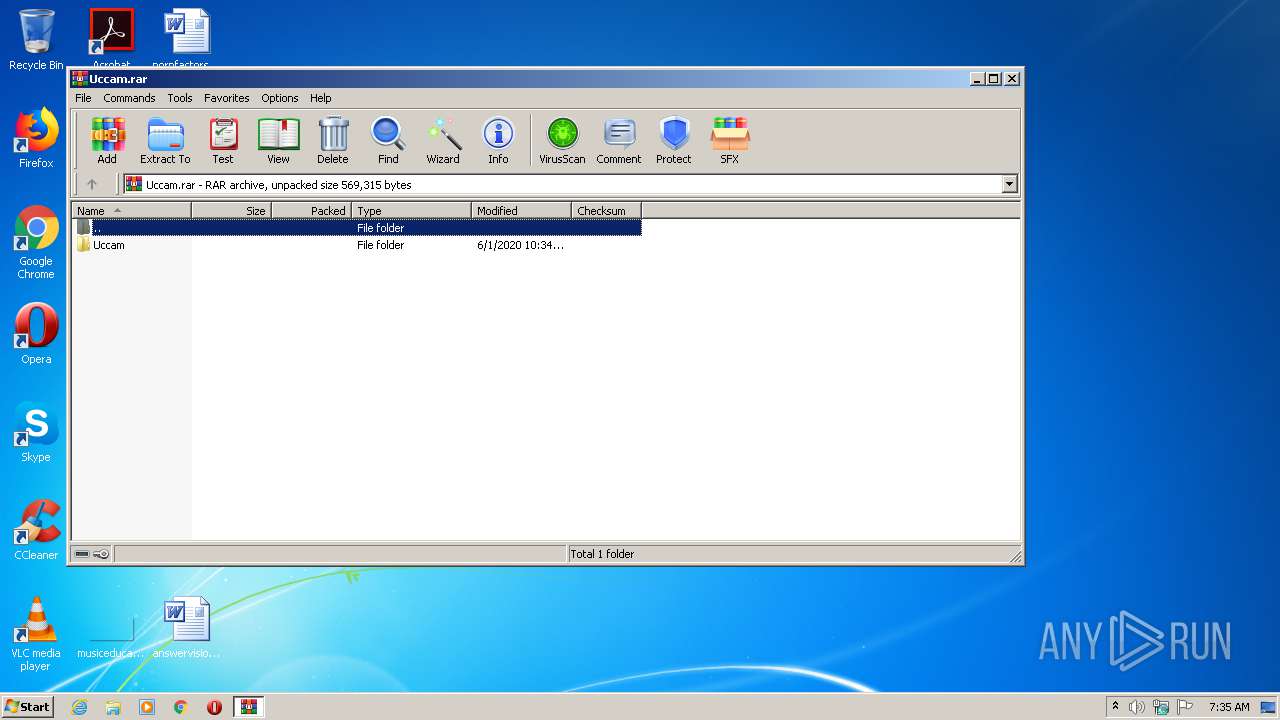
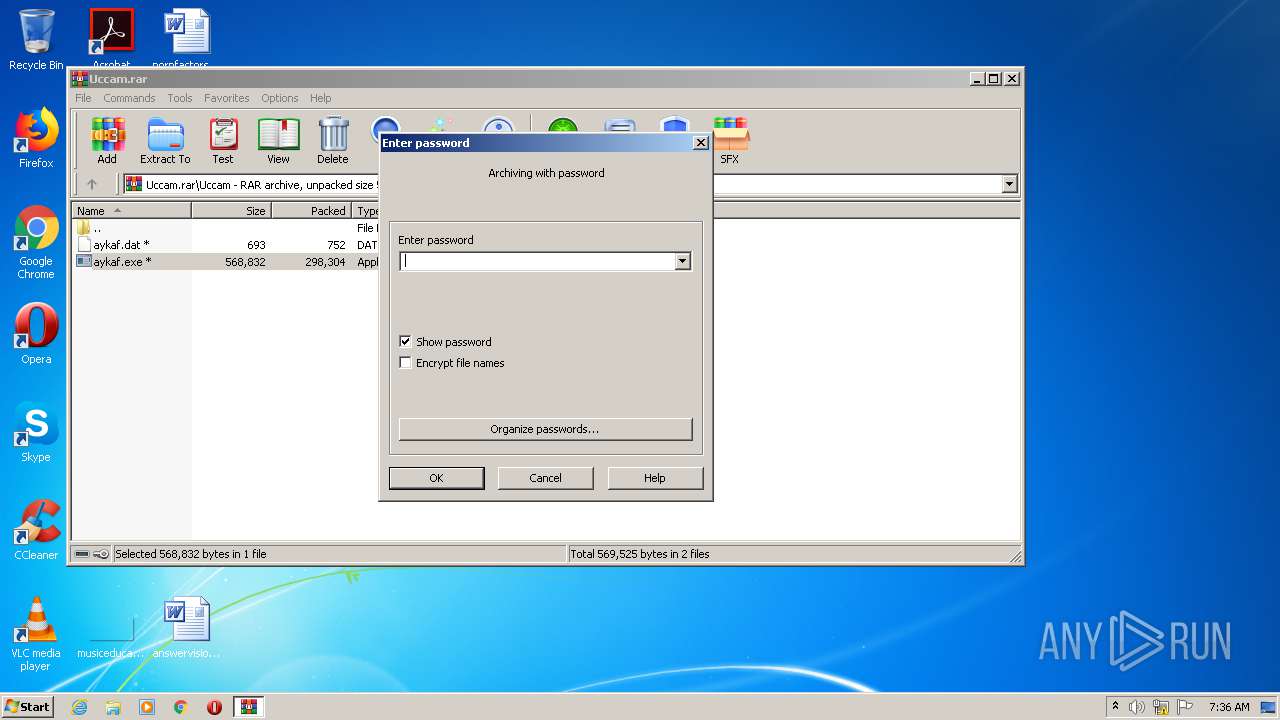
| File name: | Uccam.rar |
| Full analysis: | https://app.any.run/tasks/b0dc7e97-c1d1-40a4-90fd-2e909c1ce746 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 06:35:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | AB0165C09EBC0297C8327FFA7E6C6D1F |
| SHA1: | 886A70C08E90B7D6ED21EC1B2871A5276202DEA7 |
| SHA256: | 092171BB23BB03DE6A605B41956C2E1658C531F573AD087BF8F563D7A91AB803 |
| SSDEEP: | 6144:JhMdwJg+sE5UgCHkz0ncMppNq0kuCp/sOXFsUyU2Q2+nyTdyAF:JhCYrCHkoncwkfKOByBQ3nyNF |
MALICIOUS
Application was dropped or rewritten from another process
- aykaf.exe (PID: 2520)
- aykaf.exe (PID: 4064)
- aykaf.exe (PID: 1416)
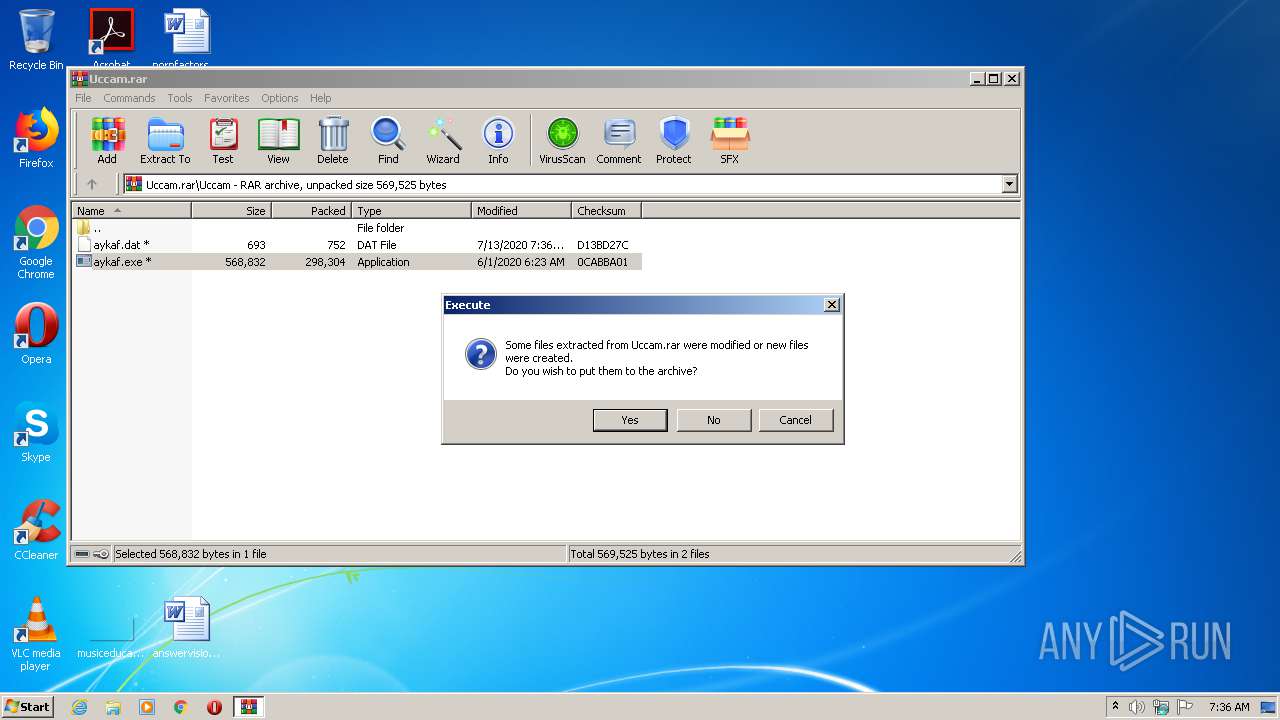
Changes the autorun value in the registry
- explorer.exe (PID: 2628)
Loads the Task Scheduler COM API
- explorer.exe (PID: 2628)
- schtasks.exe (PID: 2528)
Uses Task Scheduler to run other applications
- explorer.exe (PID: 2628)
SUSPICIOUS
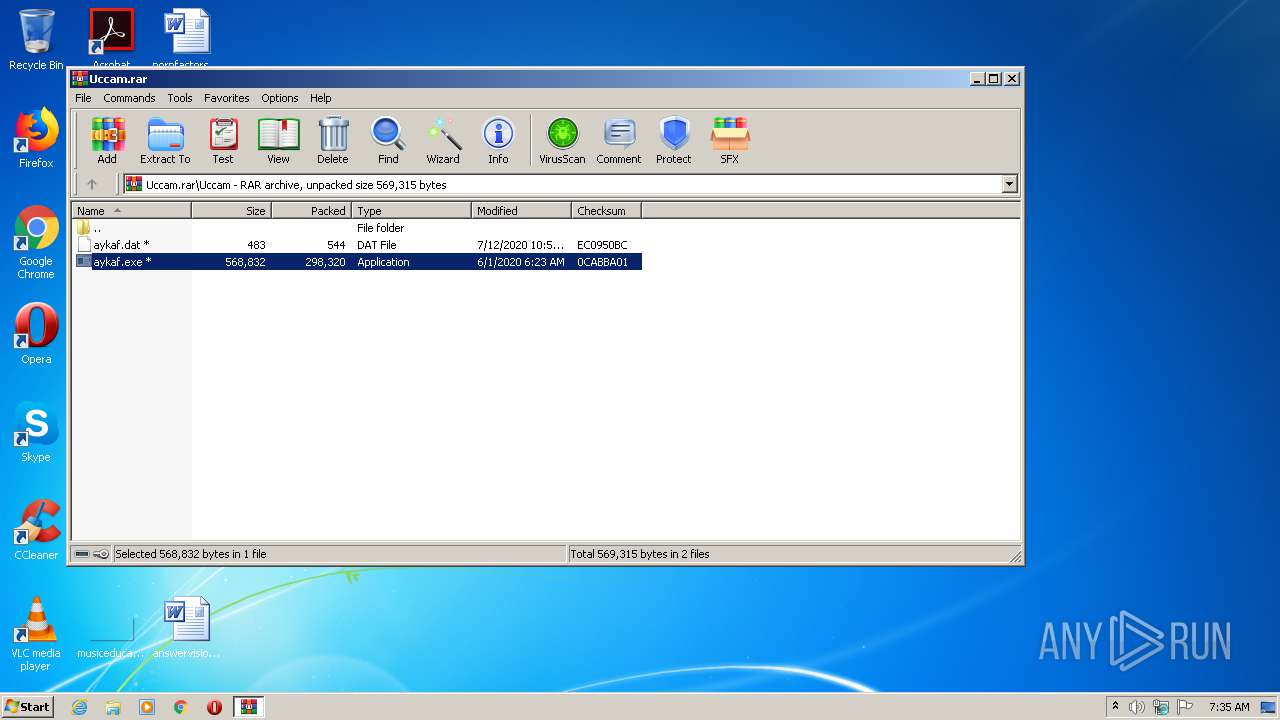
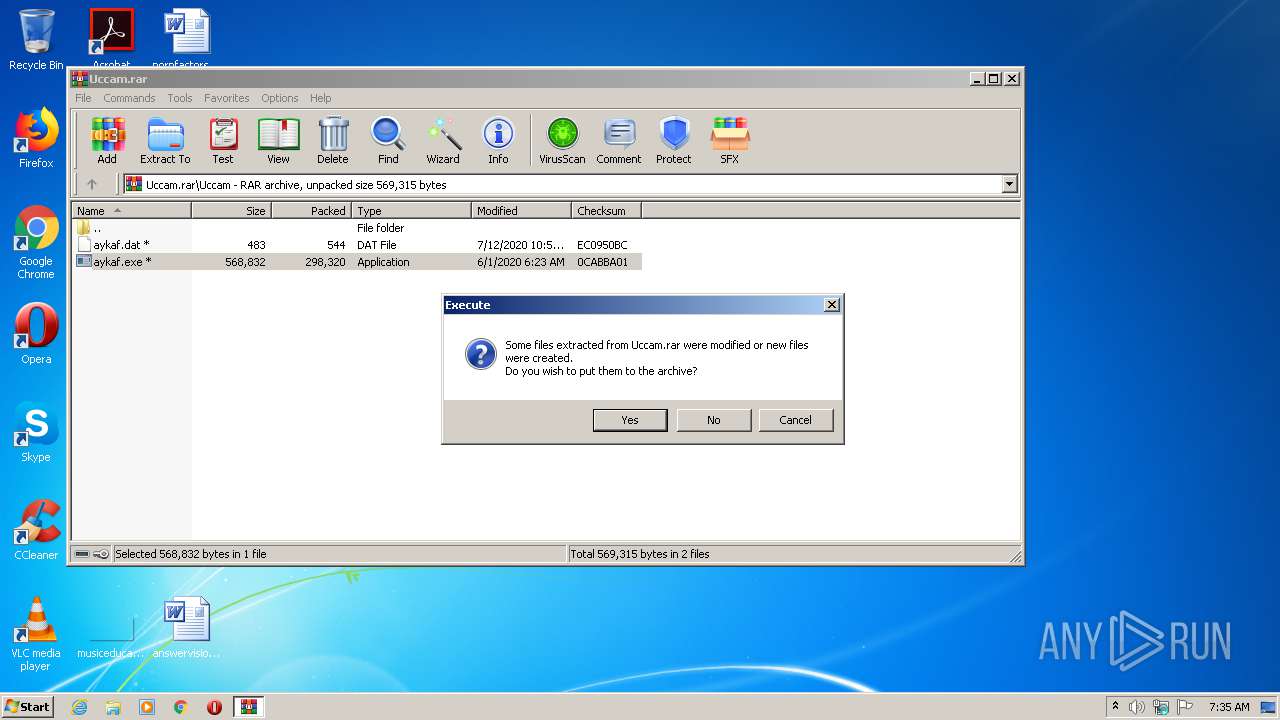
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1496)
Application launched itself
- aykaf.exe (PID: 2520)
Reads Internet Cache Settings
- explorer.exe (PID: 2628)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
40
Monitored processes
6
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1416 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.exe" /W | C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 111 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Uccam.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2528 | "C:\Windows\system32\schtasks.exe" /create /tn {C12565E3-7E71-4686-962C-CCDF2D8D62DF} /tr "\"C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.exe\"" /sc HOURLY /mo 5 /F | C:\Windows\system32\schtasks.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | aykaf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4064 | C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.exe /C | C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.exe | — | aykaf.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
603
Read events
569
Write events
34
Delete events
0
Modification events
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Uccam.rar | |||
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
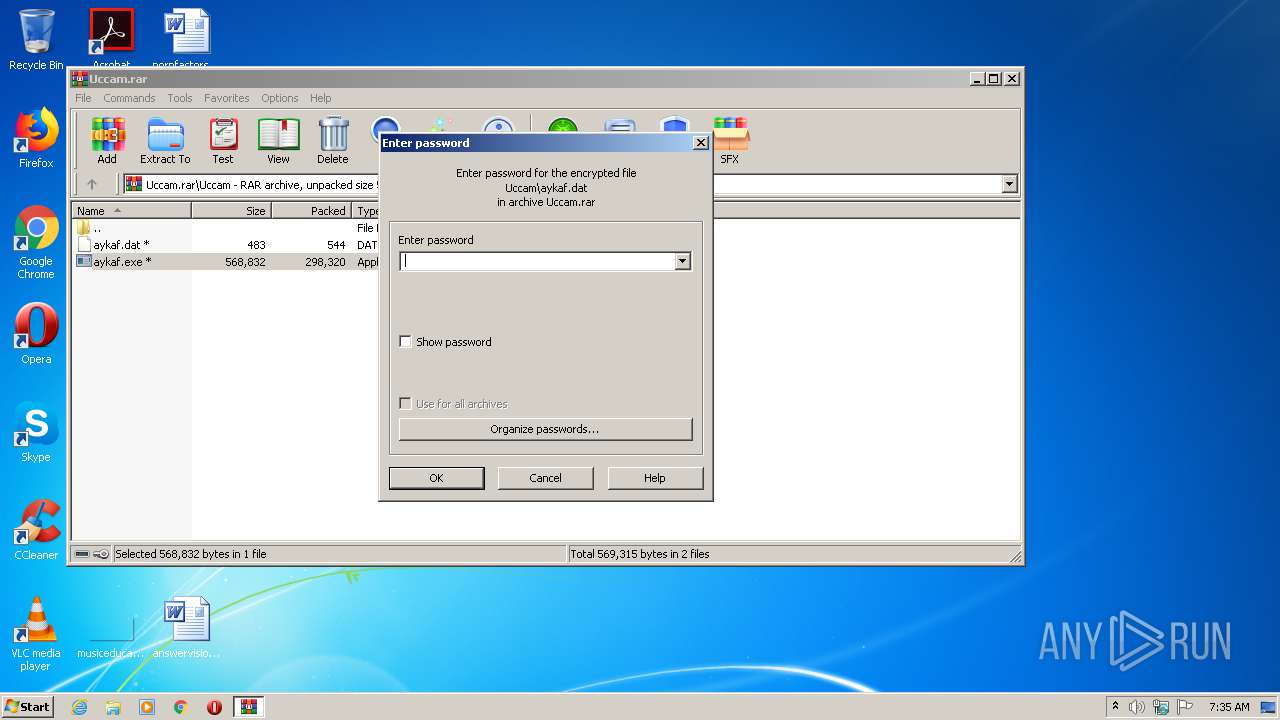
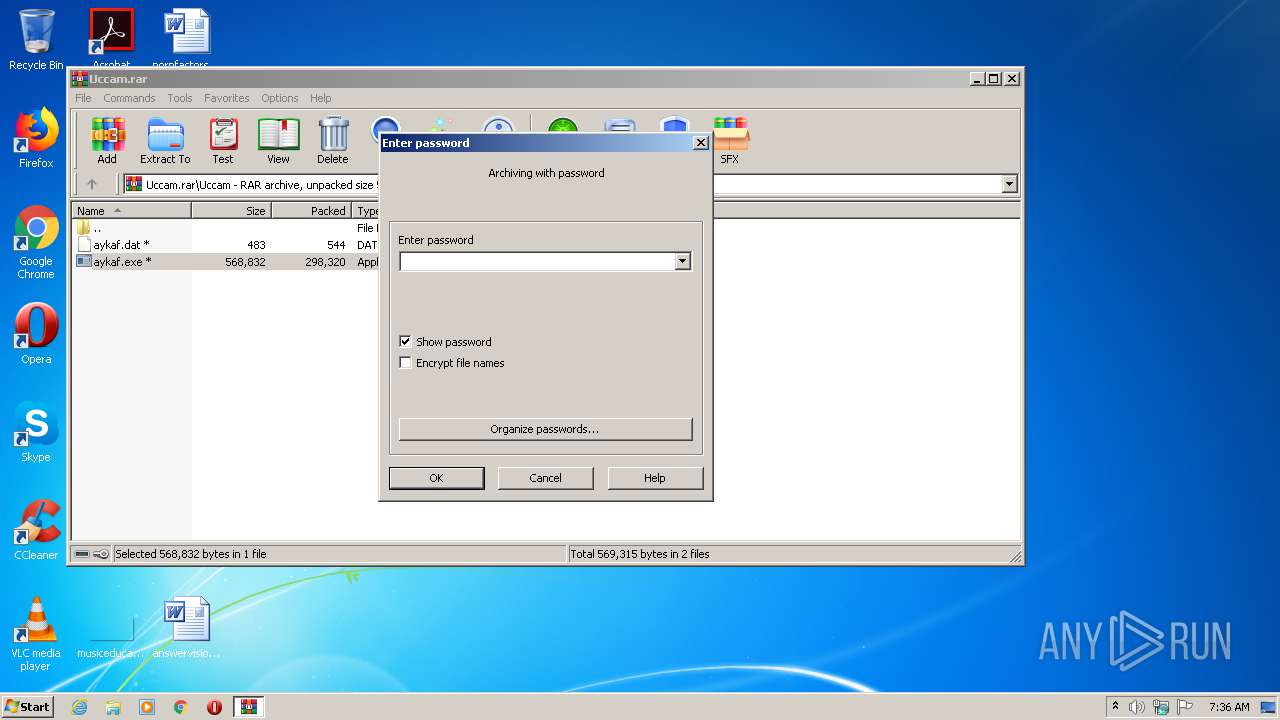
| (PID) Process: | (1496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
Executable files
1
Suspicious files
6
Text files
0
Unknown types
0
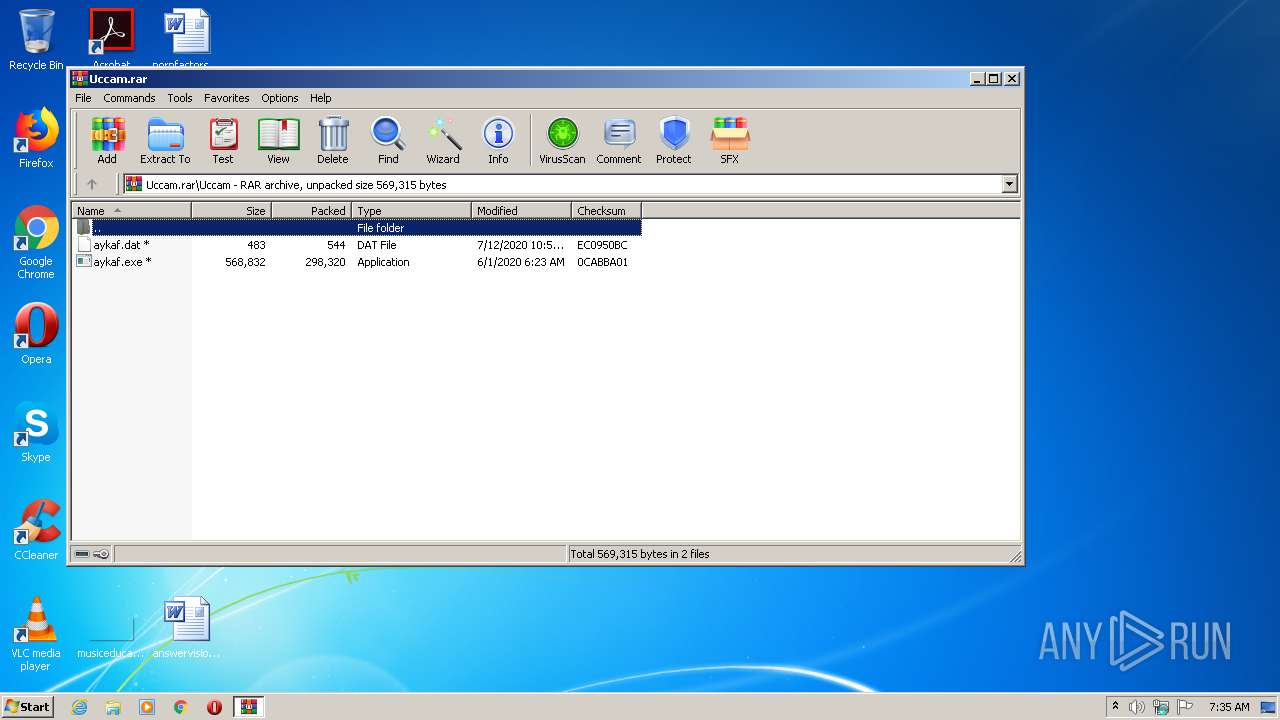
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rar_1496.364 | — | |
MD5:— | SHA256:— | |||
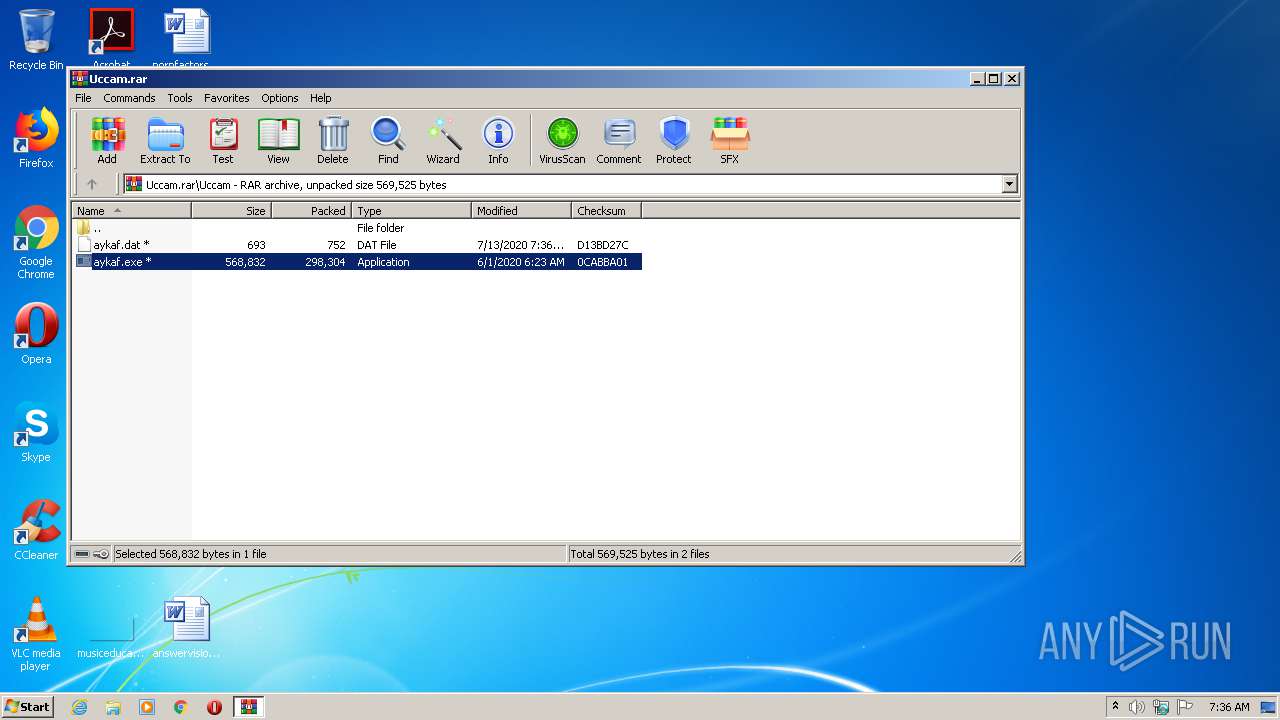
| 1496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.dat | binary | |
MD5:— | SHA256:— | |||
| 1496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.exe | executable | |
MD5:— | SHA256:— | |||
| 1496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Uccam.rar | compressed | |
MD5:— | SHA256:— | |||
| 1496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Uccam.bak1496.371 | compressed | |
MD5:— | SHA256:— | |||
| 2628 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1496.46789\Uccam\aykaf.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
10
DNS requests
3
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | explorer.exe | GET | 301 | 85.93.89.6:80 | http://www.ip-adress.com/ | DE | html | 234 b | shared |
2628 | explorer.exe | GET | 301 | 85.93.89.6:80 | http://www.ip-adress.com/ | DE | html | 234 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2628 | explorer.exe | 85.93.89.6:80 | www.ip-adress.com | Host Europe GmbH | DE | malicious |
2628 | explorer.exe | 85.93.89.6:443 | www.ip-adress.com | Host Europe GmbH | DE | malicious |
2628 | explorer.exe | 23.49.13.33:7000 | — | Akamai International B.V. | US | whitelisted |
2628 | explorer.exe | 68.116.183.68:443 | — | Charter Communications | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ip-adress.com |
| shared |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2628 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] External IP (possible Qbot) |
2628 | explorer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] External IP Address Check |
2628 | explorer.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2628 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] External IP (possible Qbot) |
2628 | explorer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] External IP Address Check |
2628 | explorer.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2 ETPRO signatures available at the full report