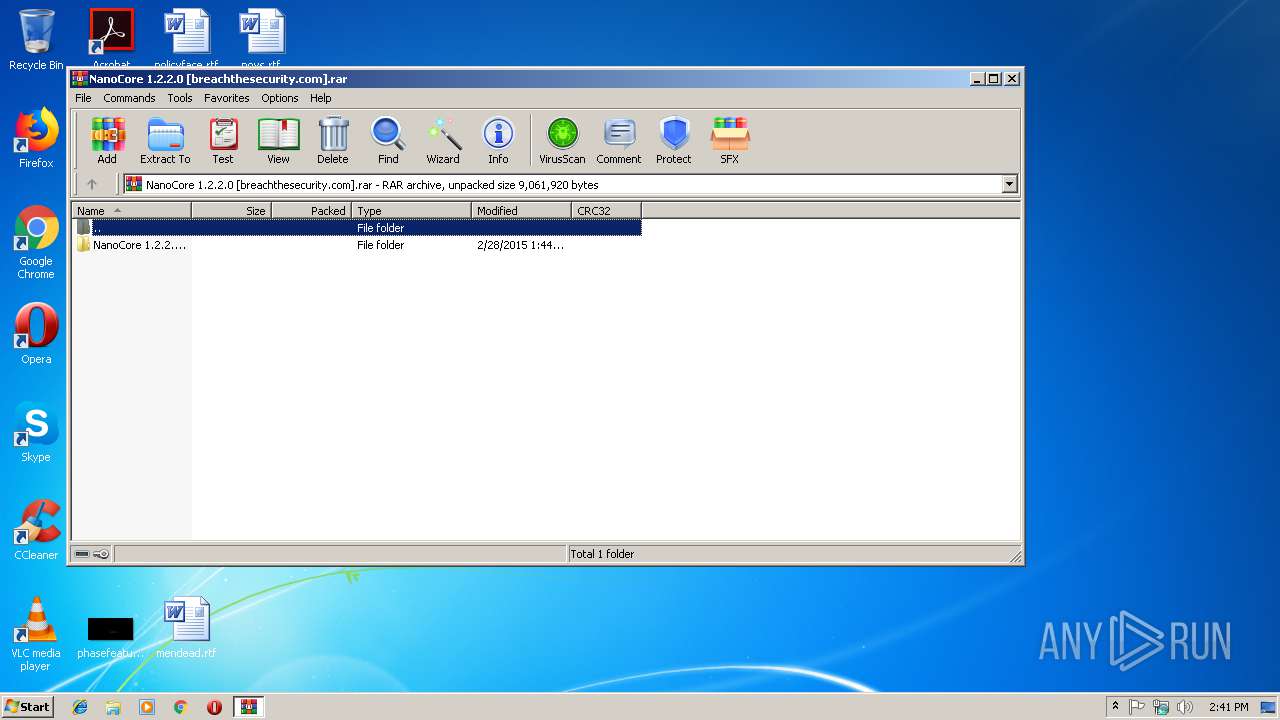
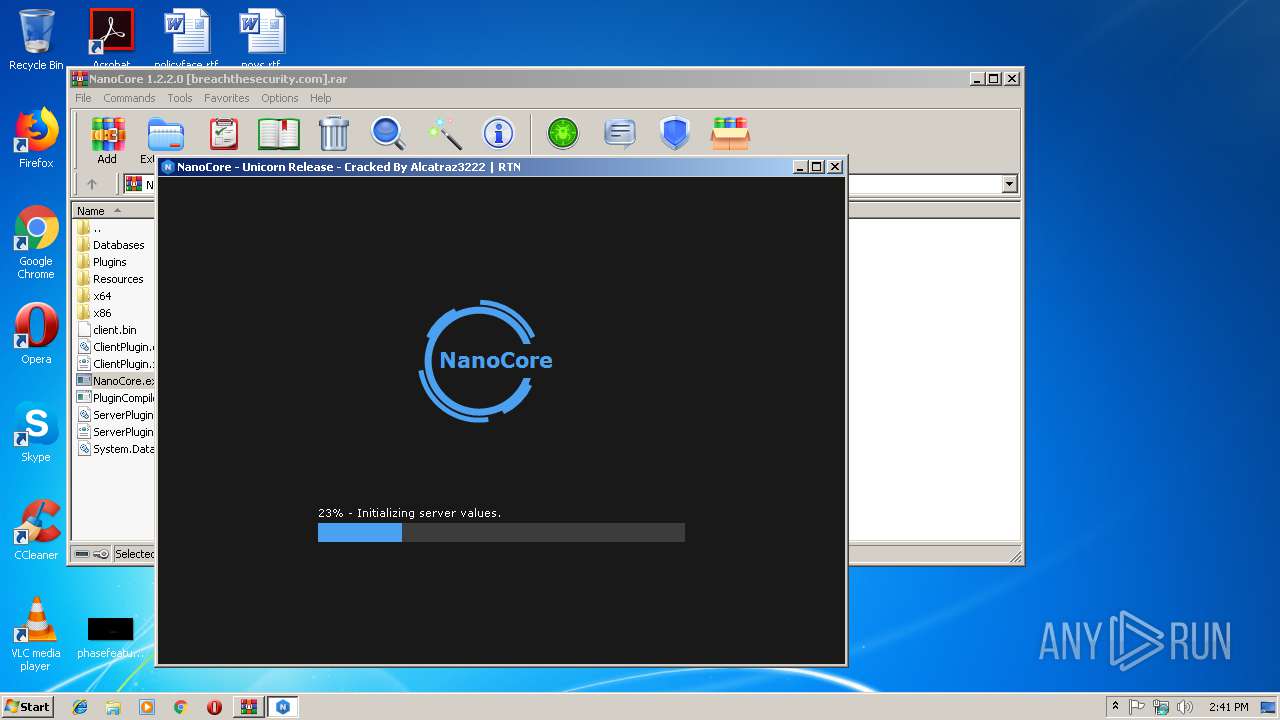
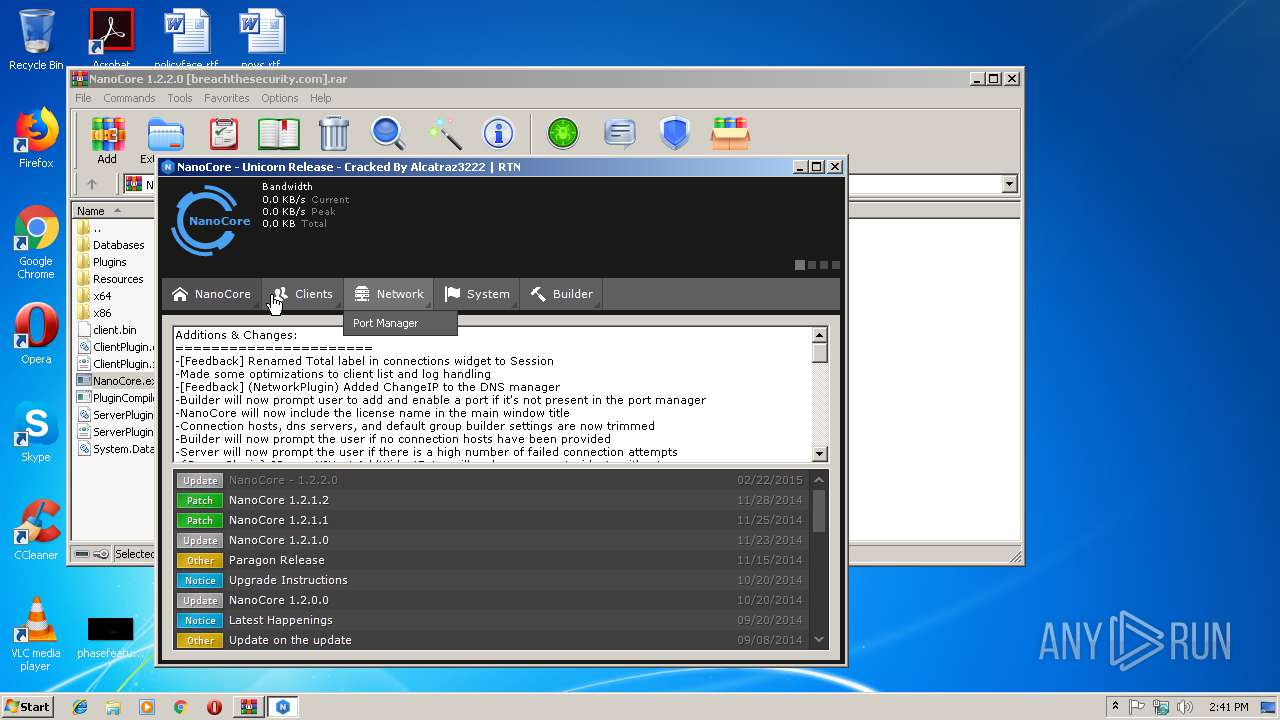
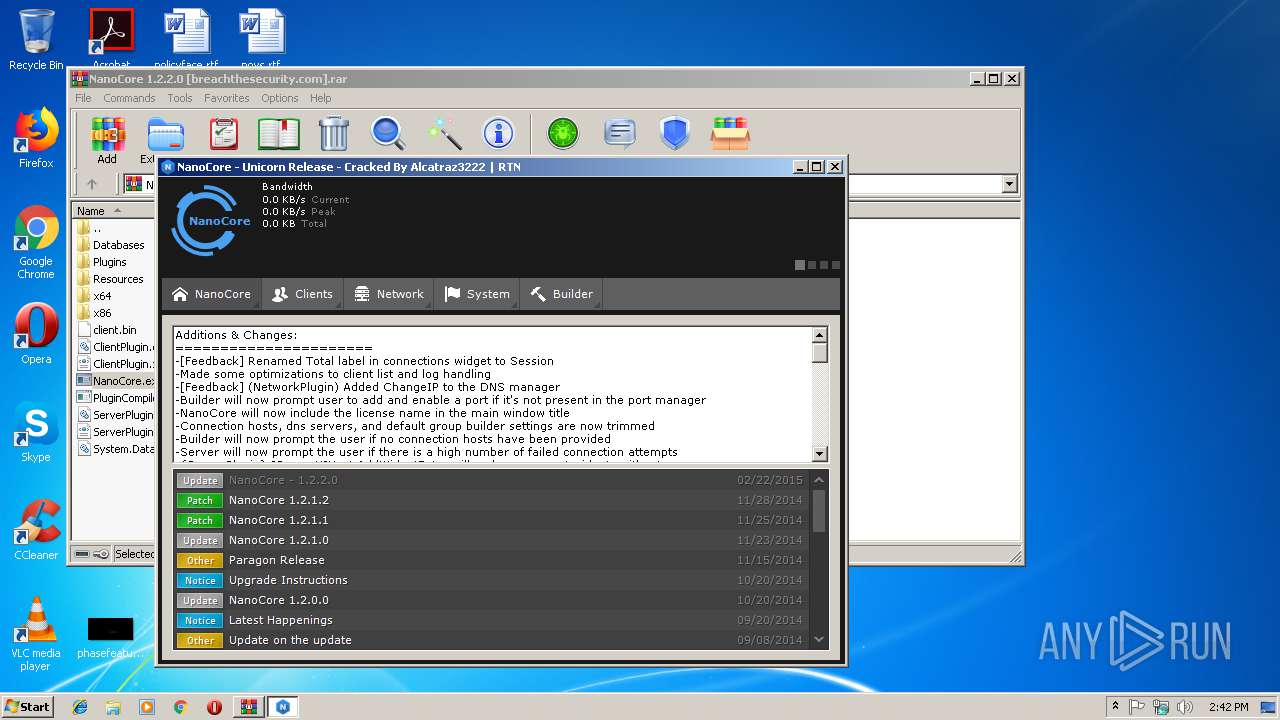
| File name: | NanoCore 1.2.2.0 [breachthesecurity.com].rar |
| Full analysis: | https://app.any.run/tasks/e5e69a08-fd65-4442-b02d-70b62f09e248 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2019, 14:40:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | CC782398D4A1BAB03F9ED491C5409BA7 |
| SHA1: | 1870390952567D3C560E55346F33E579FB789351 |
| SHA256: | 092D888C4BF27C3BEA3BA14C9E4A92B33C0376D1873F43C85EF3AD029B3196CB |
| SSDEEP: | 98304:tqFo/nbu5TvOa0JitDRyjvjKZv1UBCFCo/IxCFONOGTUgXdKdHS:kMbebSg4KgB2akgNOCzdKdHS |
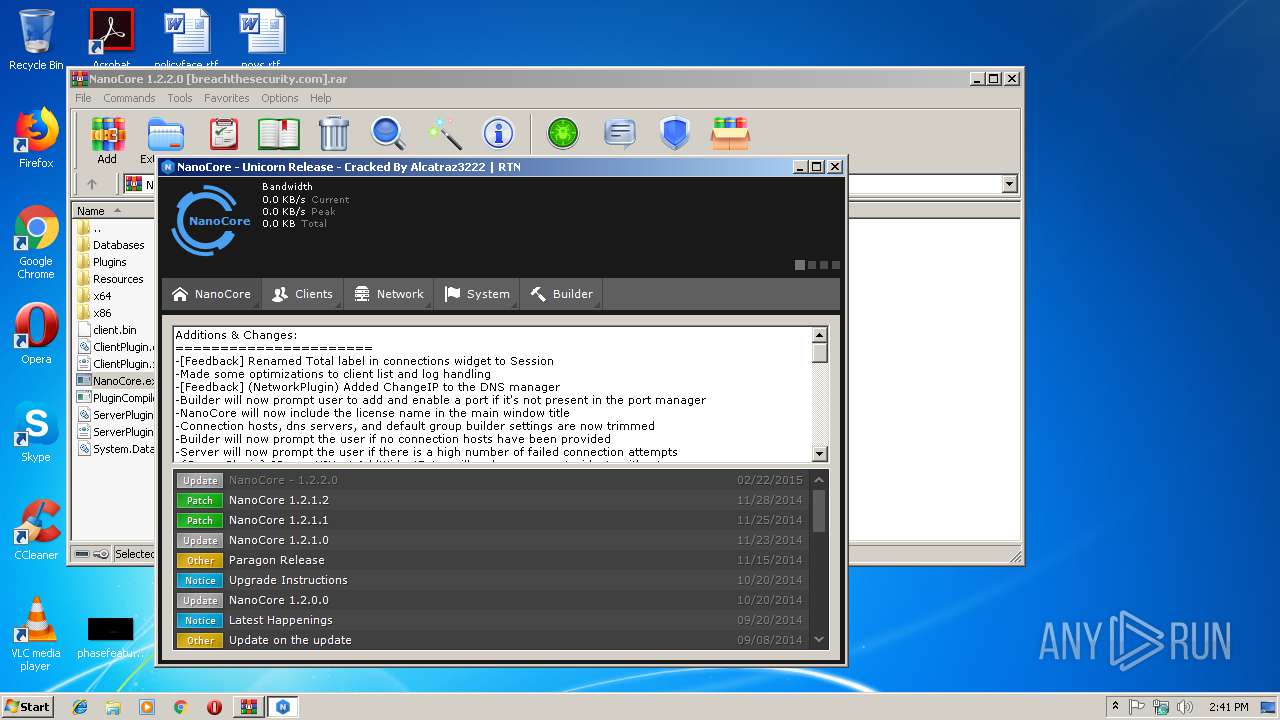
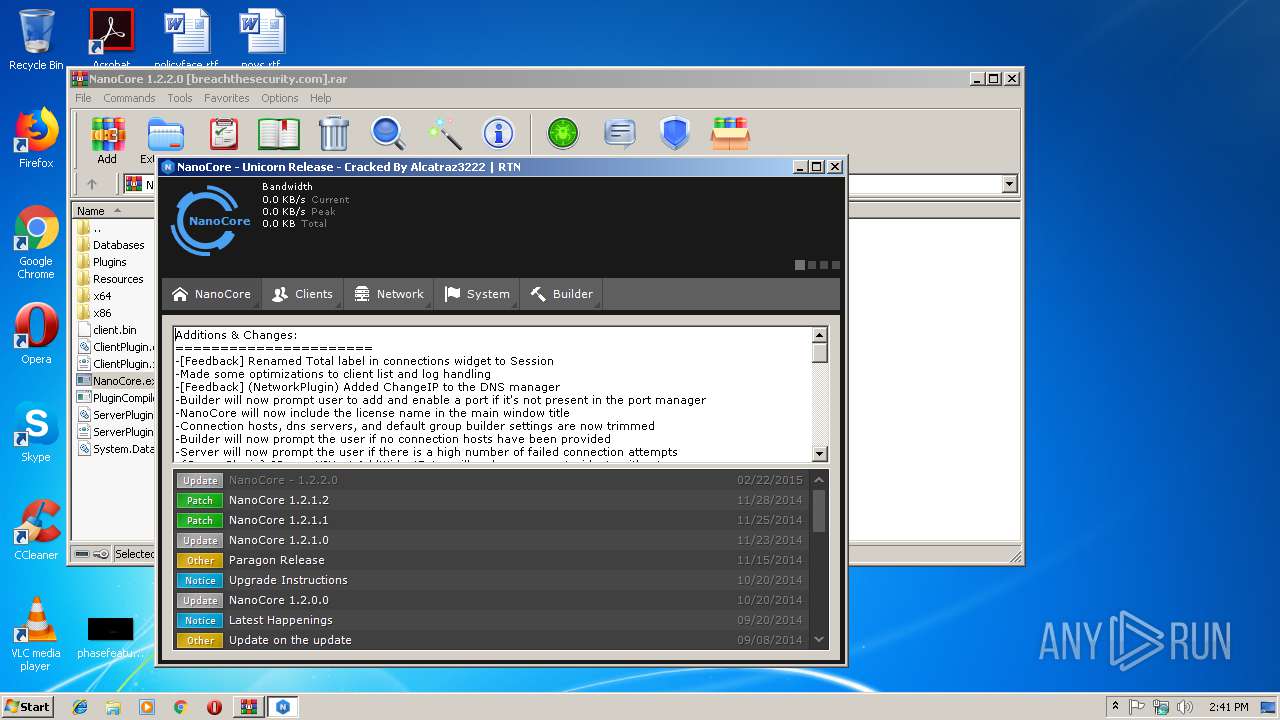
MALICIOUS
Loads dropped or rewritten executable
- NanoCore.exe (PID: 2896)
Application was dropped or rewritten from another process
- NanoCore.exe (PID: 2896)
SUSPICIOUS
Checks for external IP
- NanoCore.exe (PID: 2896)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3084)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
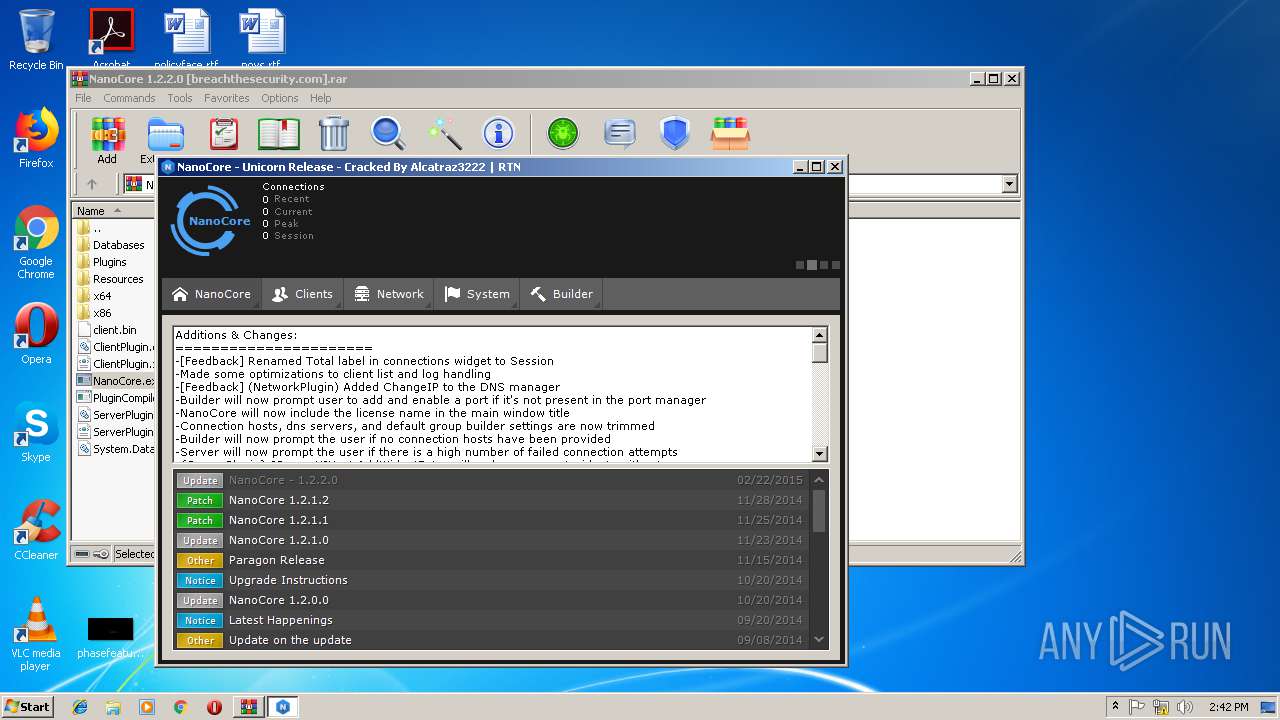
Total processes
31
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
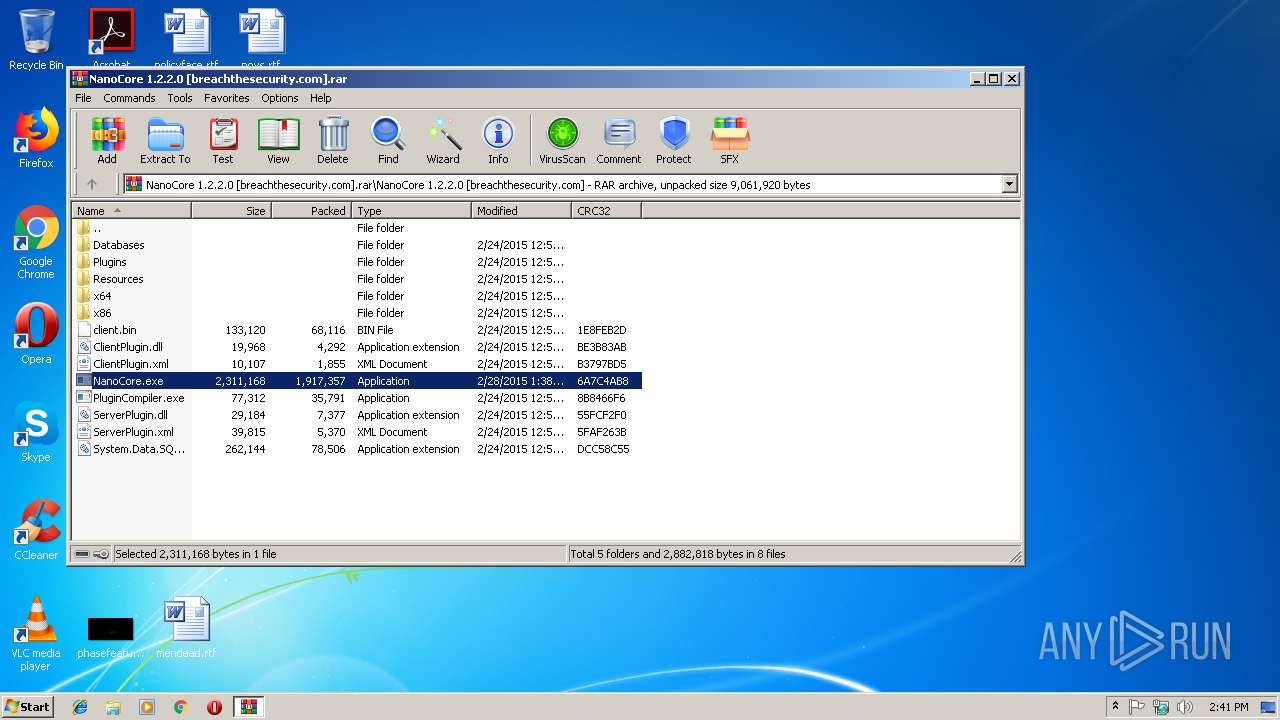
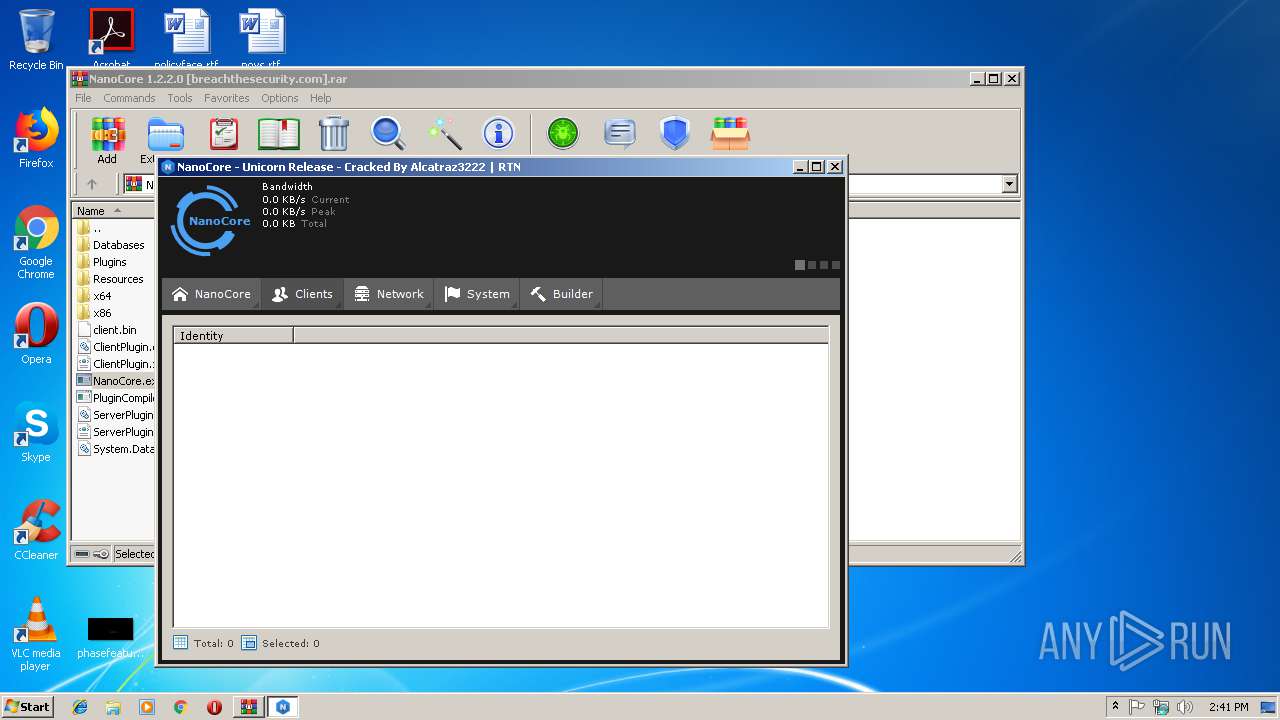
| 2896 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\NanoCore.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\NanoCore.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NanoCore Exit code: 0 Version: 1.2.2.0 Modules
| |||||||||||||||
| 3084 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NanoCore 1.2.2.0 [breachthesecurity.com].rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
459
Read events
434
Write events
25
Delete events
0
Modification events
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NanoCore 1.2.2.0 [breachthesecurity.com].rar | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
8
Suspicious files
8
Text files
336
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
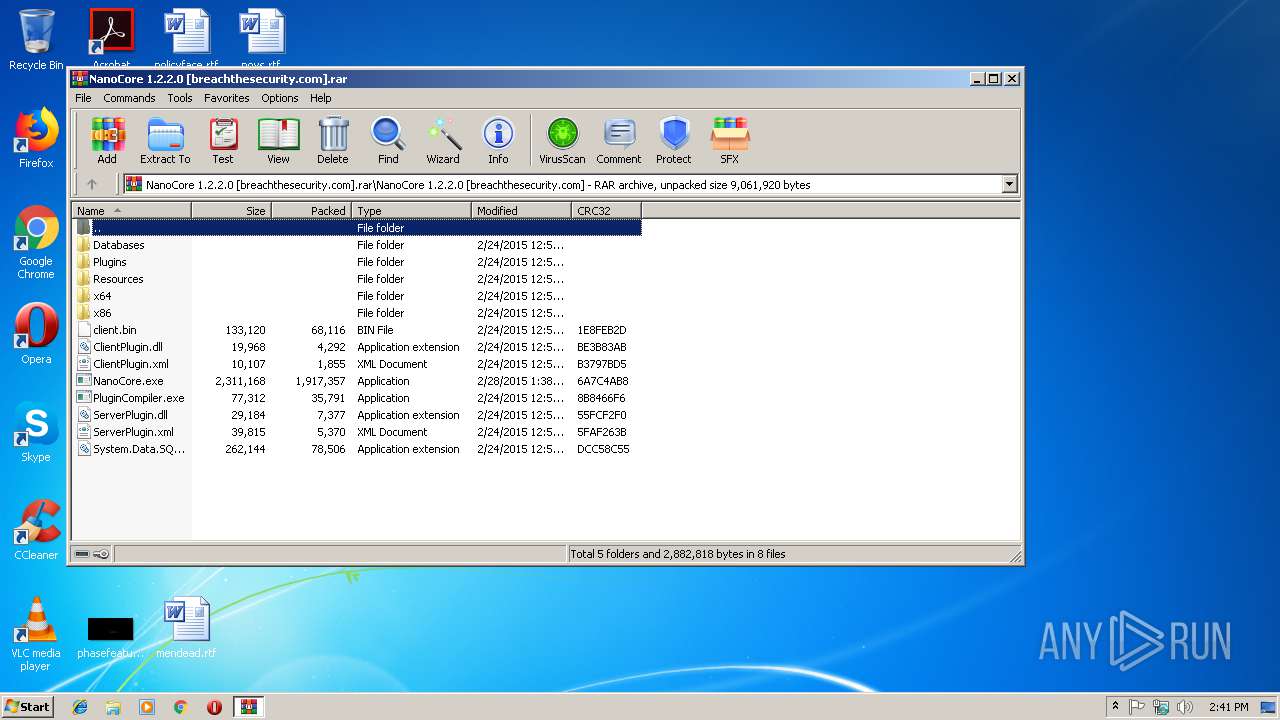
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\Plugins\ManagementPlugin.ncp | binary | |
MD5:B612C2C9A6D361A5DB14C04BA126119C | SHA256:B86FE4E126A9748A383A34D615B9598C715F2380C0AAD957495C66923902026C | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\client.bin | executable | |
MD5:906A949E34472F99BA683EFF21907231 | SHA256:9D3EA5AF7DC261BF93C76F55D702A315AA22FB241E4207DC86CD834C262245C8 | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\Plugins\NetworkPlugin.ncp | binary | |
MD5:70E5B02349742A550FBFCFB5BB78C906 | SHA256:160030B8444B6FA86775A11D1BE35DF6A75252070FC5661055884D3F8B07296D | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\ClientPlugin.dll | executable | |
MD5:BDC8945F1D799C845408522E372D1DBD | SHA256:61E9D5C0727665E9EF3F328141397BE47C65ED11AB621C644B5BBF1D67138403 | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\Plugins\CorePlugin.ncp | binary | |
MD5:7914E7302F72D330AA5F6C5C8C26DF43 | SHA256:F66985518B1E56A04F512D110F5B79F21ED91CBCBF6BD3E17EBA3DCDFB85F9B5 | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\PluginCompiler.exe | executable | |
MD5:E2D1C5DF11F9573F6C5D0A7AD1A79FBF | SHA256:0B41B2FCD0F1A4E913D3EFE293F713849D59EFEBB27BAC060AB31BED51AC2F6B | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\Databases\geolocation.sqlite | sqlite | |
MD5:0E8D861CDDEDE3A0B2B02CFC0B060B99 | SHA256:11BD851D8994D3CA9D078144679AA2DC06841ADDD0947B8FA8AD36758BDECF7A | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\Resources\ContextIcons\arrow_refresh.png | image | |
MD5:9B1A30AC871AF0684BAA0E4E76911D48 | SHA256:6141EAF716680EF3030C0DB1252BB39BF3145E4A17225D787808C7731BA9358D | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\Resources\Audio\notify.wav | wav | |
MD5:832A3652FD780EDCDB2439EC33532C0D | SHA256:45F4136E58A5F749D125D2AB54308F81954D2C5B364B66013660A6C358845D1E | |||
| 3084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\Resources\Audio\camera.wav | wav | |
MD5:4567DBE9CC7CFDFE3A13A609E20A205E | SHA256:F49EC225A0DF03534F4B9B265AEDA561FD0A6B11D53038ABAA27B3858DB41AA1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2896 | NanoCore.exe | GET | 200 | 54.243.123.39:80 | http://api.ipify.org/ | US | text | 13 b | shared |
2896 | NanoCore.exe | GET | 200 | 54.243.123.39:80 | http://api.ipify.org/ | US | text | 13 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | NanoCore.exe | 54.243.123.39:80 | api.ipify.org | Amazon.com, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2896 | NanoCore.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
2896 | NanoCore.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
Process | Message |
|---|---|
NanoCore.exe | Trying to load native SQLite library "C:\Users\admin\AppData\Local\Temp\Rar$EXa3084.28789\NanoCore 1.2.2.0 [breachthesecurity.com]\x86\SQLite.Interop.dll"...
|