3432.15583\keygen.exe | executable | |
MD5:9D1148CEB3E112865AF47710D838130C | SHA256:7BD4AC5A187C330B2FC8D4F2D710899624E174C3ECB28BD9406FF61DFD0606D6 | |||
| 680 | keygen.exe | C:\Users\admin\AppData\Local\Temp\ShOuvzqObf.DLL | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 680 | keygen.exe | C:\Users\admin\AppData\Local\Temp\eGGemVGdUePapUFneCLs.DLL | executable | |
MD5:76A9565C5F51775719EEBDA1F25530A5 | SHA256:A1A7C4F74D4FE7784ED03709E5F946B94CC10A64E3AE0AD5A9A3BECE9A8A2C0A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
13
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1372 | svchost.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
1372 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |